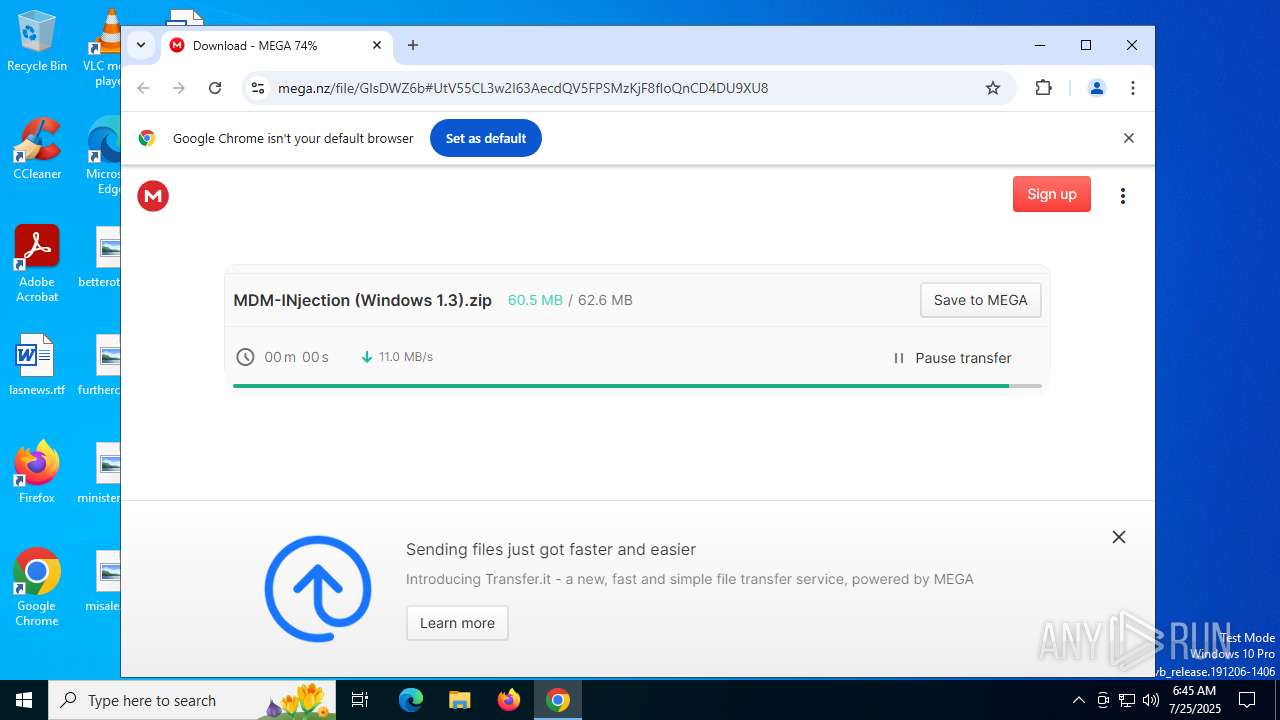
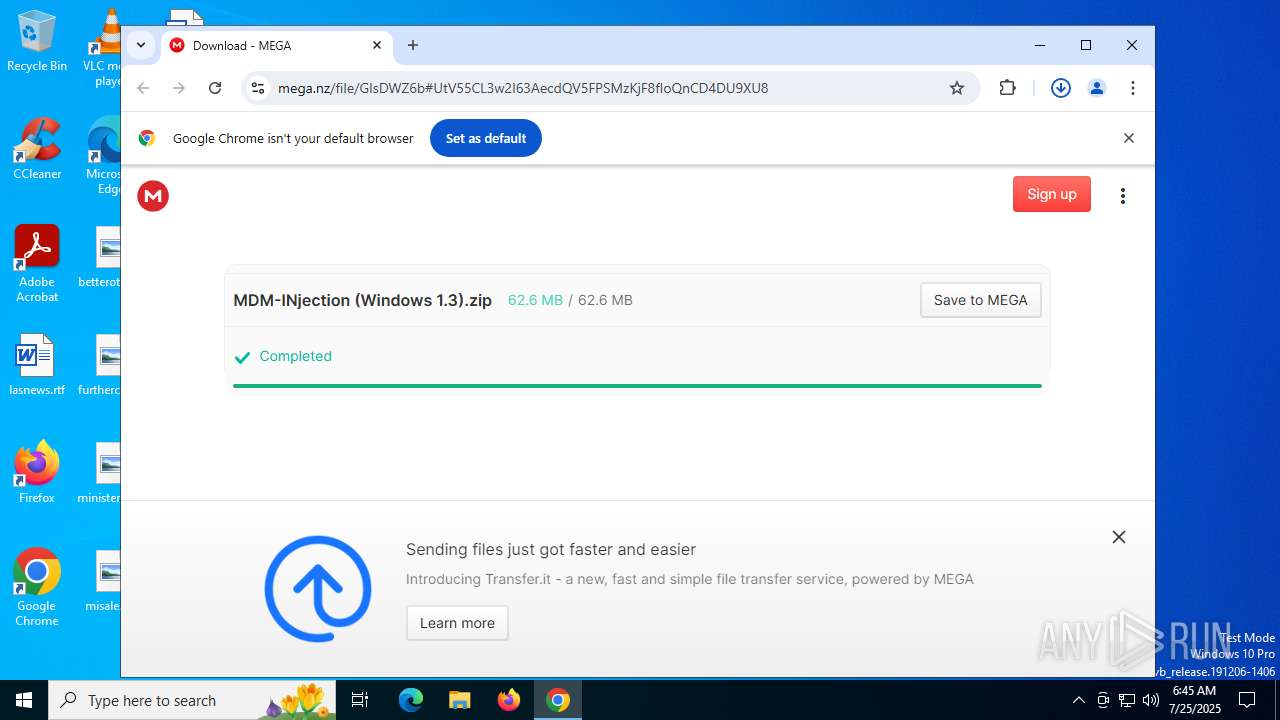
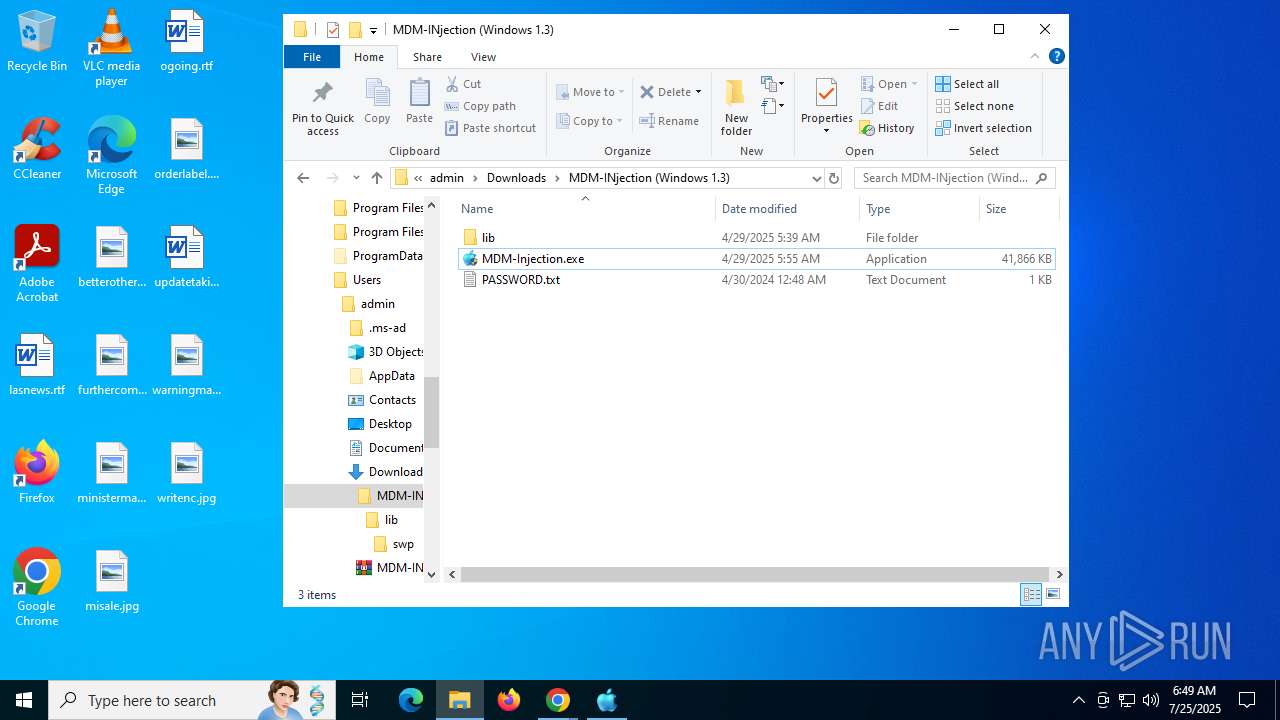
| URL: | https://mega.nz/file/GIsDWZ6b#UtV55CL3w2I63AecdQV5FPSMzKjF8fIoQnCD4DU9XU8 |
| Full analysis: | https://app.any.run/tasks/4d9fd712-c8bd-42e5-bc55-59e714160c3d |
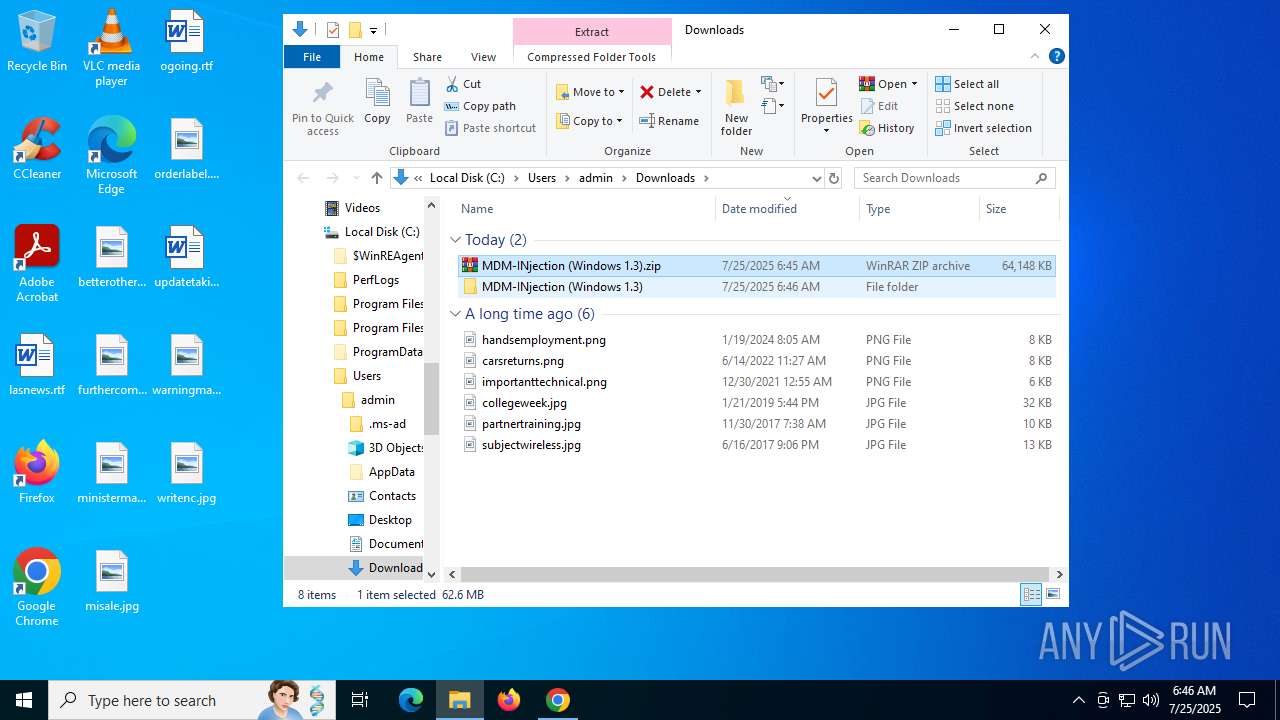
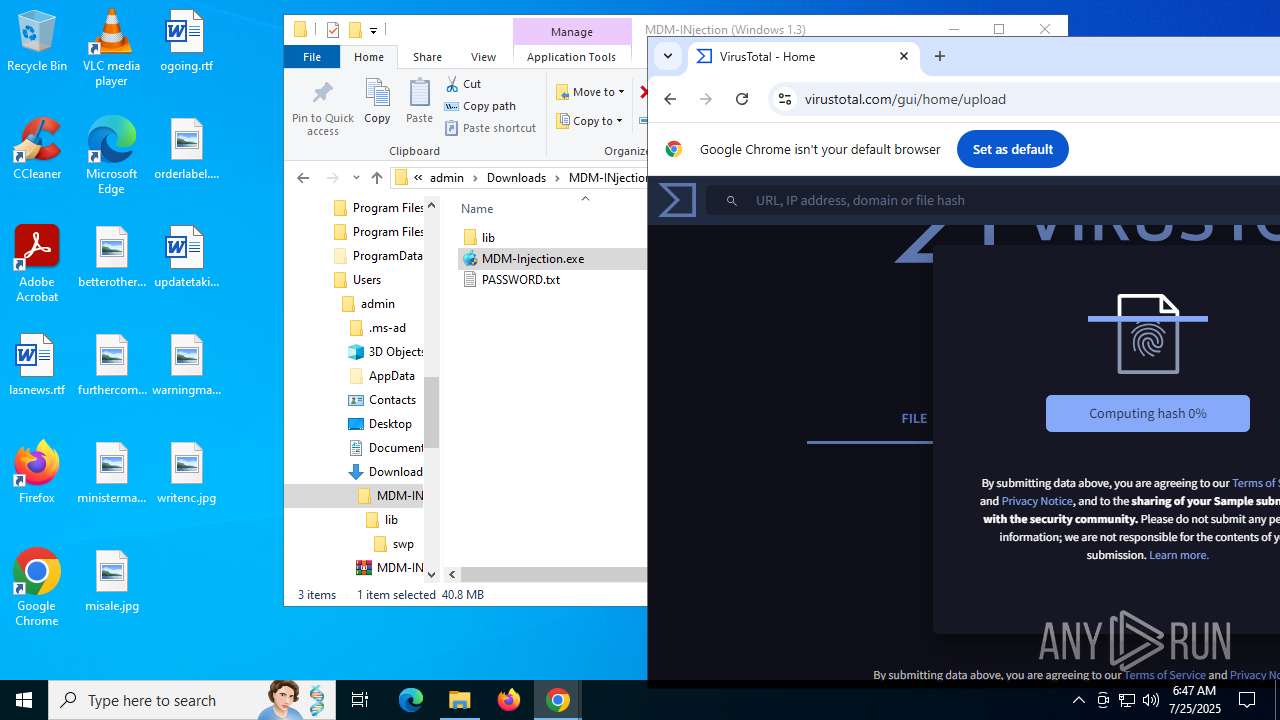
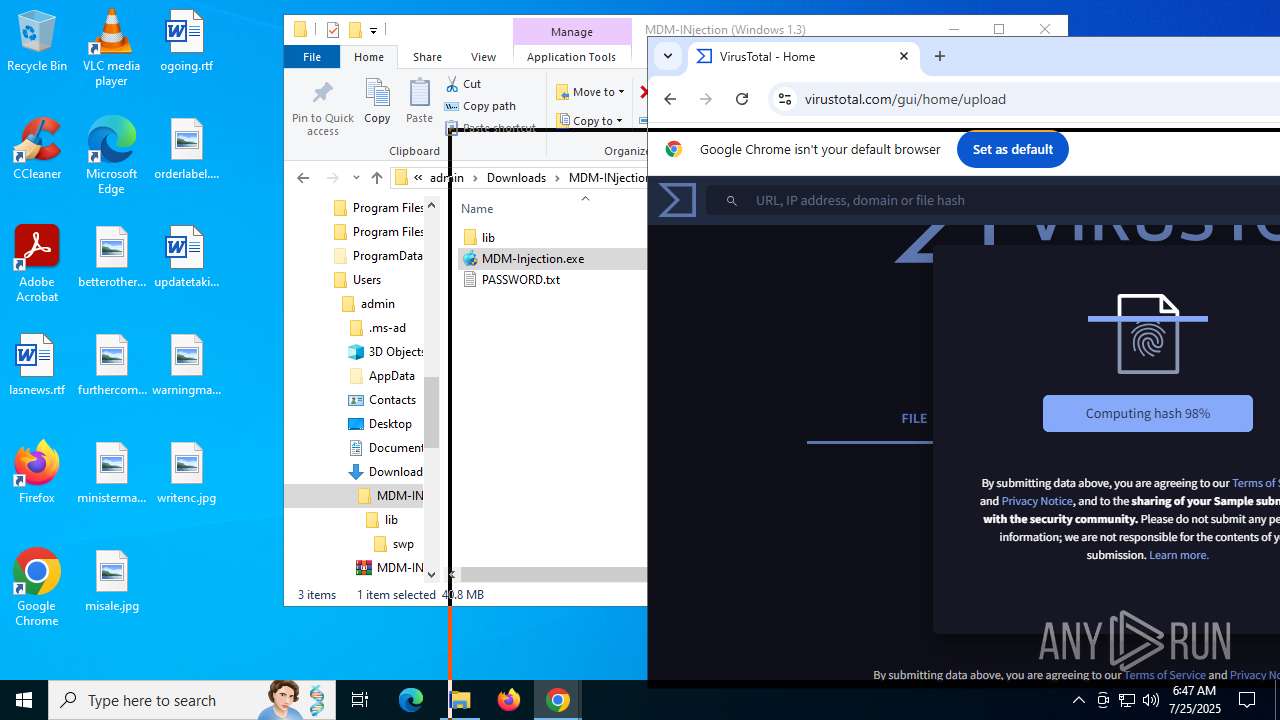
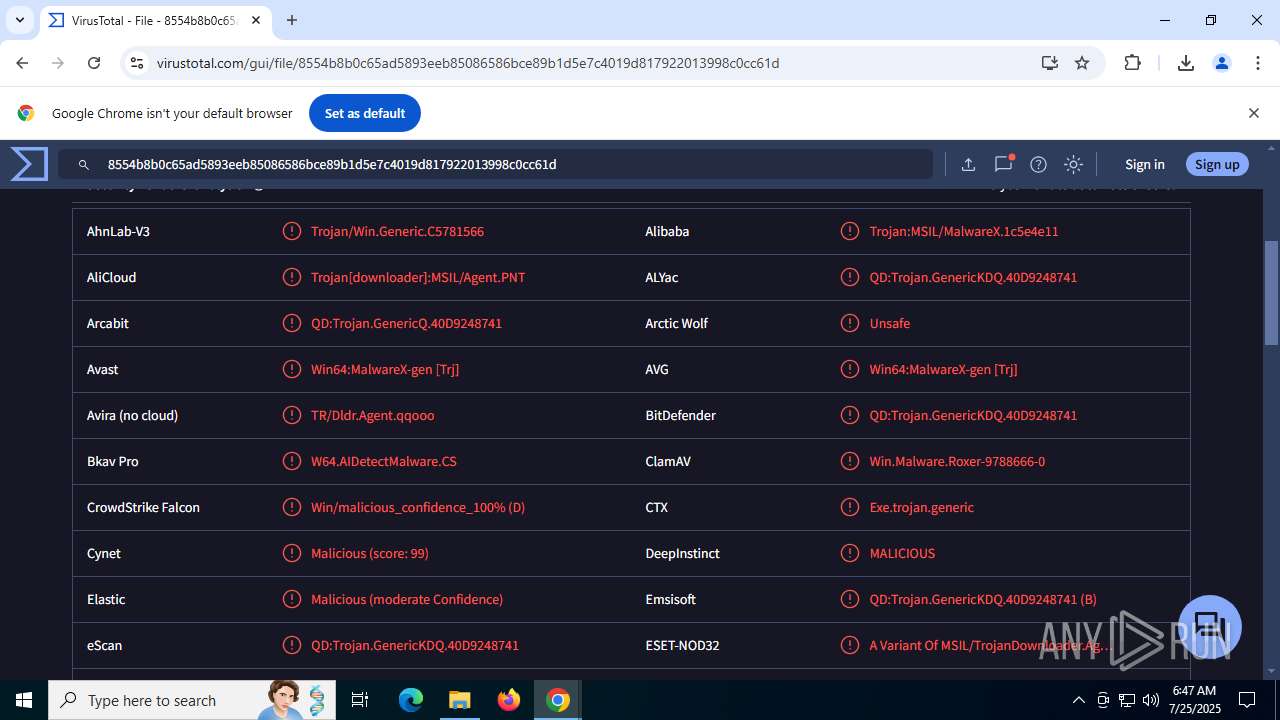
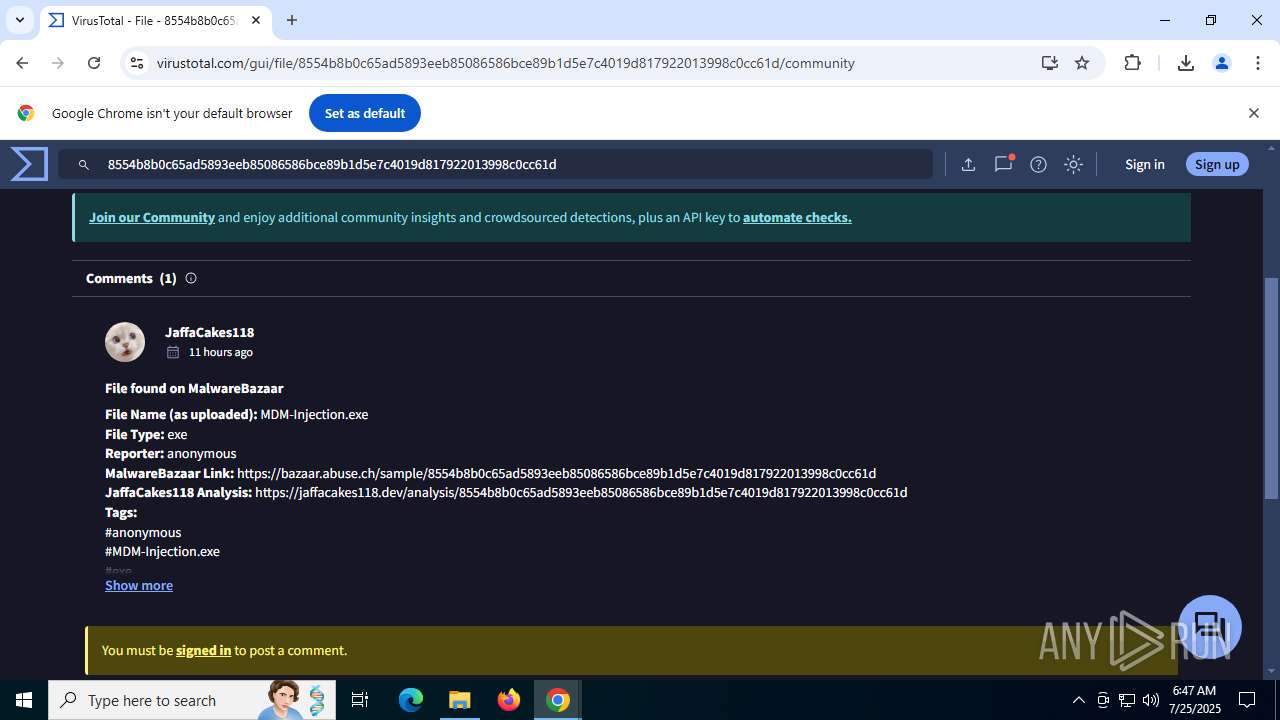
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2025, 06:45:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
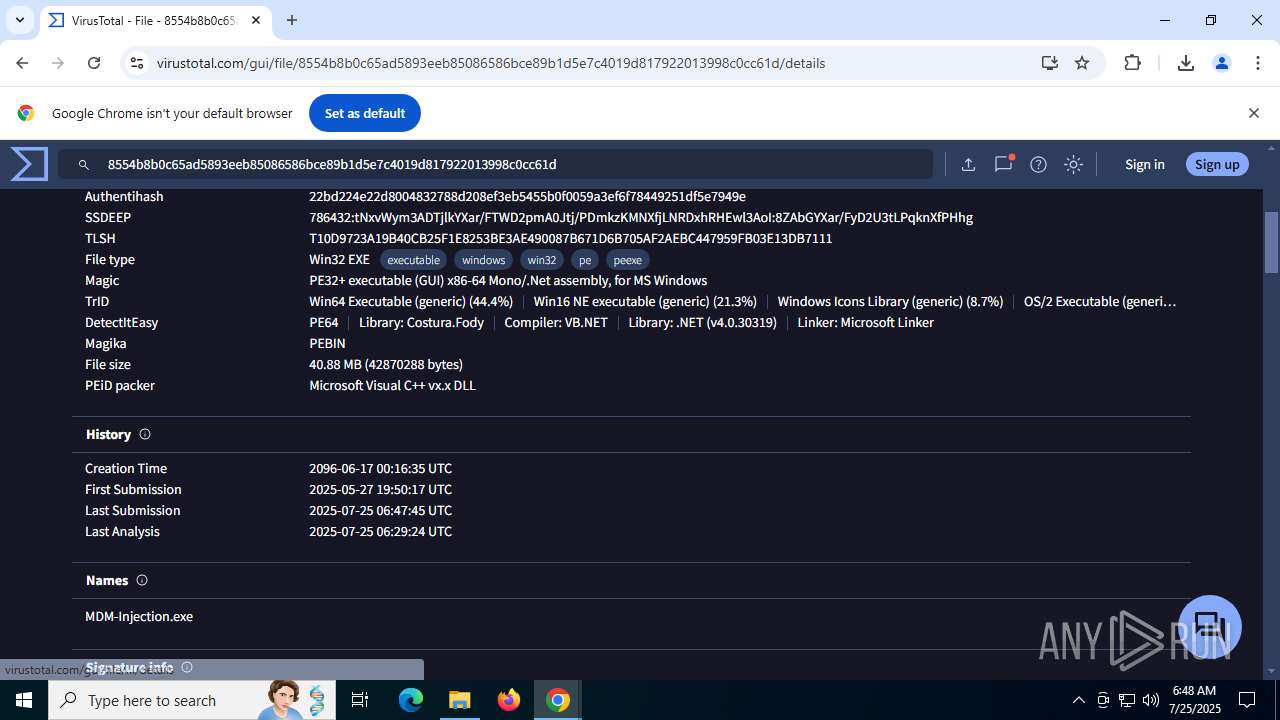
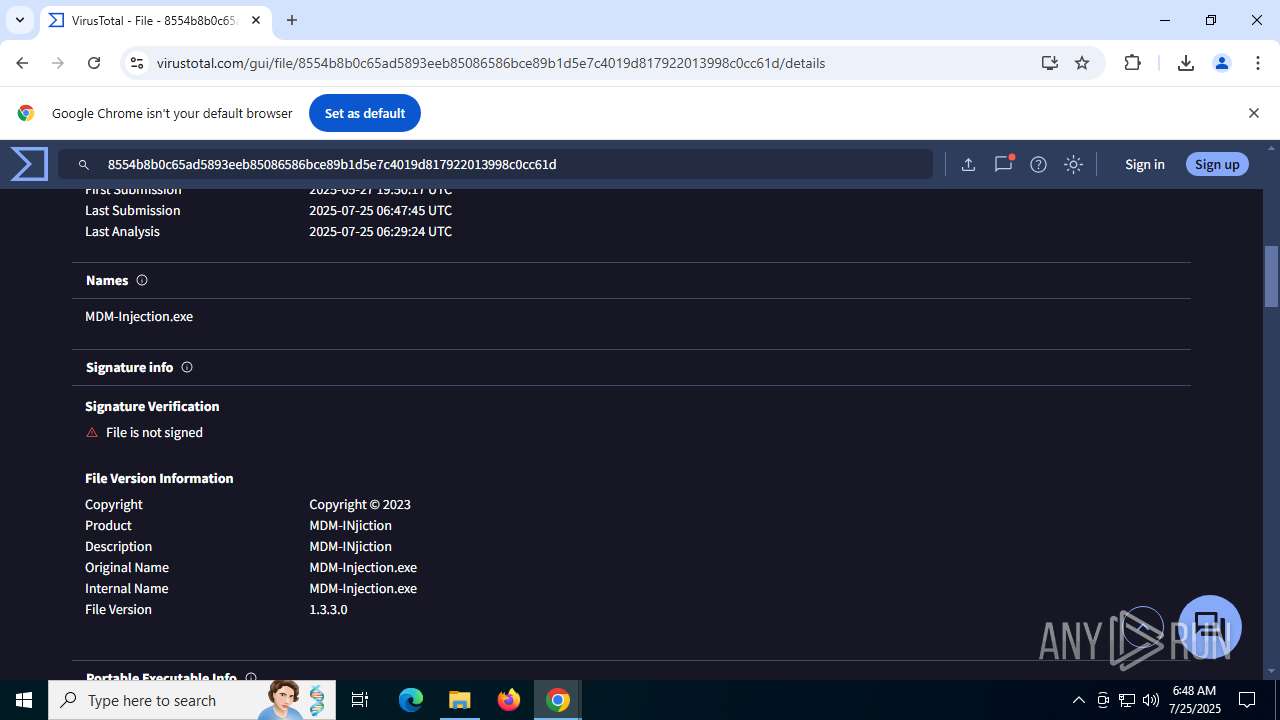
| MD5: | FB74078AF0DDBD8833794E18C6F89074 |
| SHA1: | 05B34984B8380C9826D34F1C1C72D620C0453312 |
| SHA256: | 960AE58F388C26D848D50B3F9AEB8935AE57D47432BE20E32428B32E7791194F |
| SSDEEP: | 3:N8X/iQ/msYfFoQrymhHwc9o:2t/bsF/Qc9o |
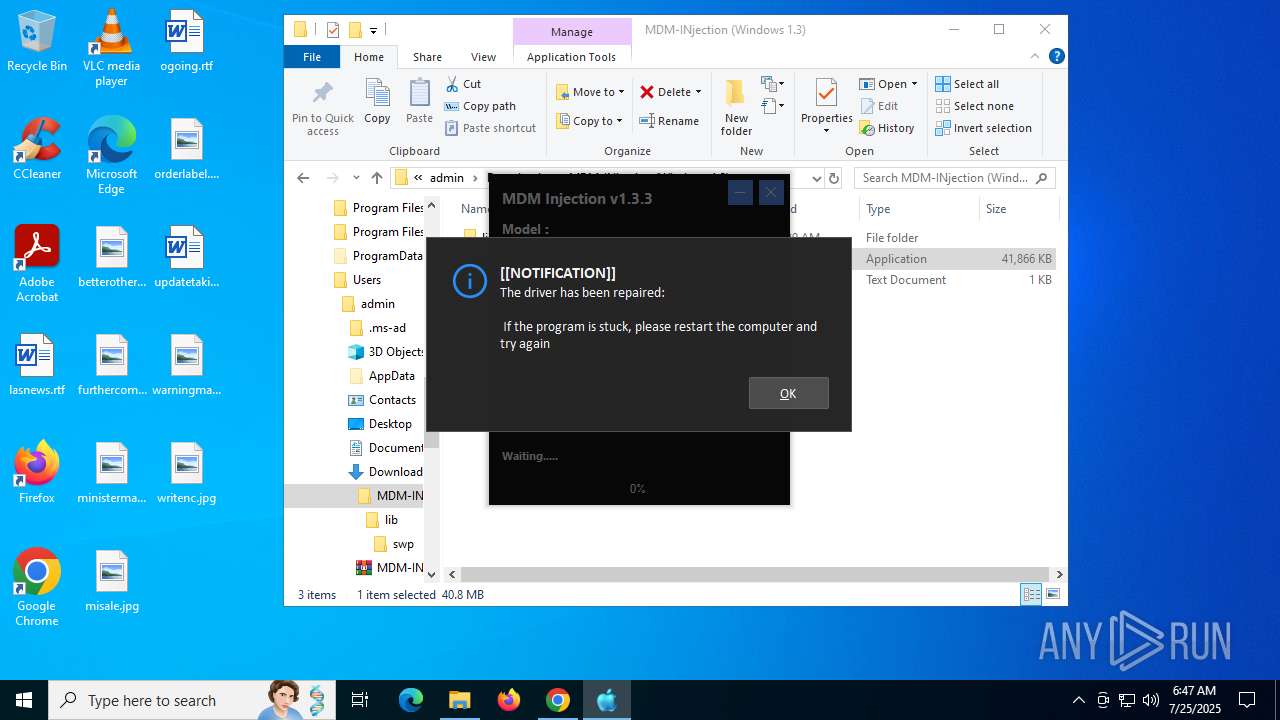
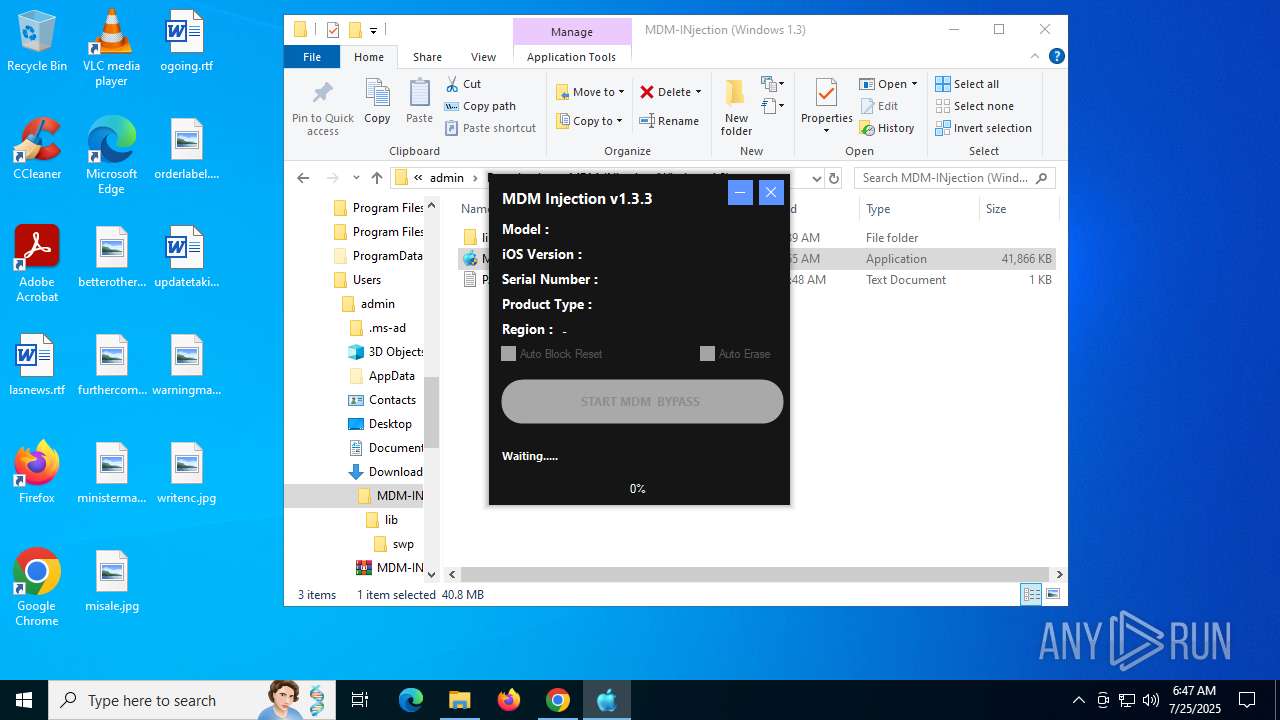
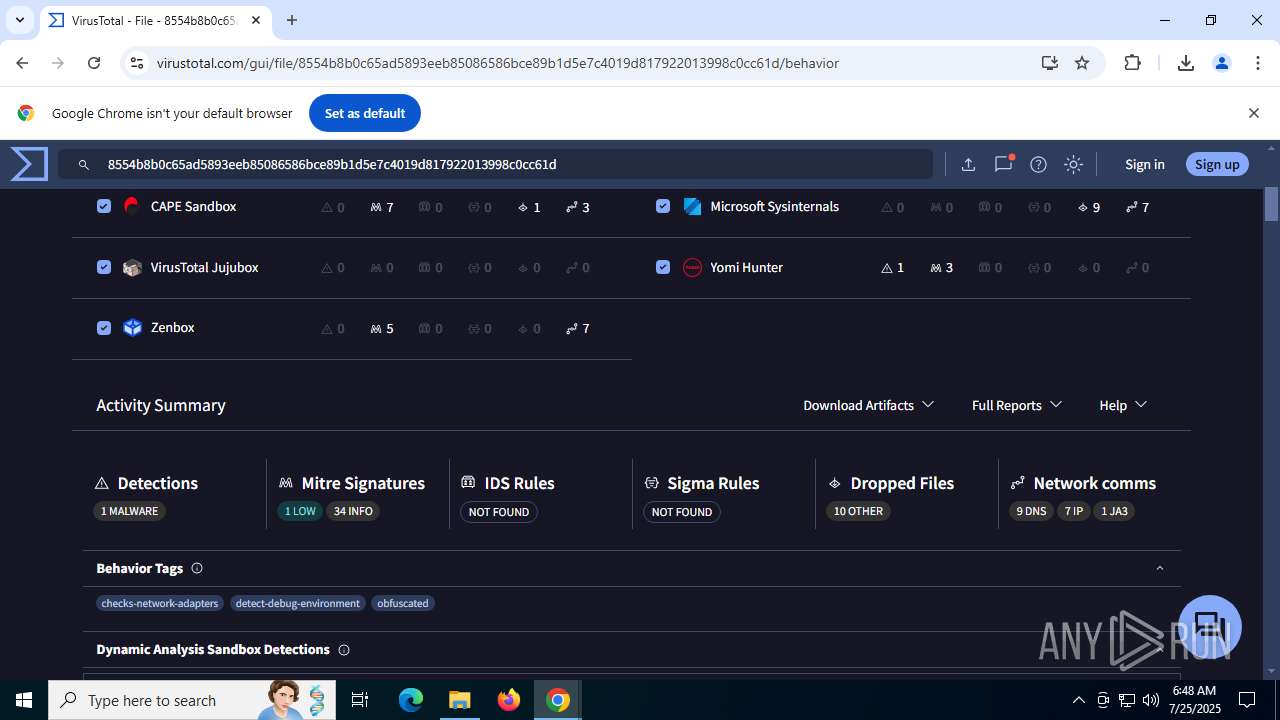
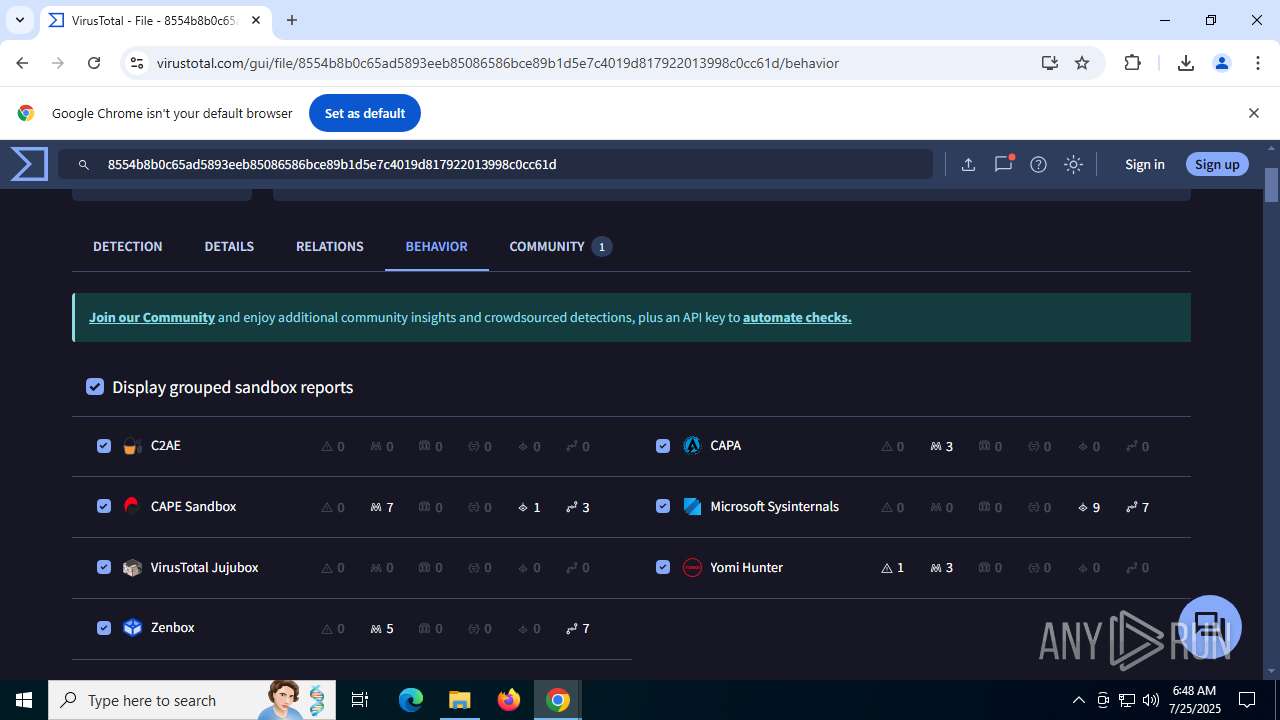
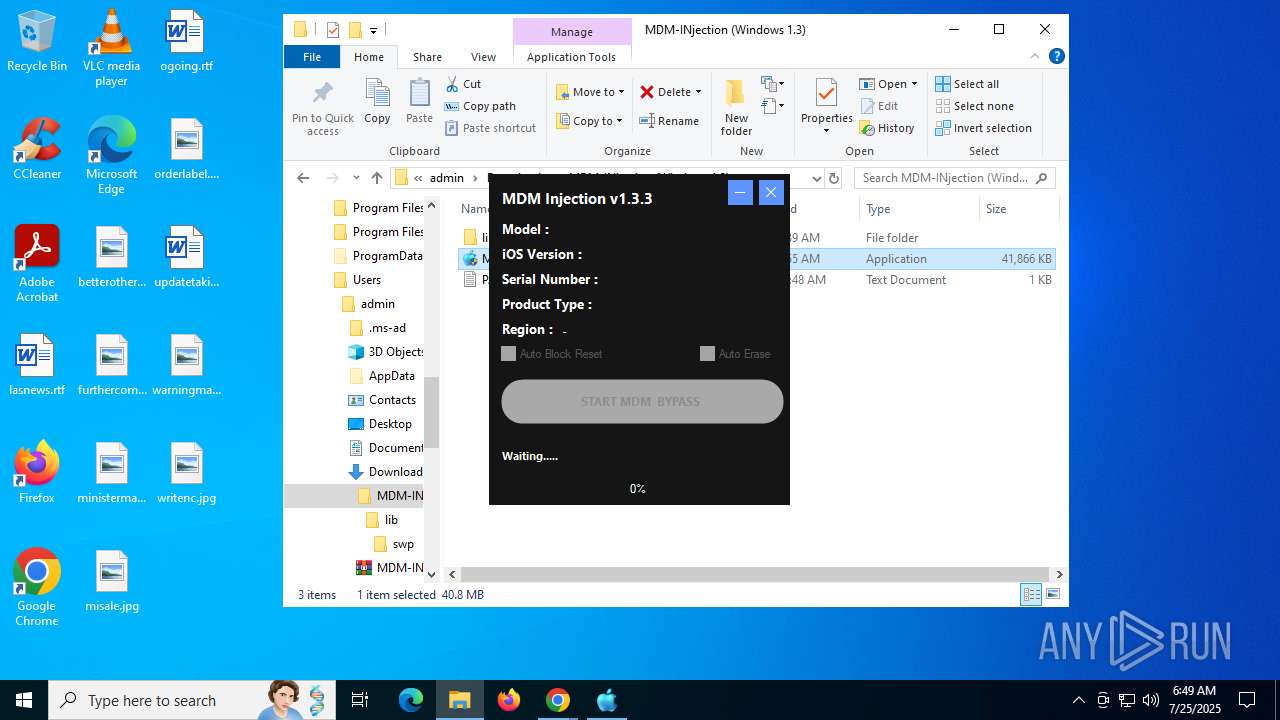
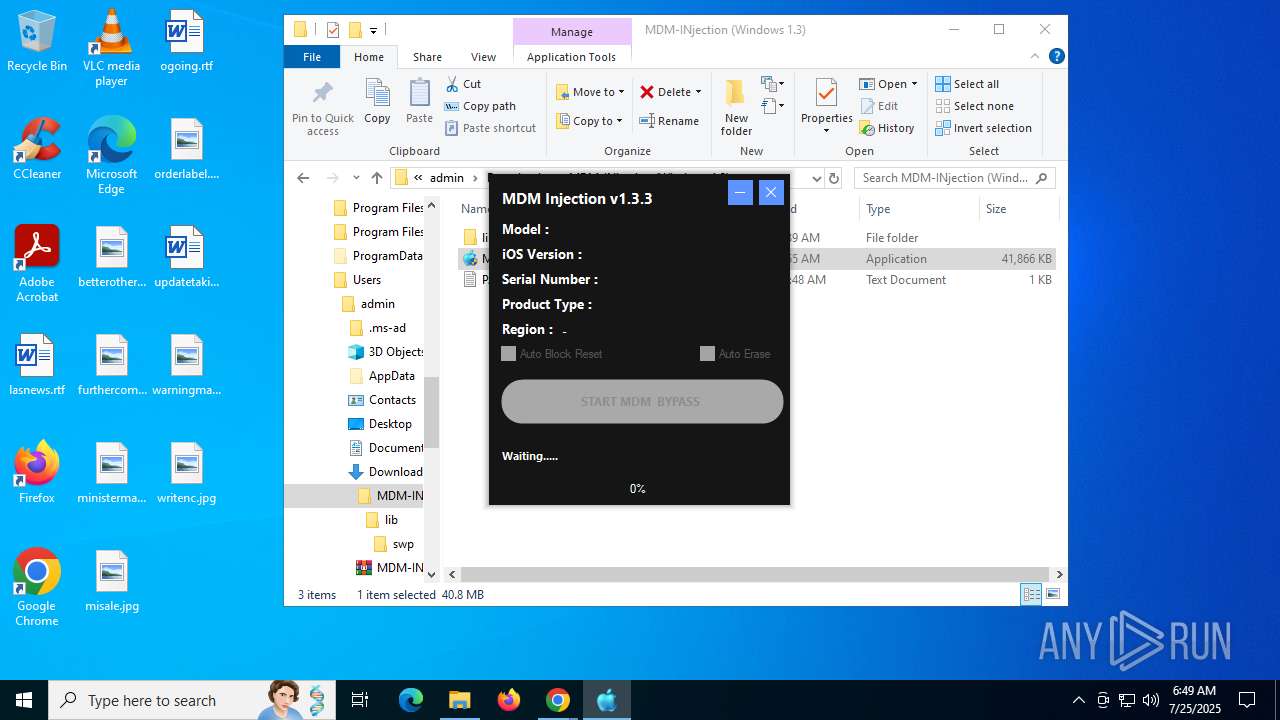
MALICIOUS
XORed URL has been found (YARA)
- MDM-Injection.exe (PID: 8140)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 7960)
Reads security settings of Internet Explorer
- MDM-Injection.exe (PID: 7852)
- MDM-Injection.exe (PID: 8044)
- MDM-Injection.exe (PID: 8140)
- WinRAR.exe (PID: 8100)
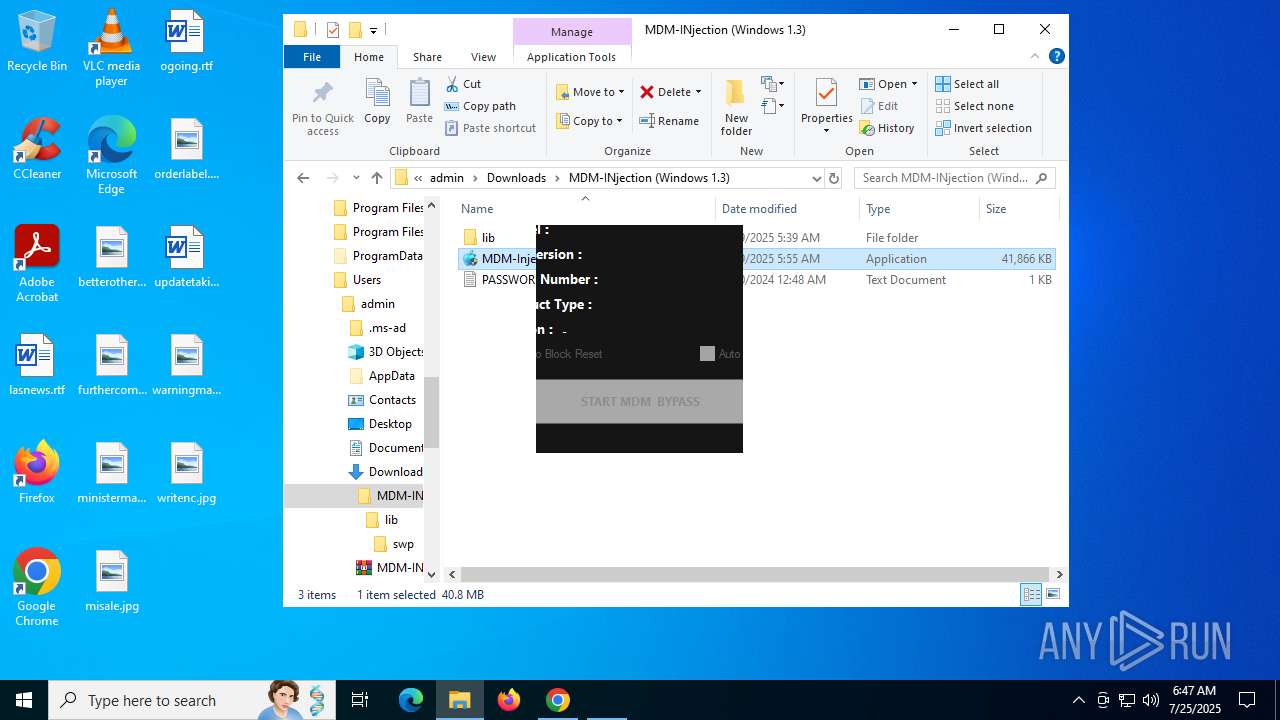
Executable content was dropped or overwritten
- MDM-Injection.exe (PID: 7852)
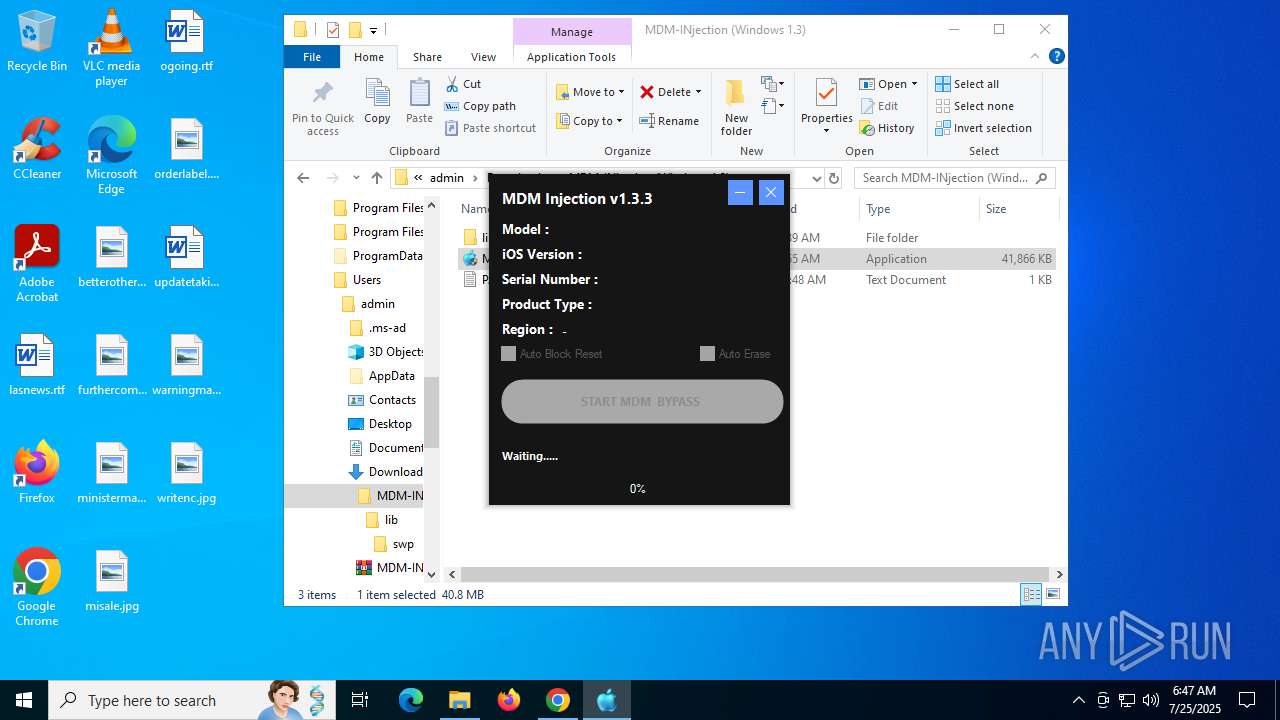
There is functionality for taking screenshot (YARA)
- MDM-Injection.exe (PID: 8140)
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 8100)
INFO
Application launched itself
- chrome.exe (PID: 5808)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 8100)
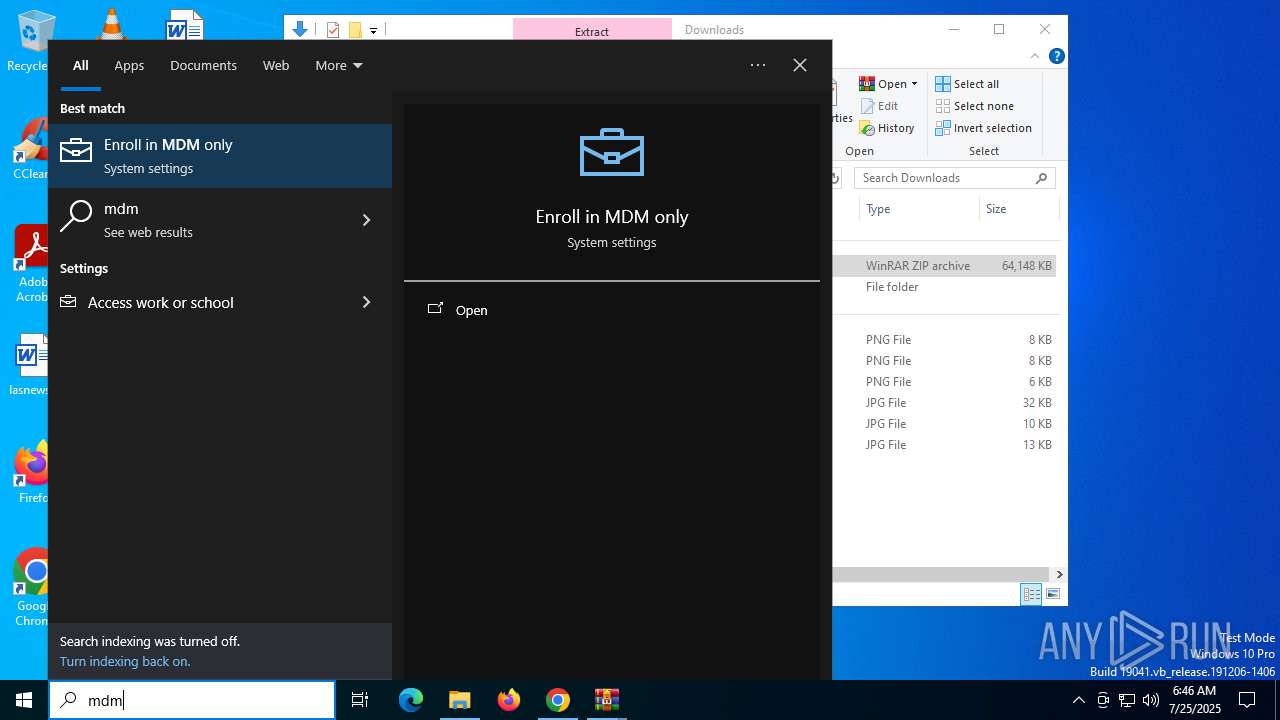
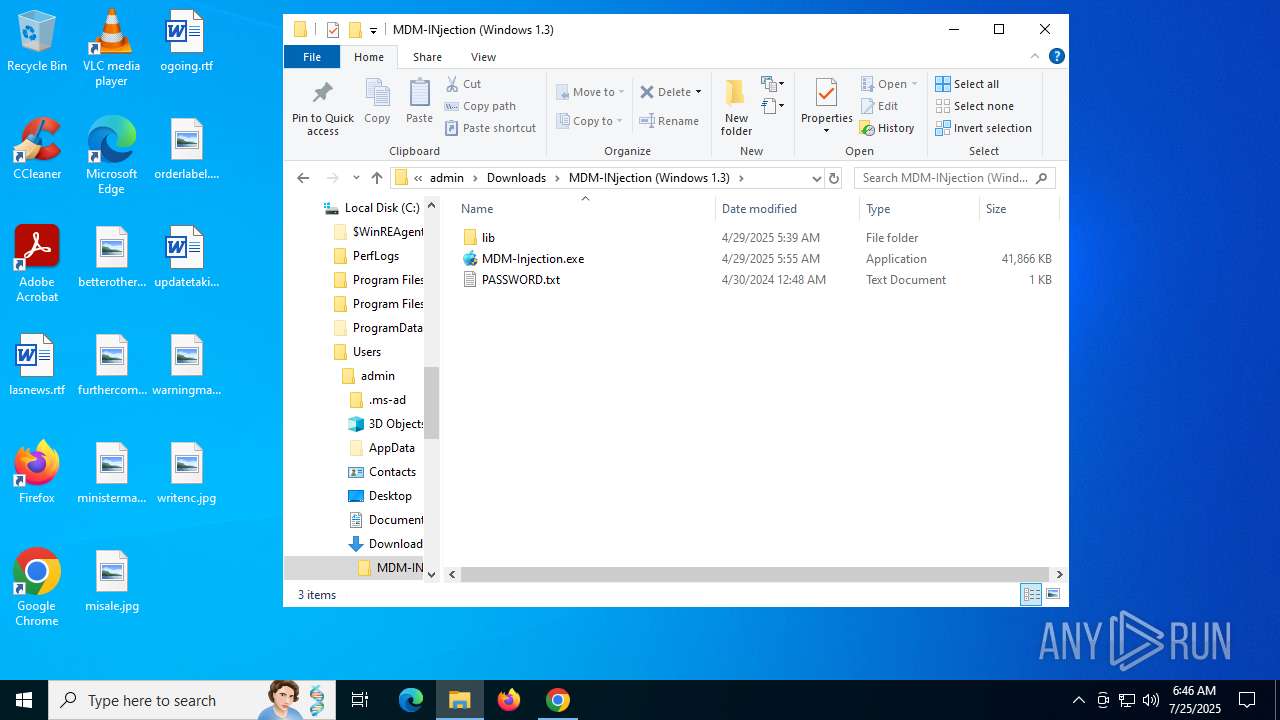
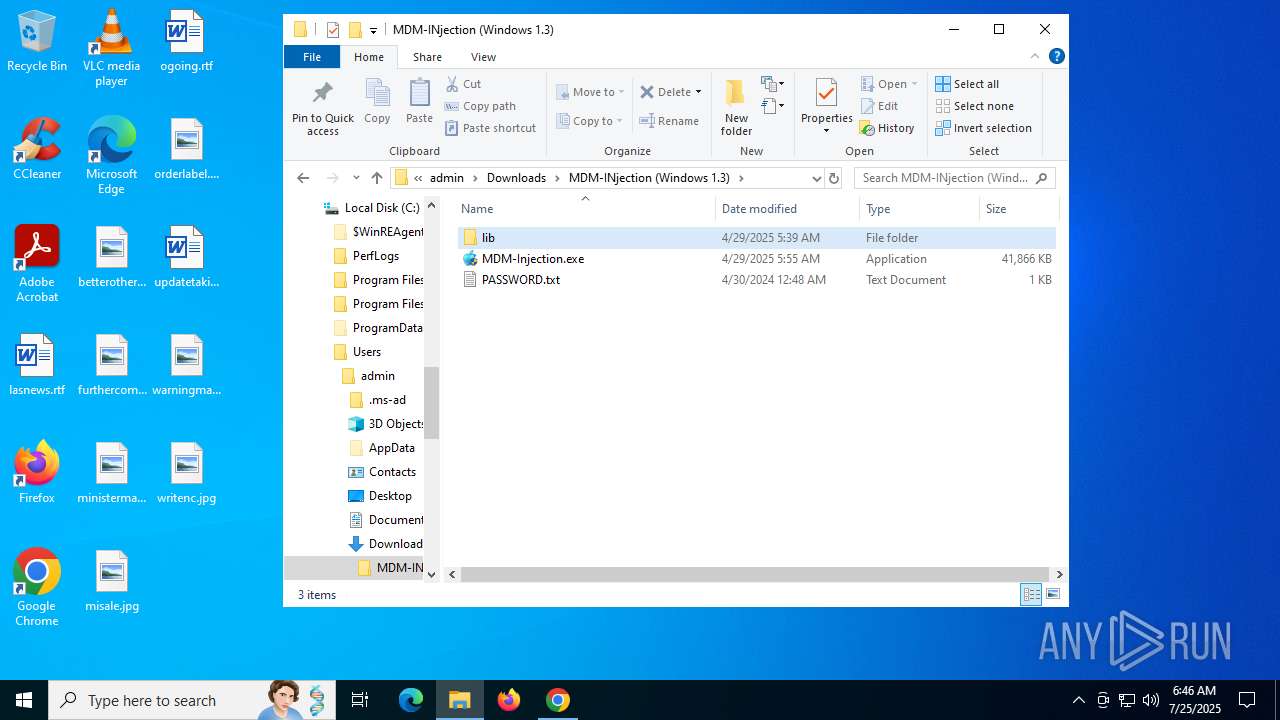
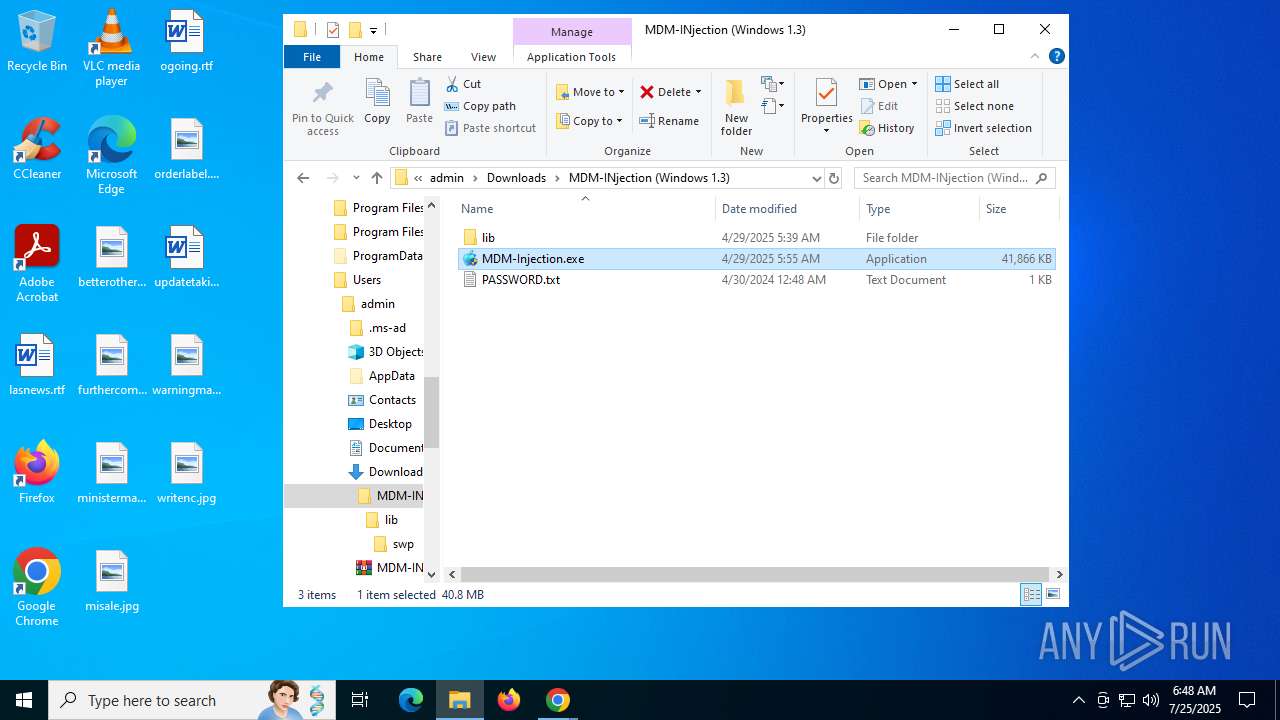
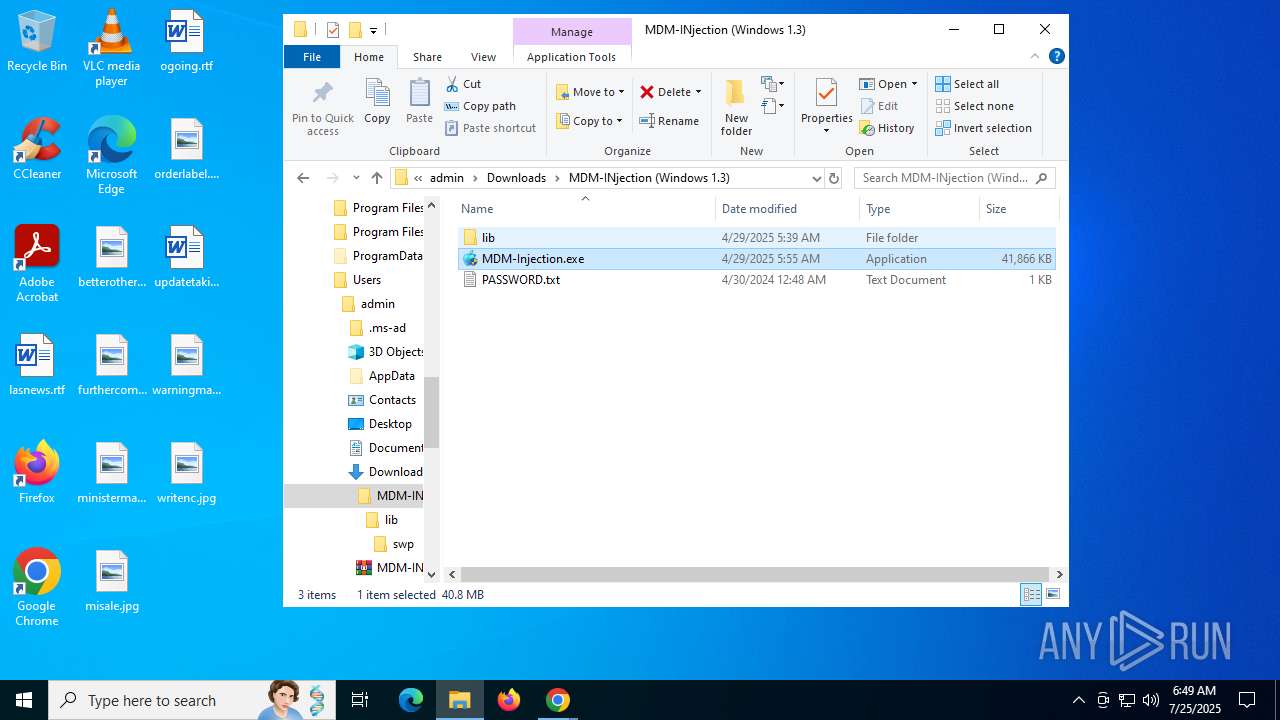
Manual execution by a user
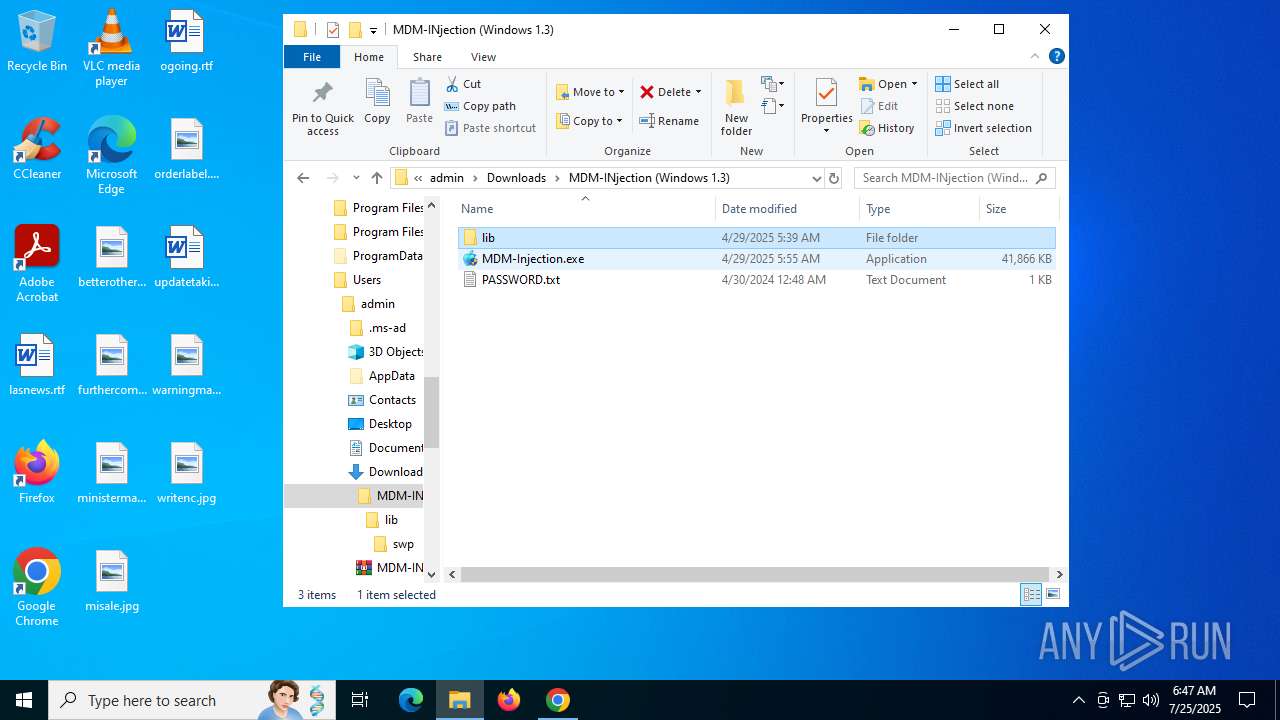
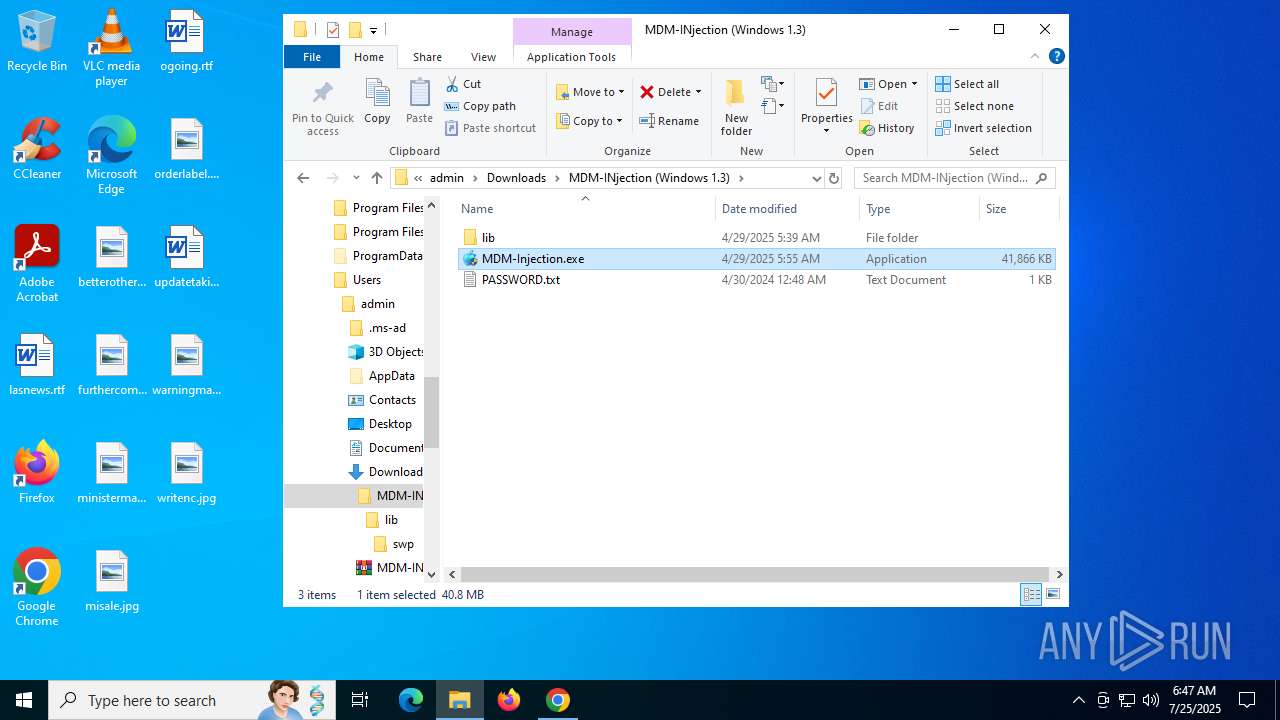
- MDM-Injection.exe (PID: 7852)
- WinRAR.exe (PID: 7960)
- MDM-Injection.exe (PID: 4120)
- MDM-Injection.exe (PID: 8044)
- MDM-Injection.exe (PID: 7048)
- MDM-Injection.exe (PID: 8140)
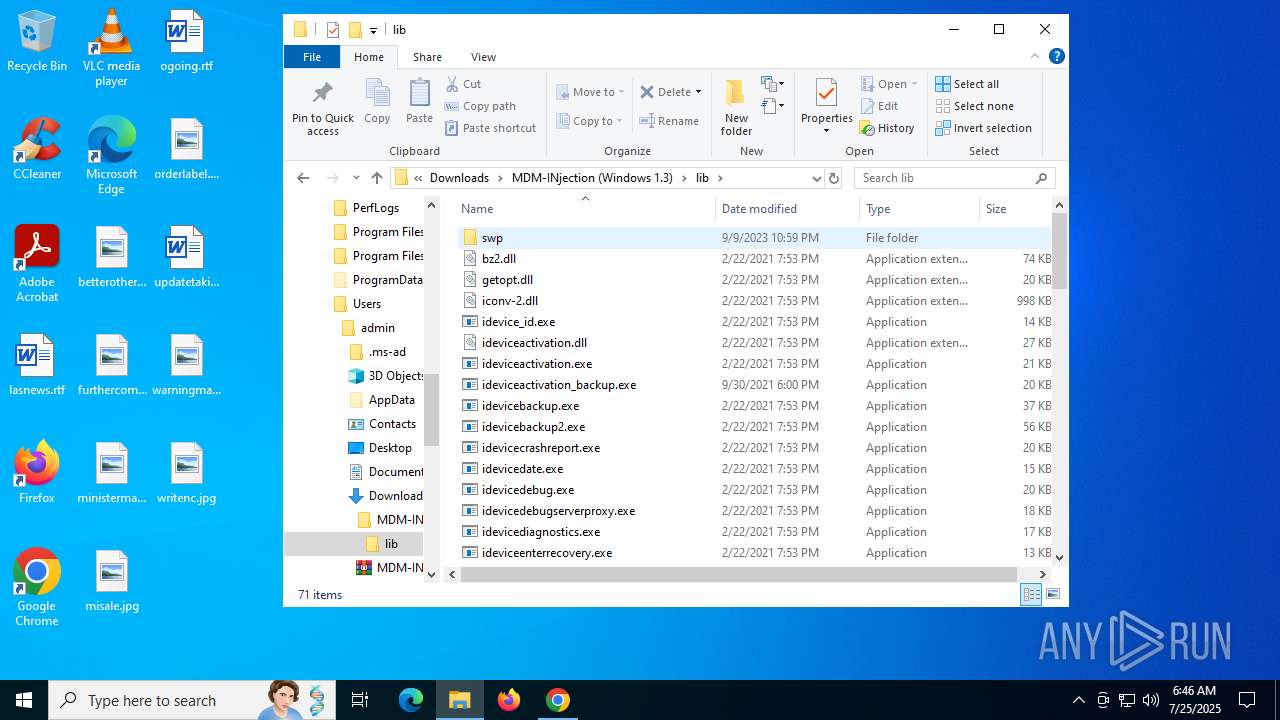
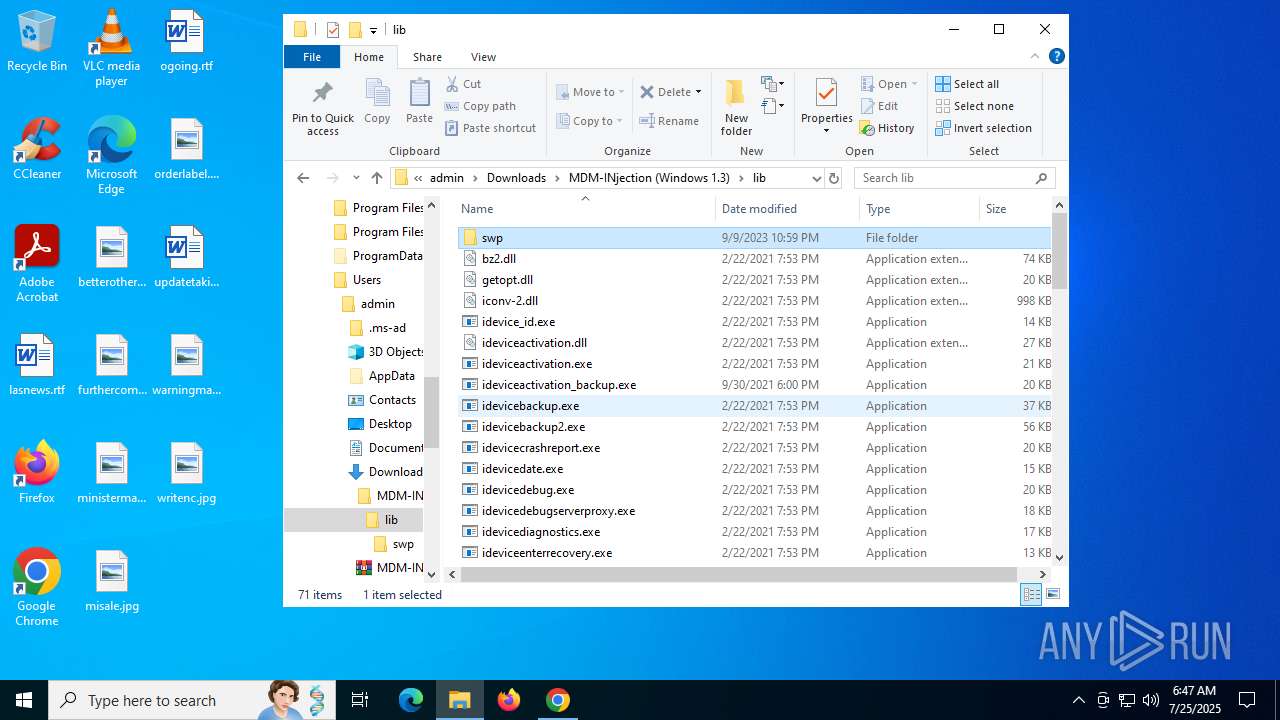
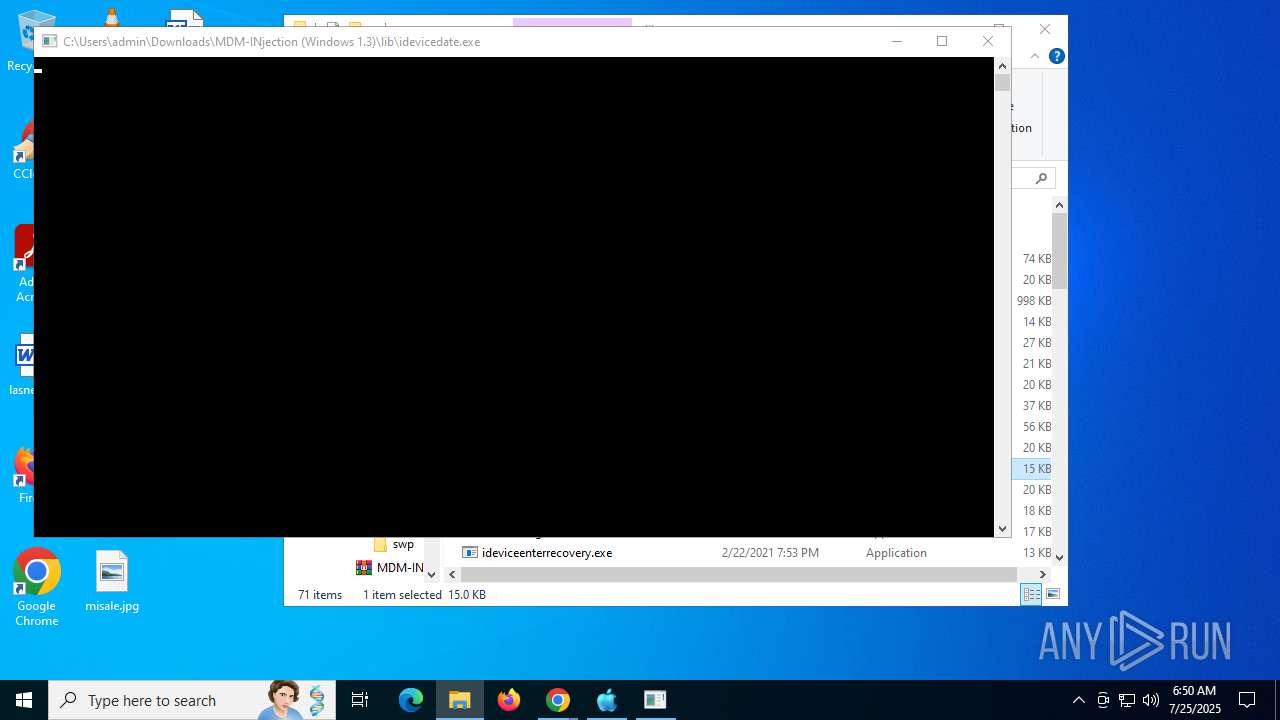
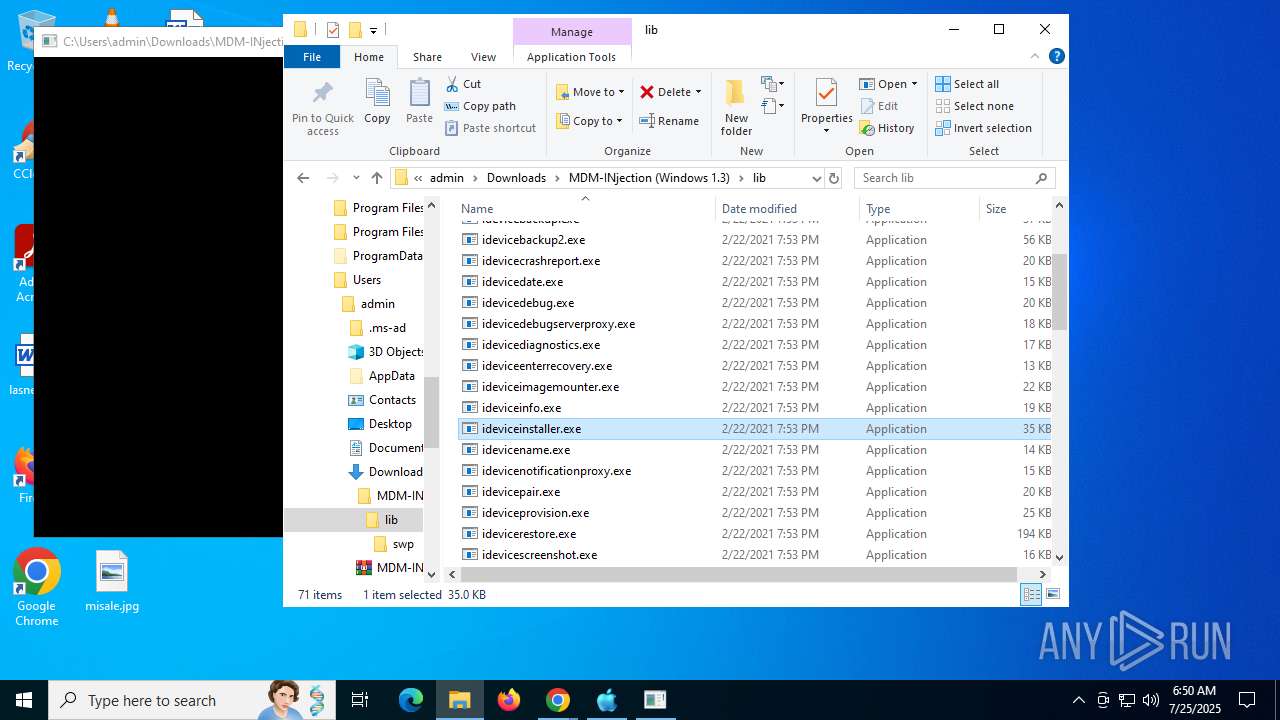
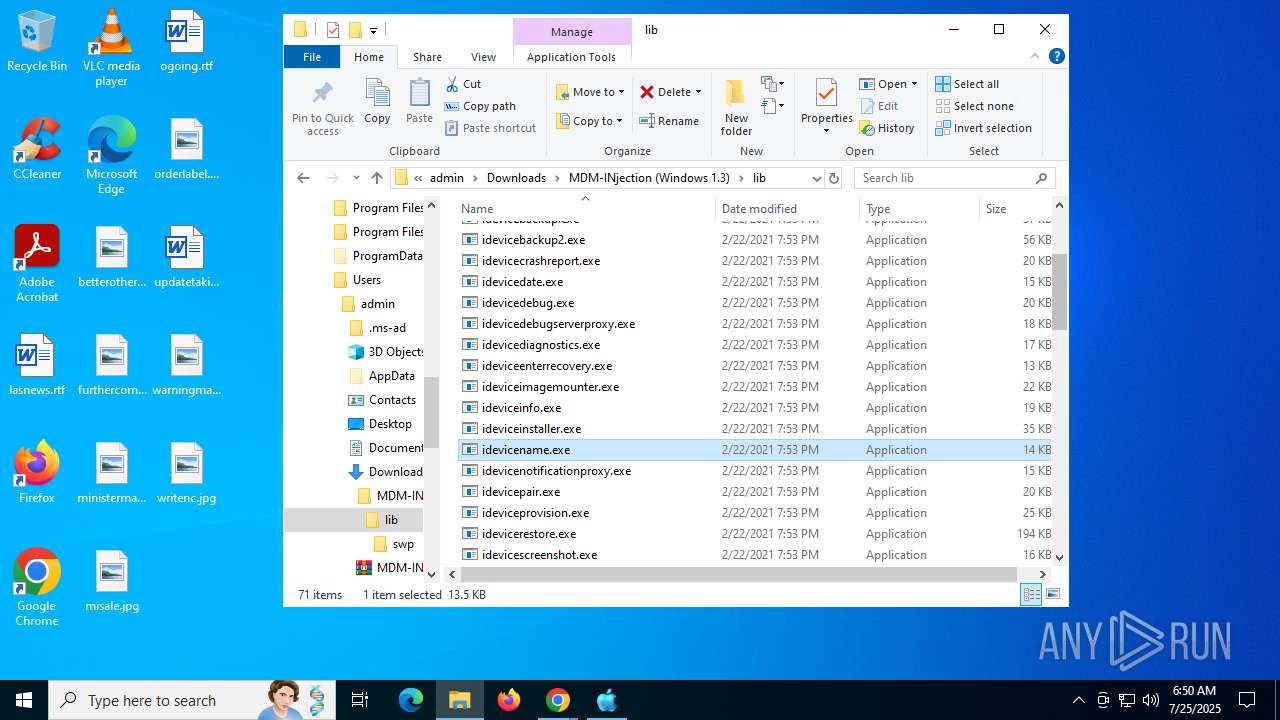
- idevice_id.exe (PID: 6776)
- ideviceactivation.exe (PID: 4700)
- ideviceactivation_backup.exe (PID: 7528)
- idevicebackup.exe (PID: 7740)
- idevicebackup2.exe (PID: 7204)
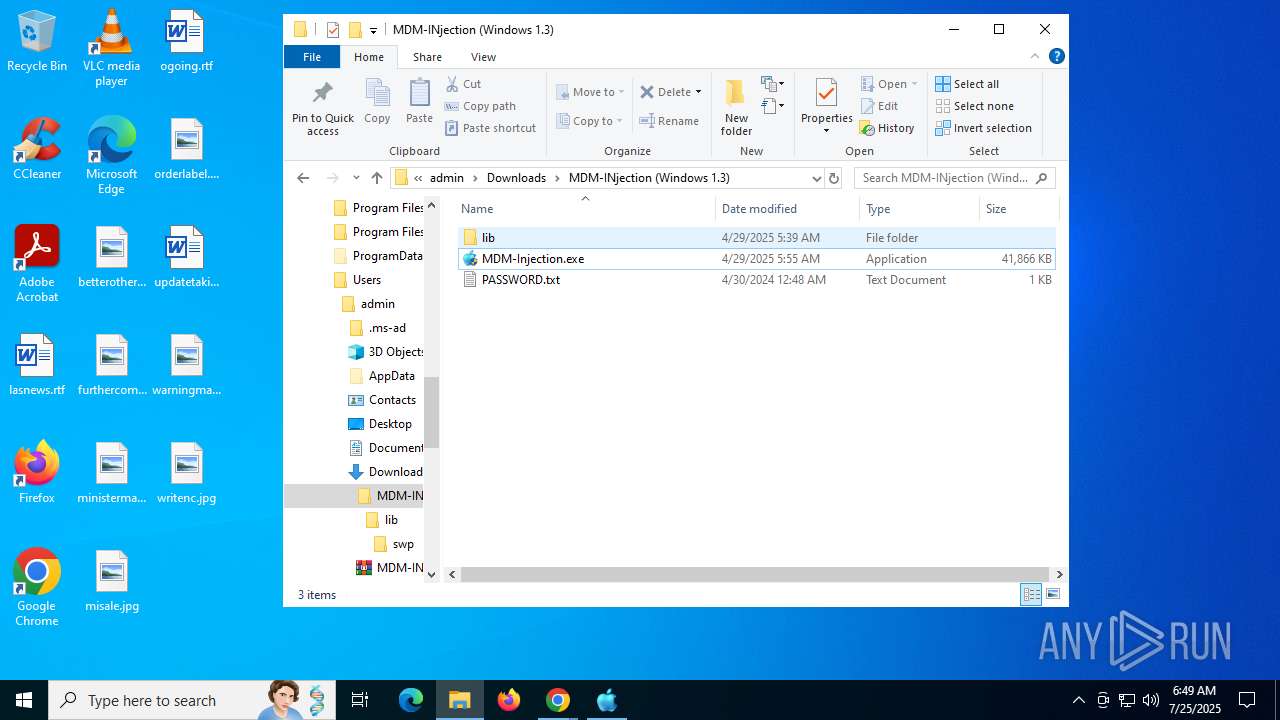
- idevicedate.exe (PID: 5556)
- idevicedebug.exe (PID: 7552)
- idevicedebugserverproxy.exe (PID: 5532)
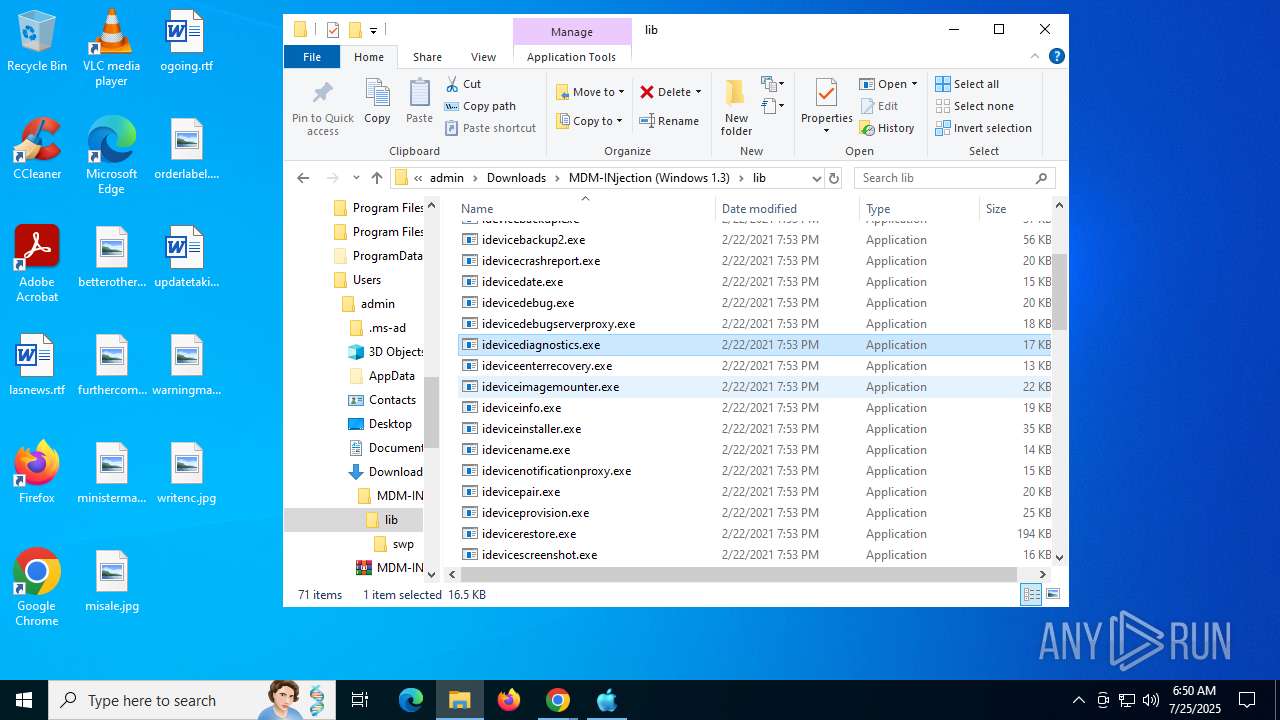
- idevicediagnostics.exe (PID: 3896)
- ideviceenterrecovery.exe (PID: 360)
- WinRAR.exe (PID: 8100)
- MDM-Injection.exe (PID: 7800)
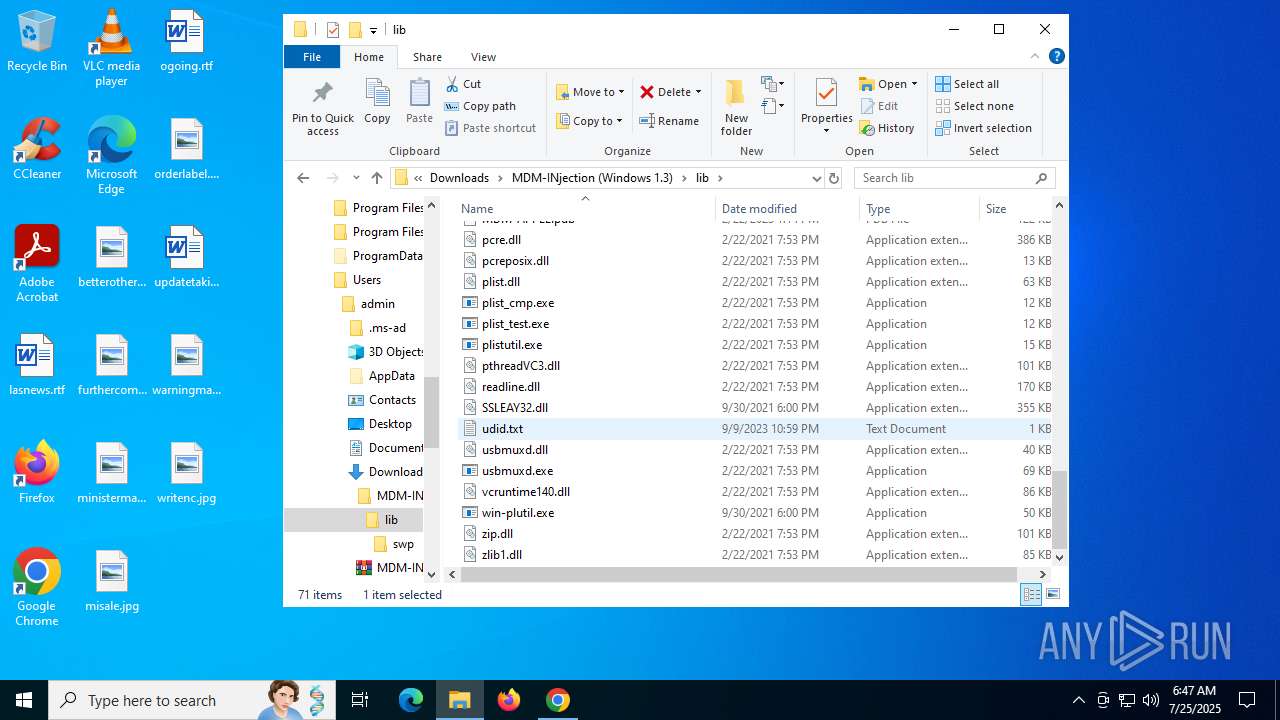
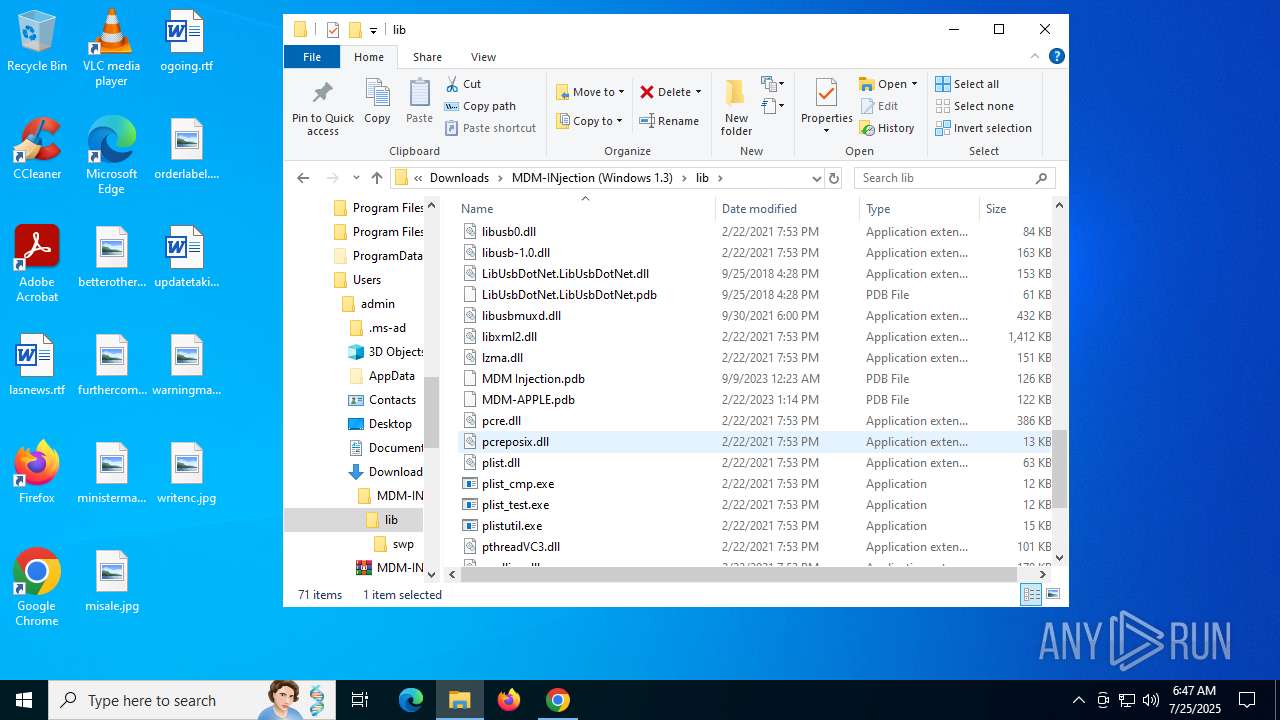
- ideviceinfo.exe (PID: 5528)
- idevicename.exe (PID: 4856)
- ideviceinstaller.exe (PID: 7356)
- ideviceimagemounter.exe (PID: 5220)
- idevicecrashreport.exe (PID: 2552)
The sample compiled with english language support
- WinRAR.exe (PID: 7960)
- MDM-Injection.exe (PID: 7852)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7960)
Reads the computer name
- MDM-Injection.exe (PID: 7852)
- MDM-Injection.exe (PID: 8044)
- MDM-Injection.exe (PID: 8140)
Reads the machine GUID from the registry
- MDM-Injection.exe (PID: 7852)
- MDM-Injection.exe (PID: 8044)
- MDM-Injection.exe (PID: 8140)
Disables trace logs
- MDM-Injection.exe (PID: 7852)
- MDM-Injection.exe (PID: 8044)
- MDM-Injection.exe (PID: 8140)
Checks supported languages
- MDM-Injection.exe (PID: 7852)
- MDM-Injection.exe (PID: 8044)
- idevice_id.exe (PID: 6776)
- ideviceactivation.exe (PID: 4700)
- MDM-Injection.exe (PID: 8140)
- idevicebackup.exe (PID: 7740)
- idevicebackup2.exe (PID: 7204)
- ideviceactivation_backup.exe (PID: 7528)
- idevicecrashreport.exe (PID: 2552)
- idevicedate.exe (PID: 5556)
- idevicedebug.exe (PID: 7552)
- idevicedebugserverproxy.exe (PID: 5532)
- idevicediagnostics.exe (PID: 3896)
- ideviceinfo.exe (PID: 5528)
- ideviceimagemounter.exe (PID: 5220)
- idevicename.exe (PID: 4856)
- ideviceinstaller.exe (PID: 7356)
- ideviceenterrecovery.exe (PID: 360)
Checks proxy server information
- MDM-Injection.exe (PID: 7852)
- slui.exe (PID: 7200)
- MDM-Injection.exe (PID: 8044)
- MDM-Injection.exe (PID: 8140)
Reads Environment values
- MDM-Injection.exe (PID: 7852)
- MDM-Injection.exe (PID: 8044)
- MDM-Injection.exe (PID: 8140)
Reads the software policy settings
- MDM-Injection.exe (PID: 7852)
- slui.exe (PID: 7200)
- MDM-Injection.exe (PID: 8044)
- MDM-Injection.exe (PID: 8140)
Creates files in the program directory
- MDM-Injection.exe (PID: 7852)
Confuser has been detected (YARA)
- MDM-Injection.exe (PID: 8140)
Reads security settings of Internet Explorer
- notepad.exe (PID: 8152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(8140) MDM-Injection.exe
Decrypted-URLs (22)http://crl.thawte.com/ThawteTimestampingCA.crl0
http://ocsp.thawte.com0
http://s.symcb.com/universal-root.crl0
http://s.symcd.com06
http://s1.symcb.com/pca3-g5.crl0
http://s2.symcb.com0
http://sv.symcb.com/sv.crl0a
http://sv.symcb.com/sv.crt0
http://ts-aia.ws.symantec.com/sha256-tss-ca.cer0(
http://ts-aia.ws.symantec.com/tss-ca-g2.cer0
http://ts-crl.ws.symantec.com/sha256-tss-ca.crl0
http://ts-crl.ws.symantec.com/tss-ca-g2.crl0(
http://ts-ocsp.ws.symantec.com07
http://www.apple.com/
http://www.symauth.com/cps0(
http://www.symauth.com/rpa00
http://www.winimage.com/zLibDll
https://d.symcb.com/cps0%
https://d.symcb.com/rpa0
https://d.symcb.com/rpa0.
https://d.symcb.com/rpa0@
https://xp.apple.com/report
Total processes
218
Monitored processes
67
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2272,i,12779465298046386890,6009248808832347966,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2452 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 360 | "C:\Users\admin\Downloads\MDM-INjection (Windows 1.3)\lib\ideviceenterrecovery.exe" | C:\Users\admin\Downloads\MDM-INjection (Windows 1.3)\lib\ideviceenterrecovery.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | idevicename.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ideviceinfo.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3212,i,12779465298046386890,6009248808832347966,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ideviceinstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --field-trial-handle=6024,i,12779465298046386890,6009248808832347966,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1624 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | idevicedate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --string-annotations --field-trial-handle=5064,i,12779465298046386890,6009248808832347966,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5076 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --field-trial-handle=5948,i,12779465298046386890,6009248808832347966,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6656 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
12 004
Read events
11 928
Write events
69
Delete events
7
Modification events
| (PID) Process: | (5808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5808) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
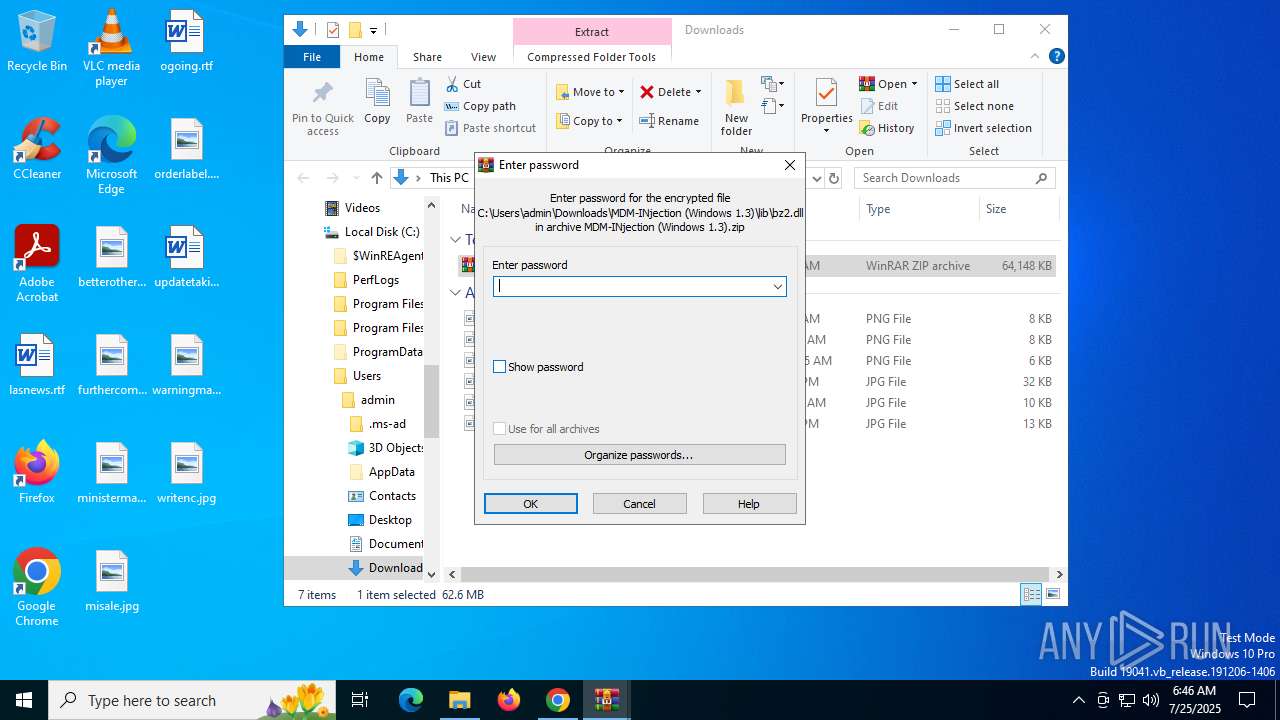
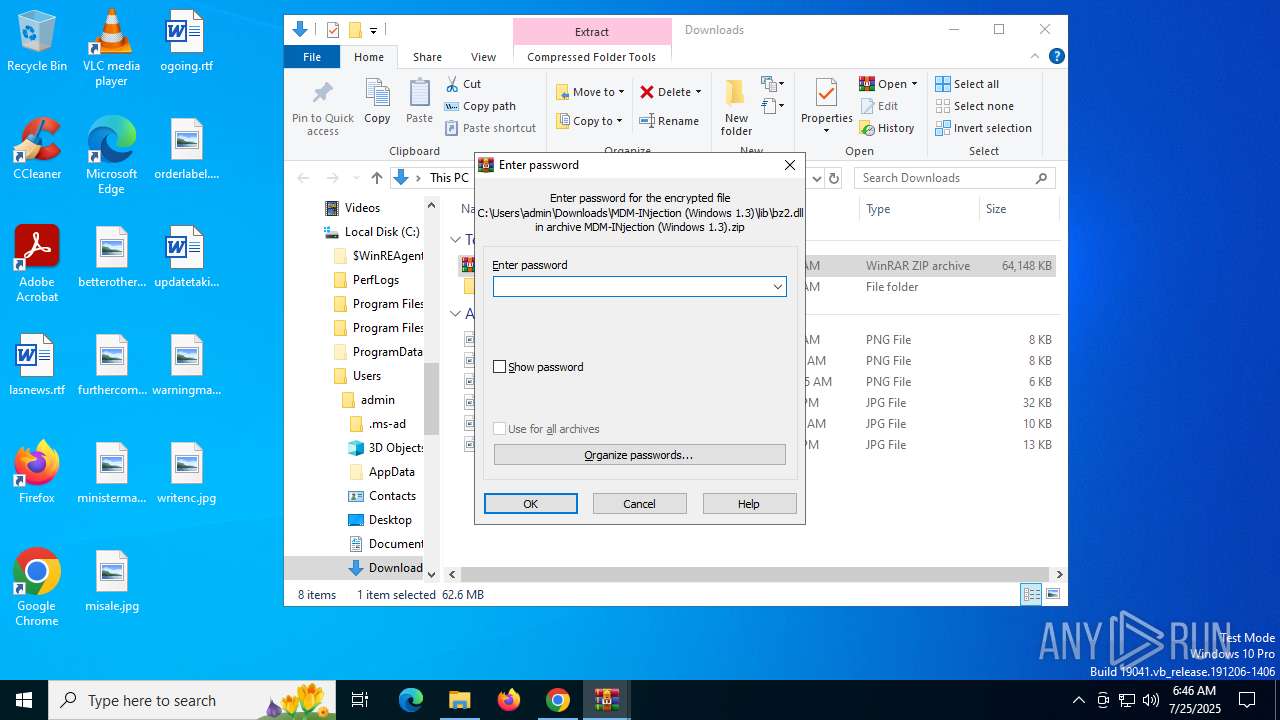
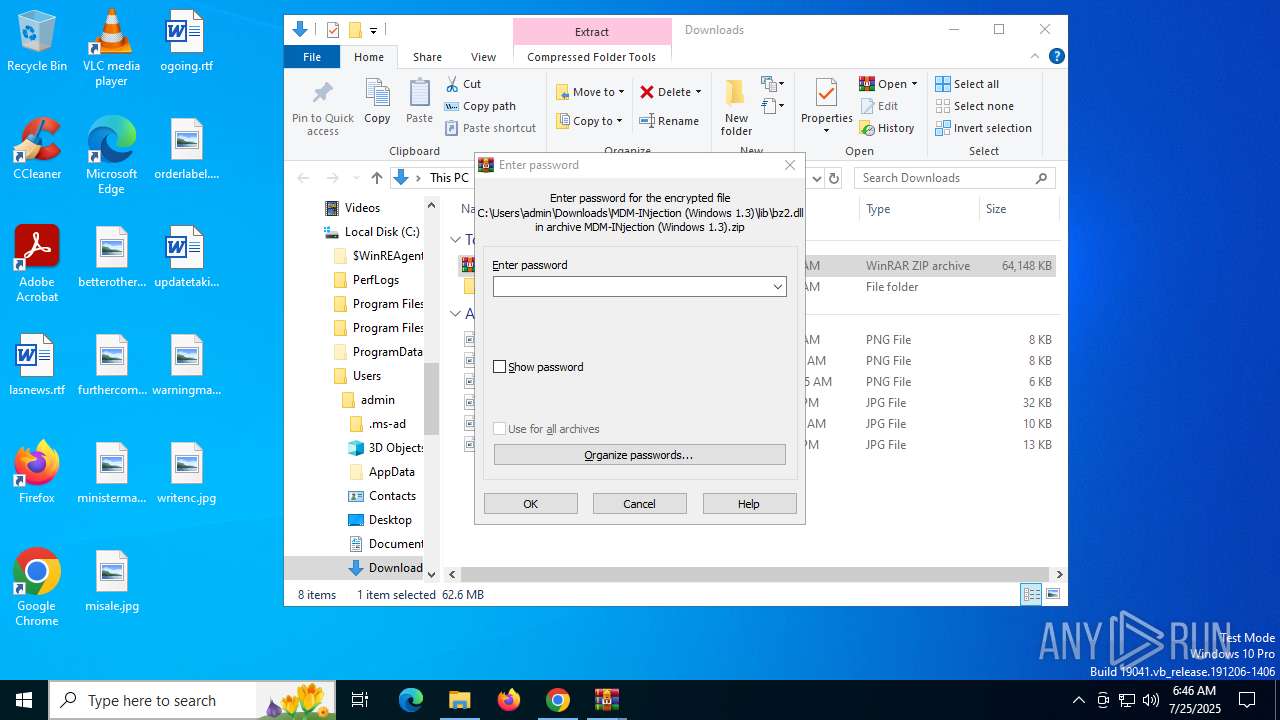
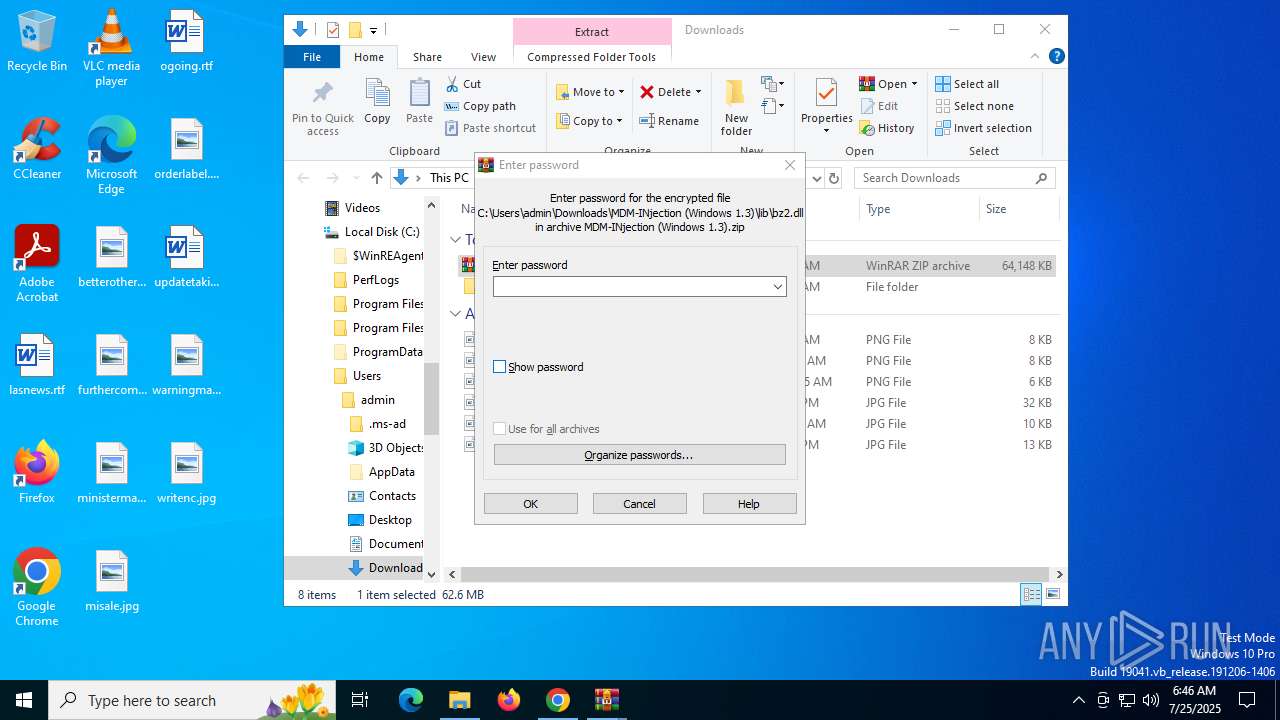
| (PID) Process: | (7960) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
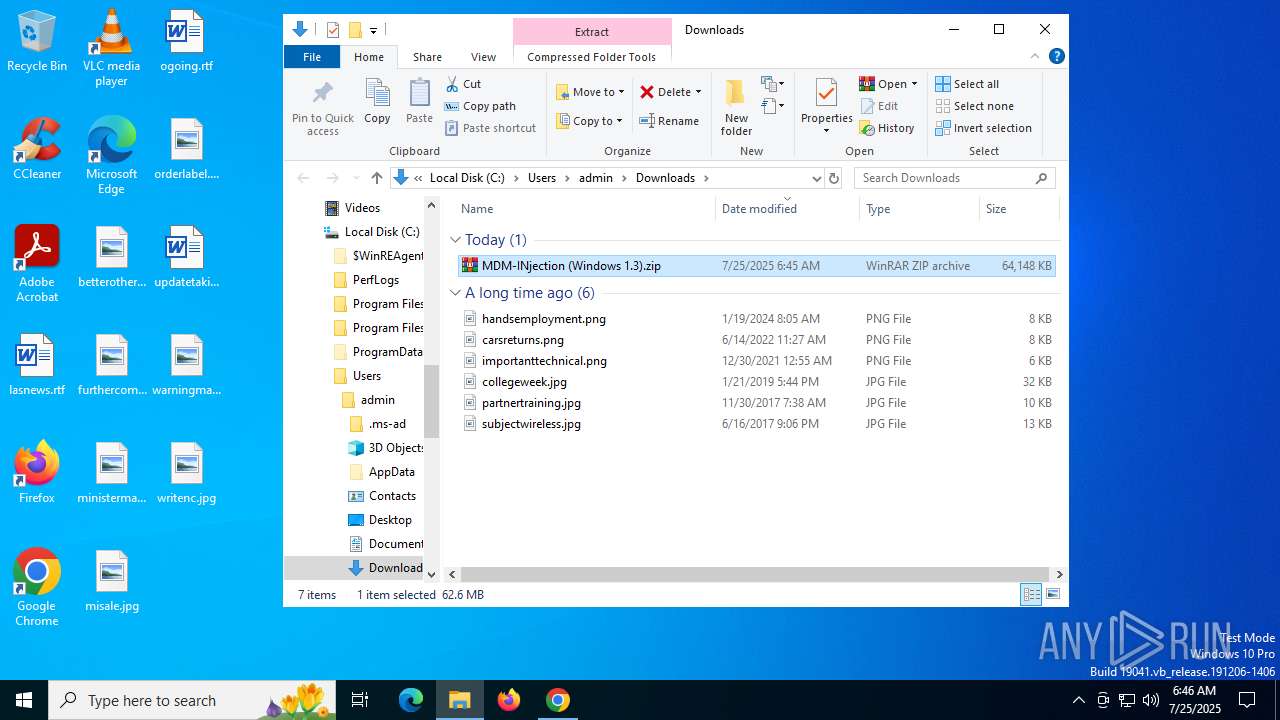
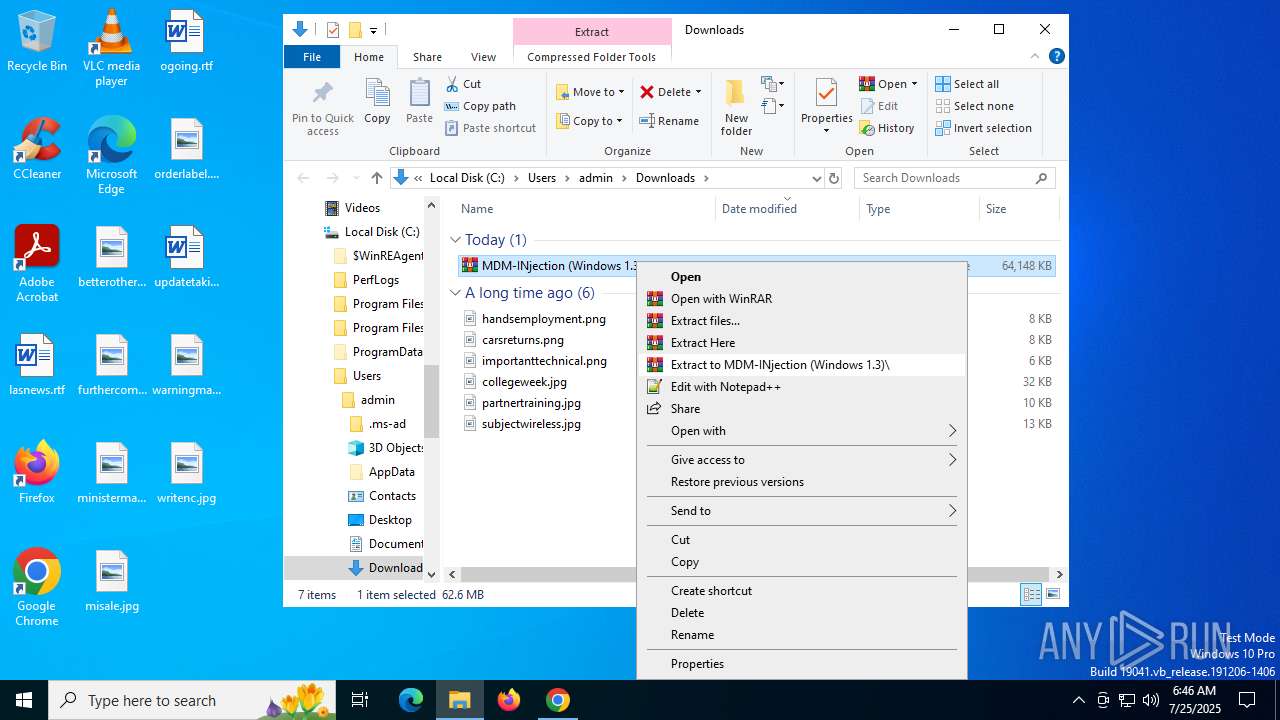
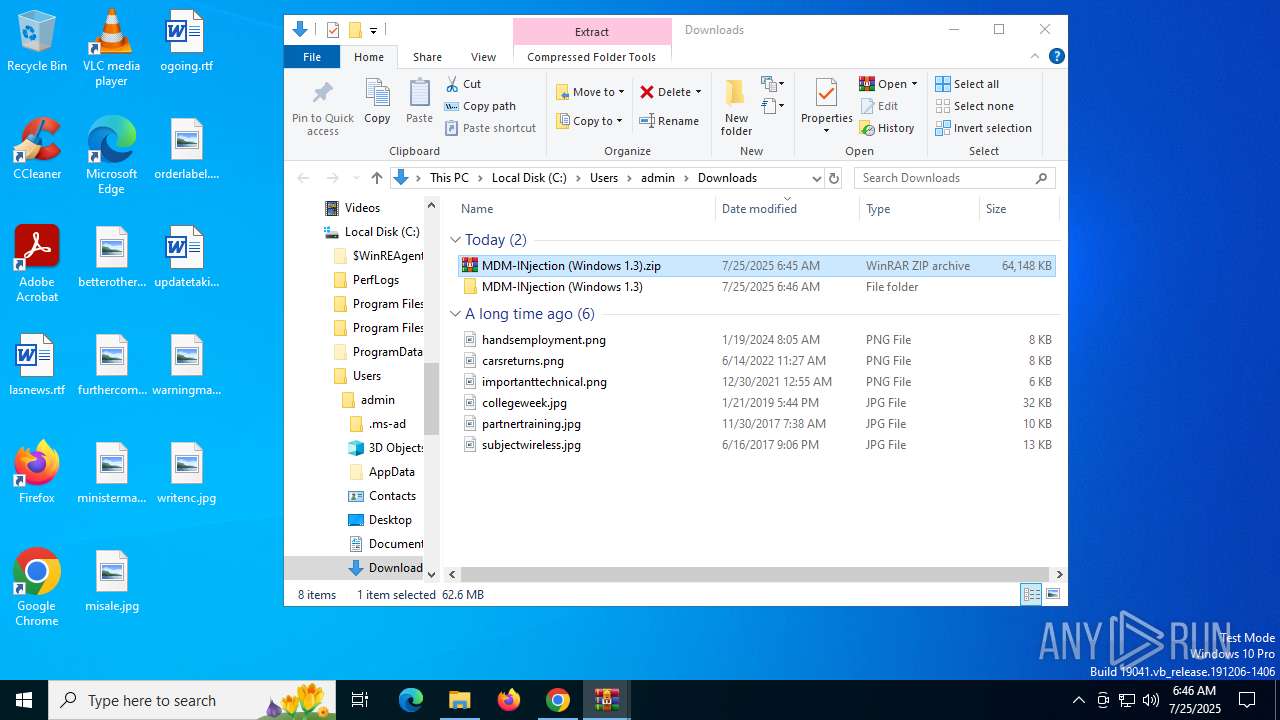
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\MDM-INjection (Windows 1.3).zip | |||
Executable files
66
Suspicious files
79
Text files
34
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF18d57b.TMP | — | |
MD5:— | SHA256:— | |||
| 5808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF18d9ff.TMP | — | |
MD5:— | SHA256:— | |||
| 5808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF18d9ff.TMP | — | |
MD5:— | SHA256:— | |||
| 5808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF18d9ff.TMP | — | |
MD5:— | SHA256:— | |||
| 5808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF18d9ff.TMP | — | |
MD5:— | SHA256:— | |||
| 5808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RF18da0f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
336
DNS requests
135
Threats
36
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2356 | chrome.exe | GET | 200 | 142.250.181.238:80 | http://clients2.google.com/time/1/current?cup2key=8:Ng8740oze2RmOozIrDFthSR5CsxmTbmL-BXpI__8OZQ&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6240 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8008 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8008 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7388 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
7388 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3400 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2356 | chrome.exe | 216.58.206.42:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
2356 | chrome.exe | 31.216.145.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
2356 | chrome.exe | 142.250.181.238:80 | clients2.google.com | GOOGLE | US | whitelisted |
2356 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2356 | chrome.exe | 142.250.184.234:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
mega.nz |
| whitelisted |
accounts.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
eu.static.mega.co.nz |
| whitelisted |
g.api.mega.co.nz |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2356 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2356 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2356 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2356 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2356 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2356 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2356 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2356 | chrome.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2356 | chrome.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2356 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |