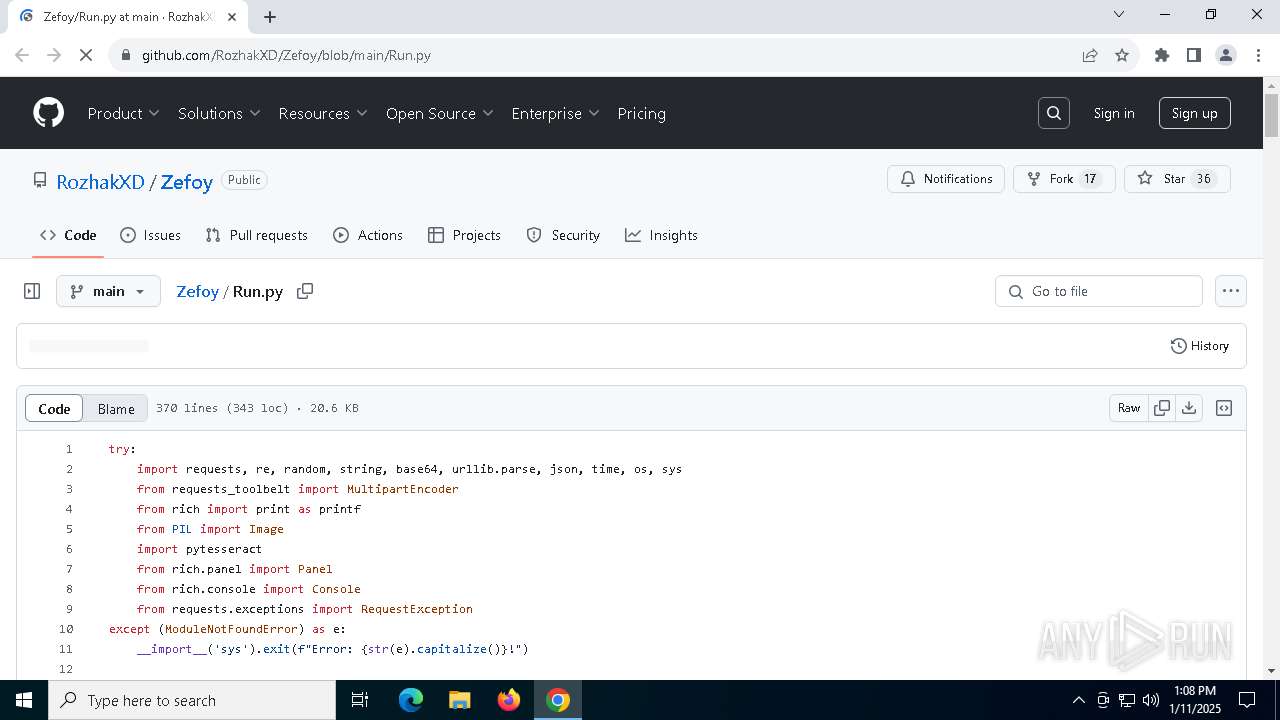
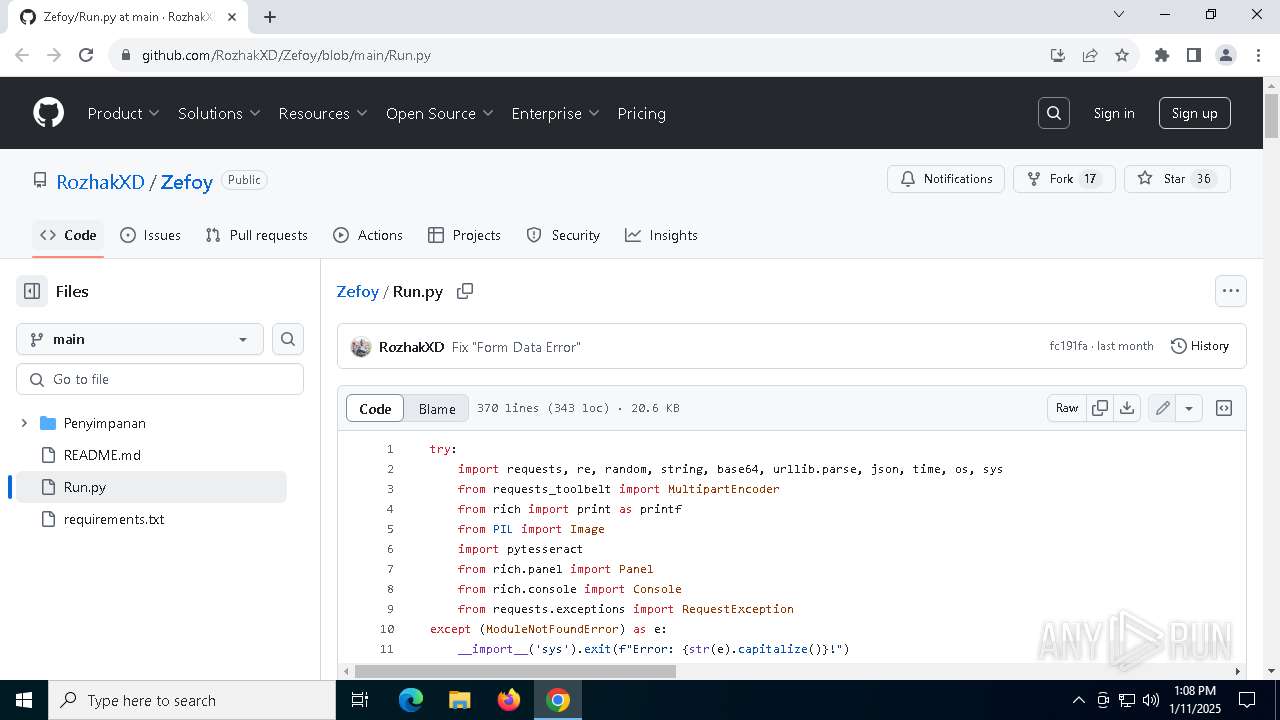
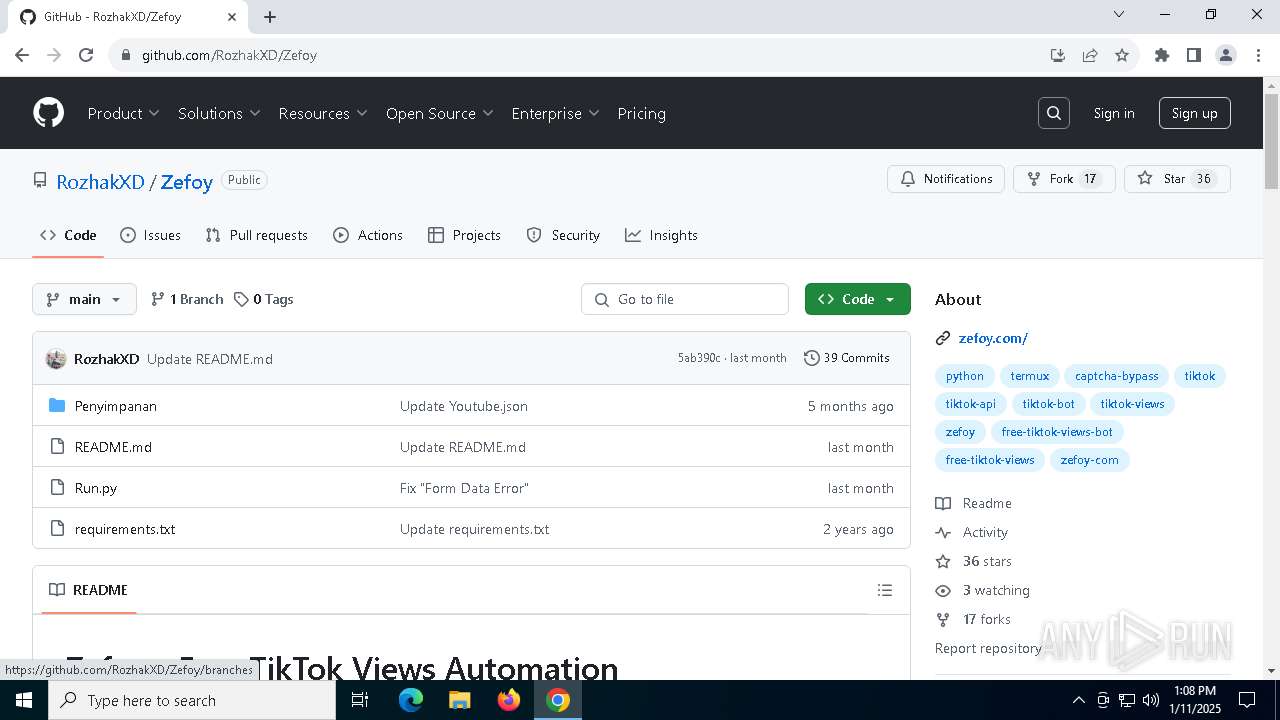
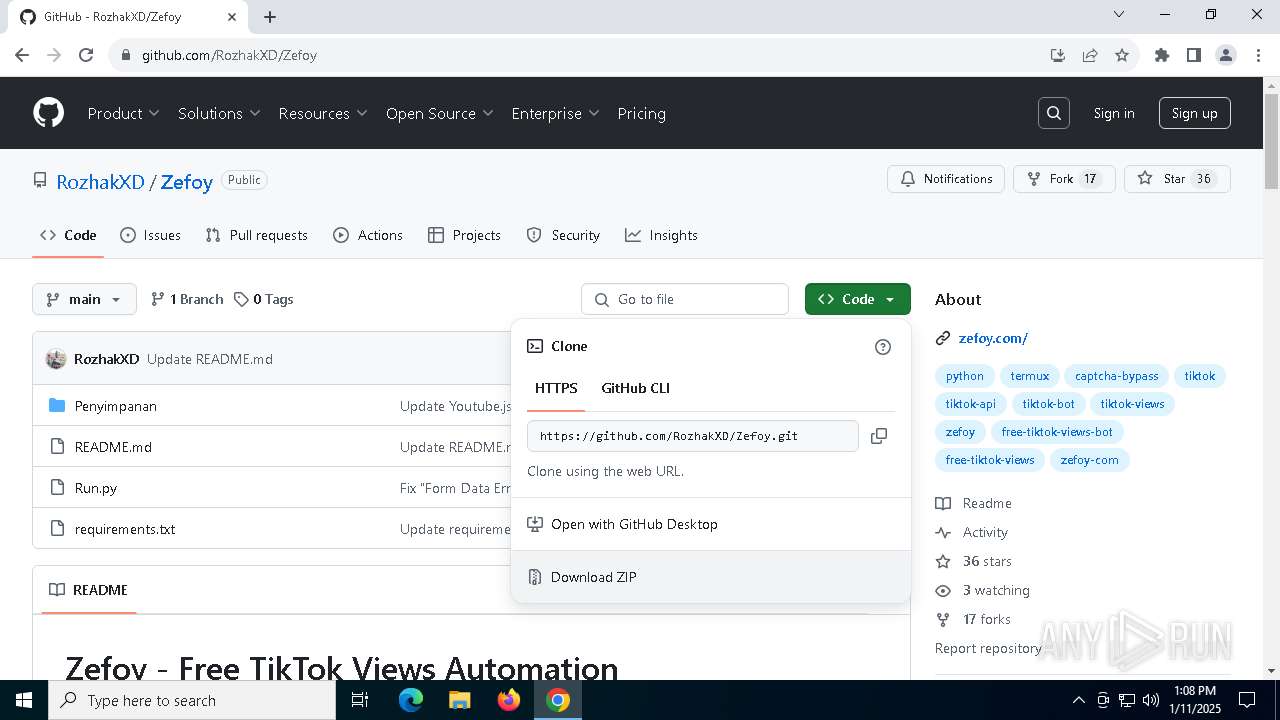
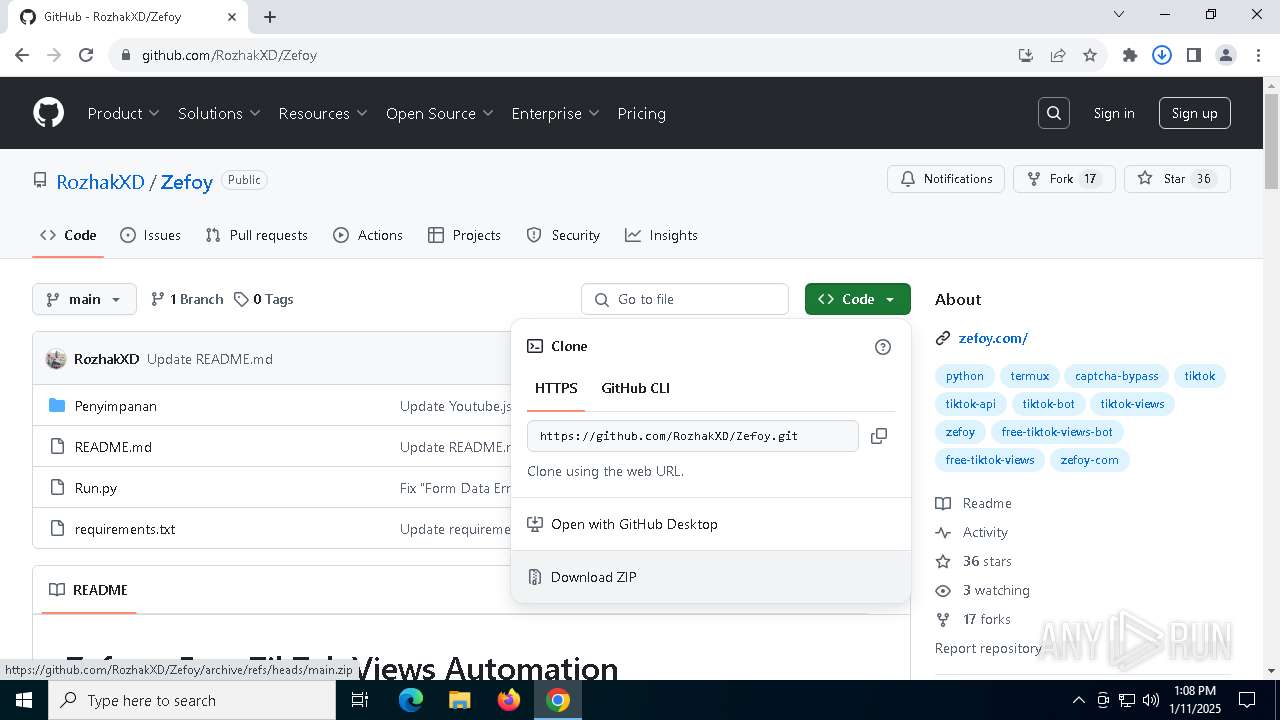
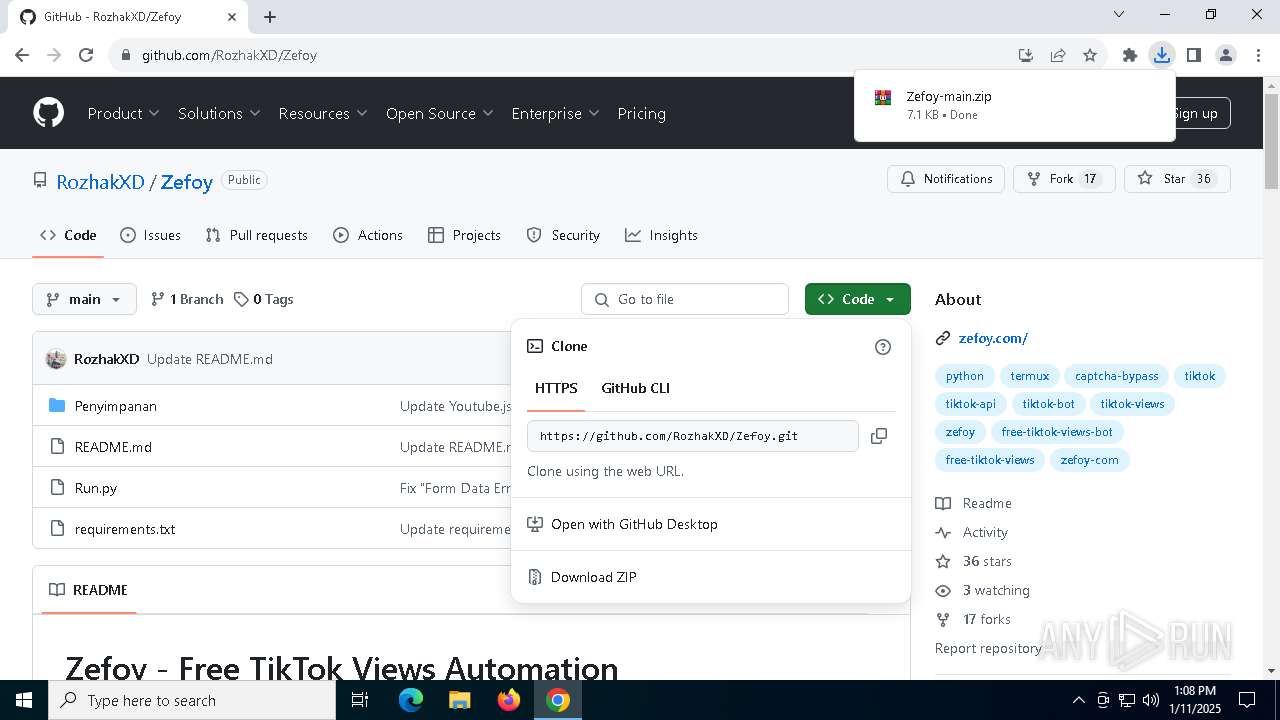
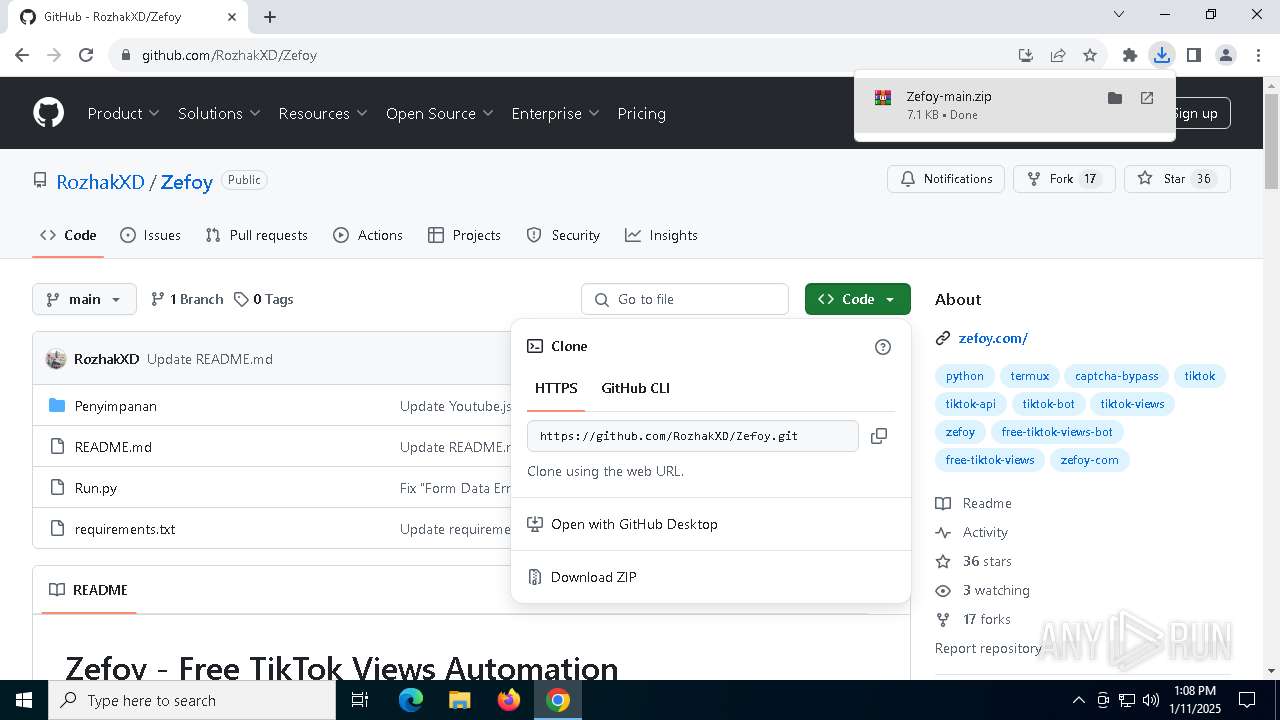
| URL: | https://github.com/RozhakXD/Zefoy/blob/main/Run.py |
| Full analysis: | https://app.any.run/tasks/c4100b09-da34-474c-8db1-bbff6b6cae58 |
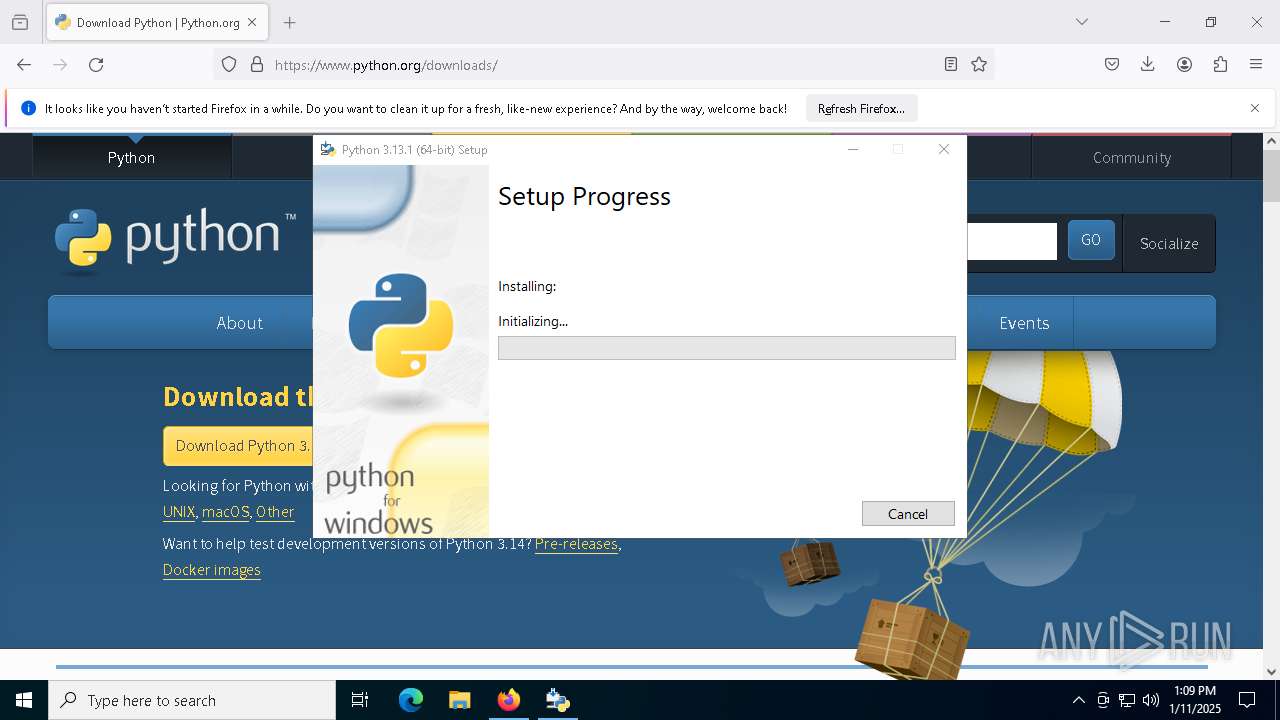
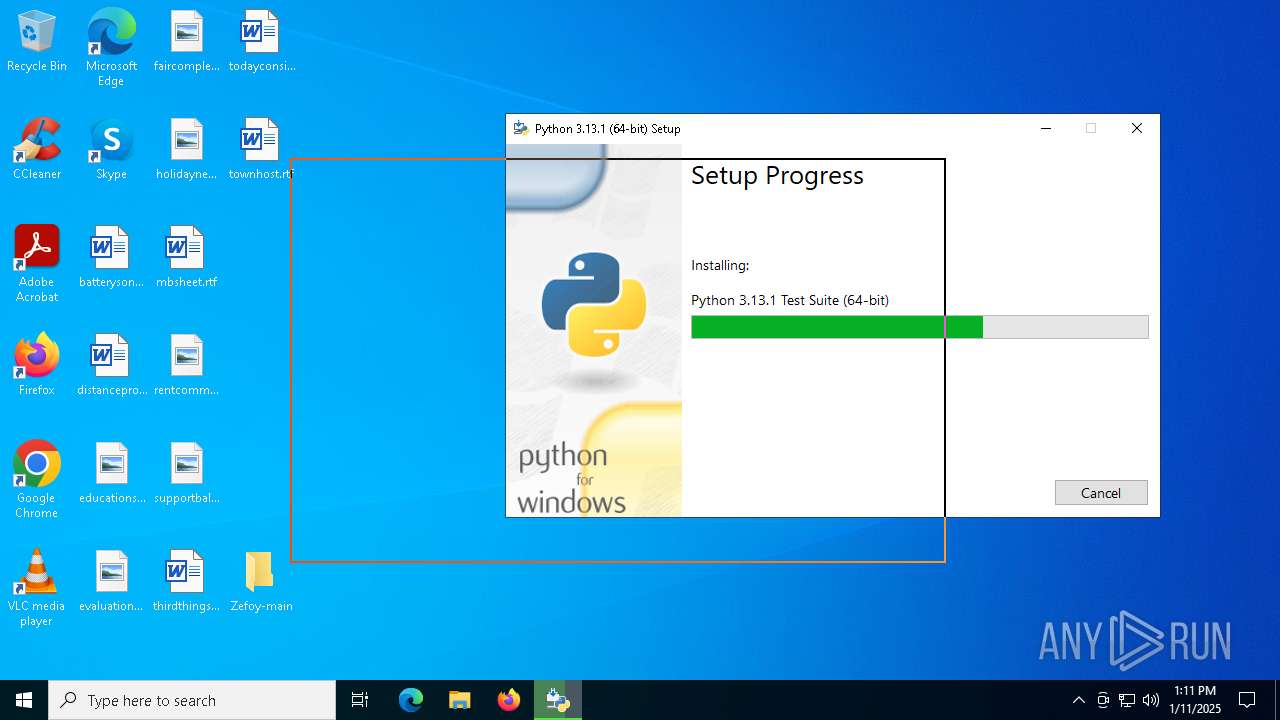
| Verdict: | Malicious activity |
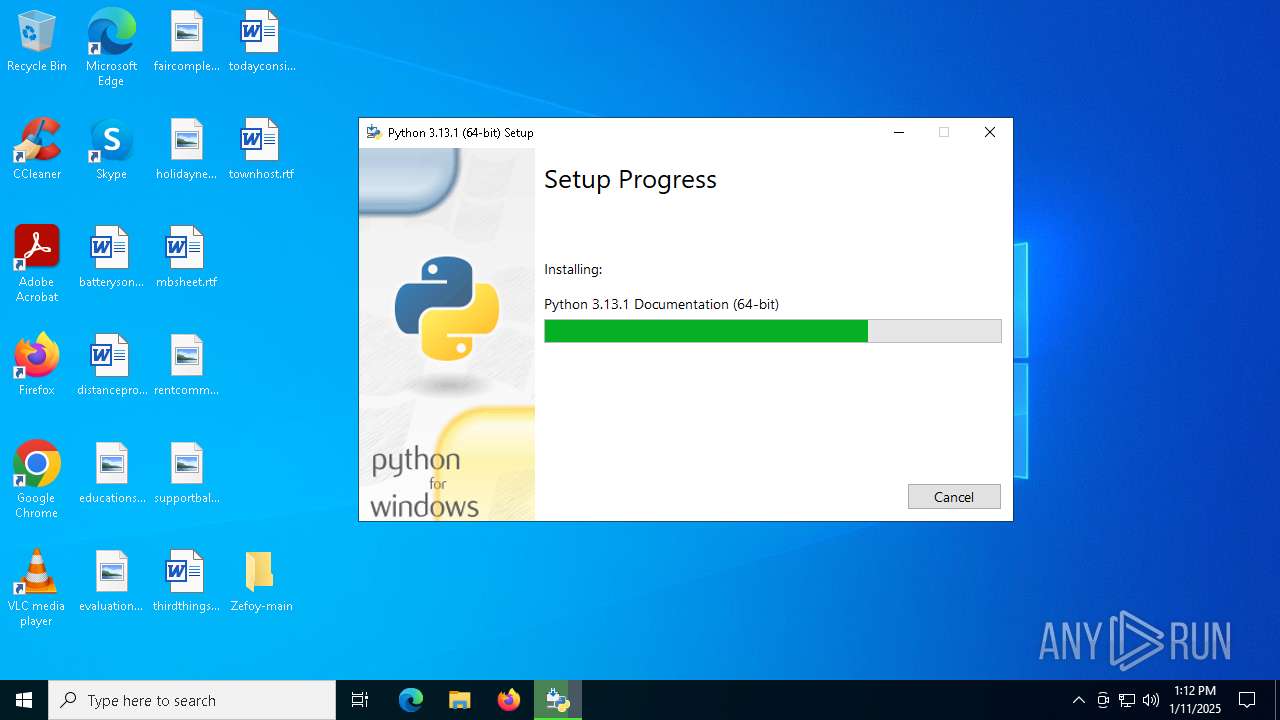
| Analysis date: | January 11, 2025, 13:08:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8F3F067F3AB852848BC9AD8F23396FE7 |
| SHA1: | 6C6B246E95DDFCC51F8D928B41E50BCBD898072B |
| SHA256: | 9624CF752B0879066F8152D617D90EE62C2D479D8A3D7EE8BB2BFE3BC2B82817 |
| SSDEEP: | 3:N8tEdqeSuccuKIERcc:2usejDyst |
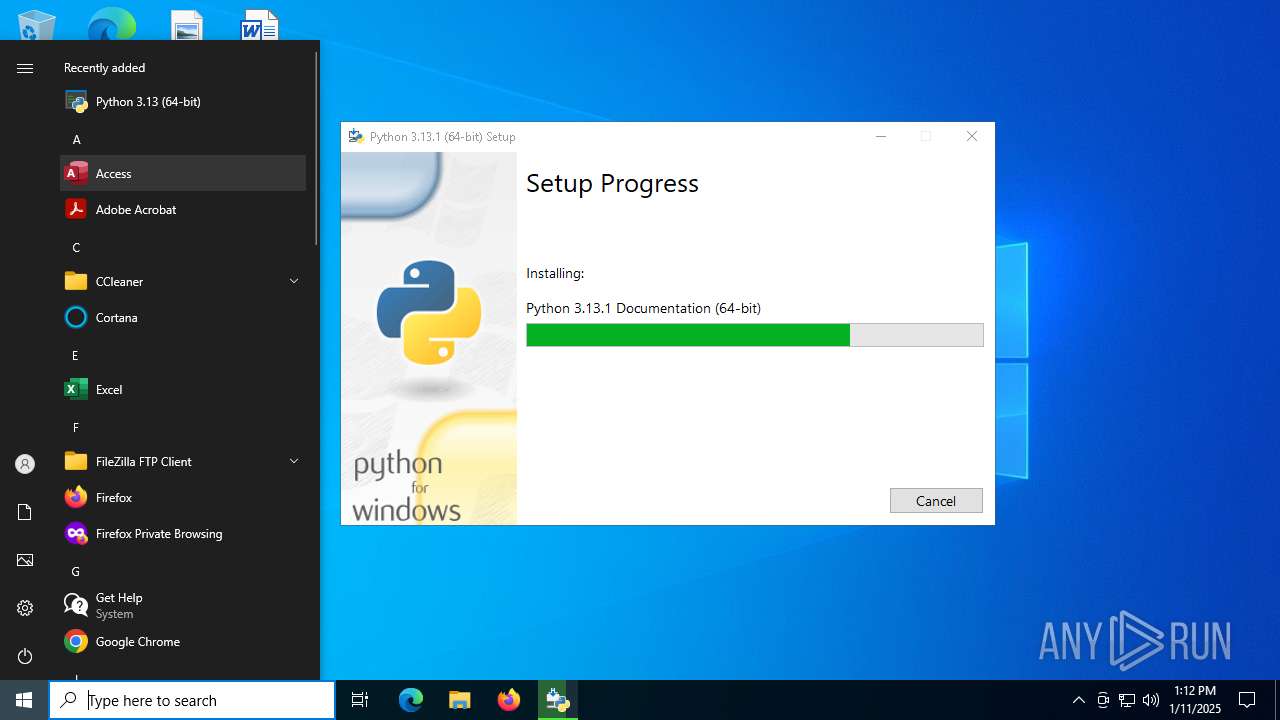
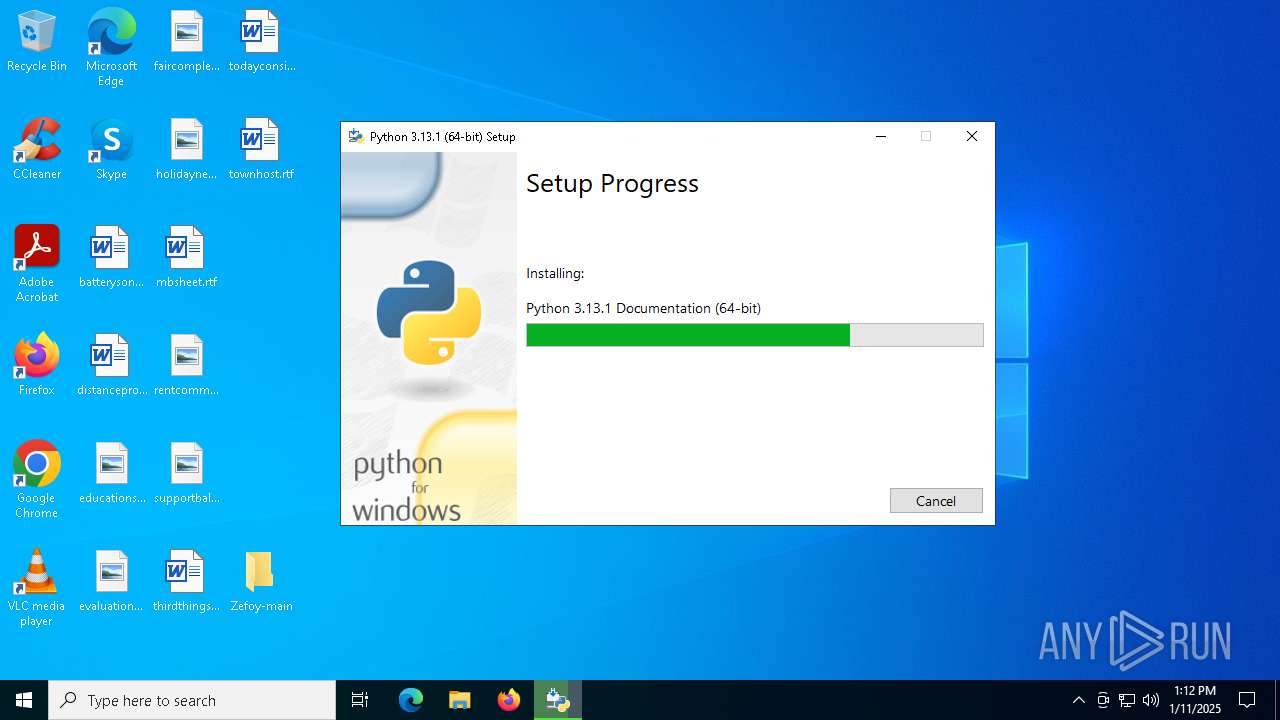
MALICIOUS
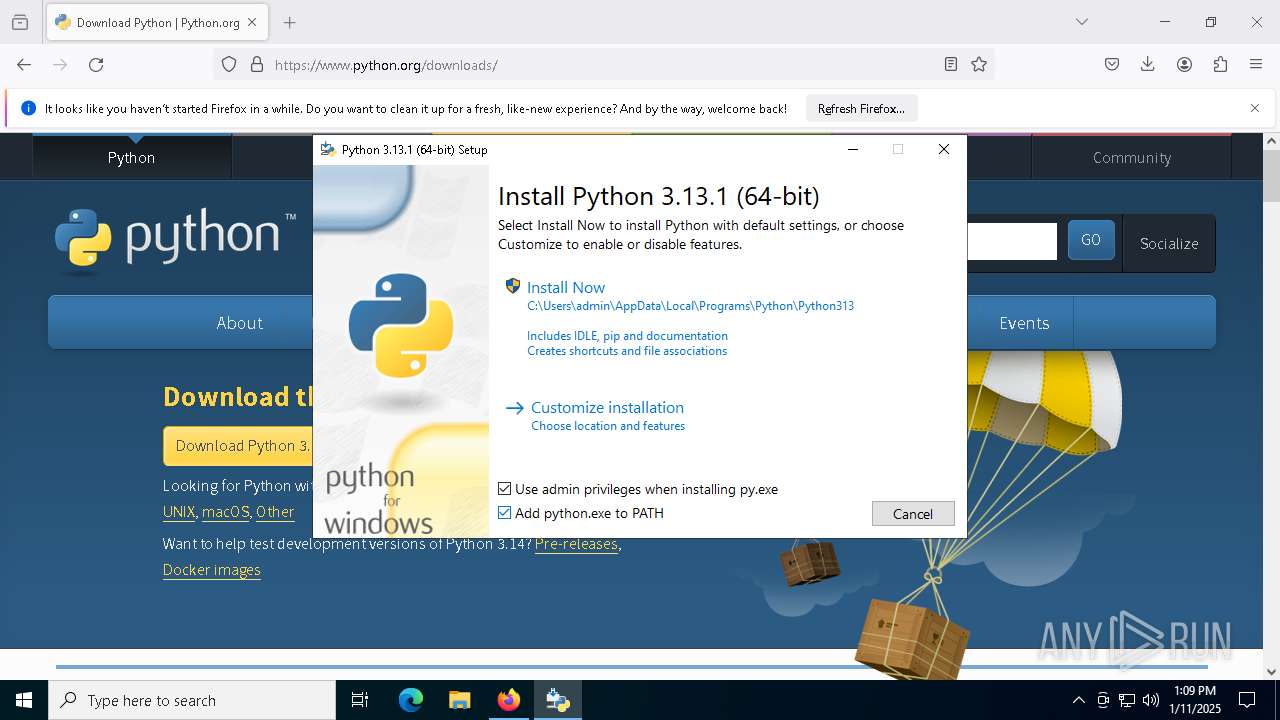
Changes the autorun value in the registry
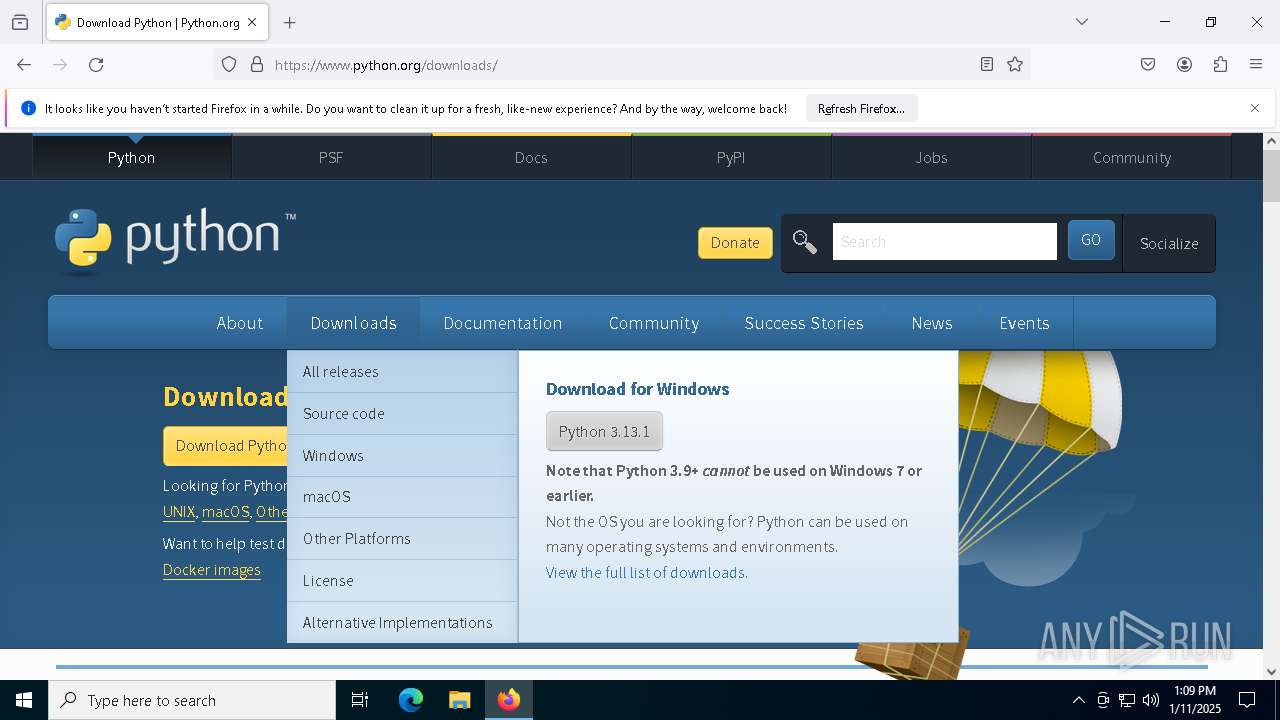
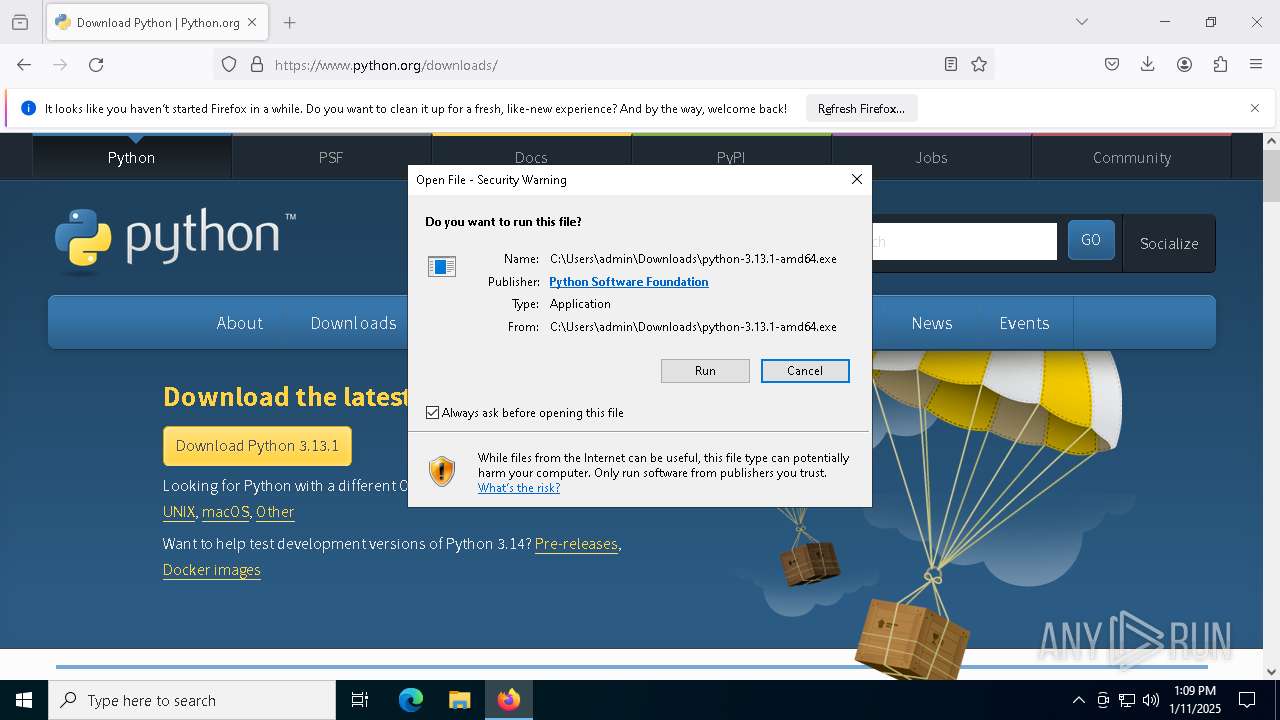
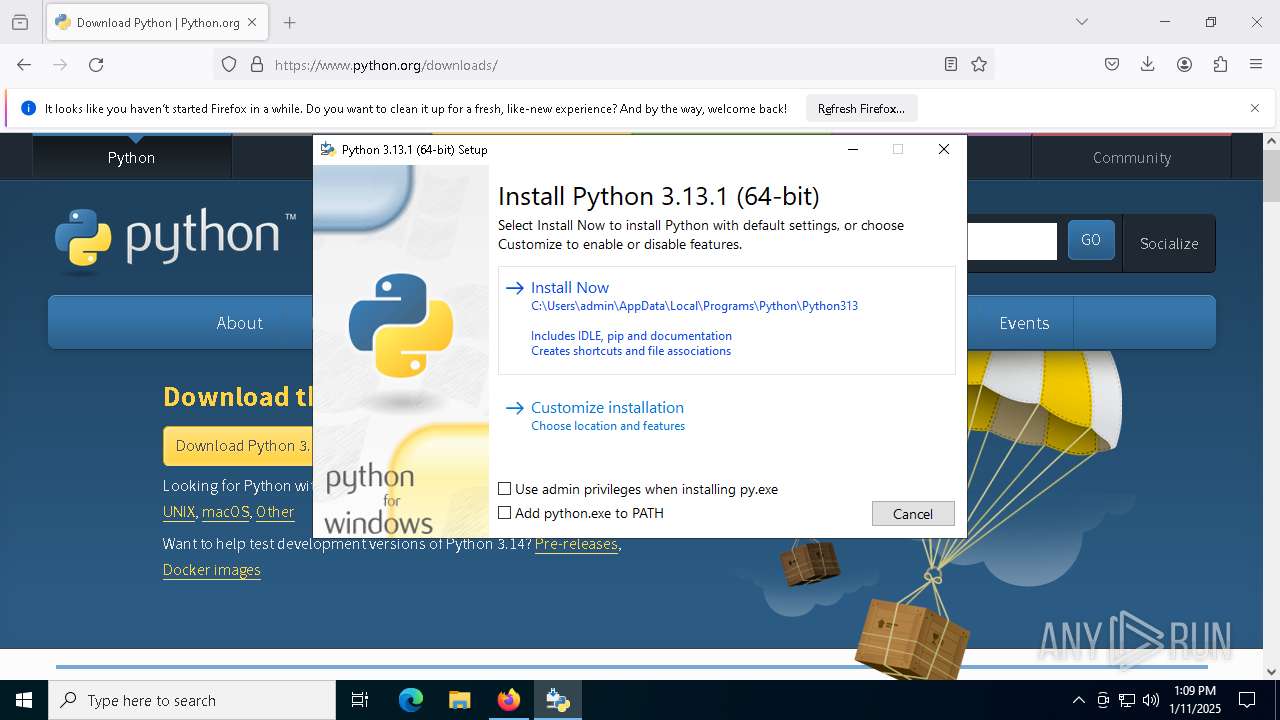
- python-3.13.1-amd64.exe (PID: 7524)
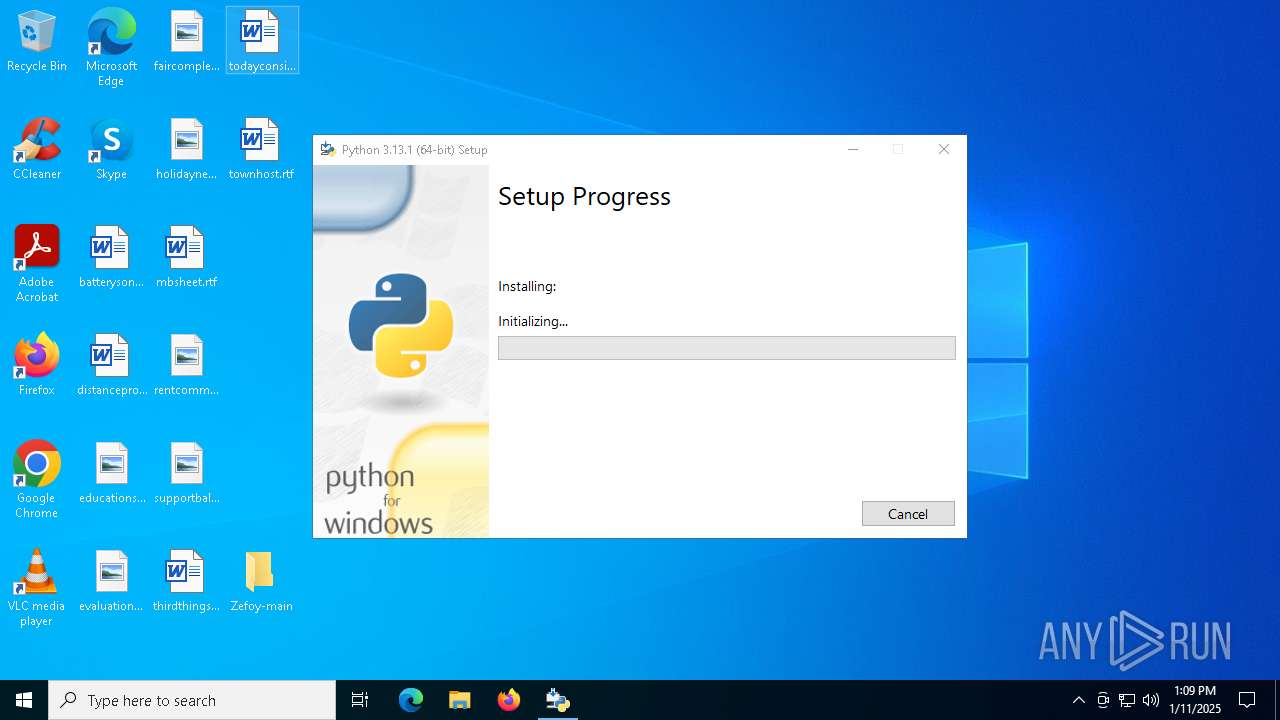
SUSPICIOUS
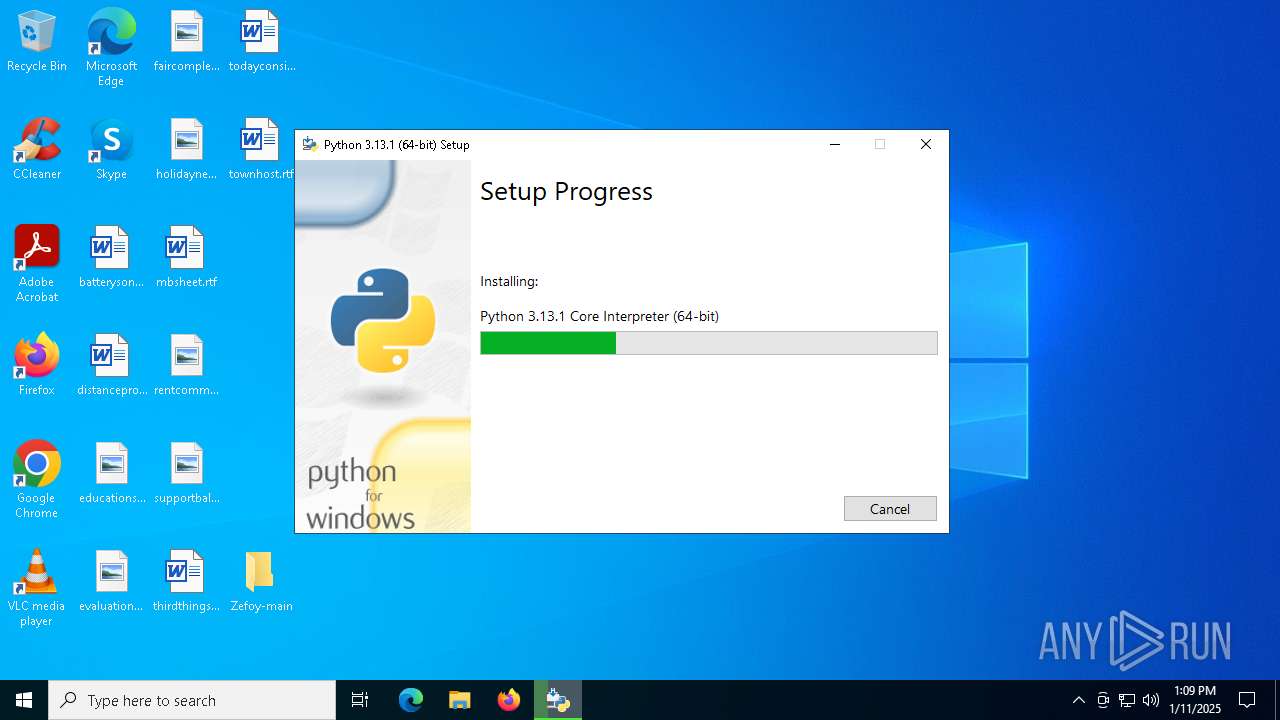
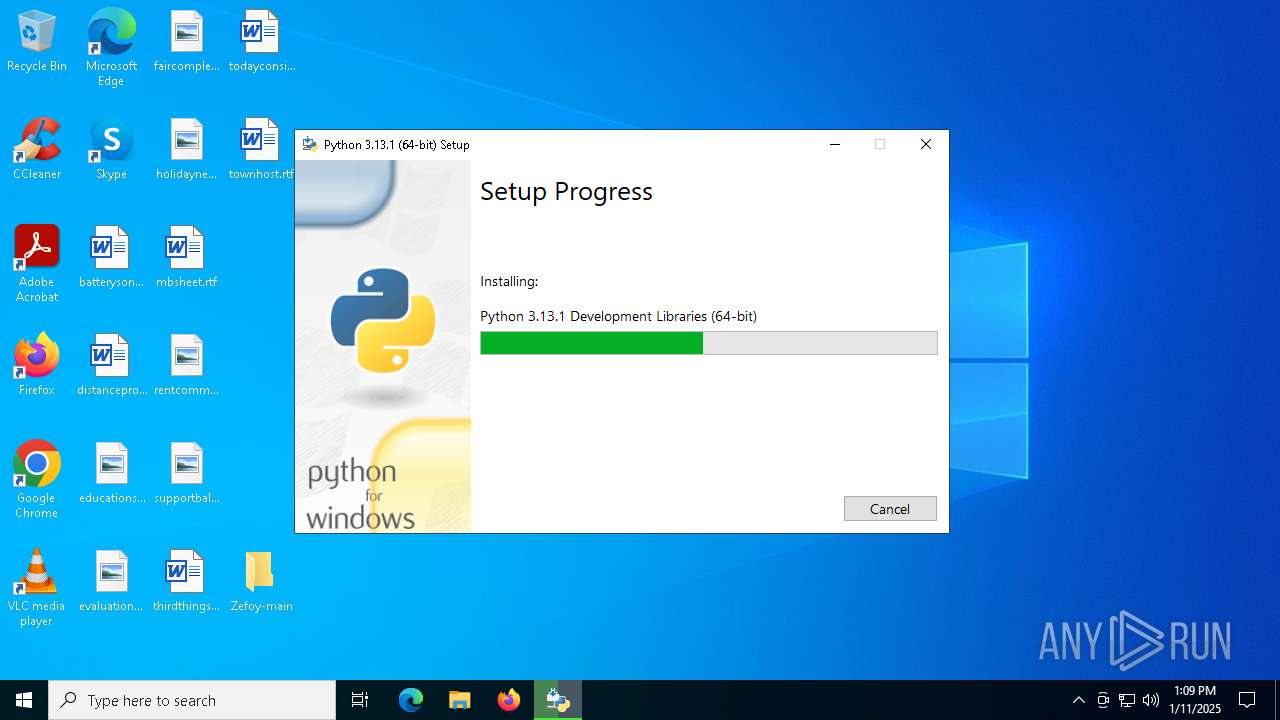
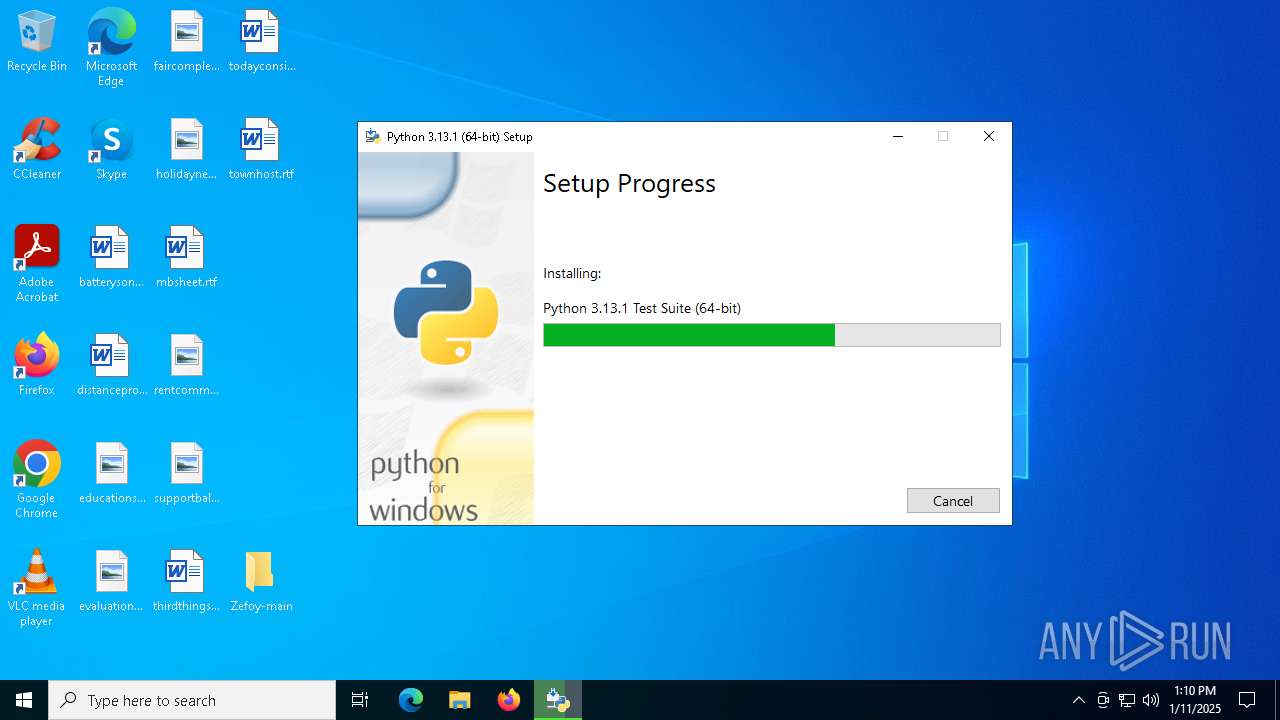
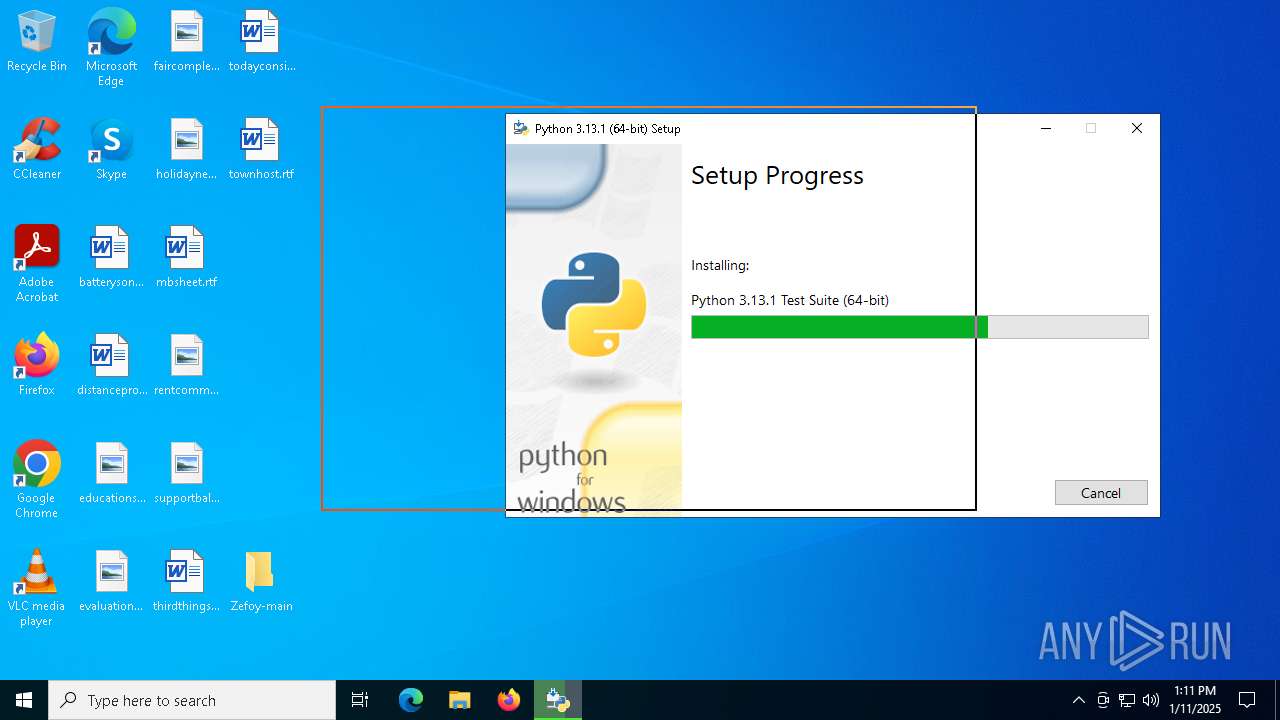
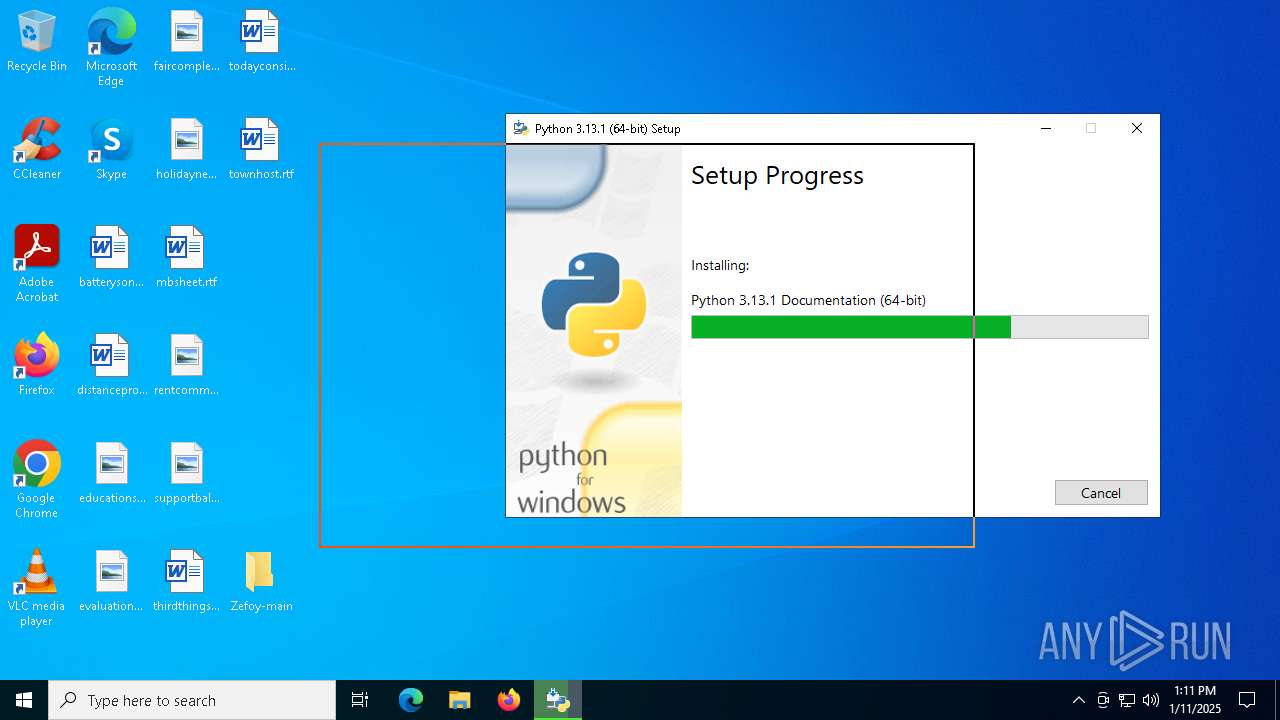
Executable content was dropped or overwritten
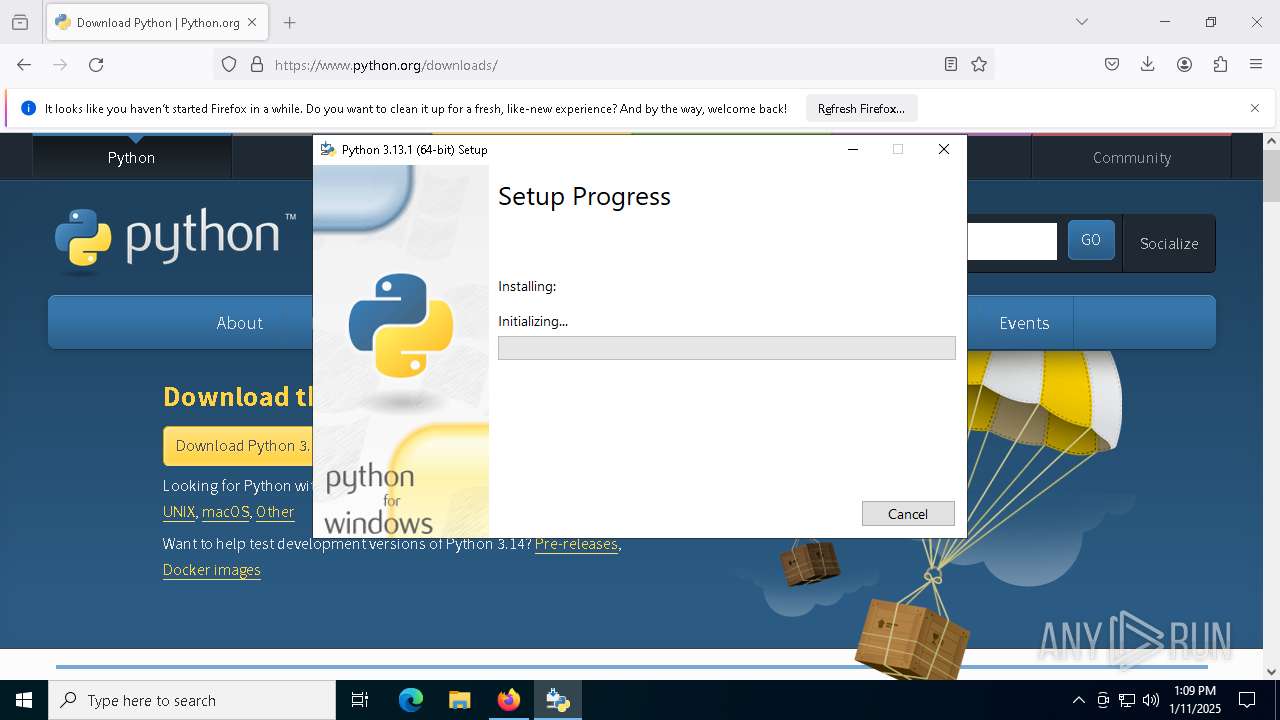
- python-3.13.1-amd64.exe (PID: 7500)
- python-3.13.1-amd64.exe (PID: 7524)
- python-3.13.1-amd64.exe (PID: 7612)
Searches for installed software
- python-3.13.1-amd64.exe (PID: 7524)
- dllhost.exe (PID: 7660)
Reads security settings of Internet Explorer
- python-3.13.1-amd64.exe (PID: 7524)
Executes as Windows Service
- VSSVC.exe (PID: 7704)
Starts itself from another location
- python-3.13.1-amd64.exe (PID: 7524)
Creates a software uninstall entry
- python-3.13.1-amd64.exe (PID: 7524)
The process drops C-runtime libraries
- python-3.13.1-amd64.exe (PID: 7524)
- msiexec.exe (PID: 5992)
Process drops legitimate windows executable
- python-3.13.1-amd64.exe (PID: 7524)
- msiexec.exe (PID: 5992)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5992)
Process drops python dynamic module
- msiexec.exe (PID: 5992)
Checks Windows Trust Settings
- msiexec.exe (PID: 5992)
INFO
Checks supported languages
- SearchApp.exe (PID: 5064)
- python-3.13.1-amd64.exe (PID: 7500)
- python-3.13.1-amd64.exe (PID: 7524)
- python-3.13.1-amd64.exe (PID: 7612)
- msiexec.exe (PID: 5992)
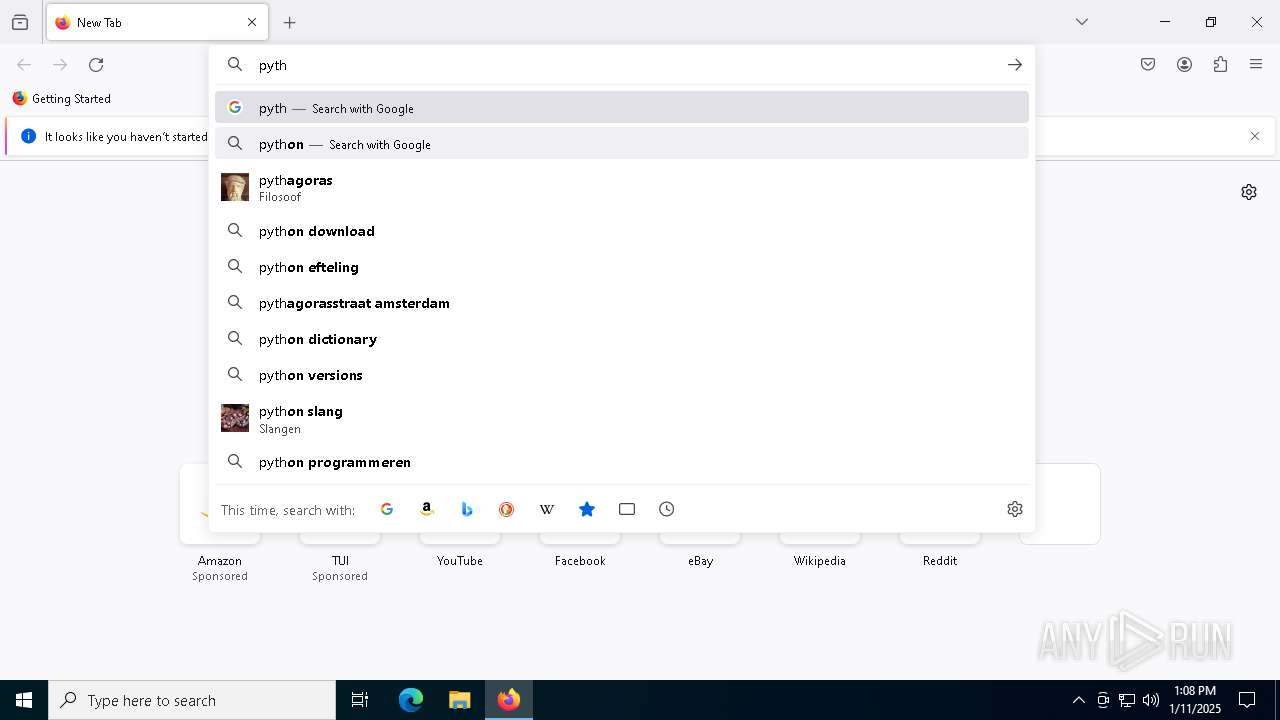
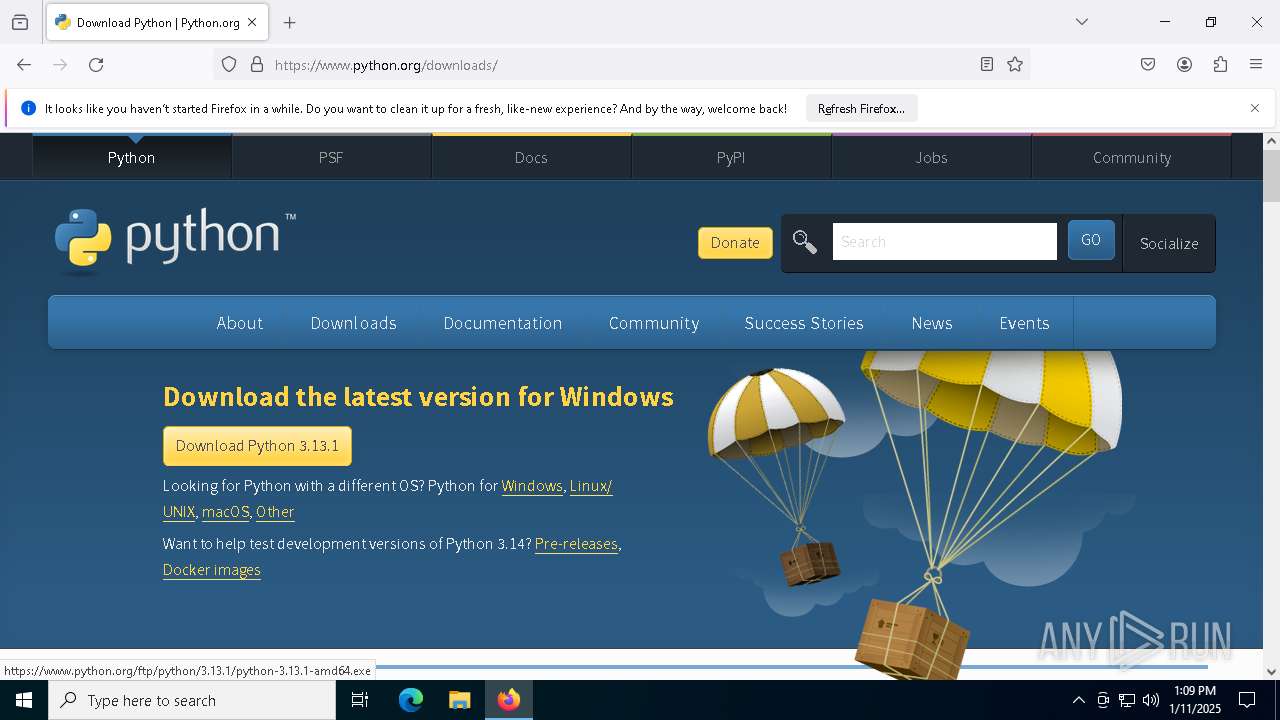
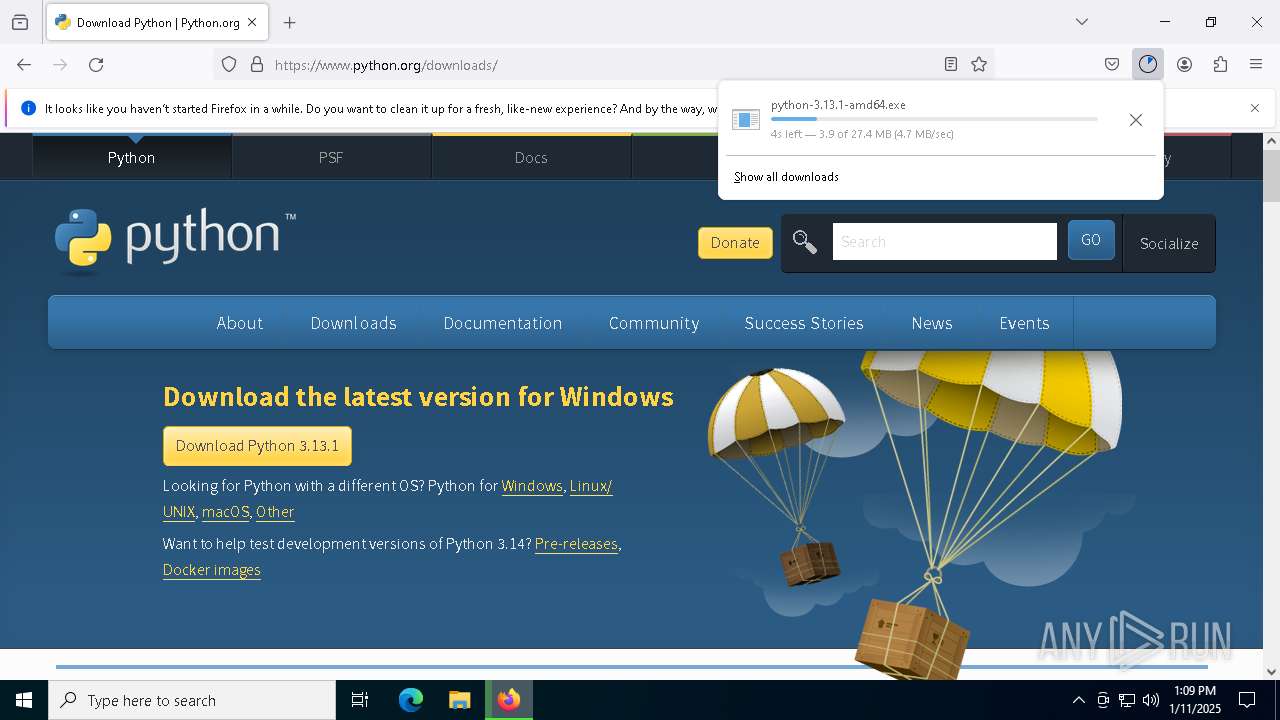
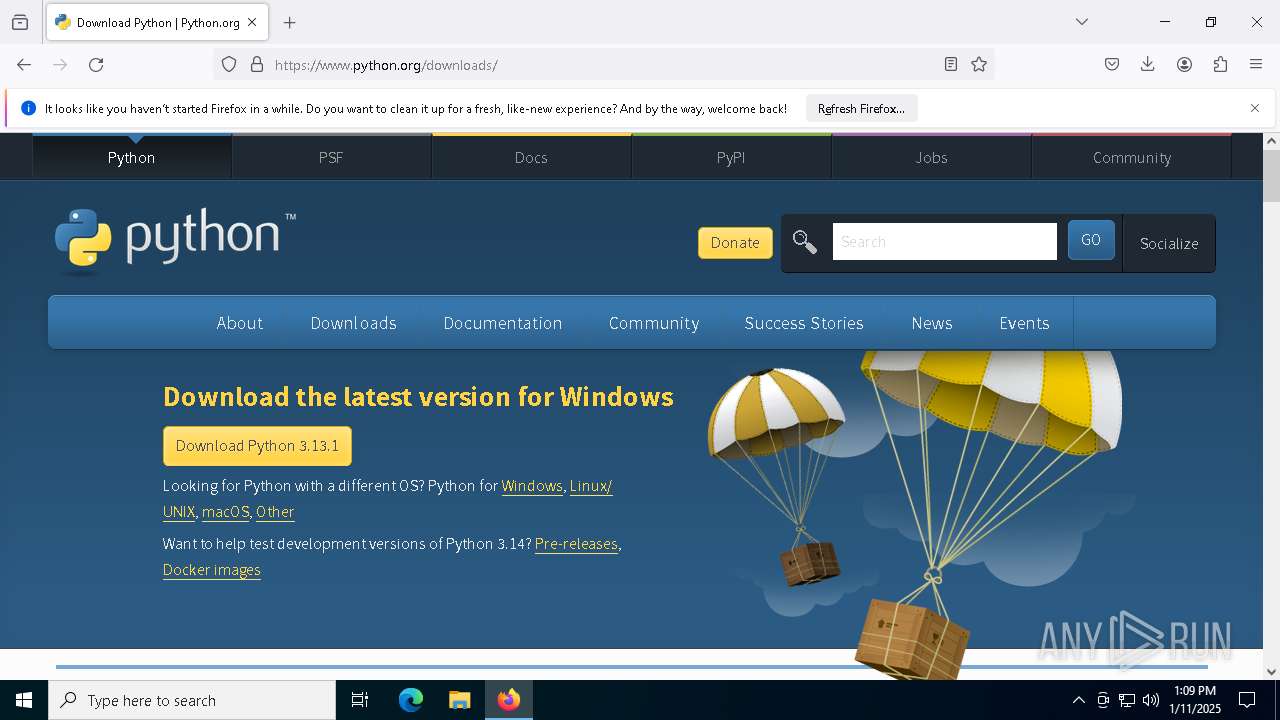
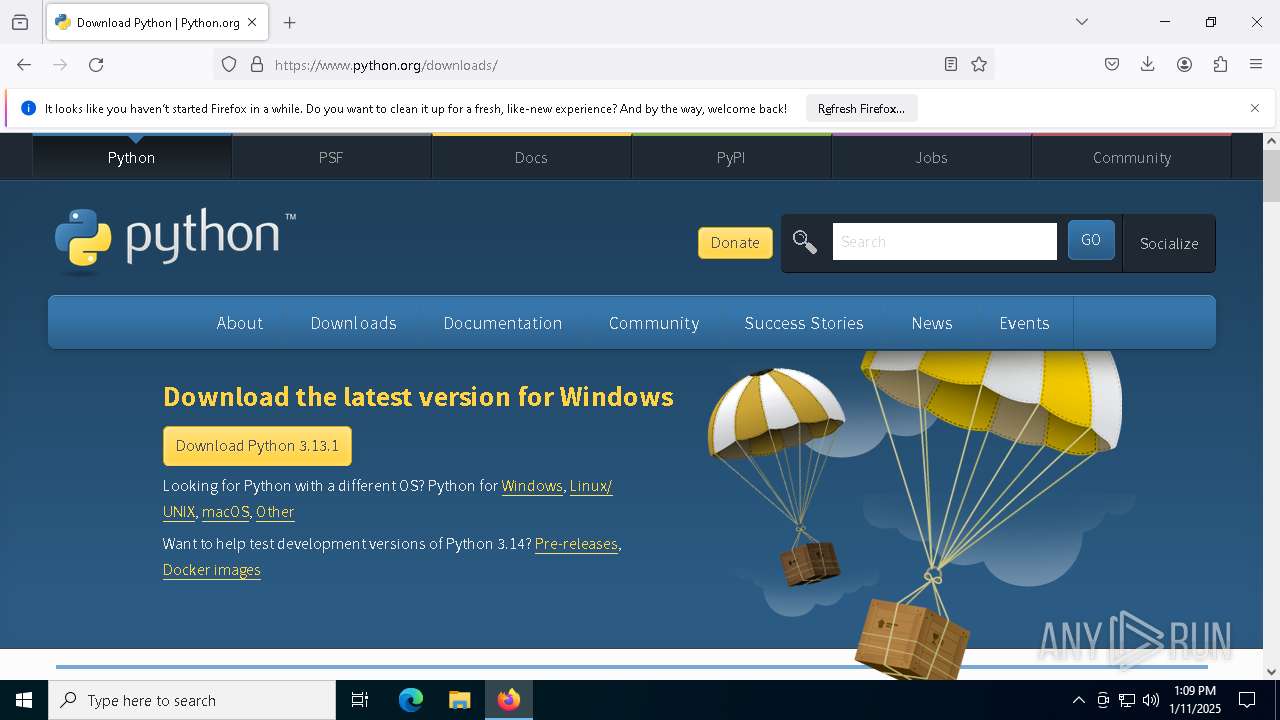
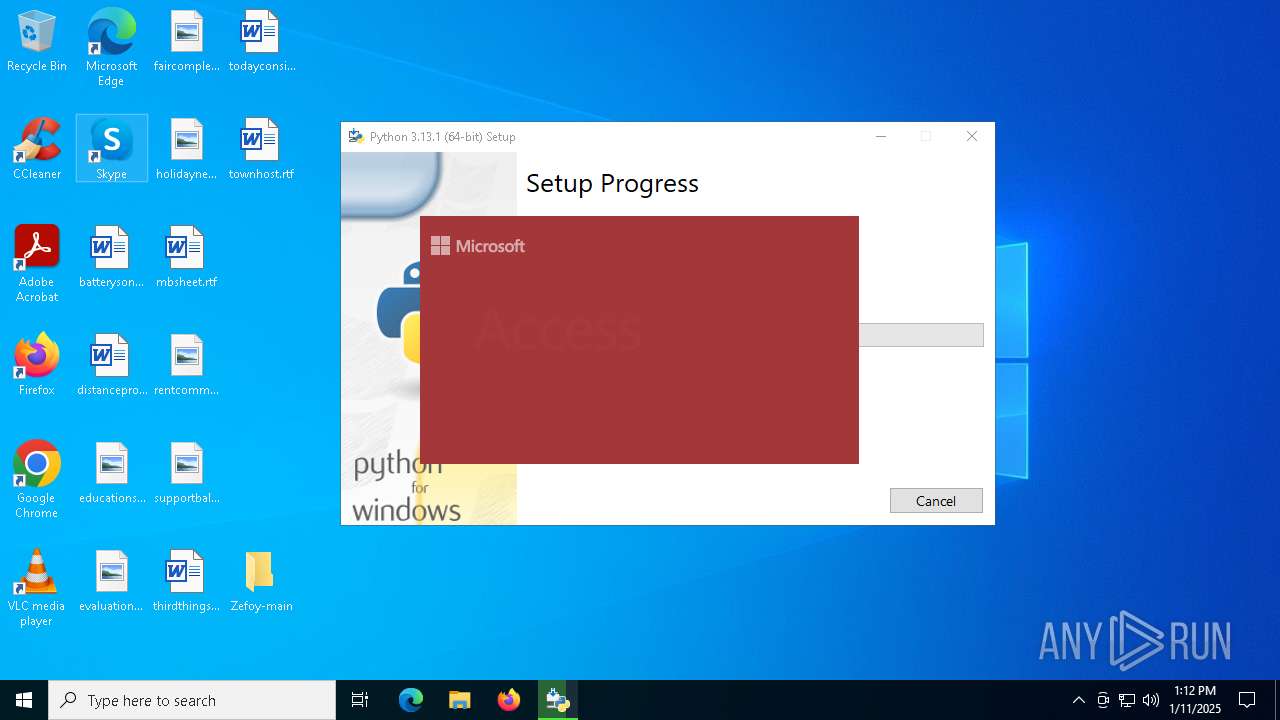
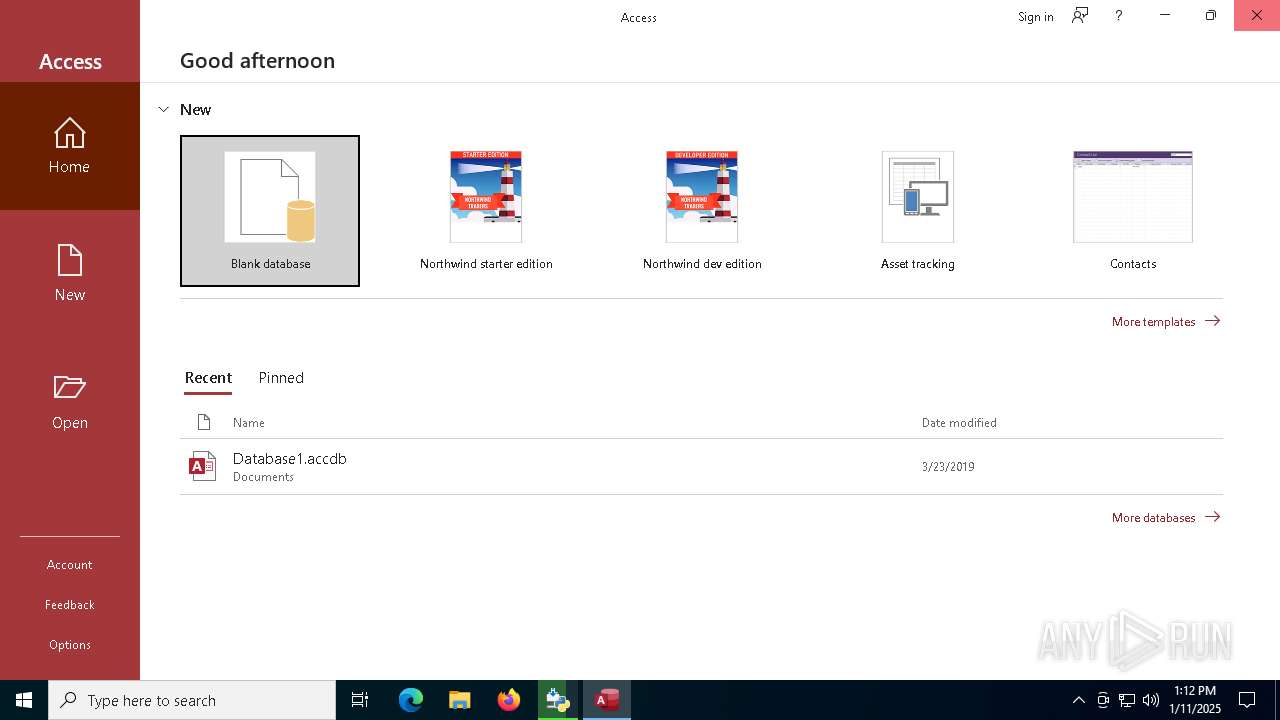
Manual execution by a user
- firefox.exe (PID: 6076)
- MSACCESS.EXE (PID: 5876)
Application launched itself
- chrome.exe (PID: 6168)
- firefox.exe (PID: 6076)
- firefox.exe (PID: 4716)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6168)
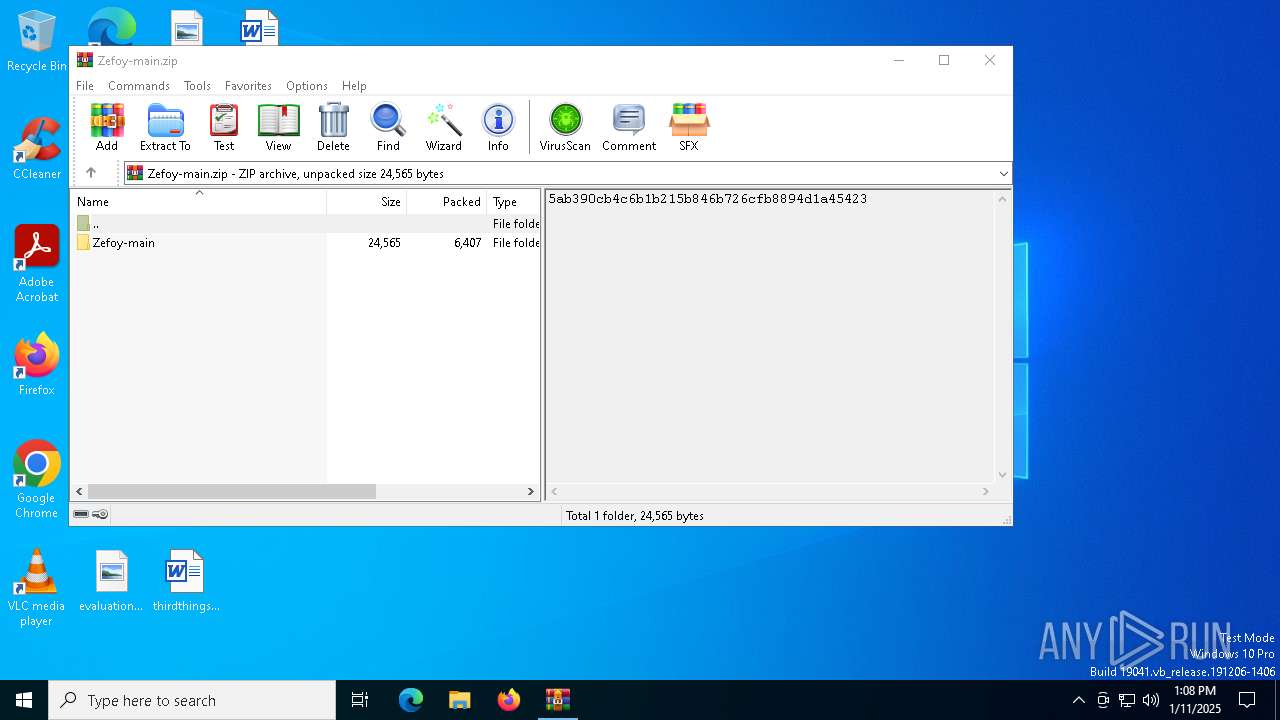
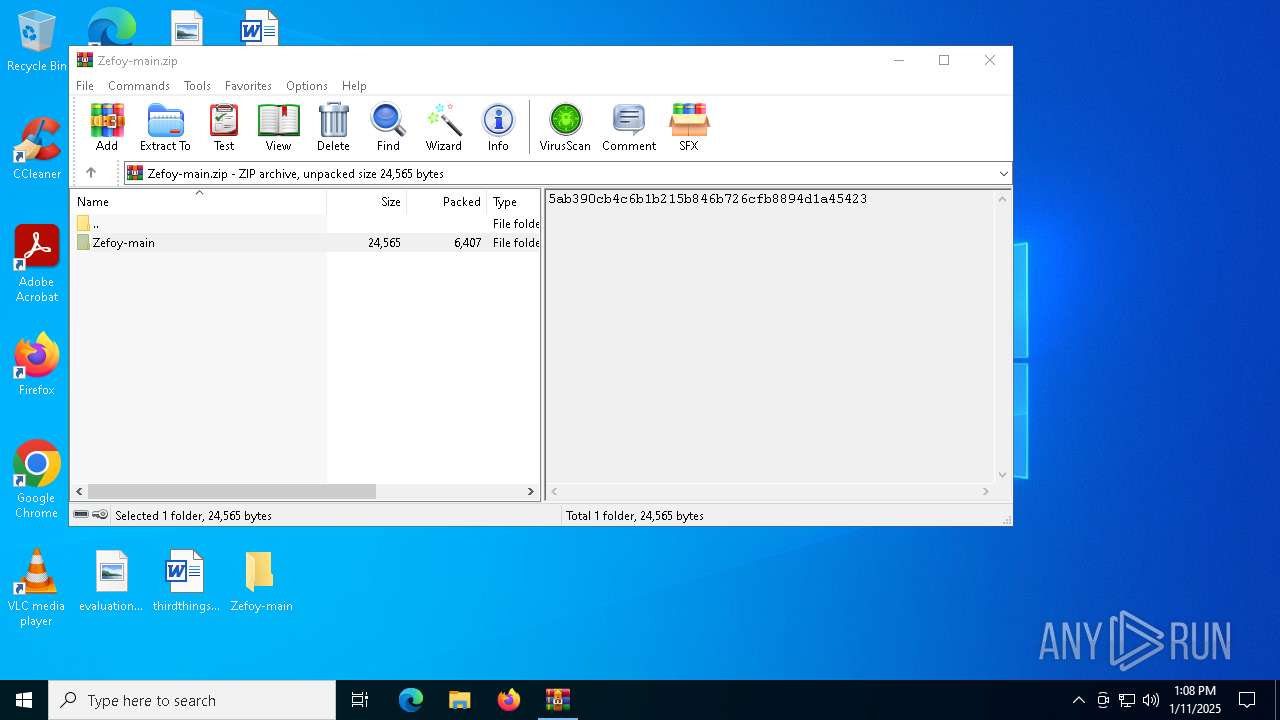
The process uses the downloaded file
- chrome.exe (PID: 6168)
- WinRAR.exe (PID: 5588)
- chrome.exe (PID: 2420)
- firefox.exe (PID: 4716)
- python-3.13.1-amd64.exe (PID: 7524)
Executable content was dropped or overwritten
- firefox.exe (PID: 4716)
- msiexec.exe (PID: 5992)
The sample compiled with english language support
- firefox.exe (PID: 4716)
- python-3.13.1-amd64.exe (PID: 7500)
- python-3.13.1-amd64.exe (PID: 7524)
- msiexec.exe (PID: 5992)
Create files in a temporary directory
- python-3.13.1-amd64.exe (PID: 7500)
- python-3.13.1-amd64.exe (PID: 7524)
Reads the computer name
- python-3.13.1-amd64.exe (PID: 7524)
- python-3.13.1-amd64.exe (PID: 7612)
- msiexec.exe (PID: 5992)
Manages system restore points
- SrTasks.exe (PID: 8164)
Process checks computer location settings
- python-3.13.1-amd64.exe (PID: 7524)
- SearchApp.exe (PID: 5064)
Creates files or folders in the user directory
- python-3.13.1-amd64.exe (PID: 7524)
- msiexec.exe (PID: 5992)
Reads the machine GUID from the registry
- python-3.13.1-amd64.exe (PID: 7524)
- python-3.13.1-amd64.exe (PID: 7612)
- msiexec.exe (PID: 5992)
- SearchApp.exe (PID: 5064)
Creates files in the program directory
- python-3.13.1-amd64.exe (PID: 7612)
Reads the software policy settings
- msiexec.exe (PID: 5992)
- SearchApp.exe (PID: 5064)
Creates a software uninstall entry
- msiexec.exe (PID: 5992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
170
Monitored processes
33
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5112 --field-trial-handle=1932,i,17135535670151876249,1532273626395403657,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4528 --field-trial-handle=1932,i,17135535670151876249,1532273626395403657,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4444 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2152 -parentBuildID 20240213221259 -prefsHandle 2144 -prefMapHandle 2132 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {9fde6db0-d883-4303-a55c-2262ecbb7d74} 4716 "\\.\pipe\gecko-crash-server-pipe.4716" 1f211281b10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 4648 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1912 -parentBuildID 20240213221259 -prefsHandle 1844 -prefMapHandle 1820 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {8f735b2c-228c-4bab-81e3-fc674d122787} 4716 "\\.\pipe\gecko-crash-server-pipe.4716" 1f21e1f0910 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 4716 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 4824 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5452 -childID 4 -isForBrowser -prefsHandle 5372 -prefMapHandle 5376 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1464 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {cc12cbd4-2d3c-4df8-b946-2fdf0b1169cb} 4716 "\\.\pipe\gecko-crash-server-pipe.4716" 1f22522a850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5064 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5548 --field-trial-handle=1932,i,17135535670151876249,1532273626395403657,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5588 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Zefoy-main.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5876 | "C:\Program Files\Microsoft Office\root\Office16\MSACCESS.EXE" | C:\Program Files\Microsoft Office\root\Office16\MSACCESS.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Access Exit code: 3221225547 Version: 16.0.16026.20146 Modules
| |||||||||||||||
Total events
59 563
Read events
55 009
Write events
4 448
Delete events
106
Modification events
