| URL: | codex.lol |
| Full analysis: | https://app.any.run/tasks/b011d152-04b4-4ef8-9b12-e2eb1dc1e066 |
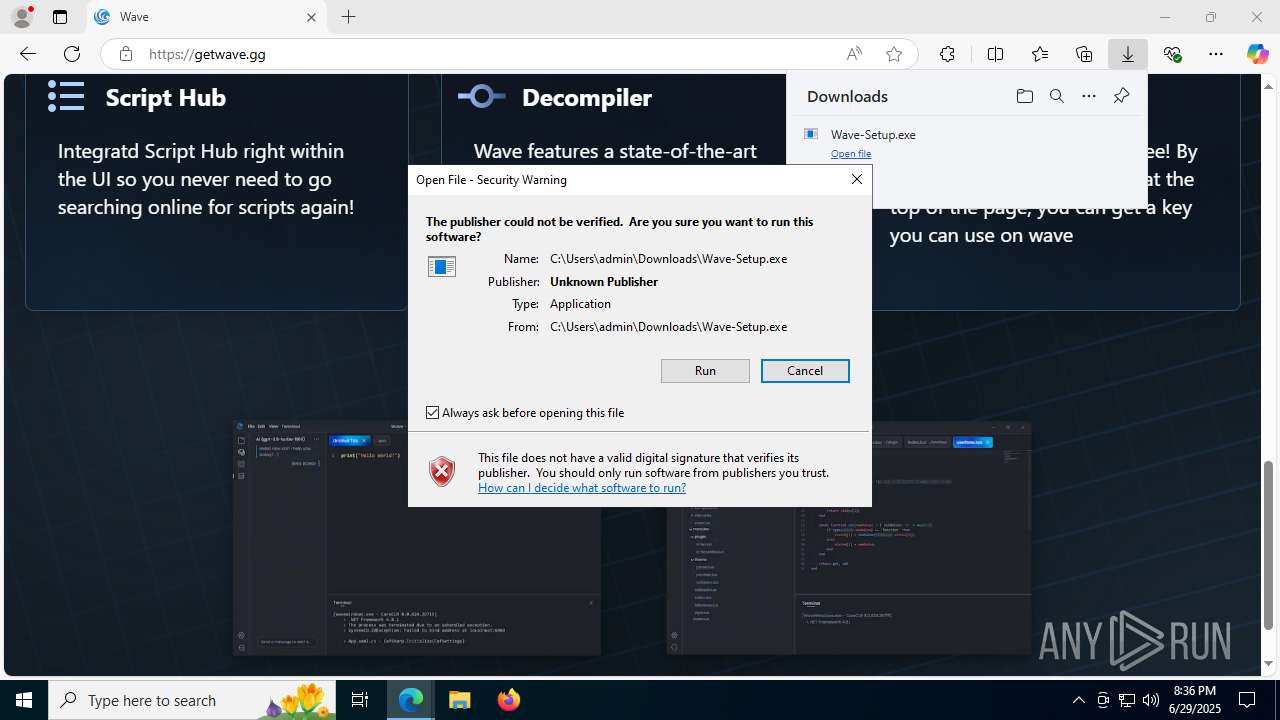
| Verdict: | Malicious activity |
| Analysis date: | June 29, 2025, 20:34:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EA145CAC6A0FB3D743474F779E3474F5 |
| SHA1: | 89E07DB8CC9CEE0A198995D113CA53D011D391FD |
| SHA256: | 95FB1D3B9FA2A0E9DB5BCB45C5C28ED07F952D99FC45BB2C7A37D1FF67F9DE81 |
| SSDEEP: | 3:3:3 |
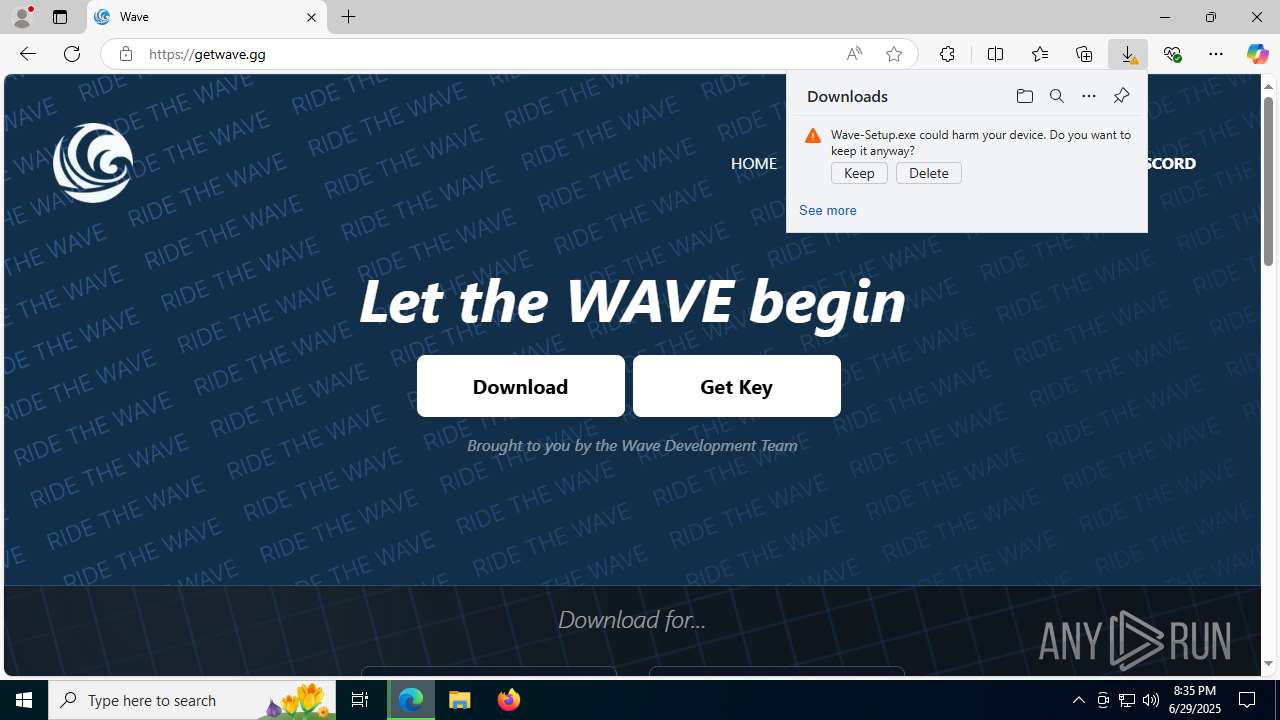
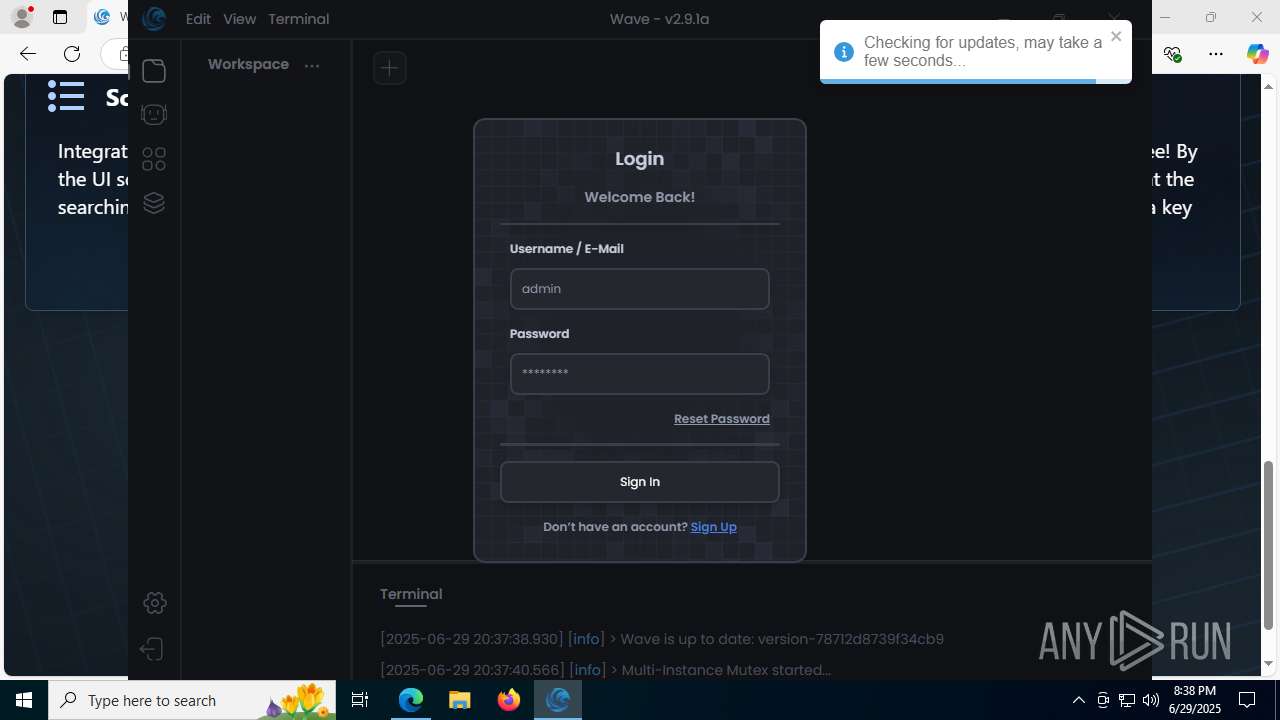
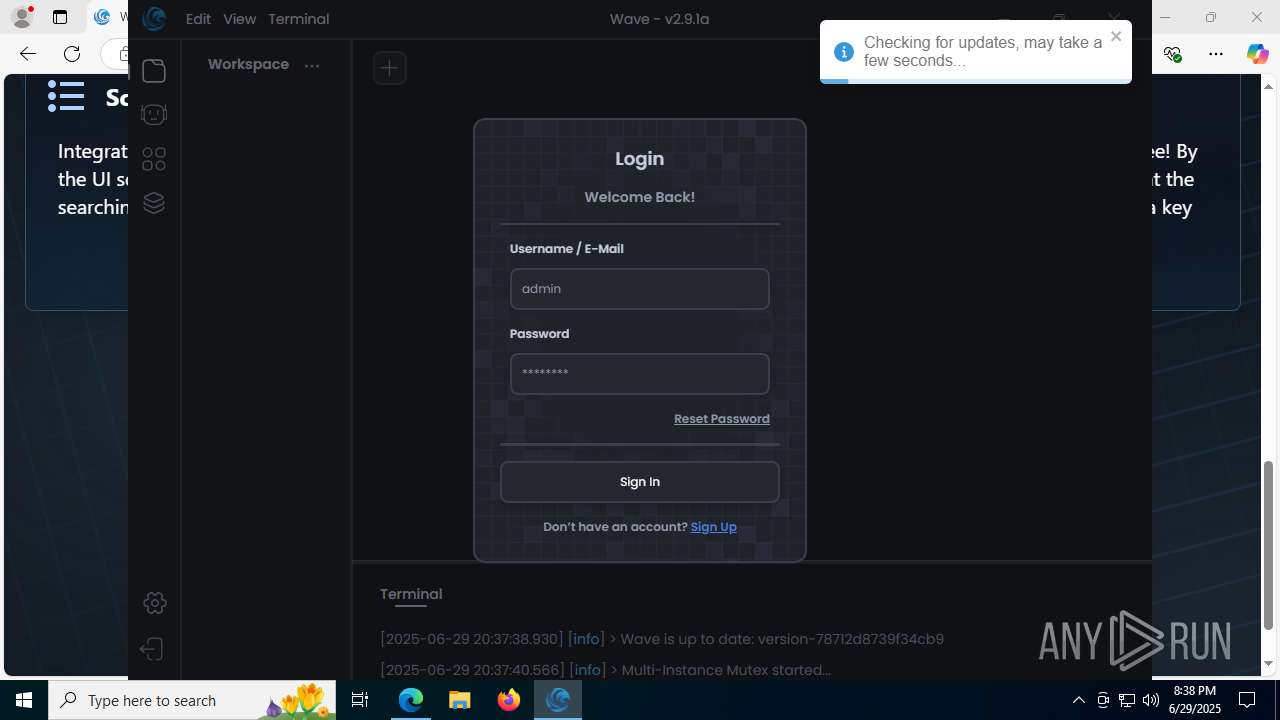
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 2180)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- Wave-Setup.exe (PID: 7108)
The process creates files with name similar to system file names
- Wave-Setup.exe (PID: 7108)
Starts CMD.EXE for commands execution
- Wave-Setup.exe (PID: 7108)
- powershell.exe (PID: 2180)
- Wave.exe (PID: 1932)
- Wave.exe (PID: 7644)
Get information on the list of running processes
- Wave-Setup.exe (PID: 7108)
- cmd.exe (PID: 7564)
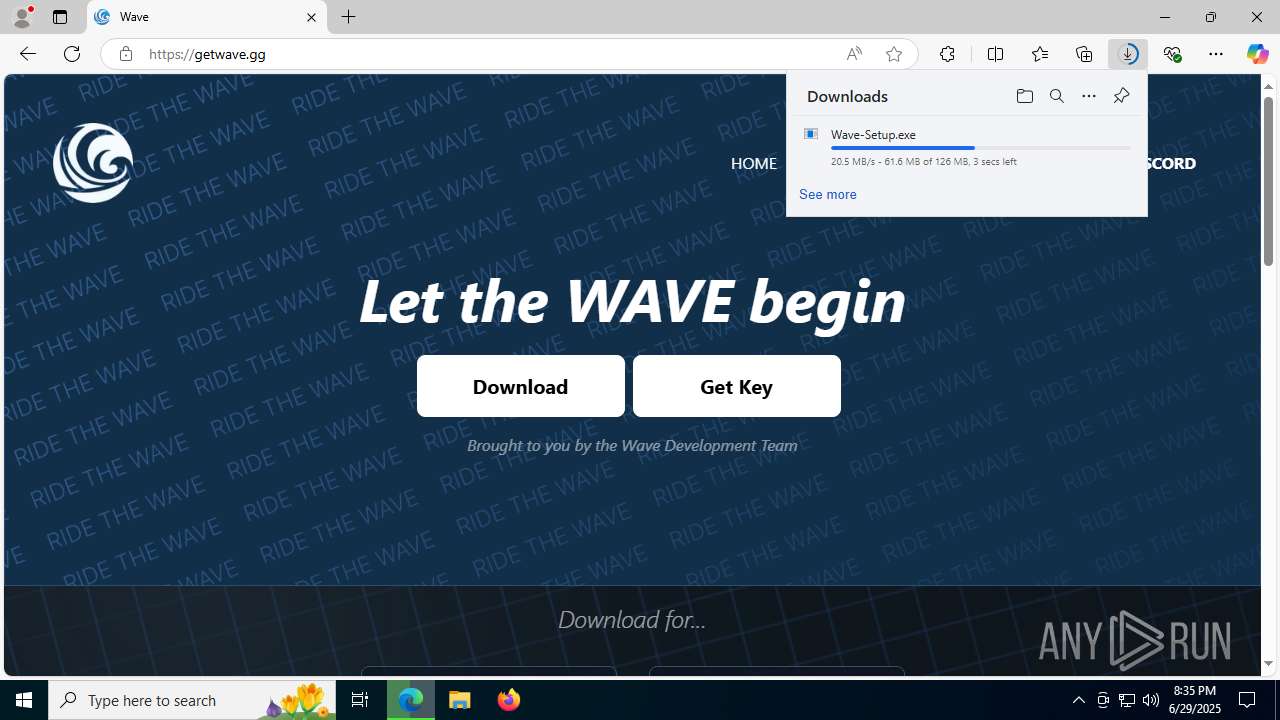
Executable content was dropped or overwritten
- Wave-Setup.exe (PID: 7108)
- Wave.exe (PID: 7644)
Reads security settings of Internet Explorer
- Wave-Setup.exe (PID: 7108)
- Wave.exe (PID: 7644)
Drops 7-zip archiver for unpacking
- Wave-Setup.exe (PID: 7108)
Process drops legitimate windows executable
- Wave-Setup.exe (PID: 7108)
Creates a software uninstall entry
- Wave-Setup.exe (PID: 7108)
There is functionality for taking screenshot (YARA)
- Wave-Setup.exe (PID: 7108)
Application launched itself
- Wave.exe (PID: 1932)
- Wave.exe (PID: 7644)
Starts process via Powershell
- powershell.exe (PID: 2180)
The executable file from the user directory is run by the CMD process
- Wave.exe (PID: 7644)
Executing commands from a ".bat" file
- powershell.exe (PID: 2180)
- Wave.exe (PID: 1932)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 32)
Starts application with an unusual extension
- cmd.exe (PID: 7820)
Detected use of alternative data streams (AltDS)
- wave-luau.exe (PID: 7944)
INFO
Checks supported languages
- identity_helper.exe (PID: 7832)
- Wave-Setup.exe (PID: 7108)
- Wave.exe (PID: 5008)
- Wave.exe (PID: 1932)
- Wave.exe (PID: 5548)
- chcp.com (PID: 3948)
- Wave.exe (PID: 7644)
- Wave.exe (PID: 7196)
- Wave.exe (PID: 7212)
- wave-luau.exe (PID: 7944)
- Wave.exe (PID: 7312)
- ClientManager.exe (PID: 4024)
- identity_helper.exe (PID: 6940)
Application launched itself
- msedge.exe (PID: 2192)
- msedge.exe (PID: 5780)
Reads the computer name
- identity_helper.exe (PID: 7832)
- Wave-Setup.exe (PID: 7108)
- Wave.exe (PID: 5548)
- Wave.exe (PID: 1932)
- Wave.exe (PID: 5008)
- Wave.exe (PID: 7644)
- Wave.exe (PID: 7196)
- Wave.exe (PID: 7212)
- identity_helper.exe (PID: 6940)
- ClientManager.exe (PID: 4024)
Reads Environment values
- identity_helper.exe (PID: 7832)
- Wave.exe (PID: 1932)
- Wave.exe (PID: 7644)
- identity_helper.exe (PID: 6940)
Executable content was dropped or overwritten
- msedge.exe (PID: 2192)
Reads the software policy settings
- slui.exe (PID: 5924)
The sample compiled with english language support
- msedge.exe (PID: 2192)
- Wave-Setup.exe (PID: 7108)
Checks proxy server information
- slui.exe (PID: 5924)
- Wave.exe (PID: 1932)
- Wave.exe (PID: 7644)
Create files in a temporary directory
- Wave-Setup.exe (PID: 7108)
- Wave.exe (PID: 1932)
- Wave.exe (PID: 7644)
Creates files or folders in the user directory
- Wave-Setup.exe (PID: 7108)
- Wave.exe (PID: 7212)
- Wave.exe (PID: 7644)
