| File name: | PK SEARCH PRIVATE.exe |
| Full analysis: | https://app.any.run/tasks/038a3d70-b690-433c-b68d-bc4d59e83fc6 |
| Verdict: | Malicious activity |
| Analysis date: | August 09, 2024, 04:17:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 02FCB926B39E8BFF8EBB5B2CAFA17900 |
| SHA1: | ED2D224E97D185DA0287B16DF2571A440251365A |
| SHA256: | 9620E628CA8333B95ADEF7B2442383F2E2981B979B301AA353148851079338F7 |
| SSDEEP: | 98304:ugIZngLSL8+jzLQ9ccUmYoJw/l7YhRuMm6JVgH4tMqswIZBjn3rXgplC9iaIuwpY:ylQNHBmp4IZQURO7FPw76vU |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- PK SEARCH PRIVATE.exe (PID: 6292)
Drops the executable file immediately after the start
- PK SEARCH PRIVATE.exe (PID: 6292)
Process drops python dynamic module
- PK SEARCH PRIVATE.exe (PID: 6292)
The process drops C-runtime libraries
- PK SEARCH PRIVATE.exe (PID: 6292)
Application launched itself
- PK SEARCH PRIVATE.exe (PID: 6292)
Loads Python modules
- PK SEARCH PRIVATE.exe (PID: 7016)
Executable content was dropped or overwritten
- PK SEARCH PRIVATE.exe (PID: 6292)
Starts CMD.EXE for commands execution
- PK SEARCH PRIVATE.exe (PID: 7016)
Connects to unusual port
- PK SEARCH PRIVATE.exe (PID: 7016)
INFO
Reads the computer name
- PK SEARCH PRIVATE.exe (PID: 6292)
- TextInputHost.exe (PID: 6552)
- PK SEARCH PRIVATE.exe (PID: 7016)
Checks supported languages
- PK SEARCH PRIVATE.exe (PID: 6292)
- TextInputHost.exe (PID: 6552)
- PK SEARCH PRIVATE.exe (PID: 7016)
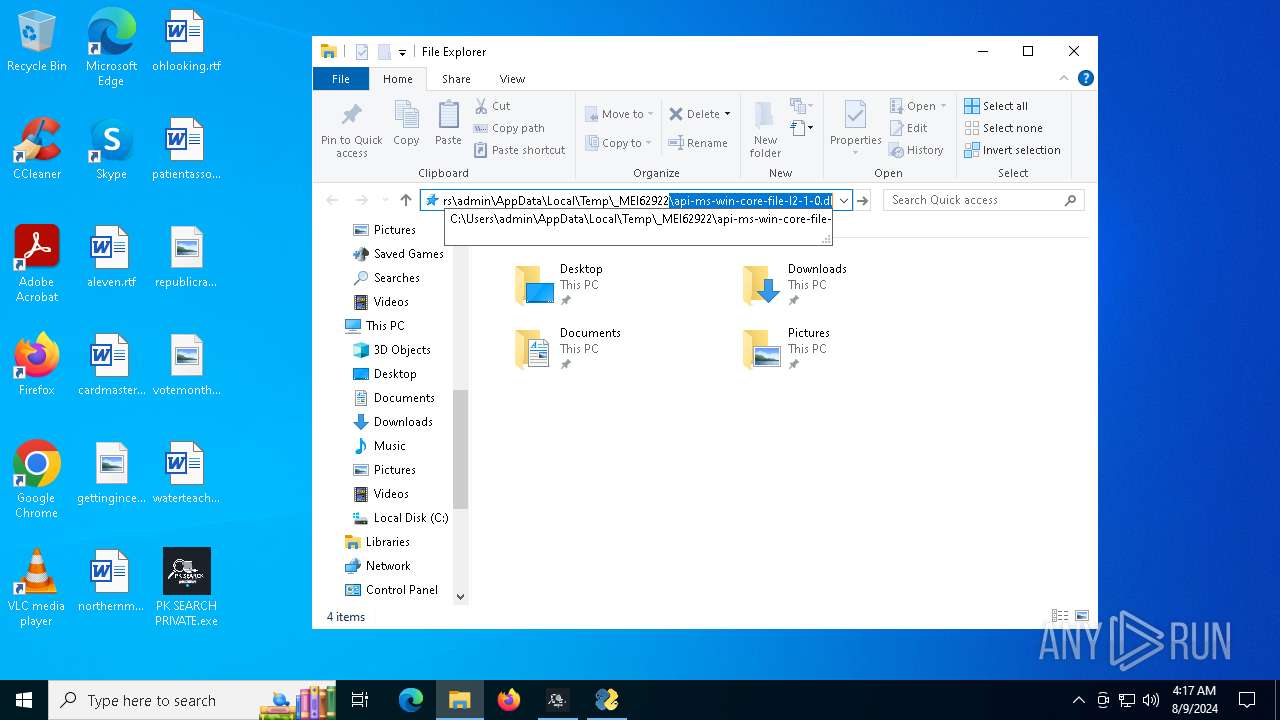
PyInstaller has been detected (YARA)
- PK SEARCH PRIVATE.exe (PID: 6292)
- PK SEARCH PRIVATE.exe (PID: 7016)
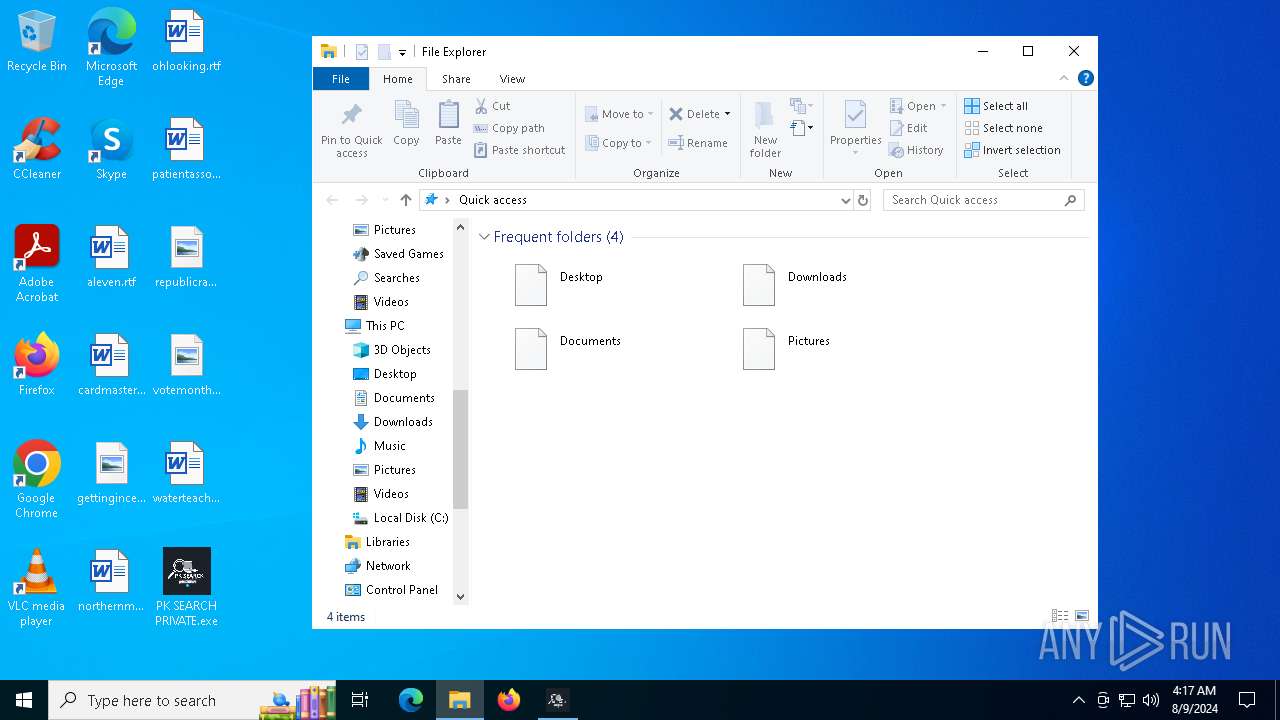
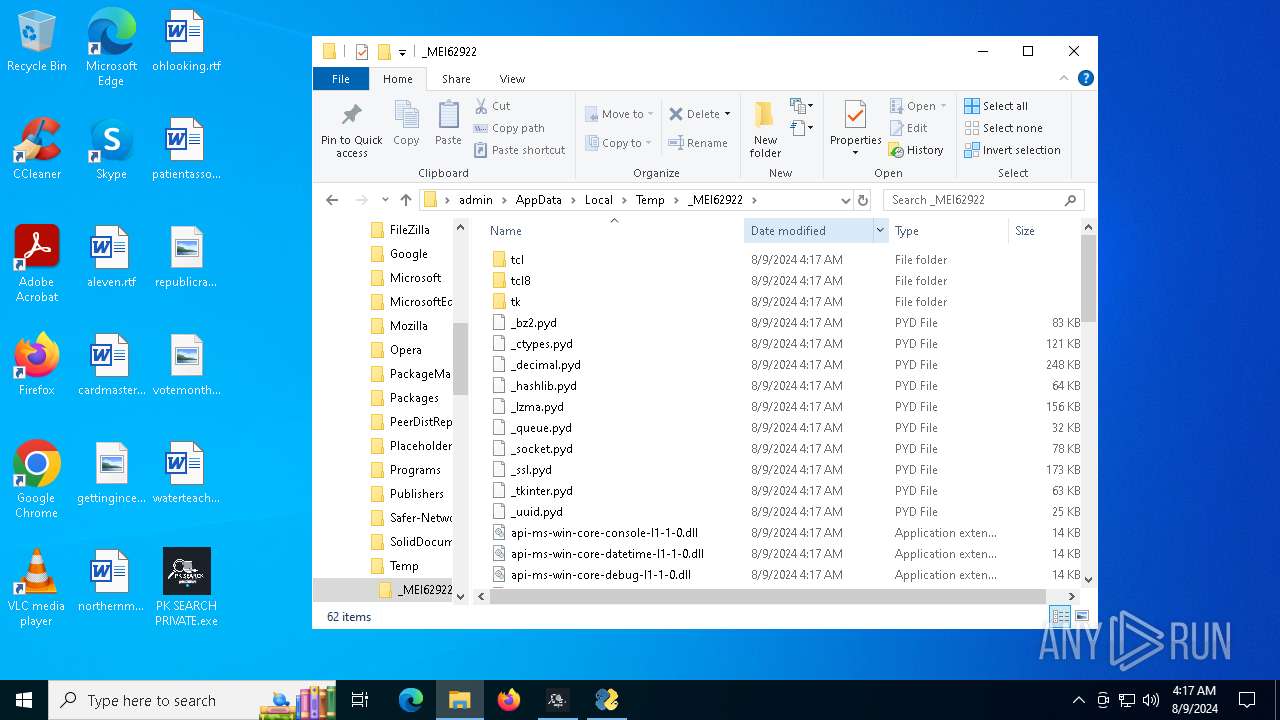
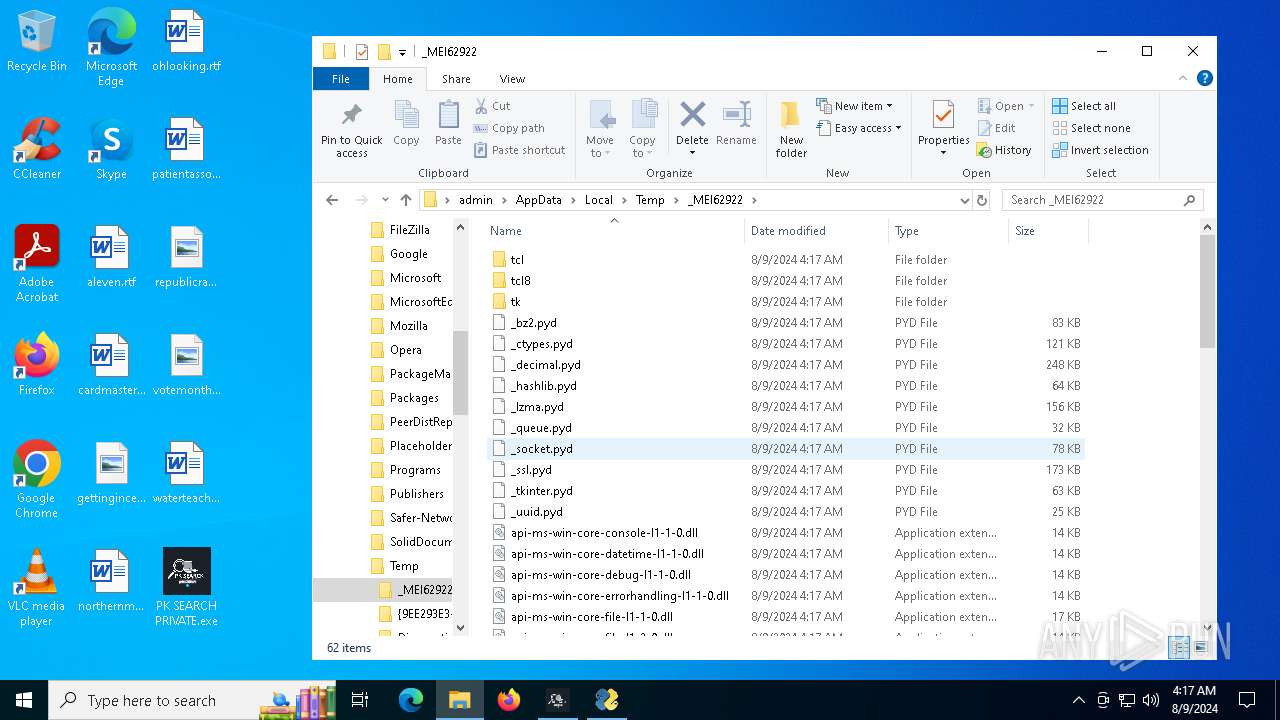
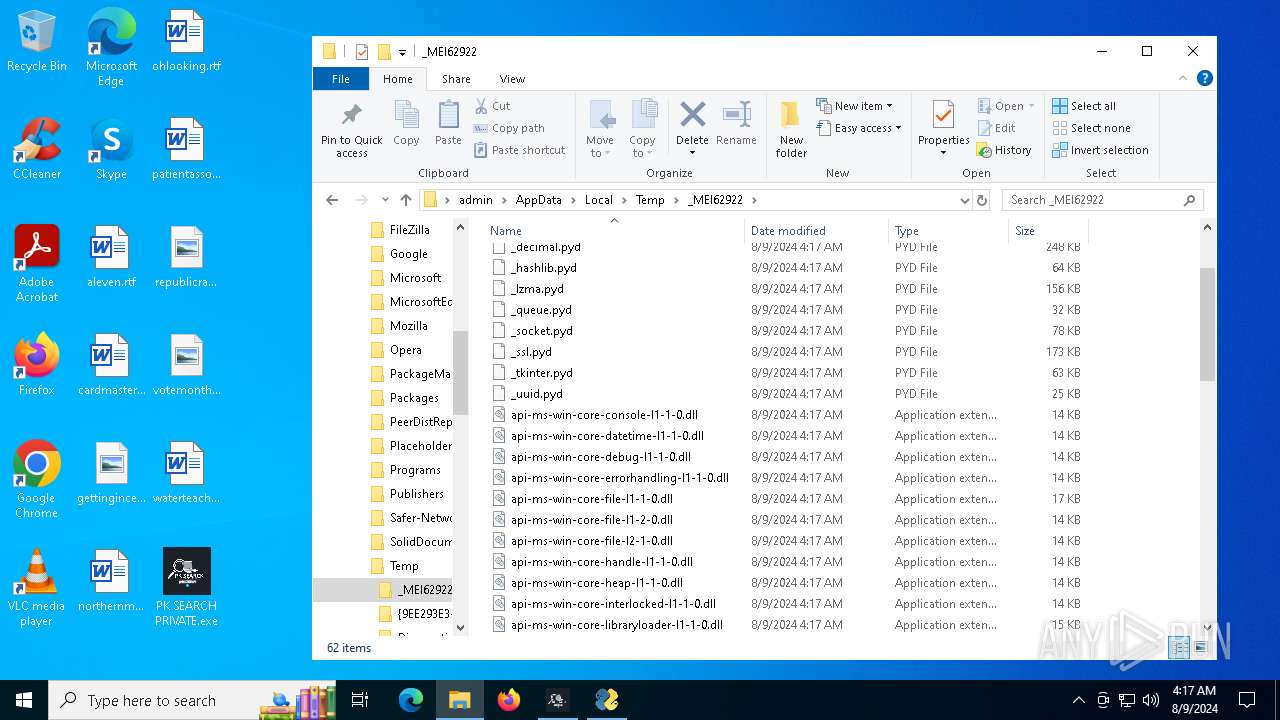
Create files in a temporary directory
- PK SEARCH PRIVATE.exe (PID: 6292)
Checks operating system version
- PK SEARCH PRIVATE.exe (PID: 7016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:09:29 13:37:11+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.35 |
| CodeSize: | 171520 |
| InitializedDataSize: | 364032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb750 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
135
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5880 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | PK SEARCH PRIVATE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5900 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6292 | "C:\Users\admin\Desktop\PK SEARCH PRIVATE.exe" | C:\Users\admin\Desktop\PK SEARCH PRIVATE.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PK SEARCH PRIVATE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6552 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 7016 | "C:\Users\admin\Desktop\PK SEARCH PRIVATE.exe" | C:\Users\admin\Desktop\PK SEARCH PRIVATE.exe | PK SEARCH PRIVATE.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
1 950
Read events
1 950
Write events
0
Delete events
0
Modification events
Executable files
58
Suspicious files
1
Text files
920
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6292 | PK SEARCH PRIVATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI62922\_bz2.pyd | executable | |
MD5:4438AFFAAA0CA1DF5B9B1CDAA0115EC1 | SHA256:EC91E2B4BACA31B992D016B84B70F110CE2B1B2DFD54F5E5BEF6270ED7D13B85 | |||
| 6292 | PK SEARCH PRIVATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI62922\_hashlib.pyd | executable | |
MD5:1524882AF71247ADECF5815A4E55366A | SHA256:6F7742DFDD371C39048D775F37DF3BC2D8D4316C9008E62347B337D64EBED327 | |||
| 6292 | PK SEARCH PRIVATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI62922\_ssl.pyd | executable | |
MD5:A0B40F1F8FC6656C5637EACACF7021F6 | SHA256:79D861F0670828DEE06C2E3523E2F9A2A90D6C6996BDE38201425AA4003119F1 | |||
| 6292 | PK SEARCH PRIVATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI62922\_queue.pyd | executable | |
MD5:8BBED19359892F8C95C802C6AD7598E9 | SHA256:4E5B7C653C1B3DC3FD7519E4F39CC8A2FB2746E0ECDC4E433FE6029F5F4D9065 | |||
| 6292 | PK SEARCH PRIVATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI62922\_decimal.pyd | executable | |
MD5:BE315973AFF9BDEB06629CD90E1A901F | SHA256:0F9C6CC463611A9B2C692382FE1CDD7A52FEA4733FFAF645D433F716F8BBD725 | |||
| 6292 | PK SEARCH PRIVATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI62922\_uuid.pyd | executable | |
MD5:4FAA479423C54D5BE2A103B46ECB4D04 | SHA256:C2AD3C1B4333BC388B6A22049C89008505C434B1B85BFF0823B19EF0CF48065A | |||
| 6292 | PK SEARCH PRIVATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI62922\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:84398CB4FA206939E4E0FBC186954776 | SHA256:853C4D3DA01987406FE31553373E21F84EDBE617E47AB4930F7EADB67F761462 | |||
| 6292 | PK SEARCH PRIVATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI62922\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:C6664A7796AEAEF78D34D70E1BB58242 | SHA256:5DE66EB61D87E0CB7CB98CE23EFD716B33B4EEEE6EC6643EEEBA8E6620D0EF10 | |||
| 6292 | PK SEARCH PRIVATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI62922\_tkinter.pyd | executable | |
MD5:89F47CD630F7DFA63268FBC52D04F9E9 | SHA256:8E4CAB61B3838F9545B5D1E0B287F18C22D360B8E6A8DACA4178CC69DF78F83D | |||
| 6292 | PK SEARCH PRIVATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI62922\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:D652FF68C59F974201BBAD6EB0353AE4 | SHA256:849A7C073A986C470AC0A7C4AD25C243C276C65CEE010830B3B061599F7FBF9C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
46
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3900 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3900 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6648 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6692 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4708 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4084 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4708 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5336 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3900 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |