| File name: | Duxa's PS4 patch repackager 6.15.18.exe |
| Full analysis: | https://app.any.run/tasks/7566e742-86a5-4431-a173-4aae52411900 |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2018, 15:42:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 7892CC956FD394DA4F49870AE3C23FFD |
| SHA1: | BD21E4A0C2E497F8039310862B1AF4F88443849D |
| SHA256: | 95FEF2F75054A7831045B35058DD8EB280B49B75272C25D44BD7E2E67E865AC4 |
| SSDEEP: | 98304:VJclsqF52N2K/eP7raxmv/ieIAUIbwhqDsZZUxCkIPscB3loEGMY+R:4pF8Z+mkv/ieKIbRbxCH0cBlv |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- Duxa's PS4 patch repackager 6.15.18.exe (PID: 3032)
- Robocopy.exe (PID: 3780)
- Robocopy.exe (PID: 3380)
- Robocopy.exe (PID: 4012)
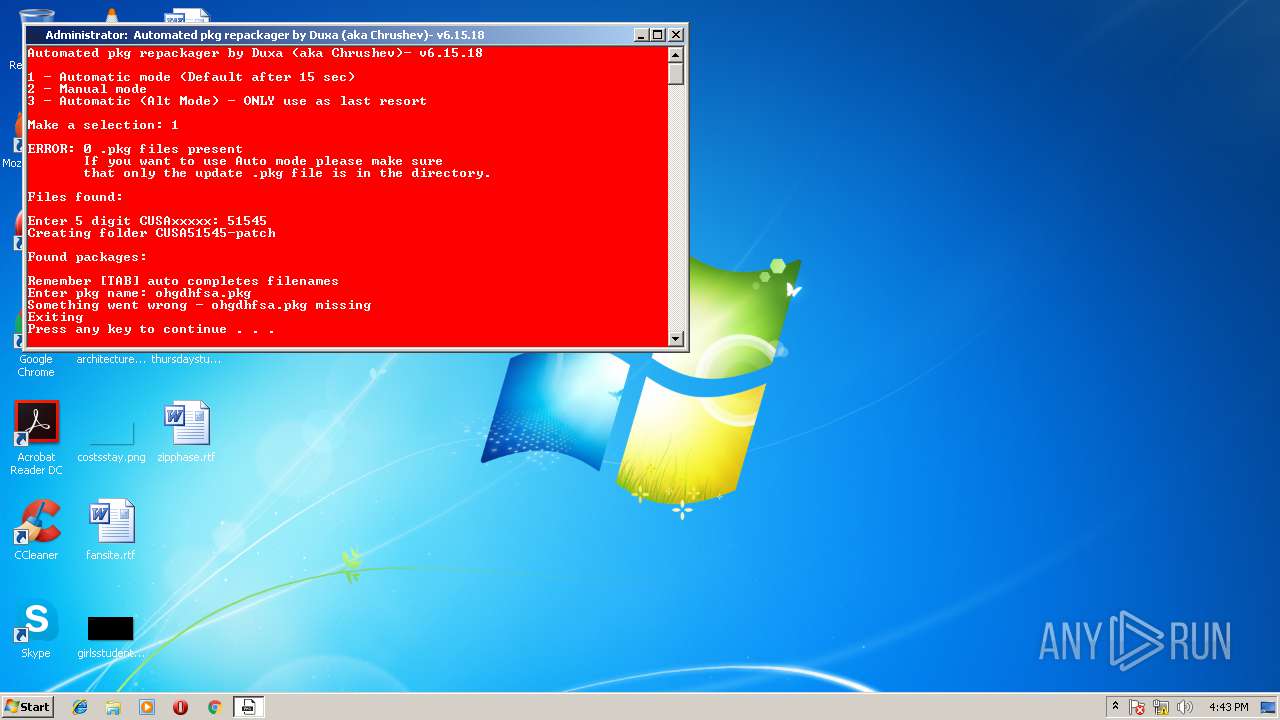
Starts CMD.EXE for commands execution
- Duxa's PS4 patch repackager 6.15.18.exe (PID: 3032)
- cmd.exe (PID: 2556)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2496)
Starts CHOICE.EXE (used to create a delay)
- cmd.exe (PID: 2556)
Application launched itself
- cmd.exe (PID: 2556)
INFO
Dropped object may contain Bitcoin addresses
- Duxa's PS4 patch repackager 6.15.18.exe (PID: 3032)
Dropped object may contain URL's
- Duxa's PS4 patch repackager 6.15.18.exe (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:11:26 20:47:21+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 49152 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x651e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.6.15.18 |
| ProductVersionNumber: | 0.6.15.18 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileVersion: | 0.6.15.18 |
| ProductVersion: | 0.6.15.18 |
| FileDescription: | PS4 update repackager (fake pkg only) |
| CompanyName: | - |
| LegalCopyright: | Duxa (aka Chrushev) |
| ProductName: | Automated pkg repackager |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 26-Nov-2012 19:47:21 |
| Detected languages: |
|
| FileVersion: | 0.6.15.18 |
| ProductVersion: | 0.6.15.18 |
| FileDescription: | PS4 update repackager (fake pkg only) |
| CompanyName: | - |
| LegalCopyright: | Duxa (aka Chrushev) |
| ProductName: | Automated pkg repackager |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 26-Nov-2012 19:47:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000BE7C | 0x0000C000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50763 |
.rdata | 0x0000D000 | 0x00000AE8 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.14255 |
.data | 0x0000E000 | 0x00AFFF78 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.9513 |
.rsrc | 0x00B0E000 | 0x00001428 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.24601 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.41409 | 636 | Latin 1 / Western European | UNKNOWN | RT_VERSION |
102 | 2.18548 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WINMM.dll |
Total processes
73
Monitored processes
39
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | C:\Windows\system32\cmd.exe /S /D /c" dir /B " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 848 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | Duxa's PS4 patch repackager 6.15.18.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 976 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\afolder\sc.exe" del "C:\Users\admin\AppData\Local\Temp\afolder\sc.exe" | C:\Windows\system32\cmd.exe | — | Duxa's PS4 patch repackager 6.15.18.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1348 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\afolder\sc.exe" del "C:\Users\admin\AppData\Local\Temp\afolder\sc.exe" | C:\Windows\system32\cmd.exe | — | Duxa's PS4 patch repackager 6.15.18.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1396 | attrib +h C:\Users\admin\AppData\Local\Temp\ztmp | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1712 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\afolder\libatrac9.dll" del "C:\Users\admin\AppData\Local\Temp\afolder\libatrac9.dll" | C:\Windows\system32\cmd.exe | — | Duxa's PS4 patch repackager 6.15.18.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1828 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\ztmp\tmp6697.exe" del "C:\Users\admin\AppData\Local\Temp\ztmp\tmp6697.exe" | C:\Windows\system32\cmd.exe | — | Duxa's PS4 patch repackager 6.15.18.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1928 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | Duxa's PS4 patch repackager 6.15.18.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2108 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\afolder\orbis-pub-cmd.exe" del "C:\Users\admin\AppData\Local\Temp\afolder\orbis-pub-cmd.exe" | C:\Windows\system32\cmd.exe | — | Duxa's PS4 patch repackager 6.15.18.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2128 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\ztmp\tmp878.bat" del "C:\Users\admin\AppData\Local\Temp\ztmp\tmp878.bat" | C:\Windows\system32\cmd.exe | — | Duxa's PS4 patch repackager 6.15.18.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
230
Read events
226
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3380) Robocopy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ResKit\Robocopy |
| Operation: | write | Name: | WaitTime |
Value: 30000 | |||
| (PID) Process: | (3380) Robocopy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ResKit\Robocopy |
| Operation: | write | Name: | RetryMax |
Value: 1000000 | |||
| (PID) Process: | (3380) Robocopy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ResKit\Robocopy |
| Operation: | write | Name: | JobDir |
Value: :: | |||
| (PID) Process: | (2412) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
Executable files
8
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3032 | Duxa's PS4 patch repackager 6.15.18.exe | C:\Users\admin\AppData\Local\Temp\afolder\orbis-pub-cmd.exe | executable | |
MD5:— | SHA256:— | |||
| 3032 | Duxa's PS4 patch repackager 6.15.18.exe | C:\Users\admin\AppData\Local\Temp\afolder\sc.exe | executable | |
MD5:— | SHA256:— | |||
| 3032 | Duxa's PS4 patch repackager 6.15.18.exe | C:\Users\admin\AppData\Local\Temp\afolder\di.exe | executable | |
MD5:— | SHA256:— | |||
| 3032 | Duxa's PS4 patch repackager 6.15.18.exe | C:\Users\admin\AppData\Local\Temp\ztmp\tmp6697.exe | text | |
MD5:3C52638971EAD82B5929D605C1314EE0 | SHA256:5614459EC05FDF6110FA8CE54C34E859671EEFFBA2B7BB4B1AD6C2C6706855AB | |||
| 3032 | Duxa's PS4 patch repackager 6.15.18.exe | C:\Users\admin\AppData\Local\Temp\afolder\trp_compare_default.css | text | |
MD5:C81F94F97FDE3589B73F45DD8DBD6579 | SHA256:F13A0E3A78EA423DD4883AA030C2E898F206EB0F08693E83A32198217253790B | |||
| 4012 | Robocopy.exe | C:\Users\admin\AppData\Local\Temp\afolder\ext\sc.exe | executable | |
MD5:— | SHA256:— | |||
| 3032 | Duxa's PS4 patch repackager 6.15.18.exe | C:\Users\admin\AppData\Local\Temp\afolder\gengp4.exe | executable | |
MD5:— | SHA256:— | |||
| 3032 | Duxa's PS4 patch repackager 6.15.18.exe | C:\Users\admin\AppData\Local\Temp\ztmp\tmp878.bat | html | |
MD5:— | SHA256:— | |||
| 3380 | Robocopy.exe | C:\Users\admin\AppData\Local\Temp\afolder\ext\di.exe | executable | |
MD5:— | SHA256:— | |||
| 3032 | Duxa's PS4 patch repackager 6.15.18.exe | C:\Users\admin\AppData\Local\Temp\afolder\libatrac9.dll | executable | |
MD5:C878A972781E4D5C70666C45B92A155A | SHA256:E1B1F3DB147D7996A5B1FBDDB2B7322E56F25BBF689F47C50638FD268FC1D3C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report