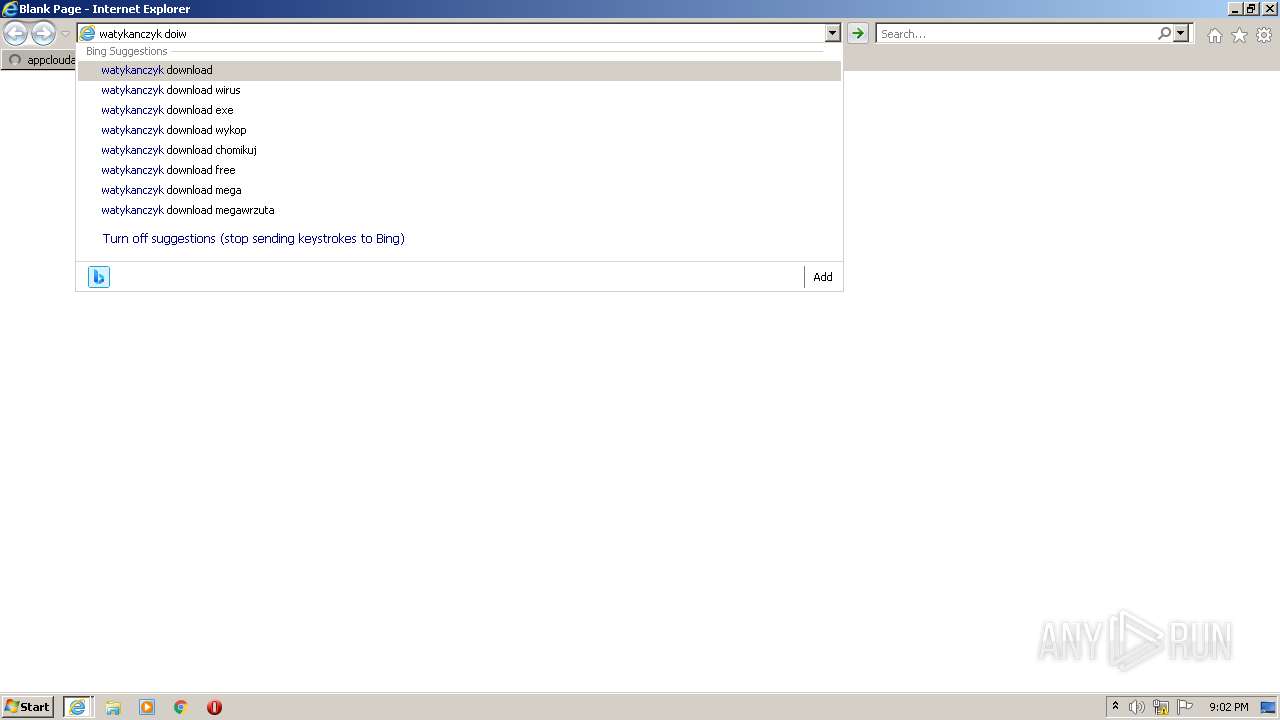
| URL: | https://appcloudactive.com/away.php?url=I4WHKFughjKzpcbEVeGSzAMCq7AwVk%2FKCLndG2RplCYUU7fINdER2EM%2FKgAuOctCpPEVsZhLWLDWxxsTC106A1I9X7Mohsu7SQUb4cbUQxBDgOBXY464AyhMvSHx%2BY%2BD6XVvVEE0fgC5vP%2B%2Bs8GEihUiB9TyU%2FOwr4cCAUkkRLY%3D |
| Full analysis: | https://app.any.run/tasks/f06aebd2-3638-4045-ad6c-9958497a3d38 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2023, 20:02:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 57892925B0A6EF3402FA291A7D8070F2 |
| SHA1: | B0BE4E5496653256BA138547A3F3C5B19273D7BE |
| SHA256: | 963D6B1C3BEB4AC0984B357A95590E890C64E7F2F9450E43EF77373E5D71E515 |
| SSDEEP: | 6:2a6VITqVrQhQn16Bn/jImAJsR4hdJomXnBk4EONeW:2fqTWrQSnQBM64hdim3i4EweW |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Create files in a temporary directory
- iexplore.exe (PID: 2696)
- iexplore.exe (PID: 1364)
Application launched itself
- iexplore.exe (PID: 2696)
Manual execution by a user
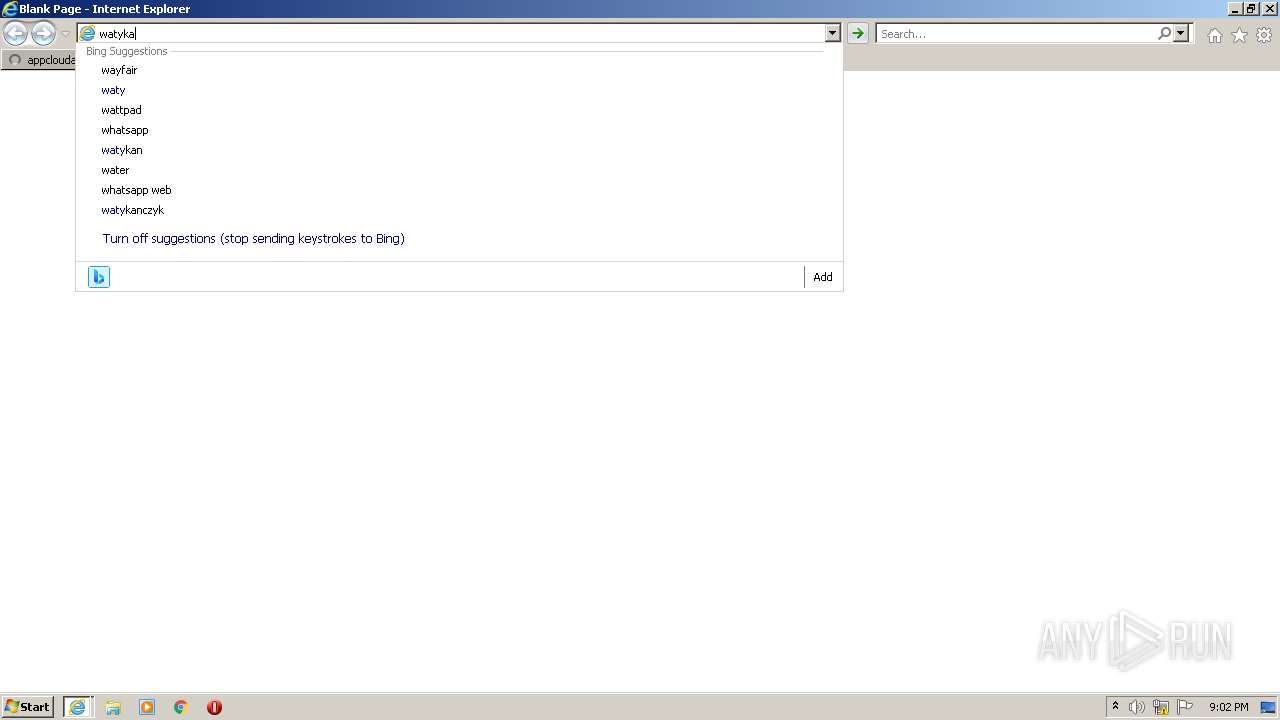
- opera.exe (PID: 3868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1364 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2696 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2696 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://appcloudactive.com/away.php?url=I4WHKFughjKzpcbEVeGSzAMCq7AwVk%2FKCLndG2RplCYUU7fINdER2EM%2FKgAuOctCpPEVsZhLWLDWxxsTC106A1I9X7Mohsu7SQUb4cbUQxBDgOBXY464AyhMvSHx%2BY%2BD6XVvVEE0fgC5vP%2B%2Bs8GEihUiB9TyU%2FOwr4cCAUkkRLY%3D" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3164 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2696 CREDAT:3937553 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3868 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
47 558
Read events
47 060
Write events
492
Delete events
6
Modification events
| (PID) Process: | (2696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
120
Text files
466
Unknown types
76
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1364 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1364 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\AAD71546A4AF211E7195C418FB3426E5 | binary | |
MD5:— | SHA256:— | |||
| 1364 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\away[1].htm | html | |
MD5:— | SHA256:— | |||
| 1364 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 1364 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 2696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 1364 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\TO6VQ3HU.txt | text | |
MD5:— | SHA256:— | |||
| 1364 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Y7O30I26.txt | text | |
MD5:— | SHA256:— | |||
| 1364 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab972.tmp | compressed | |
MD5:E71C8443AE0BC2E282C73FAEAD0A6DD3 | SHA256:95B0A5ACC5BF70D3ABDFD091D0C9F9063AA4FDE65BD34DBF16786082E1992E72 | |||
| 1364 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
97
DNS requests
37
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1364 | iexplore.exe | GET | 200 | 95.101.54.200:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgRLCyHXcSiQhO%2FqCnlxeZjh3w%3D%3D | DE | der | 503 b | shared |
1364 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2696 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
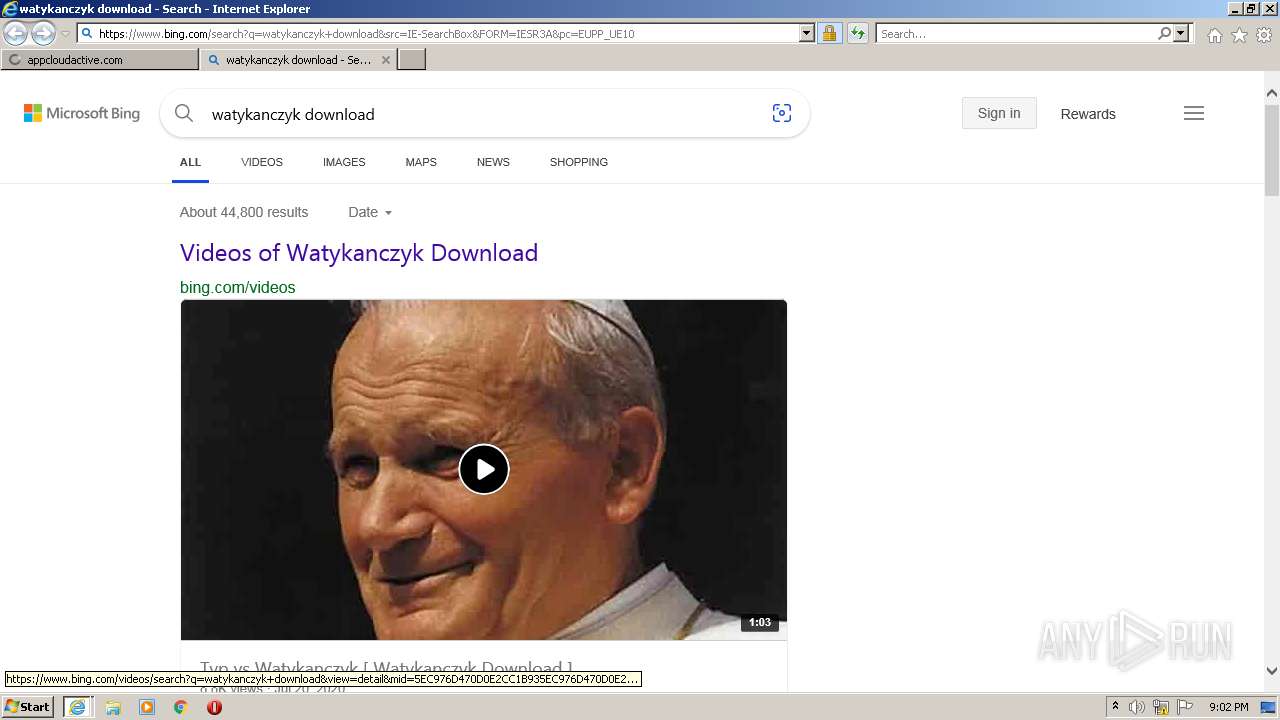
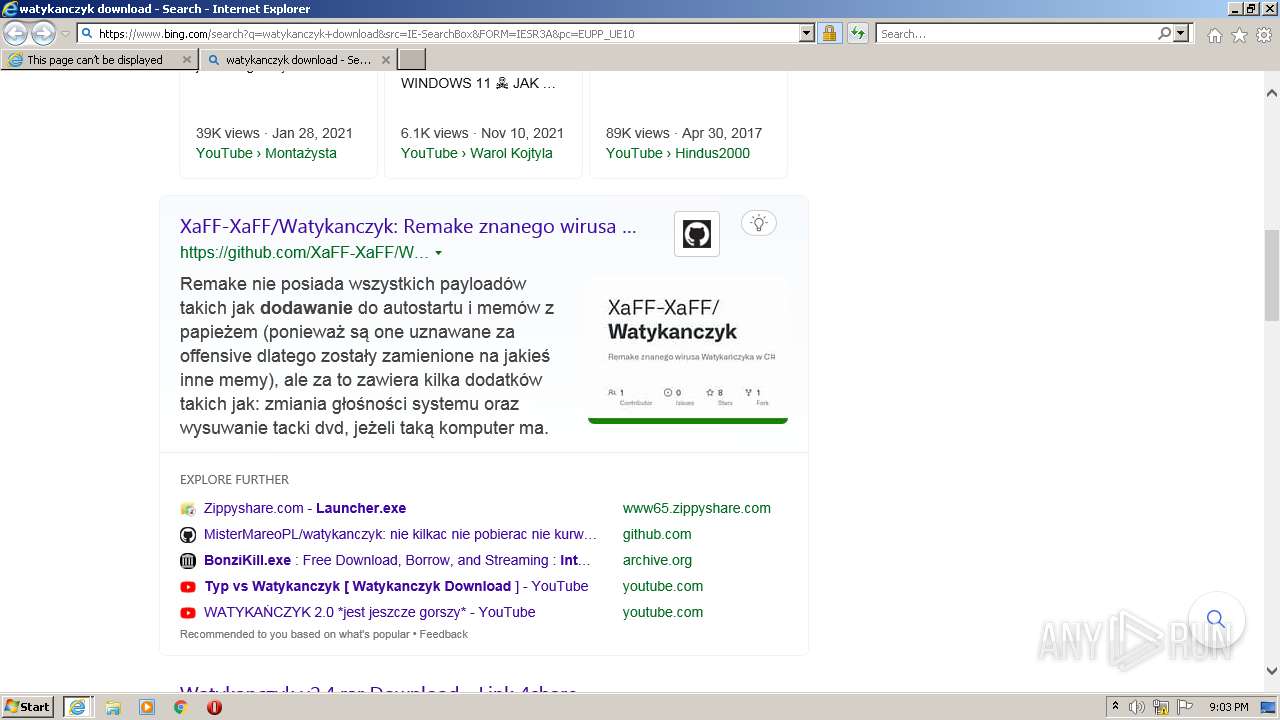
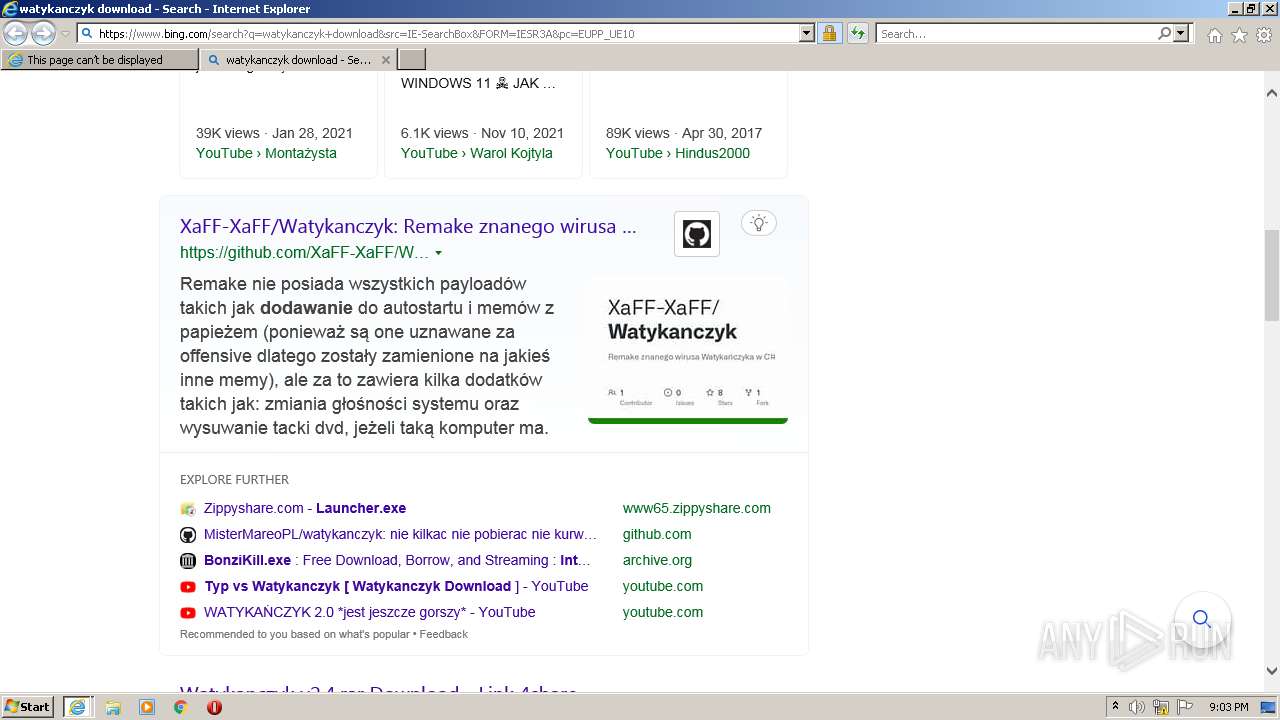
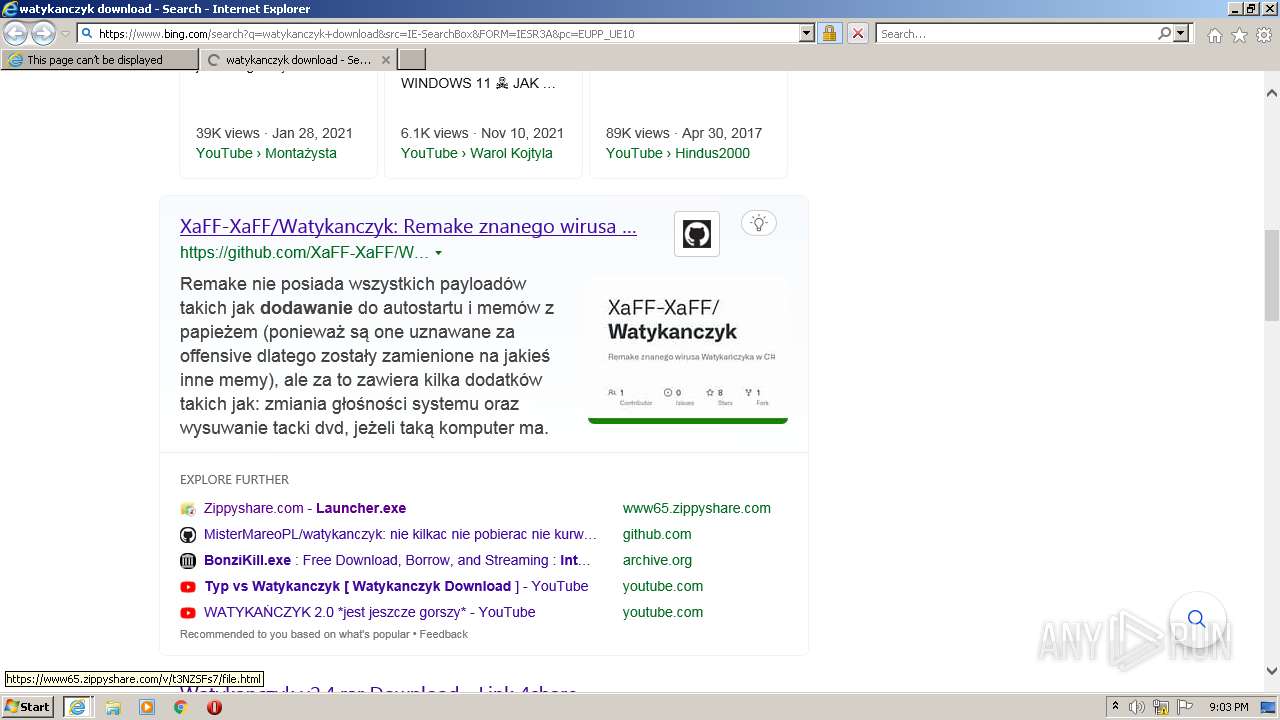
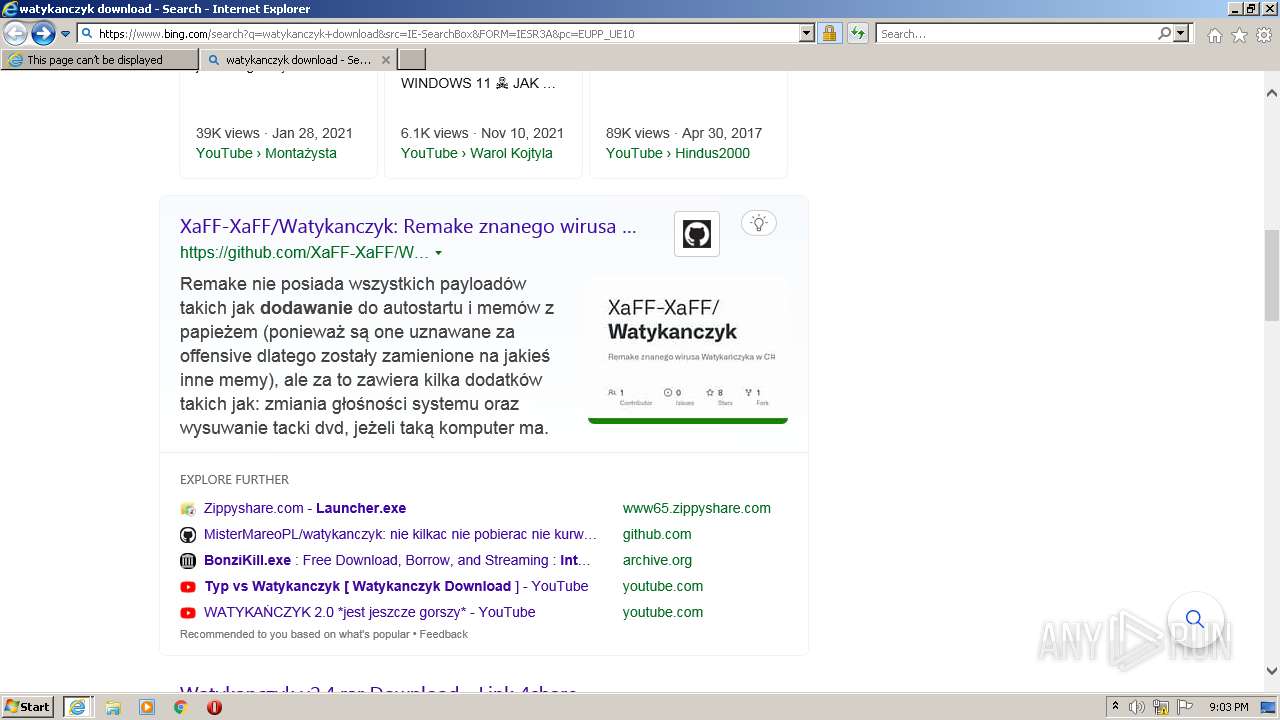
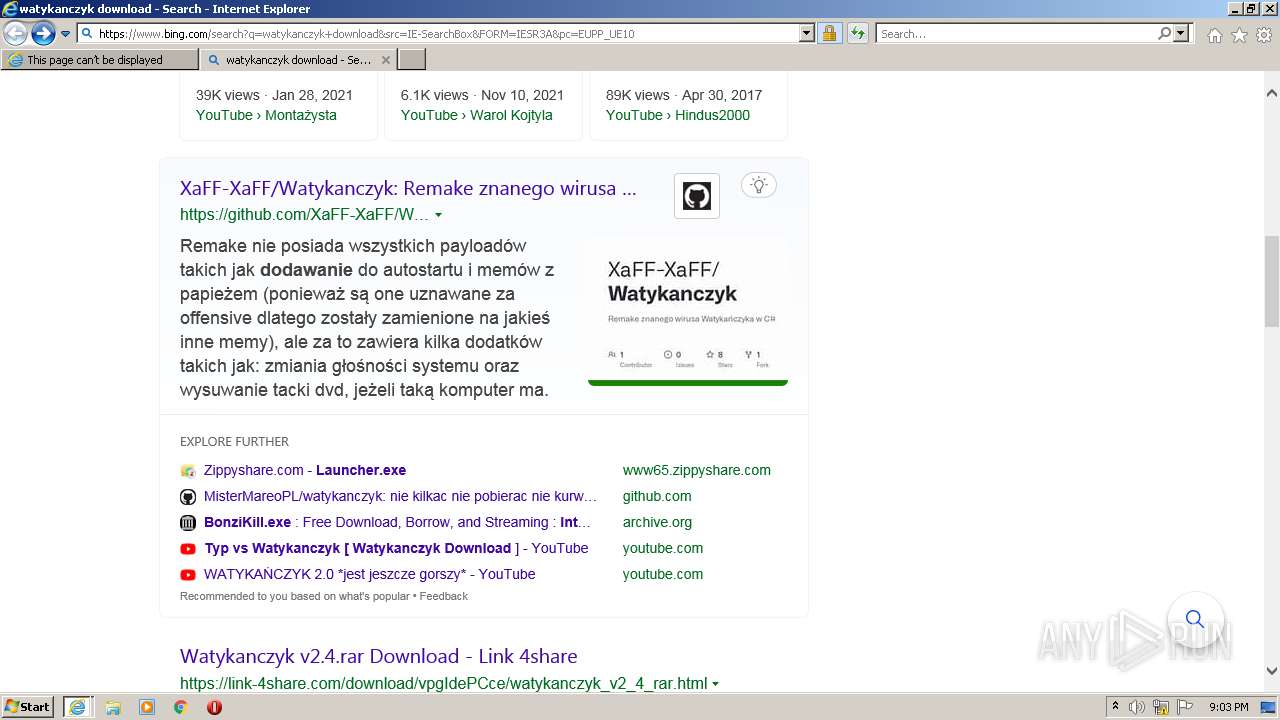
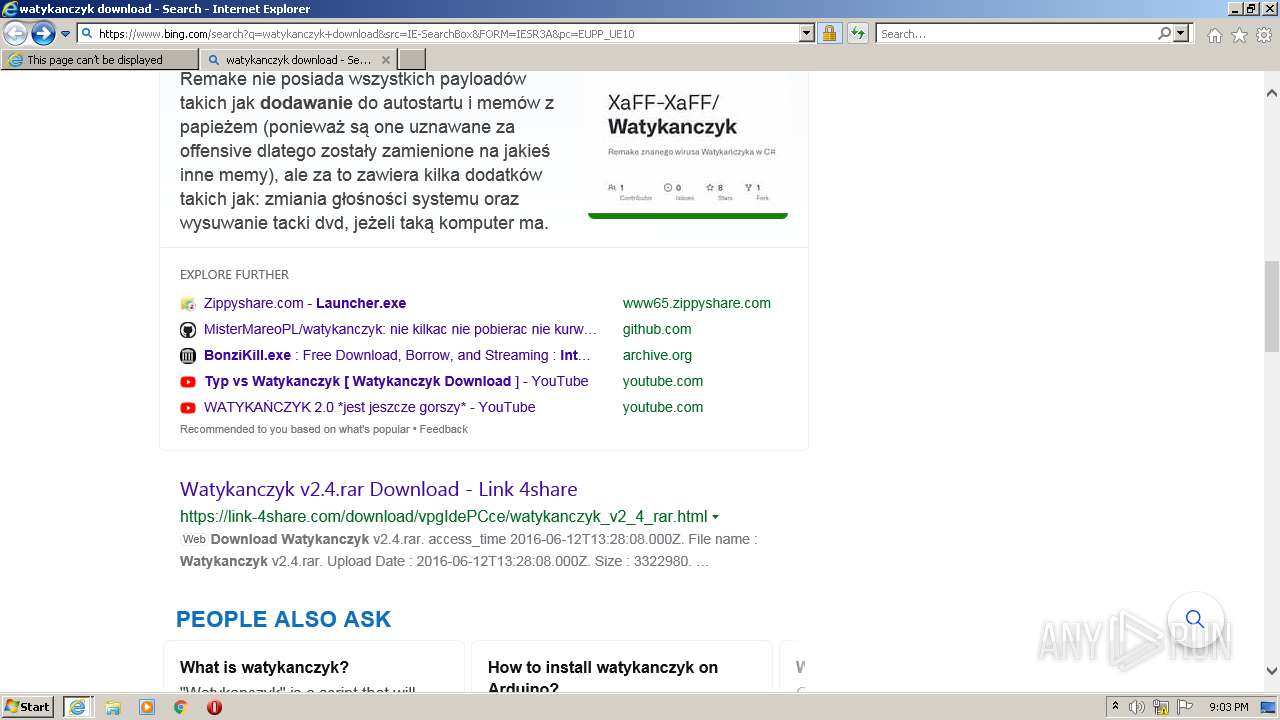
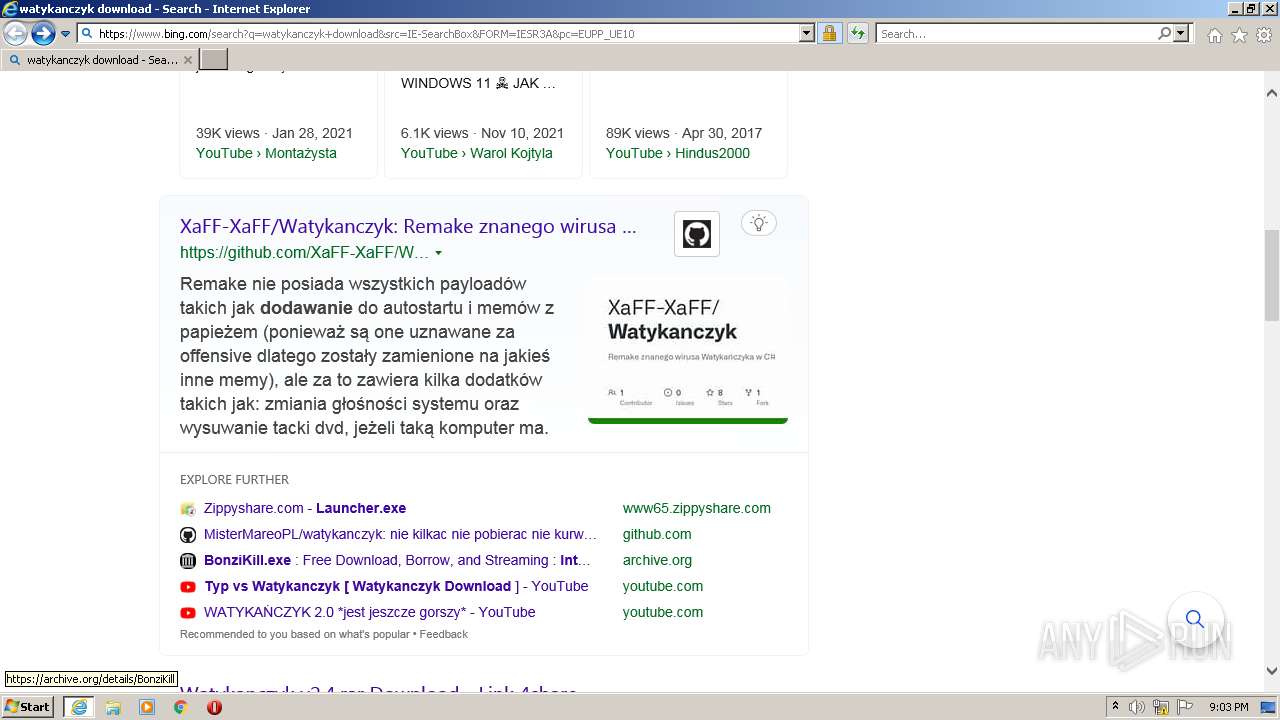
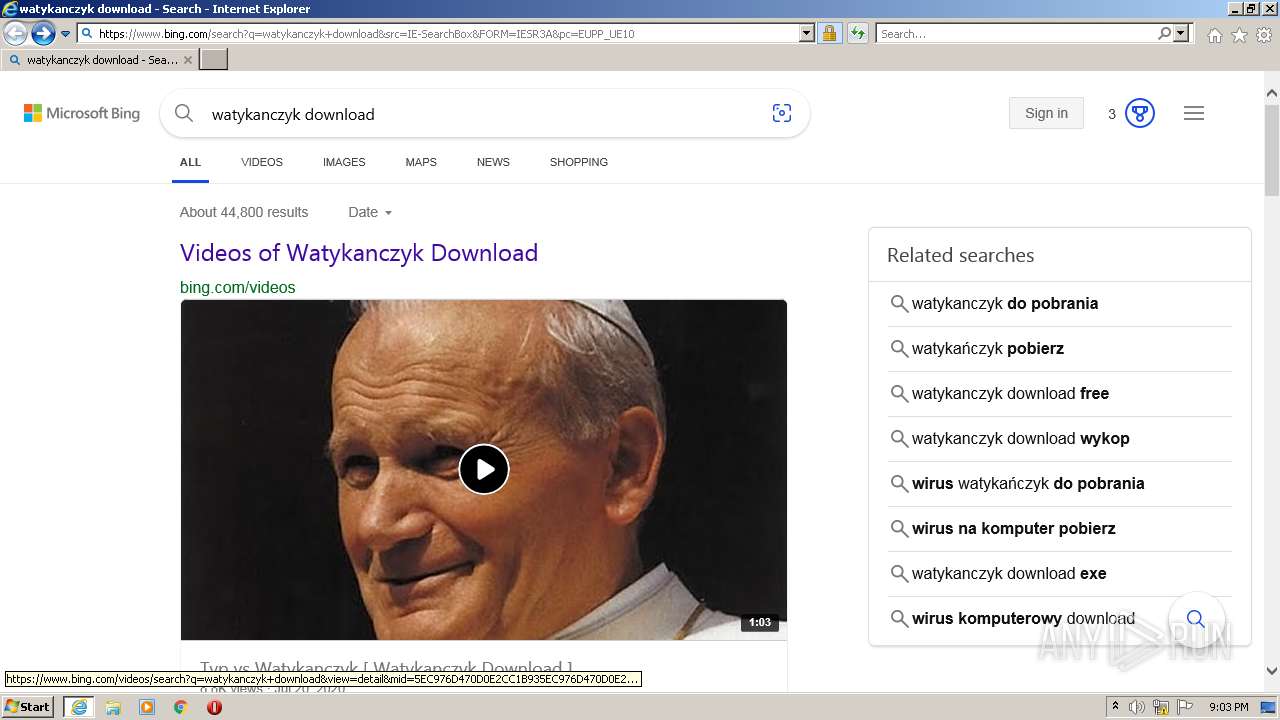
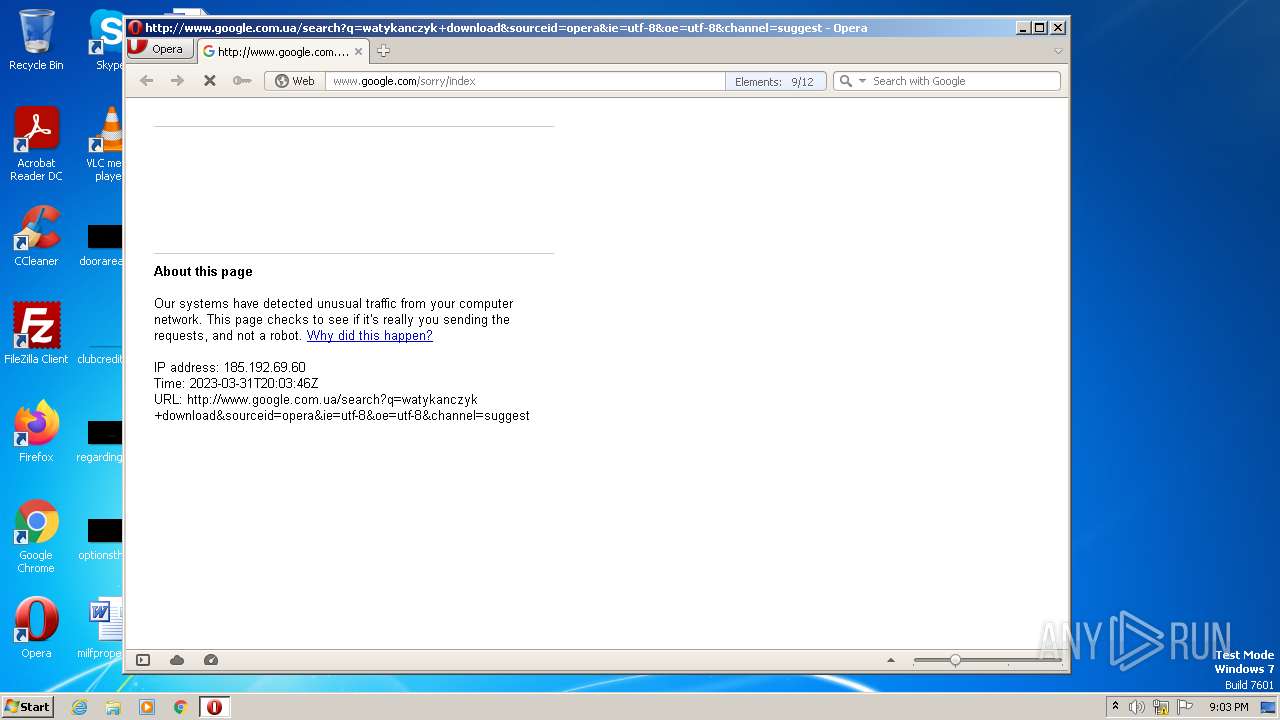
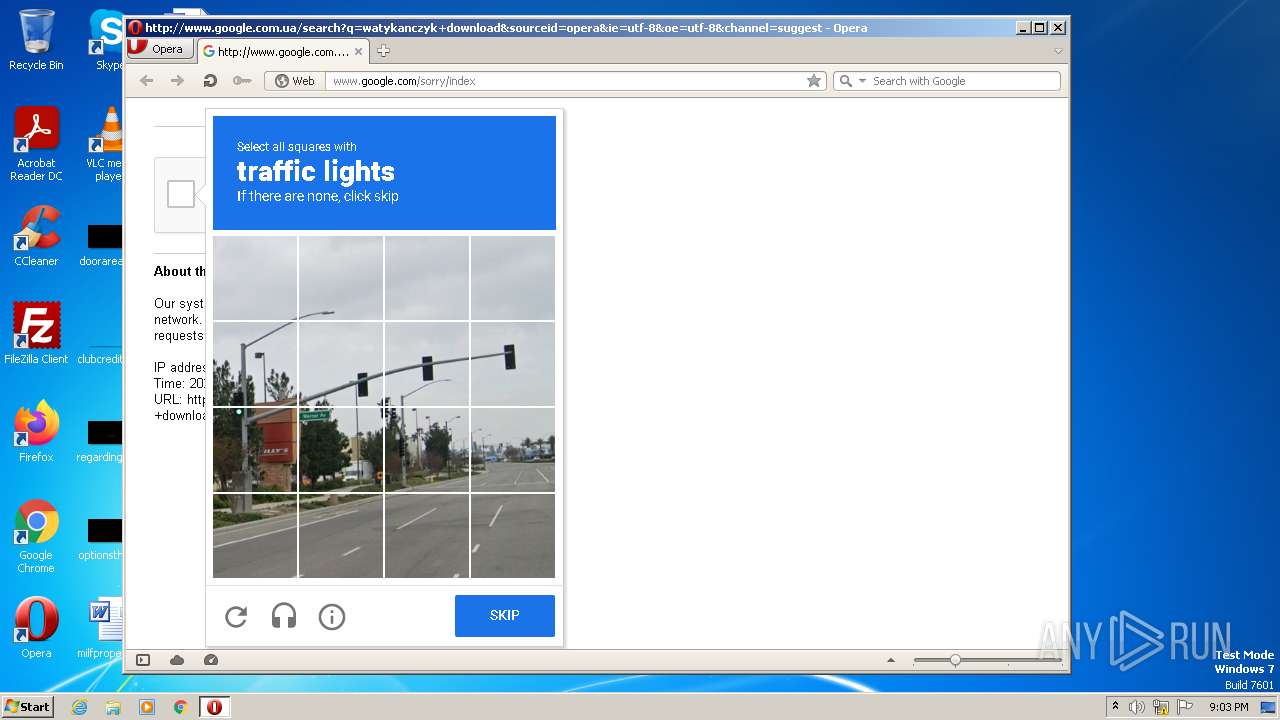
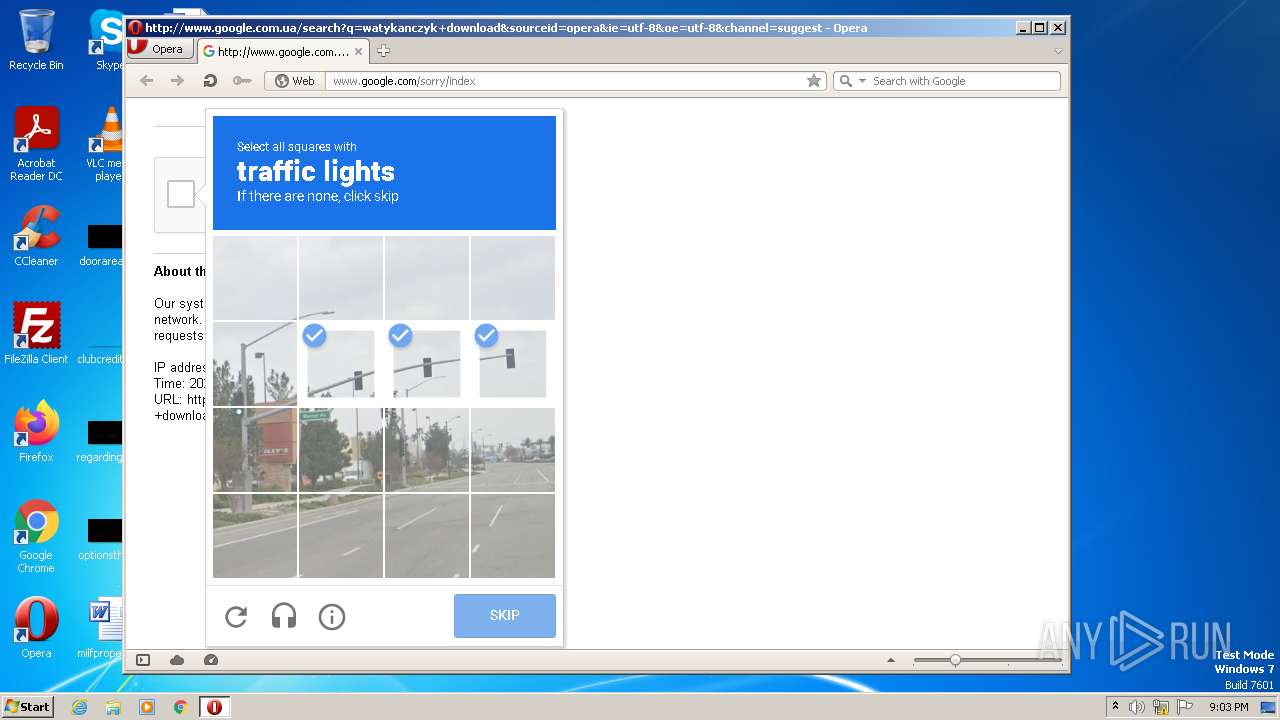
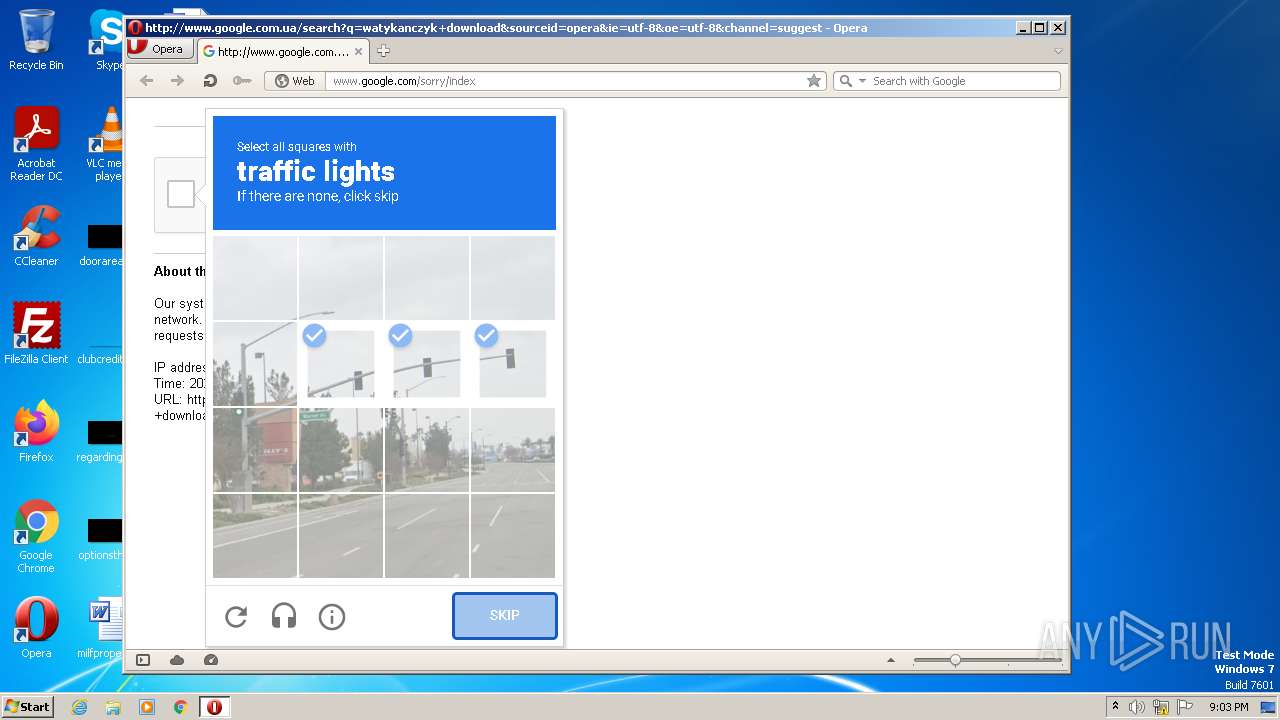
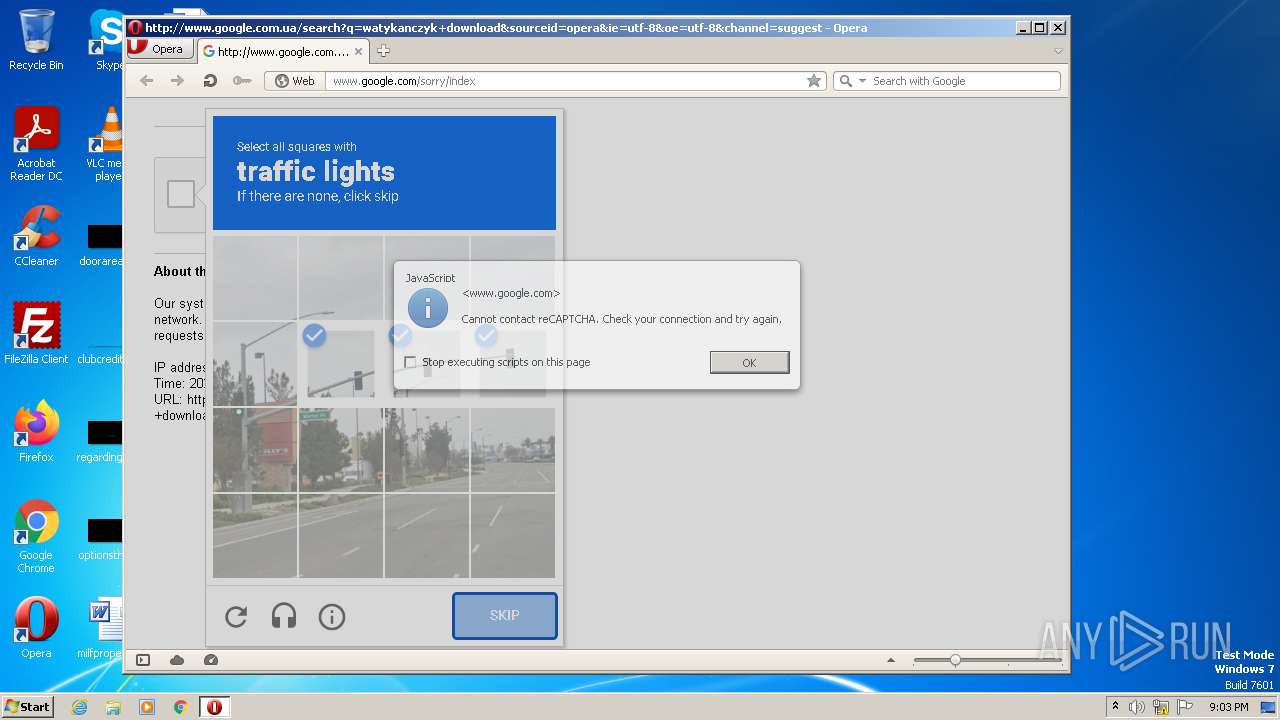
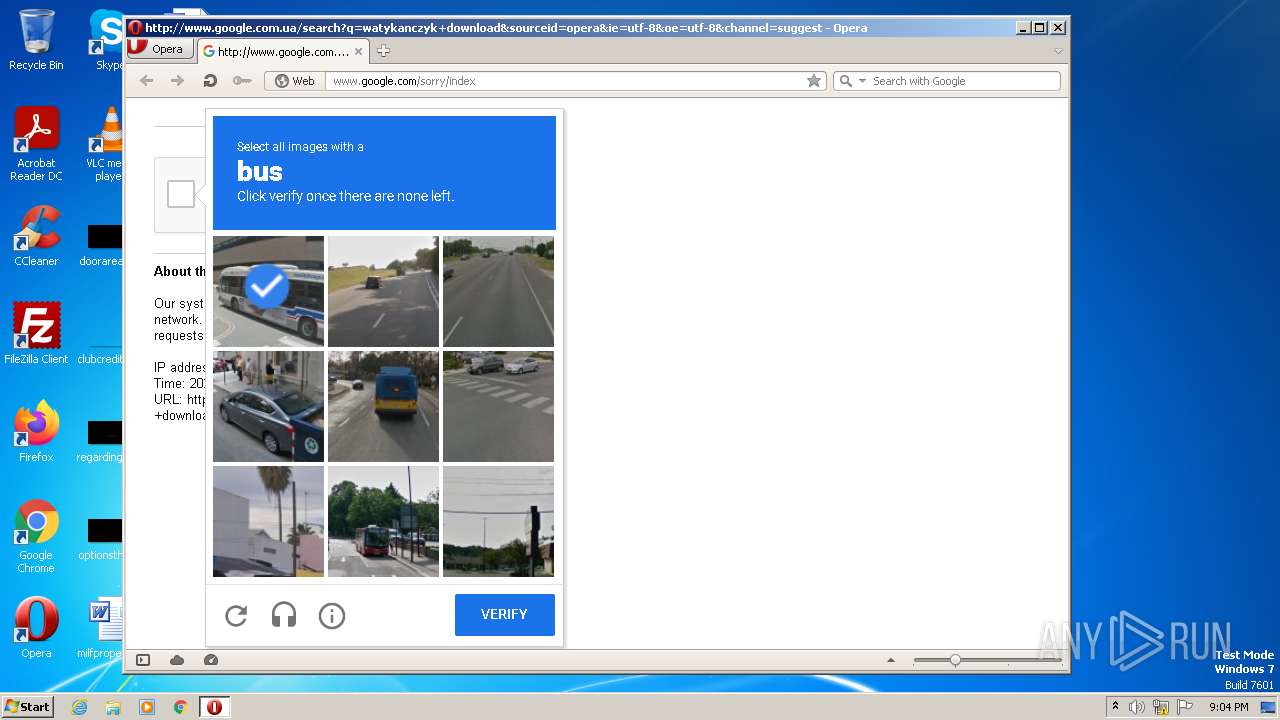
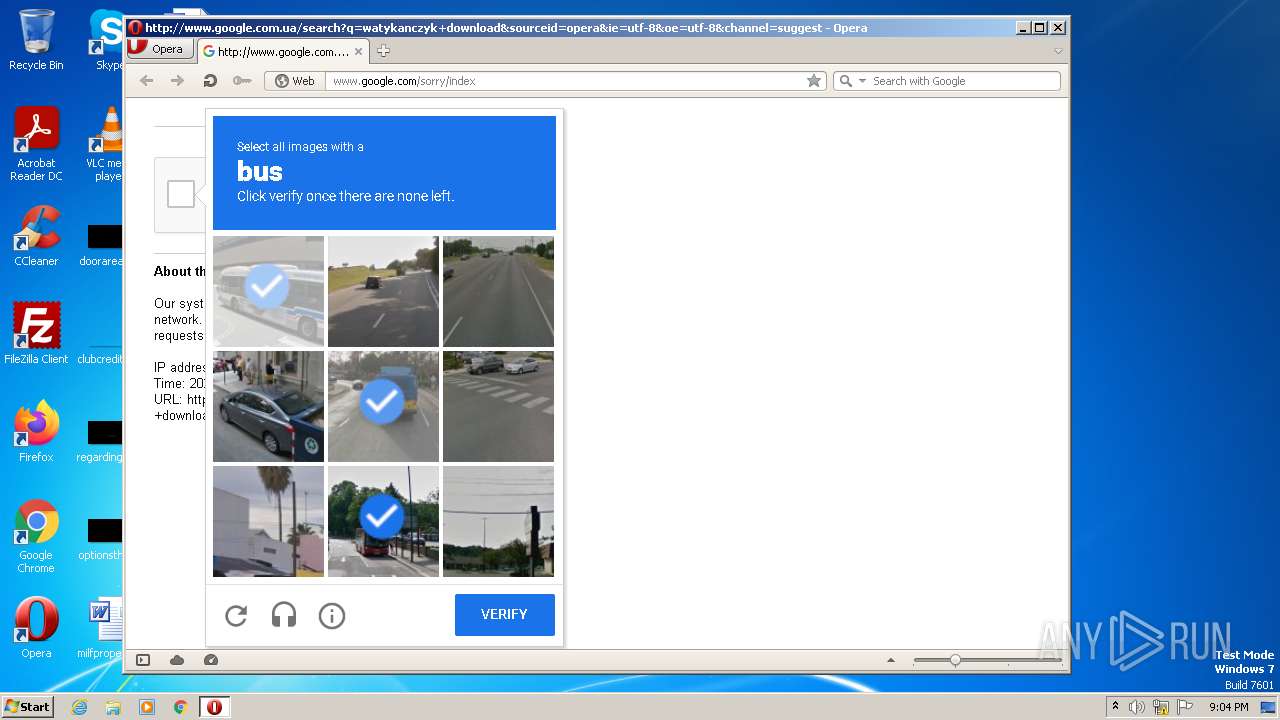
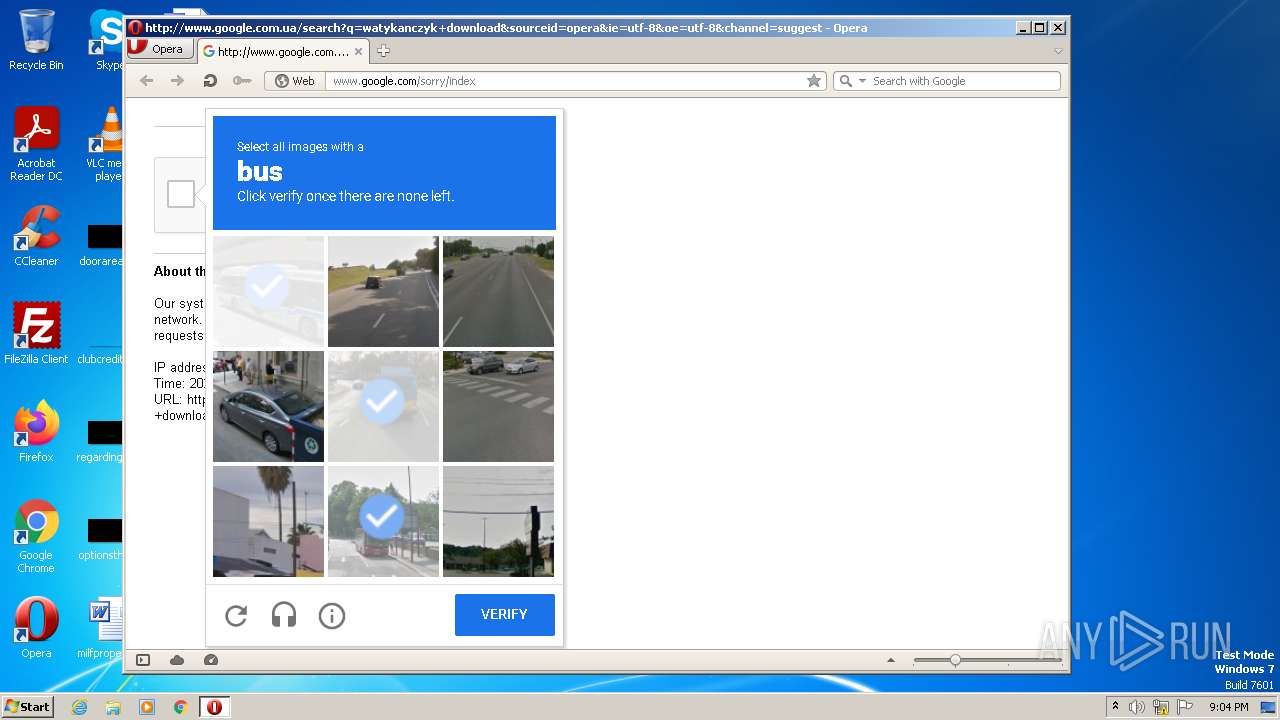
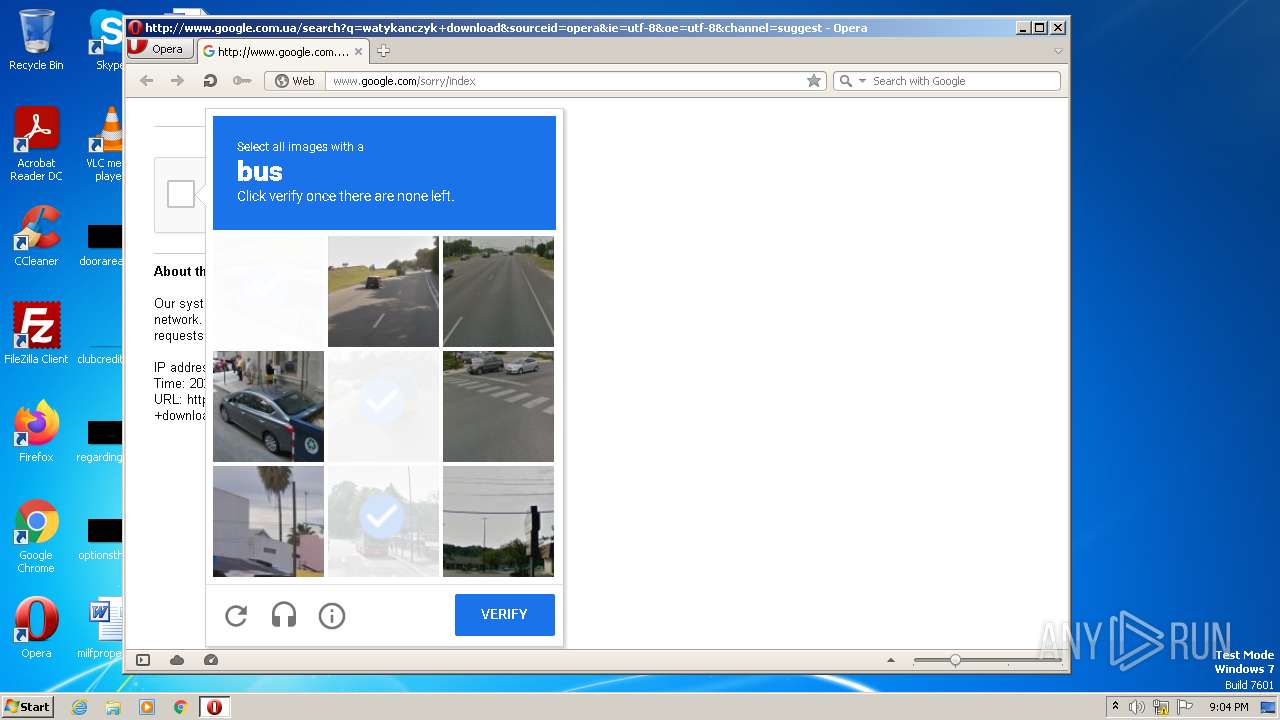
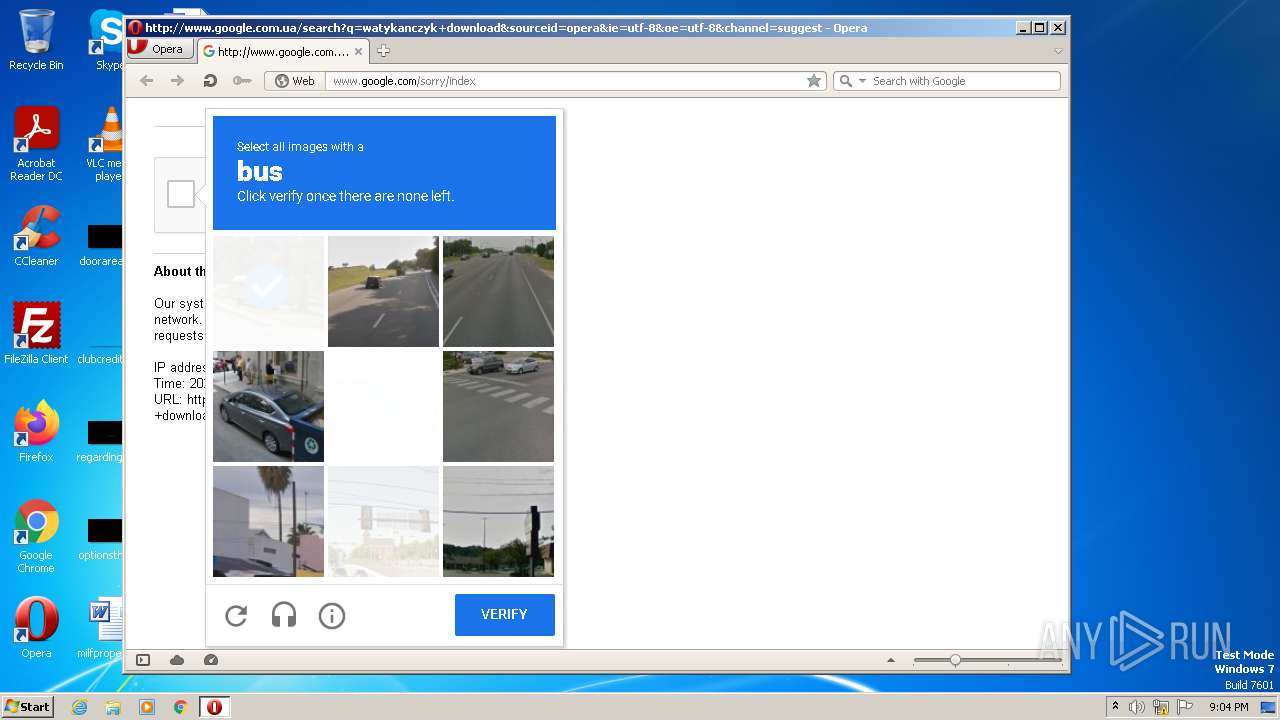
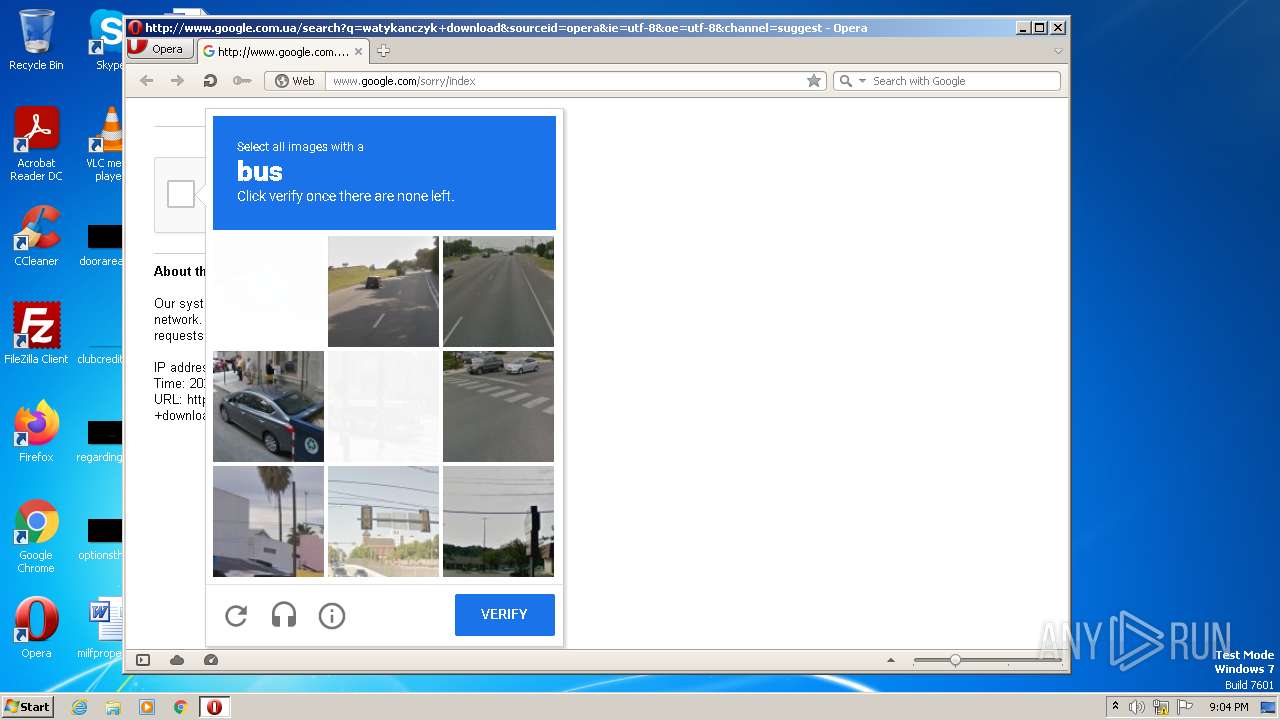
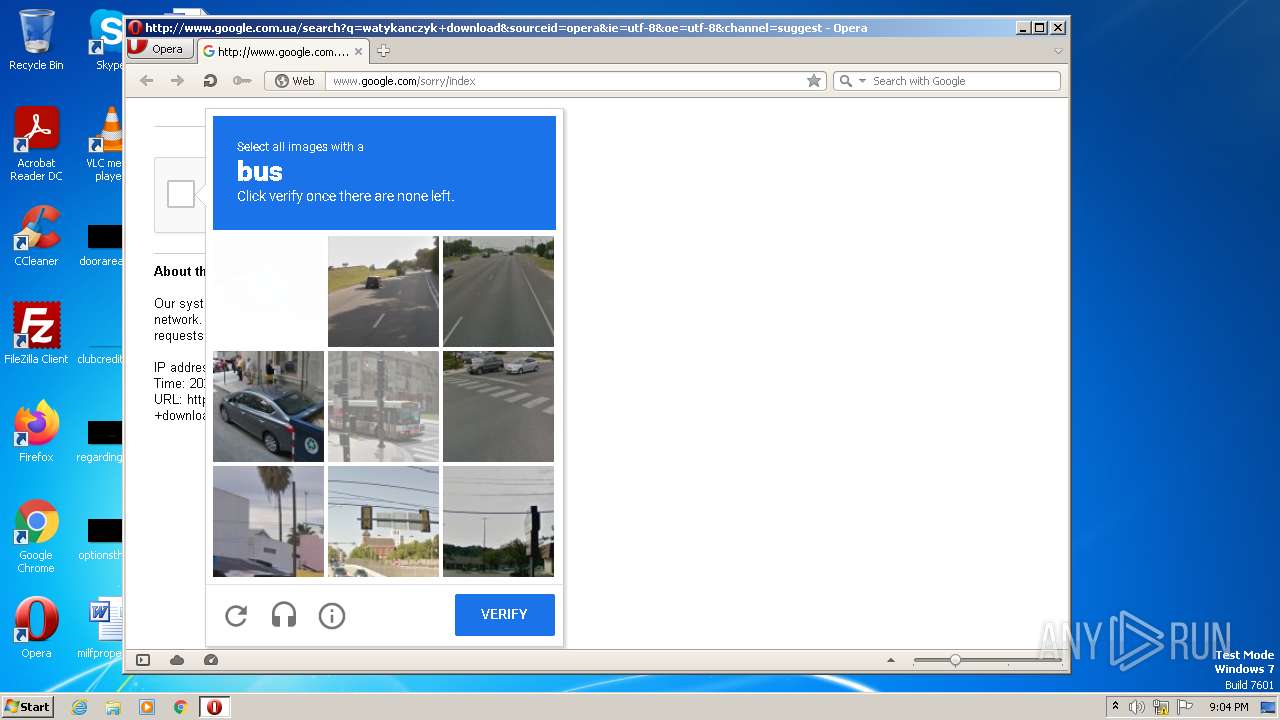
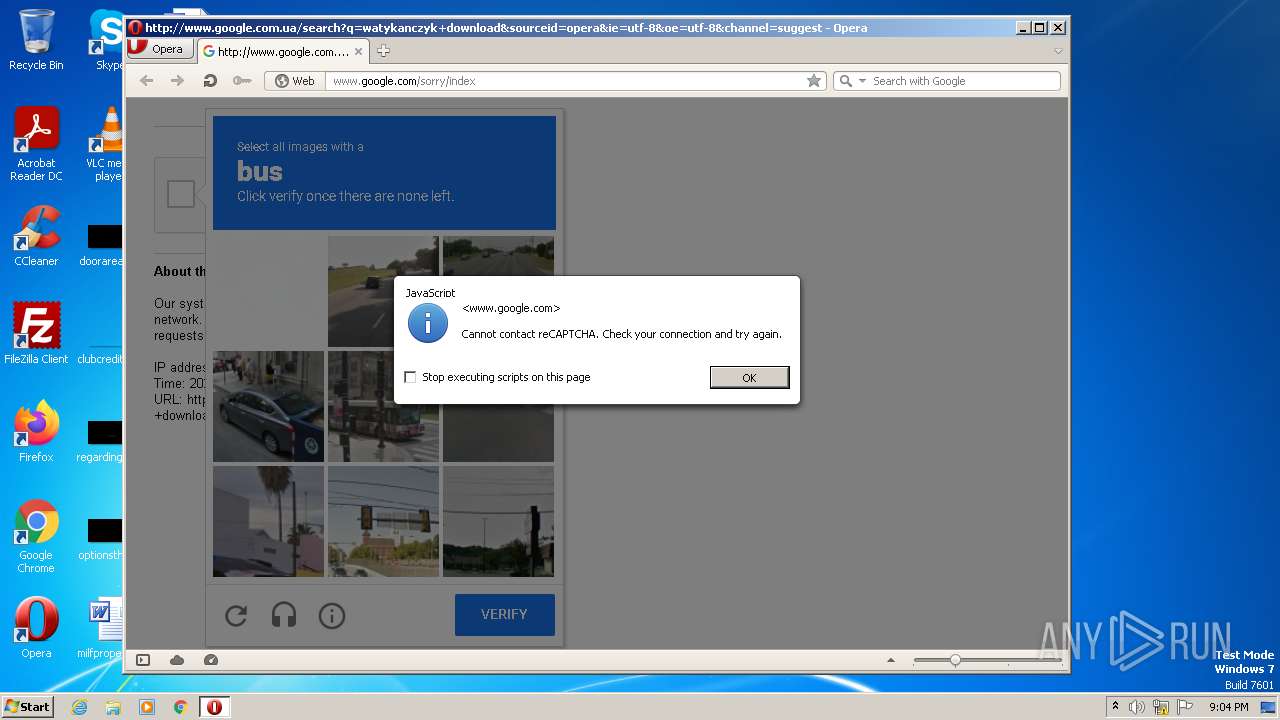
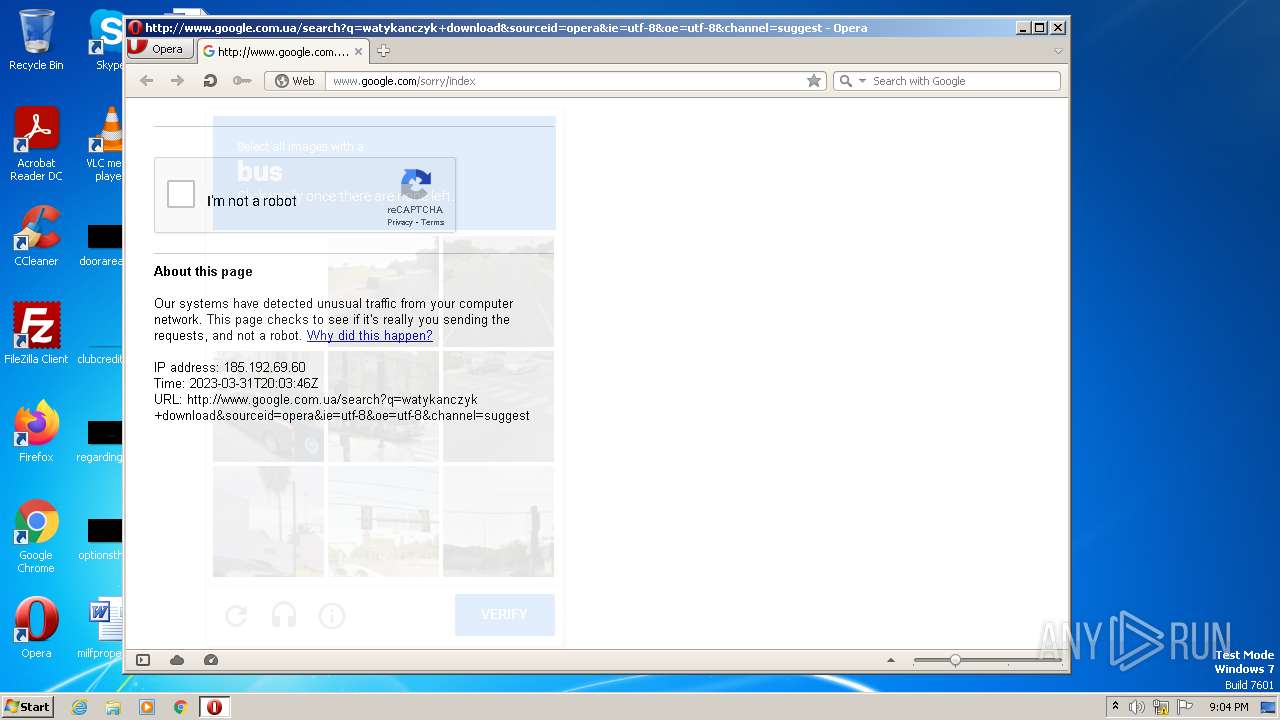
3868 | opera.exe | GET | 302 | 142.250.184.195:80 | http://www.google.com.ua/search?q=watykanczyk+download&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | html | 459 b | whitelisted |
2696 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
3164 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3868 | opera.exe | GET | 200 | 142.250.186.110:80 | http://clients1.google.com/complete/search?q=watykanczyk&client=opera-suggest-omnibox&hl=de | US | text | 107 b | whitelisted |
3164 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEH1NQqkrQx1%2BZFPnwZqNWHc%3D | US | der | 1.41 Kb | whitelisted |
3868 | opera.exe | GET | 200 | 142.250.186.110:80 | http://clients1.google.com/complete/search?q=watykanczu&client=opera-suggest-omnibox&hl=de | US | text | 37 b | whitelisted |
3868 | opera.exe | GET | 200 | 142.250.186.110:80 | http://clients1.google.com/complete/search?q=watykanczuk+d&client=opera-suggest-omnibox&hl=de | US | text | 40 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1364 | iexplore.exe | 45.77.230.212:443 | — | AS-CHOOPA | GB | suspicious |
2696 | iexplore.exe | 13.107.21.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1364 | iexplore.exe | 23.37.41.57:80 | x1.c.lencr.org | AKAMAI-AS | DE | suspicious |
1364 | iexplore.exe | 172.67.75.163:443 | trk.adtrk18.com | CLOUDFLARENET | US | suspicious |
2696 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1364 | iexplore.exe | 67.27.233.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
1364 | iexplore.exe | 104.26.8.59:443 | trk.adtrk18.com | CLOUDFLARENET | US | suspicious |
1364 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1364 | iexplore.exe | 188.114.96.3:443 | rtd.tracktrack1234.net | CLOUDFLARENET | NL | malicious |
— | — | 13.107.5.80:443 | api.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r3.o.lencr.org |
| shared |
trk.adtrk18.com |
| suspicious |
rtd.tracktrack1234.net |
| malicious |
ocsp.pki.goog |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
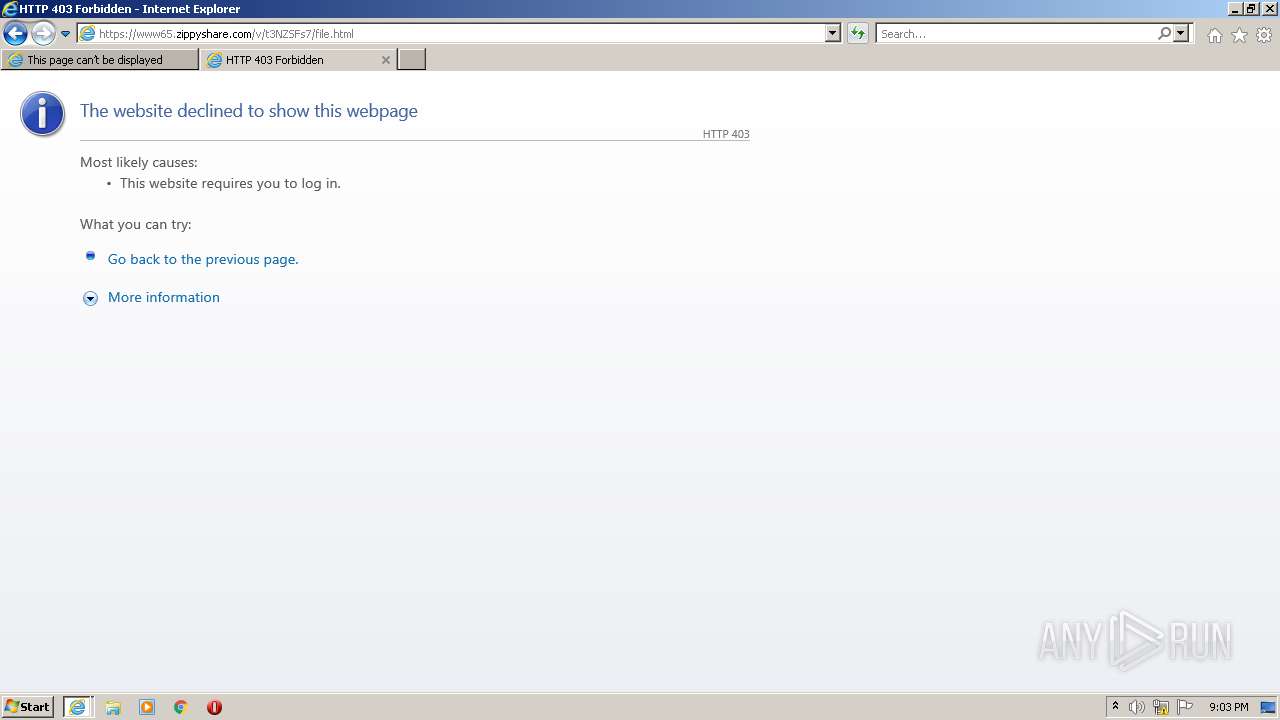
— | — | Potentially Bad Traffic | ET INFO File Sharing Related Domain in DNS Lookup (zippyshare .com) |
— | — | Potentially Bad Traffic | ET INFO File Sharing Related Domain in DNS Lookup (zippyshare .com) |
3164 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Domain (zippyshare .com in TLS SNI) |
3164 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Domain (zippyshare .com in TLS SNI) |
3868 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3868 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3868 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3868 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1 ETPRO signatures available at the full report