| (PID) Process: | (6168) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6168) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6168) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6168) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6168) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Feeds\DSB |
| Operation: | write | Name: | DynamicText |
Value: | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Feeds\DSB |
| Operation: | write | Name: | DynamicTextTruncated |
Value: | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\DynamicSearchBox |
| Operation: | write | Name: | TelemetryID |
Value: 000023C6E5EB2964DB01 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\DynamicSearchBox |
| Operation: | write | Name: | TelemetryID |
Value: 00009629E8EB2964DB01 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\Internet Explorer\DOMStorage\bing.com |
| Operation: | write | Name: | Total |
Value: 50667 | |||
Executable files
83
Suspicious files
430
Text files
2 908
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF136005.TMP | — | |
MD5:— | SHA256:— | |||
| 6168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF136005.TMP | — | |
MD5:— | SHA256:— | |||
| 6168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF136005.TMP | — | |
MD5:— | SHA256:— | |||
| 6168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF136015.TMP | — | |
MD5:— | SHA256:— | |||
| 6168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF136015.TMP | — | |
MD5:— | SHA256:— | |||
| 6168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
171
DNS requests
181
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2736 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
4716 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
4716 | firefox.exe | POST | 200 | 23.53.40.154:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
4716 | firefox.exe | POST | 200 | 142.250.185.67:80 | http://o.pki.goog/s/wr3/jLM | unknown | — | — | whitelisted |
4716 | firefox.exe | POST | 200 | 23.53.40.154:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2736 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.177:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6168 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6596 | chrome.exe | 140.82.121.3:443 | github.com | GITHUB | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
github.com |
| shared |
accounts.google.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |