| File name: | flash.exe |
| Full analysis: | https://app.any.run/tasks/fc46c864-05d1-4e8b-8bac-6228ab14ed68 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 07:30:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 4B8DFFB217FCD9DBFD00BC3369A953D1 |
| SHA1: | FCAD89B72647B0FAE4E87DFD188AB2CAB6286248 |
| SHA256: | 95FEBAD12000E0777970D544616C0B4163424A28ED513E84CDBF1DED6BB1D1F4 |
| SSDEEP: | 12288:Z6Wq4aaE6KwyF5L0Y2D1PqLOmqJ3BcFCcZq8NFVUFWVnY+tYkZ/RoGjqU4gPK6NM:vthEVaPqLOz9BFcAiIWW+tHhRoMGChW |
MALICIOUS
Changes the autorun value in the registry
- flash.exe (PID: 2560)
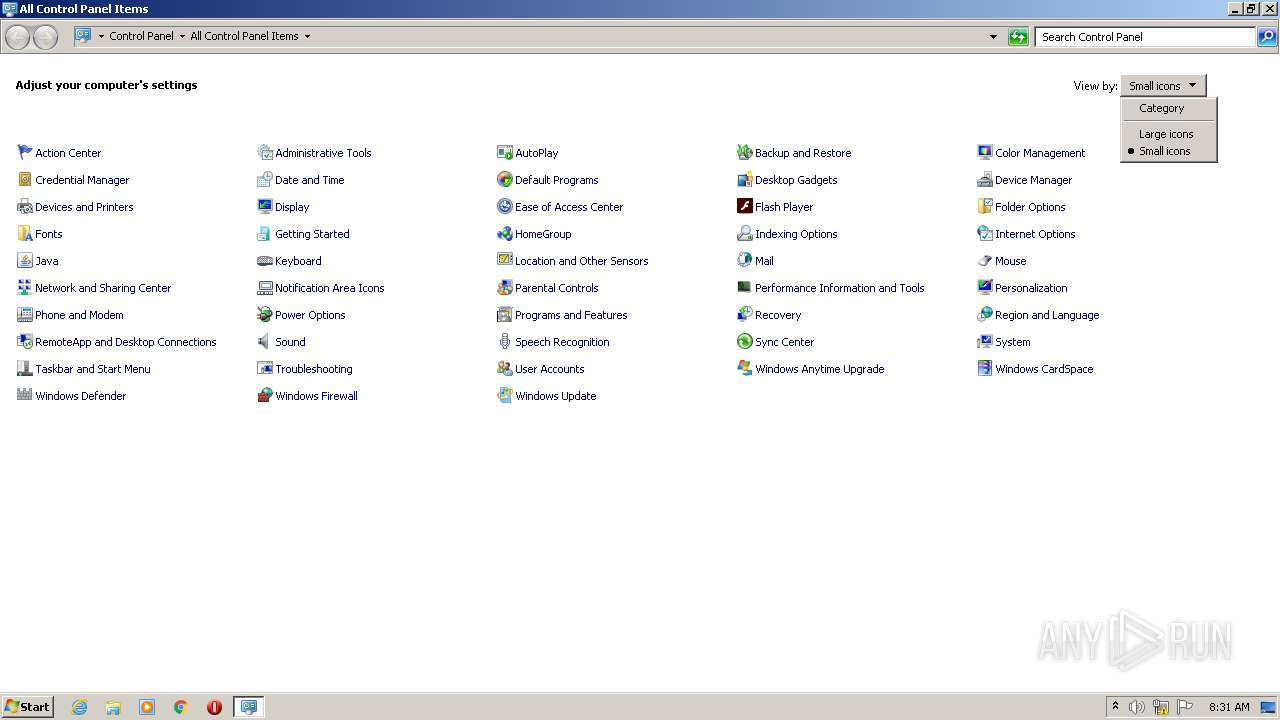
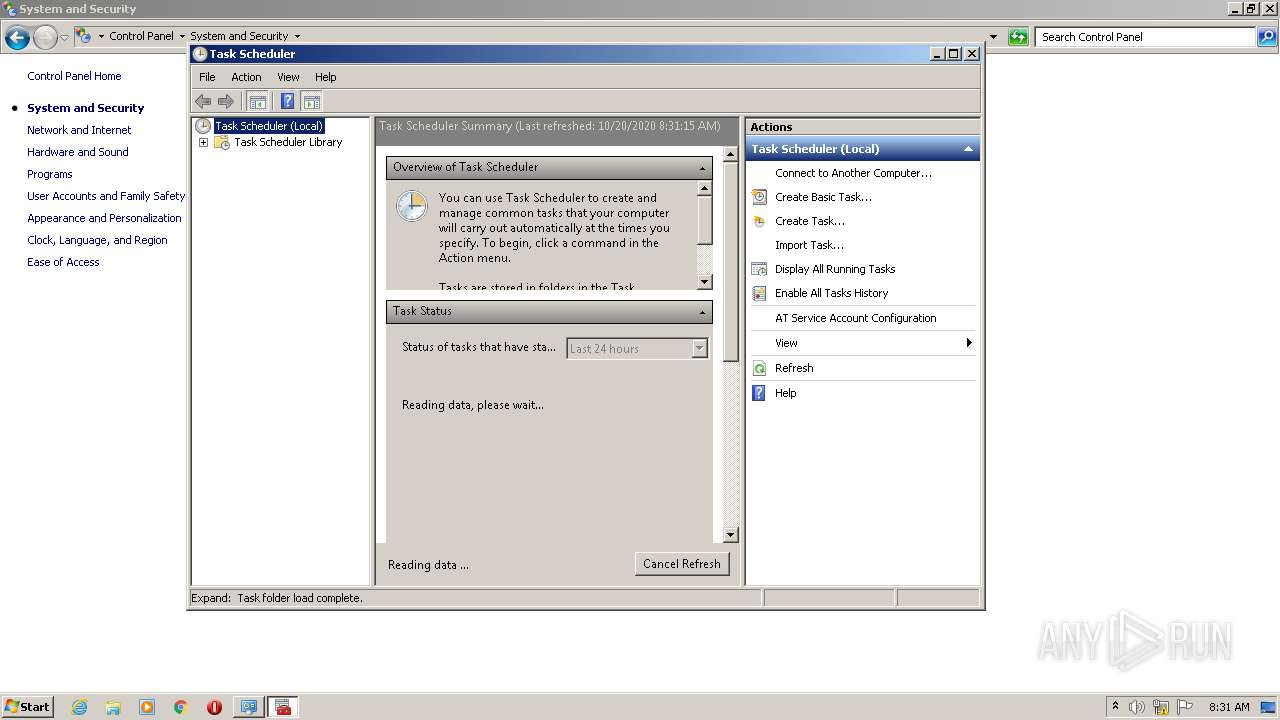
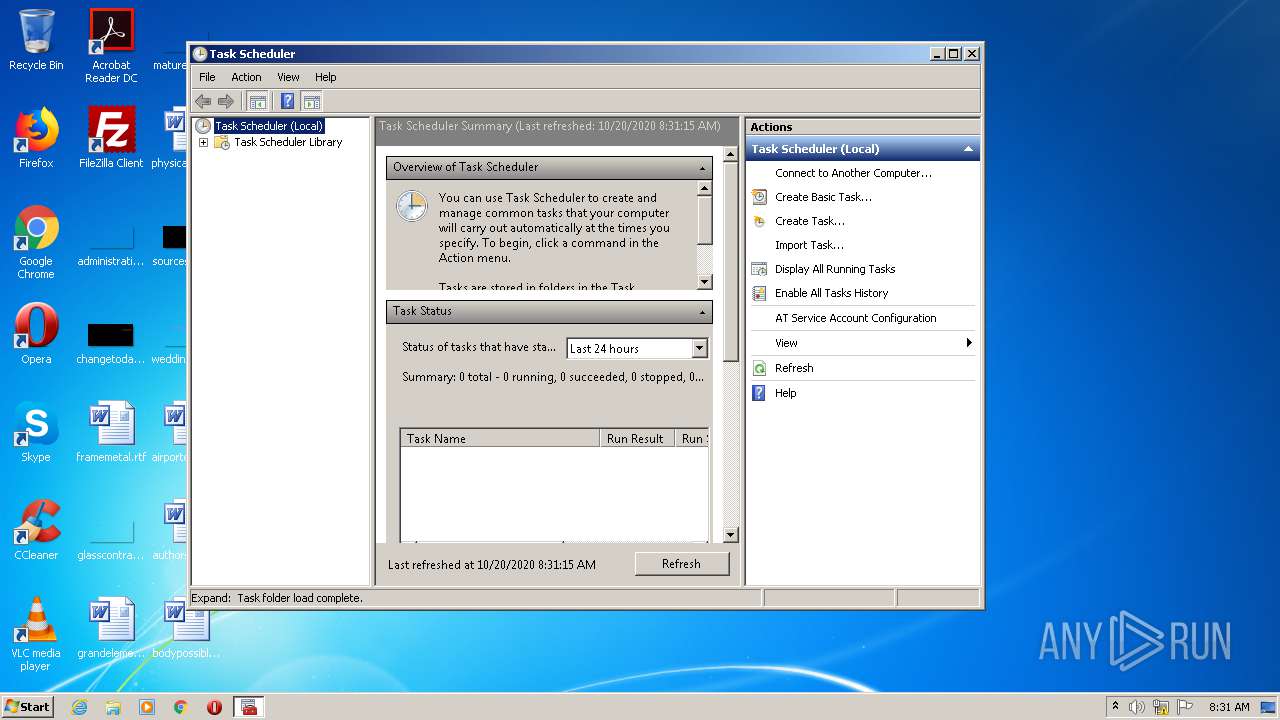
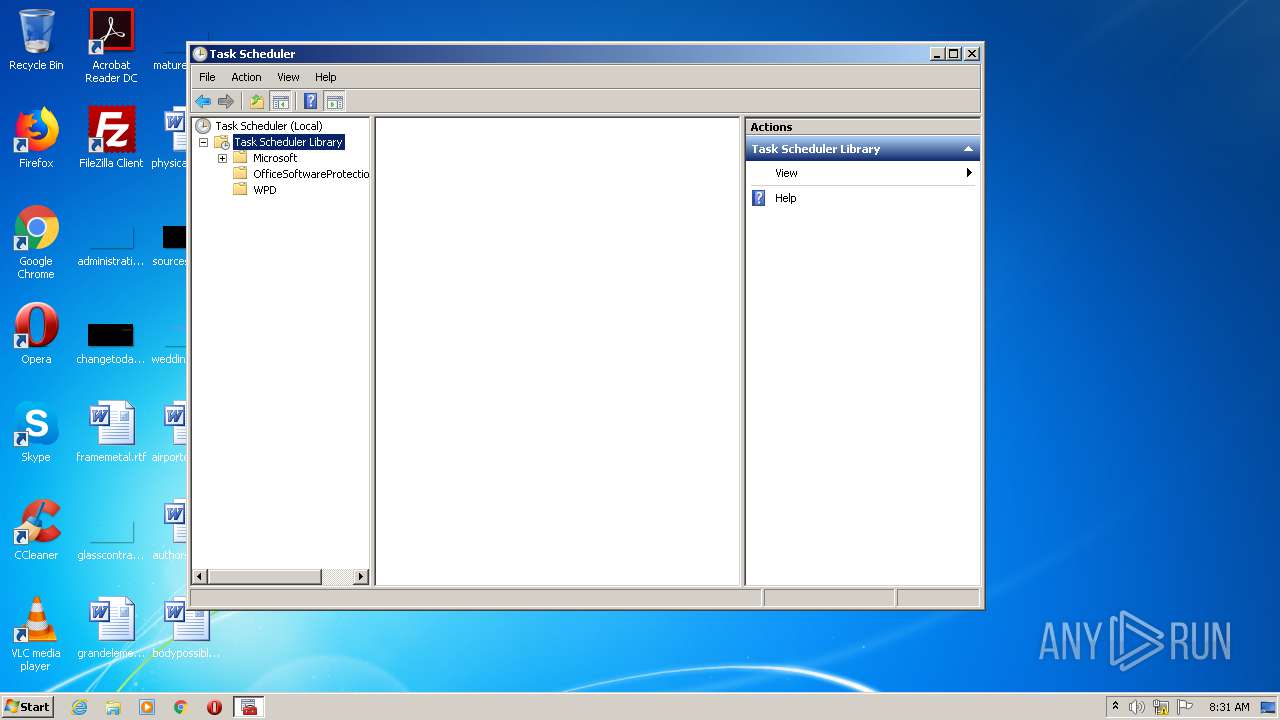
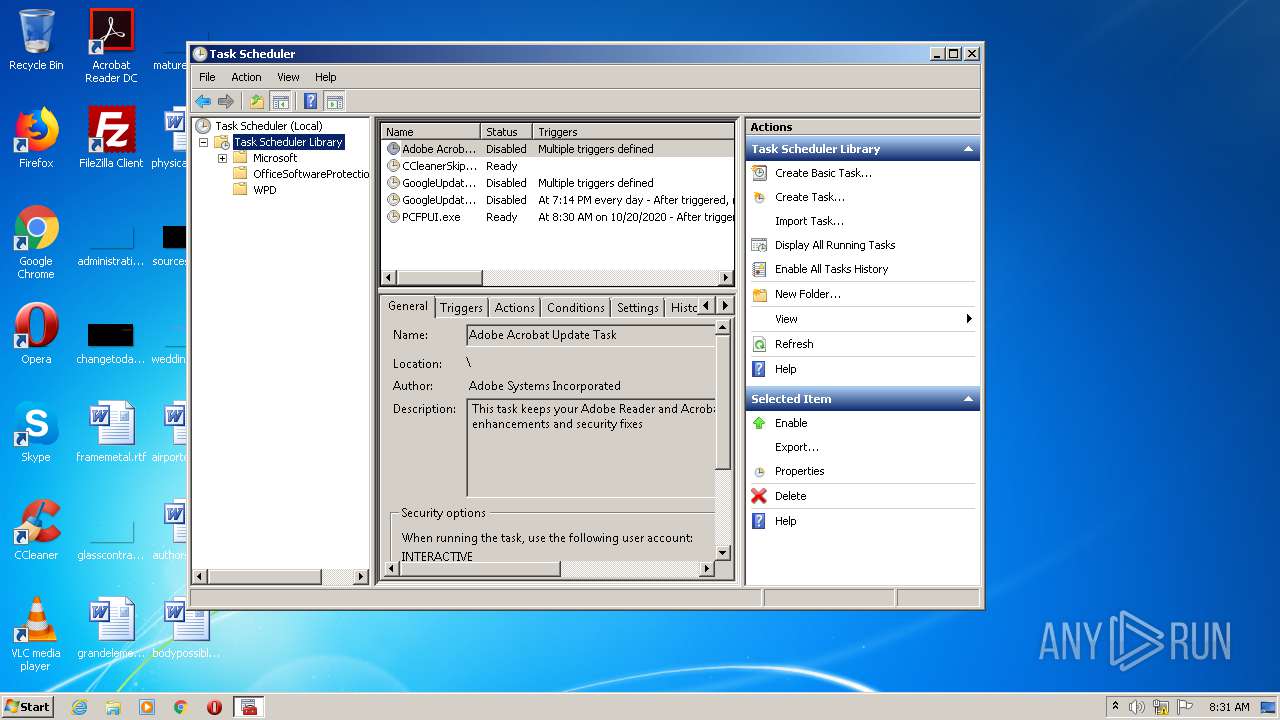
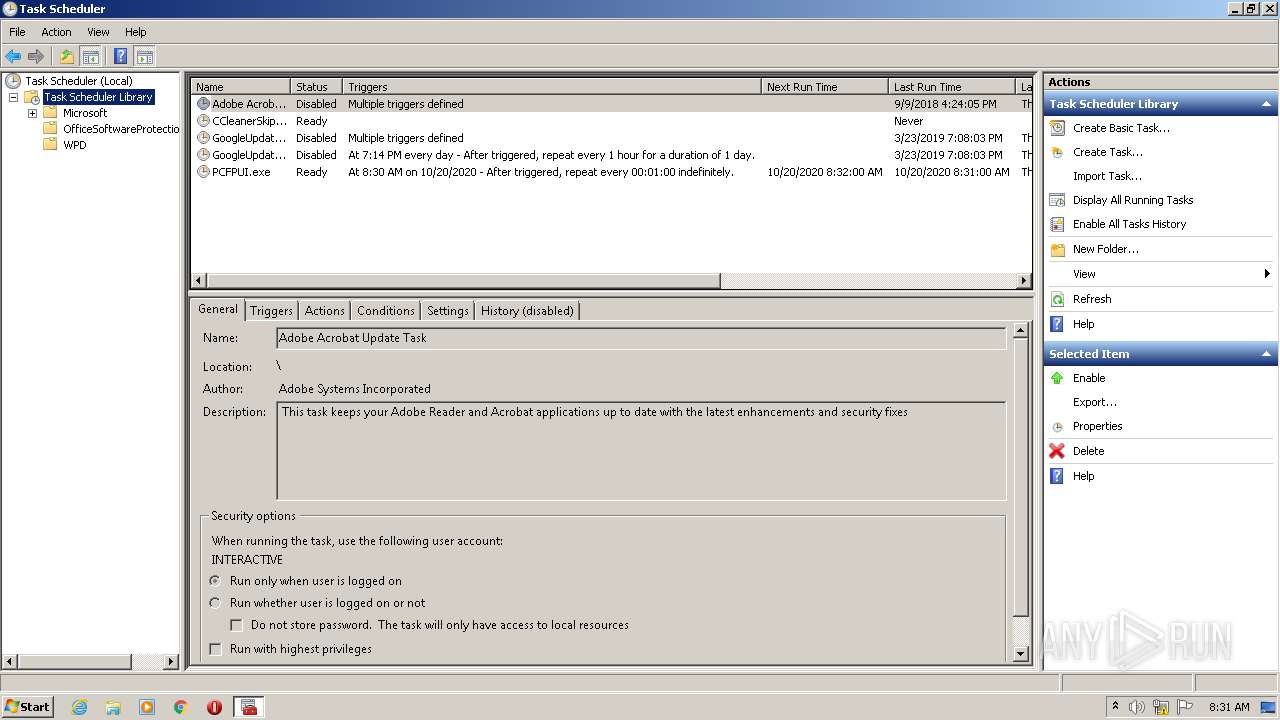
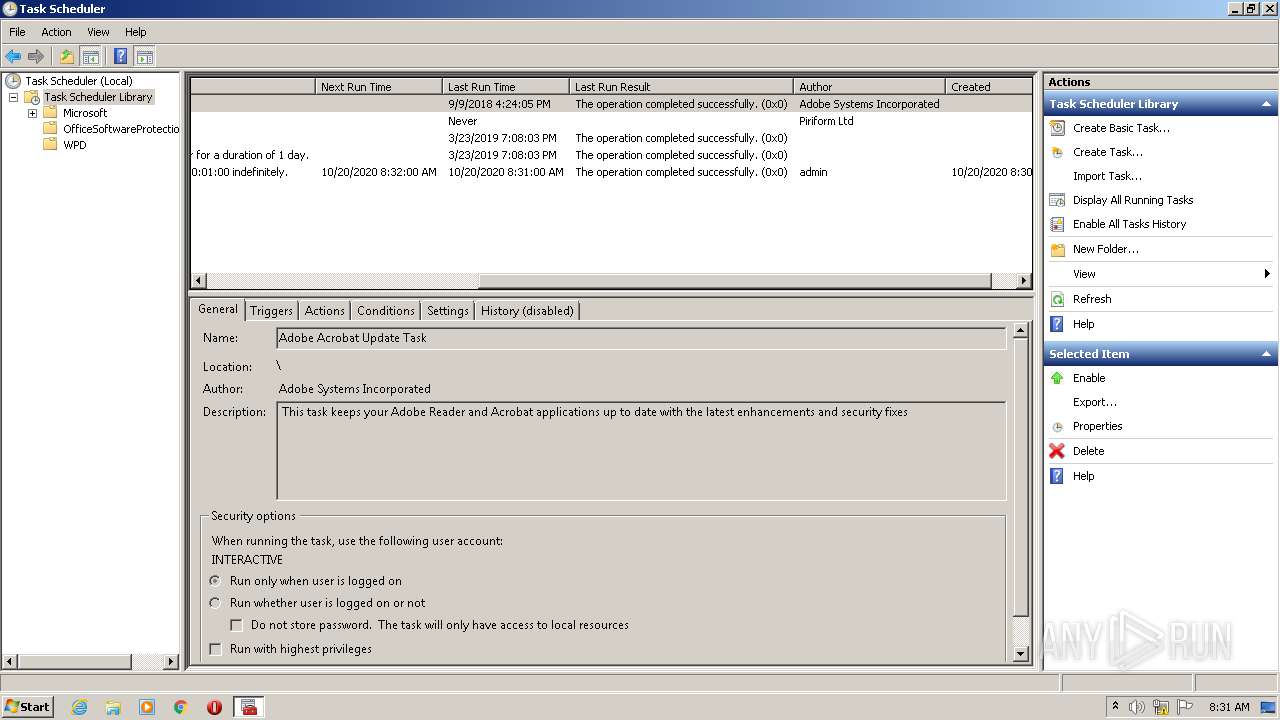
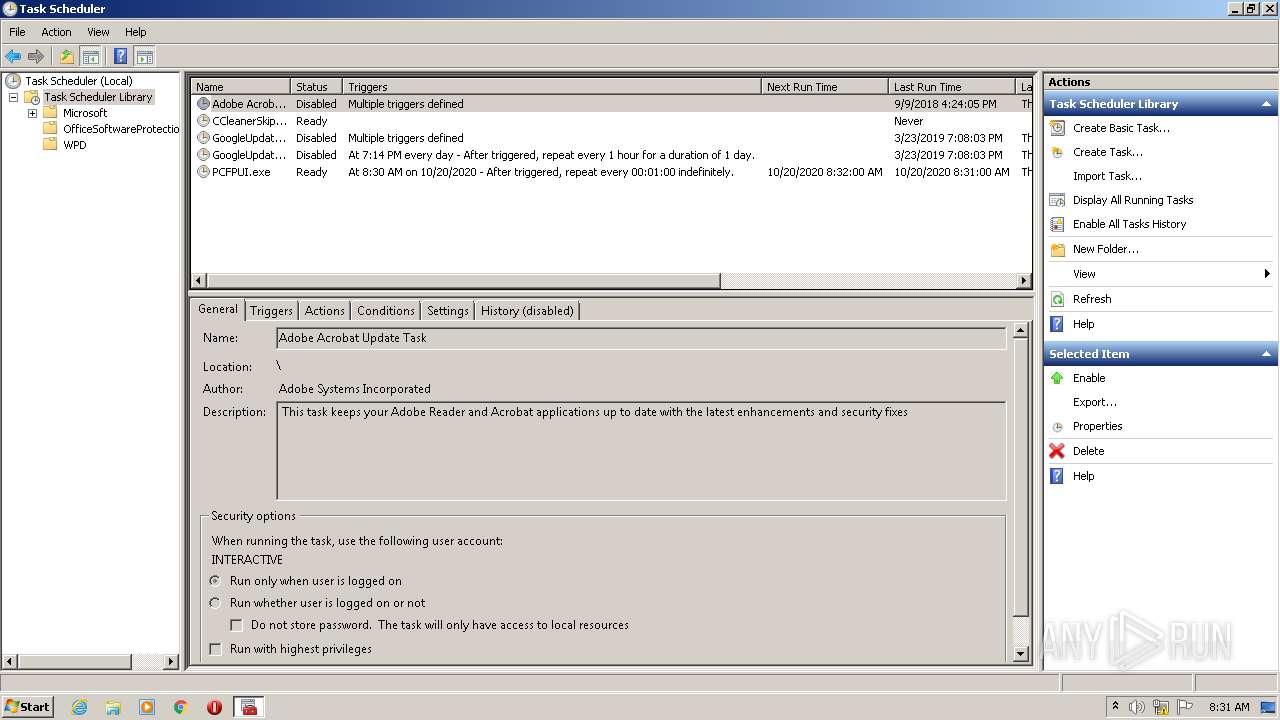
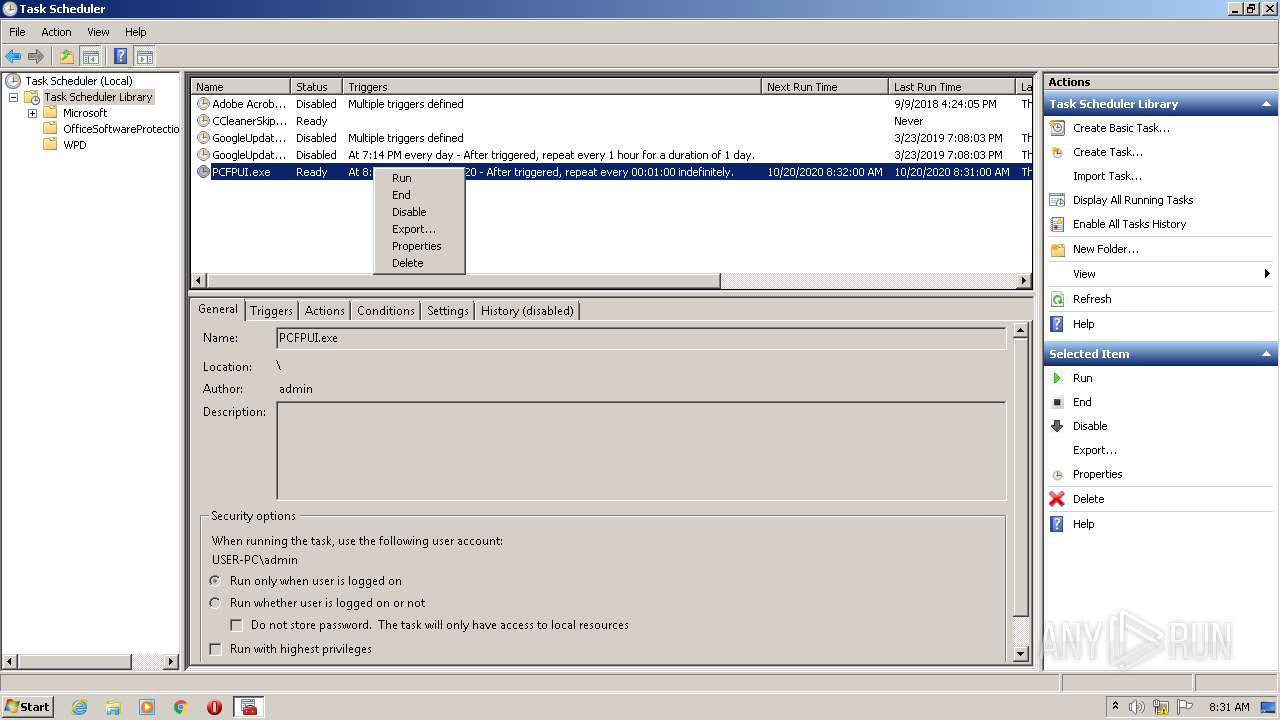
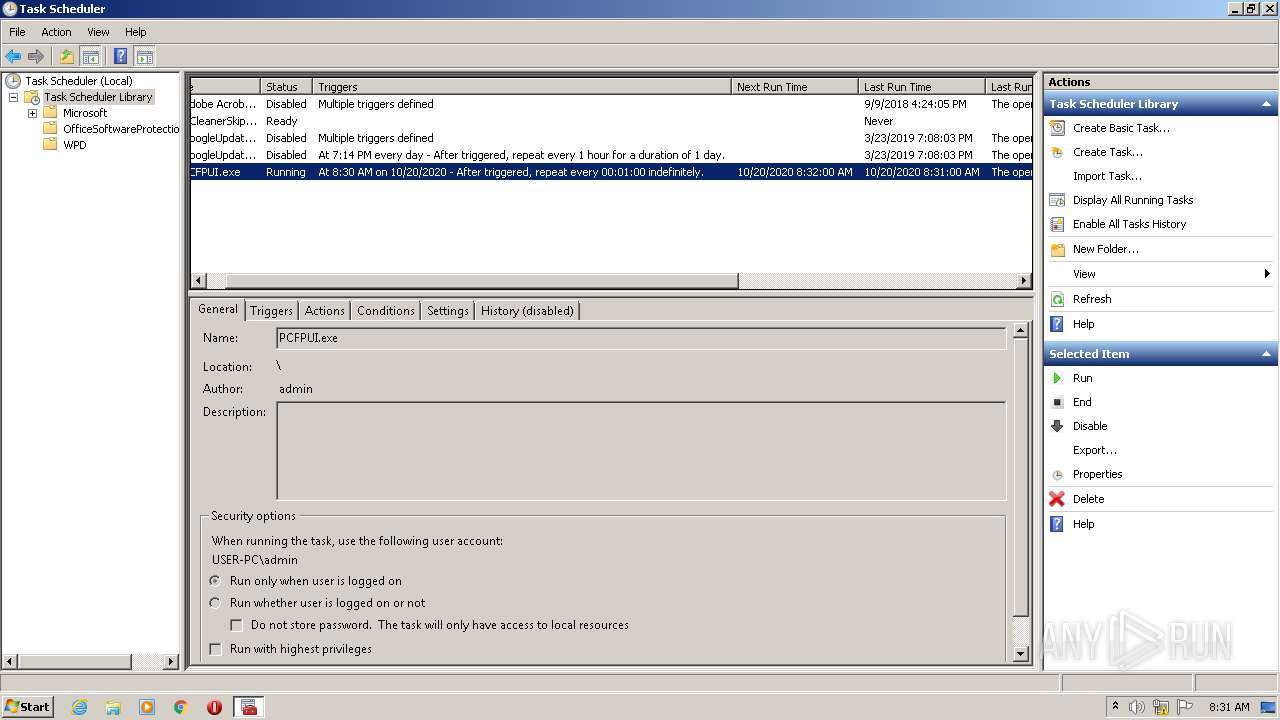
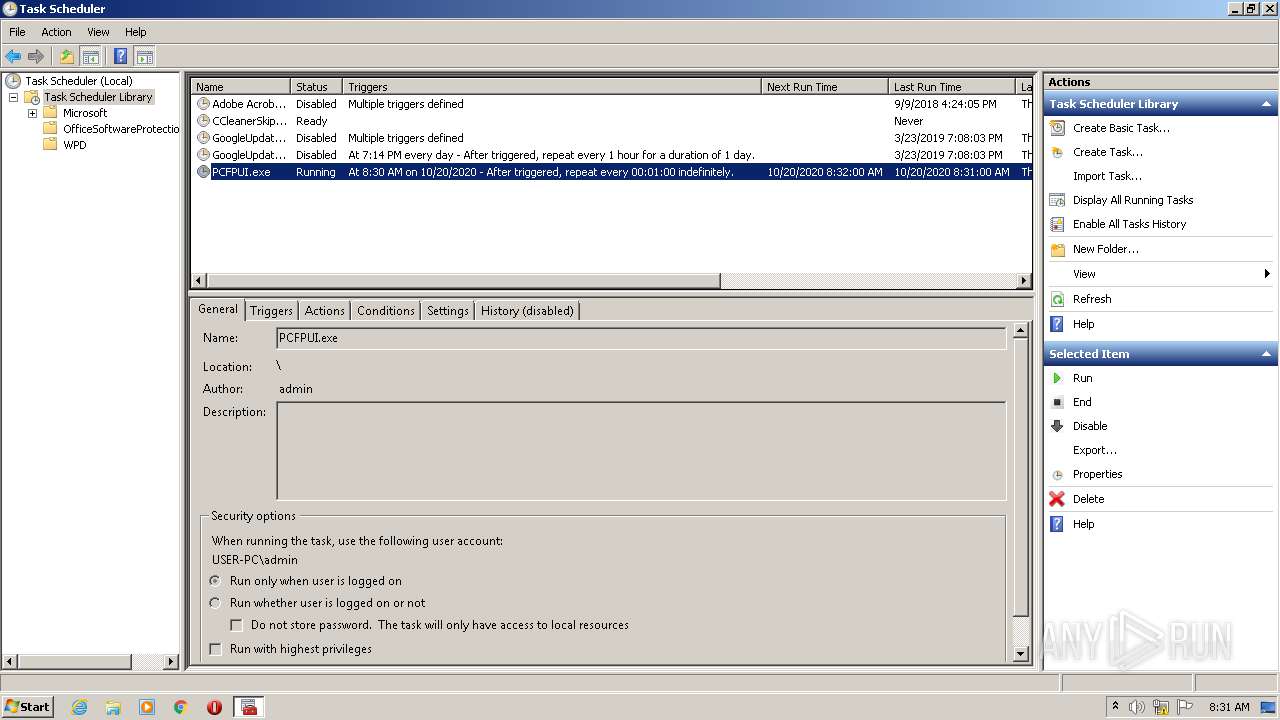
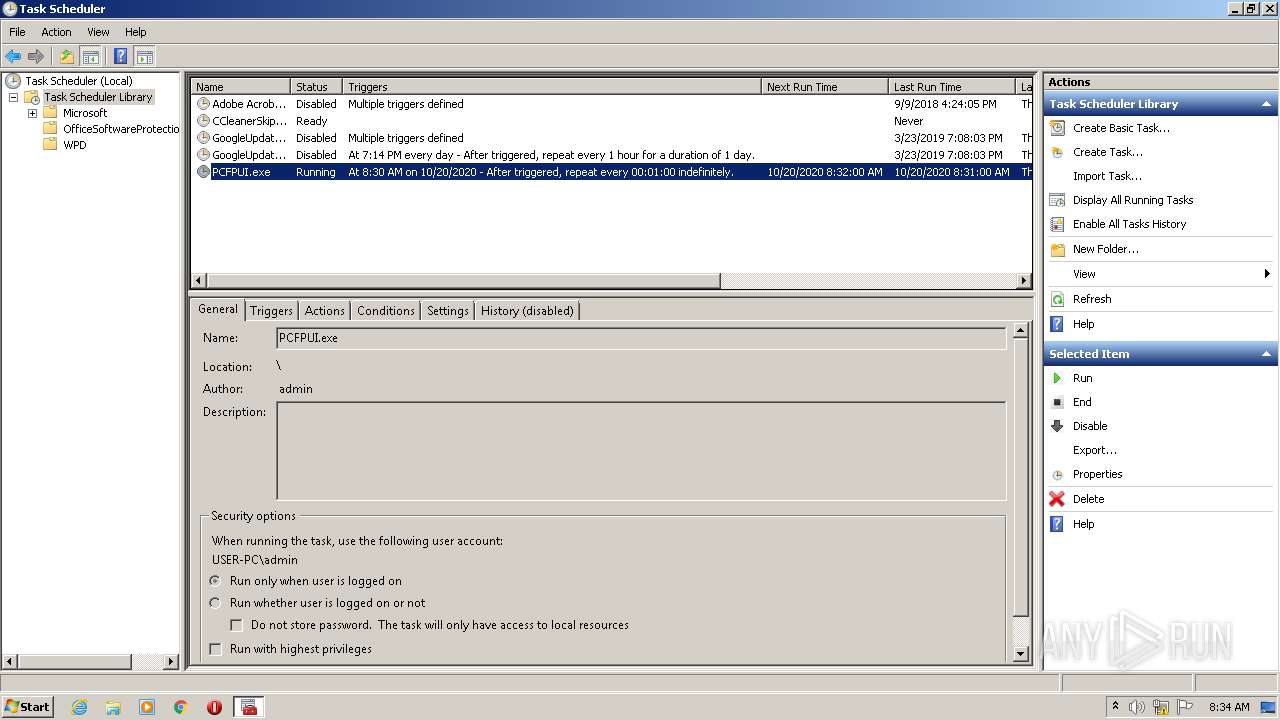
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4064)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3660)
- mmc.exe (PID: 2432)
Writes to a start menu file
- flash.exe (PID: 2560)
SUSPICIOUS
Creates files in the user directory
- flash.exe (PID: 2560)
Starts CMD.EXE for commands execution
- flash.exe (PID: 2560)
Executable content was dropped or overwritten
- flash.exe (PID: 2560)
Executes scripts
- flash.exe (PID: 2560)
Executed via Task Scheduler
- WEGPWL.exe (PID: 932)
- WEGPWL.exe (PID: 2436)
- WEGPWL.exe (PID: 2008)
- WEGPWL.exe (PID: 3852)
- WEGPWL.exe (PID: 896)
- WEGPWL.exe (PID: 1836)
INFO
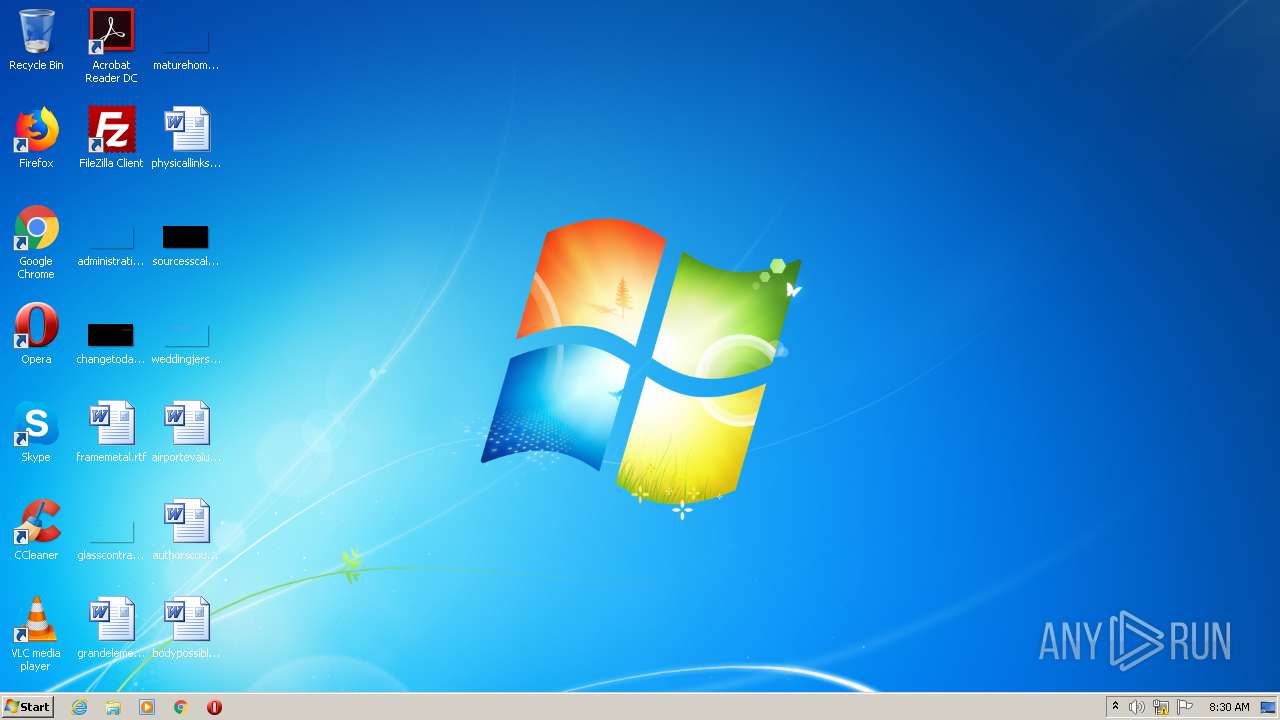
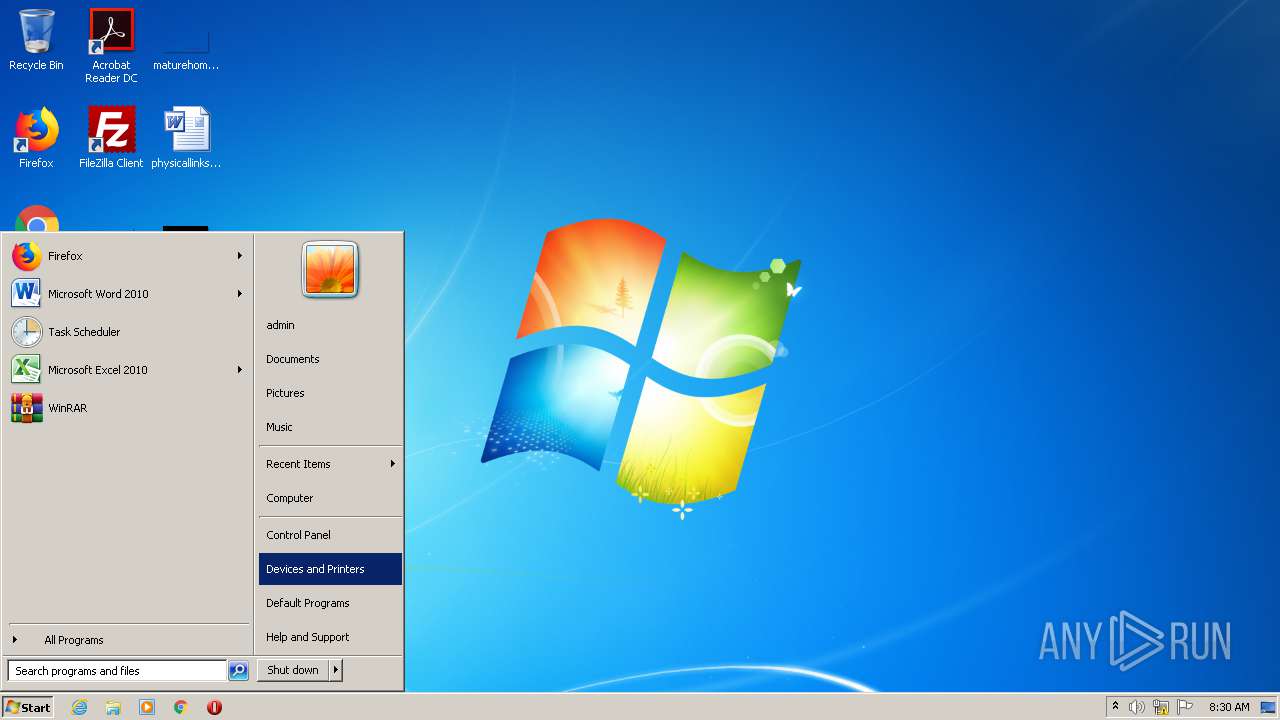
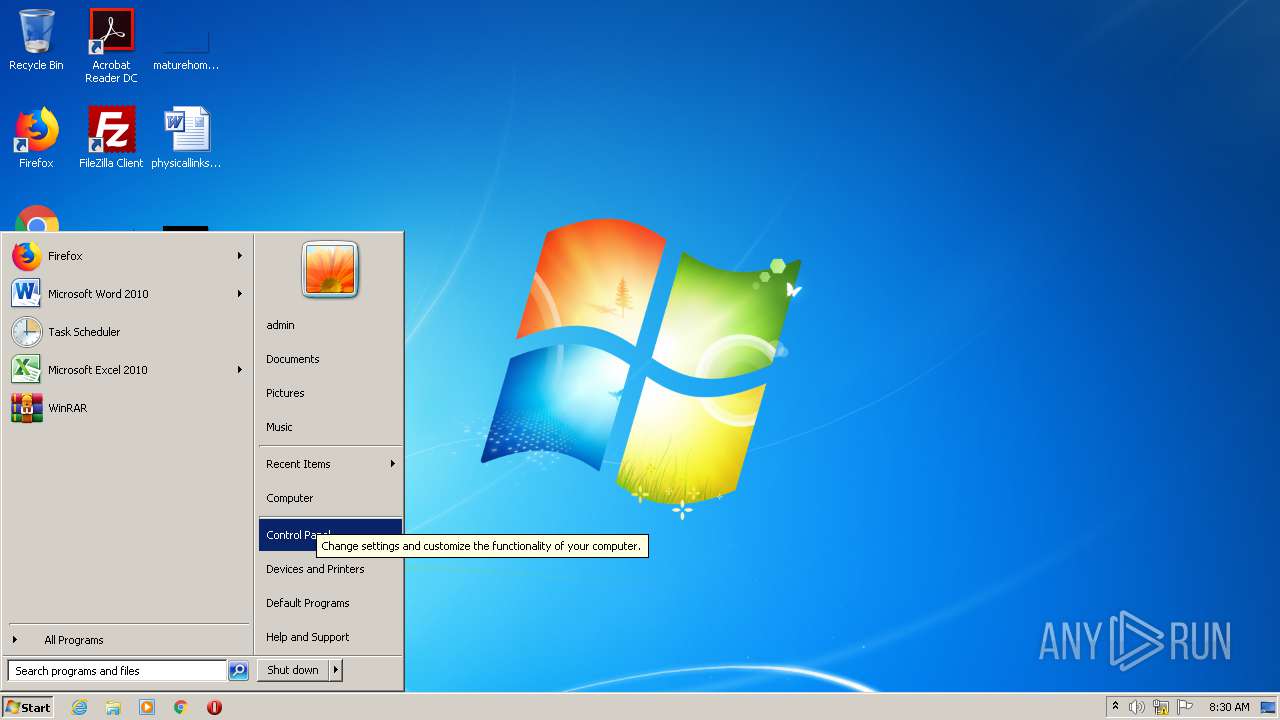
Manual execution by user
- mmc.exe (PID: 2432)
- mmc.exe (PID: 2400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | AutoIt3 compiled script executable (88.1) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (4.6) |
| .exe | | | Win32 EXE Yoda's Crypter (4.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.1) |
| .exe | | | Win32 Executable (generic) (0.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:01:29 22:32:28+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 274432 |
| InitializedDataSize: | 299008 |
| UninitializedDataSize: | 749568 |
| EntryPoint: | 0xf9f00 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.8.1 |
| ProductVersionNumber: | 3.3.8.1 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileDescription: | - |
| FileVersion: | 3, 3, 8, 1 |
| CompiledScript: | AutoIt v3 Script: 3, 3, 8, 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Jan-2012 21:32:28 |
| Detected languages: |
|
| FileDescription: | - |
| FileVersion: | 3, 3, 8, 1 |
| CompiledScript: | AutoIt v3 Script: 3, 3, 8, 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 29-Jan-2012 21:32:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x000B7000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x000B8000 | 0x00043000 | 0x00042200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92944 |
.rsrc | 0x000FB000 | 0x00049000 | 0x00048A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.53907 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.01246 | 620 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.66371 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 5.37136 | 3752 | UNKNOWN | English - United Kingdom | RT_ICON |
5 | 4.85578 | 2216 | UNKNOWN | English - United Kingdom | RT_ICON |
6 | 3.42535 | 1384 | UNKNOWN | English - United Kingdom | RT_ICON |
7 | 7.78706 | 1328 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 7.80852 | 1680 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 7.76552 | 1232 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 7.62498 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.DLL |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
Total processes
52
Monitored processes
12
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | C:\Users\admin\AppData\Roaming\Windata\WEGPWL.exe | C:\Users\admin\AppData\Roaming\Windata\WEGPWL.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 932 | C:\Users\admin\AppData\Roaming\Windata\WEGPWL.exe | C:\Users\admin\AppData\Roaming\Windata\WEGPWL.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 1836 | C:\Users\admin\AppData\Roaming\Windata\WEGPWL.exe | C:\Users\admin\AppData\Roaming\Windata\WEGPWL.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 2008 | C:\Users\admin\AppData\Roaming\Windata\WEGPWL.exe | C:\Users\admin\AppData\Roaming\Windata\WEGPWL.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 2400 | "C:\Windows\system32\mmc.exe" C:\Windows\system32\taskschd.msc | C:\Windows\system32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | "C:\Windows\system32\mmc.exe" C:\Windows\system32\taskschd.msc | C:\Windows\system32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2436 | C:\Users\admin\AppData\Roaming\Windata\WEGPWL.exe | C:\Users\admin\AppData\Roaming\Windata\WEGPWL.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 2560 | "C:\Users\admin\AppData\Local\Temp\flash.exe" | C:\Users\admin\AppData\Local\Temp\flash.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 2824 | WSCript C:\Users\admin\AppData\Local\Temp\PCFPUI.vbs | C:\Windows\system32\WSCript.exe | — | flash.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3660 | schtasks /create /tn PCFPUI.exe /tr C:\Users\admin\AppData\Roaming\Windata\WEGPWL.exe /sc minute /mo 1 | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
563
Read events
555
Write events
7
Delete events
1
Modification events
| (PID) Process: | (2560) flash.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | PCFPUI |
Value: "C:\Users\admin\AppData\Roaming\Windata\WEGPWL.exe" | |||
| (PID) Process: | (2560) flash.exe | Key: | HKEY_CURRENT_USER\Software\Win32 |
| Operation: | write | Name: | PCFPUI |
Value: 2824 | |||
| (PID) Process: | (2432) mmc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MMC\SnapIns\FX:{c7b8fb06-bfe1-4c2e-9217-7a69a95bbac4} |
| Operation: | write | Name: | HelpTopic |
Value: C:\Windows\Help\taskscheduler.chm | |||
| (PID) Process: | (2432) mmc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MMC\SnapIns\FX:{c7b8fb06-bfe1-4c2e-9217-7a69a95bbac4} |
| Operation: | write | Name: | LinkedHelpTopics |
Value: C:\Windows\Help\taskscheduler.chm | |||
| (PID) Process: | (2432) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2432) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File1 |
Value: C:\Windows\system32\taskschd.msc | |||
| (PID) Process: | (2432) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File2 |
Value: C:\Windows\system32\certmgr.msc | |||
| (PID) Process: | (2432) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File3 |
Value: C:\Windows\system32\compmgmt.msc | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2560 | flash.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\PCFPUI.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2560 | flash.exe | C:\Users\admin\AppData\Roaming\Windata\WEGPWL.exe | executable | |
MD5:— | SHA256:— | |||
| 2560 | flash.exe | C:\Users\admin\AppData\Local\Temp\PCFPUI.vbs | text | |
MD5:— | SHA256:— | |||
| 2432 | mmc.exe | C:\Users\admin\AppData\Roaming\Microsoft\MMC\taskschd | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|