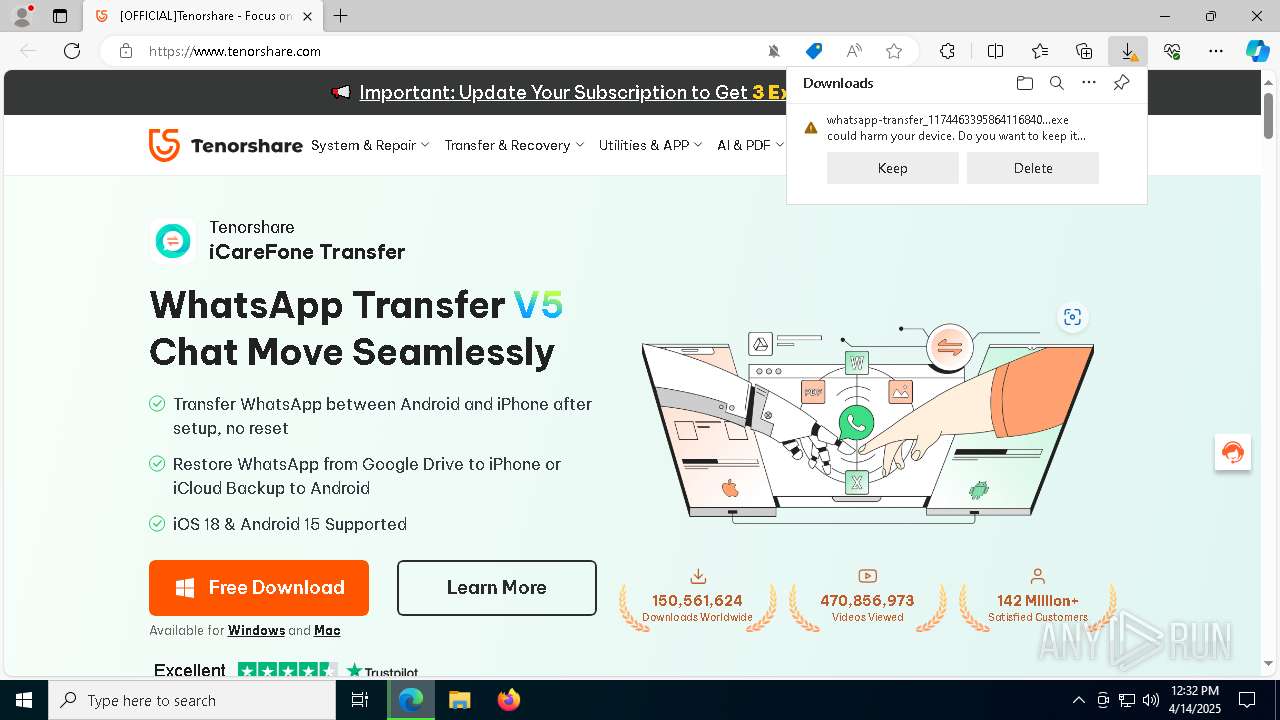
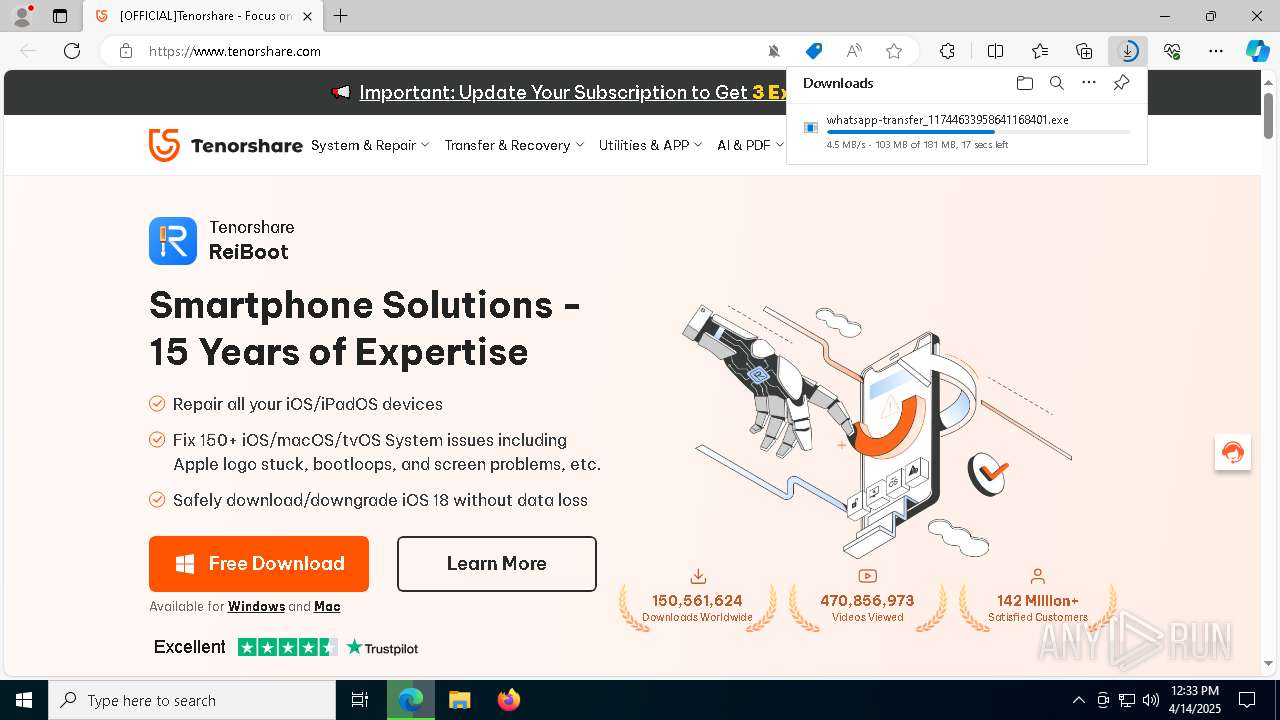
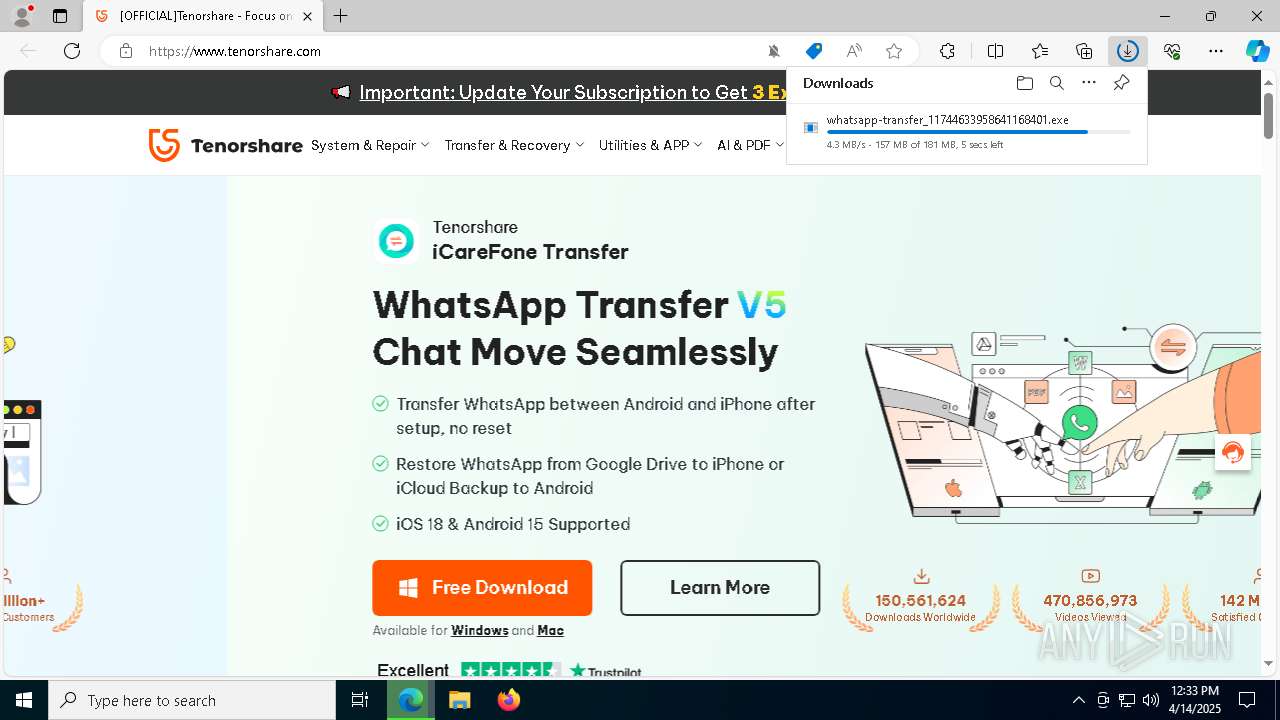
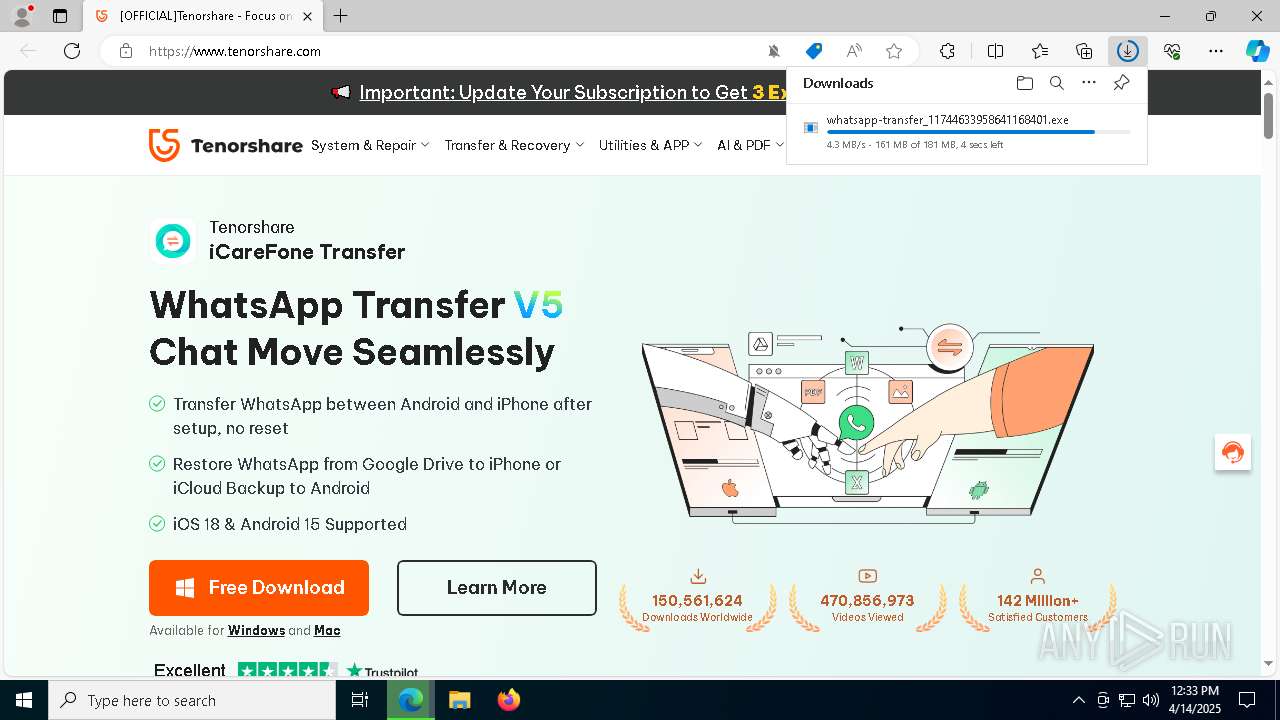
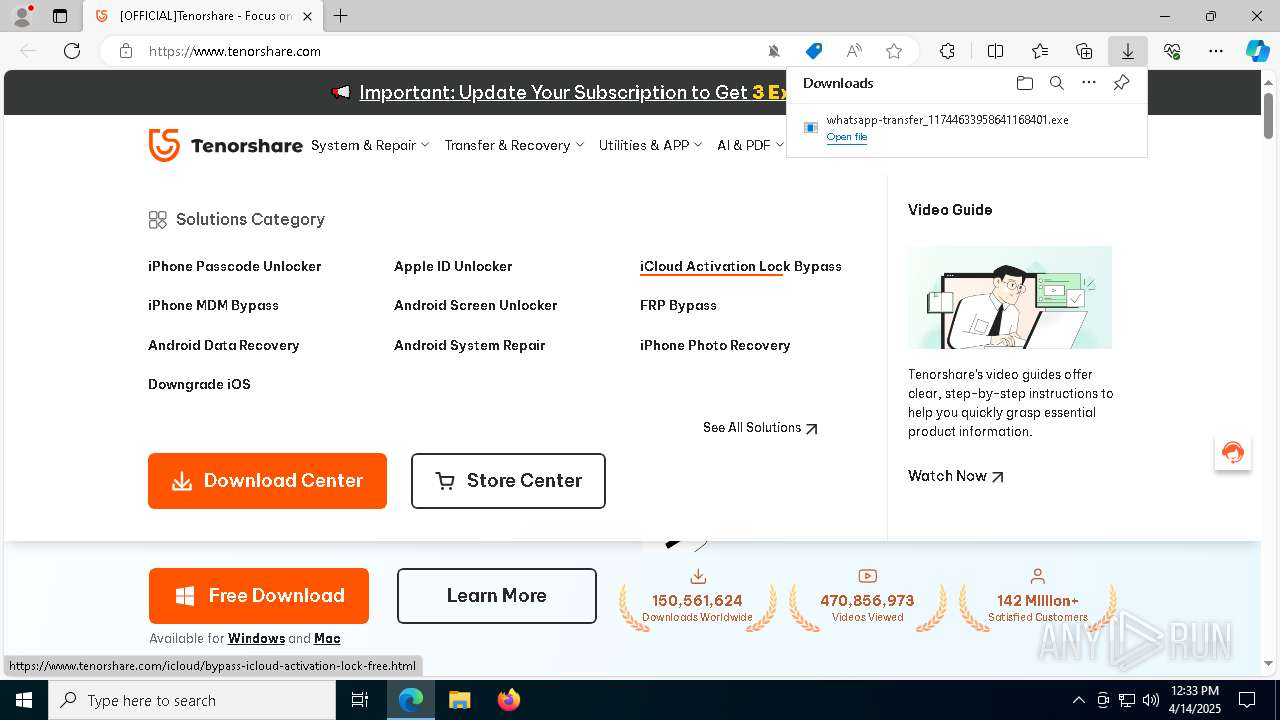
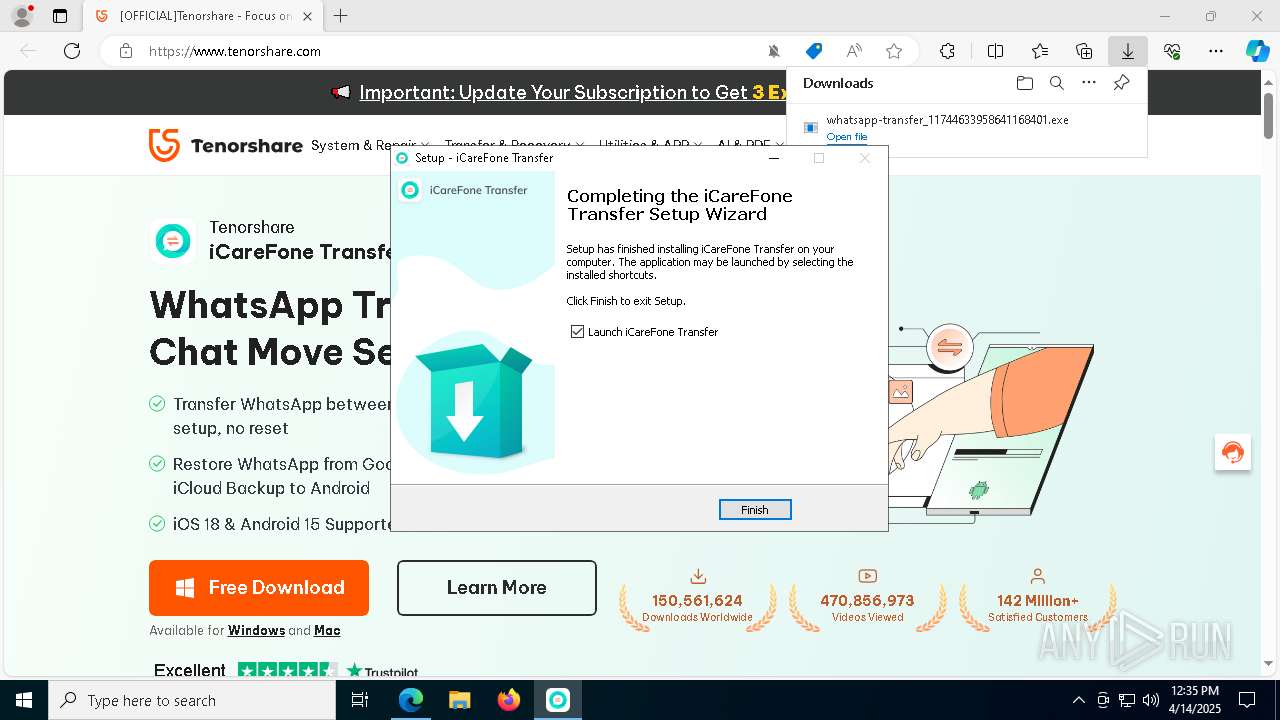
| URL: | www.tenorshare.com |
| Full analysis: | https://app.any.run/tasks/3aa7769c-e210-4e69-a57e-ade0ad93701f |
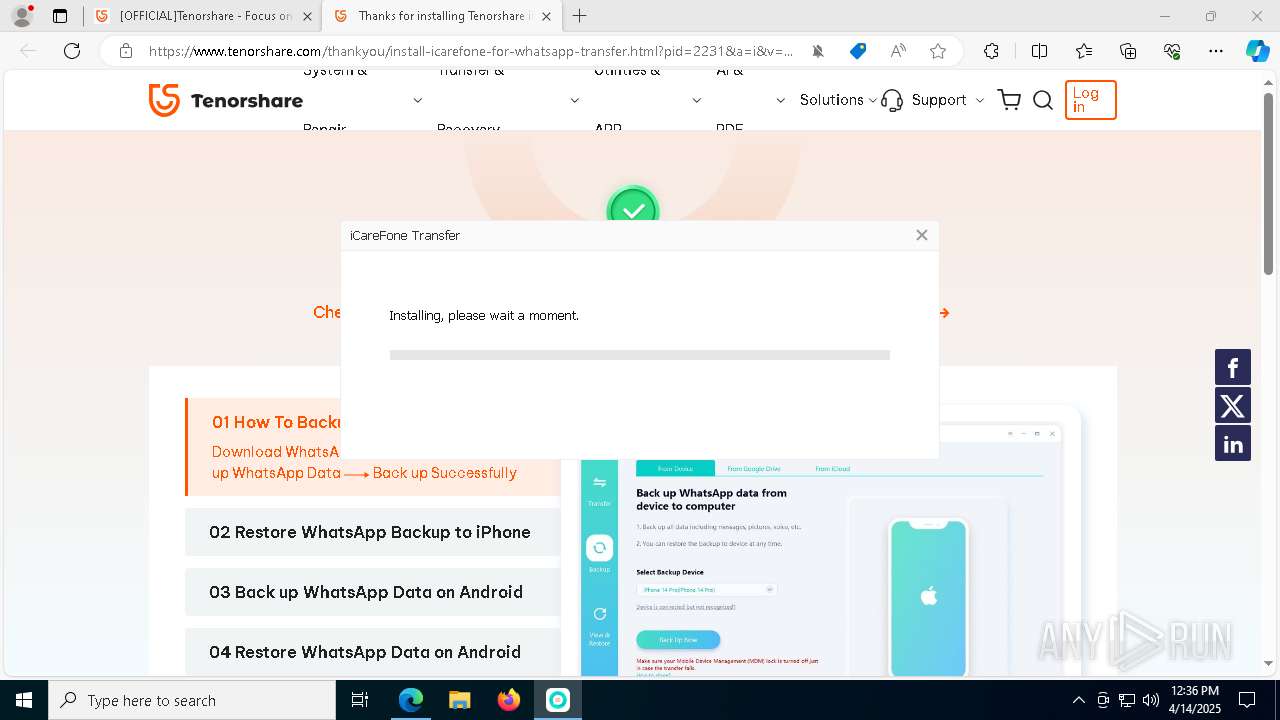
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2025, 12:32:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E0886C37A1A9902D62F5A9D41840423C |
| SHA1: | 98680B5D13E2DAEAC4D2CC481E6B97B4086E14CB |
| SHA256: | 95A92EBE71C1064F9A1E644C1AE3267B7DC32C1C20A4B7917543A6512705349F |
| SSDEEP: | 3:EvXILGKI:FLGT |
MALICIOUS
No malicious indicators.SUSPICIOUS
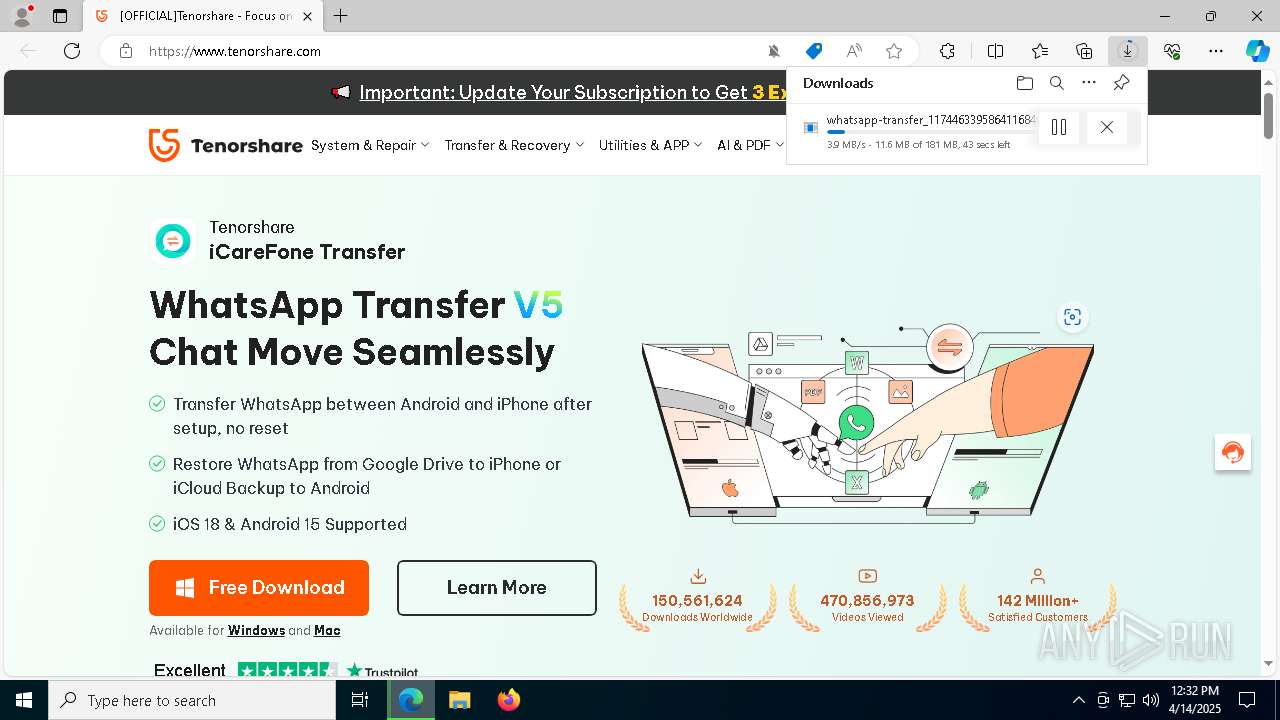
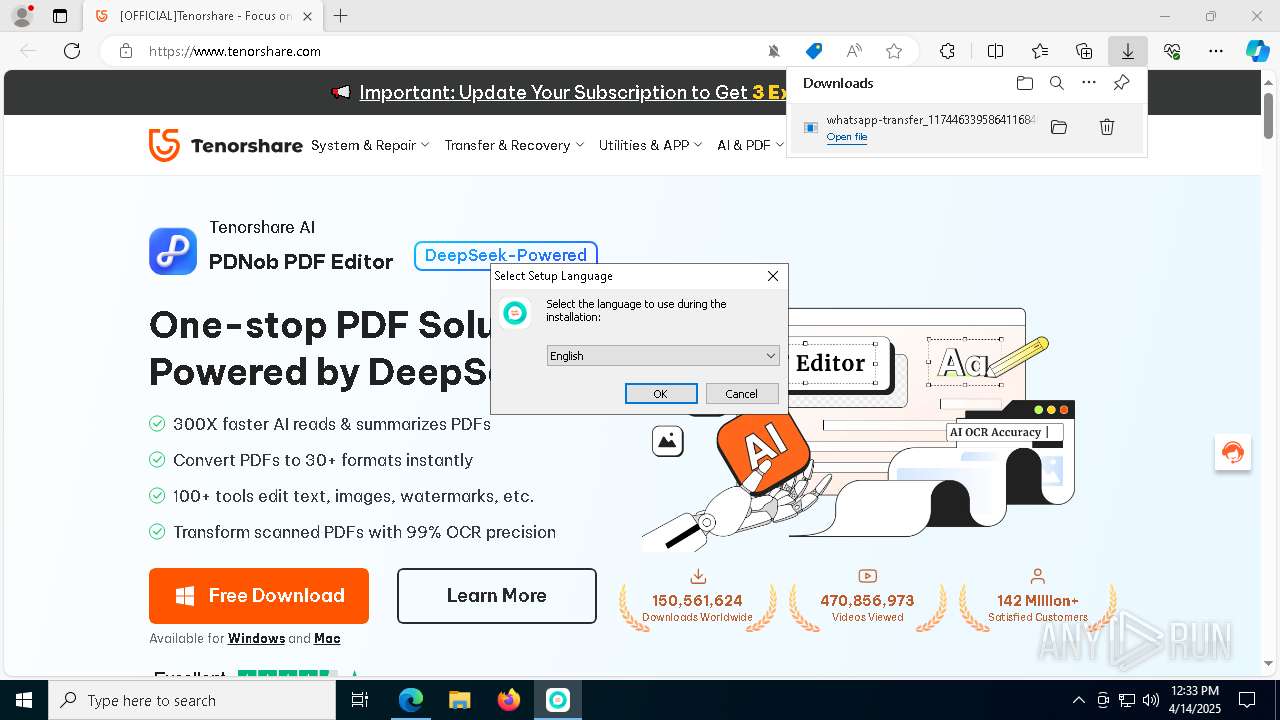
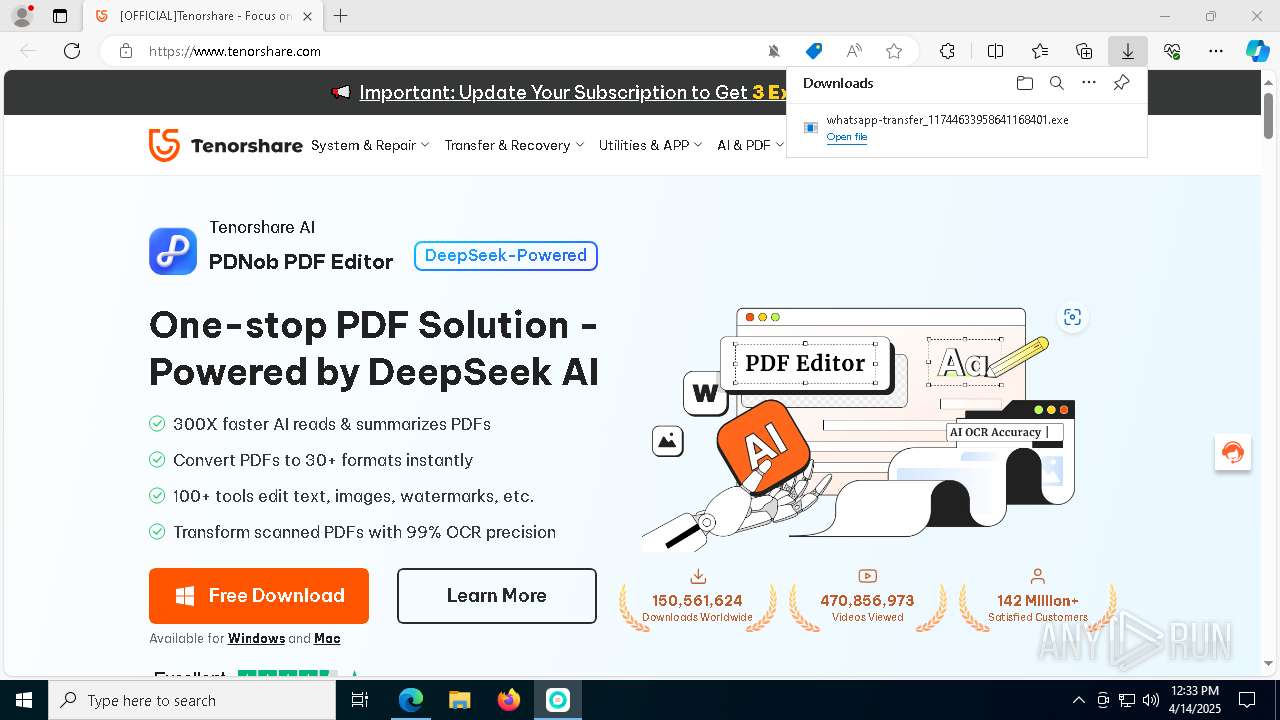
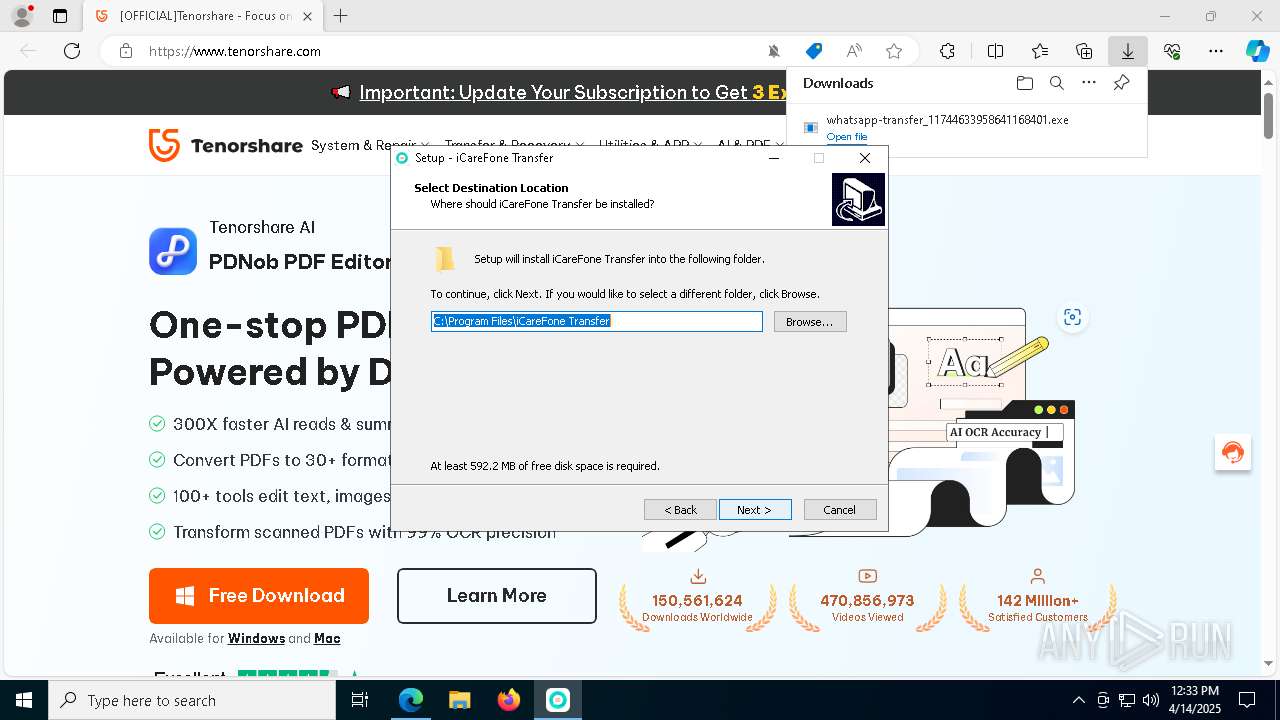
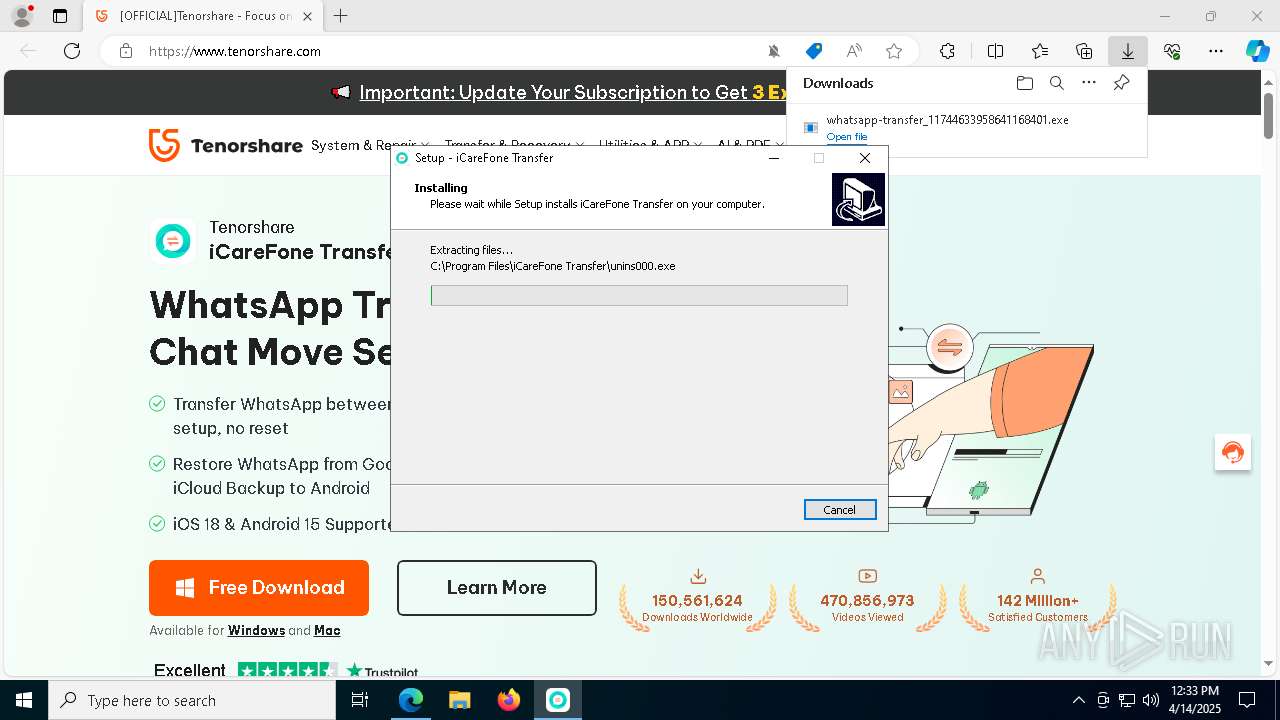
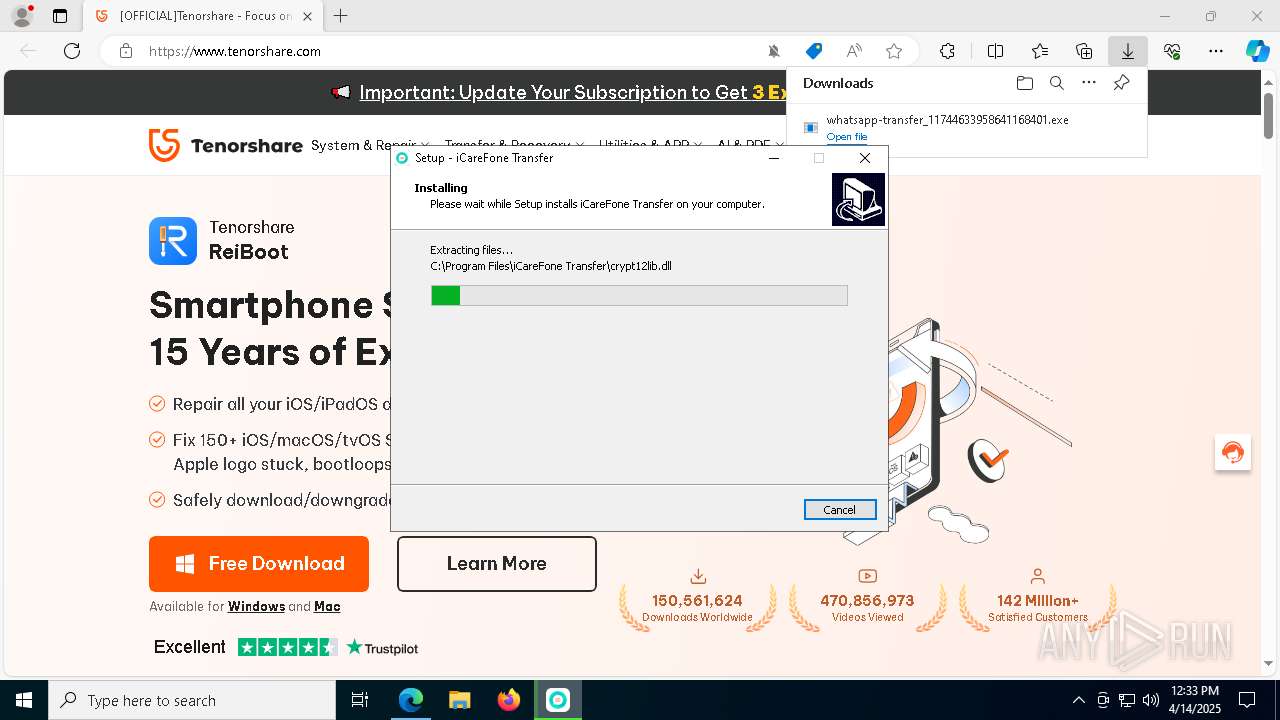
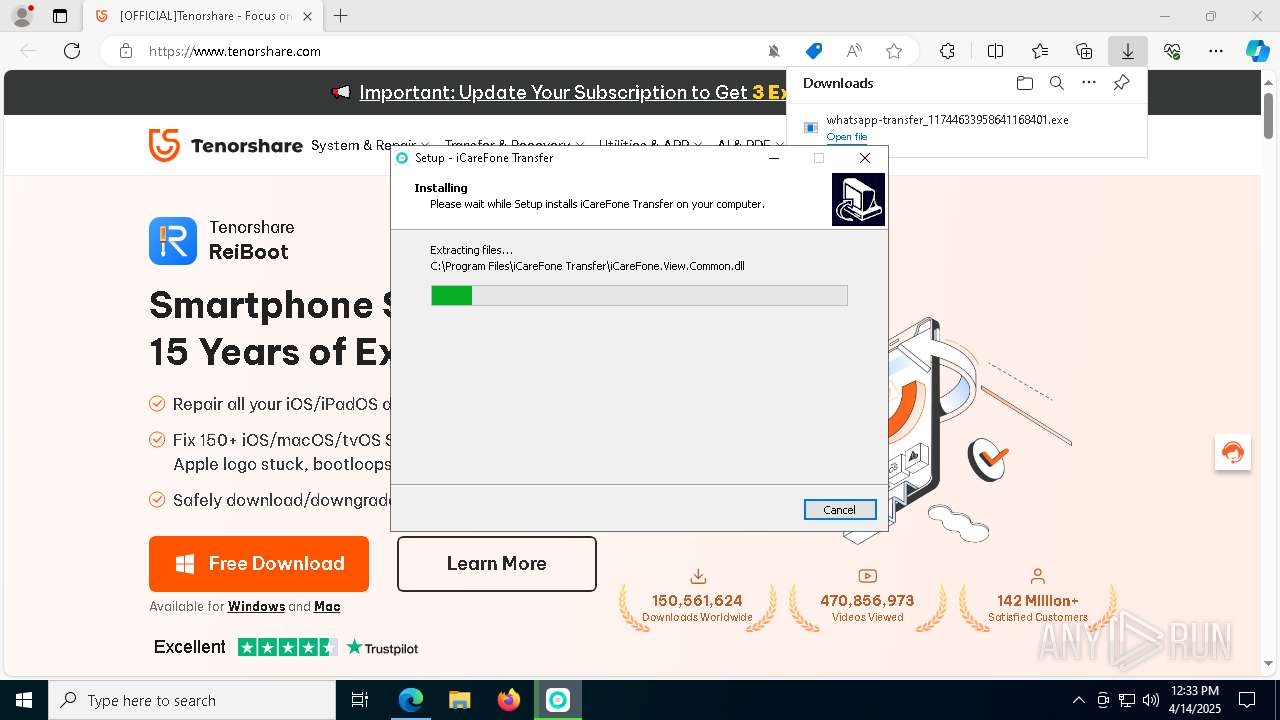
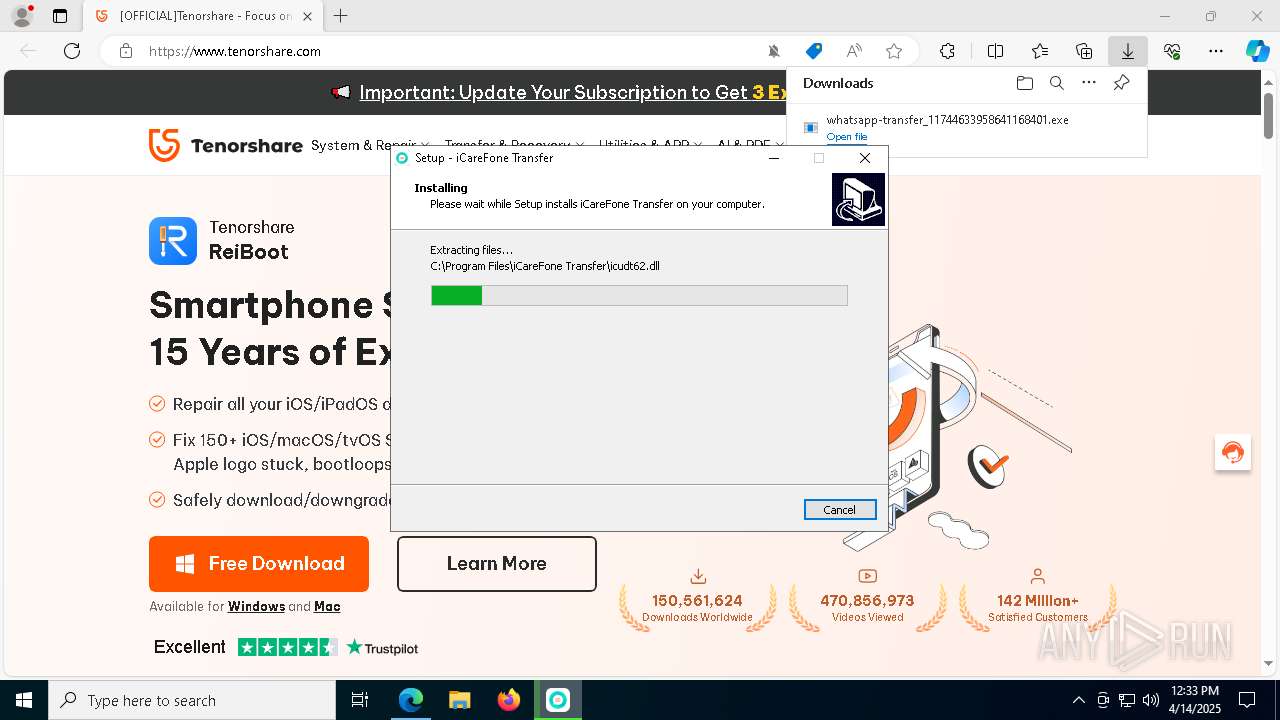
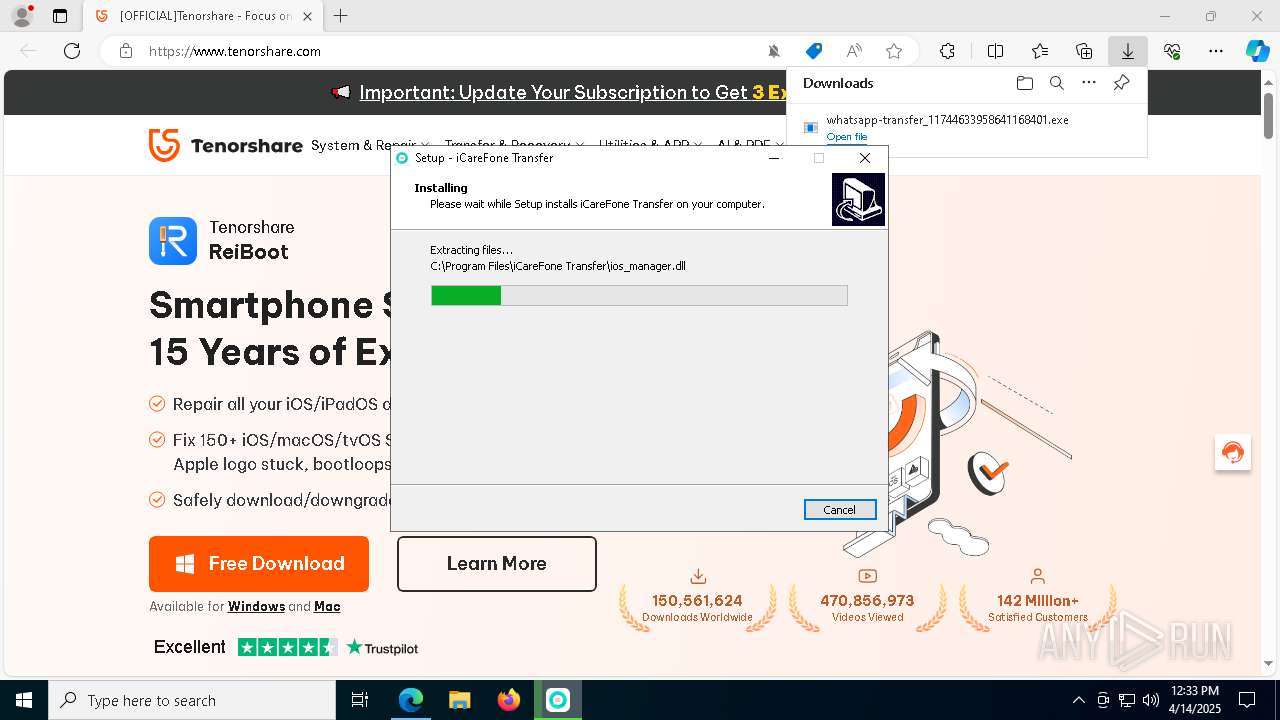
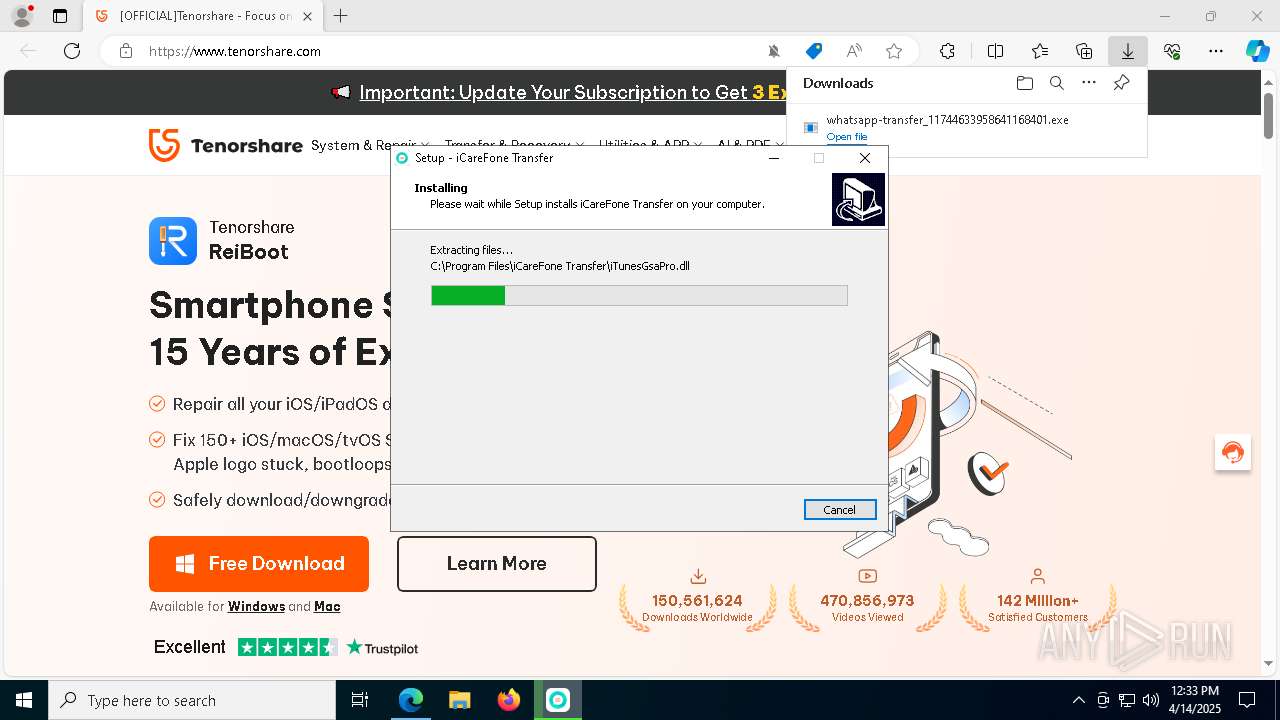
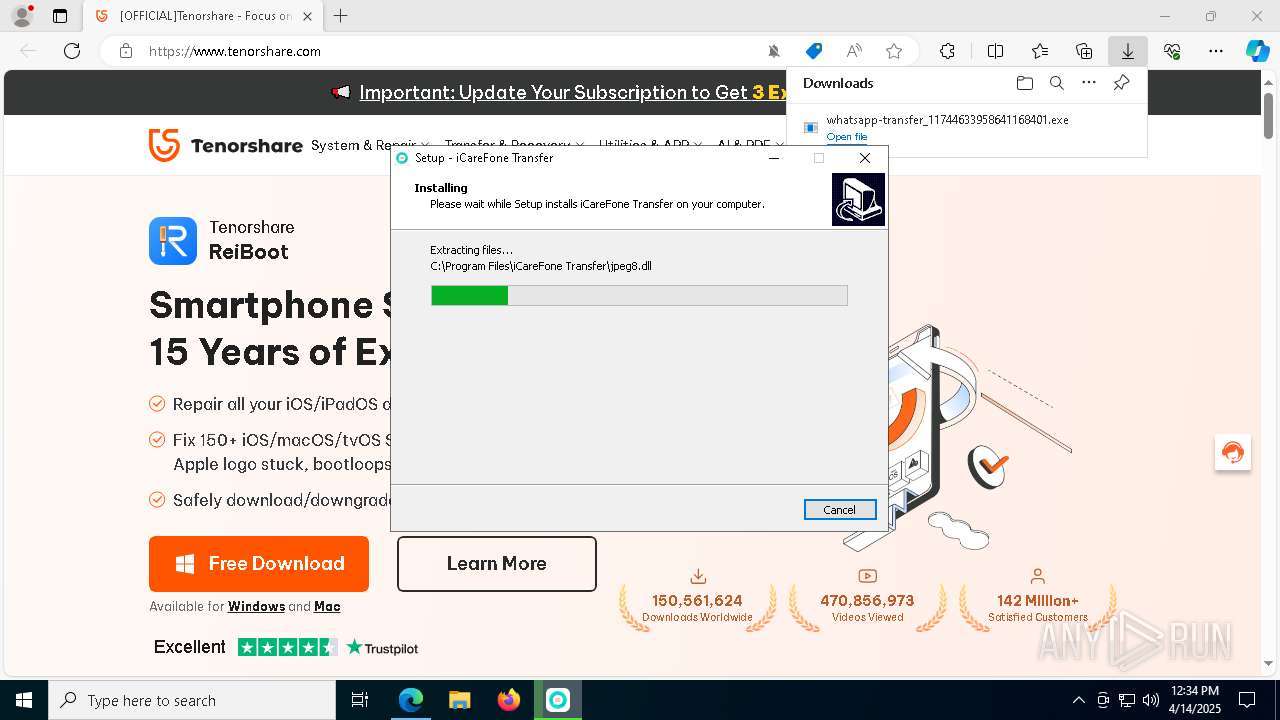
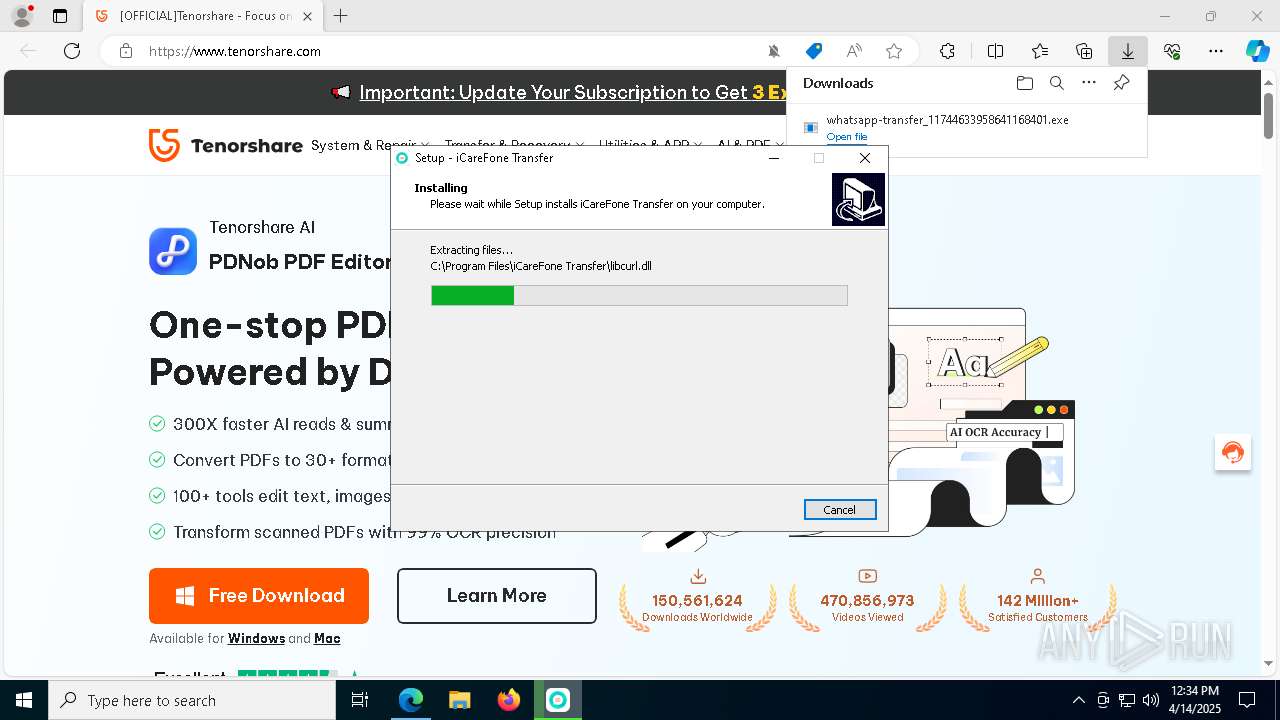
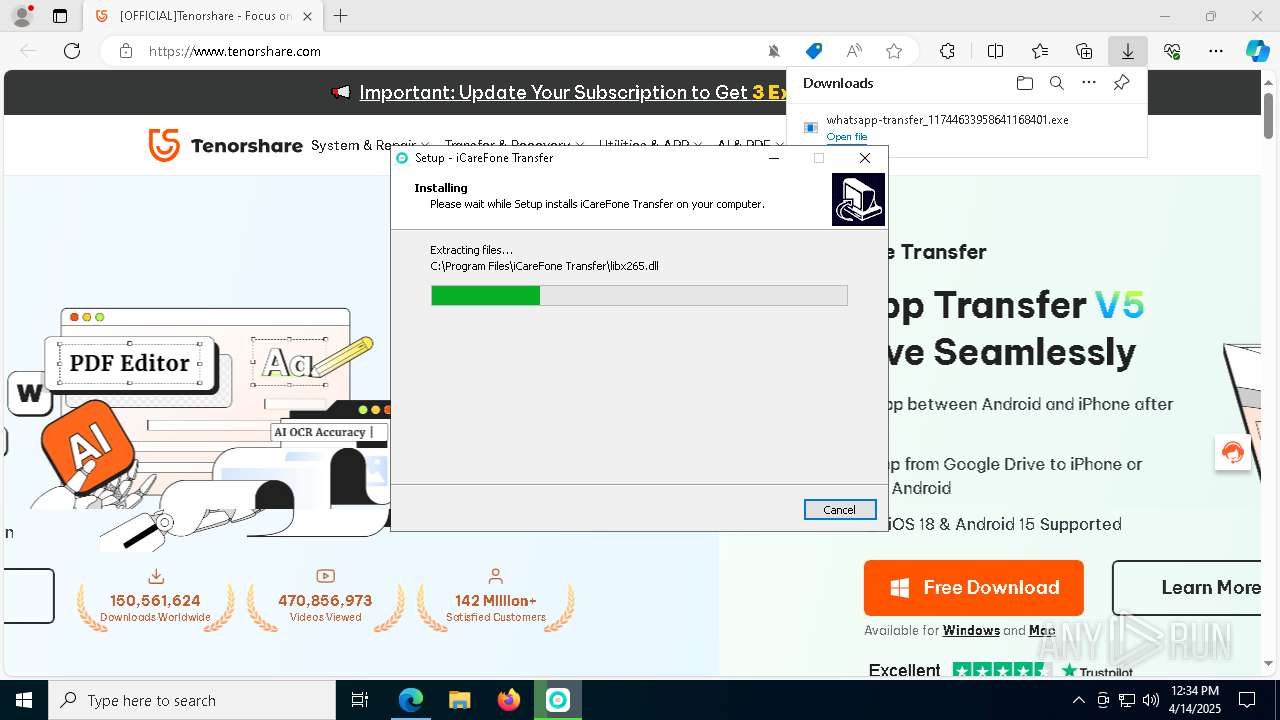
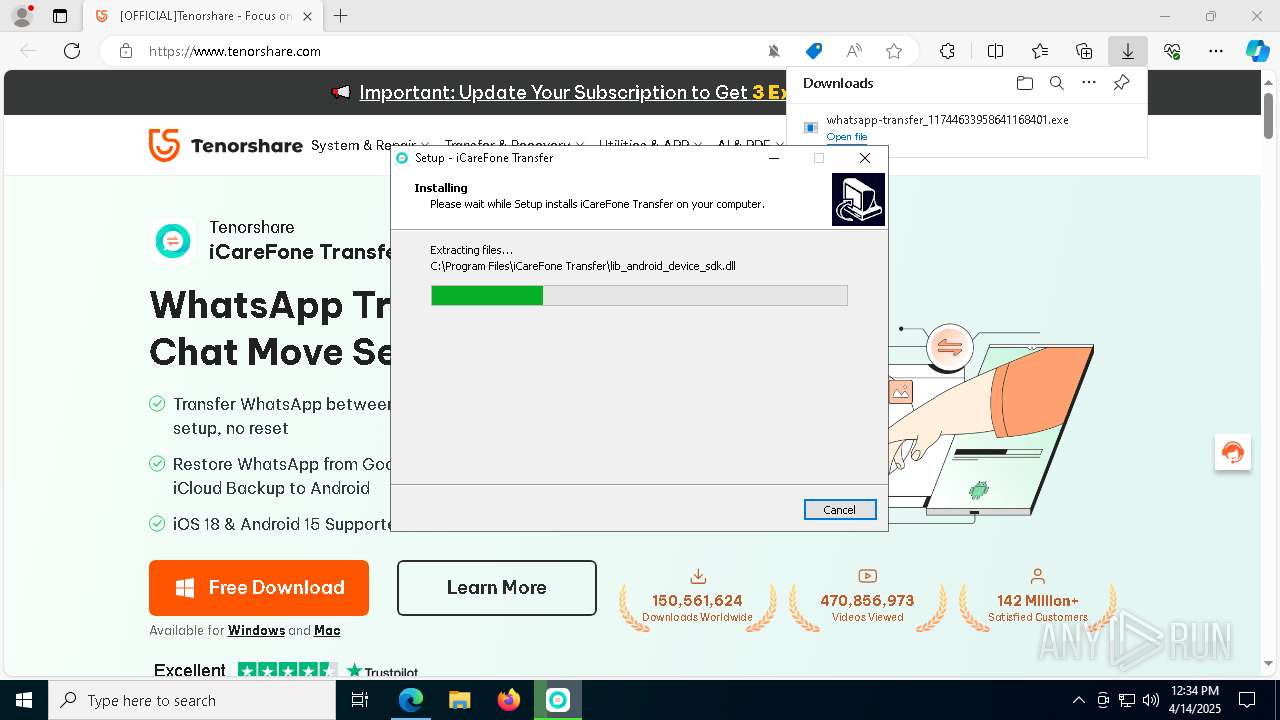
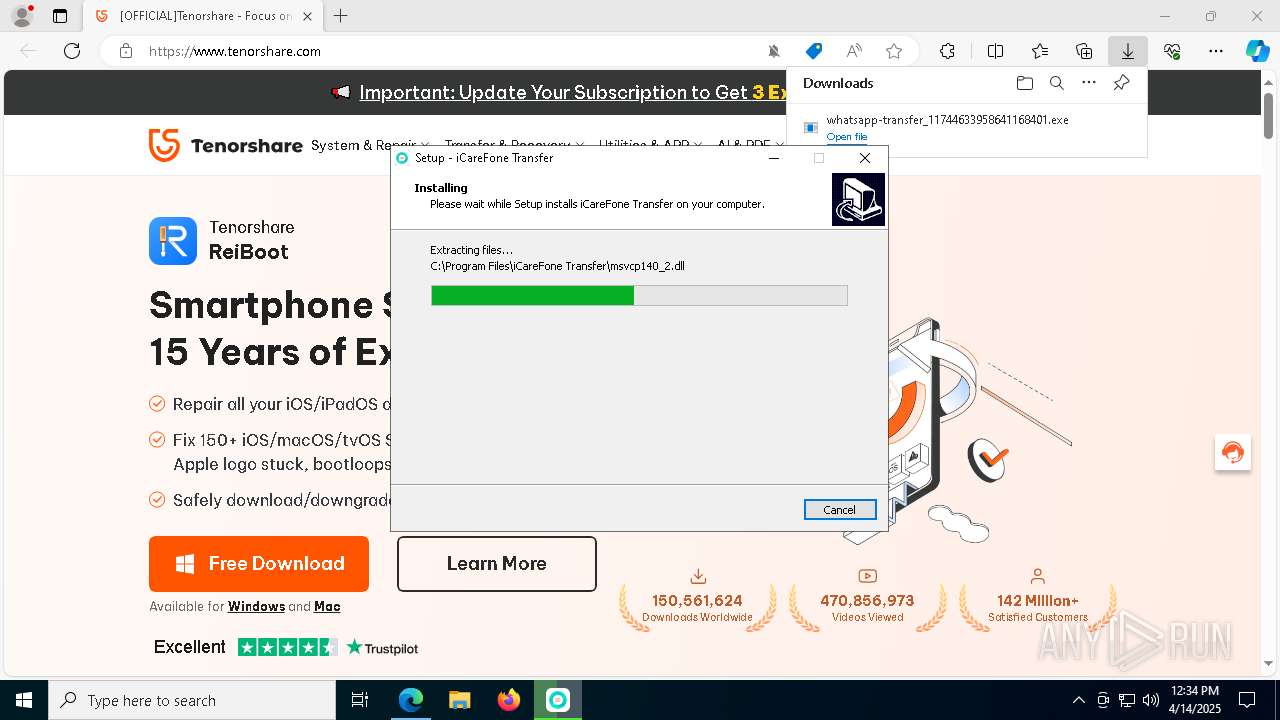
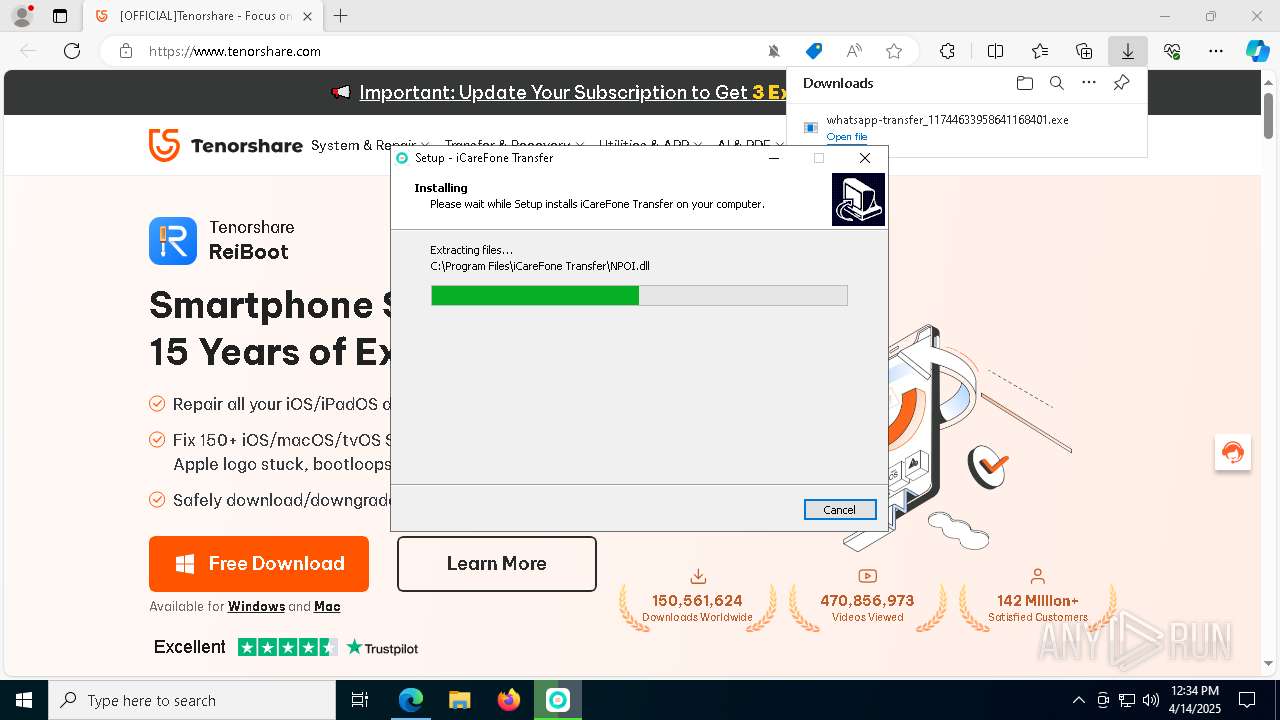
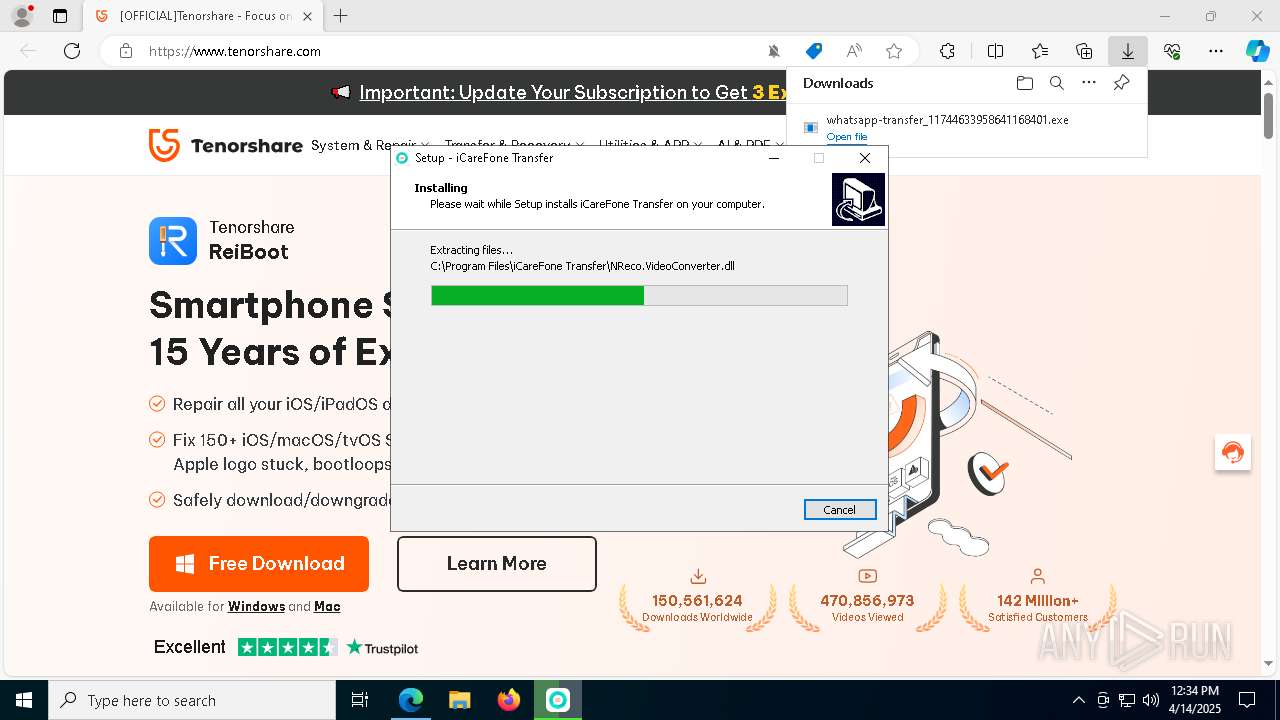
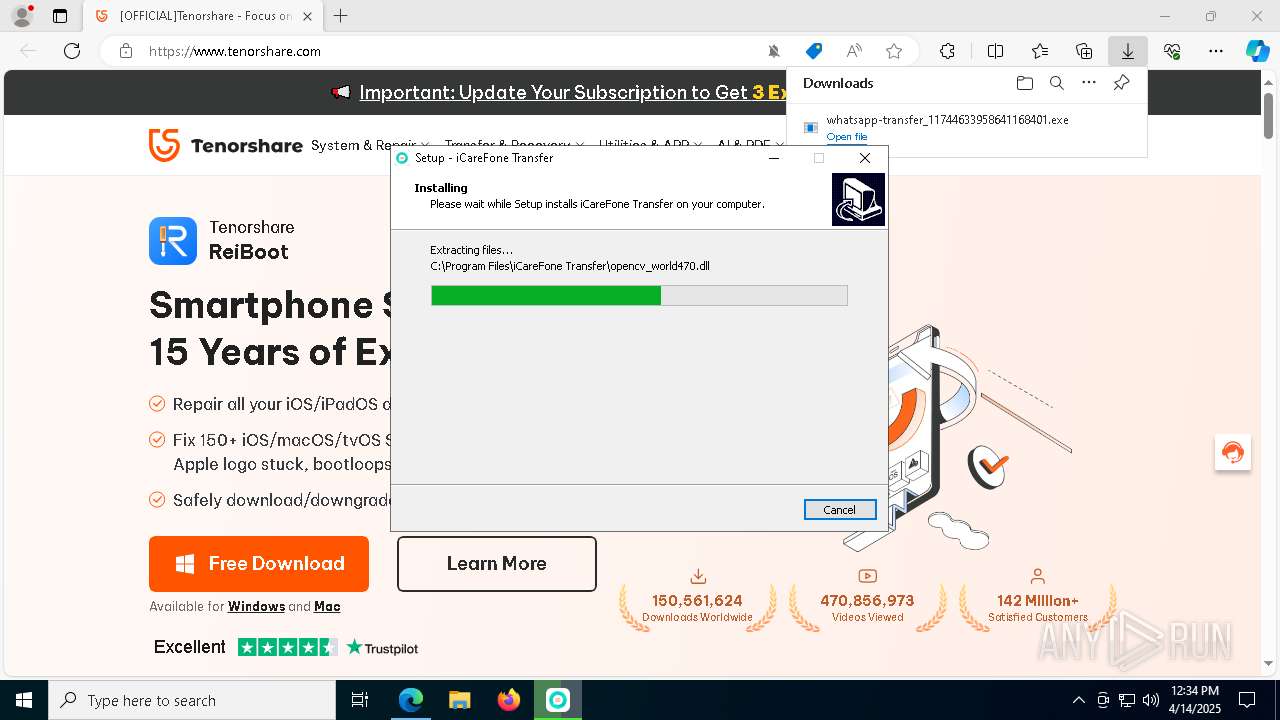
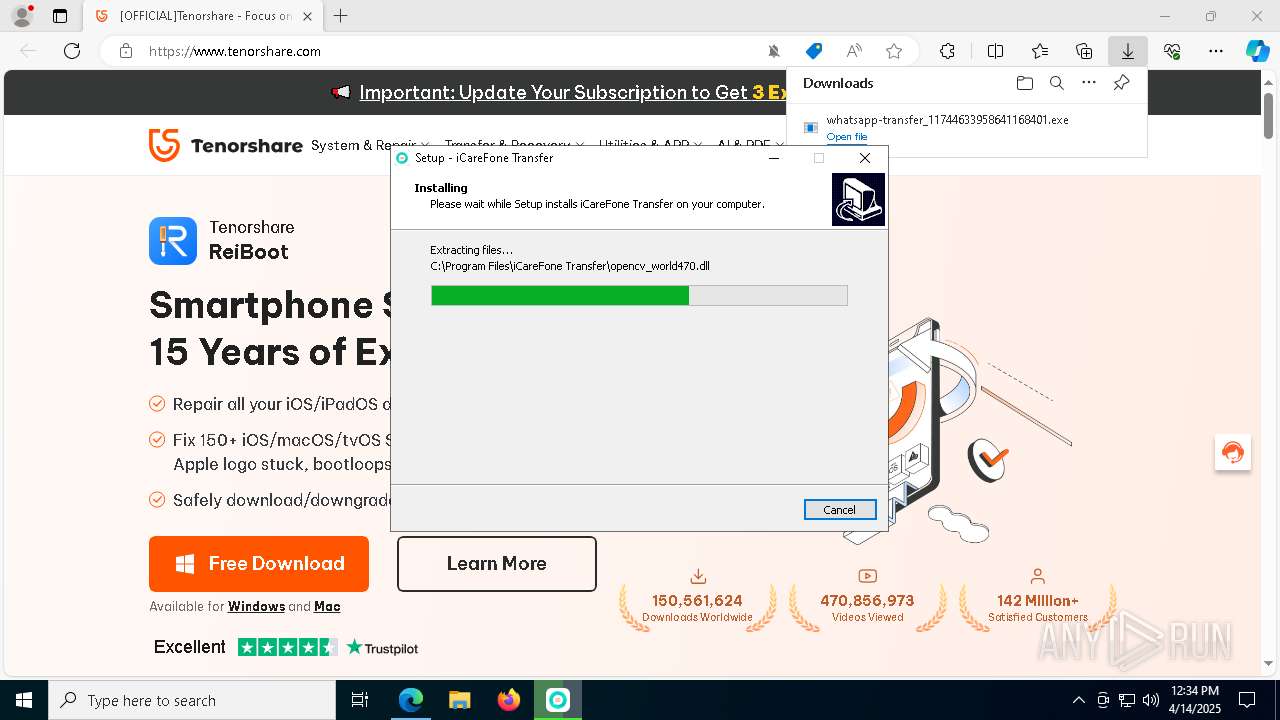
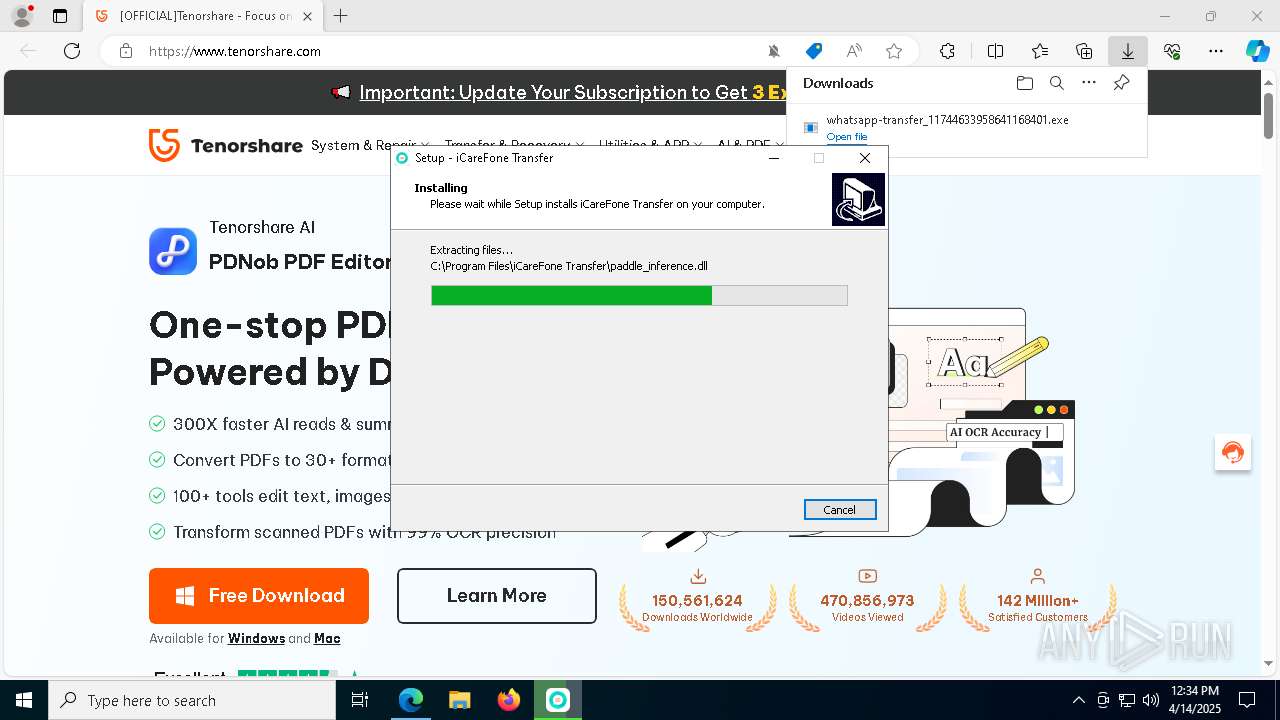
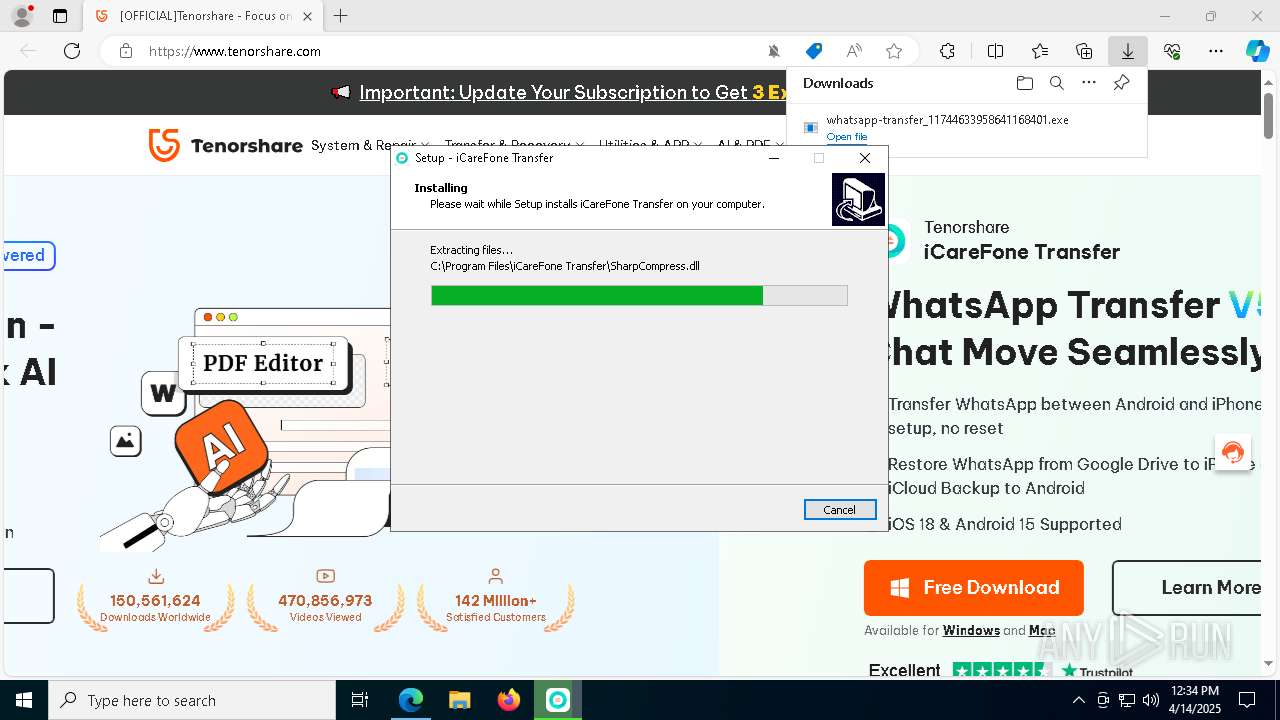
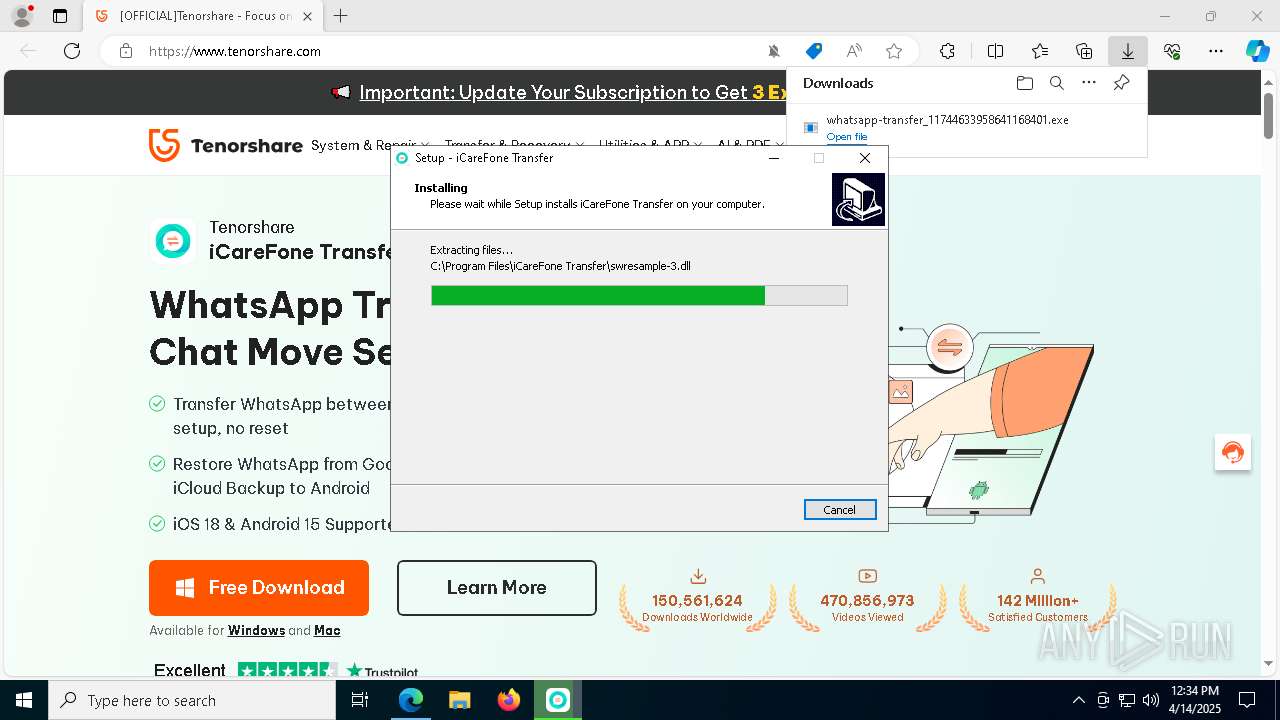
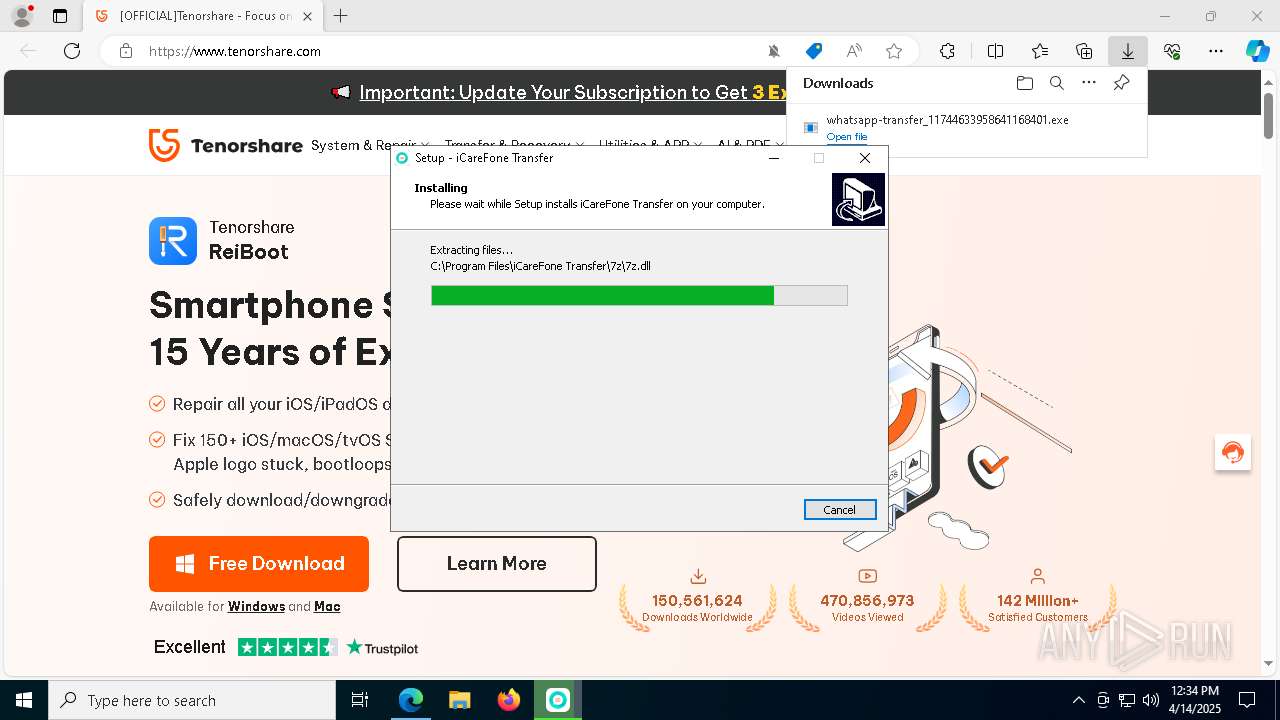
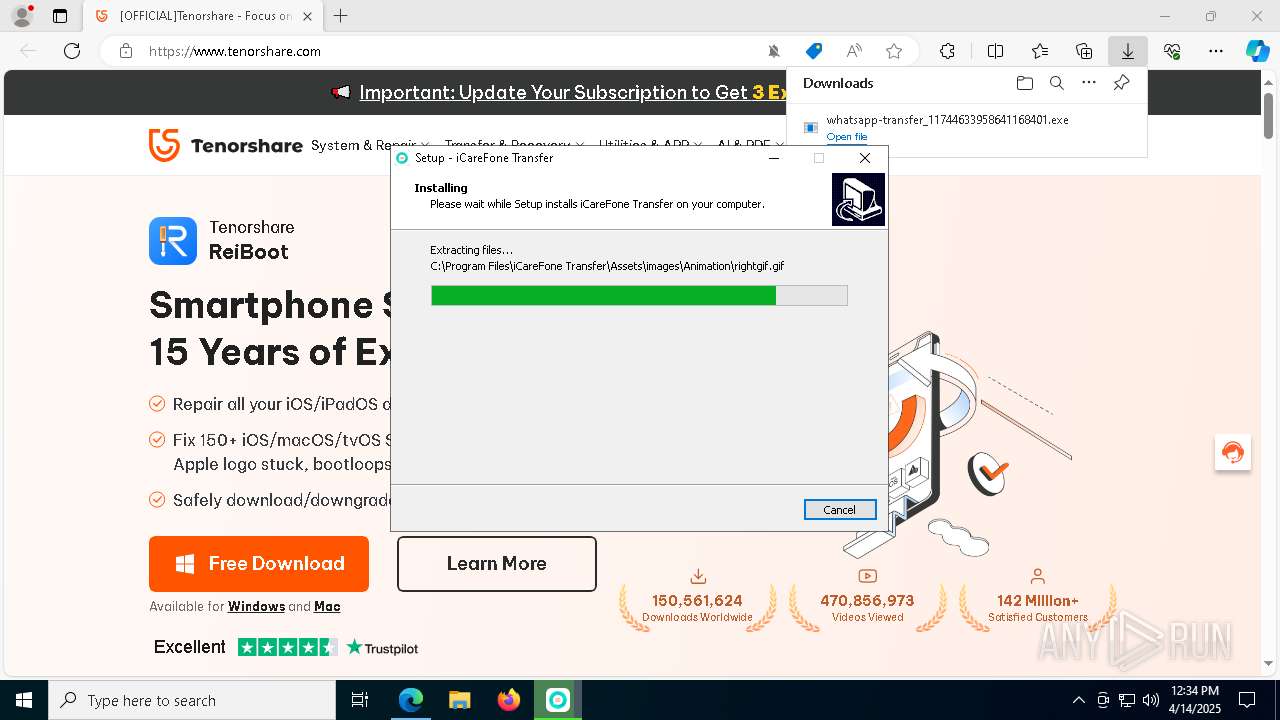
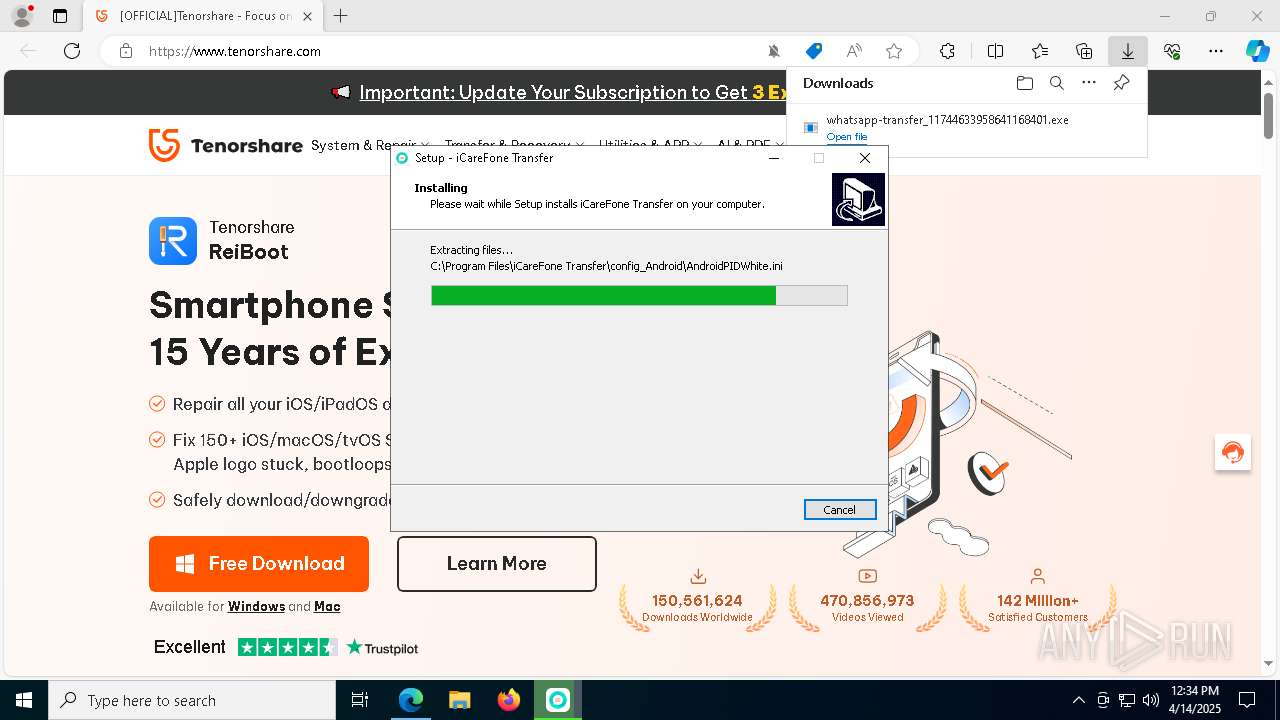
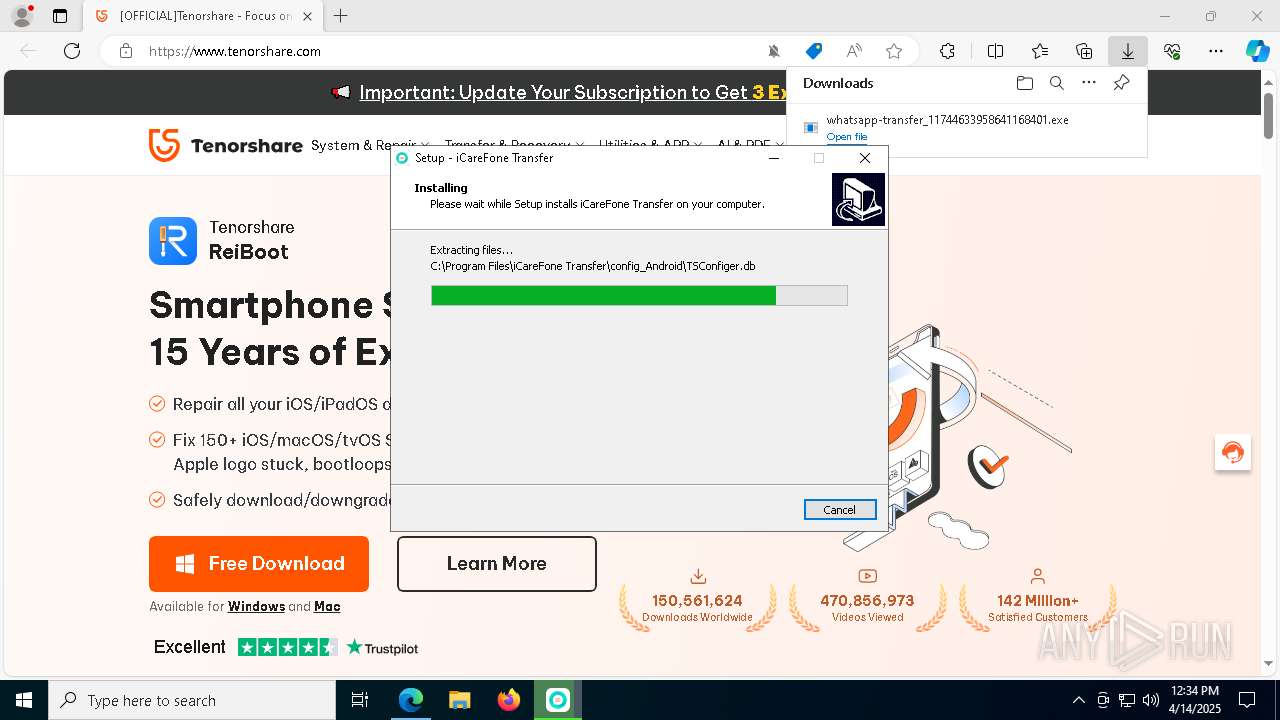
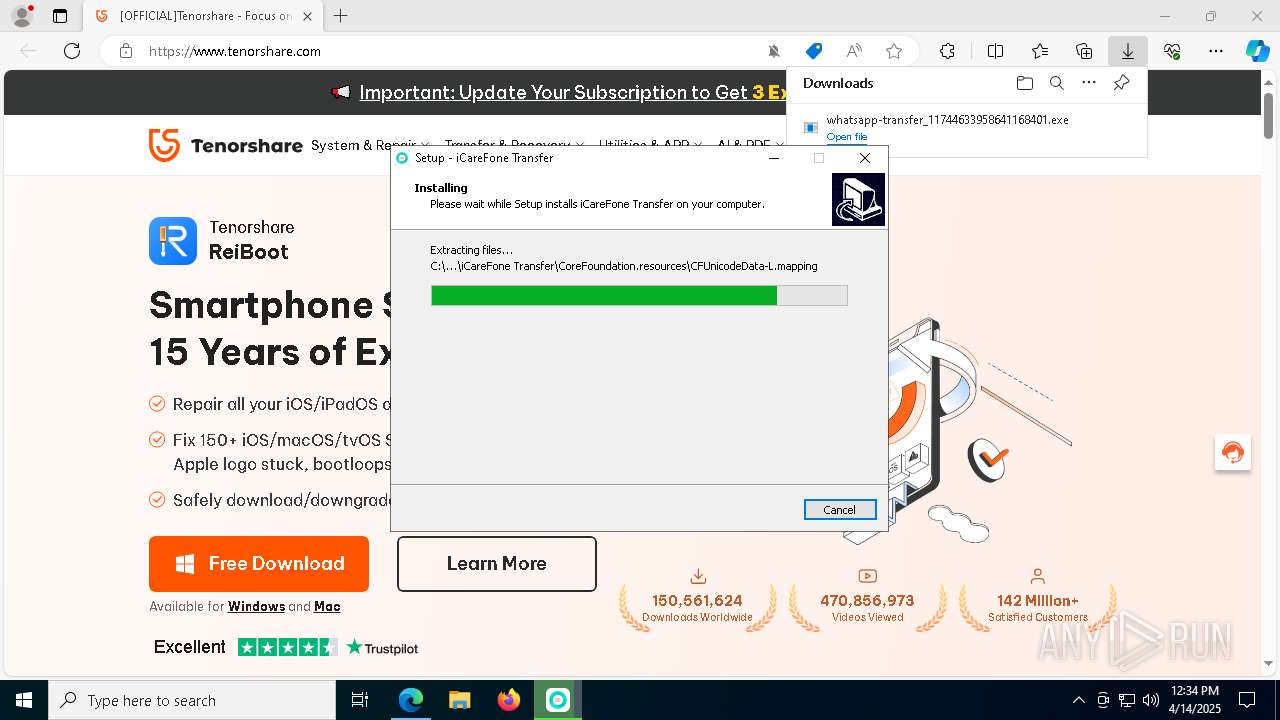
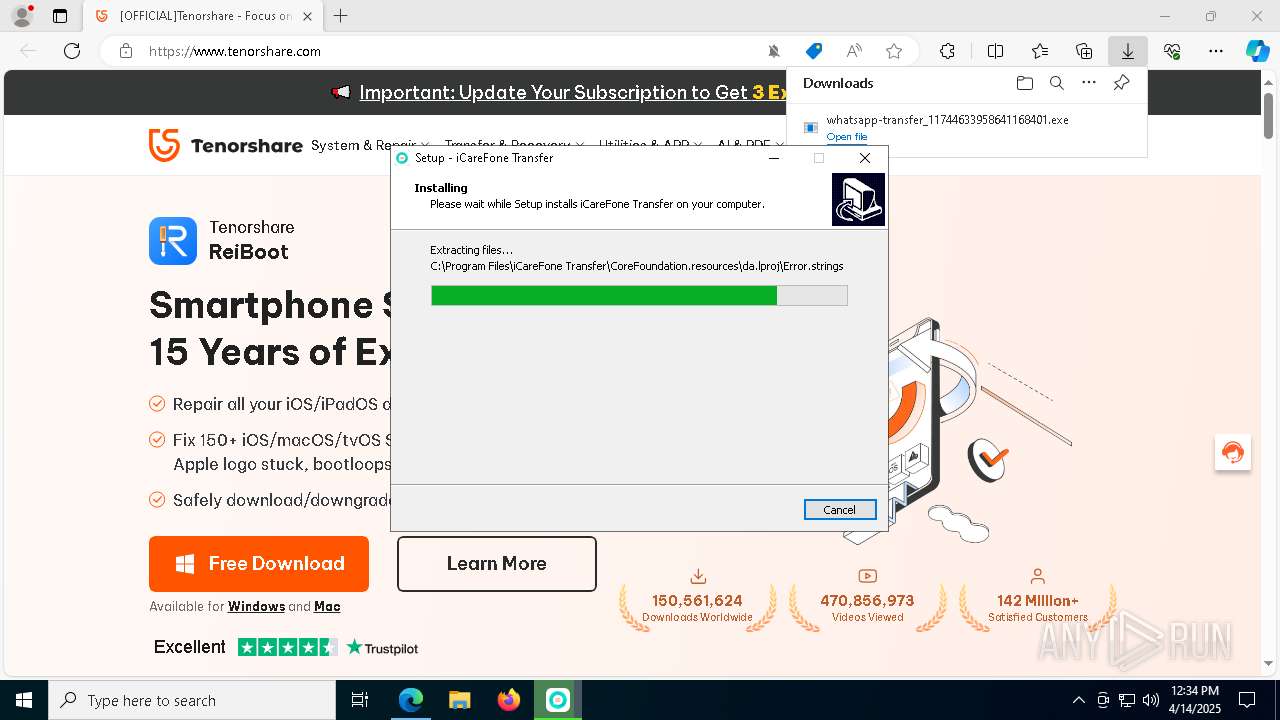
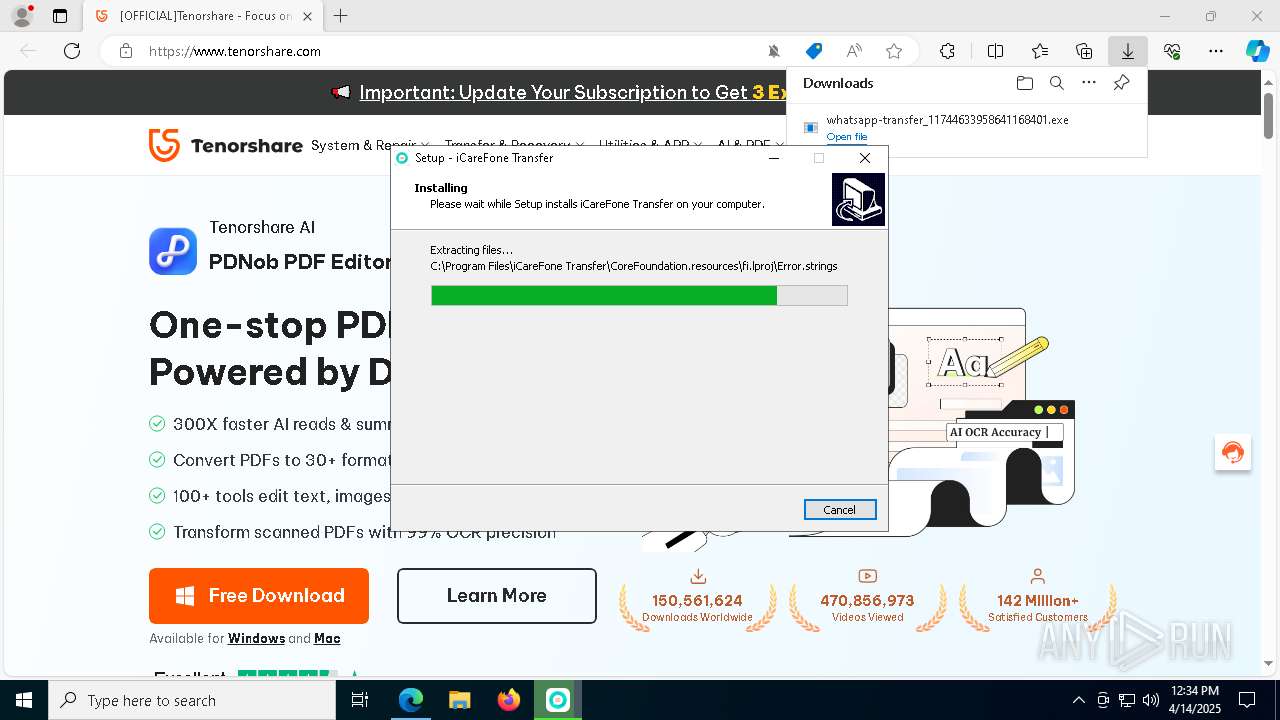
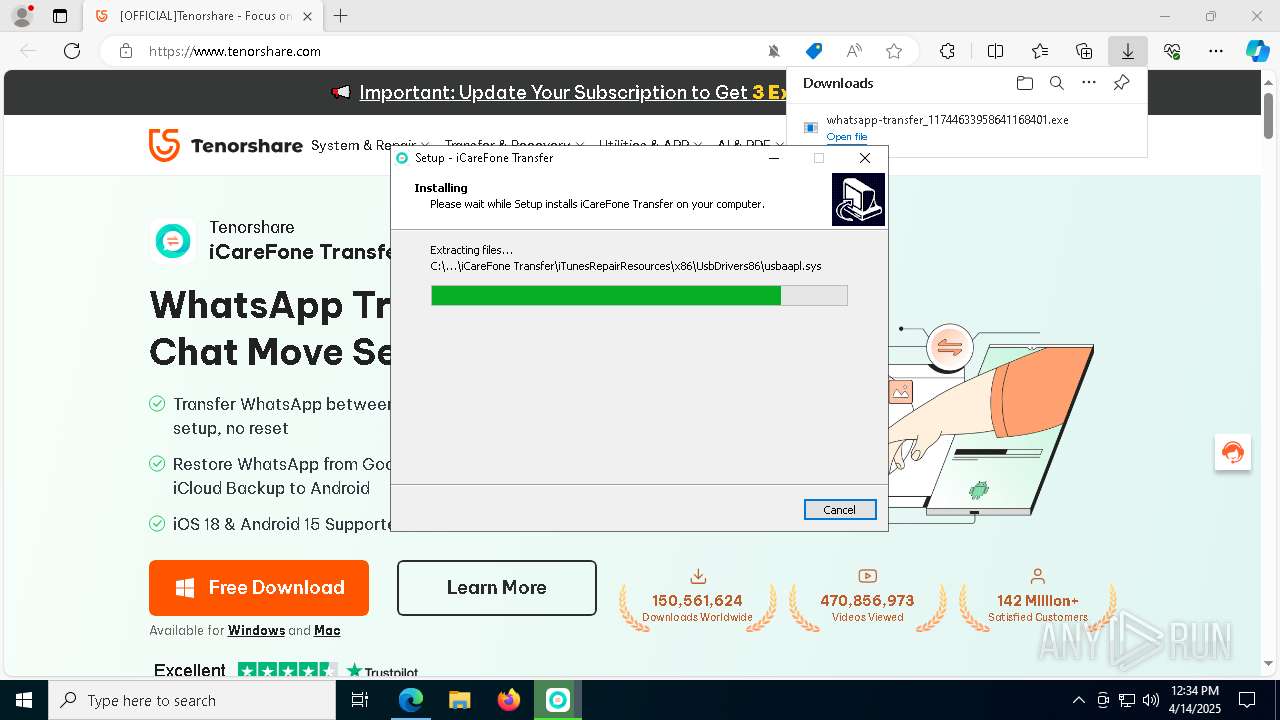
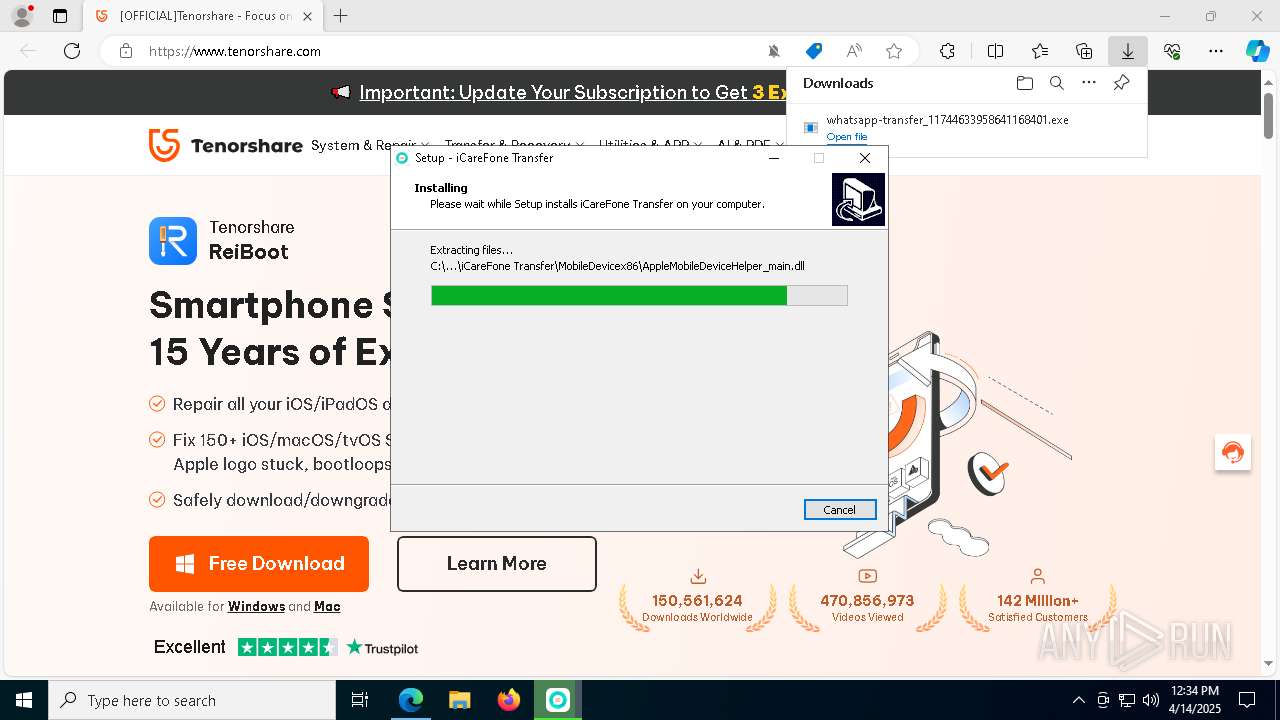
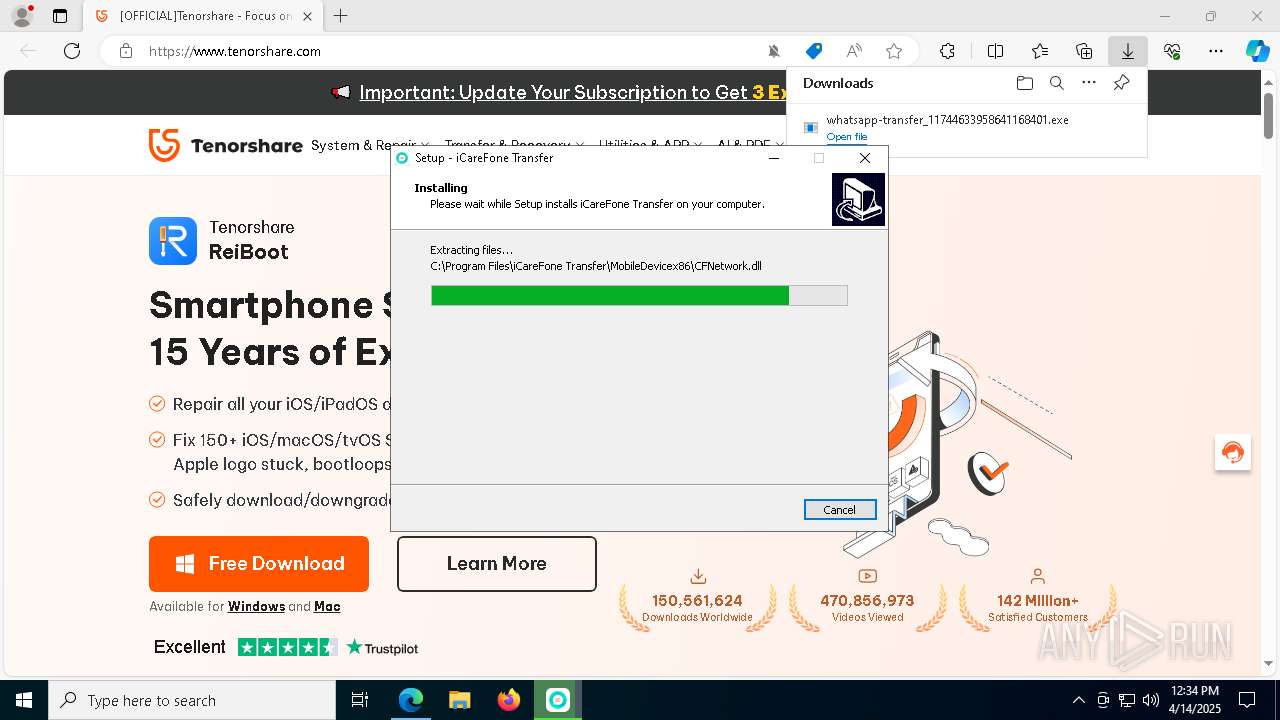
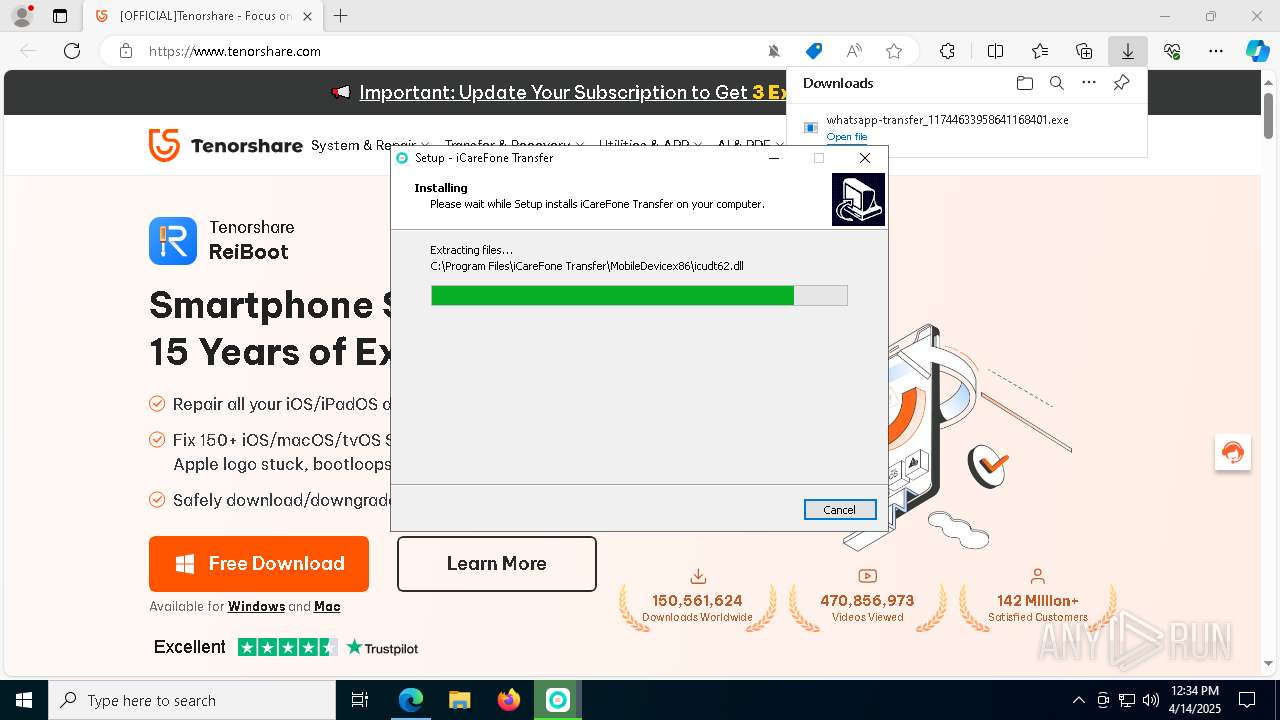
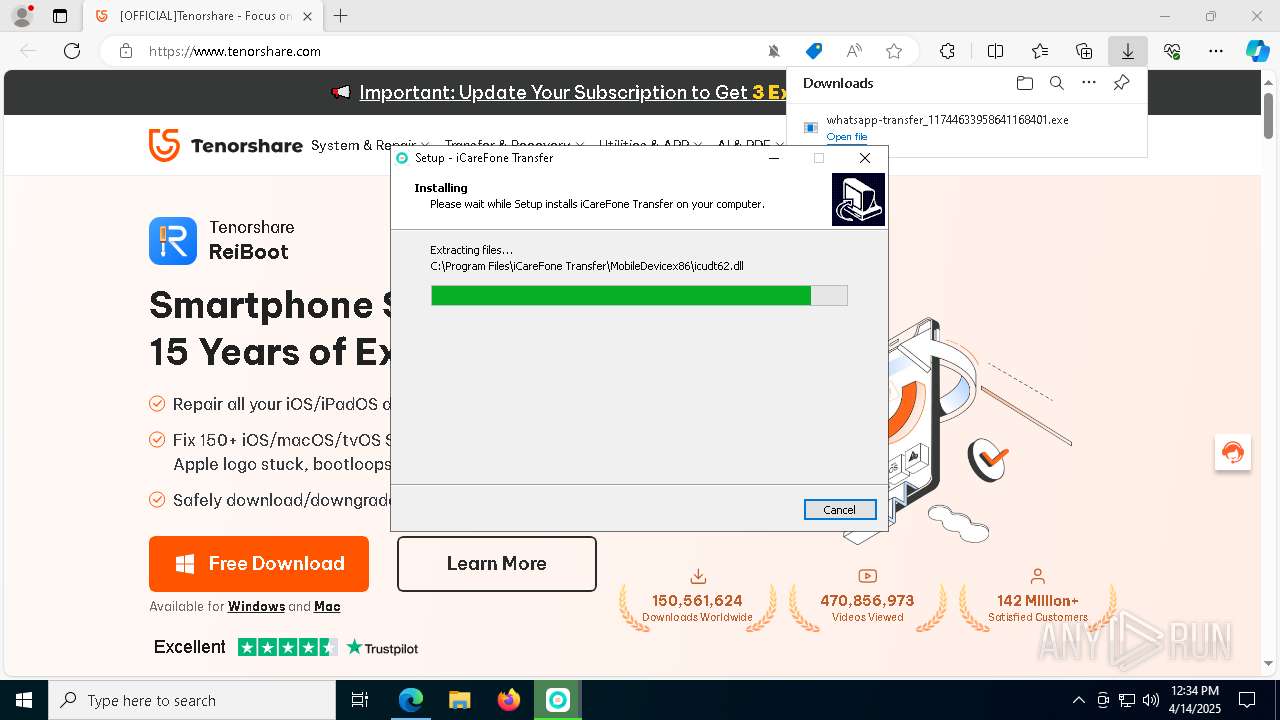
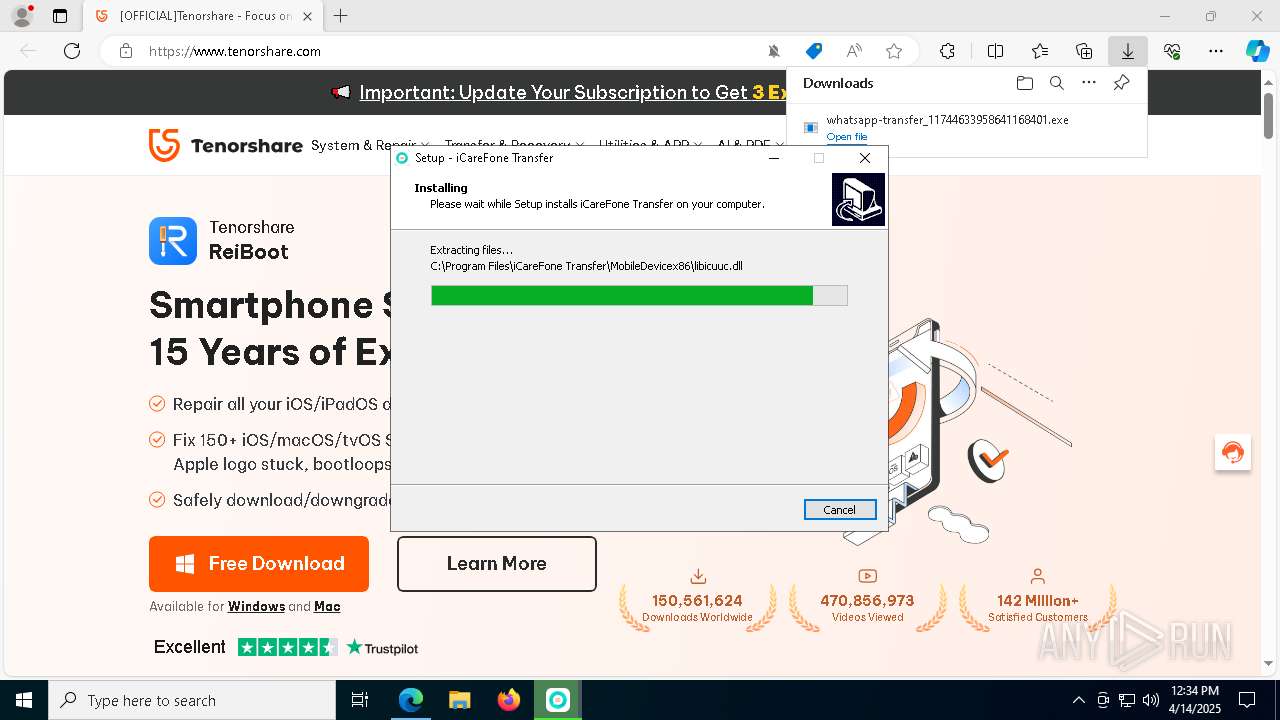
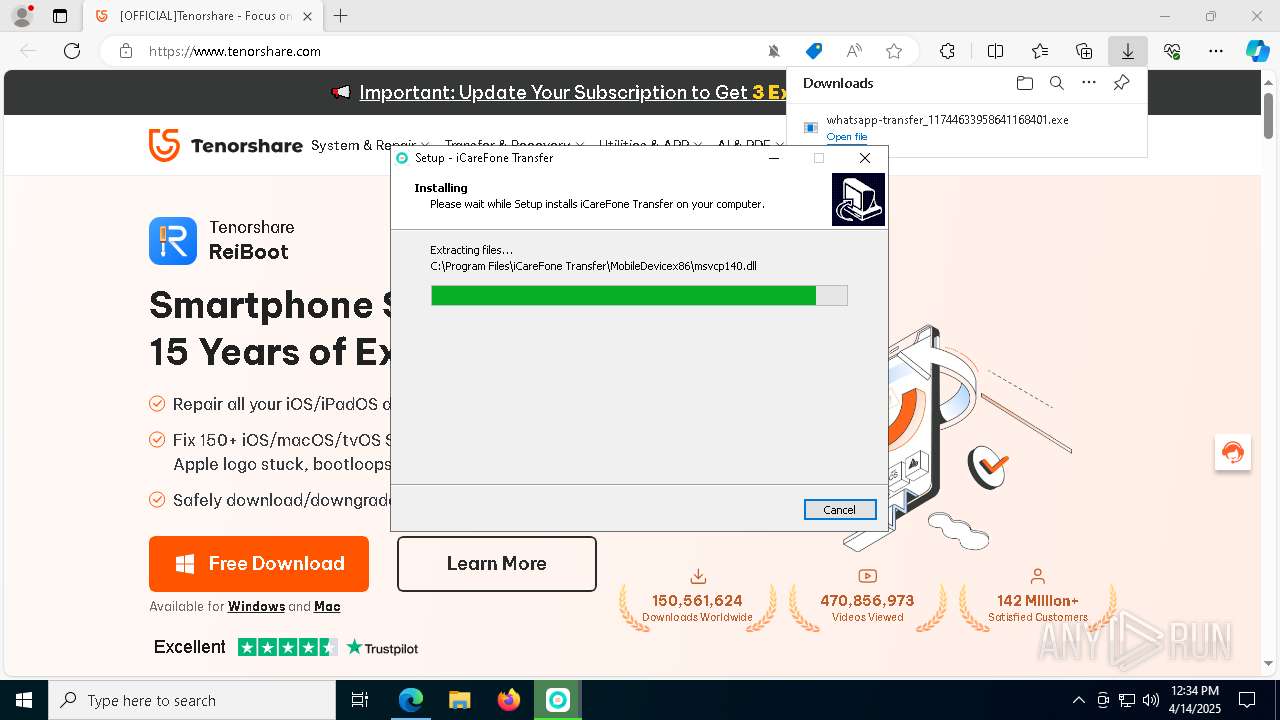
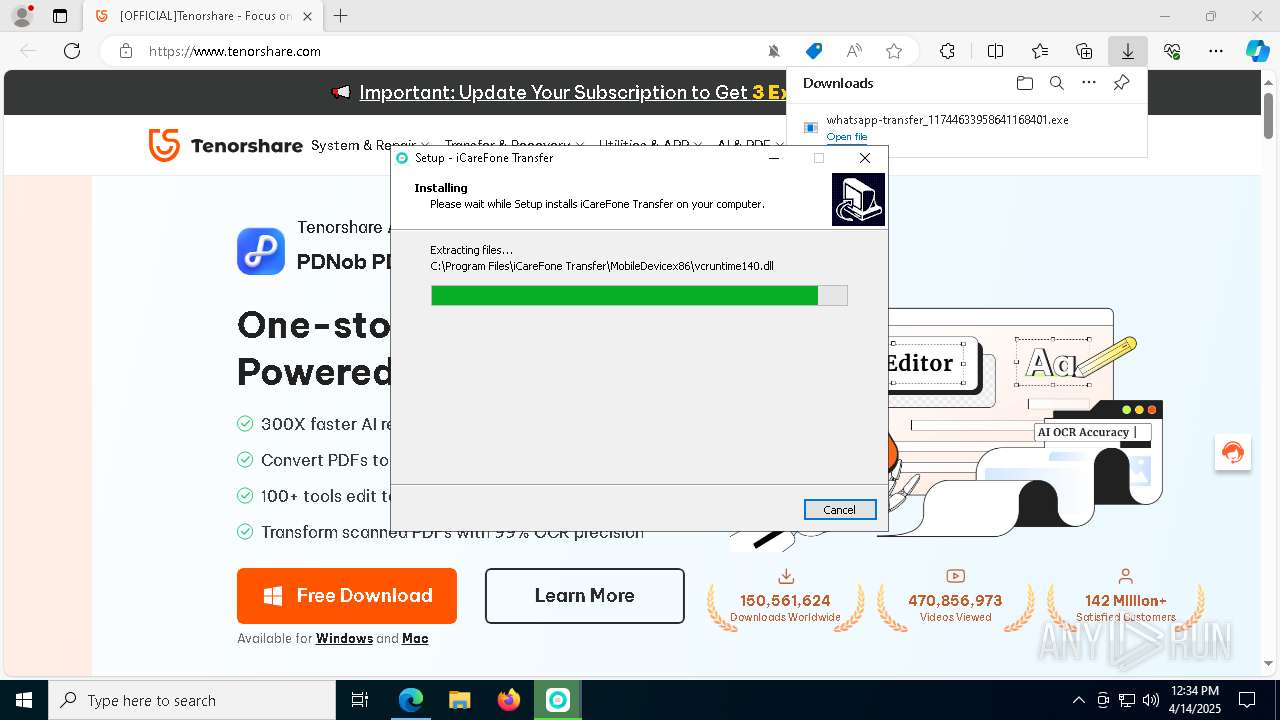
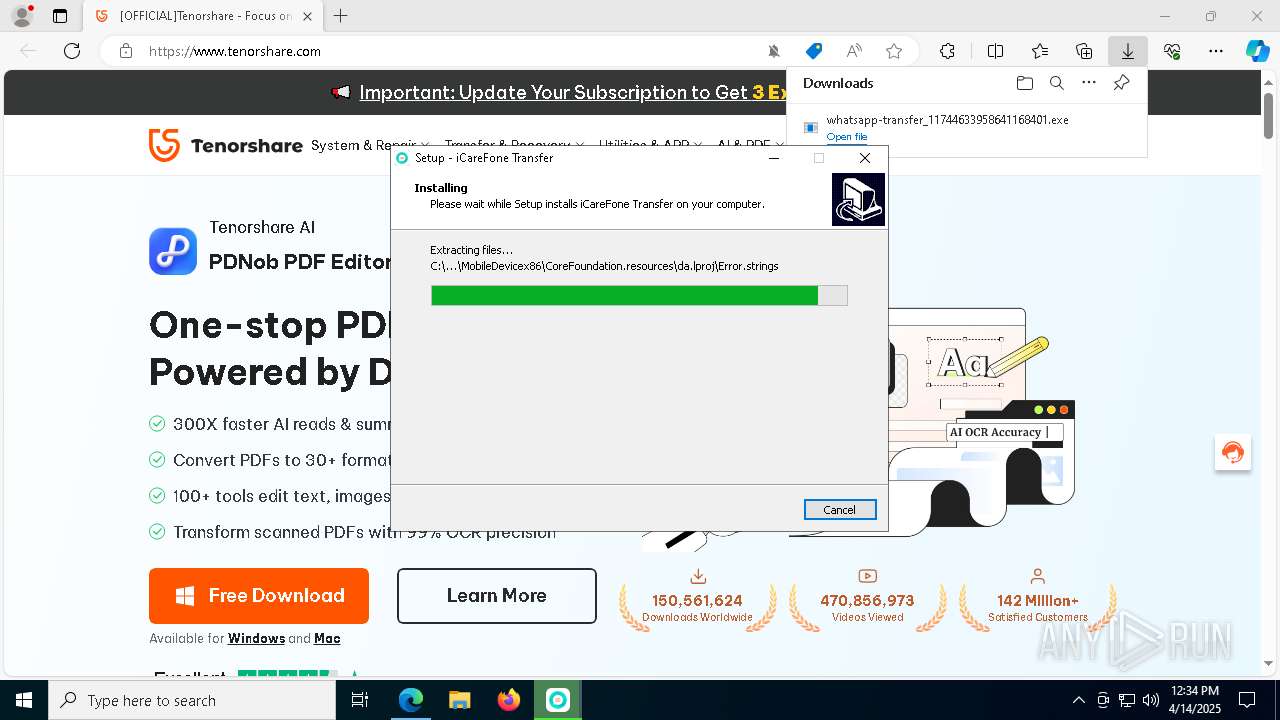
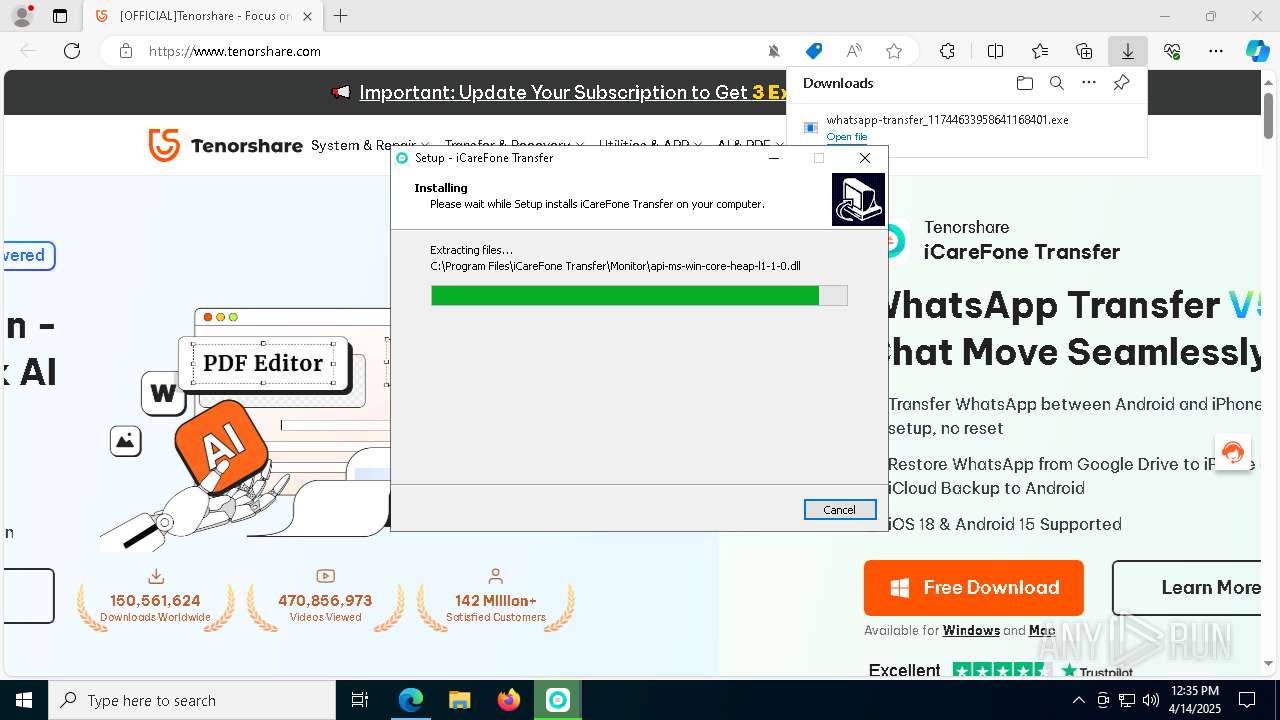
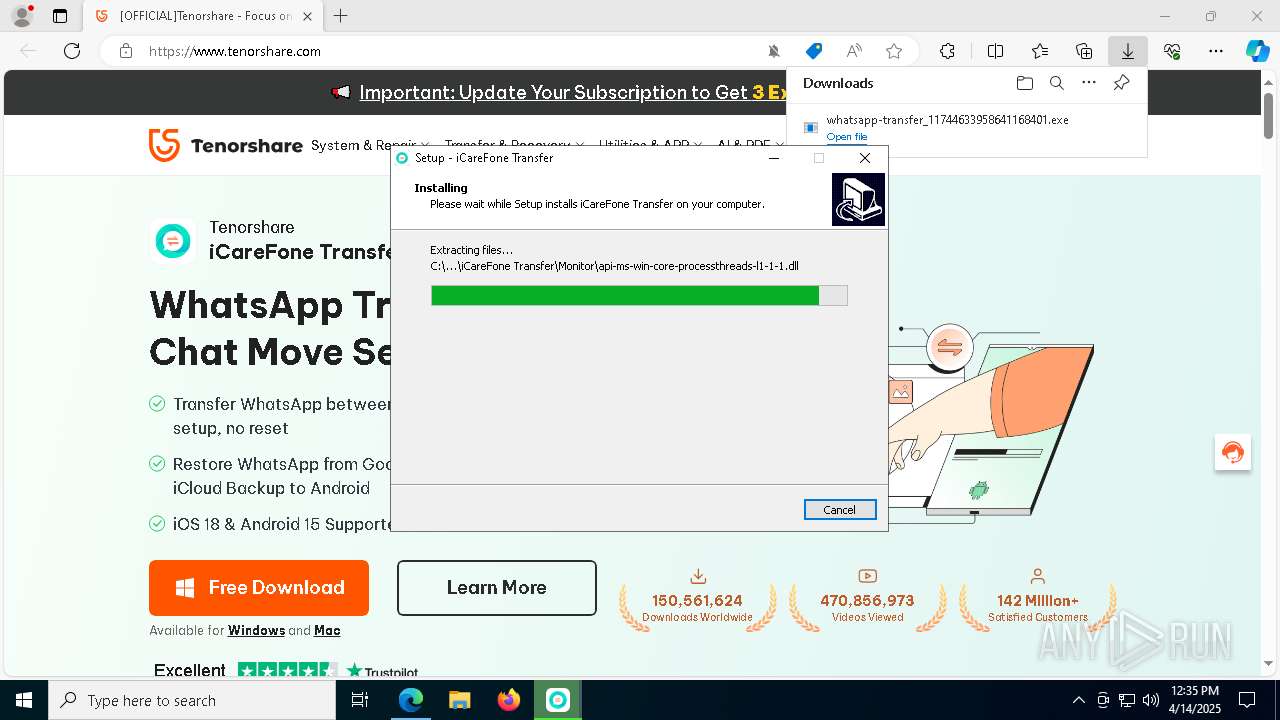
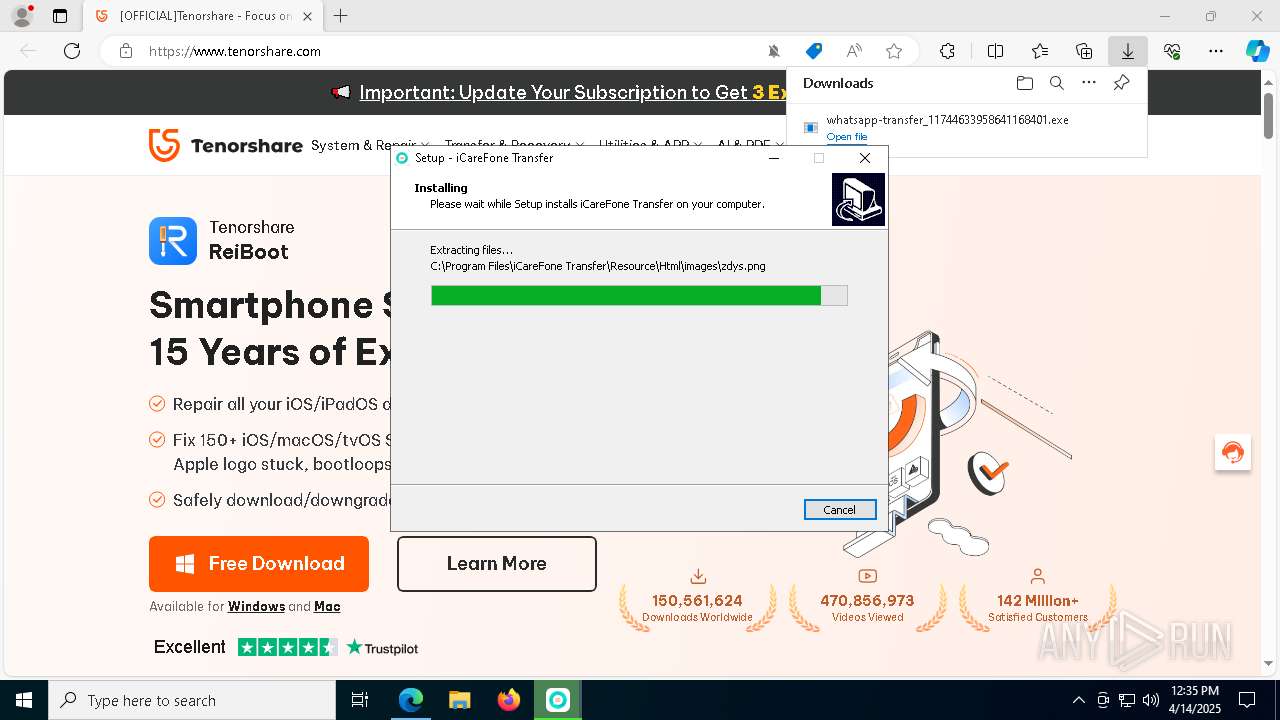
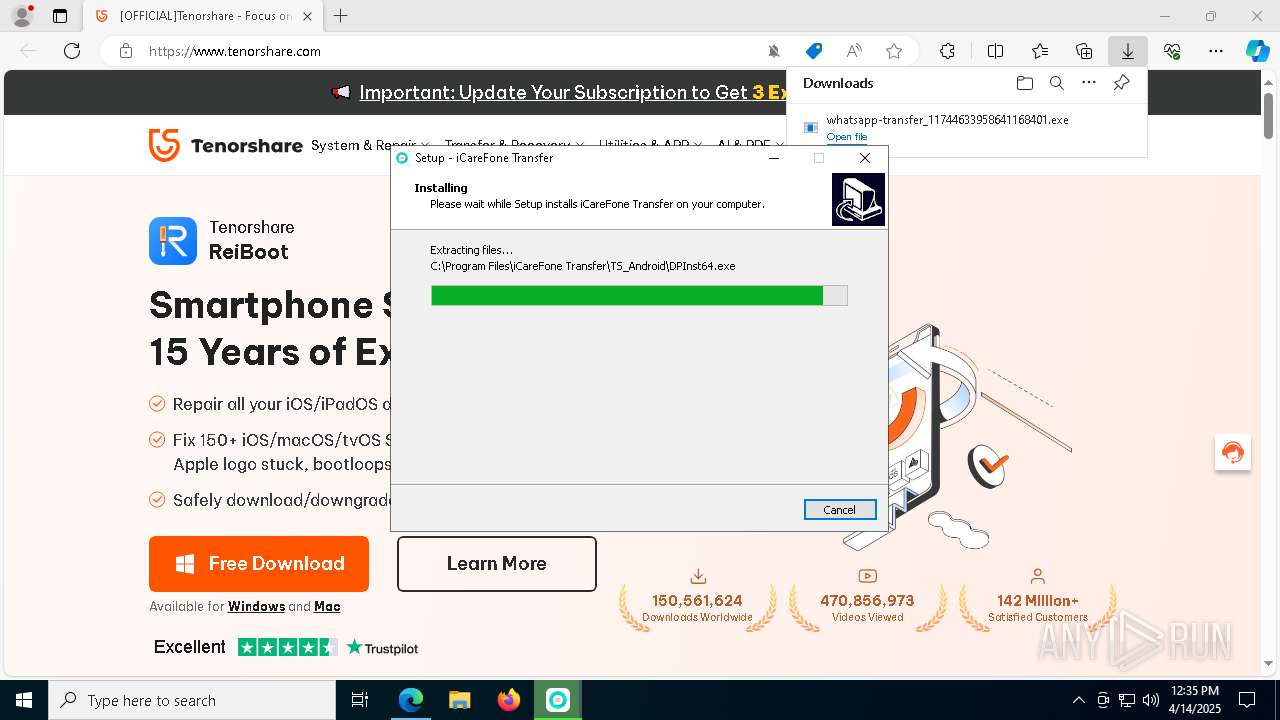
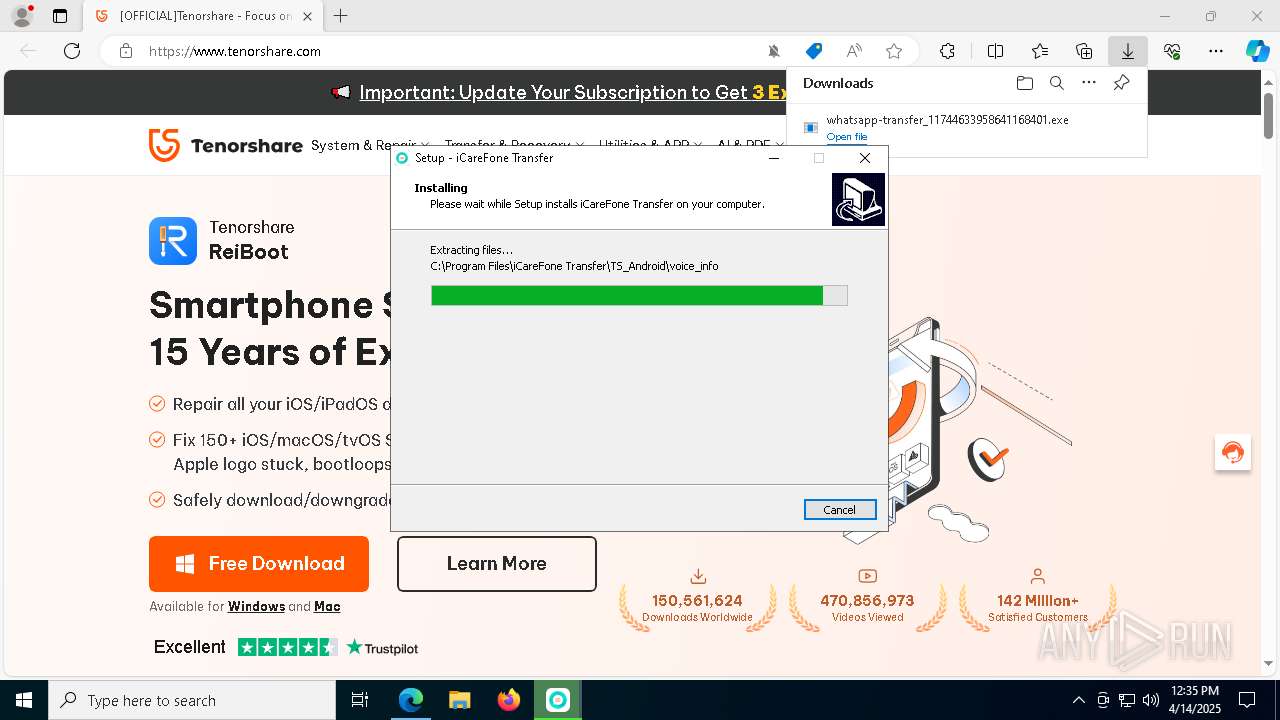
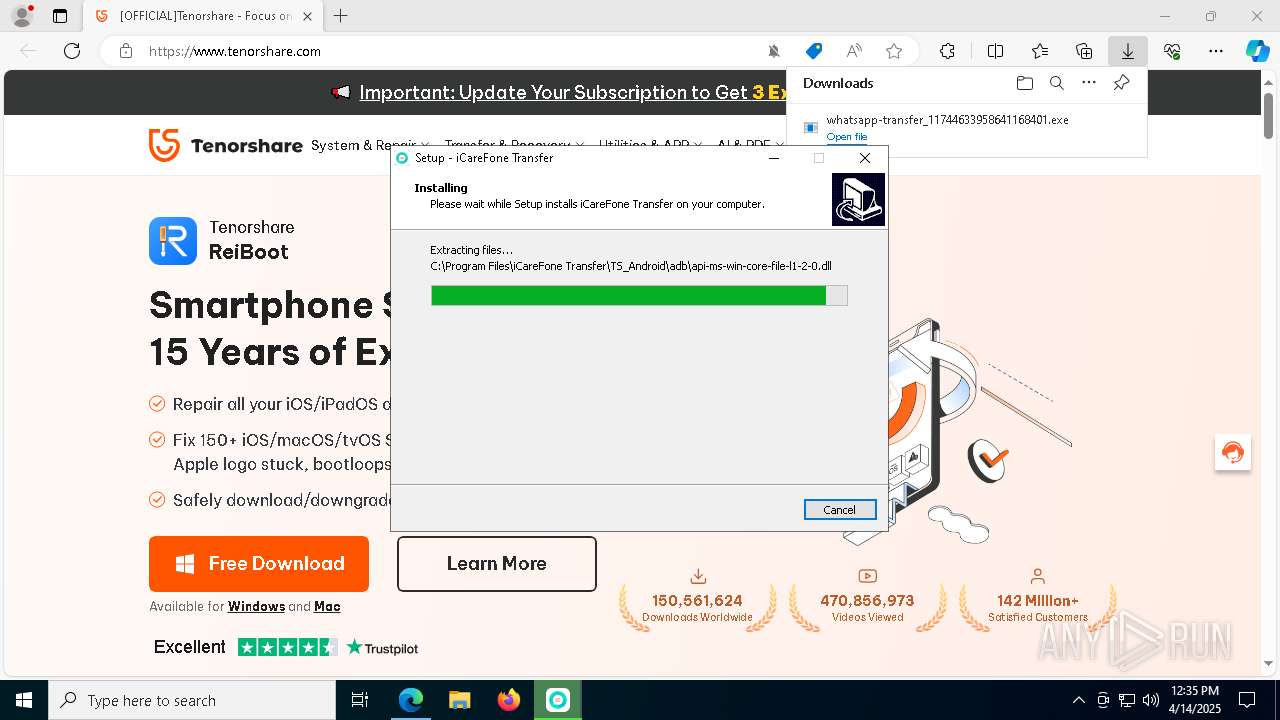
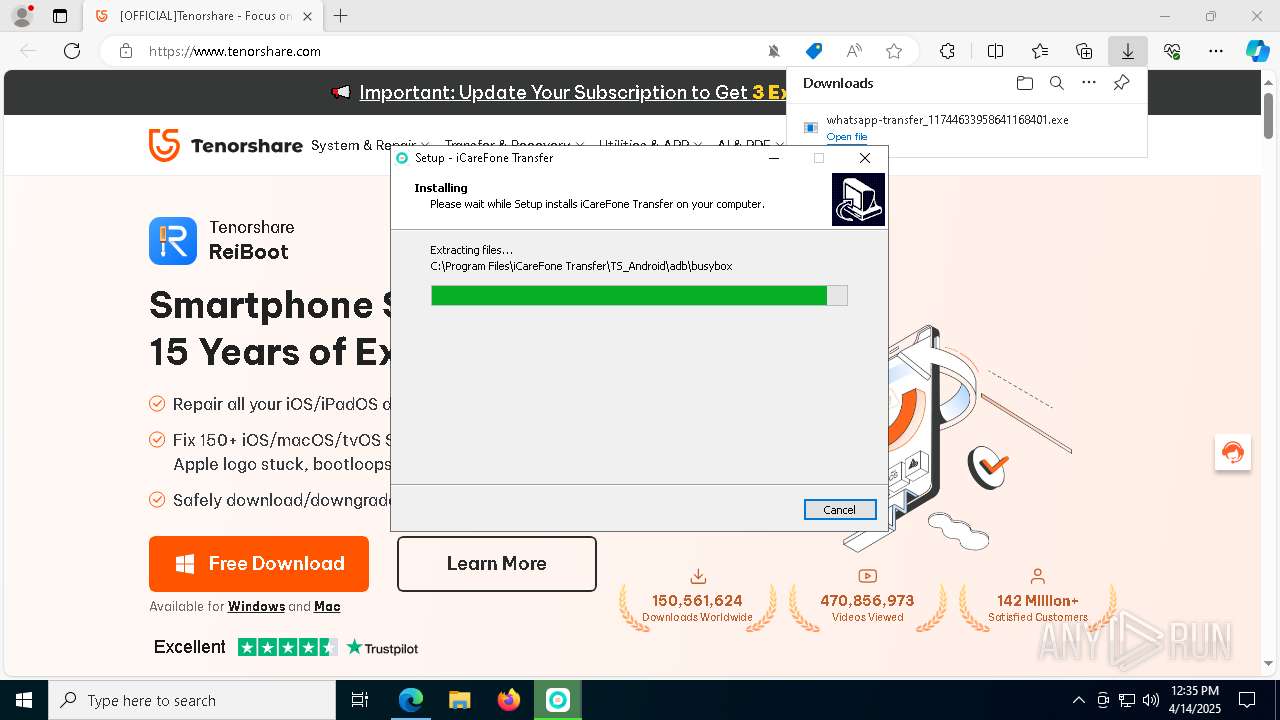
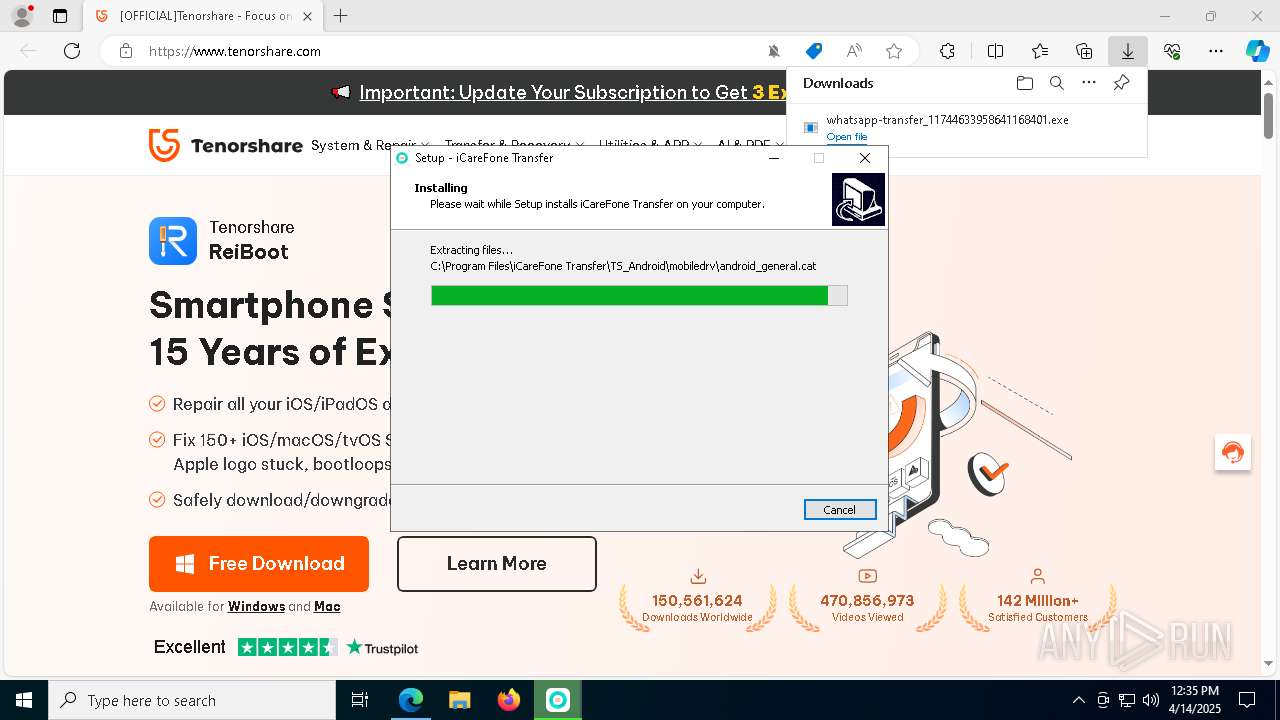
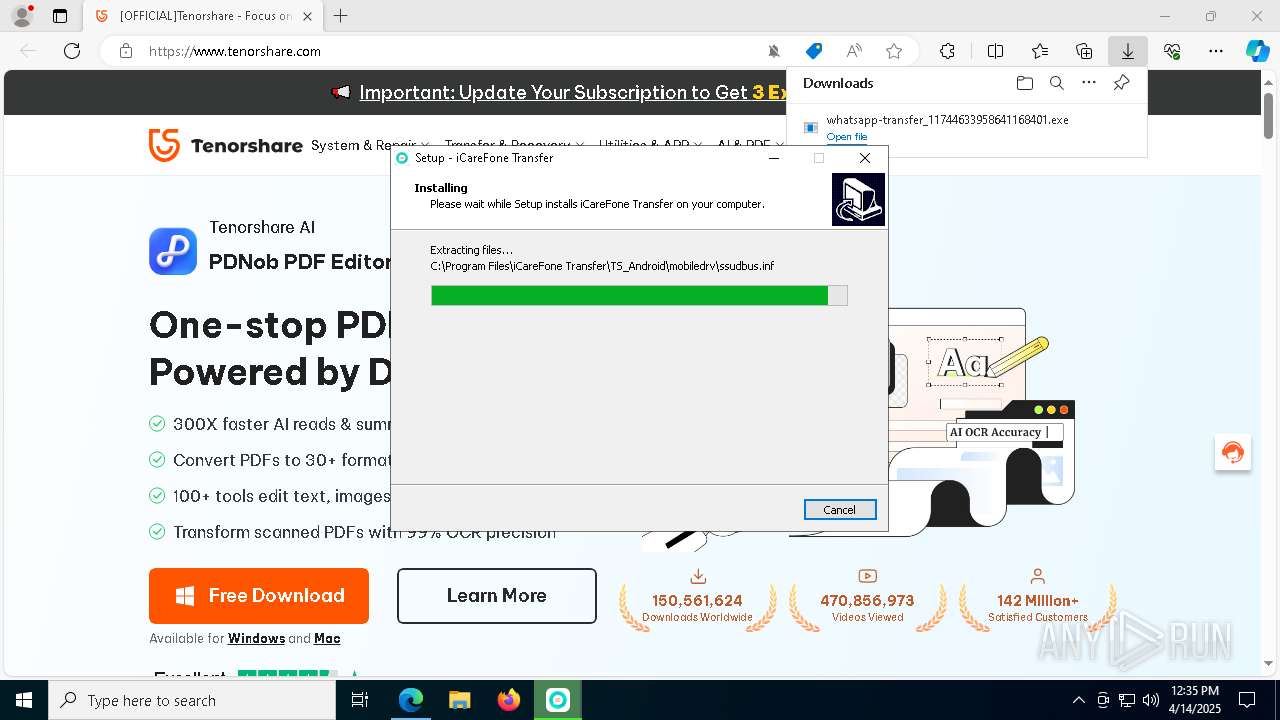
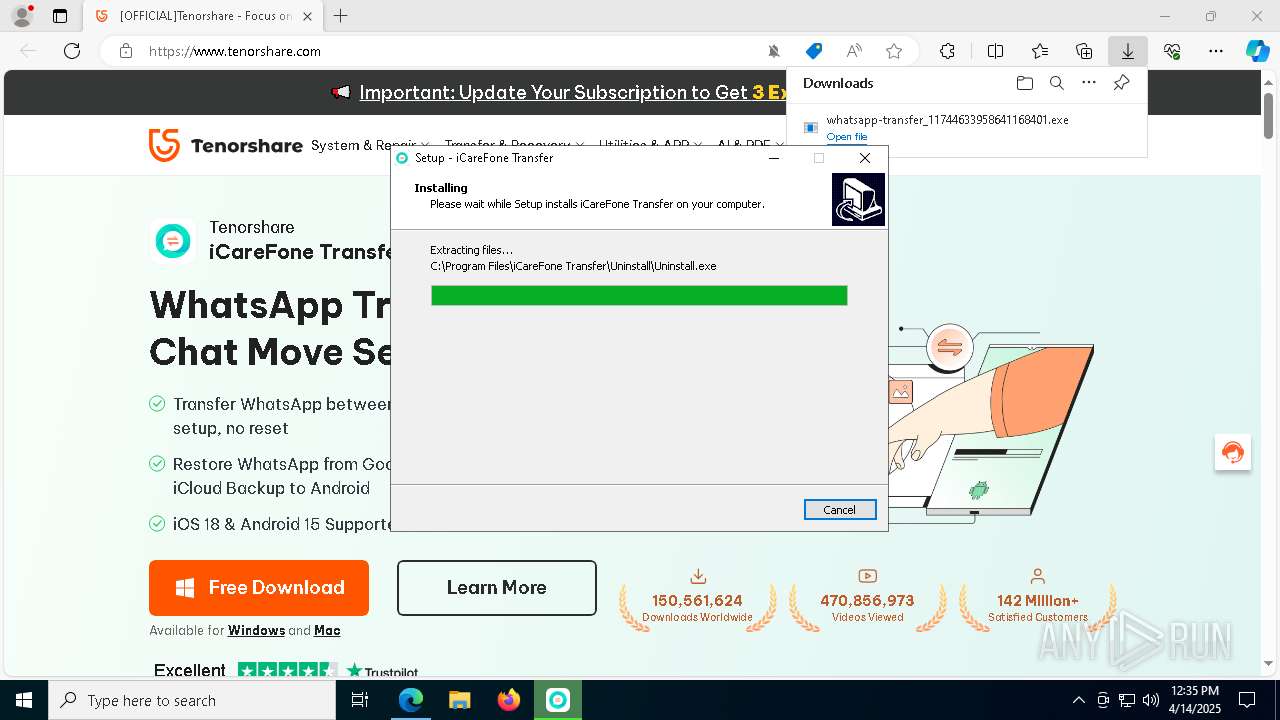
Executable content was dropped or overwritten
- whatsapp-transfer_11744633958641168401.exe (PID: 3956)
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- pnputil.exe (PID: 3156)
- pnputil.exe (PID: 540)
- drvinst.exe (PID: 8136)
- drvinst.exe (PID: 4448)
- pnputil.exe (PID: 2840)
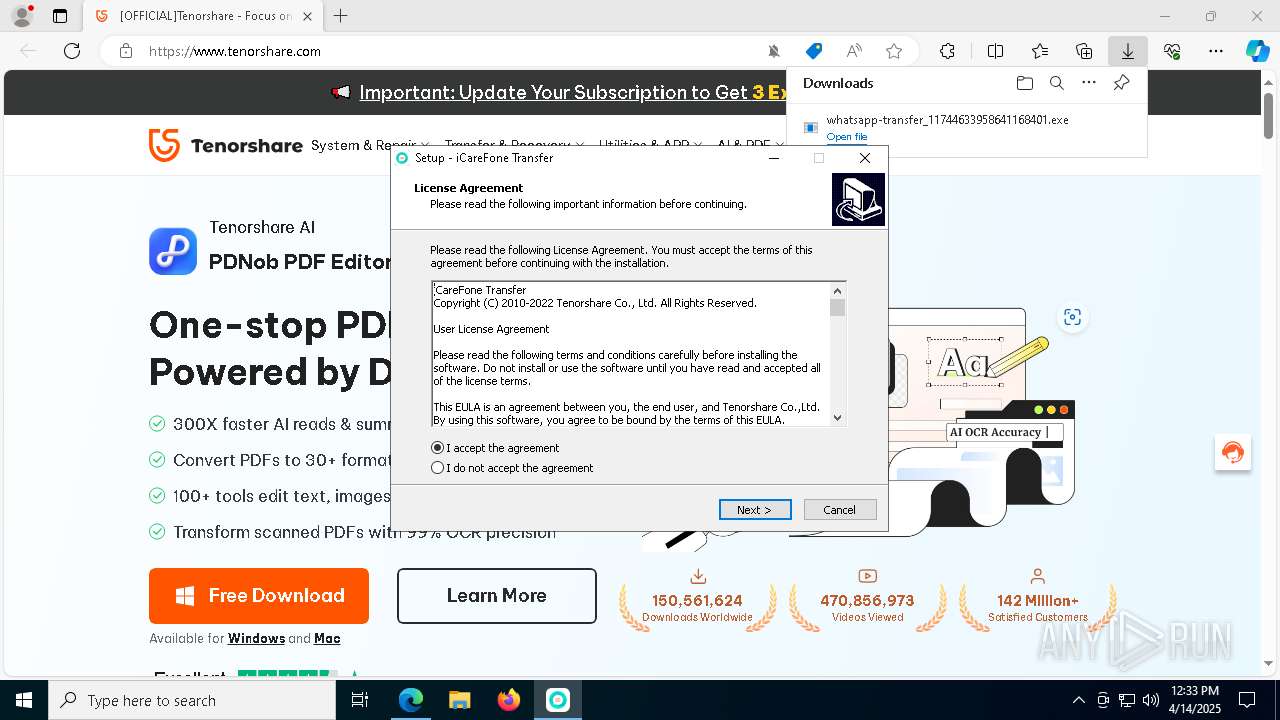
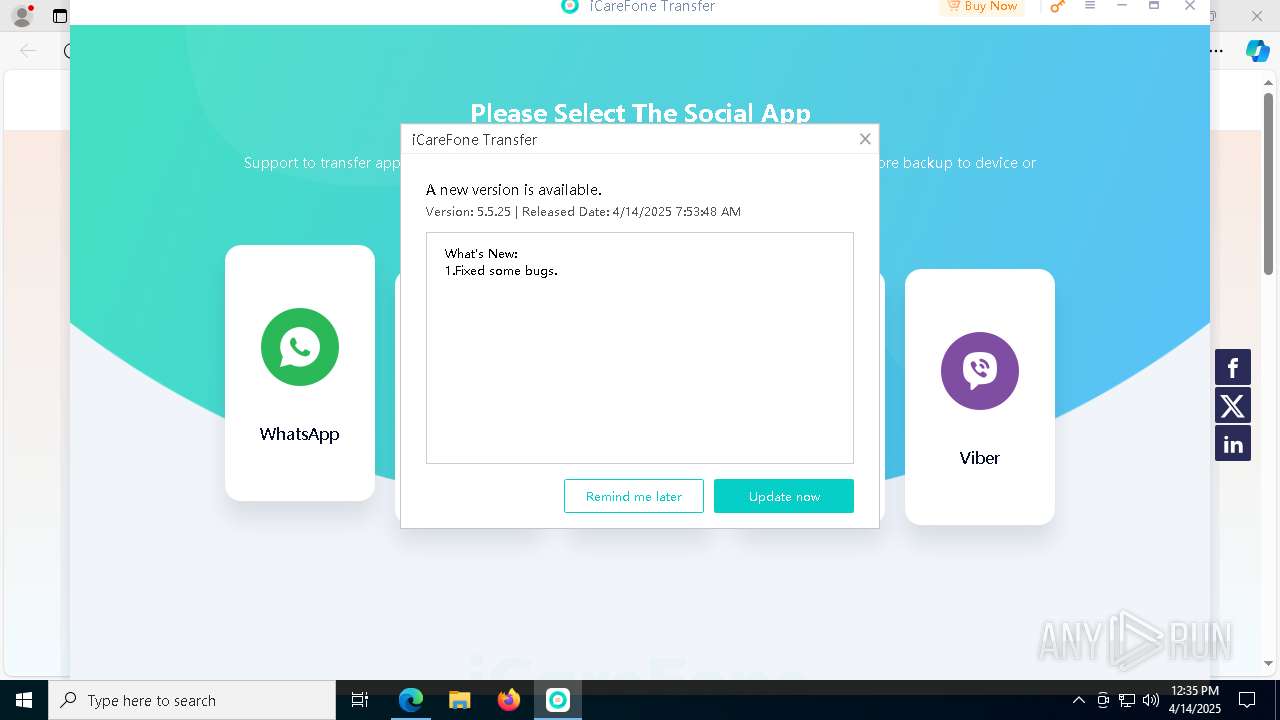
- iCareFone Transfer.exe (PID: 6512)
- ts_install.exe (PID: 4696)
- ts_install.tmp (PID: 7760)
- drvinst.exe (PID: 5400)
Process drops legitimate windows executable
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- ts_install.tmp (PID: 7760)
Reads the Windows owner or organization settings
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- ts_install.tmp (PID: 7760)
Reads security settings of Internet Explorer
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- iCareFone Transfer.exe (PID: 6512)
- NetFrameCheck.exe (PID: 7256)
- launch64.exe (PID: 6416)
- ts_install.tmp (PID: 7760)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7964)
- cmd.exe (PID: 4884)
Starts CMD.EXE for commands execution
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- launch64.exe (PID: 6416)
- iCareFone Transfer.exe (PID: 6512)
- ts_install.tmp (PID: 7760)
Process drops legitimate windows executable (CertUtil.exe)
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
Uses NETSH.EXE to add a firewall rule or allowed programs
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
Drops 7-zip archiver for unpacking
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
The process drops C-runtime libraries
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- ts_install.tmp (PID: 7760)
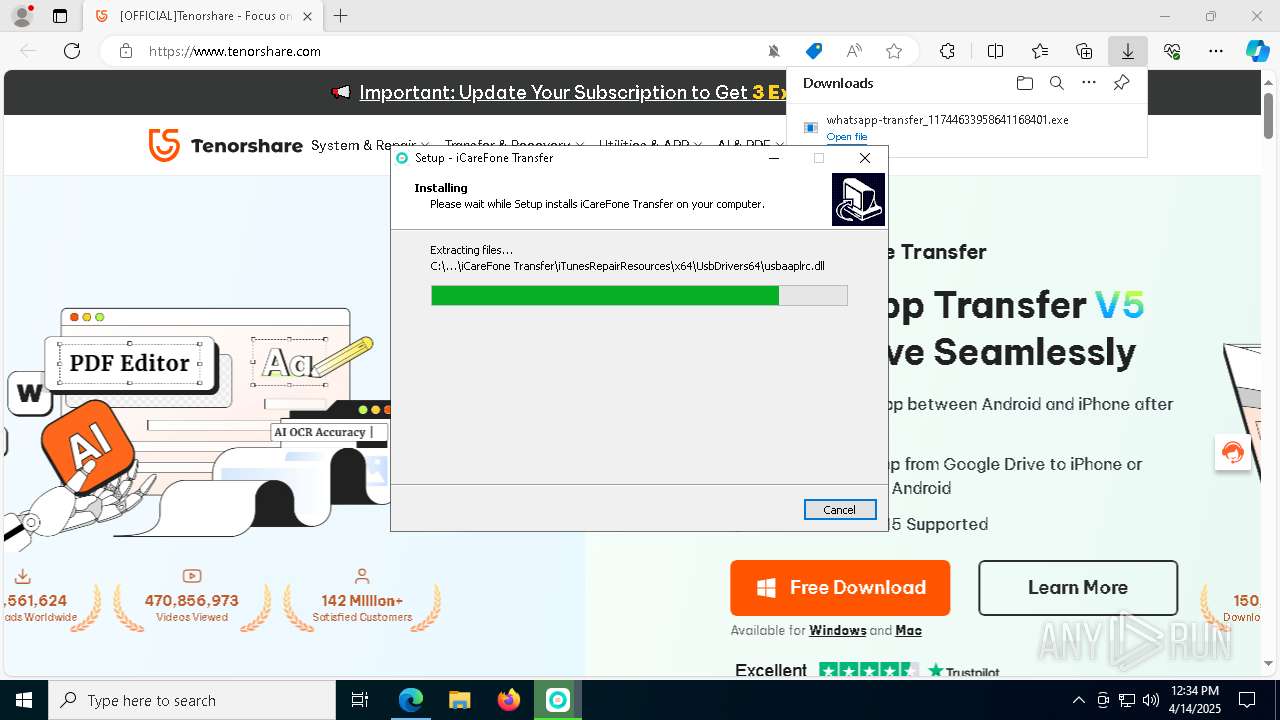
Drops a system driver (possible attempt to evade defenses)
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- pnputil.exe (PID: 3156)
- pnputil.exe (PID: 540)
- drvinst.exe (PID: 4448)
- drvinst.exe (PID: 8136)
- pnputil.exe (PID: 2840)
- drvinst.exe (PID: 5400)
Searches for installed software
- iCareFone Transfer.exe (PID: 6512)
- ts_install.tmp (PID: 7760)
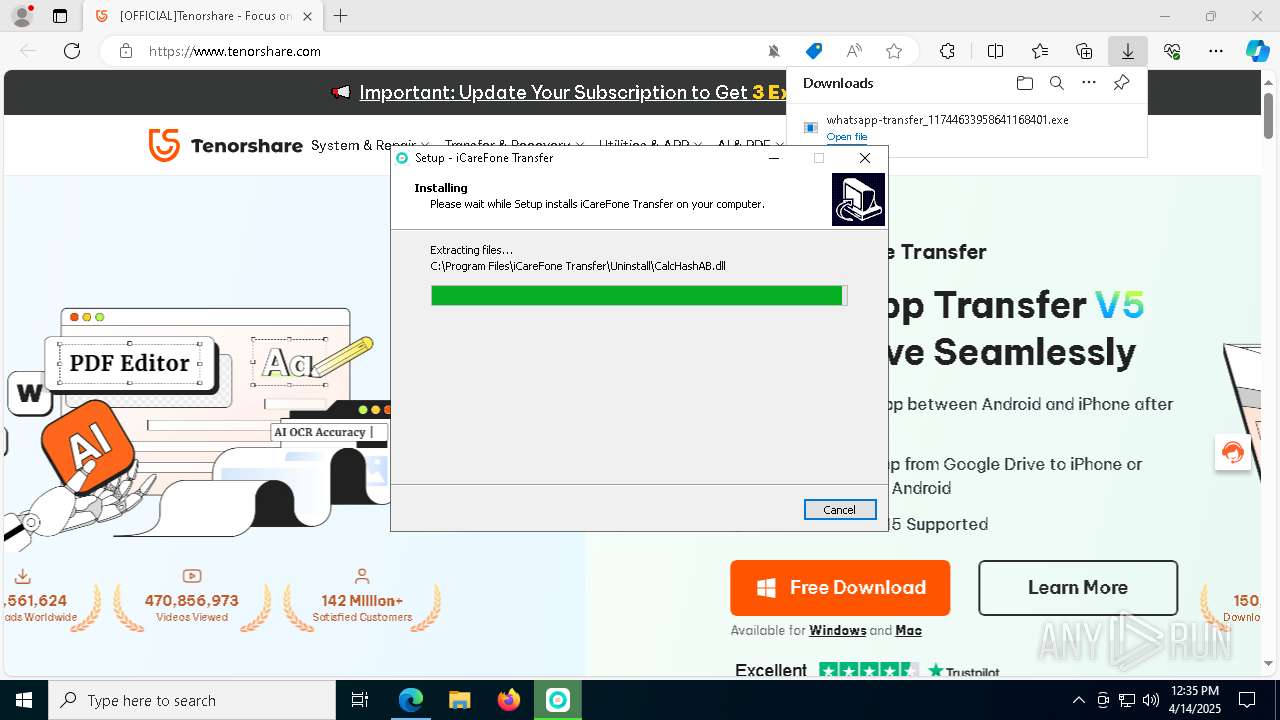
Creates a software uninstall entry
- iCareFone Transfer.exe (PID: 6512)
Potential Corporate Privacy Violation
- iCareFone Transfer.exe (PID: 6512)
Reads the date of Windows installation
- iCareFone Transfer.exe (PID: 6512)
- launch64.exe (PID: 6416)
Creates files in the driver directory
- drvinst.exe (PID: 8136)
- drvinst.exe (PID: 4448)
- drvinst.exe (PID: 5400)
INFO
Reads the computer name
- identity_helper.exe (PID: 2236)
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- iCareFone Transfer.exe (PID: 6512)
- NetFrameCheck.exe (PID: 7256)
- Monitor.exe (PID: 5796)
- launch64.exe (PID: 6416)
- AppleMobileDeviceProcess.exe (PID: 7104)
- drvinst.exe (PID: 4448)
- UpdaterInstall.exe (PID: 2192)
- ts_install.tmp (PID: 7760)
Checks supported languages
- identity_helper.exe (PID: 2236)
- whatsapp-transfer_11744633958641168401.exe (PID: 3956)
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- NetFrameCheck.exe (PID: 7256)
- iCareFone Transfer.exe (PID: 6512)
- Monitor.exe (PID: 5796)
- AppleMobileDeviceProcess.exe (PID: 7104)
- launch64.exe (PID: 6416)
- drvinst.exe (PID: 4448)
- drvinst.exe (PID: 8136)
- drvinst.exe (PID: 5400)
- UpdaterInstall.exe (PID: 2192)
- ts_install.exe (PID: 4696)
- ts_install.tmp (PID: 7760)
Reads Environment values
- identity_helper.exe (PID: 2236)
- iCareFone Transfer.exe (PID: 6512)
Executable content was dropped or overwritten
- msedge.exe (PID: 7180)
- msedge.exe (PID: 4448)
Create files in a temporary directory
- whatsapp-transfer_11744633958641168401.exe (PID: 3956)
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- iCareFone Transfer.exe (PID: 6512)
- pnputil.exe (PID: 3156)
- pnputil.exe (PID: 540)
- pnputil.exe (PID: 2840)
- UpdaterInstall.exe (PID: 2192)
- ts_install.exe (PID: 4696)
- ts_install.tmp (PID: 7760)
Application launched itself
- msedge.exe (PID: 7180)
Reads the software policy settings
- slui.exe (PID: 6324)
- iCareFone Transfer.exe (PID: 6512)
- drvinst.exe (PID: 8136)
- drvinst.exe (PID: 4448)
- slui.exe (PID: 2288)
- drvinst.exe (PID: 5400)
The sample compiled with chinese language support
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- ts_install.tmp (PID: 7760)
Detects InnoSetup installer (YARA)
- whatsapp-transfer_11744633958641168401.exe (PID: 3956)
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
Compiled with Borland Delphi (YARA)
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- whatsapp-transfer_11744633958641168401.exe (PID: 3956)
Creates files in the program directory
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- NetFrameCheck.exe (PID: 7256)
- iCareFone Transfer.exe (PID: 6512)
- AppleMobileDeviceProcess.exe (PID: 7104)
- ts_install.tmp (PID: 7760)
Process checks computer location settings
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- NetFrameCheck.exe (PID: 7256)
- launch64.exe (PID: 6416)
- iCareFone Transfer.exe (PID: 6512)
- ts_install.tmp (PID: 7760)
The sample compiled with english language support
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
- msedge.exe (PID: 4448)
- pnputil.exe (PID: 3156)
- drvinst.exe (PID: 8136)
- pnputil.exe (PID: 540)
- drvinst.exe (PID: 4448)
- pnputil.exe (PID: 2840)
- drvinst.exe (PID: 5400)
- ts_install.tmp (PID: 7760)
The sample compiled with Italian language support
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
The sample compiled with arabic language support
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
The sample compiled with korean language support
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
The sample compiled with japanese language support
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
The sample compiled with german language support
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
The sample compiled with spanish language support
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
The sample compiled with french language support
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
Checks proxy server information
- slui.exe (PID: 2288)
- iCareFone Transfer.exe (PID: 6512)
Creates a software uninstall entry
- whatsapp-transfer_11744633958641168401.tmp (PID: 5116)
Reads the machine GUID from the registry
- iCareFone Transfer.exe (PID: 6512)
- drvinst.exe (PID: 8136)
- drvinst.exe (PID: 4448)
- drvinst.exe (PID: 5400)
Reads product name
- iCareFone Transfer.exe (PID: 6512)
Confuser has been detected (YARA)
- iCareFone Transfer.exe (PID: 6512)
Disables trace logs
- iCareFone Transfer.exe (PID: 6512)
Creates files or folders in the user directory
- iCareFone Transfer.exe (PID: 6512)
VMProtect protector has been detected
- iCareFone Transfer.exe (PID: 6512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
243
Monitored processes
101
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | pnputil -i -a "C:\Program Files\iCareFone Transfer\iTunesRepairResources\x64\AppleKis\AppleKIS.inf" | C:\Windows\System32\pnputil.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft PnP Utility - Tool to add, delete, export, and enumerate driver packages. Exit code: 3758096971 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6100 --field-trial-handle=2340,i,3854616777189106431,12960608105572373090,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=7436 --field-trial-handle=2340,i,3854616777189106431,12960608105572373090,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 960 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5608 --field-trial-handle=2340,i,3854616777189106431,12960608105572373090,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6072 --field-trial-handle=2340,i,3854616777189106431,12960608105572373090,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7484 --field-trial-handle=2340,i,3854616777189106431,12960608105572373090,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6860 --field-trial-handle=2340,i,3854616777189106431,12960608105572373090,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=7796 --field-trial-handle=2340,i,3854616777189106431,12960608105572373090,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=5392 --field-trial-handle=2340,i,3854616777189106431,12960608105572373090,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
21 758
Read events
21 684
Write events
74
Delete events
0
Modification events
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DF4BBF8752912F00 | |||
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4438CB8752912F00 | |||
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197386 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {43FC0836-8208-4BE3-8AE4-D23185B8D4D1} | |||
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197386 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5D0AB931-5D76-40BC-8554-ADFE372C00E6} | |||
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197386 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EDB62FB9-DF4F-4943-B977-611A8604DA0B} | |||
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197386 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2D200C3A-F4AA-44AC-A343-573E408A9C43} | |||
Executable files
1 165
Suspicious files
594
Text files
459
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b836.TMP | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b836.TMP | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b836.TMP | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b846.TMP | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b865.TMP | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
66
TCP/UDP connections
212
DNS requests
216
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7084 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7084 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7376 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744950975&P2=404&P3=2&P4=IXkOut65zRv8dAr6COvZ%2bbCyfdRA9FV8ER0sEUb9NppDP%2fneiOPdMi5ToX3Dc1AD%2boXAYNp3RjR0LE1AfyPBzA%3d%3d | unknown | — | — | whitelisted |
7376 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744950975&P2=404&P3=2&P4=IXkOut65zRv8dAr6COvZ%2bbCyfdRA9FV8ER0sEUb9NppDP%2fneiOPdMi5ToX3Dc1AD%2boXAYNp3RjR0LE1AfyPBzA%3d%3d | unknown | — | — | whitelisted |
7376 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744950975&P2=404&P3=2&P4=IXkOut65zRv8dAr6COvZ%2bbCyfdRA9FV8ER0sEUb9NppDP%2fneiOPdMi5ToX3Dc1AD%2boXAYNp3RjR0LE1AfyPBzA%3d%3d | unknown | — | — | whitelisted |
7376 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744950975&P2=404&P3=2&P4=IXkOut65zRv8dAr6COvZ%2bbCyfdRA9FV8ER0sEUb9NppDP%2fneiOPdMi5ToX3Dc1AD%2boXAYNp3RjR0LE1AfyPBzA%3d%3d | unknown | — | — | whitelisted |
7376 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744950975&P2=404&P3=2&P4=IXkOut65zRv8dAr6COvZ%2bbCyfdRA9FV8ER0sEUb9NppDP%2fneiOPdMi5ToX3Dc1AD%2boXAYNp3RjR0LE1AfyPBzA%3d%3d | unknown | — | — | whitelisted |
7376 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744950974&P2=404&P3=2&P4=cR%2fj%2f9yyo6seDEEFCskGU19NUr7IcZr7jMitKat9XLj%2b3f6JWIlO8YzKIVtANdRoDFEJ4apK694wYboHnpVC%2bw%3d%3d | unknown | — | — | whitelisted |
7376 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744950974&P2=404&P3=2&P4=cR%2fj%2f9yyo6seDEEFCskGU19NUr7IcZr7jMitKat9XLj%2b3f6JWIlO8YzKIVtANdRoDFEJ4apK694wYboHnpVC%2bw%3d%3d | unknown | — | — | whitelisted |
7376 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744950975&P2=404&P3=2&P4=IXkOut65zRv8dAr6COvZ%2bbCyfdRA9FV8ER0sEUb9NppDP%2fneiOPdMi5ToX3Dc1AD%2boXAYNp3RjR0LE1AfyPBzA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7180 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7484 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7484 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7484 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7484 | msedge.exe | 104.18.24.249:443 | www.tenorshare.com | CLOUDFLARENET | — | whitelisted |
7484 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.tenorshare.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7484 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7484 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7484 | msedge.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
7484 | msedge.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
7484 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7484 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7484 | msedge.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
7484 | msedge.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
6512 | iCareFone Transfer.exe | Potential Corporate Privacy Violation | ET INFO Unsupported/Fake Windows NT Version 5.0 |