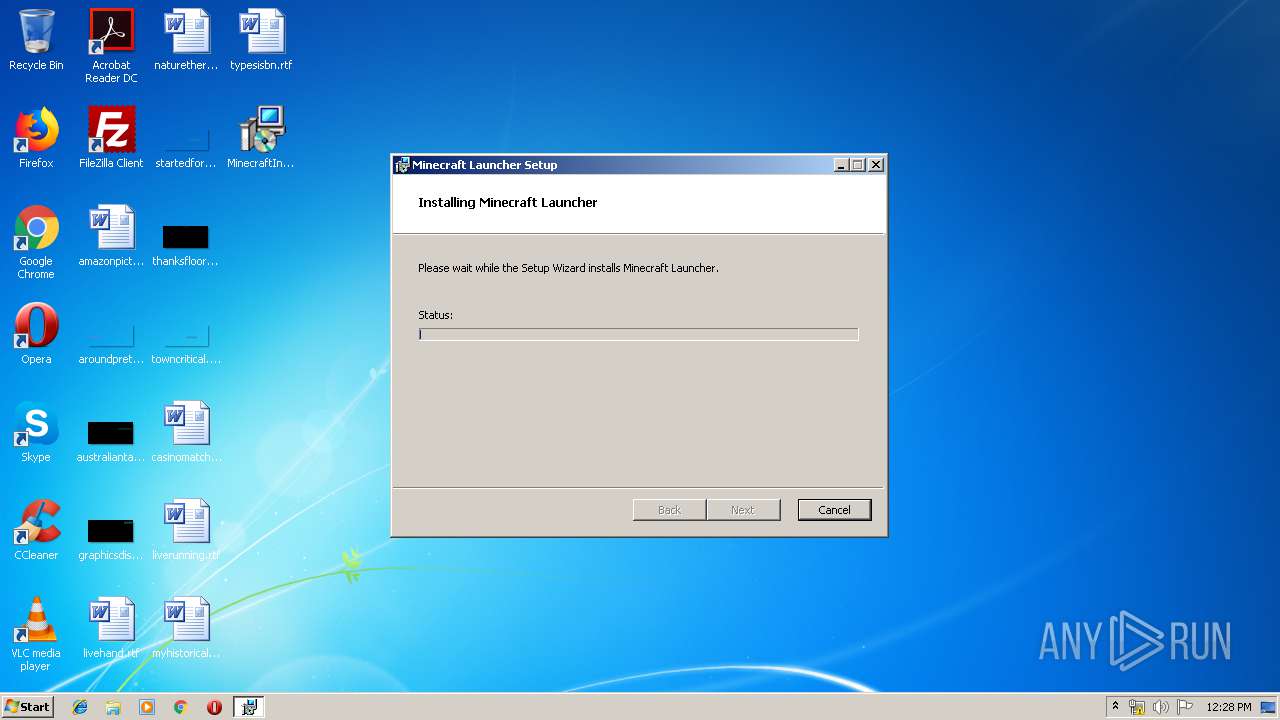
| File name: | MinecraftInstaller.msi |
| Full analysis: | https://app.any.run/tasks/3d30af14-5c73-4052-848f-0adc5680a28c |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2019, 11:27:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
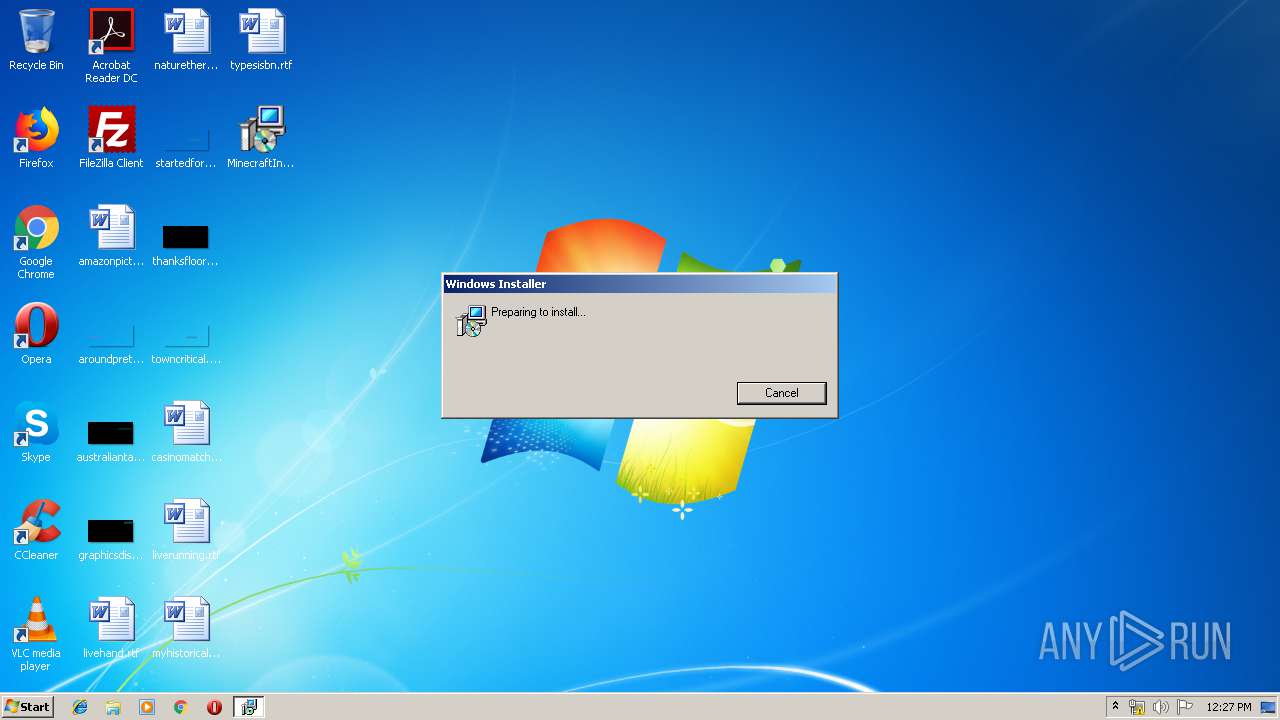
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Minecraft Launcher, Author: Mojang, Keywords: Installer, Comments: This installer database contains the logic and data required to install Minecraft Launcher., Template: Intel;1033, Revision Number: {E4CF6E5B-7B8F-4839-AC3F-E1EE3789E159}, Create Time/Date: Thu Feb 21 07:06:06 2019, Last Saved Time/Date: Thu Feb 21 07:06:06 2019, Number of Pages: 200, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.9.1006.0), Security: 2 |
| MD5: | A5B7FB34E00B1467F73691A426A26EAA |
| SHA1: | D099CBF8ECB7D11141A023F741803FD9C7309DAA |
| SHA256: | 96481BDDDF7D8B4F3A8A1DE6622C2A6CD81D205A83BBF0974F9E683F14B72332 |
| SSDEEP: | 24576:8cJF3UeXTBJemGNqLMor/oB2MsBVjVJfzjUnE0WTM9AudAUYvdjM40b:8cz1aQLVU2MsBVZJLF0WEb |
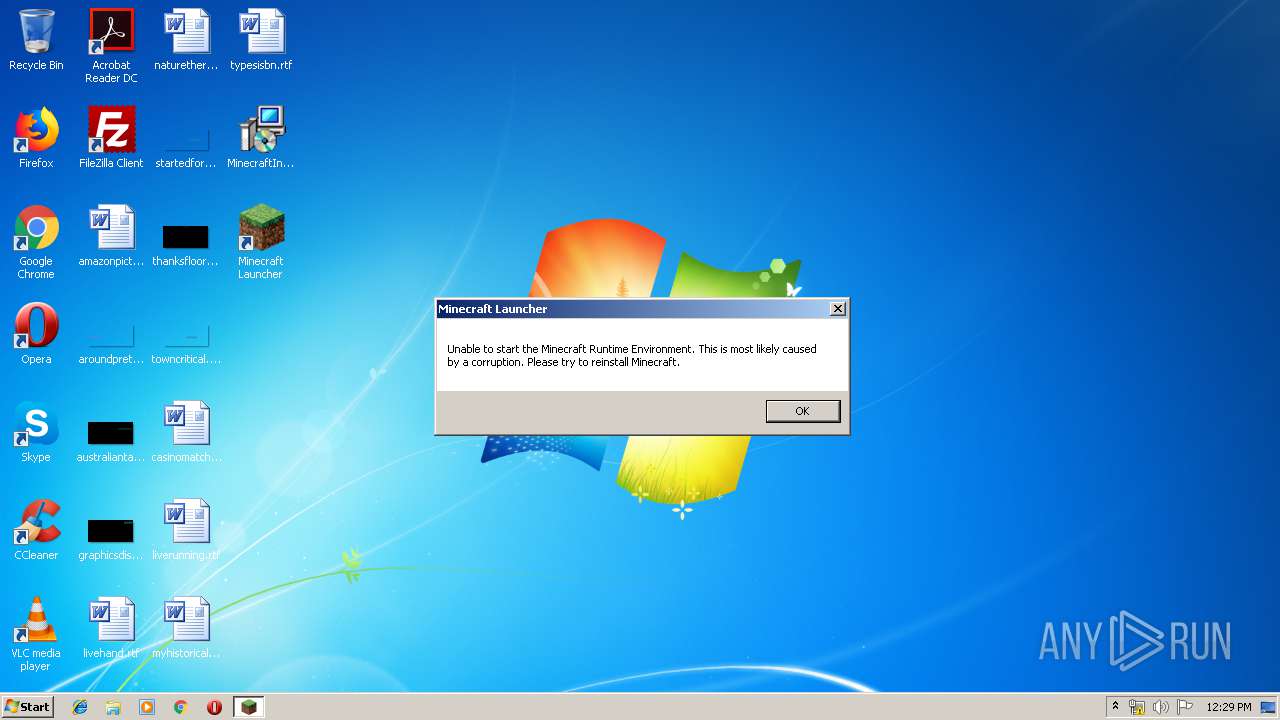
MALICIOUS
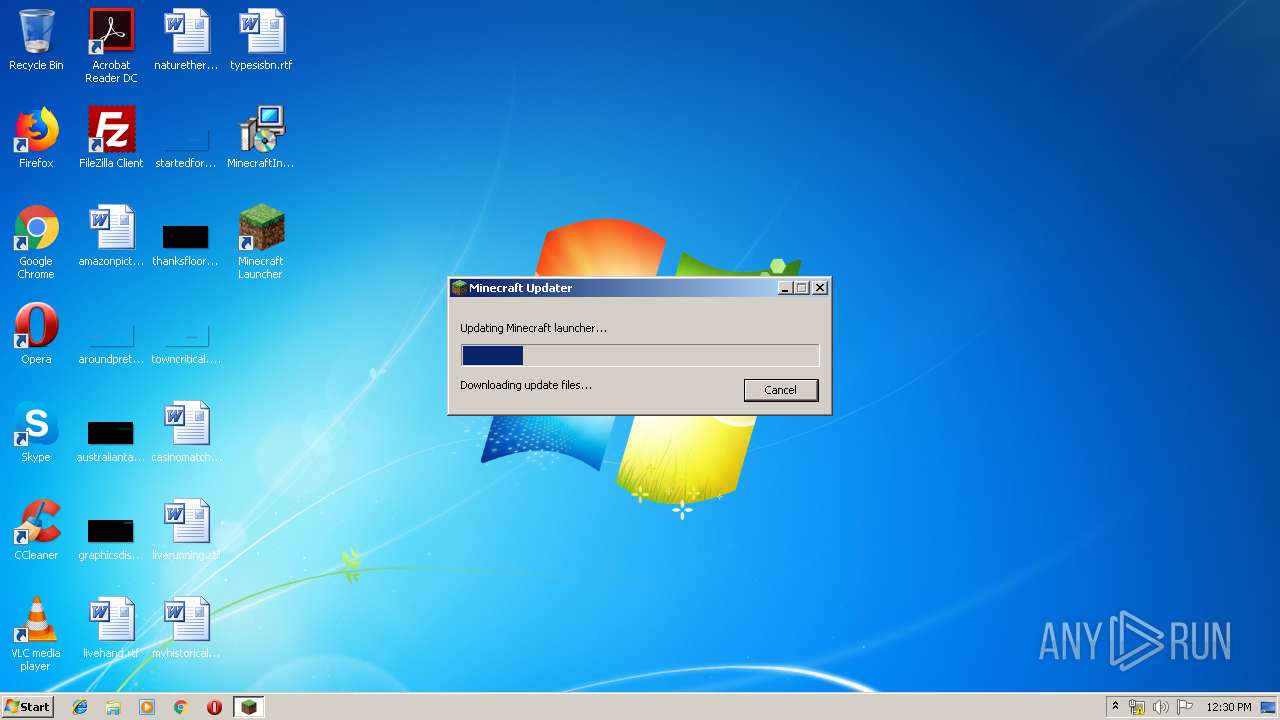
Application was dropped or rewritten from another process
- MinecraftLauncher.exe (PID: 1396)
- MinecraftLauncher.exe (PID: 1792)
SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 3124)
- msiexec.exe (PID: 2156)
- MinecraftLauncher.exe (PID: 1396)
Executed as Windows Service
- vssvc.exe (PID: 4016)
Executed via COM
- DrvInst.exe (PID: 2432)
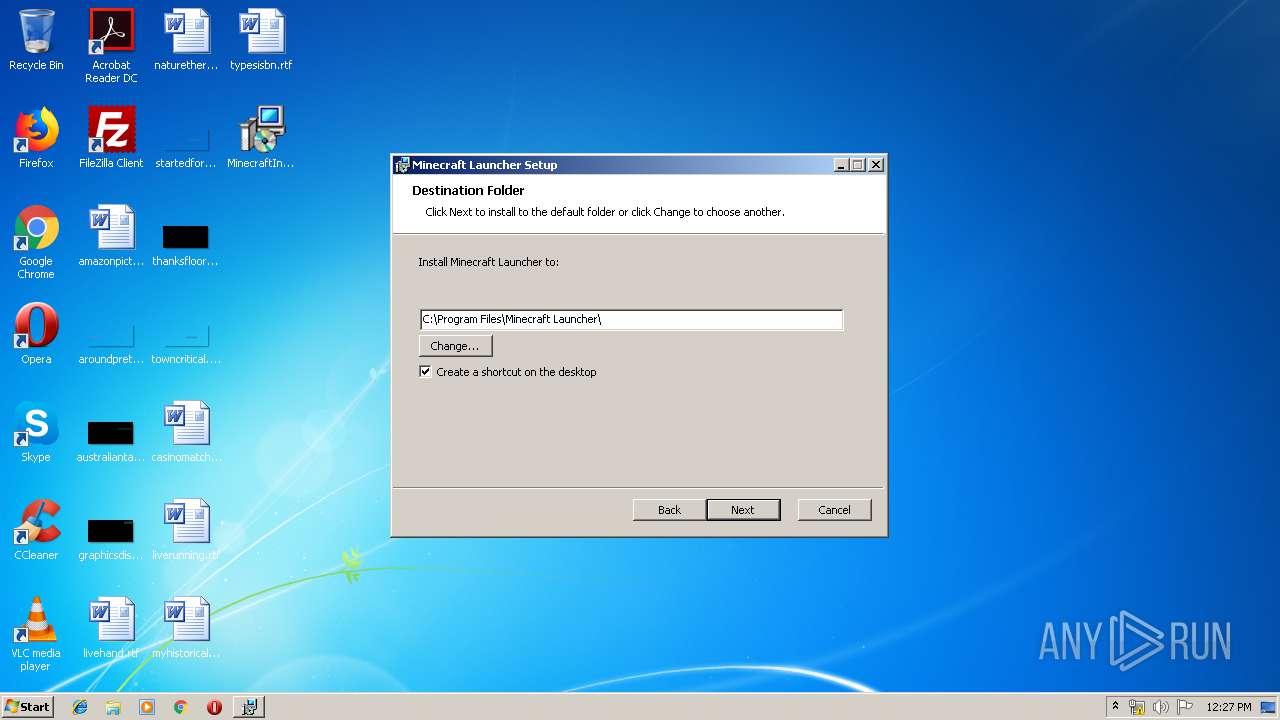
Creates files in the program directory
- MinecraftLauncher.exe (PID: 1396)
Creates files in the user directory
- MinecraftLauncher.exe (PID: 1792)
INFO
Application launched itself
- msiexec.exe (PID: 2156)
- chrome.exe (PID: 2980)
Searches for installed software
- msiexec.exe (PID: 2156)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2520)
- MsiExec.exe (PID: 1440)
- MsiExec.exe (PID: 2852)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 2432)
Changes settings of System certificates
- DrvInst.exe (PID: 2432)
Low-level read access rights to disk partition
- vssvc.exe (PID: 4016)
Creates files in the program directory
- msiexec.exe (PID: 2156)
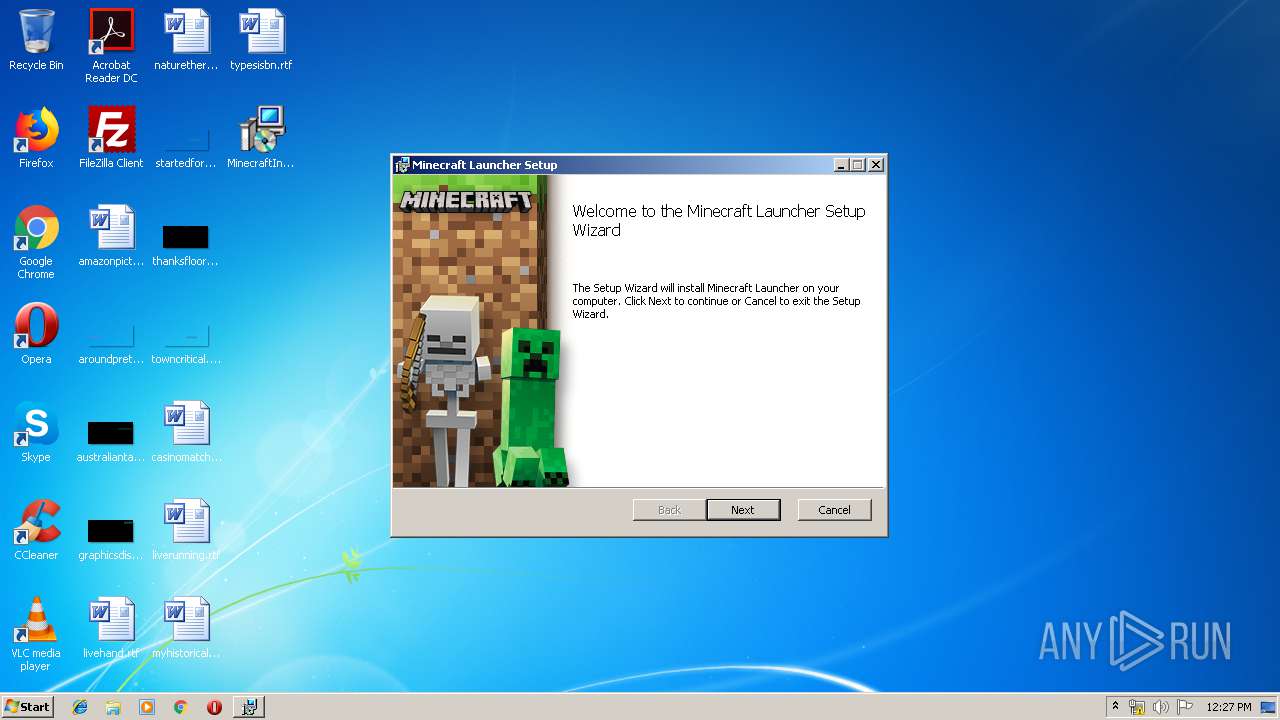
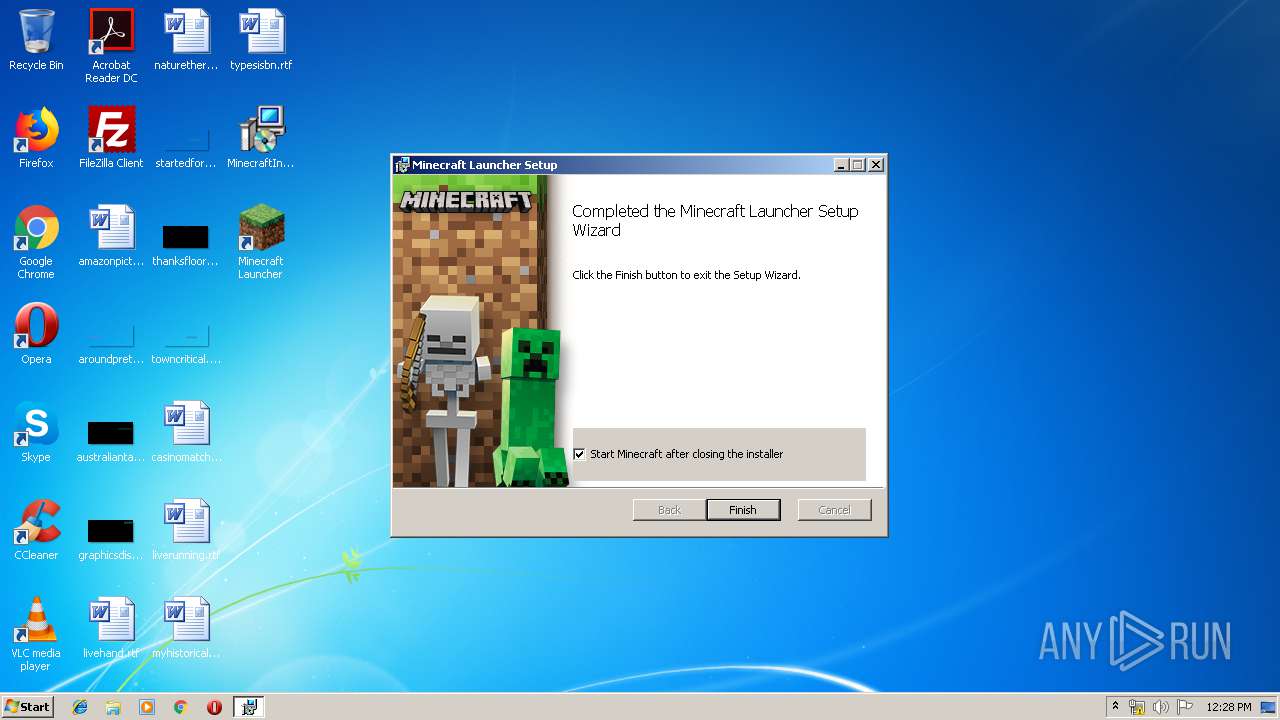
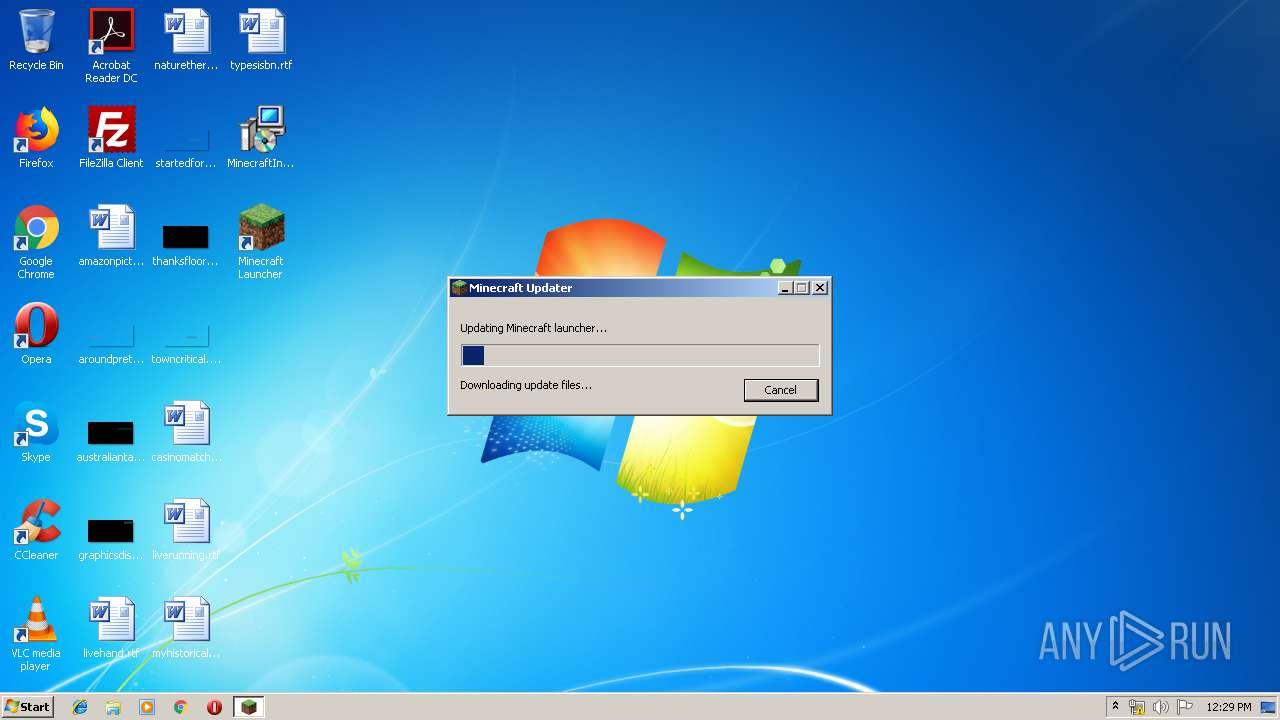
Manual execution by user
- MinecraftLauncher.exe (PID: 1396)
- chrome.exe (PID: 2980)
Creates a software uninstall entry
- msiexec.exe (PID: 2156)
Reads settings of System Certificates
- chrome.exe (PID: 2980)
Dropped object may contain Bitcoin addresses
- MinecraftLauncher.exe (PID: 1396)
Modifies the open verb of a shell class
- chrome.exe (PID: 2980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (95.3) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (3.2) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Minecraft Launcher |
| Author: | Mojang |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Minecraft Launcher. |
| Template: | Intel;1033 |
| RevisionNumber: | {E4CF6E5B-7B8F-4839-AC3F-E1EE3789E159} |
| CreateDate: | 2019:02:21 07:06:06 |
| ModifyDate: | 2019:02:21 07:06:06 |
| Pages: | 200 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.9.1006.0) |
| Security: | Read-only recommended |
Total processes
68
Monitored processes
33
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15864763000278769752,13932886620377381878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11351358825467100730 --mojo-platform-channel-handle=4948 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3516 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15864763000278769752,13932886620377381878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11058146171352932499 --mojo-platform-channel-handle=2448 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15864763000278769752,13932886620377381878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11776167126749783133 --mojo-platform-channel-handle=2660 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Minecraft Launcher\MinecraftLauncher.exe" | C:\Program Files\Minecraft Launcher\MinecraftLauncher.exe | explorer.exe | ||||||||||||
User: admin Company: Mojang Integrity Level: MEDIUM Description: Minecraft launcher Exit code: 0 Version: 1.0.1.0 Modules
| |||||||||||||||
| 1440 | C:\Windows\system32\MsiExec.exe -Embedding C9AD153233CFF3B6D52EB2F19827FCBB | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15864763000278769752,13932886620377381878,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2494947684546124202 --mojo-platform-channel-handle=3692 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6b8f0f18,0x6b8f0f28,0x6b8f0f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Minecraft Launcher\MinecraftLauncher.exe" | C:\Program Files\Minecraft Launcher\MinecraftLauncher.exe | MsiExec.exe | ||||||||||||
User: admin Company: Mojang Integrity Level: MEDIUM Description: Minecraft launcher Exit code: 1 Version: 1.0.1.0 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,15864763000278769752,13932886620377381878,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16615264563638068521 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16615264563638068521 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 086
Read events
657
Write events
412
Delete events
17
Modification events
| (PID) Process: | (3124) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2156) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000009A50F66E9110D5016C080000500B0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2156) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000009A50F66E9110D5016C080000500B0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2156) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (2156) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000002E866D6F9110D5016C080000500B0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2156) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000088E86F6F9110D5016C080000440D0000E803000001000000000000000000000071CF103D3538364A98F909EE87051E2D0000000000000000 | |||
| (PID) Process: | (4016) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000A4367E6F9110D501B00F000078090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4016) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000A4367E6F9110D501B00F0000680E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4016) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000A4367E6F9110D501B00F0000880E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4016) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000A4367E6F9110D501B00F0000CC050000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
121
Suspicious files
395
Text files
372
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2156 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2156 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF4BC18D9711EB0595.TMP | — | |
MD5:— | SHA256:— | |||
| 2156 | msiexec.exe | C:\Windows\Installer\MSI99E8.tmp | — | |
MD5:— | SHA256:— | |||
| 4016 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2156 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF098087828DEC2790.TMP | — | |
MD5:— | SHA256:— | |||
| 2156 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{3d10cf71-3835-4a36-98f9-09ee87051e2d}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 2432 | DrvInst.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
| 1396 | MinecraftLauncher.exe | C:\Users\admin\AppData\Local\Temp\Cab63ED.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | MinecraftLauncher.exe | C:\Users\admin\AppData\Local\Temp\Tar63EE.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | MinecraftLauncher.exe | C:\Users\admin\AppData\Local\Temp\Cab640E.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
53
DNS requests
36
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2980 | chrome.exe | GET | 200 | 173.194.183.201:80 | http://r4---sn-aigl6nl7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=217.147.89.18&mm=28&mn=sn-aigl6nl7&ms=nvh&mt=1558524173&mv=u&pl=22&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2980 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
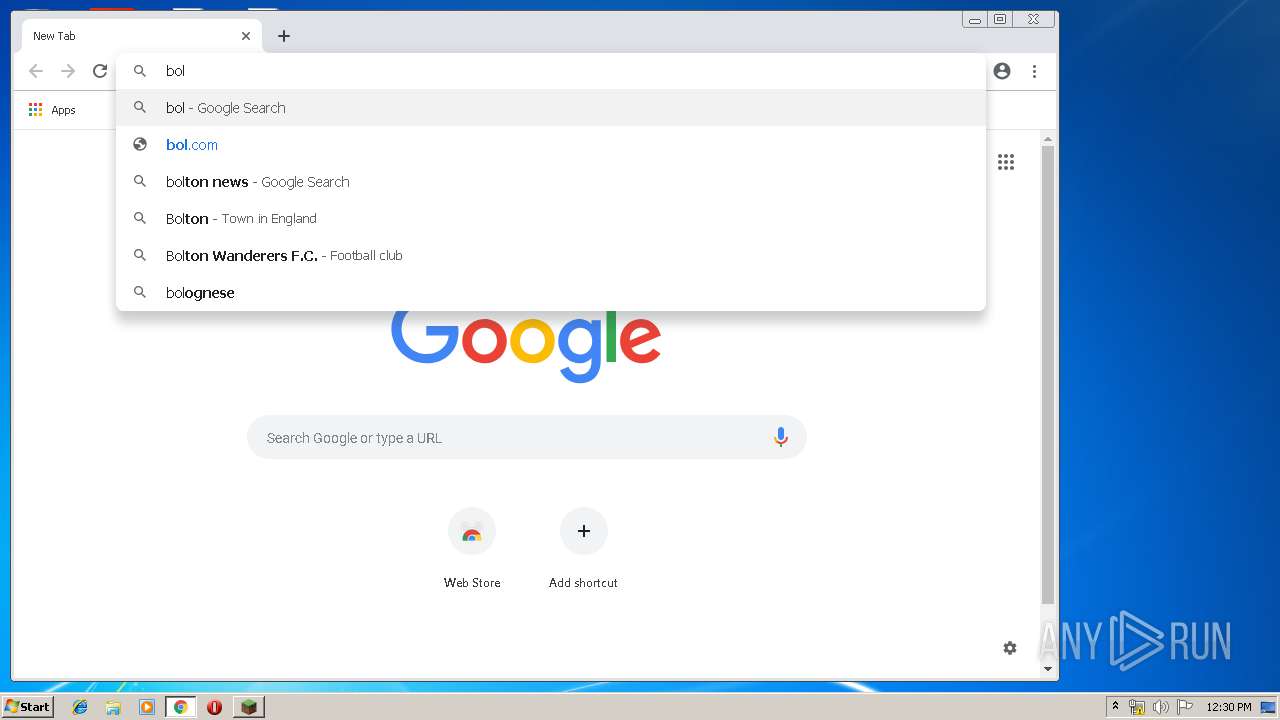
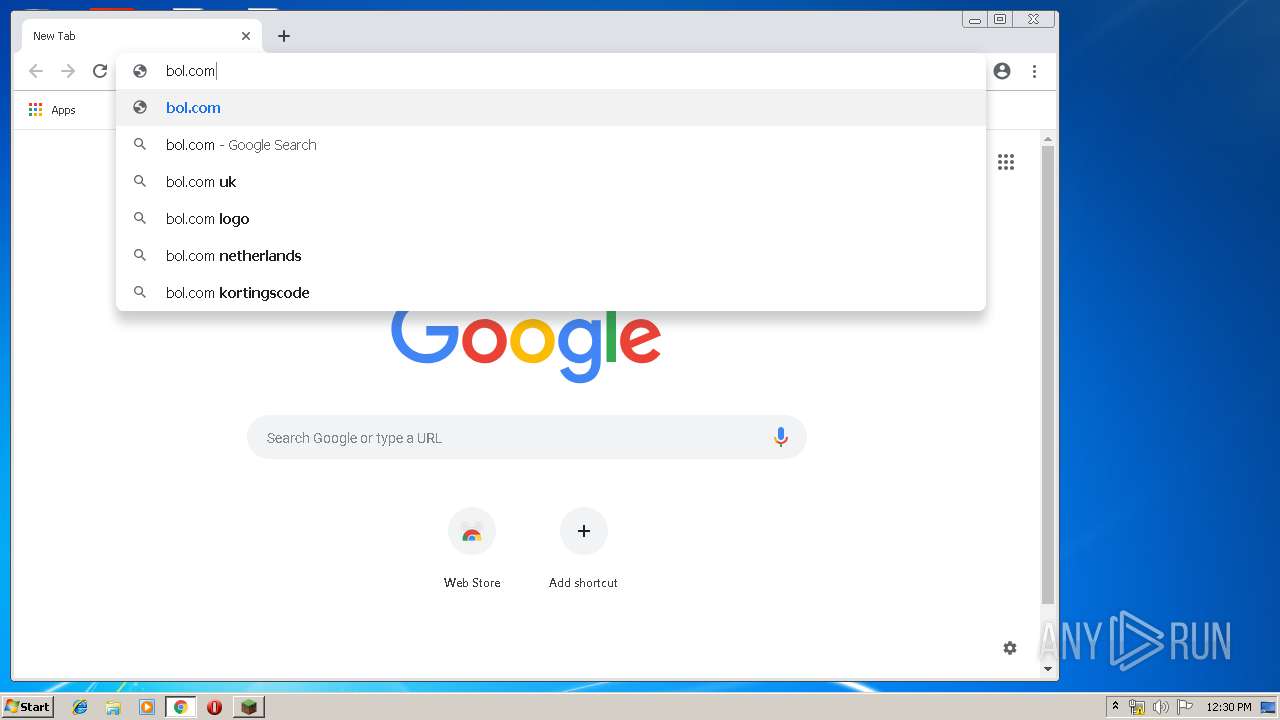
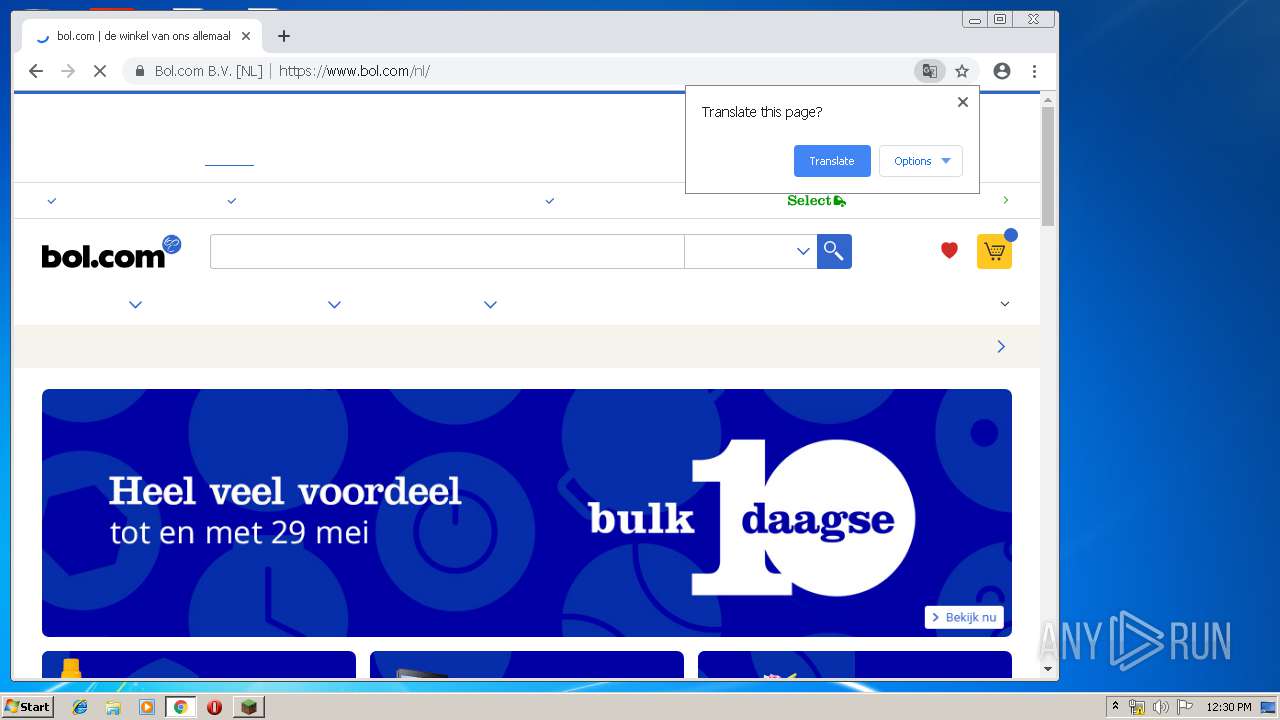
2980 | chrome.exe | GET | 301 | 185.14.169.113:80 | http://bol.com/ | NL | html | 231 b | whitelisted |
2980 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAl4yTN3pjCCQtSPEHMRuGI%3D | US | der | 471 b | whitelisted |
2980 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
1396 | MinecraftLauncher.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
1396 | MinecraftLauncher.exe | GET | 200 | 52.85.182.55:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1792 | MinecraftLauncher.exe | 54.239.168.115:443 | launchermeta.mojang.com | Amazon.com, Inc. | US | unknown |
1396 | MinecraftLauncher.exe | 54.239.168.115:443 | launchermeta.mojang.com | Amazon.com, Inc. | US | unknown |
1396 | MinecraftLauncher.exe | 52.85.182.55:80 | x.ss2.us | Amazon.com, Inc. | US | whitelisted |
1396 | MinecraftLauncher.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2980 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 216.58.205.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 185.14.169.113:80 | bol.com | bol.com BV | NL | suspicious |
2980 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 185.14.169.125:443 | www.bol.com | bol.com BV | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
launchermeta.mojang.com |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
launcher.mojang.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |