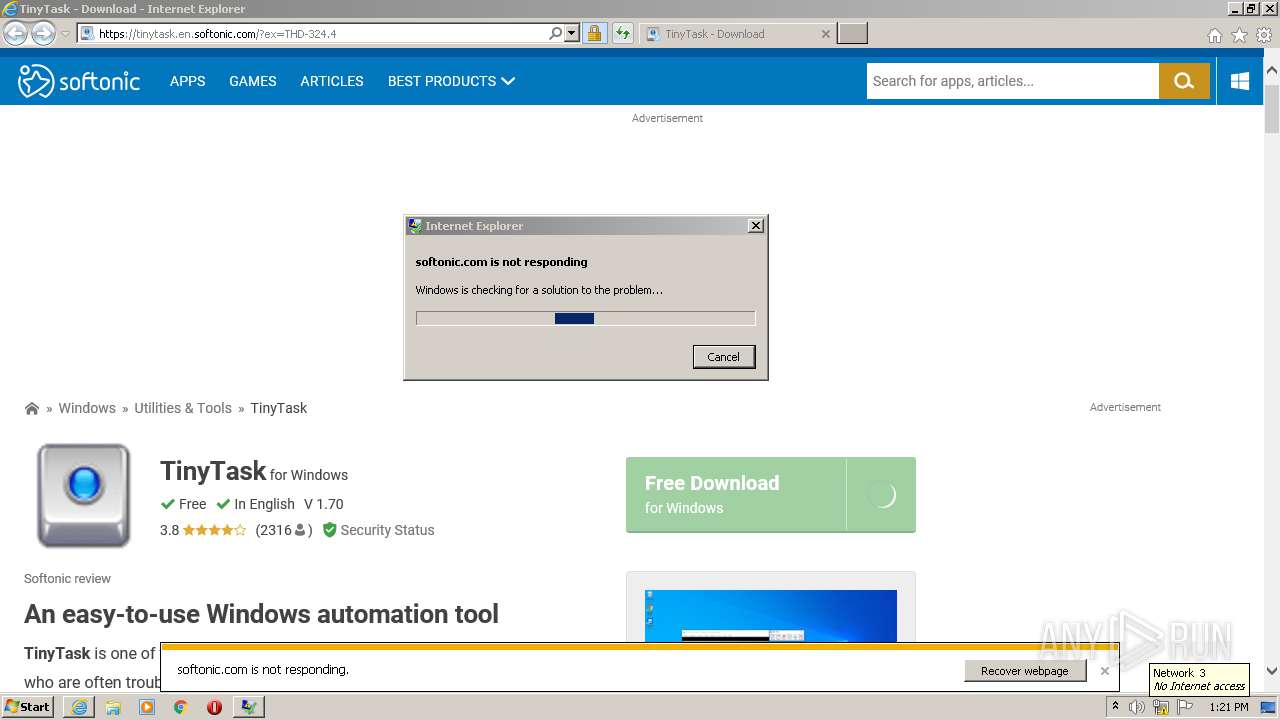
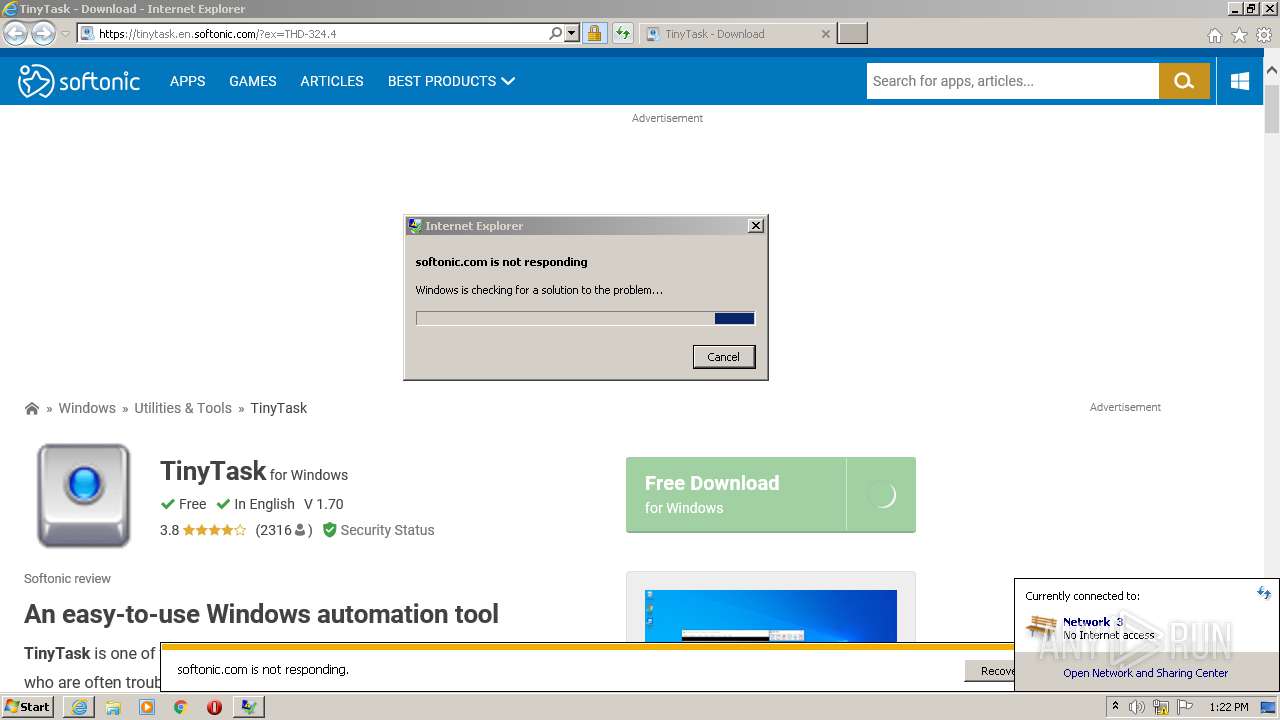
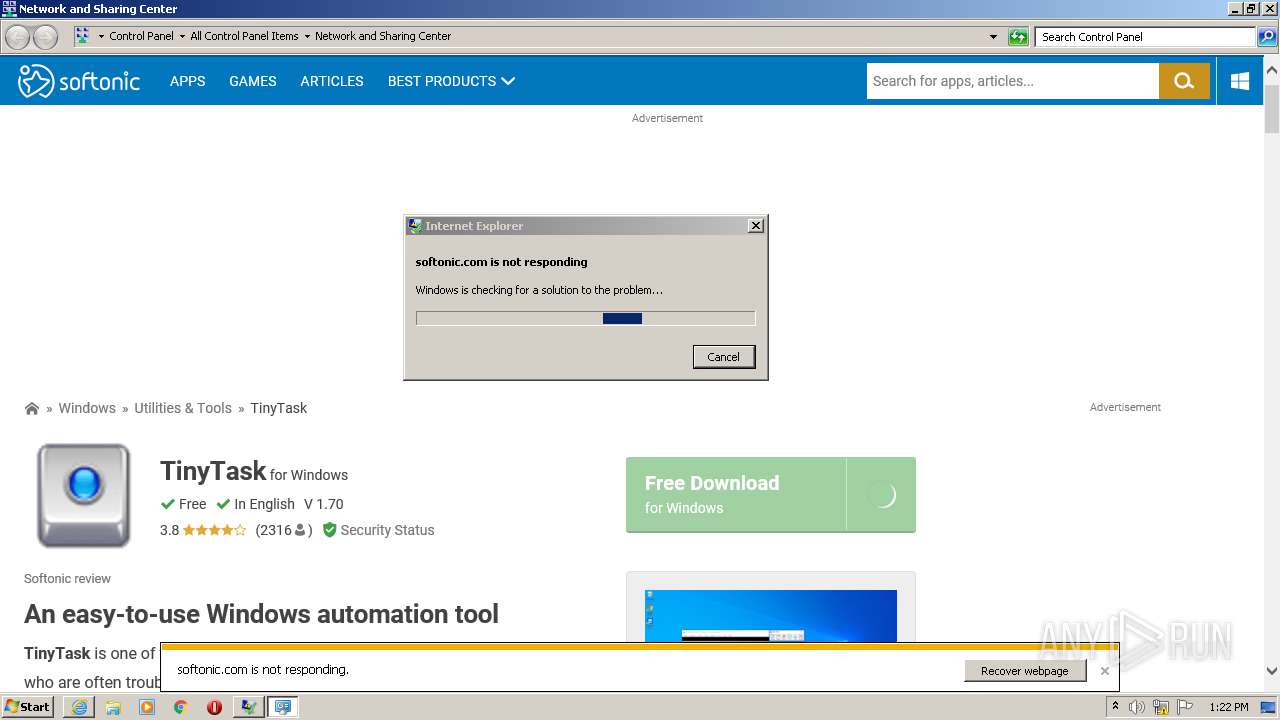
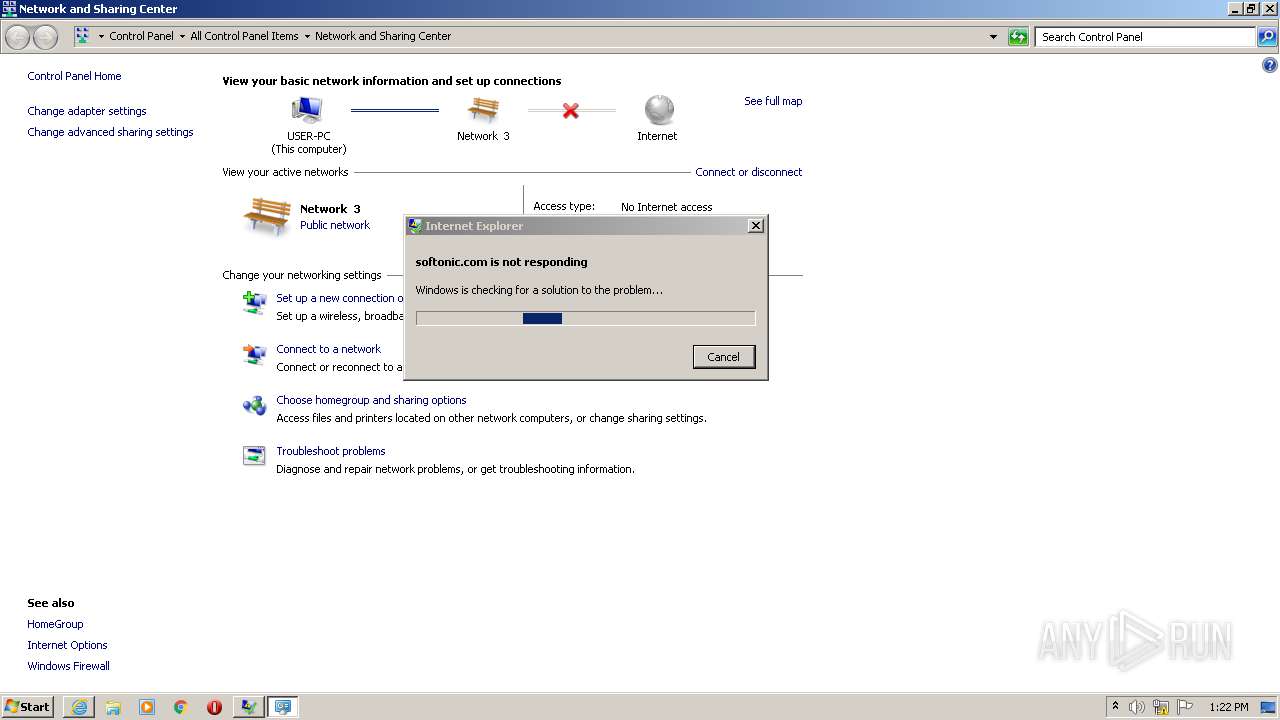
| URL: | https://tinytask.en.softonic.com |
| Full analysis: | https://app.any.run/tasks/9e6df656-f69b-4383-a343-feaf858f0c49 |
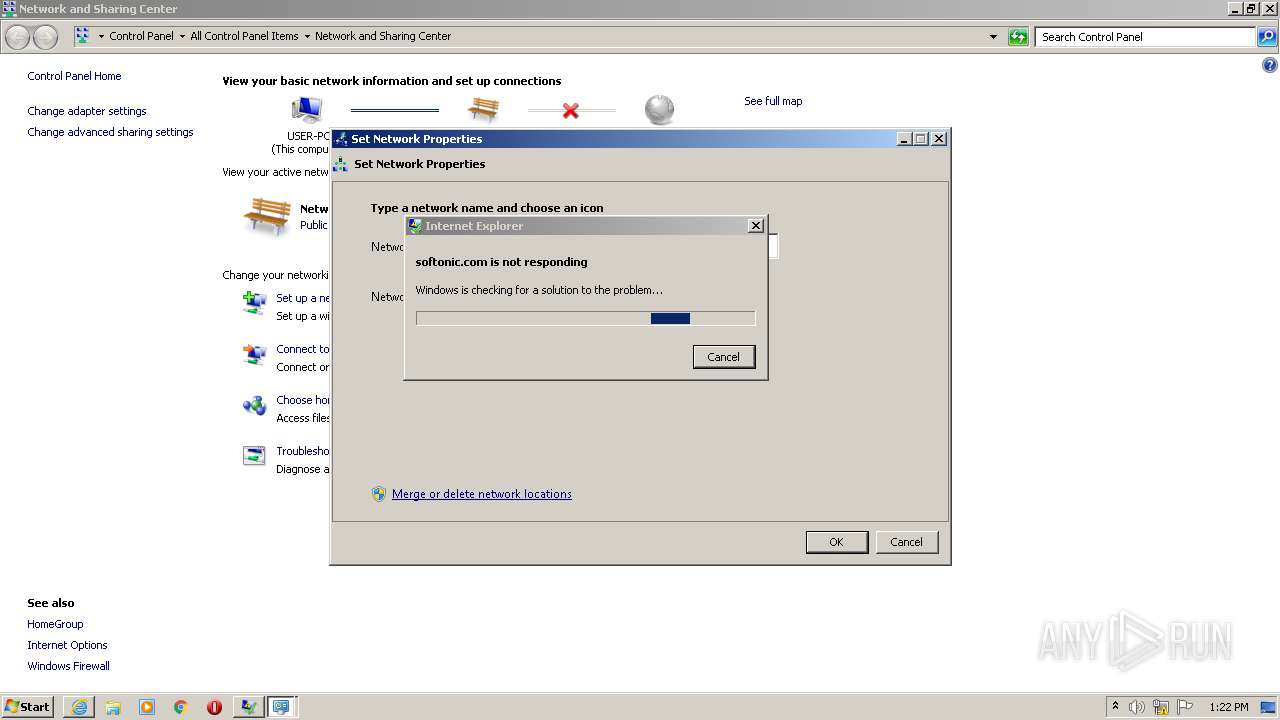
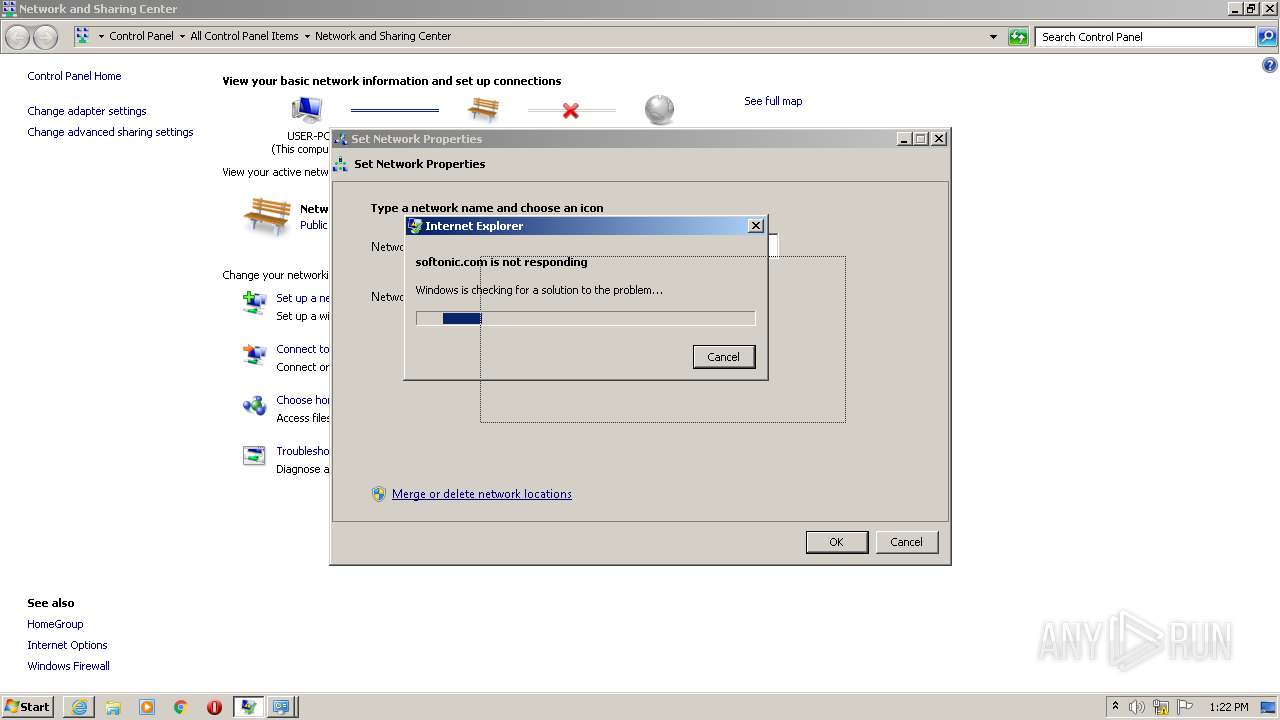
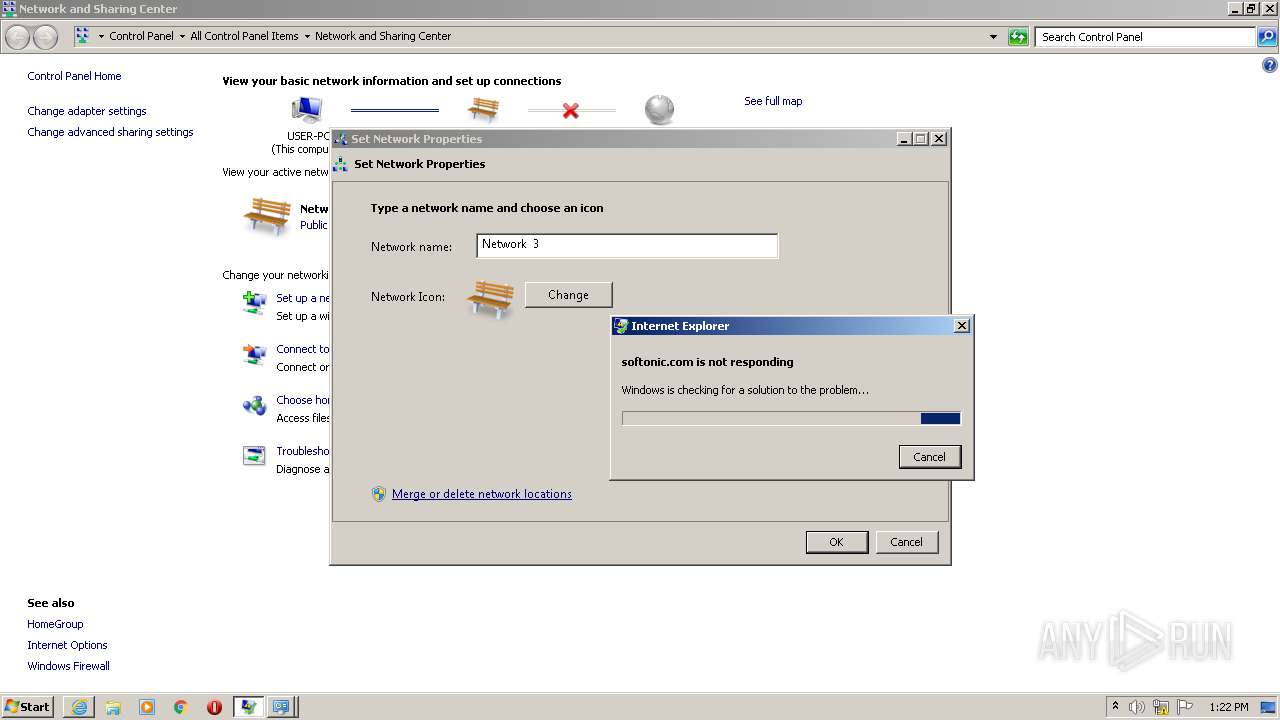
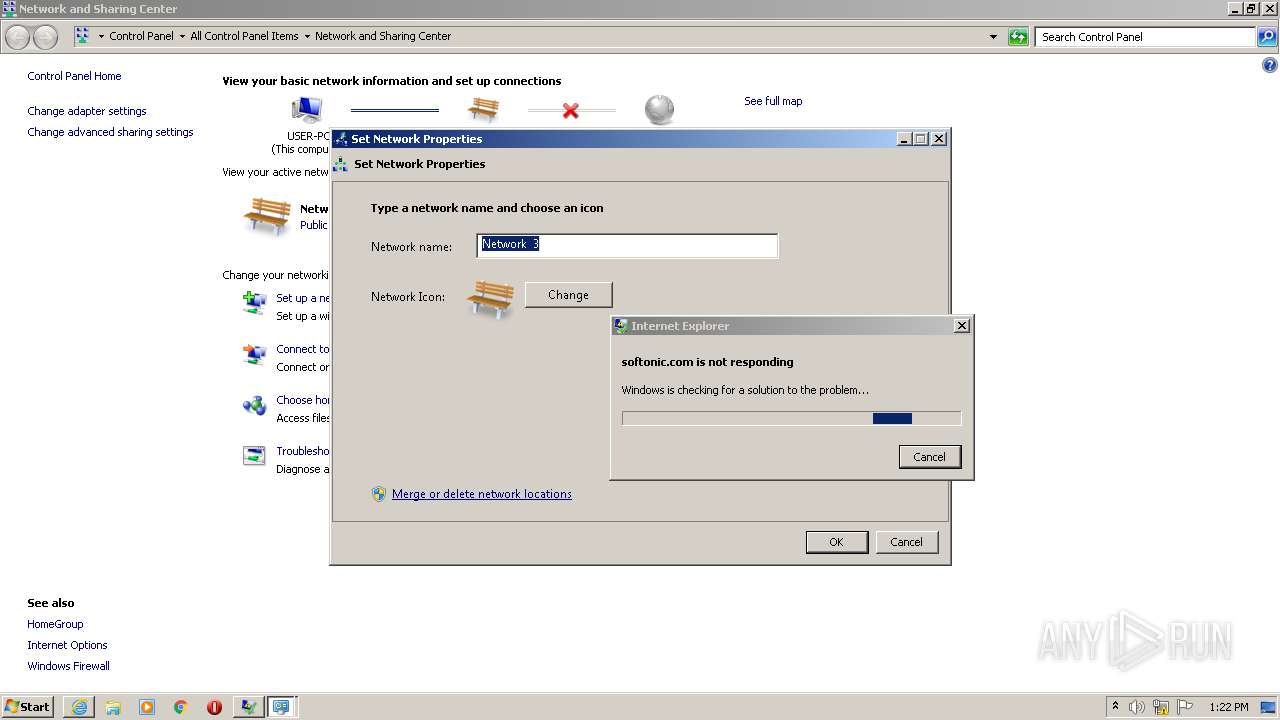
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2021, 13:20:04 |
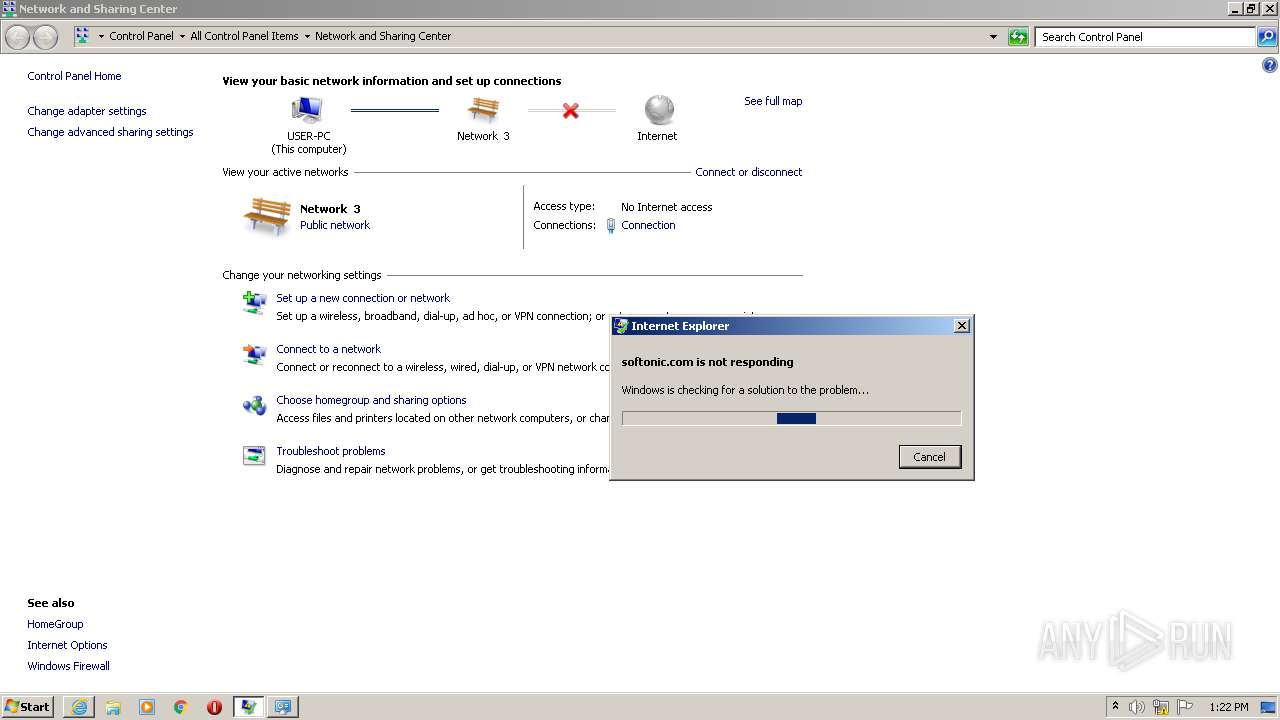
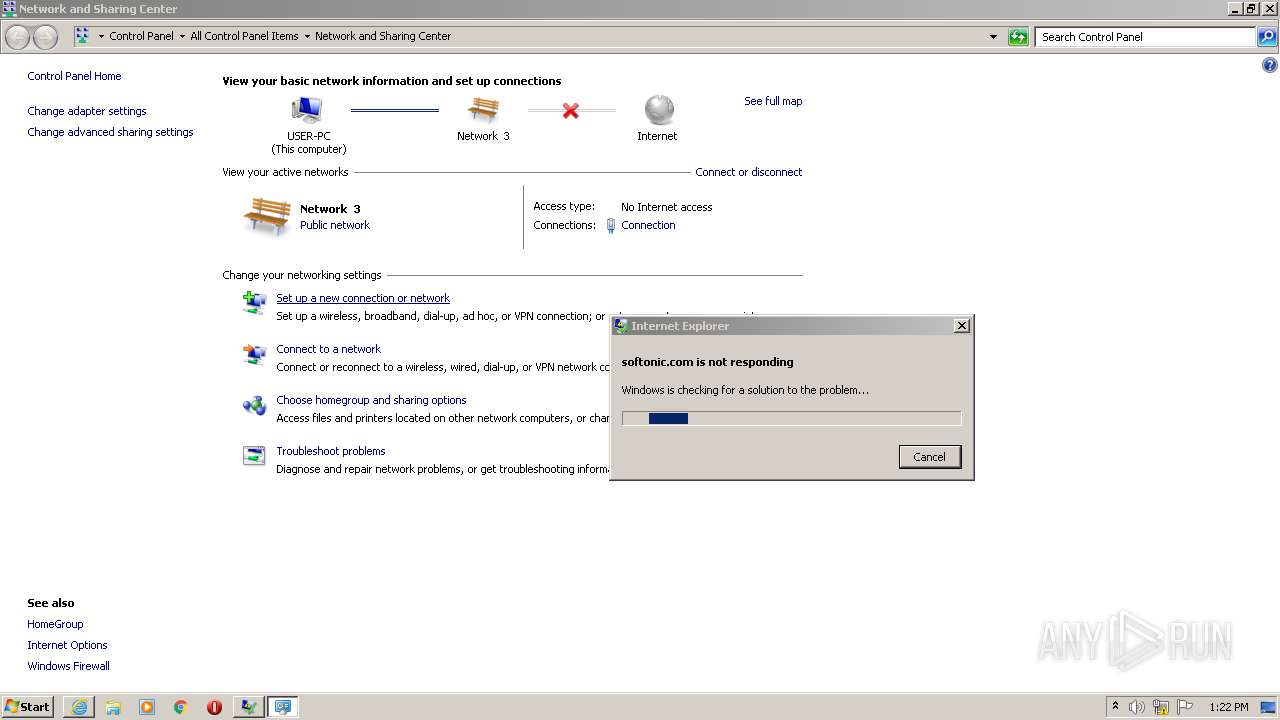
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4BD5B5DD5C5F80D50E3AC6AC14DF33CA |
| SHA1: | 8158C915EEA2B36789AD24698C38C0FBDEDC4390 |
| SHA256: | 96147B549D6F6884C314DD67A6E67874D123054CB0213A28A02E3DB9551F00D9 |
| SSDEEP: | 3:N8EFJDHLGKI:2EFJLGKI |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes settings of System certificates
- iexplore.exe (PID: 2576)
Changes internet zones settings
- iexplore.exe (PID: 2576)
Reads settings of System Certificates
- iexplore.exe (PID: 1244)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 2576)
Creates files in the user directory
- iexplore.exe (PID: 2576)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 1244)
Reads internet explorer settings
- iexplore.exe (PID: 1244)
- iexplore.exe (PID: 2748)
Application launched itself
- iexplore.exe (PID: 2576)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2576)
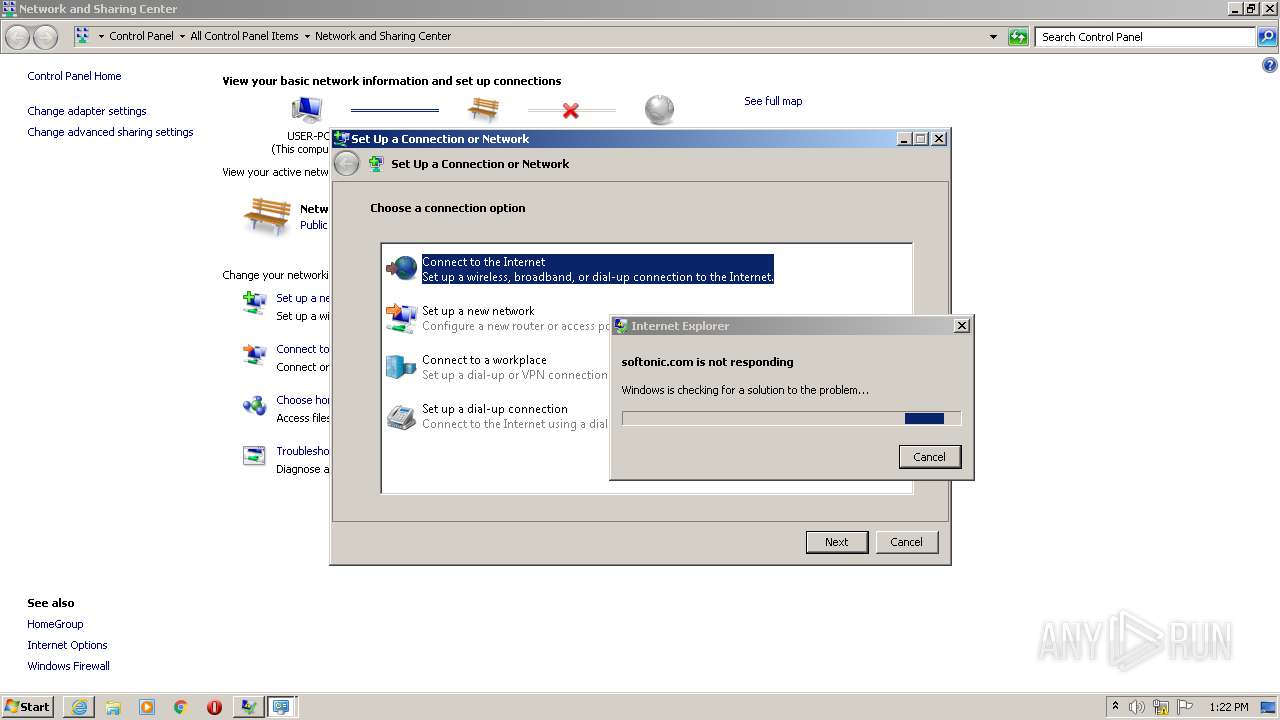
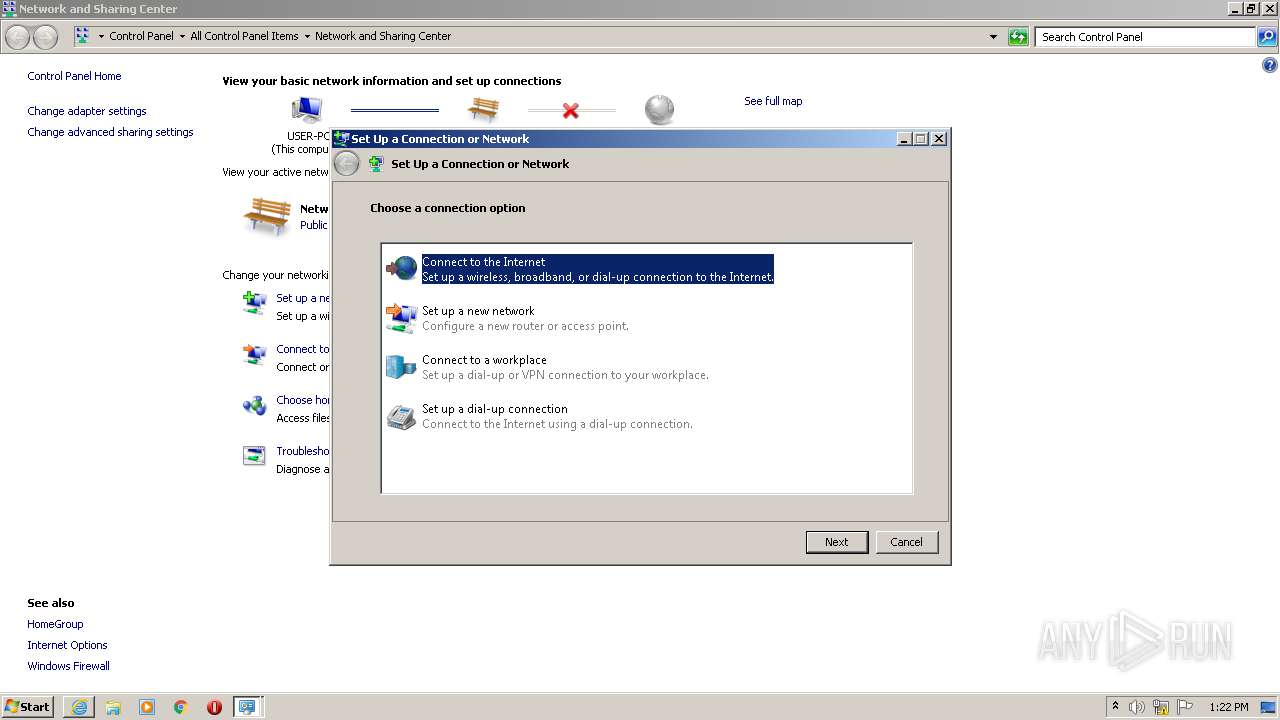
Manual execution by user
- rundll32.exe (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1244 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2576 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 3489660927 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
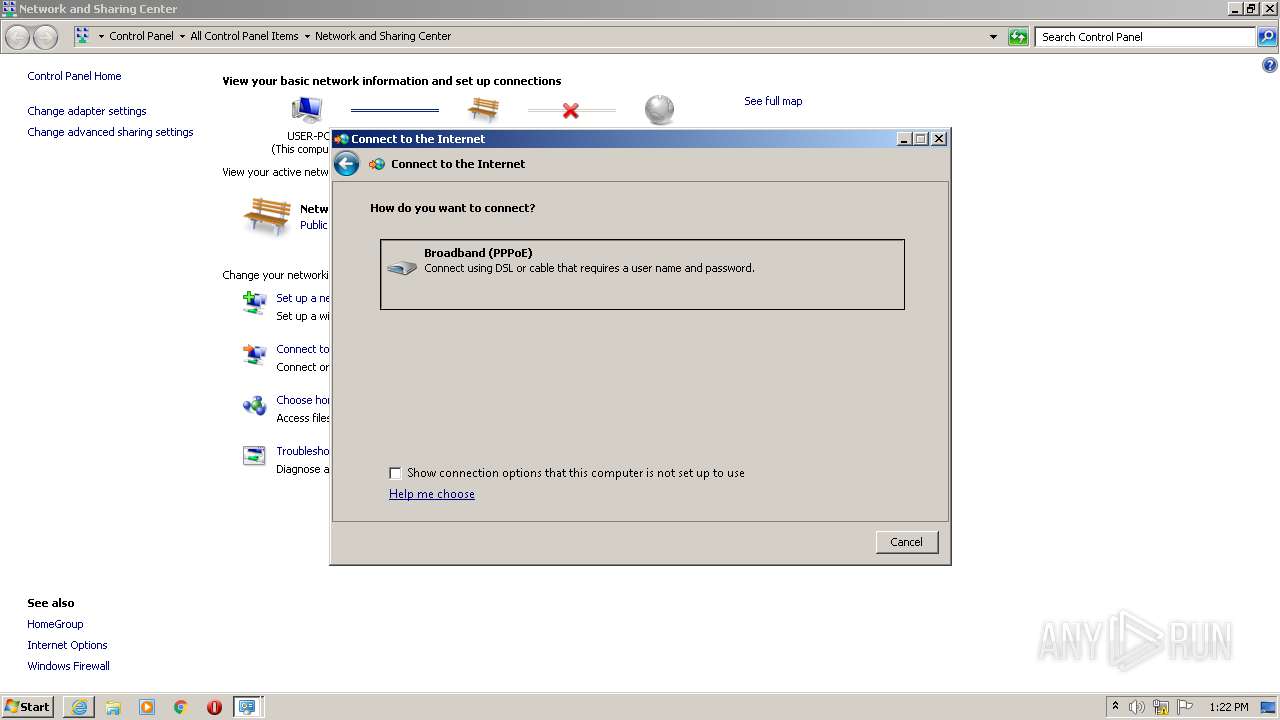
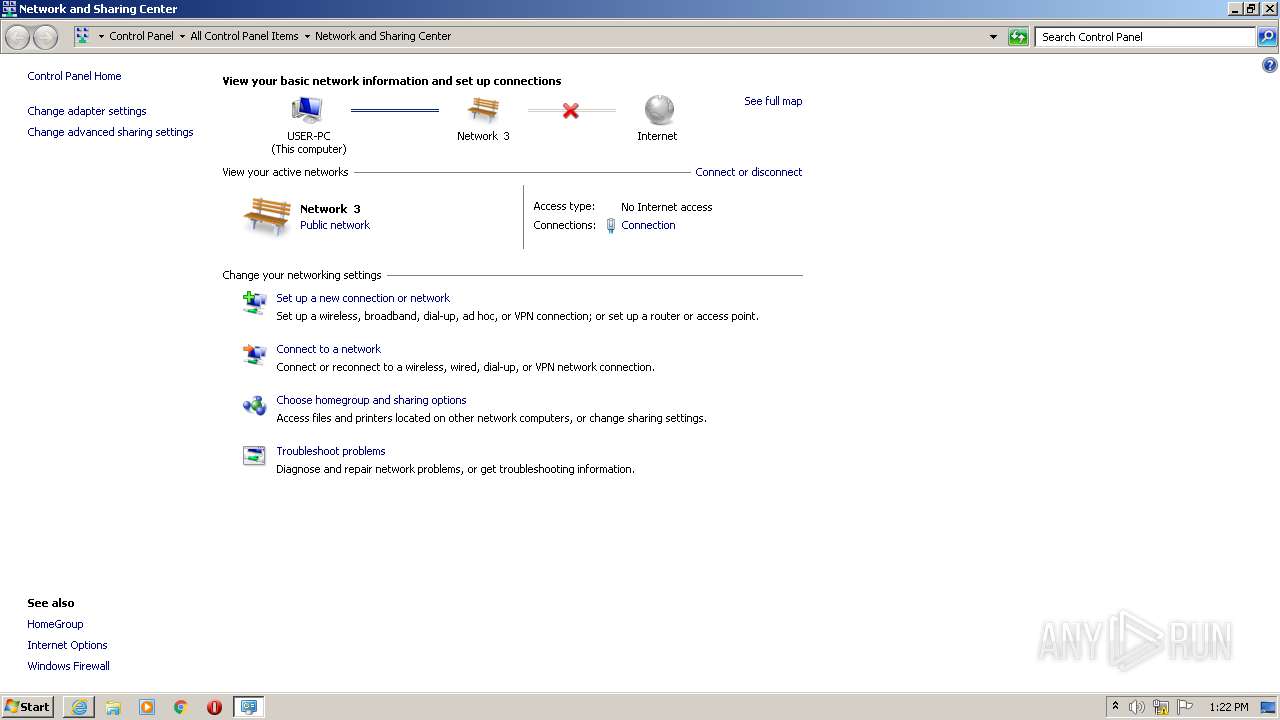
| 2140 | "C:\Windows\system32\rundll32.exe" pnidui.dll,NwCategoryWiz {52c5c750-d462-4323-8c07-09cf65c667bb} 1 | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Internet Explorer\iexplore.exe" https://tinytask.en.softonic.com | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2576 CREDAT:3216661 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 215
Read events
983
Write events
228
Delete events
4
Modification events
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 68377584 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30875221 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
166
Text files
136
Unknown types
81
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1244 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab3A8B.tmp | — | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar3A8C.tmp | — | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\NYGFR0FN.txt | — | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50960638BC28B25C3B86386594FA9228 | der | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\50960638BC28B25C3B86386594FA9228 | binary | |
MD5:— | SHA256:— | |||
| 1244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
82
TCP/UDP connections
156
DNS requests
63
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1244 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1244 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1244 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
1244 | iexplore.exe | GET | 200 | 2.16.186.10:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
1244 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
1244 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEBm1t35JjvGrLGsJ38EQ5FI%3D | US | der | 471 b | whitelisted |
1244 | iexplore.exe | GET | 200 | 2.16.186.10:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
1244 | iexplore.exe | GET | 200 | 13.226.156.21:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
1244 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEBm1t35JjvGrLGsJ38EQ5FI%3D | US | der | 471 b | whitelisted |
1244 | iexplore.exe | GET | 200 | 2.16.186.10:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1244 | iexplore.exe | 13.226.156.74:80 | o.ss2.us | — | US | whitelisted |
1244 | iexplore.exe | 35.227.233.104:443 | tinytask.en.softonic.com | — | US | malicious |
1244 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1244 | iexplore.exe | 13.226.159.11:443 | sdk.privacy-center.org | — | US | whitelisted |
1244 | iexplore.exe | 142.250.185.162:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
1244 | iexplore.exe | 151.101.2.133:443 | sc.sftcdn.net | Fastly | US | malicious |
1244 | iexplore.exe | 172.217.23.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
1244 | iexplore.exe | 13.226.158.204:443 | c.amazon-adsystem.com | — | US | unknown |
1244 | iexplore.exe | 23.79.147.62:443 | images.sftcdn.net | Akamai International B.V. | US | unknown |
1244 | iexplore.exe | 204.79.197.200:443 | bat.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tinytask.en.softonic.com |
| malicious |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
sc.sftcdn.net |
| whitelisted |
sdk.privacy-center.org |
| shared |
securepubads.g.doubleclick.net |
| whitelisted |
spn-v1.revampcdn.com |
| suspicious |
www.googletagmanager.com |
| whitelisted |
c.amazon-adsystem.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
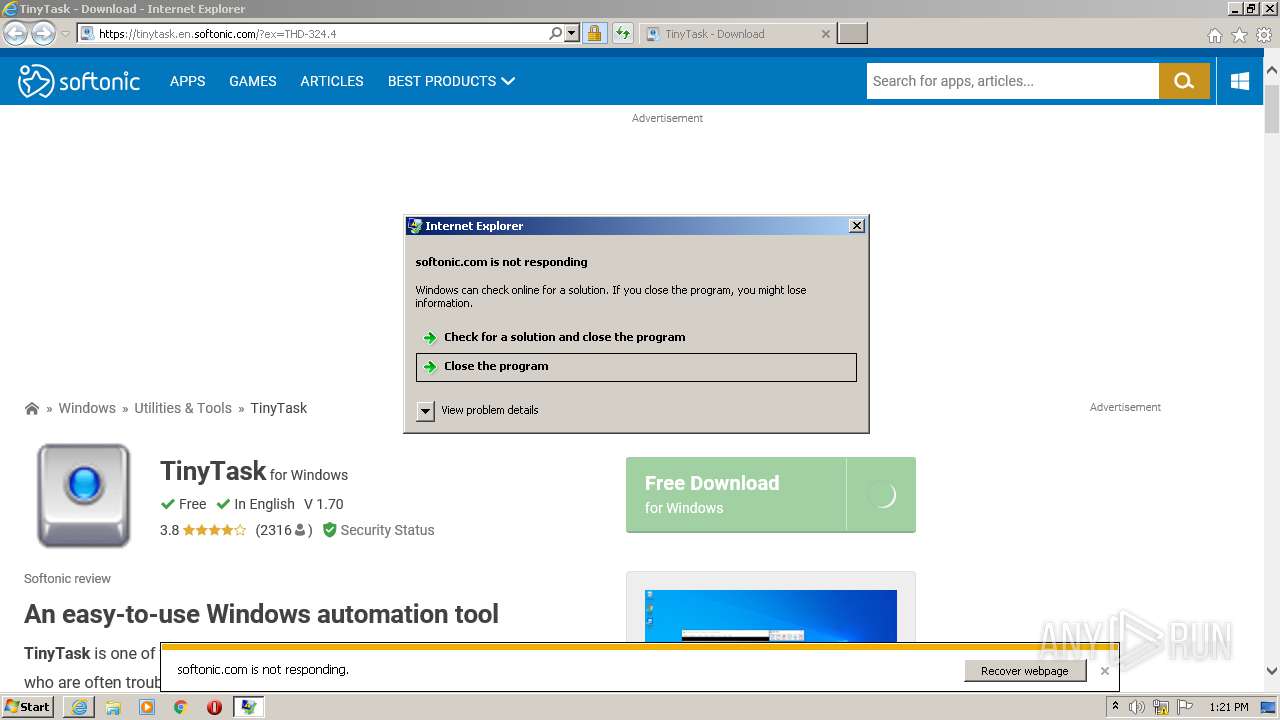
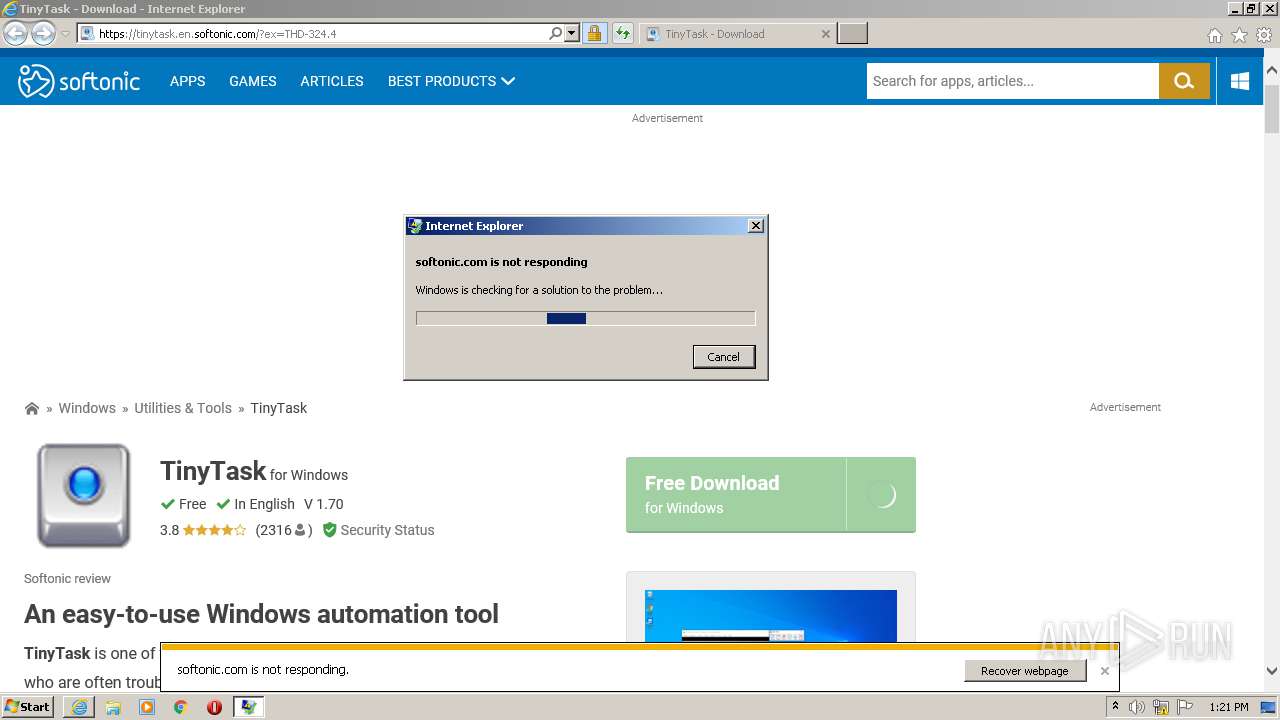
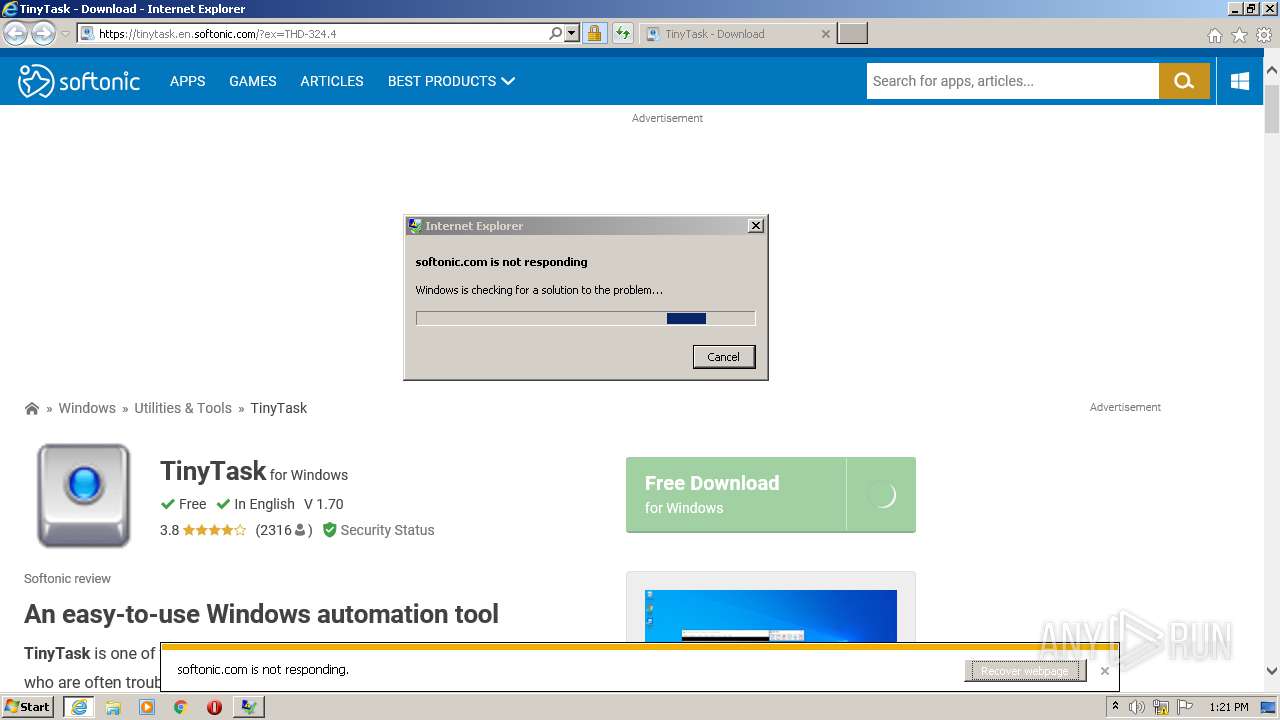
1716 | werfault.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |
1716 | werfault.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |