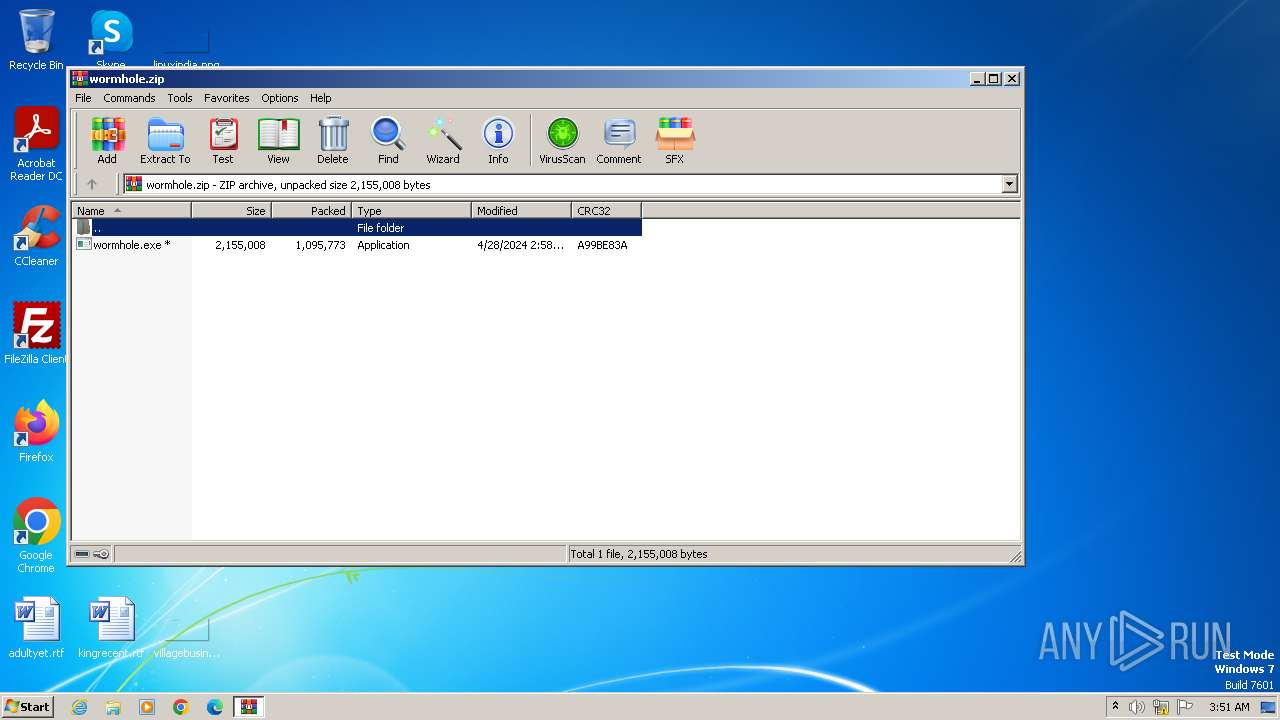
| File name: | wormhole.zip |
| Full analysis: | https://app.any.run/tasks/7eb75d1c-7b72-4e17-a237-ed232f366e31 |
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2024, 02:51:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 388131178A49A5E13708D68223F77E68 |
| SHA1: | 10EDC157542A58F1028166BA2835DB4F068F984A |
| SHA256: | 95F4A79A1BC4CCCC60B37C0A05323189A9FC0037E9D35A975EA15D954B875844 |
| SSDEEP: | 49152:7/Uk9Y7eT5t8TeCB9AD0ApD9WvPn1PuxTzNh3Ptn0VeRe4EfeJccDK6nX687C1vr:oX7MCIpDa1WxTzrPtn0Vce4ieDHX6sCF |
MALICIOUS
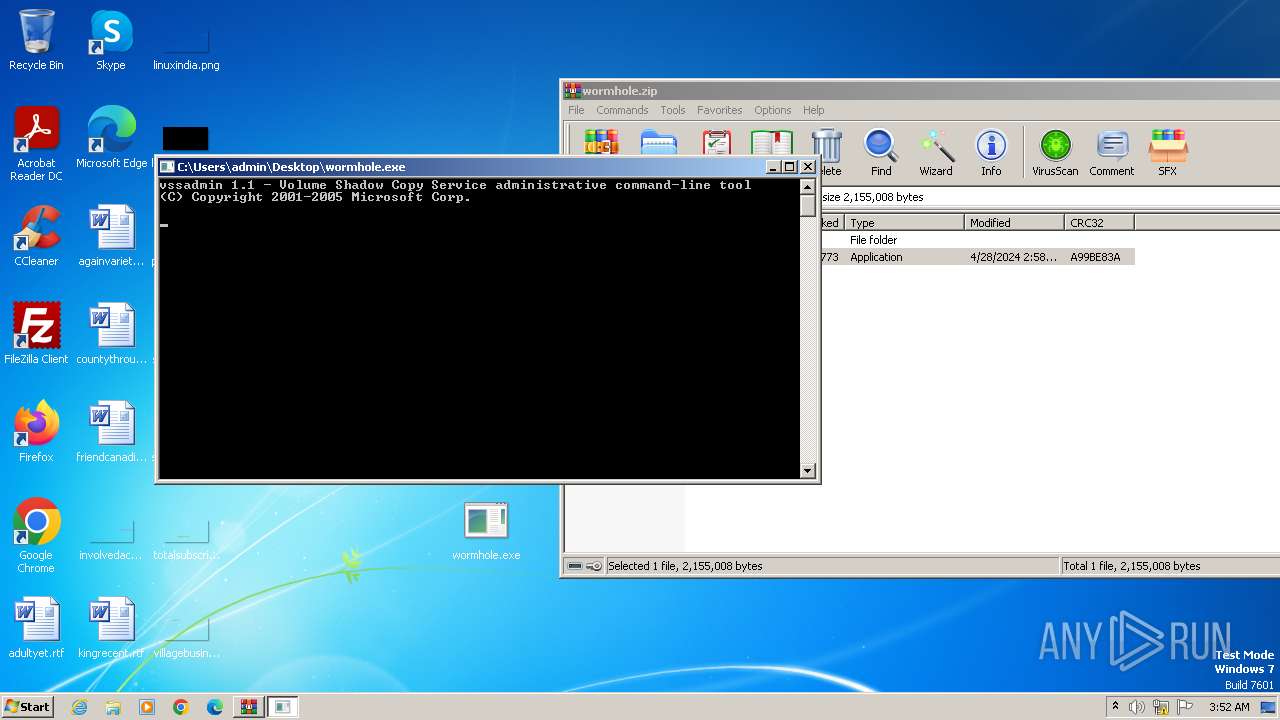
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3972)
- wormhole.exe (PID: 112)
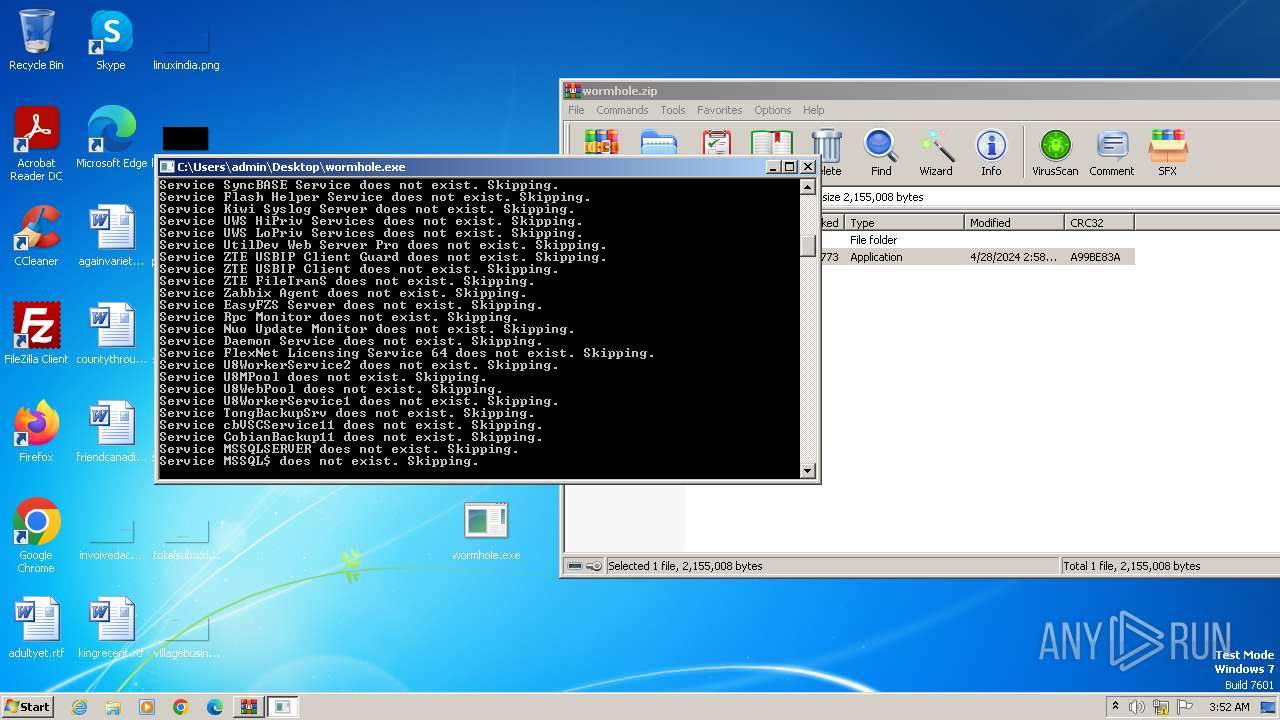
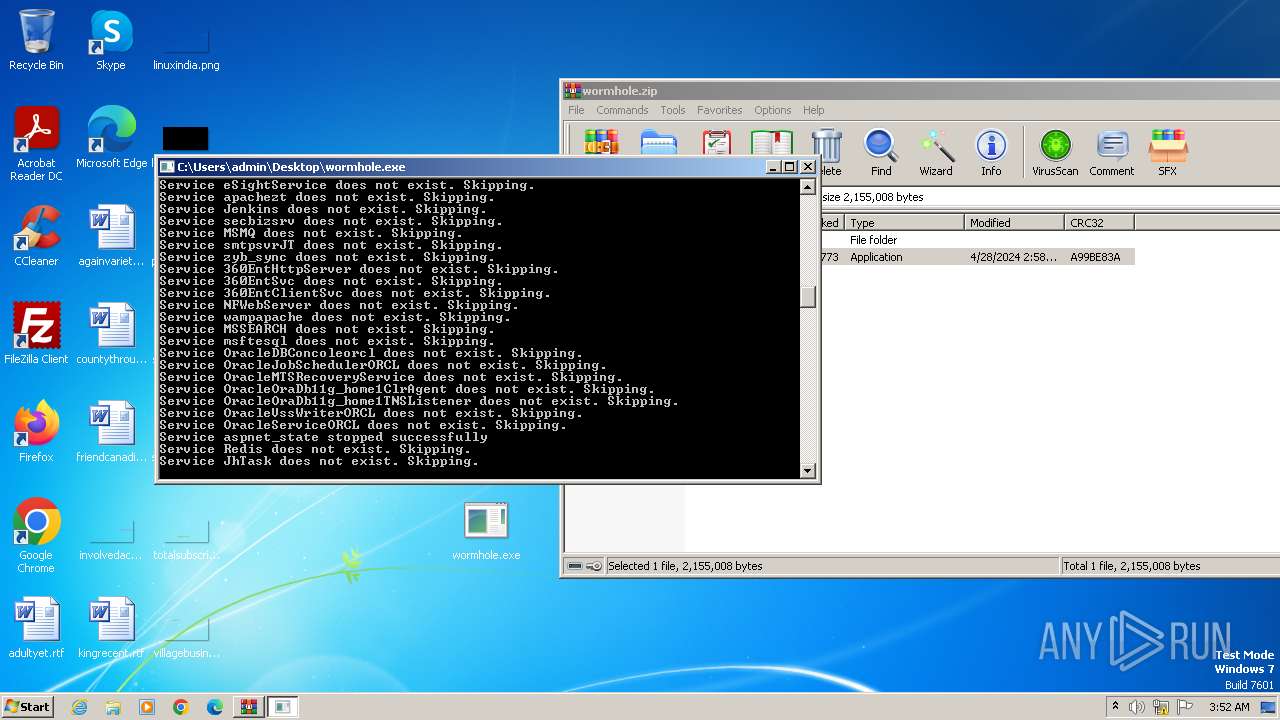
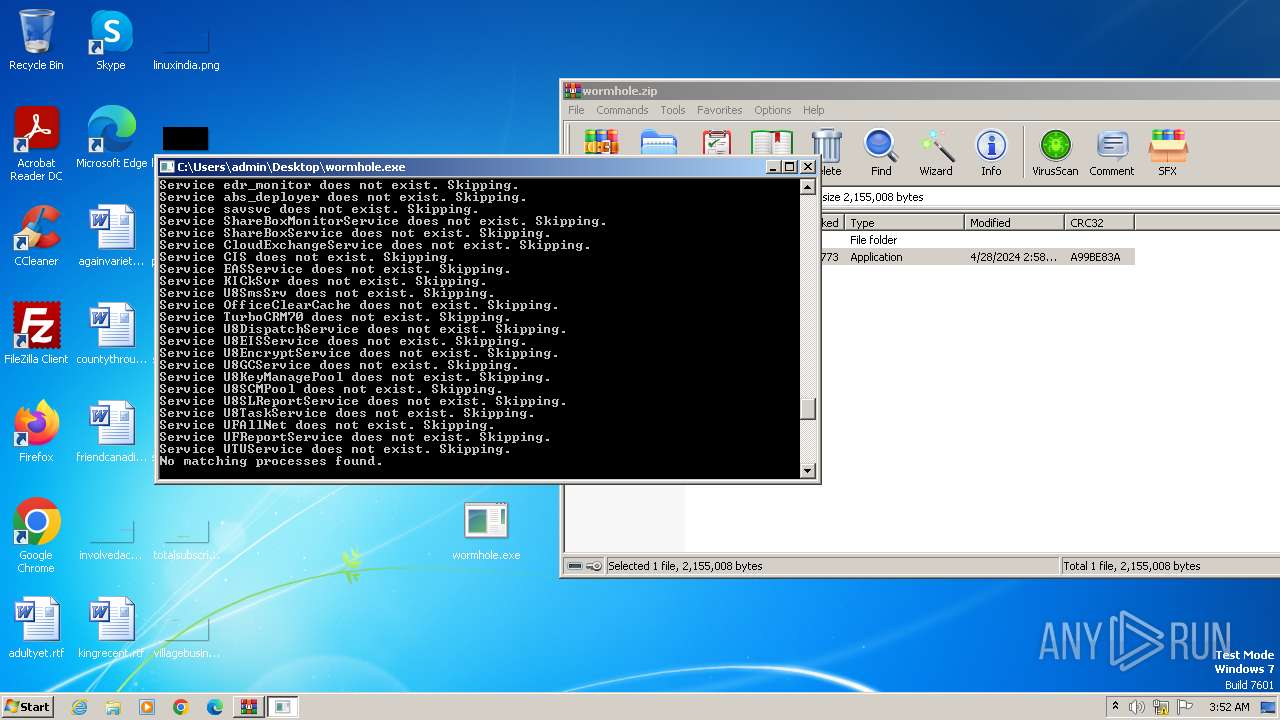
Deletes shadow copies
- cmd.exe (PID: 1876)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 1432)
The process drops C-runtime libraries
- wormhole.exe (PID: 112)
Starts CMD.EXE for commands execution
- wormhole.exe (PID: 112)
Creates file in the systems drive root
- wormhole.exe (PID: 112)
Executable content was dropped or overwritten
- wormhole.exe (PID: 112)
Process drops legitimate windows executable
- wormhole.exe (PID: 112)
INFO
Checks supported languages
- wormhole.exe (PID: 112)
Reads the computer name
- wormhole.exe (PID: 112)
Reads the machine GUID from the registry
- wormhole.exe (PID: 112)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3972)
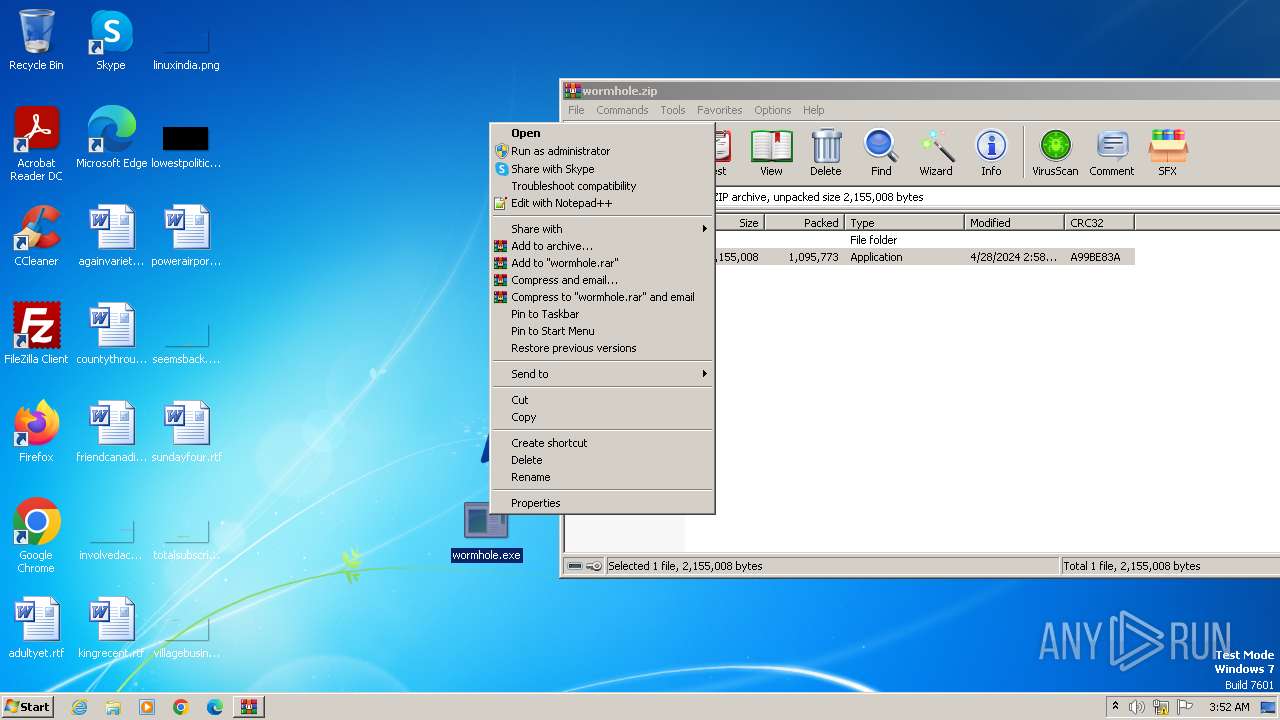
Manual execution by a user
- wormhole.exe (PID: 112)
Creates files in the program directory
- wormhole.exe (PID: 112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
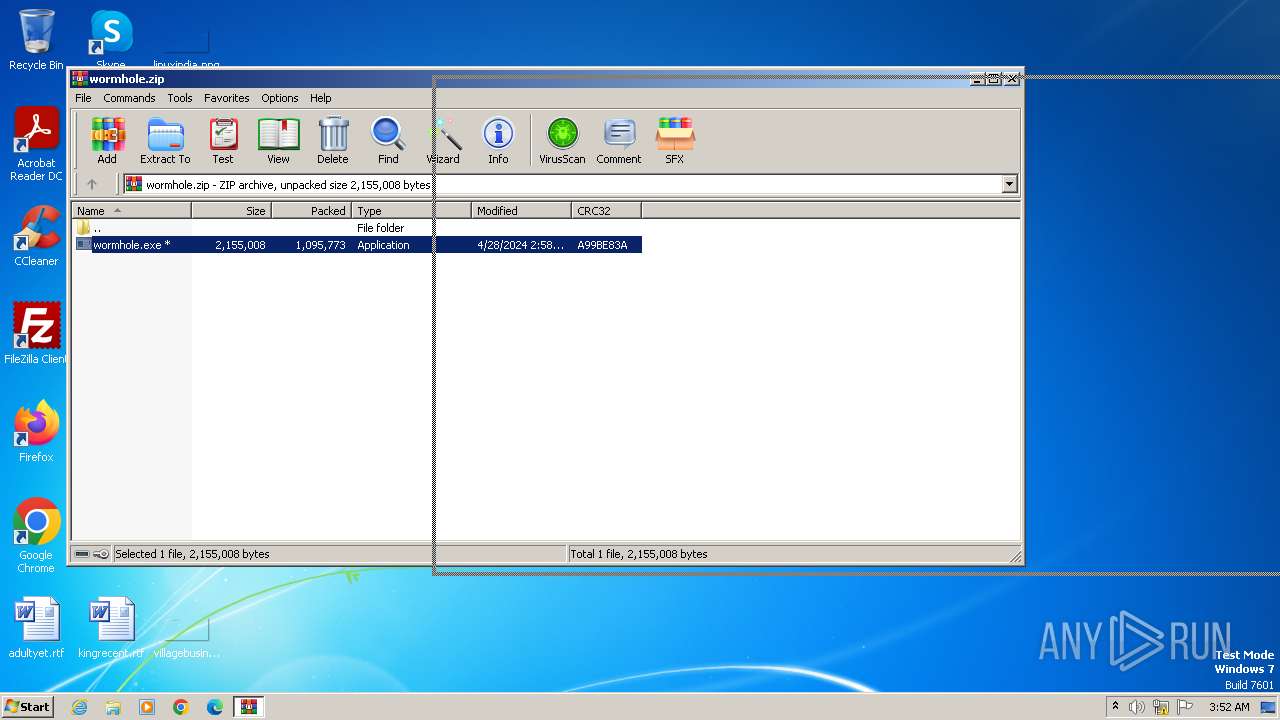
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:04:28 09:58:40 |
| ZipCRC: | 0xa99be83a |
| ZipCompressedSize: | 1095773 |
| ZipUncompressedSize: | 2155008 |
| ZipFileName: | wormhole.exe |
Total processes
42
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 112 | "C:\Users\admin\Desktop\wormhole.exe" | C:\Users\admin\Desktop\wormhole.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 116 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1432 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1876 | C:\Windows\system32\cmd.exe /c vssadmin delete shadows /all /quiet | C:\Windows\System32\cmd.exe | — | wormhole.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
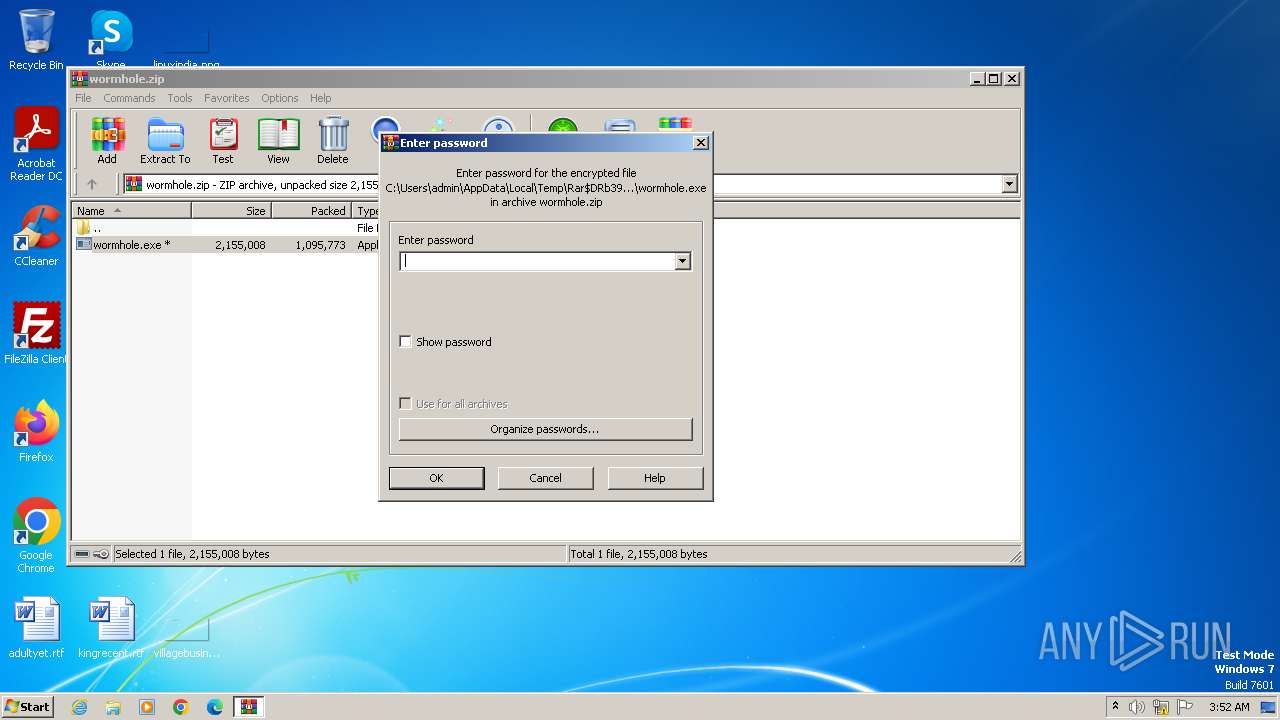
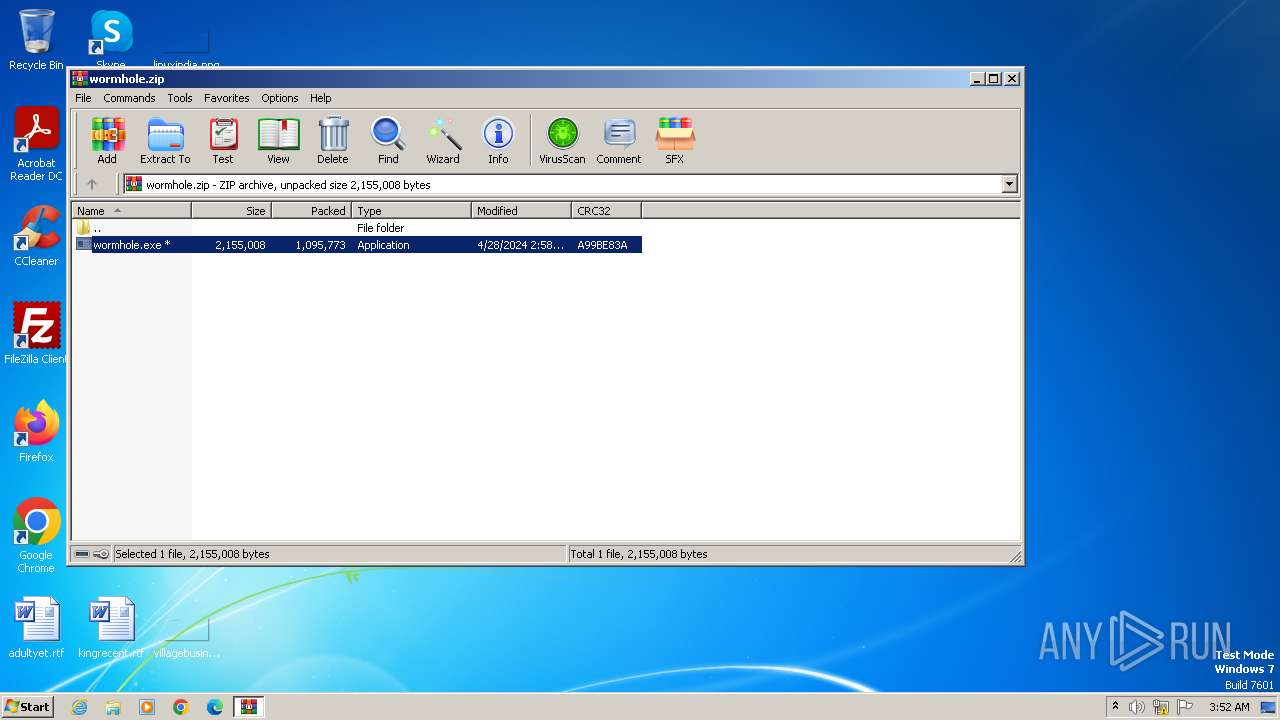
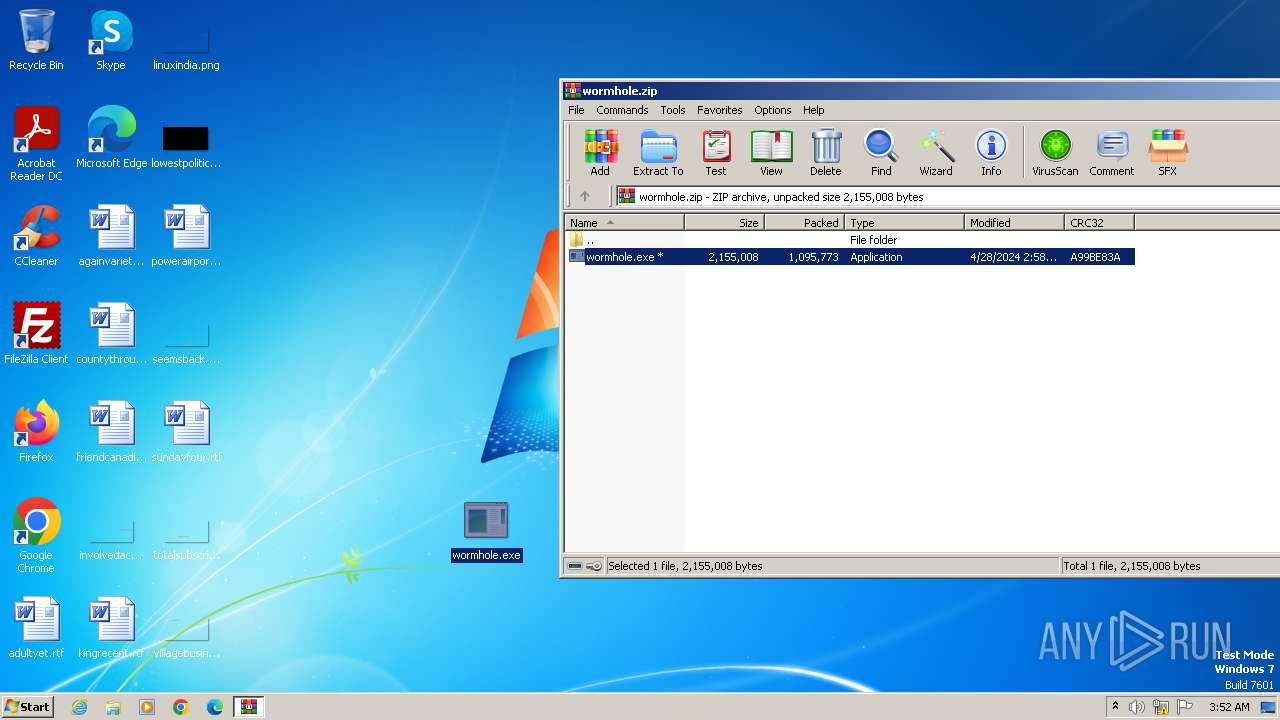
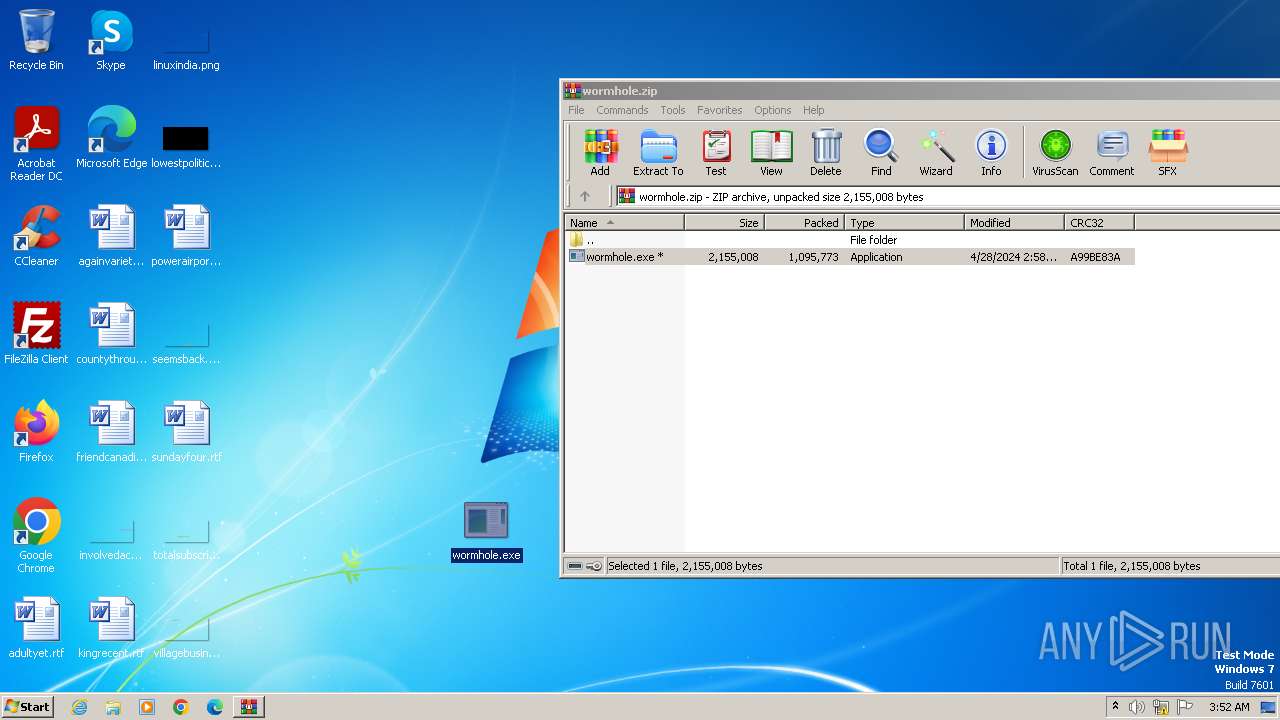
| 3972 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\wormhole.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
3 607
Read events
3 595
Write events
12
Delete events
0
Modification events
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\wormhole.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
48
Suspicious files
989
Text files
2 666
Unknown types
845
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 112 | wormhole.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\How to recover files encrypted by Wormhole.txt | — | |
MD5:— | SHA256:— | |||
| 112 | wormhole.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500\How to recover files encrypted by Wormhole.txt | — | |
MD5:— | SHA256:— | |||
| 112 | wormhole.exe | C:\Users\How to recover files encrypted by Wormhole.txt | — | |
MD5:— | SHA256:— | |||
| 112 | wormhole.exe | C:\MSOCache\How to recover files encrypted by Wormhole.txt | — | |
MD5:— | SHA256:— | |||
| 112 | wormhole.exe | C:\MSOCache\All Users\How to recover files encrypted by Wormhole.txt | — | |
MD5:— | SHA256:— | |||
| 112 | wormhole.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\How to recover files encrypted by Wormhole.txt | — | |
MD5:— | SHA256:— | |||
| 3972 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3972.3612\wormhole.exe | executable | |
MD5:C903FD67189AC67C68A2DC535246920A | SHA256:8B301EA74563E786042A59B4AC95BB4EF738FB8C7D71D1E5F3C6CE90DBFA1980 | |||
| 112 | wormhole.exe | C:\$Recycle.Bin\How to recover files encrypted by Wormhole.txt | text | |
MD5:AB02D0FFA1C210576023882747974327 | SHA256:0889B92FD64665A581117D62E5845D94F284DABB9B865B34BEB326789D3BDE19 | |||
| 112 | wormhole.exe | C:\MSOCache\All Users\{90140000-0015-0410-0000-0000000FF1CE}-C\branding.xml.Wormhole | xml | |
MD5:F7C500511D38AA91A50D7ED747B573EC | SHA256:866DCB821CB6942CF036FCC371ABD4D0CAD763D9F97A59279F34328C7BA1CC3E | |||
| 112 | wormhole.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.xml.Wormhole | xml | |
MD5:A8F5ADBA09ECCF58D2B1FB57D2A8BD80 | SHA256:BF88EA73C18E4608C569113DFF23E9F2FC51A3E037F268EBDBDEABCF6C2E7A14 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |