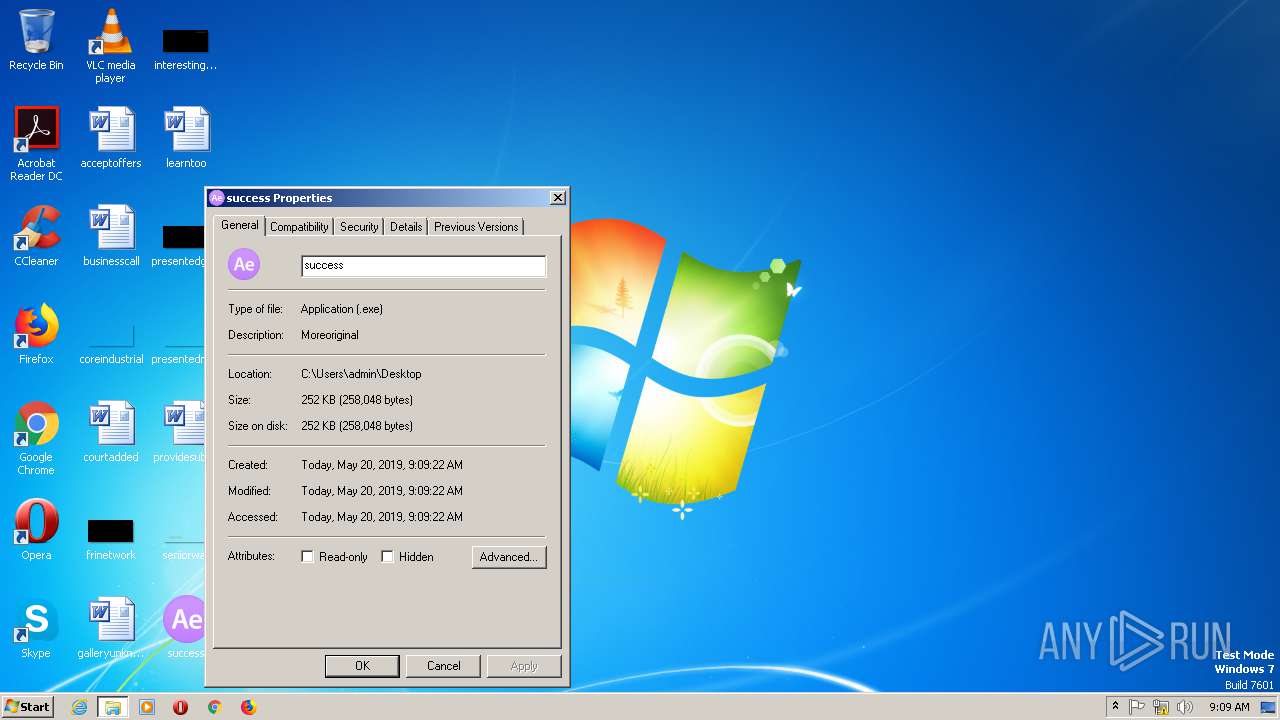
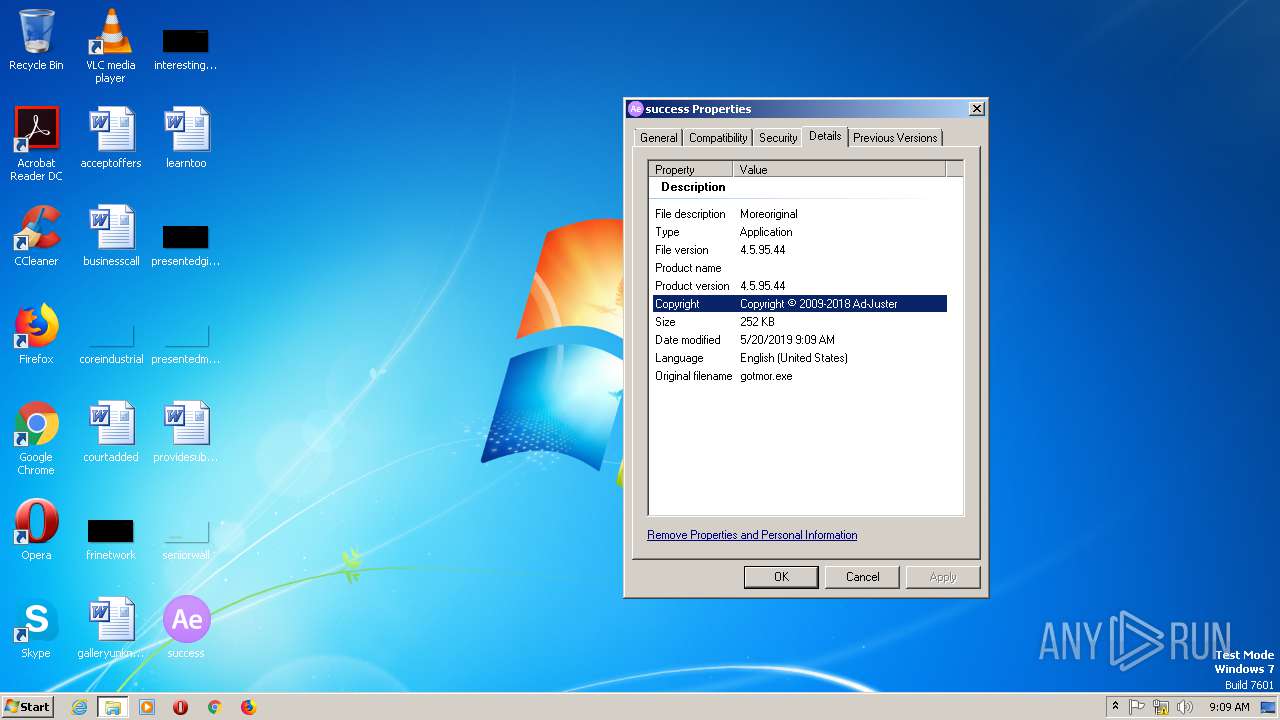
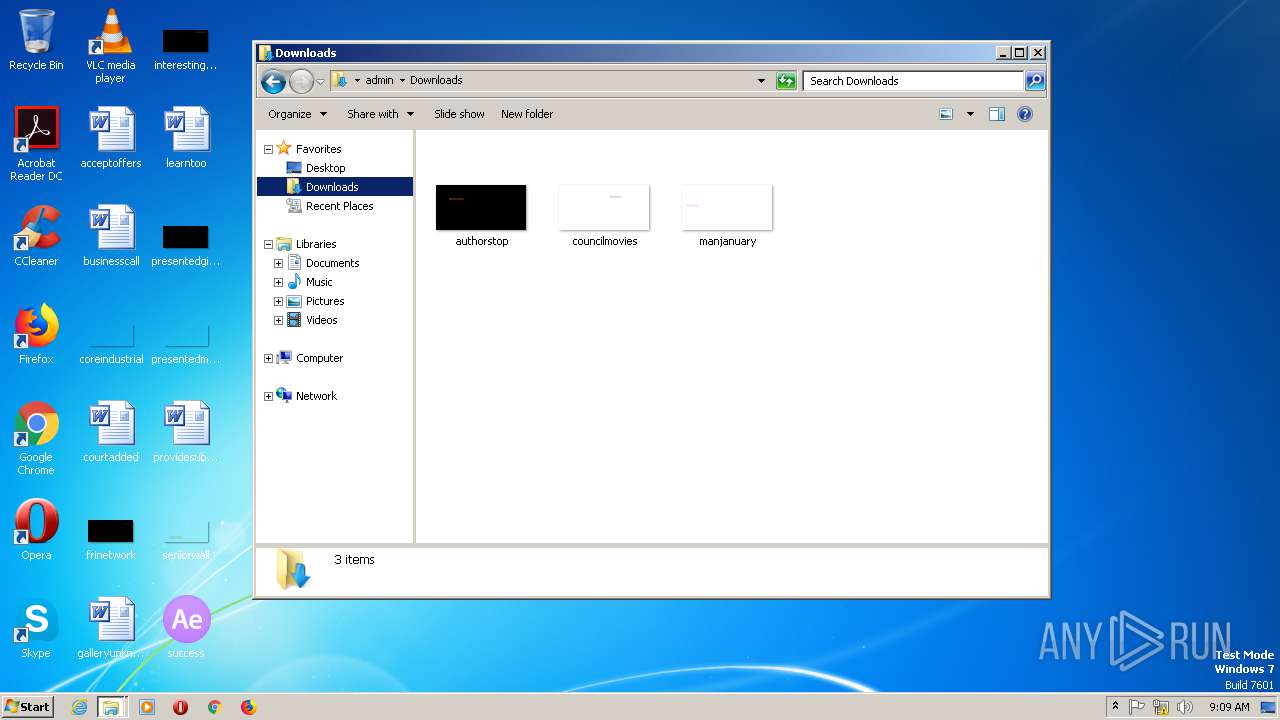
| File name: | success |
| Full analysis: | https://app.any.run/tasks/e4f79fa5-1908-4791-8e49-bd966a4ff139 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 09:09:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9EF548E73315B705A8BFC1623B0ABB7D |
| SHA1: | 6A734BACEB9E629E54B2496884E792A4F5172056 |
| SHA256: | 95A8E61B9B9FE243257CF8F3D539D66A01B7D539E4BE2798A78AB7942D525D94 |
| SSDEEP: | 3072:FTuyRKOf/FByC4a53wM60h/zMUhuOsij32oyZEU+ftcofWnGba4G9:FbK0/FwCzJwT0iU5vj32ofh/WnGba4G |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 2764)
- iexplore.exe (PID: 3020)
- iexplore.exe (PID: 148)
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 1124)
- iexplore.exe (PID: 2772)
- iexplore.exe (PID: 2332)
- iexplore.exe (PID: 1152)
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 2460)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 148)
- iexplore.exe (PID: 2764)
- iexplore.exe (PID: 3020)
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 1124)
- iexplore.exe (PID: 2772)
- iexplore.exe (PID: 2332)
- iexplore.exe (PID: 1152)
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 2460)
Changes internet zones settings
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 2764)
- iexplore.exe (PID: 3020)
- iexplore.exe (PID: 148)
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 1124)
- iexplore.exe (PID: 2772)
- iexplore.exe (PID: 2332)
- iexplore.exe (PID: 1152)
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 2460)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 2088)
- IEXPLORE.EXE (PID: 2684)
- IEXPLORE.EXE (PID: 2448)
- IEXPLORE.EXE (PID: 3016)
- IEXPLORE.EXE (PID: 1348)
- IEXPLORE.EXE (PID: 1964)
- IEXPLORE.EXE (PID: 2736)
- IEXPLORE.EXE (PID: 2668)
- IEXPLORE.EXE (PID: 2908)
- IEXPLORE.EXE (PID: 2872)
- IEXPLORE.EXE (PID: 2804)
Reads the machine GUID from the registry
- iexplore.exe (PID: 3020)
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 2764)
- iexplore.exe (PID: 148)
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 1124)
- iexplore.exe (PID: 2772)
- iexplore.exe (PID: 2332)
- iexplore.exe (PID: 1152)
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 2460)
Reads settings of System Certificates
- iexplore.exe (PID: 2100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:05:18 12:39:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 122368 |
| InitializedDataSize: | 167936 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2eaa |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
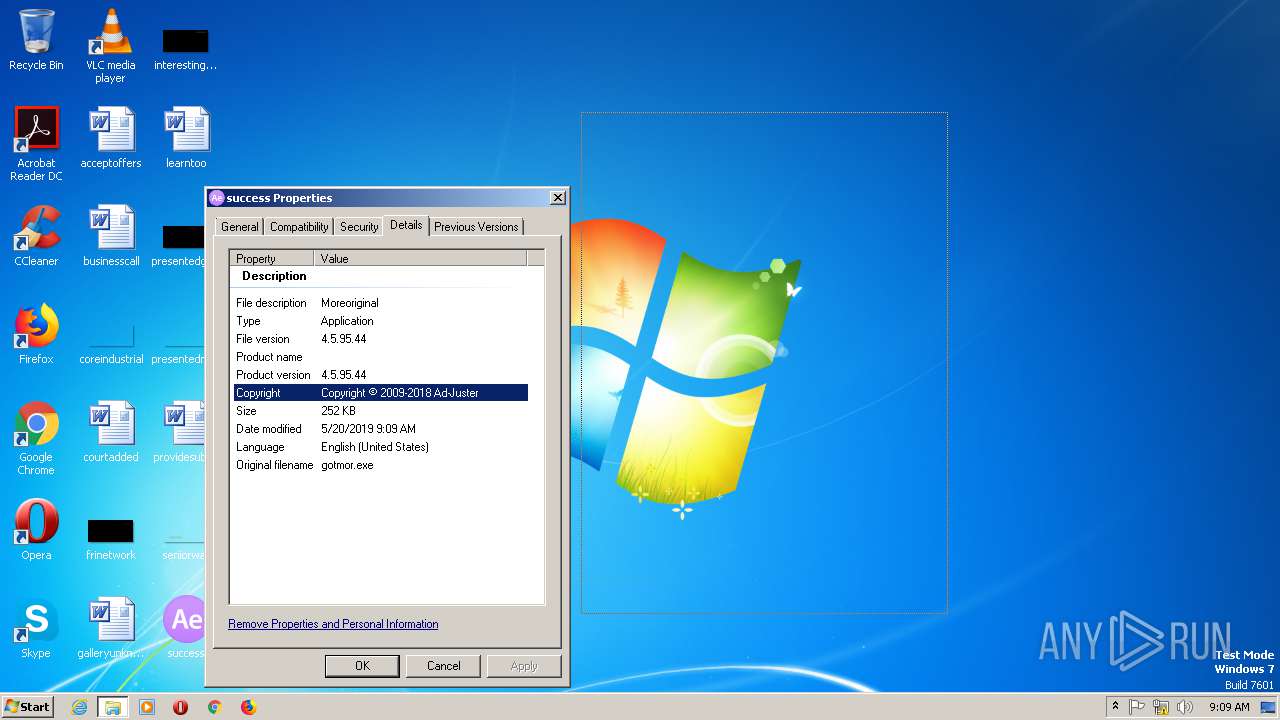
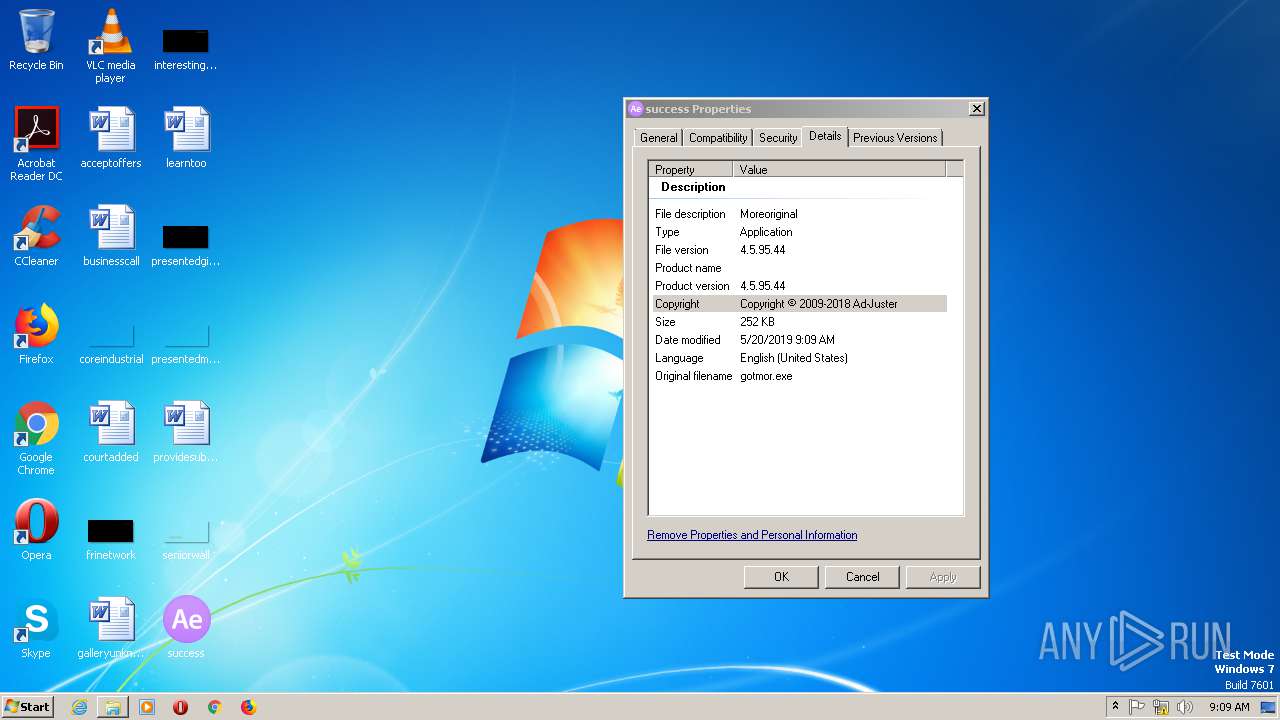
| FileVersionNumber: | 4.5.95.44 |
| ProductVersionNumber: | 4.5.95.44 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Ad-Juster |
| FileVersion: | 4.5.95.44 |
| InternalName: | gotmor.exe |
| FileDescription: | Moreoriginal |
| LegalCopyright: | Copyright © 2009-2018 Ad-Juster |
| OriginalFileName: | gotmor.exe |
| ProductVersion: | 4.5.95.44 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-May-2012 10:39:00 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Ad-Juster |
| FileVersion: | 4.5.95.44 |
| InternalName: | gotmor.exe |
| FileDescription: | Moreoriginal |
| LegalCopyright: | Copyright © 2009-2018 Ad-Juster |
| OriginalFilename: | gotmor.exe |
| ProductVersion: | 4.5.95.44 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-May-2012 10:39:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001DCCA | 0x0001DE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.97002 |
.rdata | 0x0001F000 | 0x00003D0C | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.32953 |
.data | 0x00023000 | 0x0000BD80 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.0075 |
.rsrc | 0x0002F000 | 0x00017670 | 0x00017800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.59932 |
.reloc | 0x00047000 | 0x00001A80 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.34113 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.43422 | 21640 | UNKNOWN | English - United States | RT_ICON |
3 | 4.37438 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 4.64343 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.78143 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.03605 | 2440 | UNKNOWN | English - United States | RT_ICON |
7 | 5.26937 | 1128 | UNKNOWN | English - United States | RT_ICON |
201 | 2.98748 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
OLEACC.dll |
USER32.dll |
ole32.dll |
Total processes
59
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:1124 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1964 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2076 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2088 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2764 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2448 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:3020 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
3 841
Read events
3 410
Write events
420
Delete events
11
Modification events
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 2 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 3467508912 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30740203 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3767670552 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30740203 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
0
Suspicious files
3
Text files
90
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2100 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFA7CAB60F0C5EC9D.TMP | — | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0B89F267E1D717C2.TMP | — | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{0C478AC9-7ADF-11E9-9B0A-5254004AAD21}.dat | — | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{0C478ACB-7ADF-11E9-9B0A-5254004AAD21}.dat | binary | |
MD5:— | SHA256:— | |||
| 2764 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3D26ED6F027E0F74.TMP | — | |
MD5:— | SHA256:— | |||
| 2764 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{22A8BD99-7ADF-11E9-9B0A-5254004AAD21}.dat | — | |
MD5:— | SHA256:— | |||
| 2764 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF10117D19B679E773.TMP | — | |
MD5:— | SHA256:— | |||
| 2764 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{22A8BD97-7ADF-11E9-9B0A-5254004AAD21}.dat | — | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\iecompatviewlist[1].xml | xml | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\IECompatData\iecompatdata.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
33
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2100 | iexplore.exe | GET | 304 | 152.199.19.161:443 | https://iecvlist.microsoft.com/ie11blocklist/1401746408/versionlistWin7.xml | US | — | — | whitelisted |
2100 | iexplore.exe | GET | 200 | 152.199.19.161:443 | https://r20swj13mr.microsoft.com/ieblocklist/v1/urlblocklist.bin | US | — | — | whitelisted |
2100 | iexplore.exe | GET | 200 | 152.199.19.161:443 | https://iecvlist.microsoft.com/IE11/1479242656000/iecompatviewlist.xml | US | xml | 362 Kb | whitelisted |
2684 | IEXPLORE.EXE | POST | 404 | 47.245.11.157:80 | http://f1.maso.at/index.html | US | html | 123 b | malicious |
2892 | success.exe | POST | 404 | 47.245.11.157:80 | http://f1.maso.at/index.html | US | html | 162 b | malicious |
2100 | iexplore.exe | GET | 200 | 152.199.19.161:443 | https://r20swj13mr.microsoft.com/ieblocklist/v1/urlblockindex.bin | US | binary | 16 b | whitelisted |
2088 | IEXPLORE.EXE | POST | 404 | 47.245.11.157:80 | http://f1.maso.at/index.html | US | html | 123 b | malicious |
2908 | IEXPLORE.EXE | POST | 404 | 47.245.11.157:80 | http://f1.maso.at/index.html | US | html | 123 b | malicious |
2448 | IEXPLORE.EXE | POST | 404 | 47.245.11.157:80 | http://f1.maso.at/index.html | US | html | 123 b | malicious |
3016 | IEXPLORE.EXE | POST | 404 | 47.245.11.157:80 | http://f1.maso.at/index.html | US | html | 123 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2892 | success.exe | 172.104.136.243:53 | — | Linode, LLC | DE | malicious |
2684 | IEXPLORE.EXE | 47.245.11.157:80 | f1.maso.at | — | US | malicious |
2892 | success.exe | 47.245.11.157:80 | f1.maso.at | — | US | malicious |
2088 | IEXPLORE.EXE | 47.245.11.157:80 | f1.maso.at | — | US | malicious |
2448 | IEXPLORE.EXE | 47.245.11.157:80 | f1.maso.at | — | US | malicious |
— | — | 172.104.136.243:53 | — | Linode, LLC | DE | malicious |
3016 | IEXPLORE.EXE | 47.245.11.157:80 | f1.maso.at | — | US | malicious |
1348 | IEXPLORE.EXE | 47.245.11.157:80 | f1.maso.at | — | US | malicious |
1964 | IEXPLORE.EXE | 47.245.11.157:80 | f1.maso.at | — | US | malicious |
2668 | IEXPLORE.EXE | 47.245.11.157:80 | f1.maso.at | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
f1.maso.at |
| malicious |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |