| File name: | mrsys.exe |
| Full analysis: | https://app.any.run/tasks/75f42c5a-efeb-4295-bb44-0843871eaabc |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2019, 19:11:13 |
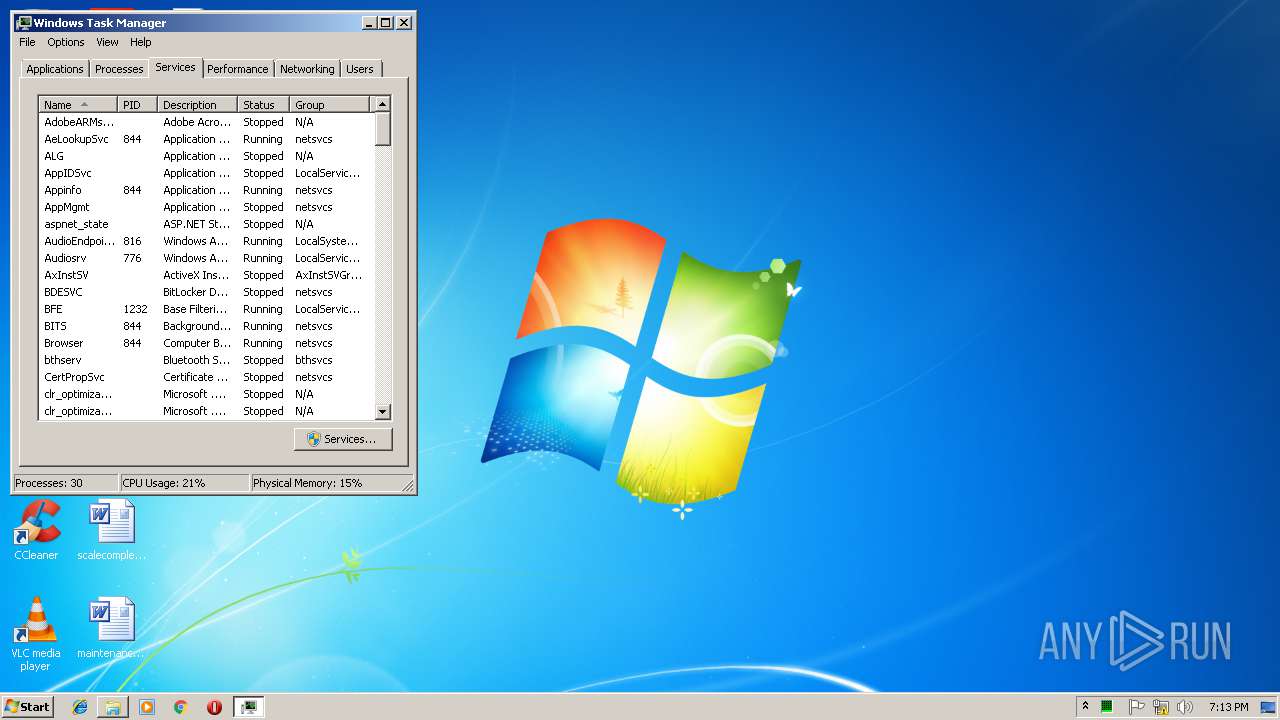
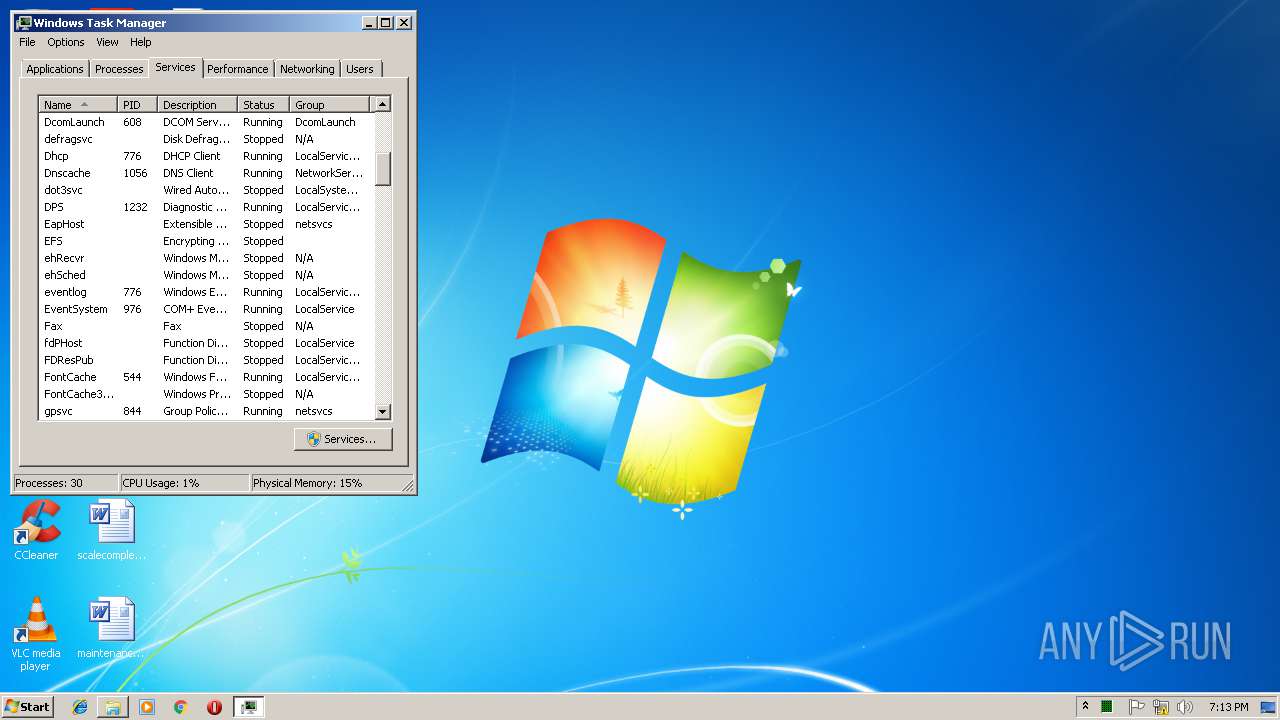
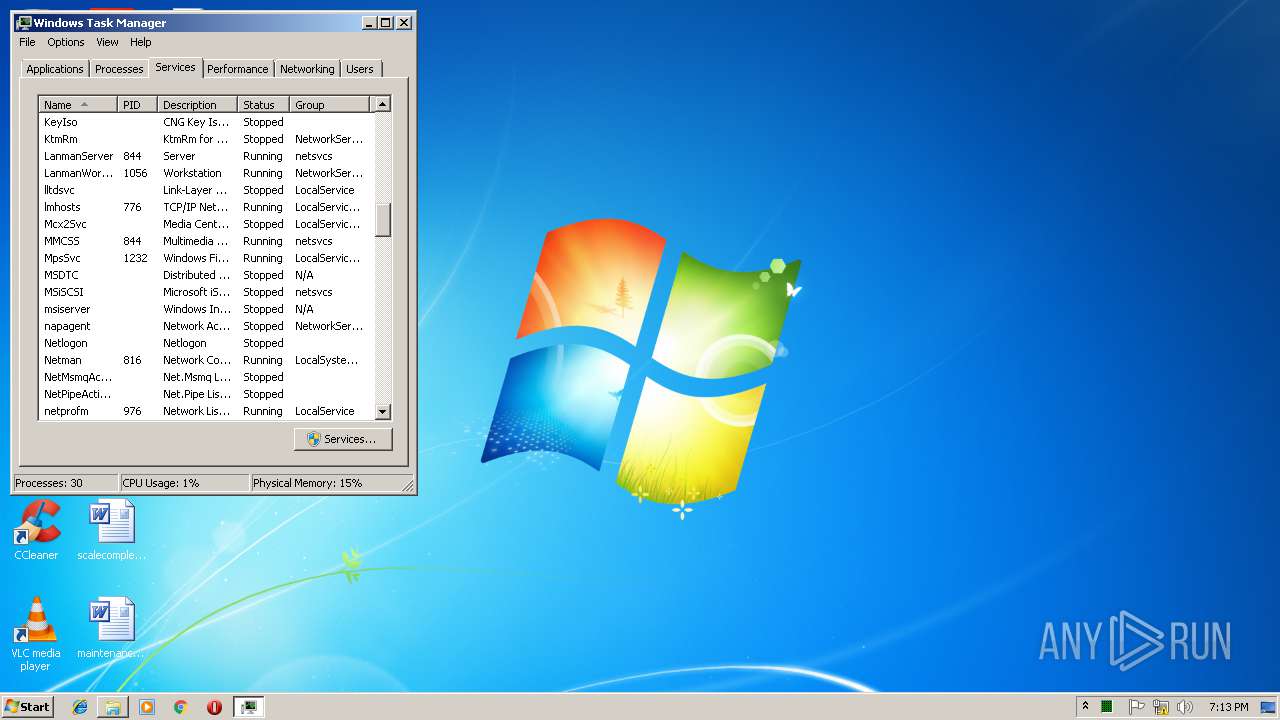
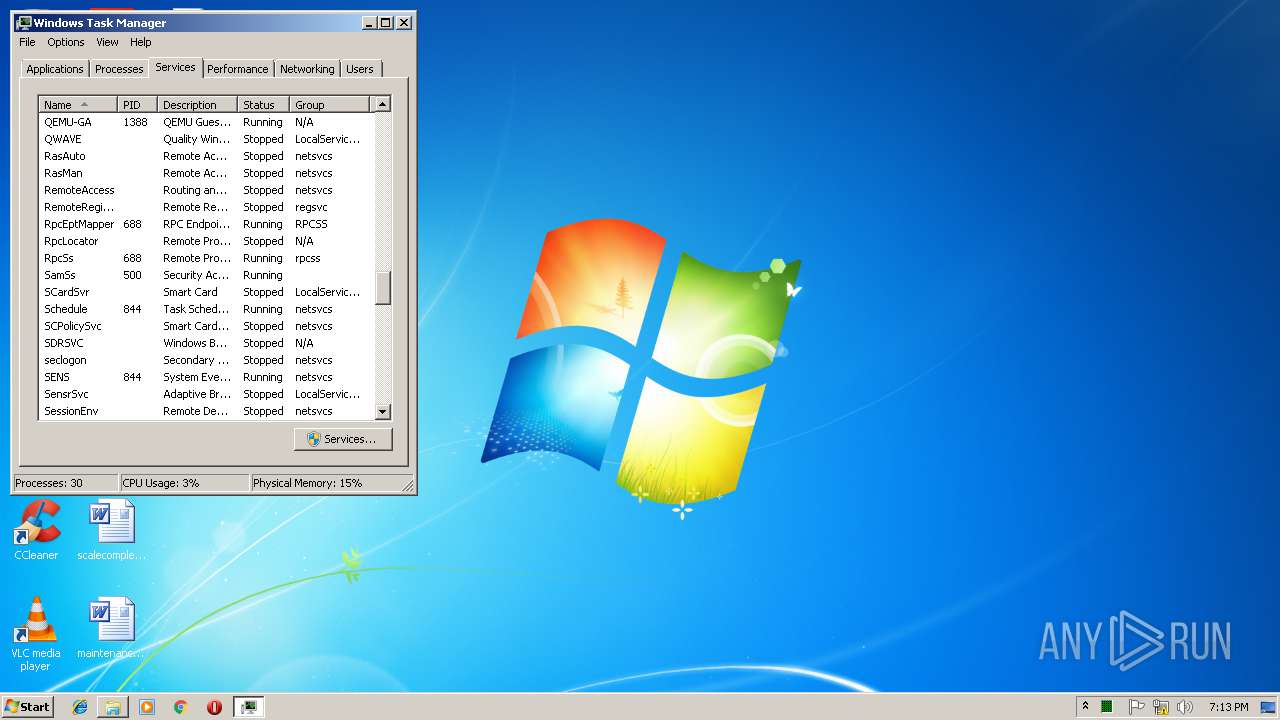
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8B835CE4E01BA60AB1DDC99E75F4A5A7 |
| SHA1: | 9178622ED018A7469EEE95A382F35570525FAAAD |
| SHA256: | 964DD9A8A687CA69415719B3F5BB8B5486FAB62191593F4AA5C2CBEE73B9EEAF |
| SSDEEP: | 3072:zvEfVUzSLhIVbV6i5LirrlZrHyrUHUckoMQ2RN6un1:zvEN2U+T6i5LirrllHy4HUcMQY6a |
MALICIOUS
Changes the login/logoff helper path in the registry
- explorer.exe (PID: 3108)
- svchost.exe (PID: 2432)
Changes the autorun value in the registry
- svchost.exe (PID: 2432)
- explorer.exe (PID: 3108)
SUSPICIOUS
Starts itself from another location
- mrsys.exe (PID: 3640)
- svchost.exe (PID: 2432)
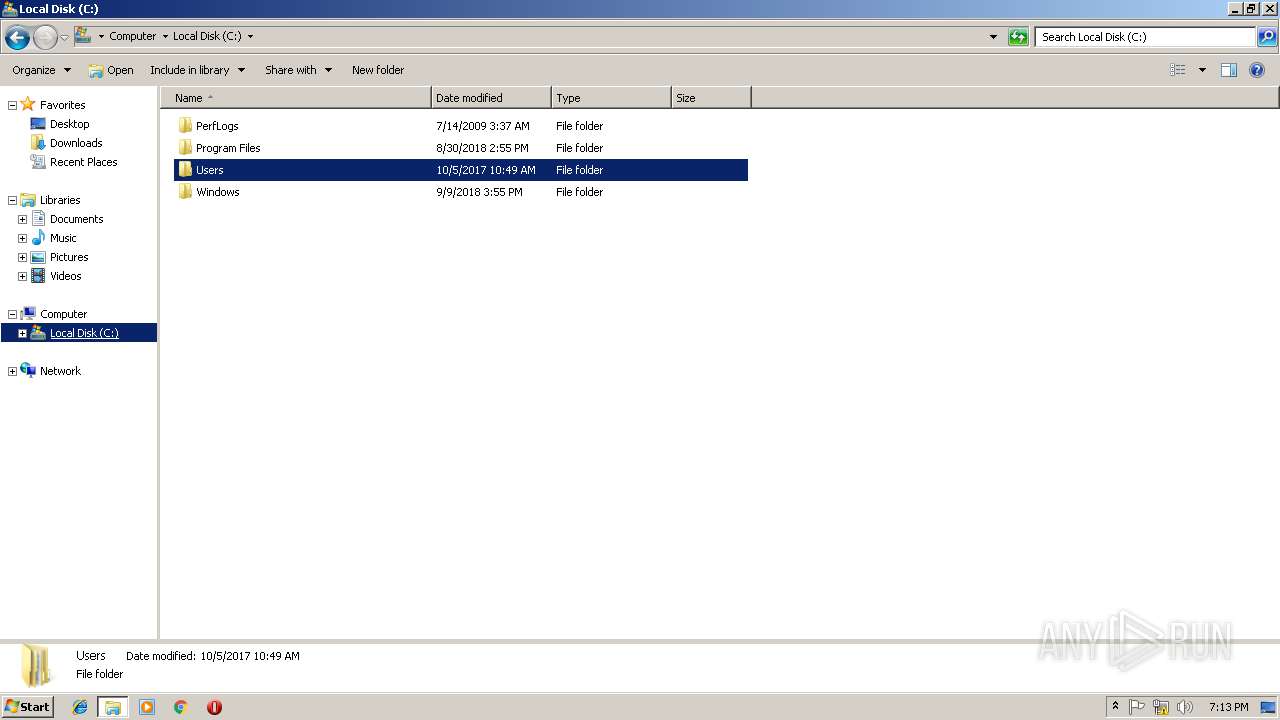
Creates files in the Windows directory
- explorer.exe (PID: 3108)
- spoolsv.exe (PID: 4032)
- mrsys.exe (PID: 3640)
Executable content was dropped or overwritten
- spoolsv.exe (PID: 4032)
- explorer.exe (PID: 3108)
- mrsys.exe (PID: 3640)
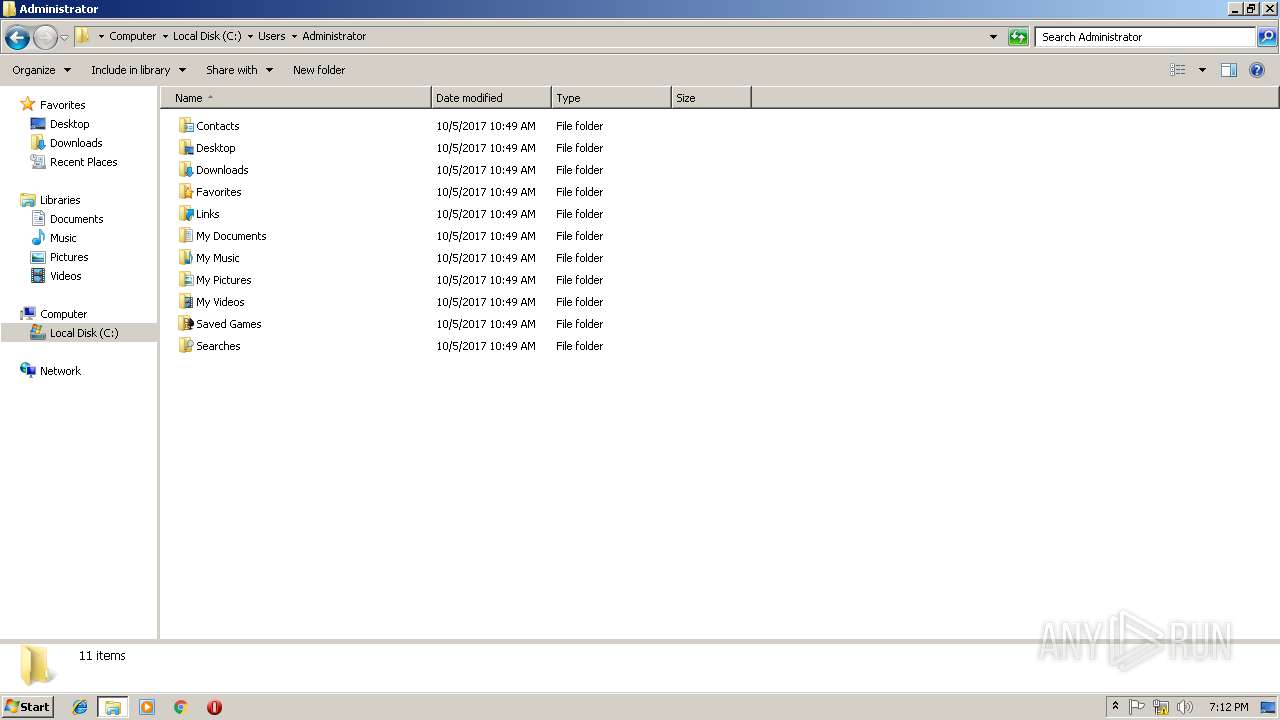
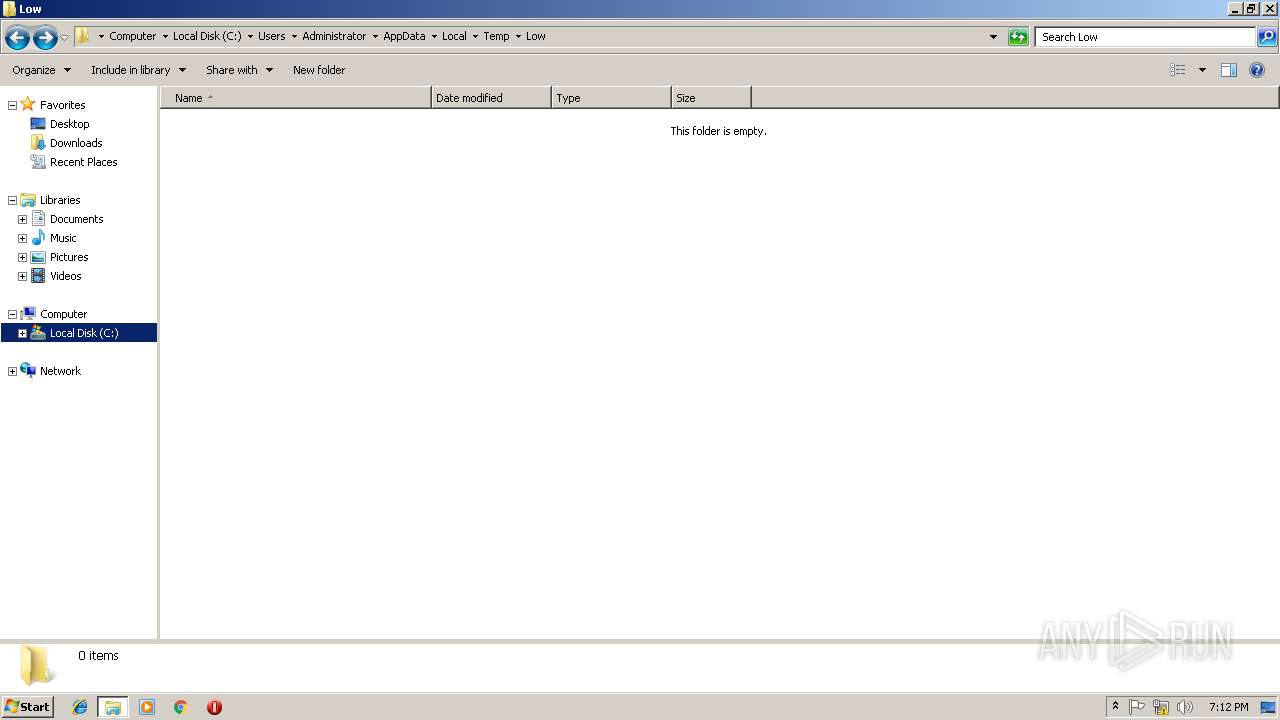
Creates files in the user directory
- explorer.exe (PID: 3108)
Removes files from Windows directory
- svchost.exe (PID: 2432)
- explorer.exe (PID: 3108)
- mrsys.exe (PID: 3640)
- spoolsv.exe (PID: 4032)
Creates executable files which already exist in Windows
- spoolsv.exe (PID: 4032)
- mrsys.exe (PID: 3640)
Creates or modifies windows services
- svchost.exe (PID: 2432)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (54.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (20.8) |
| .exe | | | Win64 Executable (generic) (18.4) |
| .exe | | | Win32 Executable (generic) (3) |
| .exe | | | Generic Win/DOS Executable (1.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:06:14 21:01:16+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 176128 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3670 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft |
| ProductName: | Win |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | Win |
| OriginalFileName: | Win.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2011 19:01:16 |
| Detected languages: |
|
| CompanyName: | Microsoft |
| ProductName: | Win |
| FileVersion: | 1.00 |
| ProductVersion: | 1.00 |
| InternalName: | Win |
| OriginalFilename: | Win.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 14-Jun-2011 19:01:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002A728 | 0x0002B000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.9472 |
.data | 0x0002C000 | 0x00001B74 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002E000 | 0x000005E0 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.39541 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.12197 | 500 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 2.08785 | 3280 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
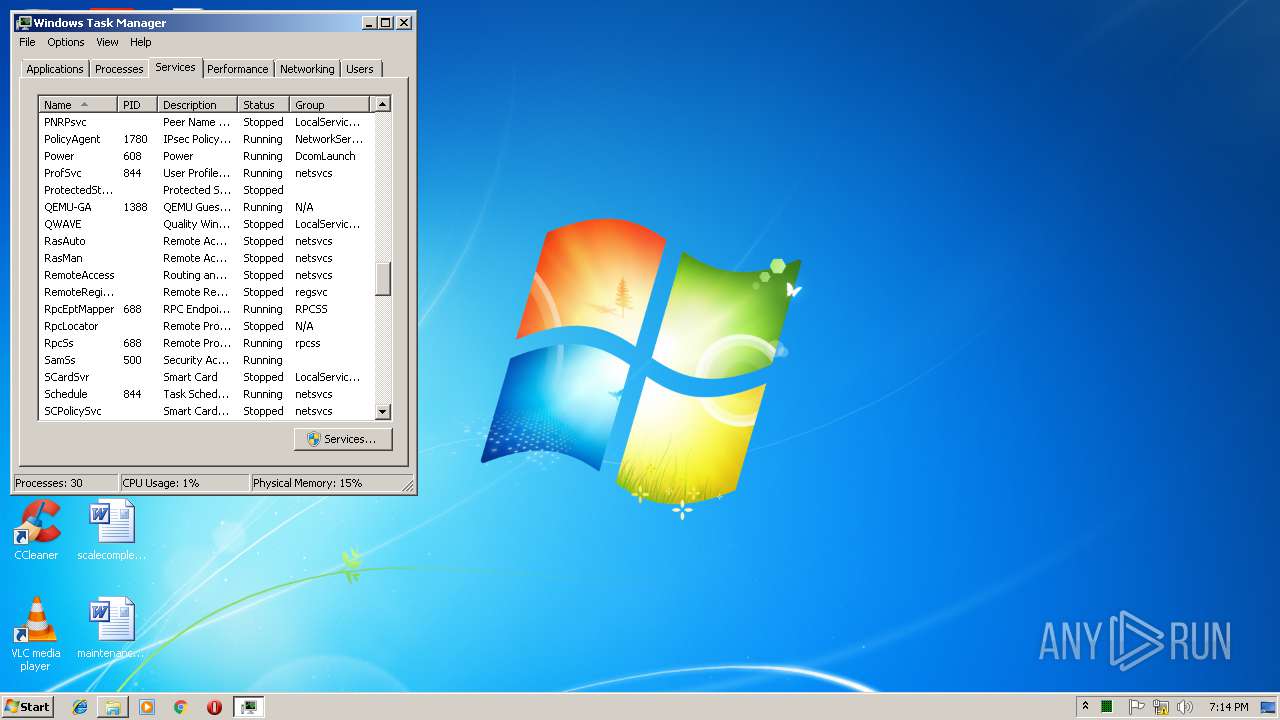
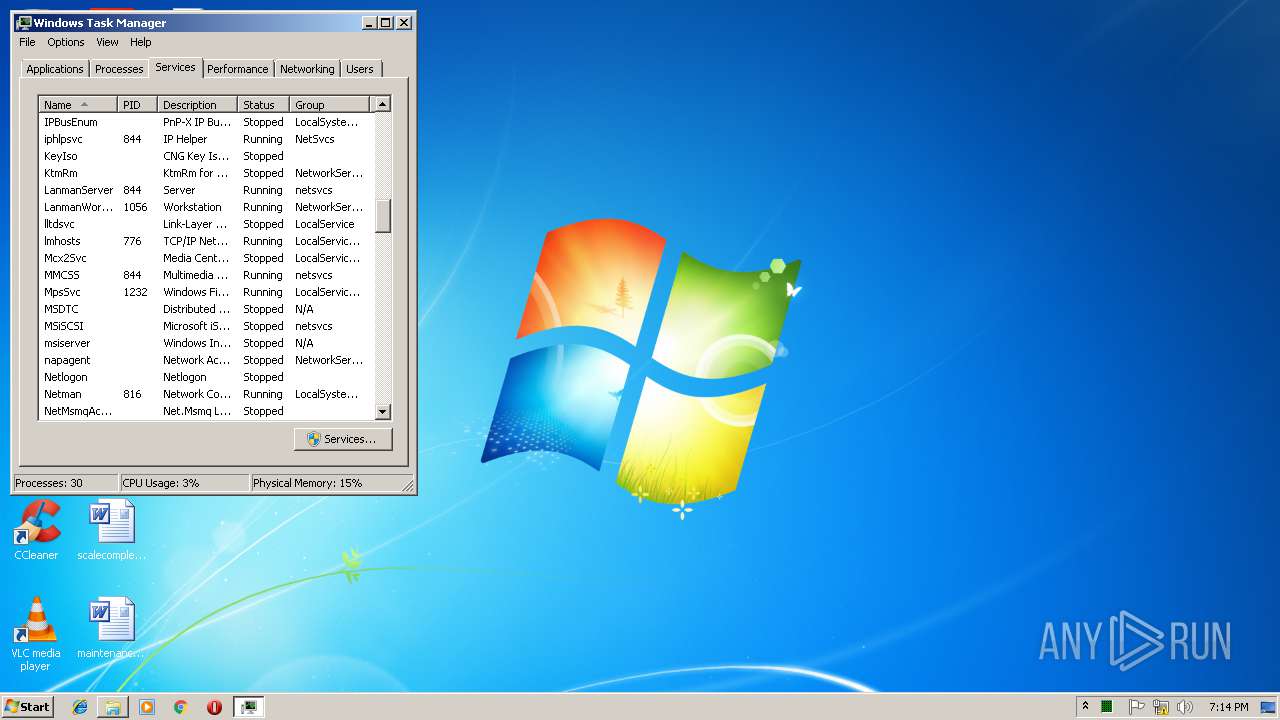
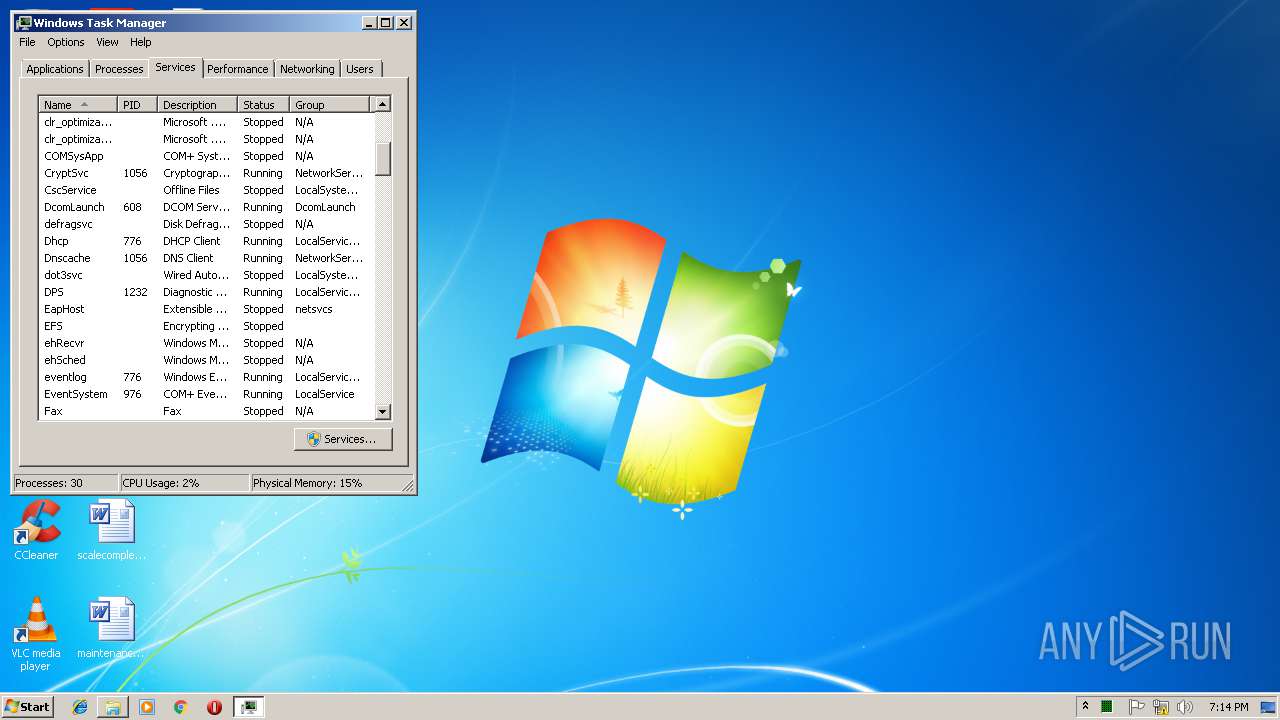
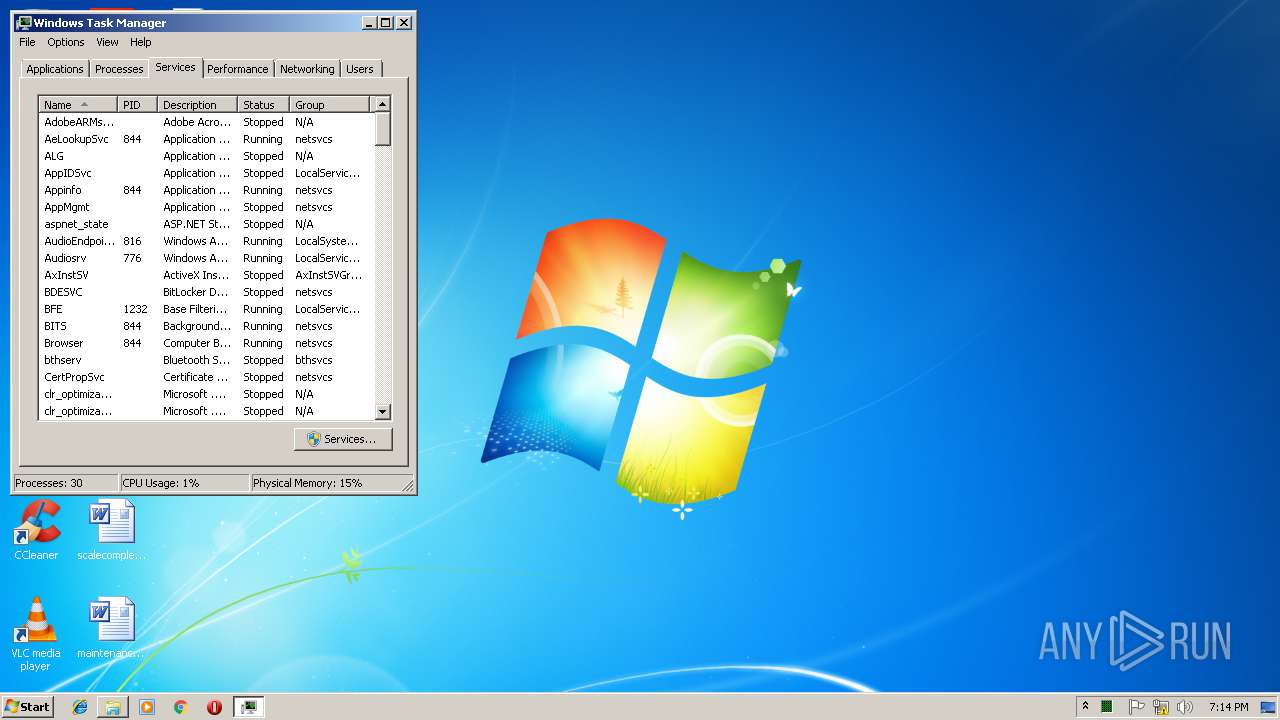
Total processes
56
Monitored processes
13
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | at 19:17 /interactive /every:M,T,W,Th,F,S,Su c:\windows\system\svchost.exe | C:\Windows\system32\at.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Schedule service command line interface Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
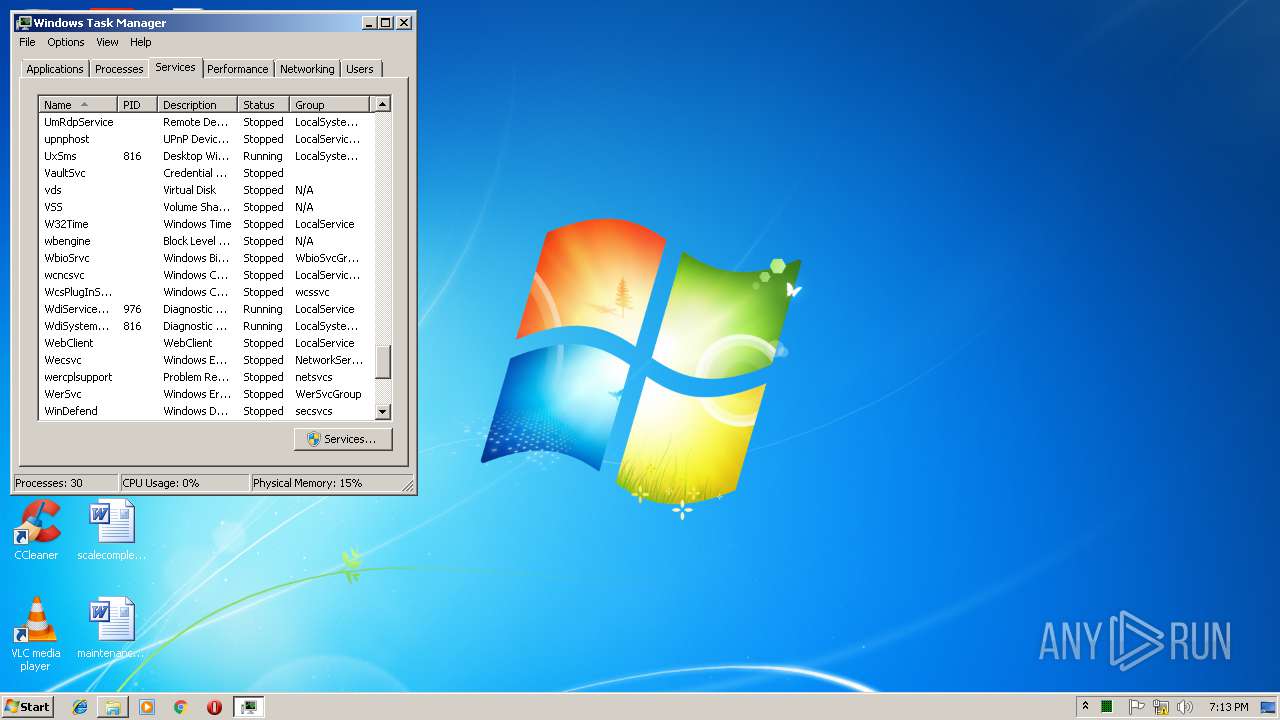
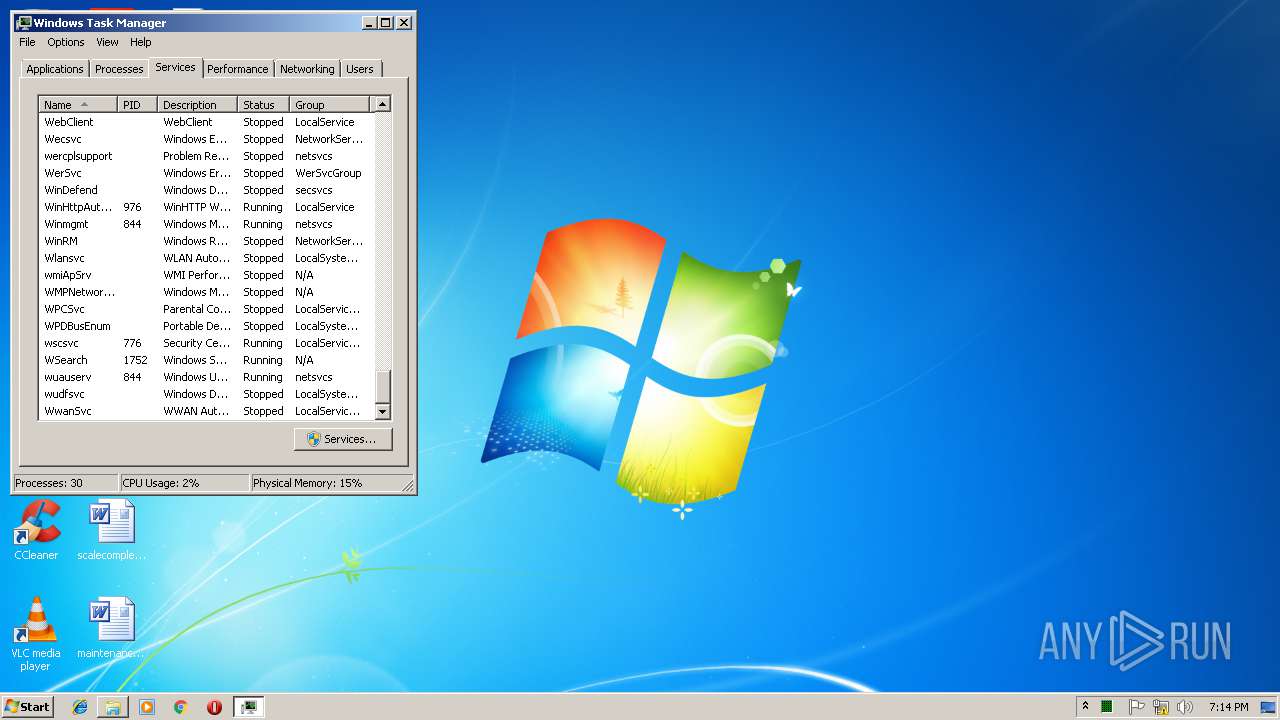
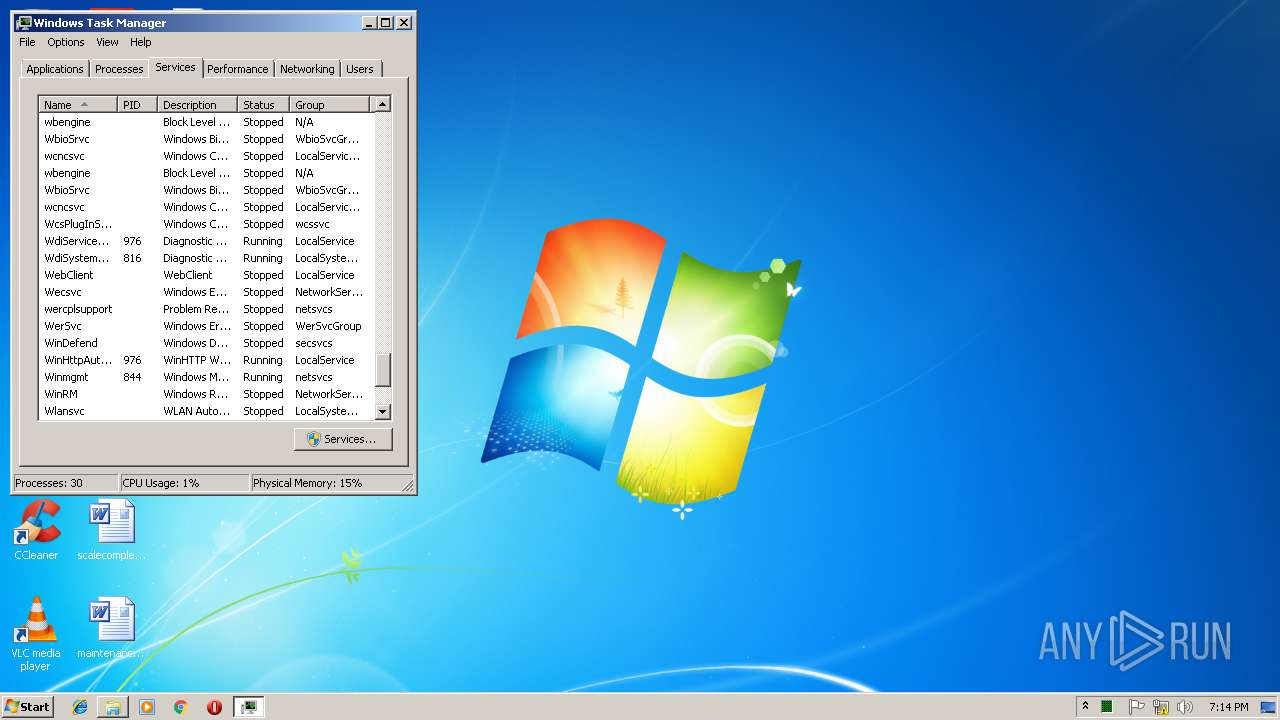
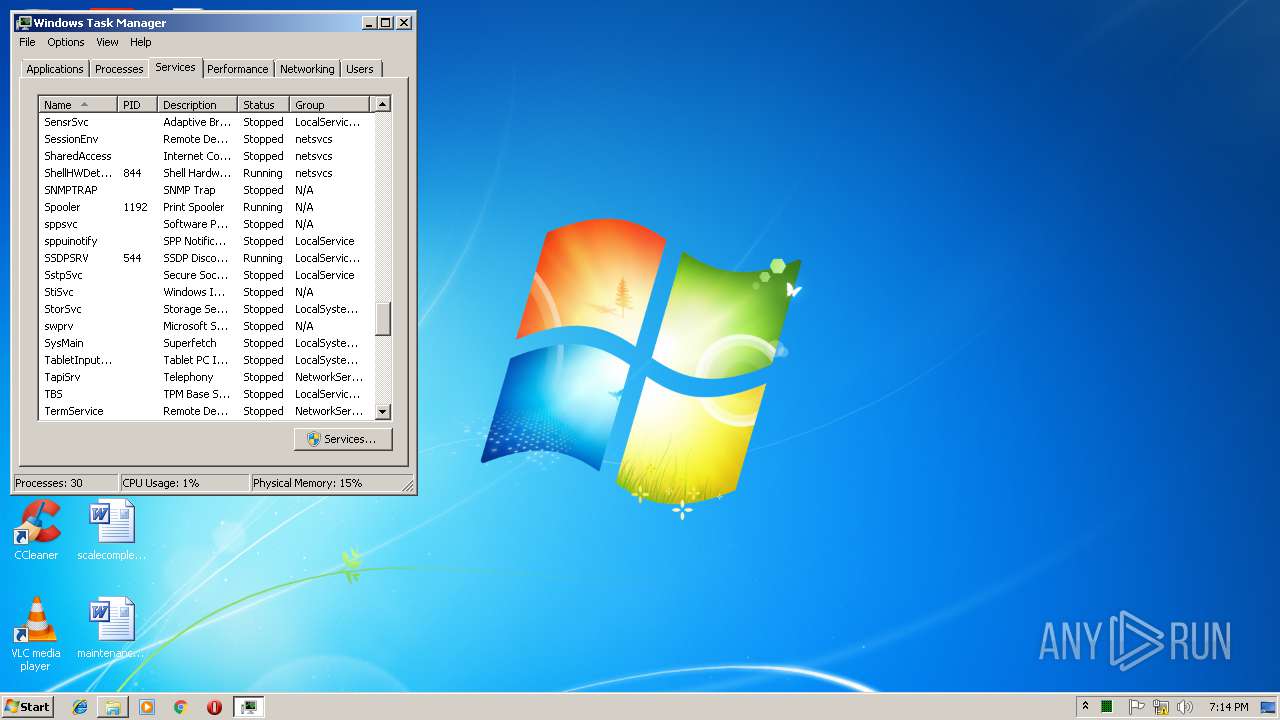
| 2308 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2320 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2404 | at 19:15 /interactive /every:M,T,W,Th,F,S,Su c:\windows\system\svchost.exe | C:\Windows\system32\at.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Schedule service command line interface Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | c:\windows\system\svchost.exe | c:\windows\system\svchost.exe | spoolsv.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2576 | at 19:16 /interactive /every:M,T,W,Th,F,S,Su c:\windows\system\svchost.exe | C:\Windows\system32\at.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Schedule service command line interface Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2884 | at 19:18 /interactive /every:M,T,W,Th,F,S,Su c:\windows\system\svchost.exe | C:\Windows\system32\at.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Schedule service command line interface Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
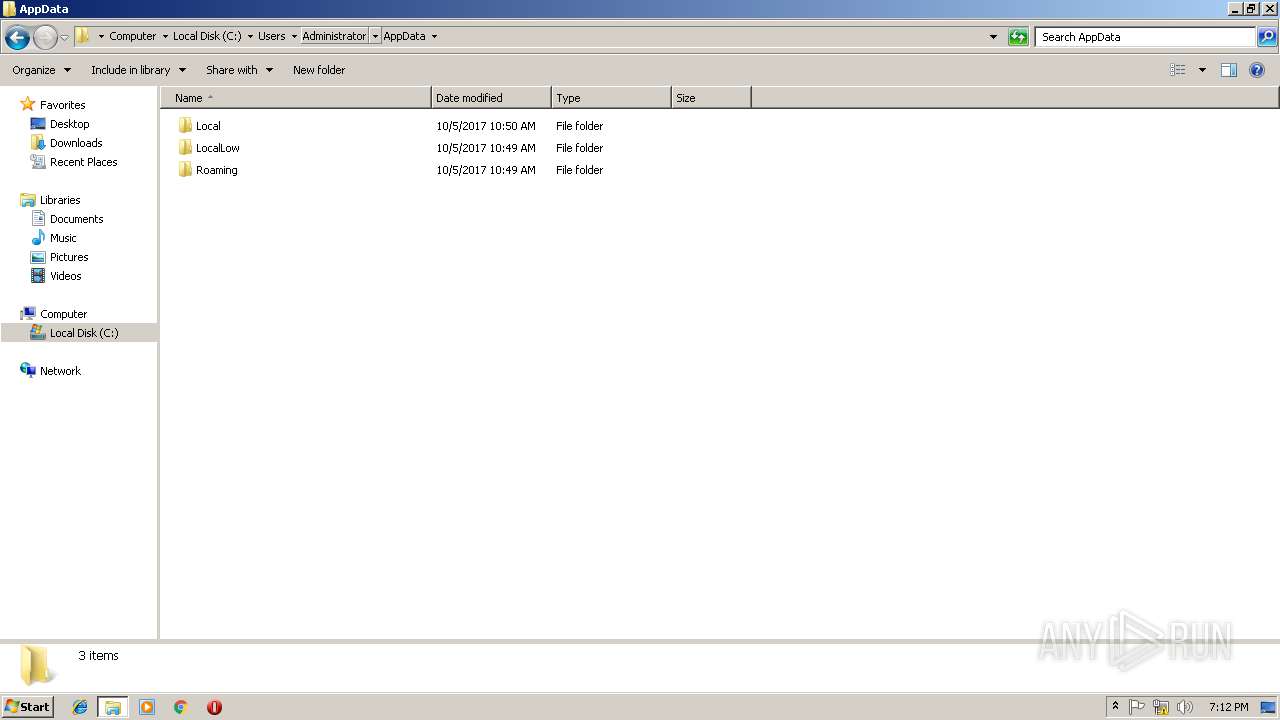
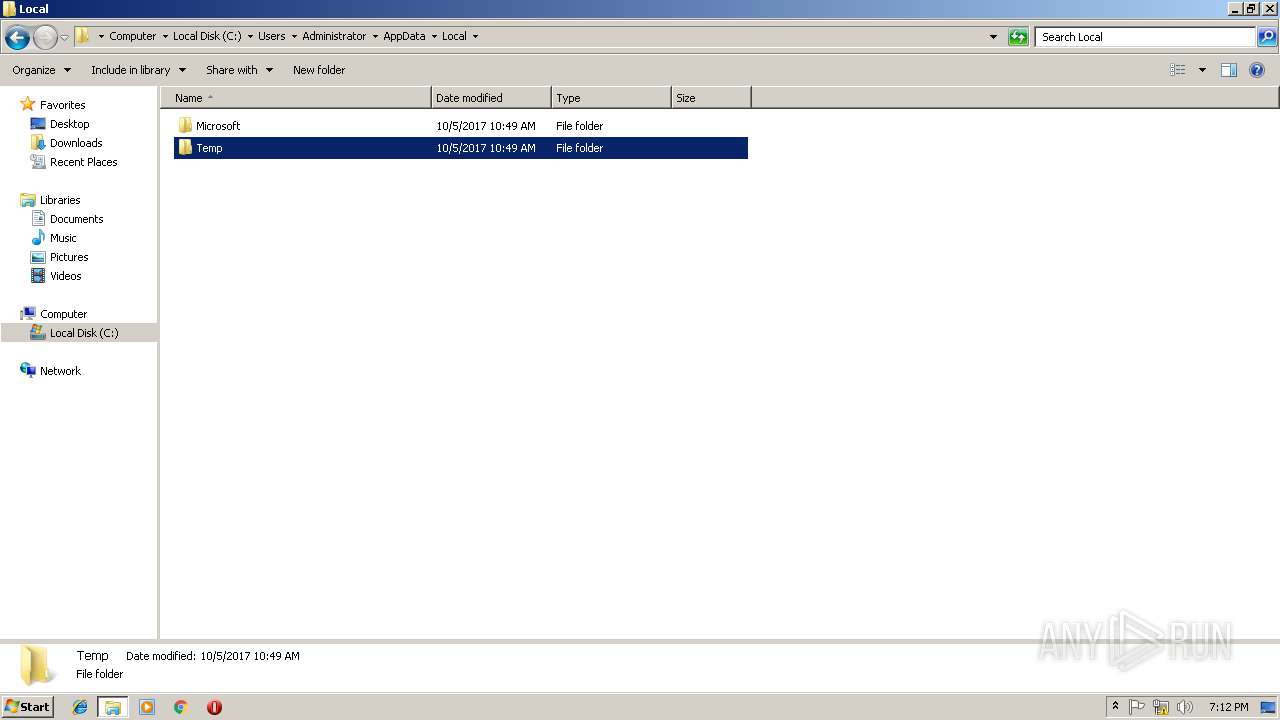
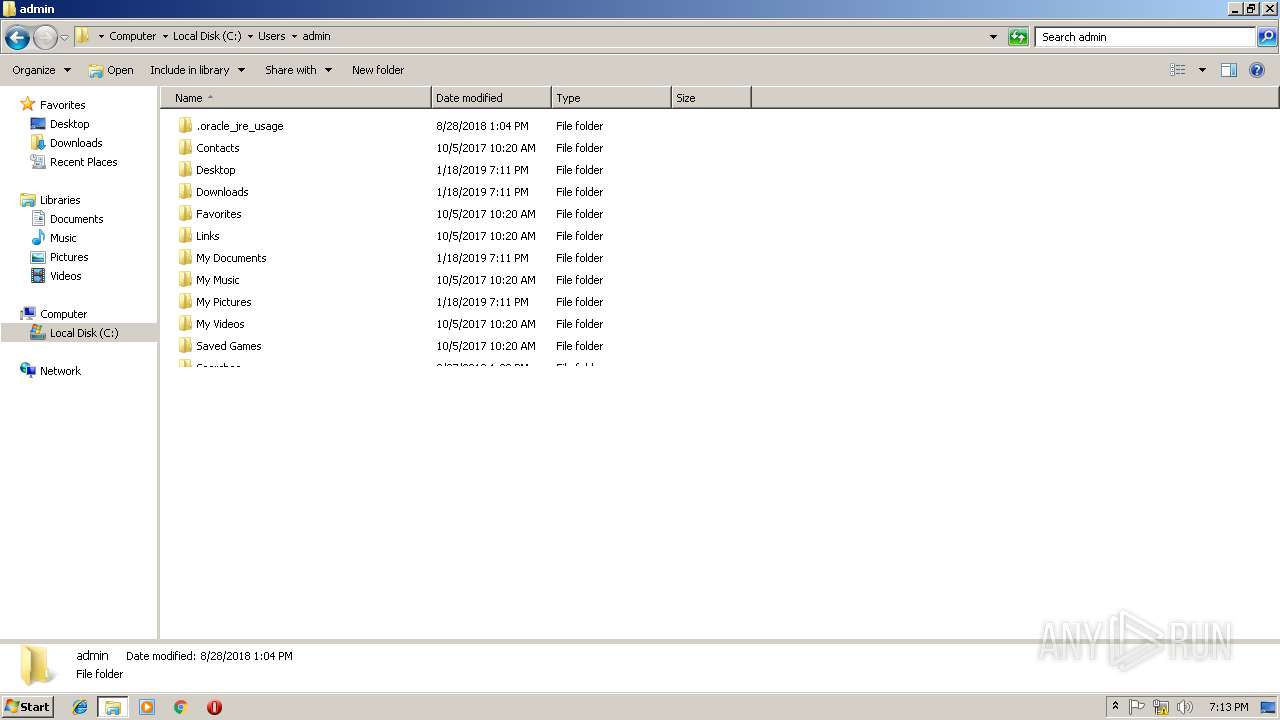
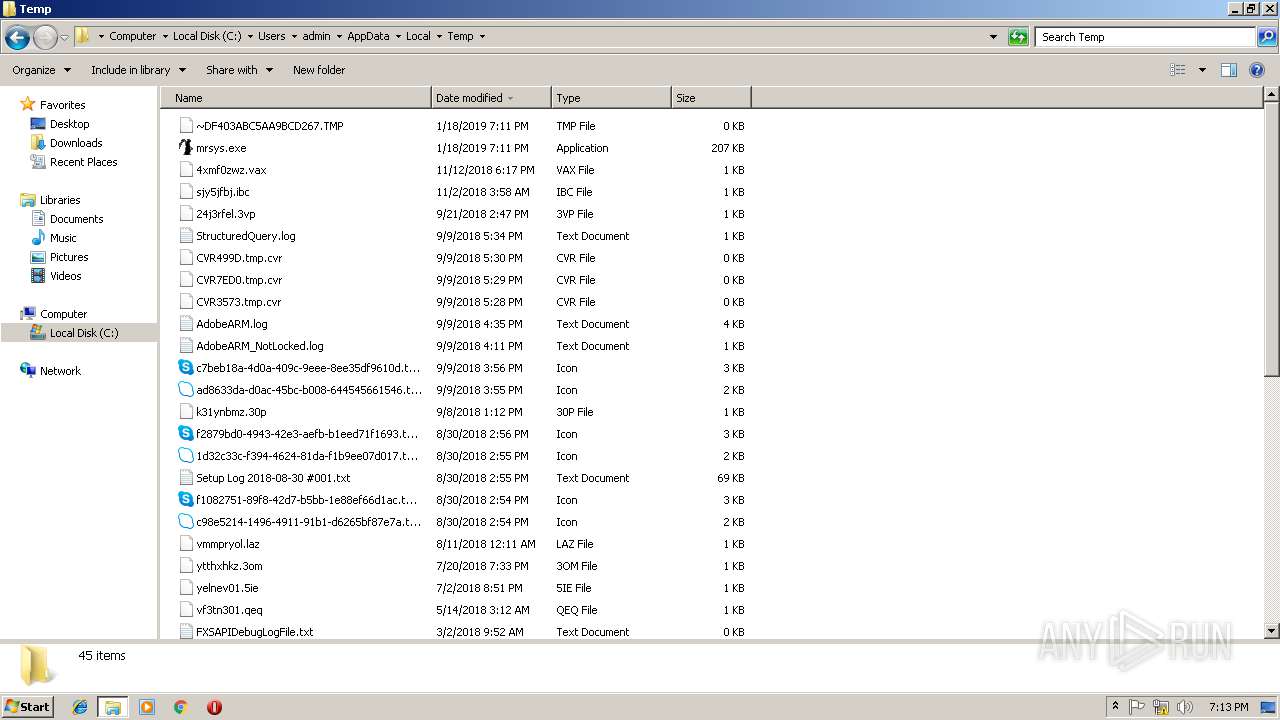
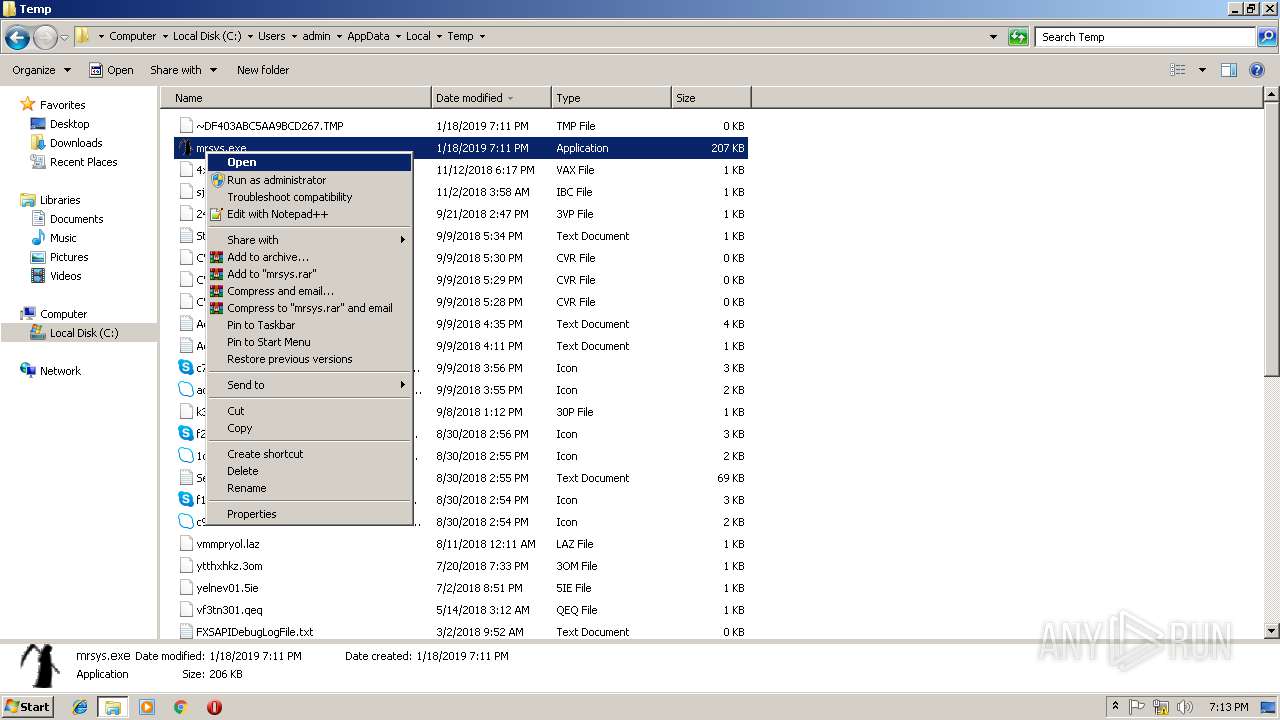
| 2932 | "C:\Users\admin\AppData\Local\Temp\mrsys.exe" | C:\Users\admin\AppData\Local\Temp\mrsys.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3108 | c:\windows\system\explorer.exe | c:\windows\system\explorer.exe | mrsys.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
263
Read events
204
Write events
55
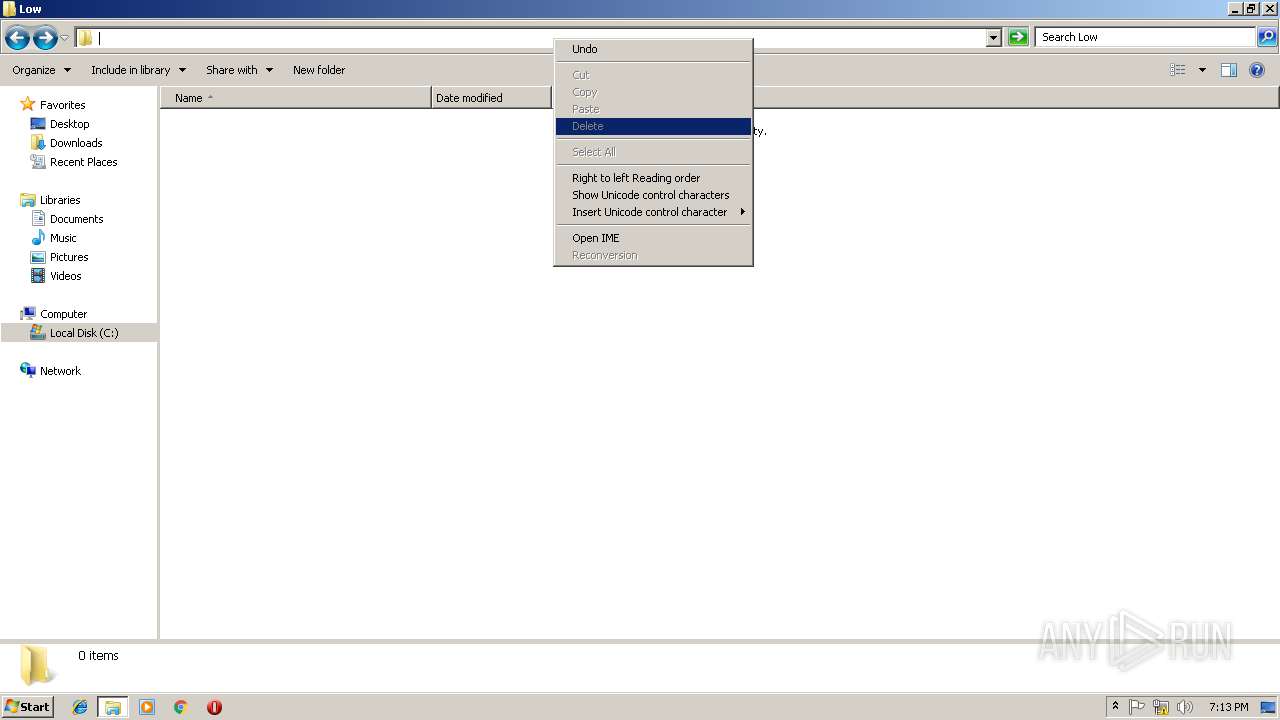
Delete events
4
Modification events
| (PID) Process: | (2932) mrsys.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (3640) mrsys.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (3108) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\system\explorer.exe RO | |||
| (PID) Process: | (3108) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\system\svchost.exe RO | |||
| (PID) Process: | (3108) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | shell |
Value: C:\Windows\explorer.exe, c:\windows\system\explorer.exe | |||
| (PID) Process: | (3108) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Active Setup\Installed Components\{Y479C6D0-OTRW-U5GH-S1EE-E0AC10B4E666} |
| Operation: | write | Name: | StubPath |
Value: C:\Users\admin\AppData\Roaming\mrsys.exe MR | |||
| (PID) Process: | (2432) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\system\explorer.exe RO | |||
| (PID) Process: | (2432) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\system\svchost.exe RO | |||
| (PID) Process: | (2432) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | shell |
Value: C:\Windows\explorer.exe, c:\windows\system\explorer.exe | |||
| (PID) Process: | (2432) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Active Setup\Installed Components\{F146C9B1-VMVQ-A9RC-NUFL-D0BA00B4E999} |
| Operation: | write | Name: | StubPath |
Value: C:\Users\admin\AppData\Roaming\mrsys.exe MR | |||
Executable files
4
Suspicious files
0
Text files
0
Unknown types
0
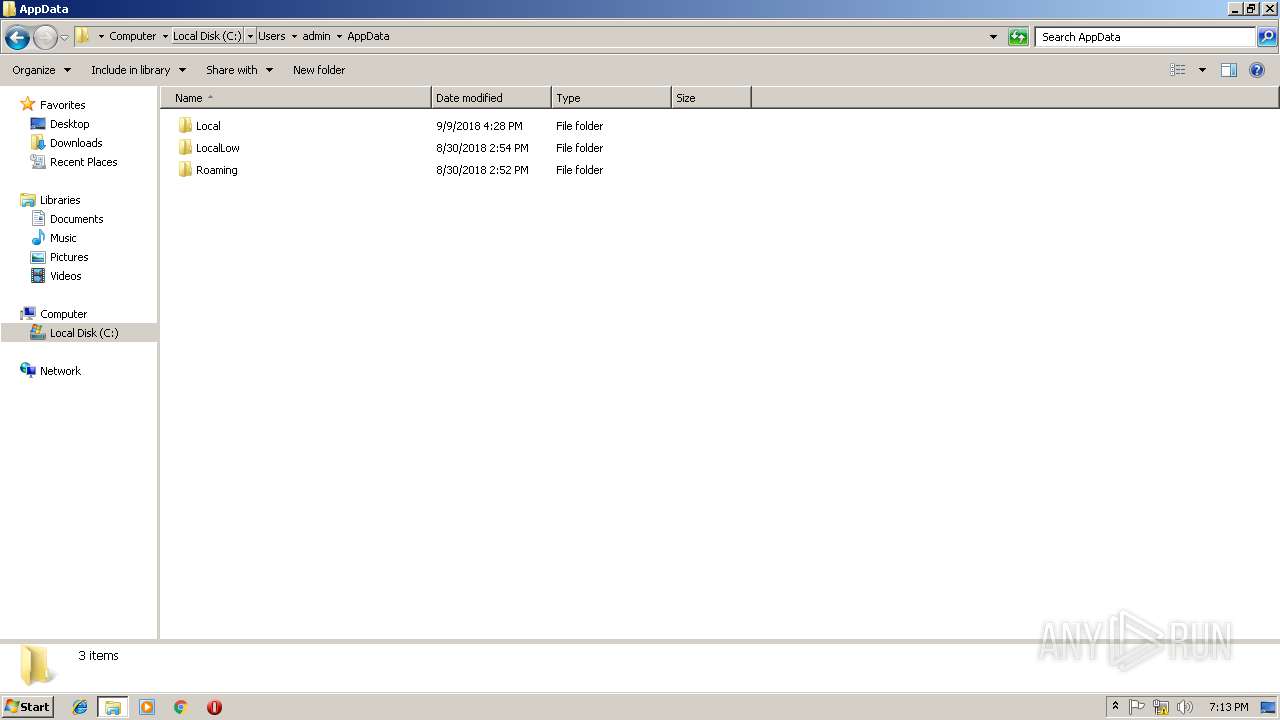
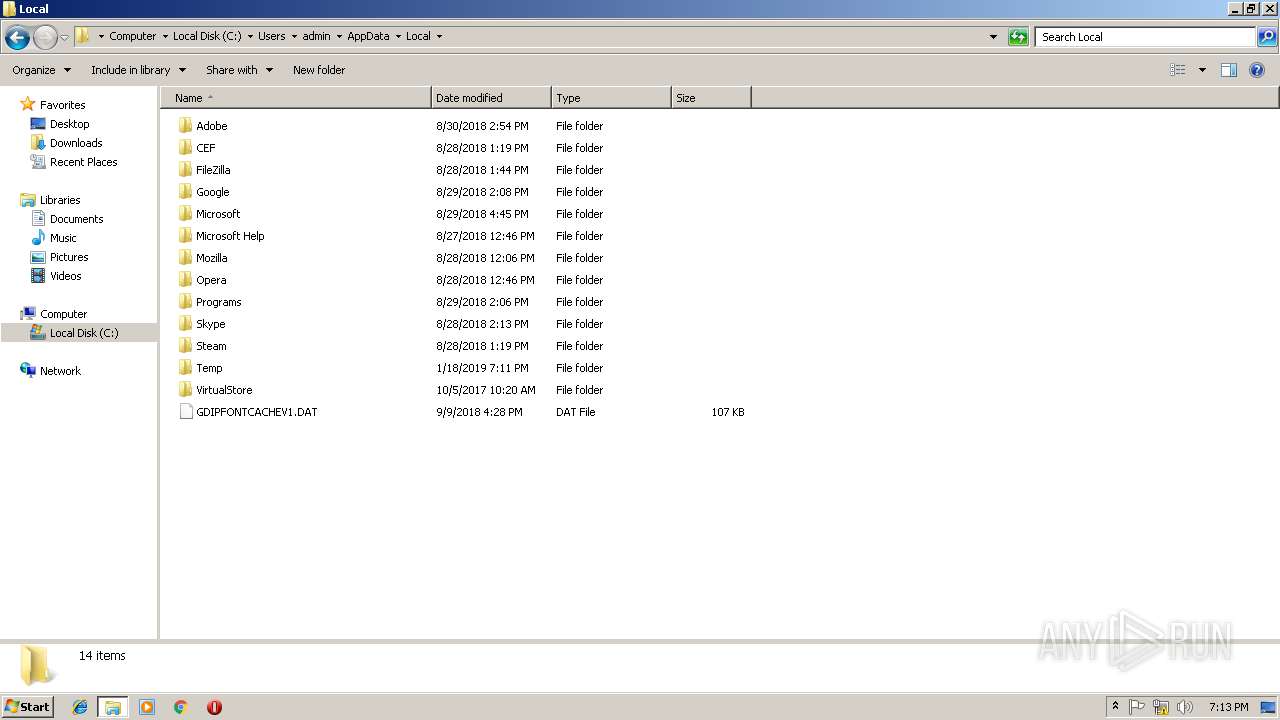
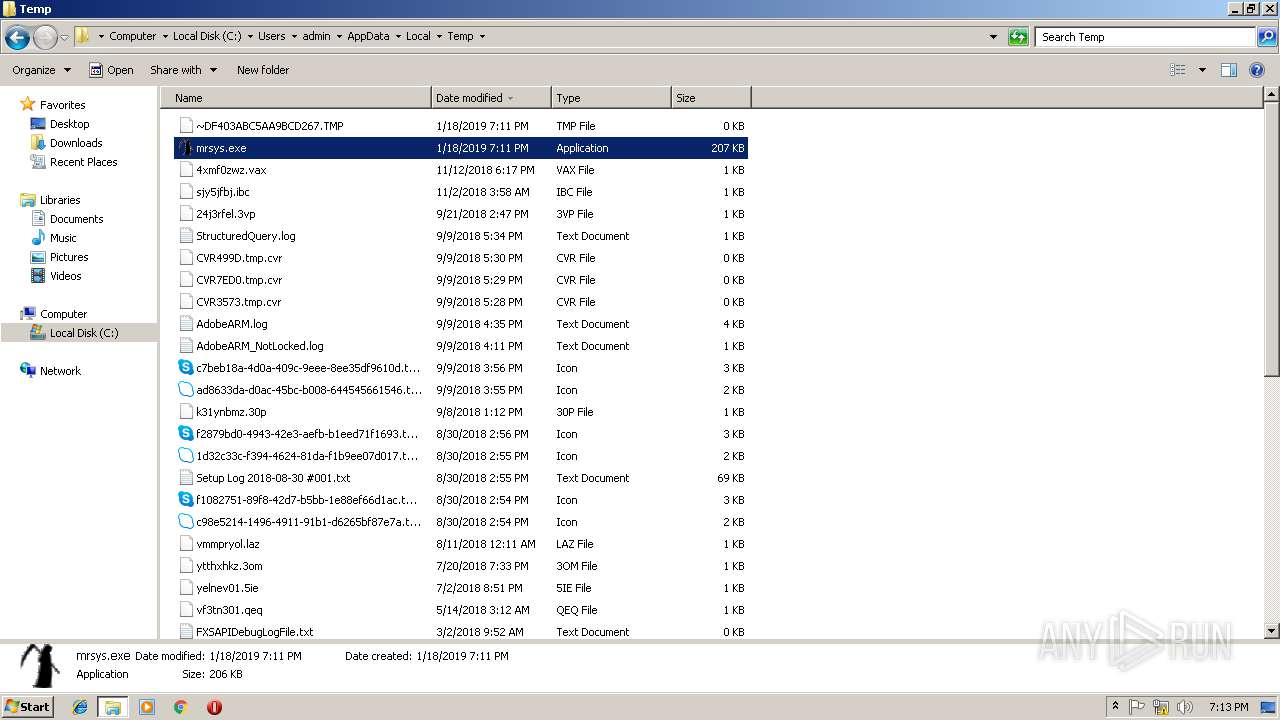
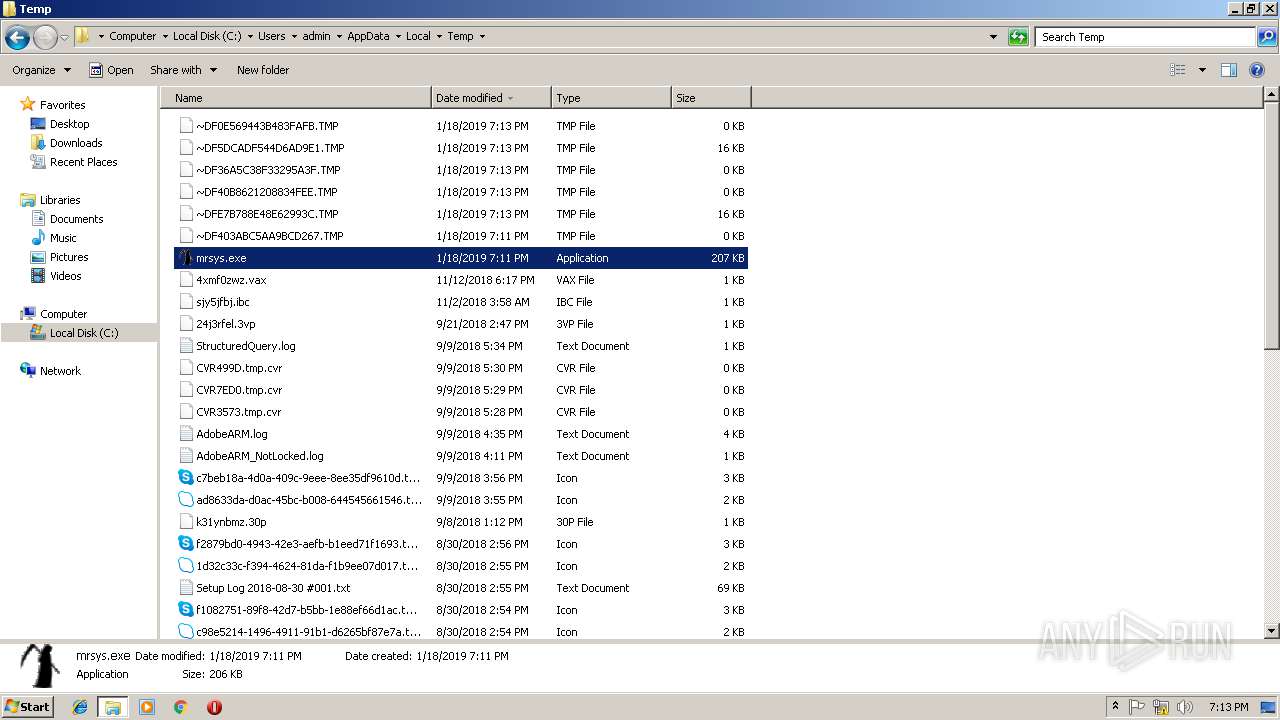
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
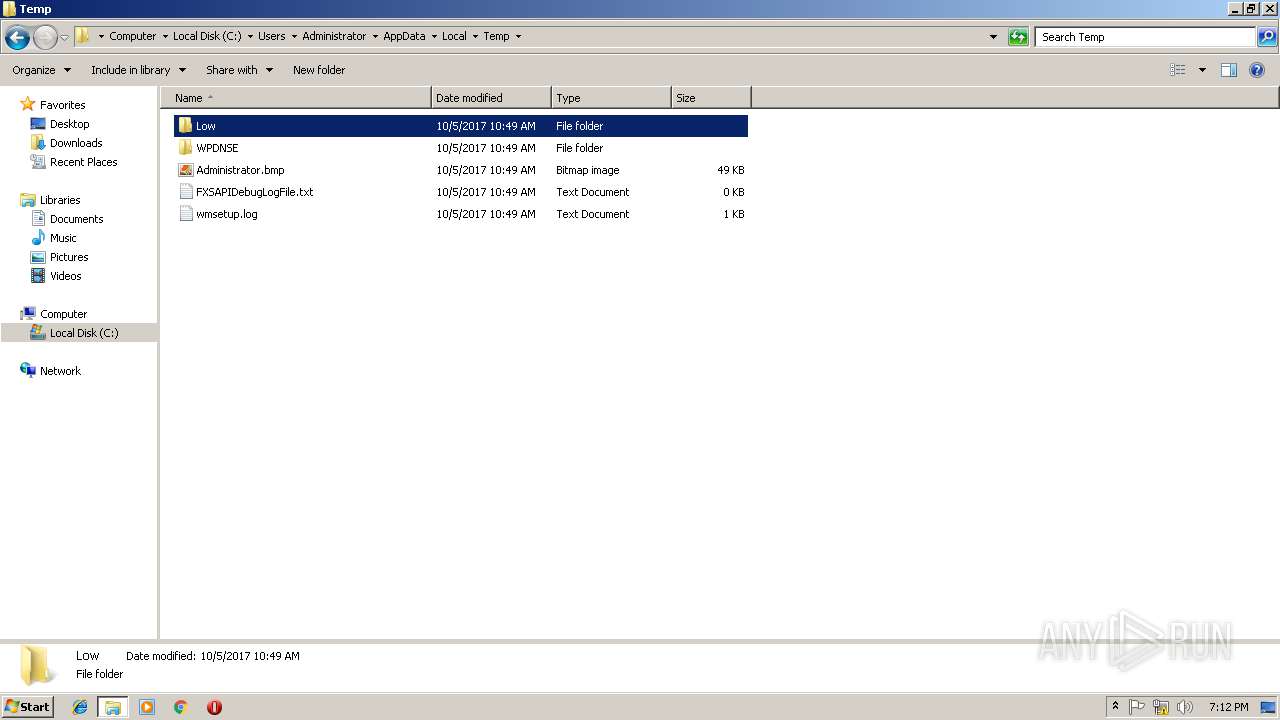
| 2932 | mrsys.exe | C:\Users\admin\AppData\Local\Temp\~DF403ABC5AA9BCD267.TMP | — | |
MD5:— | SHA256:— | |||
| 3552 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DF40B8621208834FEE.TMP | — | |
MD5:— | SHA256:— | |||
| 4032 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DF36A5C38F33295A3F.TMP | — | |
MD5:— | SHA256:— | |||
| 3640 | mrsys.exe | C:\Users\admin\AppData\Local\Temp\~DF0E569443B483FAFB.TMP | — | |
MD5:— | SHA256:— | |||
| 3640 | mrsys.exe | C:\windows\system\explorer.exe | executable | |
MD5:81E340796AD20C47F0C05DC3F387EE77 | SHA256:7AC2F20CBB36767BB1528F1AF42ED63136D20D9B33081A940EFD91EB8A9D4B83 | |||
| 3108 | explorer.exe | C:\windows\system\spoolsv.exe | executable | |
MD5:A92F341FE92E29426B2B04ED8B6D6DD2 | SHA256:9BAF8E62630933C78952625714F324E58697D4265079F4239E4EEDF631C113B2 | |||
| 3108 | explorer.exe | C:\Users\admin\AppData\Roaming\mrsys.exe | executable | |
MD5:5135293CEAA9F40F647B44FA48D52787 | SHA256:B001119F35BA08978EB915B4E1210074BBA22C4412D34F8EFAE8CC31464A537B | |||
| 4032 | spoolsv.exe | C:\windows\system\svchost.exe | executable | |
MD5:86730B5CA2A036AEA6974B64CF93FF8B | SHA256:6B69A160F630E38DDF8FF874AD76DED3D493ABCCC740576E2E5CFDCA9FC61F52 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report