| download: | SCU5Setup.exe |
| Full analysis: | https://app.any.run/tasks/5ef88adb-b989-4c2d-a63b-3b8496dc5686 |
| Verdict: | Malicious activity |
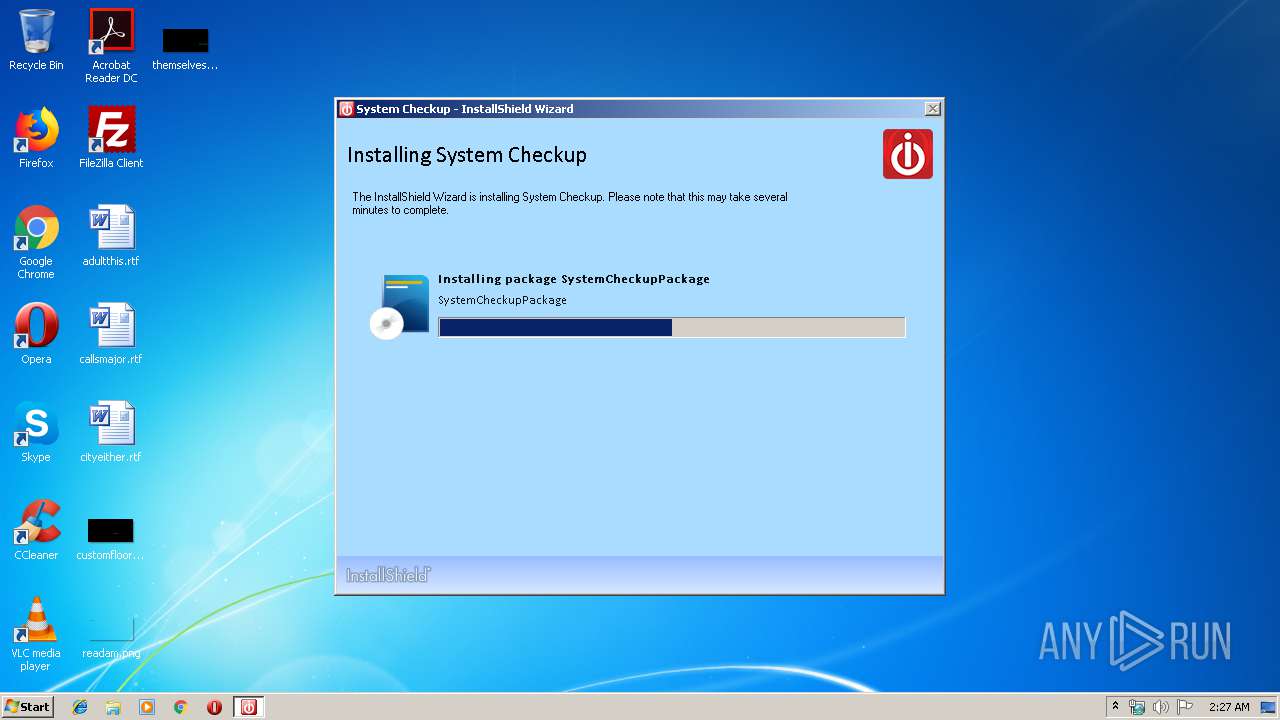
| Analysis date: | September 19, 2019, 01:27:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 95ACBF43A61D21E90EDAB20EF37A4A72 |
| SHA1: | 2DF31D6B9AA3C079E6818D0D6148E5C7FC3BA4C1 |
| SHA256: | 95E13FDC24506E9F45D057C2AE7ED69DB60BDF56455E40ABB50C5E1199739CDC |
| SSDEEP: | 196608:xMhYply8HDnjE5RI7J6SpgldeNlG600t40Les7B5L0TaH37VRdKw:xTygDjkRY6Spgwld/rgTxw |
MALICIOUS
Uses Task Scheduler to run other applications
- SCU5-Installer.exe (PID: 4040)
- cmd.exe (PID: 1428)
Application was dropped or rewritten from another process
- SCU5-Installer.exe (PID: 3388)
- SCU.exe (PID: 2136)
- SCU5-Installer.exe (PID: 4040)
- SCU.exe (PID: 2760)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2092)
- SCU.exe (PID: 2136)
- schtasks.exe (PID: 3080)
Loads dropped or rewritten executable
- _isAD9A.exe (PID: 3928)
- SCU5-Installer.exe (PID: 4040)
- _isAD9A.exe (PID: 3672)
Changes the autorun value in the registry
- _isAD9A.exe (PID: 3928)
SUSPICIOUS
Application launched itself
- _isAD9A.exe (PID: 3928)
Starts itself from another location
- SCU5Setup.exe (PID: 3168)
Executable content was dropped or overwritten
- SCU5Setup.exe (PID: 3168)
- SCU5-Installer.exe (PID: 4040)
- SCU5-Installer.exe (PID: 3388)
- _isAD9A.exe (PID: 3928)
Executed via COM
- DrvInst.exe (PID: 2384)
Executed as Windows Service
- vssvc.exe (PID: 3816)
Searches for installed software
- SCU5-Installer.exe (PID: 4040)
Starts CMD.EXE for commands execution
- SCU.exe (PID: 2136)
Creates files in the program directory
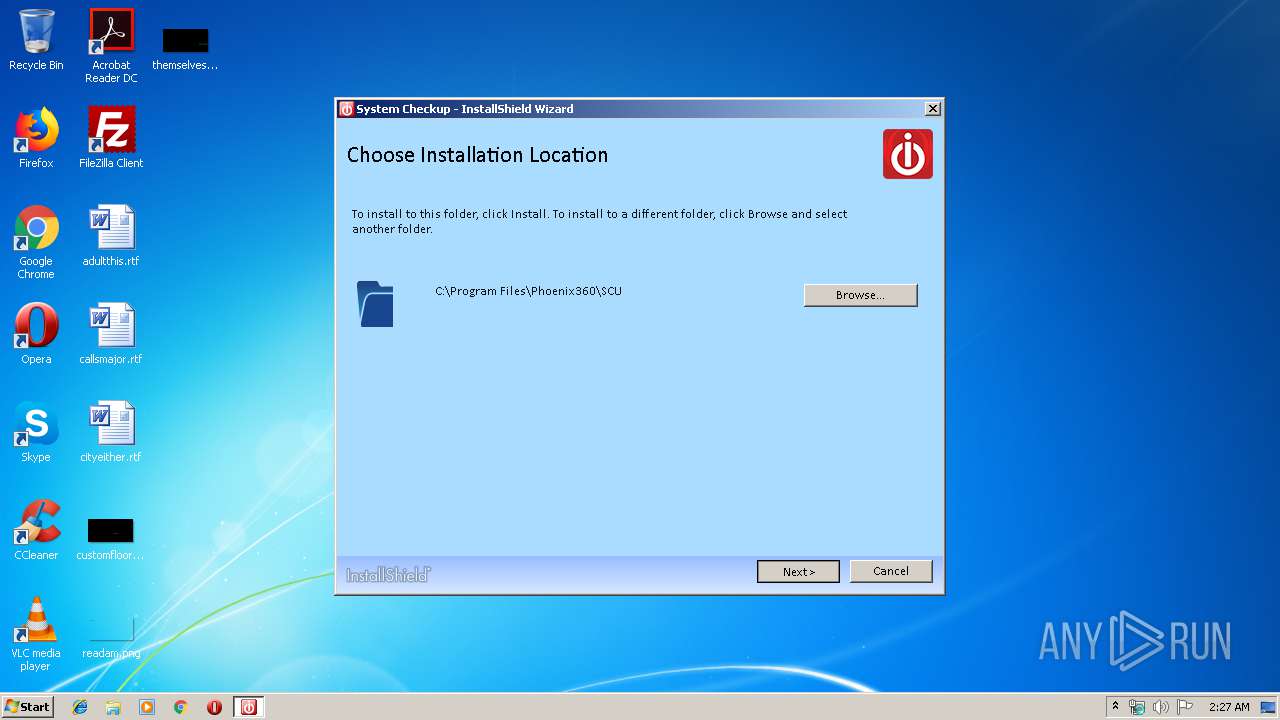
- SCU5-Installer.exe (PID: 4040)
Reads Environment values
- SCU.exe (PID: 2136)
Creates a software uninstall entry
- SCU5-Installer.exe (PID: 4040)
Reads internet explorer settings
- SCU.exe (PID: 2136)
Uses TASKKILL.EXE to kill process
- _isAD9A.exe (PID: 3672)
INFO
Changes settings of System certificates
- DrvInst.exe (PID: 2384)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 2384)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3816)
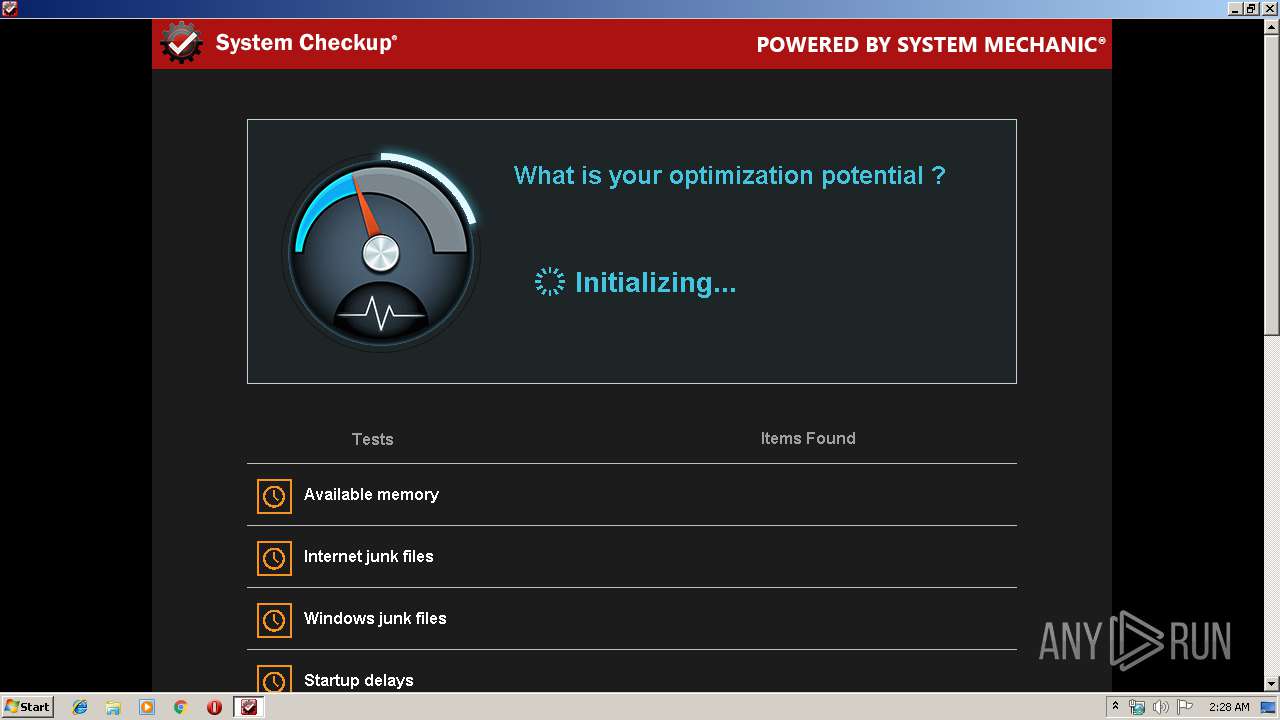
Manual execution by user
- SCU.exe (PID: 2760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:14 22:03:07+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 861184 |
| InitializedDataSize: | 673280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9bb19 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.3.226 |
| ProductVersionNumber: | 5.0.3.226 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
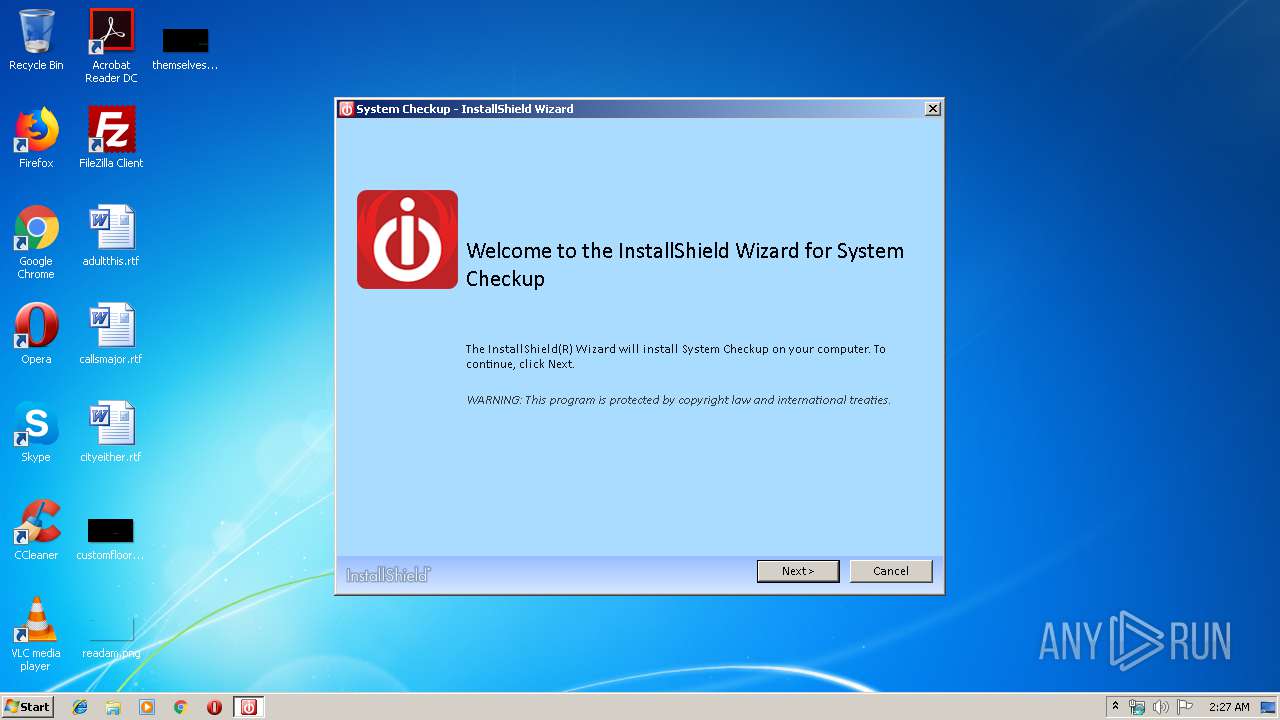
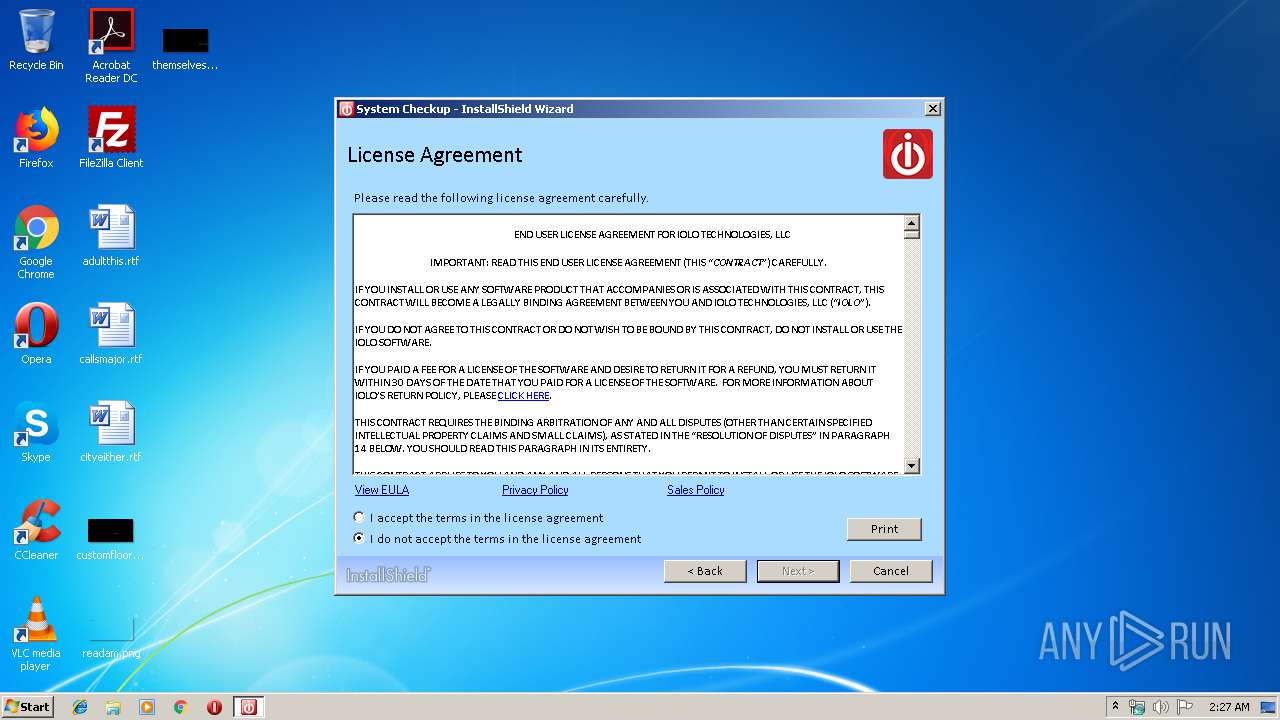
| CompanyName: | iolo technologies, LLC |
| FileDescription: | System Checkup Installer |
| FileVersion: | 5.0.3.226 |
| InternalName: | SetupSuite |
| LegalCopyright: | Copyright (c) 2018 iolo Technologies, LLC |
| OriginalFileName: | InstallShield SetupSuite.exe |
| ProductName: | System Checkup |
| ProductVersion: | 5.0.3.226 |
| InternalBuildNumber: | 182945 |
| ISInternalVersion: | 24.0.464 |
| ISInternalDescription: | Setup Suite Launcher Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-May-2018 20:03:07 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Flexera |
| FileDescription: | Setup Suite Launcher Unicode |
| FileVersion: | 24.0.464 |
| InternalName: | SetupSuite |
| LegalCopyright: | Copyright (c) 2018 Flexera. All Rights Reserved. |
| OriginalFilename: | InstallShield SetupSuite.exe |
| ProductName: | InstallShield |
| ProductVersion: | 24.0 |
| Internal Build Number: | 182945 |
| ISInternalVersion: | 24.0.464 |
| ISInternalDescription: | Setup Suite Launcher Unicode |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-May-2018 20:03:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000D2031 | 0x000D2200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40821 |
.orpc | 0x000D4000 | 0x000001A2 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.75465 |
.rdata | 0x000D5000 | 0x00049B5C | 0x00049C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.47449 |
.data | 0x0011F000 | 0x00006734 | 0x00005A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.7607 |
.gfids | 0x00126000 | 0x00000134 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.46666 |
.tls | 0x00127000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00128000 | 0x00043DE4 | 0x00043E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.7881 |
.reloc | 0x0016C000 | 0x00010C98 | 0x00010E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56176 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07176 | 640 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.31163 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.94006 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.80407 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 6.12892 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 7.97727 | 73611 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 1.94502 | 72 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 6.20034 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 6.22422 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 6.2354 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
msi.dll (delay-loaded) |
ole32.dll |
Total processes
55
Monitored processes
15
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1428 | "C:\Windows\System32\cmd.exe" /C schtasks /create /tn "iolo System Checkup" /tr "\"C:\Program Files\Phoenix360\SCU\SCU.exe\" /toast" /sc hourly /mo 2 /st 08:00:00 | C:\Windows\System32\cmd.exe | — | SCU.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2092 | C:\Windows\System32\schtasks.exe /delete /tn "iolo System Checkup SetTask" /f | C:\Windows\System32\schtasks.exe | — | SCU5-Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Phoenix360\SCU\SCU.exe" | C:\Program Files\Phoenix360\SCU\SCU.exe | _isAD9A.exe | ||||||||||||
User: admin Company: iolo technologies, LLC Integrity Level: HIGH Description: System Checkup Exit code: 0 Version: 5.0.3.226 Modules
| |||||||||||||||
| 2384 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot22" "" "" "695c3f483" "00000000" "000005BC" "000003C8" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Phoenix360\SCU\SCU.exe" | C:\Program Files\Phoenix360\SCU\SCU.exe | — | explorer.exe | |||||||||||
User: admin Company: iolo technologies, LLC Integrity Level: MEDIUM Description: System Checkup Exit code: 0 Version: 5.0.3.226 | |||||||||||||||
| 3036 | C:\Windows\explorer.exe | C:\Windows\explorer.exe | — | _isAD9A.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3040 | System32\taskkill.exe /F /IM SCU.exe | C:\Windows\System32\taskkill.exe | — | _isAD9A.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3080 | schtasks /create /tn "iolo System Checkup" /tr "\"C:\Program Files\Phoenix360\SCU\SCU.exe\" /toast" /sc hourly /mo 2 /st 08:00:00 | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3168 | "C:\Users\admin\AppData\Local\Temp\SCU5Setup.exe" | C:\Users\admin\AppData\Local\Temp\SCU5Setup.exe | explorer.exe | ||||||||||||
User: admin Company: iolo technologies, LLC Integrity Level: HIGH Description: System Checkup Installer Exit code: 0 Version: 5.0.3.226 Modules
| |||||||||||||||
| 3388 | "C:\Users\admin\AppData\Local\Downloaded Installations\{495D186A-FDE4-4F54-B701-BD2E7C5CBF3C}\SCU5-Installer.exe" -s -f1".\SystemCheckup_install.iss" SUITE=True LANG=en | C:\Users\admin\AppData\Local\Downloaded Installations\{495D186A-FDE4-4F54-B701-BD2E7C5CBF3C}\SCU5-Installer.exe | _isAD9A.exe | ||||||||||||
User: admin Company: iolo technologies, LLC Integrity Level: HIGH Description: InstallScript Setup Launcher Unicode Exit code: 0 Version: 5.0.3.226 Modules
| |||||||||||||||
Total events
1 113
Read events
860
Write events
248
Delete events
5
Modification events
| (PID) Process: | (3928) _isAD9A.exe | Key: | HKEY_CURRENT_USER\Software\InstallShield\SuiteInstallers\{A78D6051-5694-49CA-A0D8-D3F95A892C2E} |
| Operation: | write | Name: | InfoPath |
Value: C:\Users\admin\AppData\Local\Temp\{B67FD018-00CE-4920-B52A-F97E0CD32485}\_isAE55 | |||
| (PID) Process: | (3928) _isAD9A.exe | Key: | HKEY_CURRENT_USER\Software\InstallShield\SuiteInstallers\{A78D6051-5694-49CA-A0D8-D3F95A892C2E} |
| Operation: | write | Name: | Reboot |
Value: 1 | |||
| (PID) Process: | (3928) _isAD9A.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | {A78D6051-5694-49CA-A0D8-D3F95A892C2E} |
Value: "C:\Users\admin\AppData\Local\Temp\SCU5Setup.exe" | |||
| (PID) Process: | (4040) SCU5-Installer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000001408D96D896ED501C80F0000C40F0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4040) SCU5-Installer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000006E6ADB6D896ED501C80F0000C40F0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4040) SCU5-Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 24 | |||
| (PID) Process: | (4040) SCU5-Installer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000163F316E896ED501C80F0000C40F0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4040) SCU5-Installer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000070A1336E896ED501C80F0000A40D0000E8030000010000000000000000000000CFE67682BC09C444B2F6F09121CDC6CD0000000000000000 | |||
| (PID) Process: | (3816) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E651446E896ED501E80E0000300A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3816) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E651446E896ED501E80E0000680E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
18
Suspicious files
14
Text files
229
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3168 | SCU5Setup.exe | C:\Users\admin\AppData\Local\Temp\{83F2464F-CB71-4A4D-9381-A4EBDBB09C91}\_isAD9A.exe | executable | |
MD5:— | SHA256:— | |||
| 3928 | _isAD9A.exe | C:\Users\admin\AppData\Local\Temp\{B67FD018-00CE-4920-B52A-F97E0CD32485}\setup.xml | xml | |
MD5:— | SHA256:— | |||
| 3928 | _isAD9A.exe | C:\Users\admin\AppData\Local\Temp\{B67FD018-00CE-4920-B52A-F97E0CD32485}\1033\ioloEULA.rtf | text | |
MD5:— | SHA256:— | |||
| 3928 | _isAD9A.exe | C:\Users\admin\AppData\Local\Temp\{B67FD018-00CE-4920-B52A-F97E0CD32485}\Setup_UI.dll | executable | |
MD5:— | SHA256:— | |||
| 3928 | _isAD9A.exe | C:\Users\admin\AppData\Local\Temp\{B67FD018-00CE-4920-B52A-F97E0CD32485}\scale-150\Repair.png | image | |
MD5:C404CB5D0854361968716C3AB8630F92 | SHA256:ABDCECCB0963B6A2621BC1C1477C5D7FA0743E6656275FF1E3402464D7946C87 | |||
| 3928 | _isAD9A.exe | C:\Users\admin\AppData\Local\Temp\{B67FD018-00CE-4920-B52A-F97E0CD32485}\scale-150\Folder.png | image | |
MD5:F3F9575A23F7C4CD35C8324231F5BD9E | SHA256:2EE9AA1DDA88CD9964D342DDA3FE56164C9906D5441E8381297F4DCDAE6C3E9D | |||
| 3928 | _isAD9A.exe | C:\Users\admin\AppData\Local\Temp\{B67FD018-00CE-4920-B52A-F97E0CD32485}\scale-150\Application.png | image | |
MD5:46B2EB6C23572DA87ADA5A342F854641 | SHA256:016604E80FFC9921EE9CA036B6DDE317094C9D1CD8BF4928087317C708EB7C84 | |||
| 3928 | _isAD9A.exe | C:\Users\admin\AppData\Local\Temp\{B67FD018-00CE-4920-B52A-F97E0CD32485}\scale-150\ISLogoSmall.png | image | |
MD5:A7D73D5BFF3EFF52325A53642FD31552 | SHA256:8B4F5BD1C8F01EF4775453A53FC827621B6FD2F2723D52DF6CE64E5D66595C33 | |||
| 3928 | _isAD9A.exe | C:\Users\admin\AppData\Local\Temp\{B67FD018-00CE-4920-B52A-F97E0CD32485}\scale-150\ISLogoBig.png | image | |
MD5:D1EF62B54F9891D47FC45CEC0DC3BA66 | SHA256:C2CC87D11211DBC67AE85BF317393912A4DEB092A70A4D1AA746F31F4E127A18 | |||
| 3928 | _isAD9A.exe | C:\Users\admin\AppData\Local\Temp\{B67FD018-00CE-4920-B52A-F97E0CD32485}\scale-150\Typical.png | image | |
MD5:BE7A62B3CF3AA240CCBB2E8CDF60F29F | SHA256:1D21BEA5C93FCED9F777A86F2B7D9EE11B697BCB4D9306794A81BEBA60CA7AAC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2136 | SCU.exe | GET | 200 | 216.246.89.93:80 | http://svc.iolo.com/__svc/installer/record.aspx?p=918D30D3-AD9B-43A8-9EF7-463075DC93CD&b=ecom+general+General+iolohome+en&m=USER-PC-6.1.7601-vyryl&t=1&v=5.0.3.226 | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2136 | SCU.exe | 216.246.89.93:80 | svc.iolo.com | Server Central Network | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
svc.iolo.com |
| unknown |
Threats
Process | Message |
|---|---|
SCU5-Installer.exe | Getting existing security descriptor for 'MACHINE\Software\SCU' |
SCU5-Installer.exe | Failed to obtain existing security descriptor, last error: 0x00000002 |