- Wave.exe (PID: 1932)
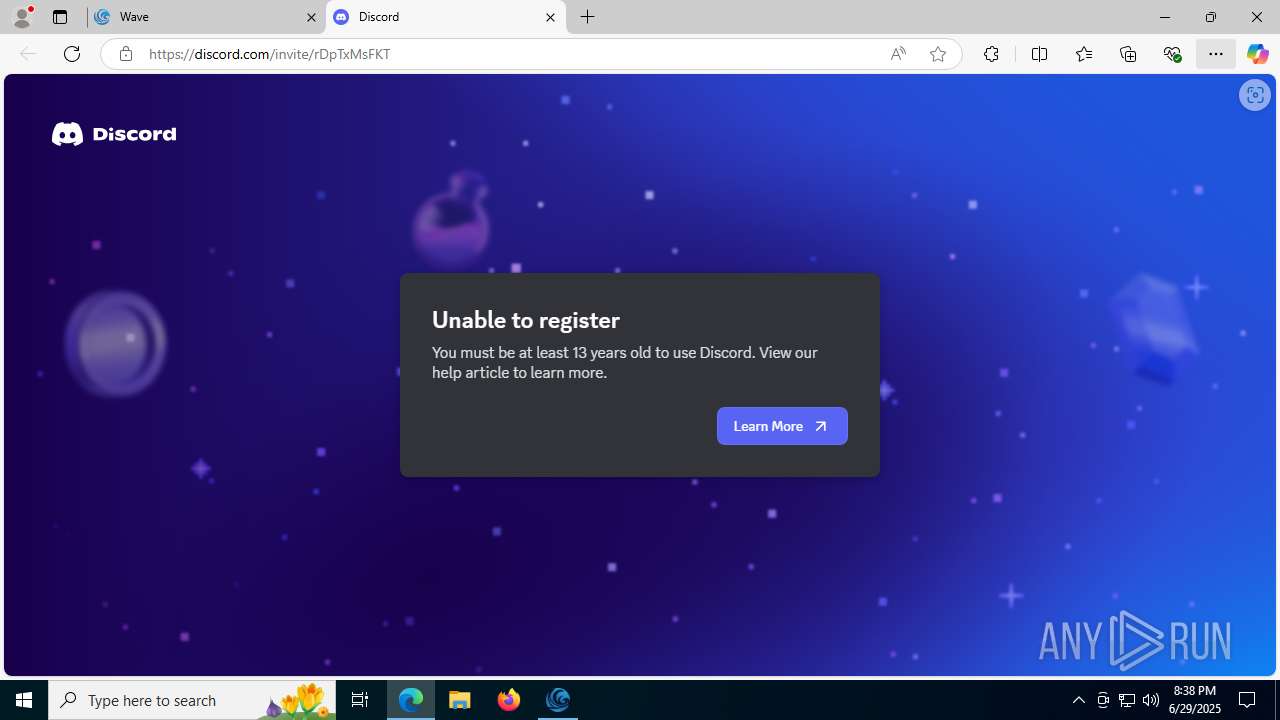
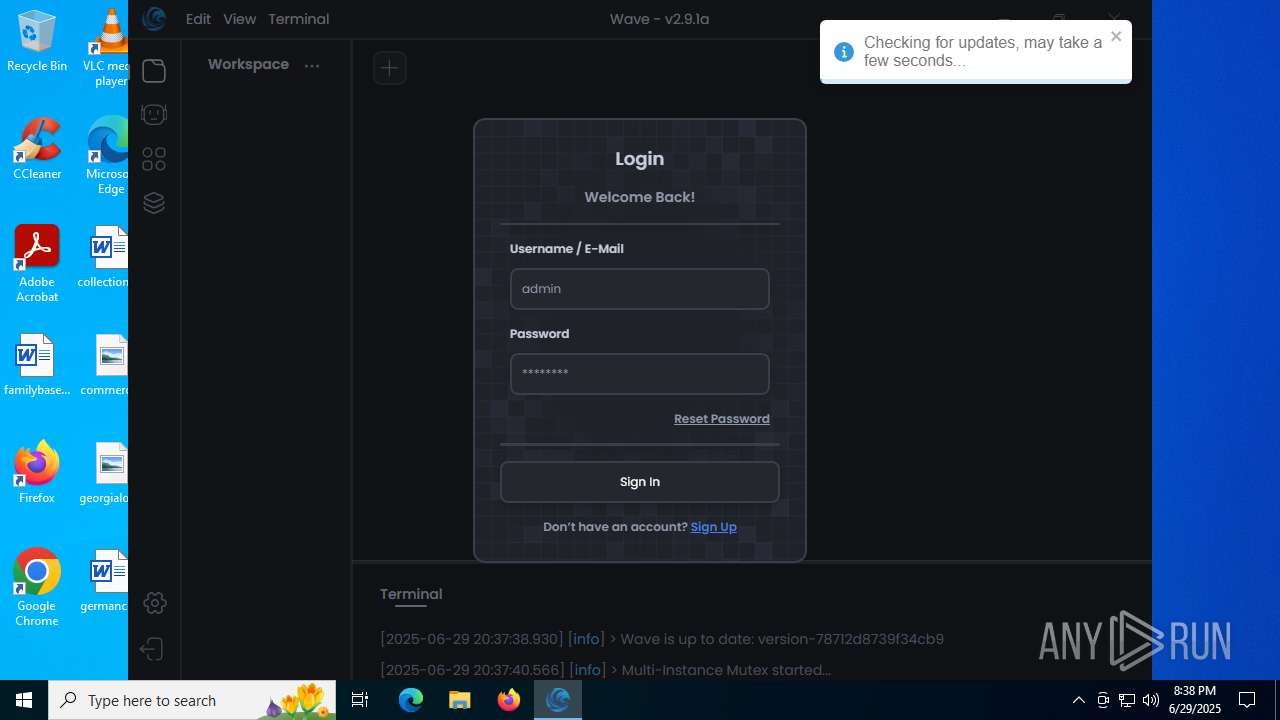
Manual execution by a user
- Wave.exe (PID: 1932)
Reads product name
- Wave.exe (PID: 1932)
- Wave.exe (PID: 7644)
Reads the machine GUID from the registry
- Wave.exe (PID: 1932)
- Wave.exe (PID: 7644)
Drops encrypted JS script (Microsoft Script Encoder)
- Wave.exe (PID: 1932)
- Wave.exe (PID: 7644)
Changes the display of characters in the console
- cmd.exe (PID: 7820)
Process checks computer location settings
- Wave.exe (PID: 7644)
- Wave.exe (PID: 7312)
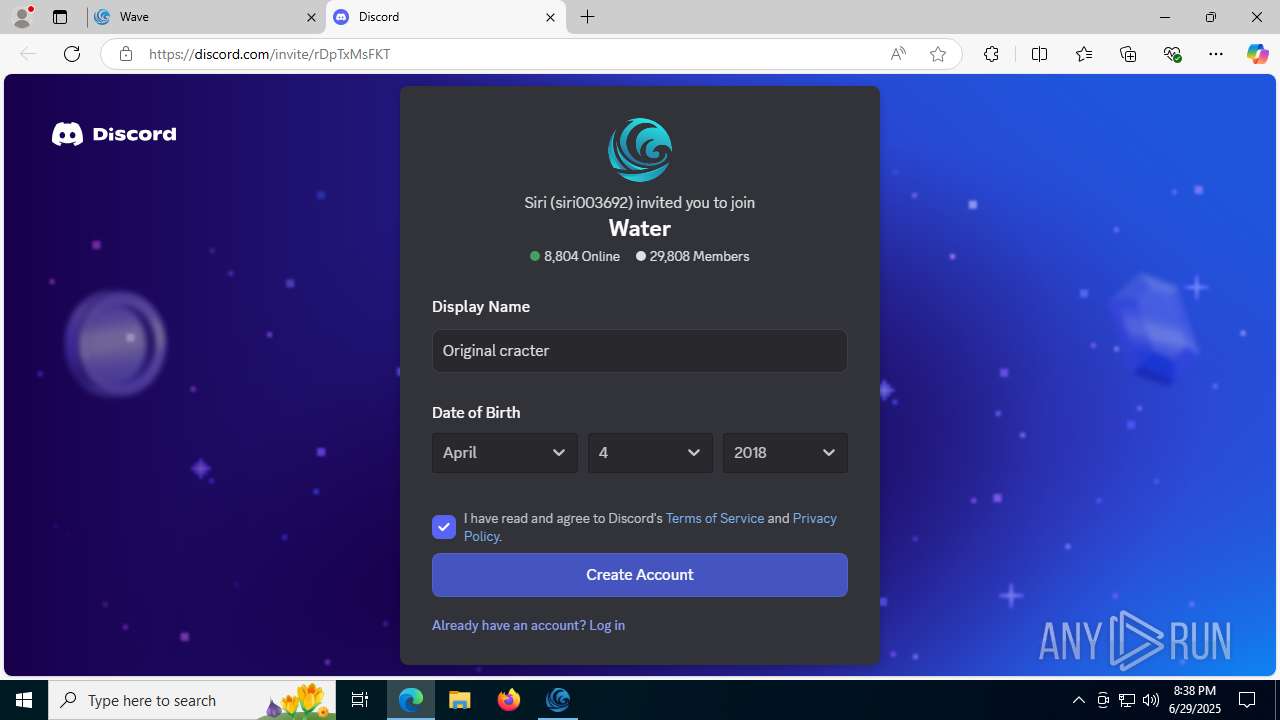
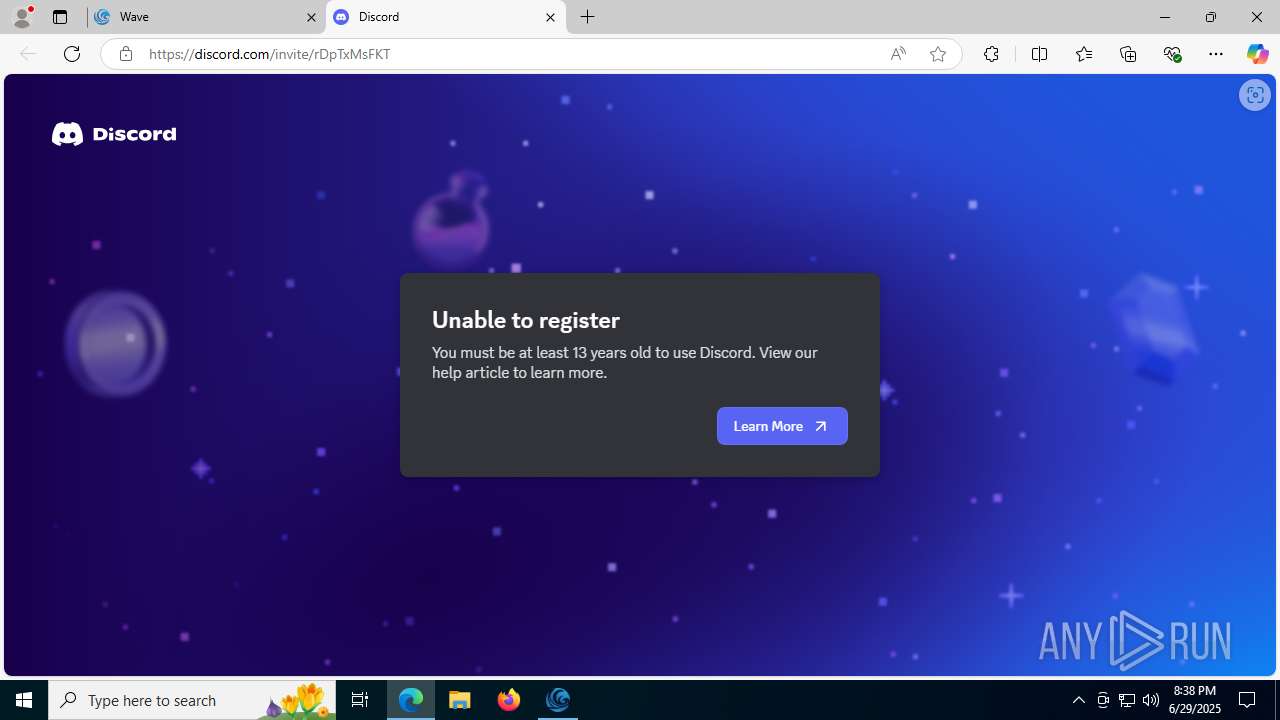
Attempting to use instant messaging service
- msedge.exe (PID: 5080)
ROBLOX mutex has been found
- ClientManager.exe (PID: 4024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
224
Monitored processes
82
Malicious processes
3
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | C:\WINDOWS\system32\cmd.exe /d /s /c "powershell.exe Start-Process -FilePath "'C:\Users\admin\AppData\Local\Temp\1ef937b444eb8c21116ee0130196653c\execute.bat'" -WindowStyle hidden -Verb runAs" | C:\Windows\System32\cmd.exe | — | Wave.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5716,i,16349604926979821500,2396077689413977187,262144 --variations-seed-version --mojo-platform-channel-handle=5692 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 756 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4236,i,16349604926979821500,2396077689413977187,262144 --variations-seed-version --mojo-platform-channel-handle=4220 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Internet Explorer\iexplore.exe" "codex.lol" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1932 | "C:\Users\admin\AppData\Local\Programs\Wave\Wave.exe" | C:\Users\admin\AppData\Local\Programs\Wave\Wave.exe | — | explorer.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Wave Version: 0.5.8 Modules
| |||||||||||||||
| 1976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2716,i,11054121237358119674,1360504533289125244,262144 --variations-seed-version --mojo-platform-channel-handle=2740 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2768,i,16349604926979821500,2396077689413977187,262144 --variations-seed-version --mojo-platform-channel-handle=2636 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2180 | powershell.exe Start-Process -FilePath "'C:\Users\admin\AppData\Local\Temp\1ef937b444eb8c21116ee0130196653c\execute.bat'" -WindowStyle hidden -Verb runAs | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --from-ie-to-edge=8 -- "http://codex.lol/" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 021
Read events
19 887
Write events
71
Delete events
63
Modification events
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1720) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (2192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721710 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5104CA23-8E68-48C5-B073-9DDA2E801CA4} | |||
Executable files
48
Suspicious files
643
Text files
137
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF175ee9.TMP | — | |
MD5:— | SHA256:— | |||
| 2192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF175ef8.TMP | — | |
MD5:— | SHA256:— | |||
| 2192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF175ef8.TMP | — | |
MD5:— | SHA256:— | |||
| 2192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175ef8.TMP | — | |
MD5:— | SHA256:— | |||
| 2192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF175ef8.TMP | — | |
MD5:— | SHA256:— | |||
| 2192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
129
DNS requests
128
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5080 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:Etz64MzltlX0XEPdoPVXy2he73mpVw9CWnf4-mCneug&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
6876 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.150:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8100 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8100 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8104 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751589317&P2=404&P3=2&P4=MQW%2fone3%2fmTKyRhhn4J9hbgHaF0SQs4JVMKBt9GayQ7PlDJ8g295xYfwP0a4NltkWI6sbQC53d%2bEoMpGLaWlVA%3d%3d | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8104 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751589317&P2=404&P3=2&P4=MQW%2fone3%2fmTKyRhhn4J9hbgHaF0SQs4JVMKBt9GayQ7PlDJ8g295xYfwP0a4NltkWI6sbQC53d%2bEoMpGLaWlVA%3d%3d | unknown | — | — | whitelisted |
8104 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751589317&P2=404&P3=2&P4=MQW%2fone3%2fmTKyRhhn4J9hbgHaF0SQs4JVMKBt9GayQ7PlDJ8g295xYfwP0a4NltkWI6sbQC53d%2bEoMpGLaWlVA%3d%3d | unknown | — | — | whitelisted |
8104 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1751589318&P2=404&P3=2&P4=g00BcjX2DsJfI%2f1odu%2bGm664JQVI%2bSJP5zLyD2Kuool%2bjQiJQvOkTVEU6oHxe84i2hH2d9viZLJ67DTQ5d2Ylw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3936 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5080 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5080 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5080 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5080 | msedge.exe | 104.26.6.49:443 | codex.lol | CLOUDFLARENET | US | unknown |
5080 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
codex.lol |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5080 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5080 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5080 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5080 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
5080 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5080 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5080 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
5080 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |