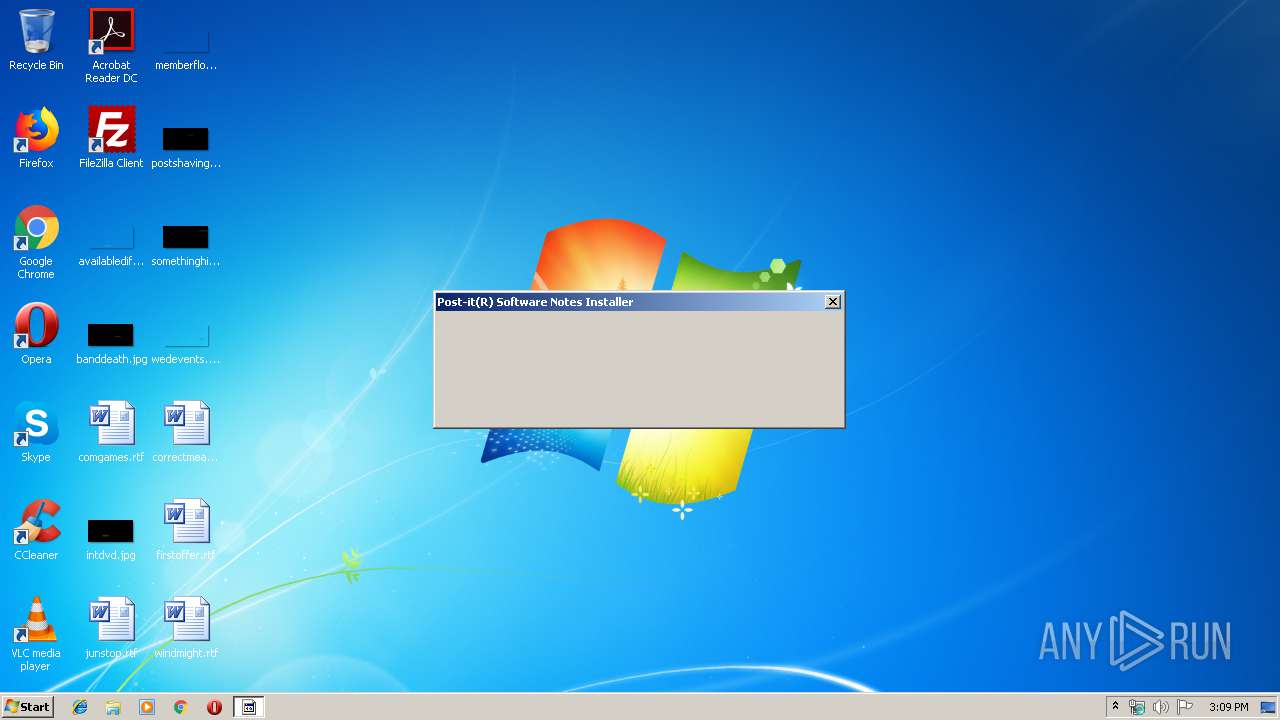
| File name: | pn31lous_74.cynet |
| Full analysis: | https://app.any.run/tasks/2f251696-4b81-468a-b4c5-2703874246ff |
| Verdict: | Malicious activity |
| Analysis date: | October 28, 2019, 15:09:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, ZIP self-extracting archive (WinZip) |
| MD5: | 768ADFC4D20694F922233FE293D6EF78 |
| SHA1: | 865B63316CE08FC1EBE1A9C4F06DD71F295E98FD |
| SHA256: | 95A1DB7D510E8E63C15770FB8BF1CEEF1C1B8833C19604E94C64599318496D90 |
| SSDEEP: | 49152:kGOJHoAKSDEn9eOBIv3tSr77kjyUYnfr:NOJ9KSA9eOBjr7ISr |
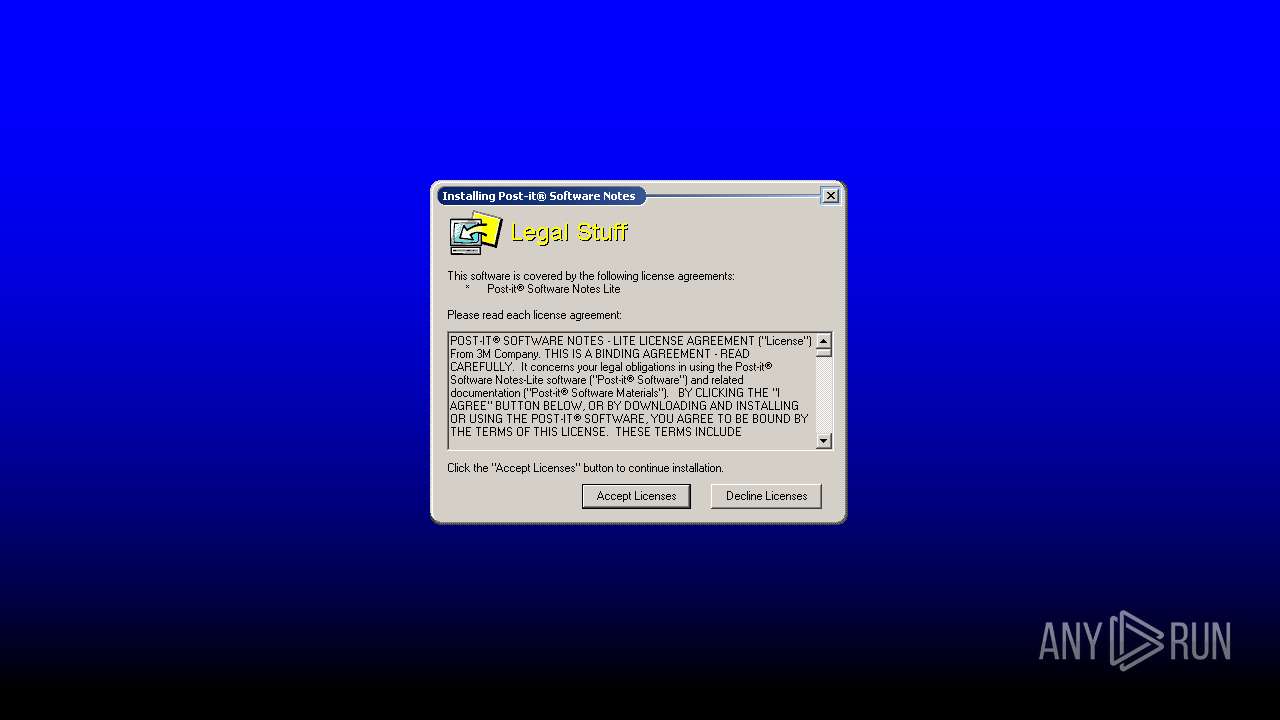
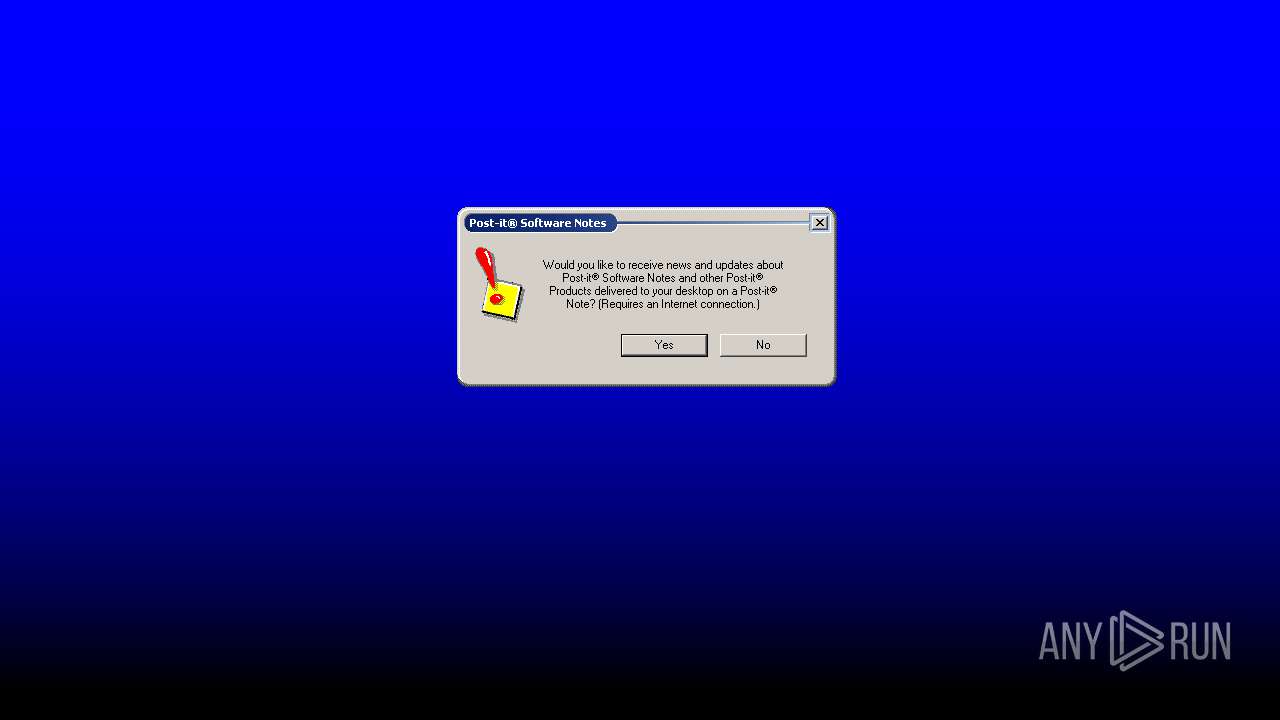
MALICIOUS
Loads dropped or rewritten executable
- setup.exe (PID: 4092)
- PsnLite.exe (PID: 4028)
- FauxNote.exe (PID: 2840)
- PSNGive.exe (PID: 600)
- PsnLite.exe (PID: 2608)
- PSNGive.exe (PID: 3136)
Application was dropped or rewritten from another process
- PsnLite.exe (PID: 4028)
- setup.exe (PID: 4092)
- FauxNote.exe (PID: 2840)
- PSNGive.exe (PID: 600)
- PsnLite.exe (PID: 2608)
- PSNGive.exe (PID: 3136)
Writes to a start menu file
- setup.exe (PID: 4092)
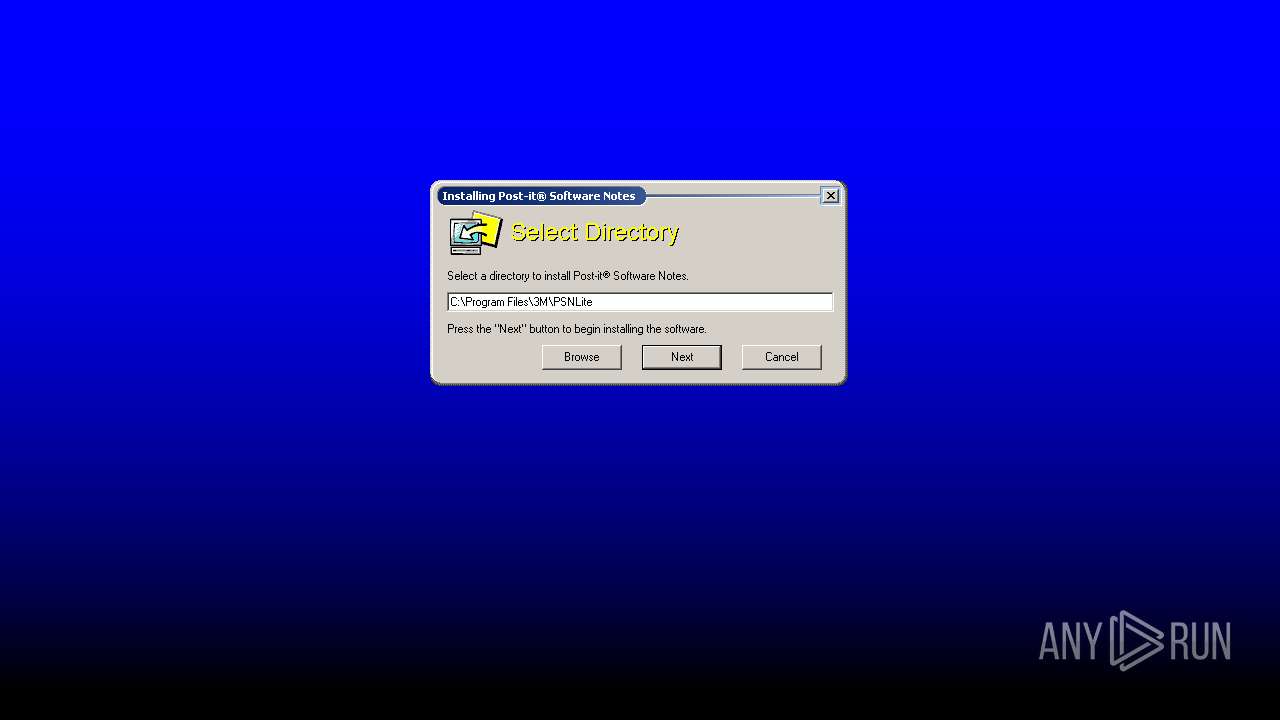
SUSPICIOUS
Executable content was dropped or overwritten
- pn31lous_74.cynet.exe (PID: 252)
- setup.exe (PID: 4092)
Creates files in the Windows directory
- setup.exe (PID: 4092)
Removes files from Windows directory
- setup.exe (PID: 4092)
Creates COM task schedule object
- setup.exe (PID: 4092)
Creates files in the program directory
- setup.exe (PID: 4092)
Creates a software uninstall entry
- setup.exe (PID: 4092)
Starts CMD.EXE for commands execution
- setup.exe (PID: 4092)
Creates files in the user directory
- PsnLite.exe (PID: 2608)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Winzip Win32 self-extracting archive (generic) (60.3) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (17.2) |
| .exe | | | Win32 Executable (generic) (11.8) |
| .exe | | | Generic Win/DOS Executable (5.2) |
| .exe | | | DOS Executable Generic (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1997:07:16 15:32:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 4.2 |
| CodeSize: | 16384 |
| InitializedDataSize: | 12800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x32aa |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jul-1997 13:32:43 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 16-Jul-1997 13:32:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00003F9E | 0x00004000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.29618 |
.rdata | 0x00005000 | 0x00000094 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.83668 |
.data | 0x00006000 | 0x00001585 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.84208 |
.idata | 0x00008000 | 0x000009F2 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.1753 |
.rsrc | 0x00009000 | 0x00000504 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.03223 |
.reloc | 0x0000A000 | 0x0000080C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.53637 |
_winzip_ | 0x0000B000 | 0x001D3000 | 0x001D2800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.99836 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.37086 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
GDI32.dll |
KERNEL32.dll |
USER32.dll |
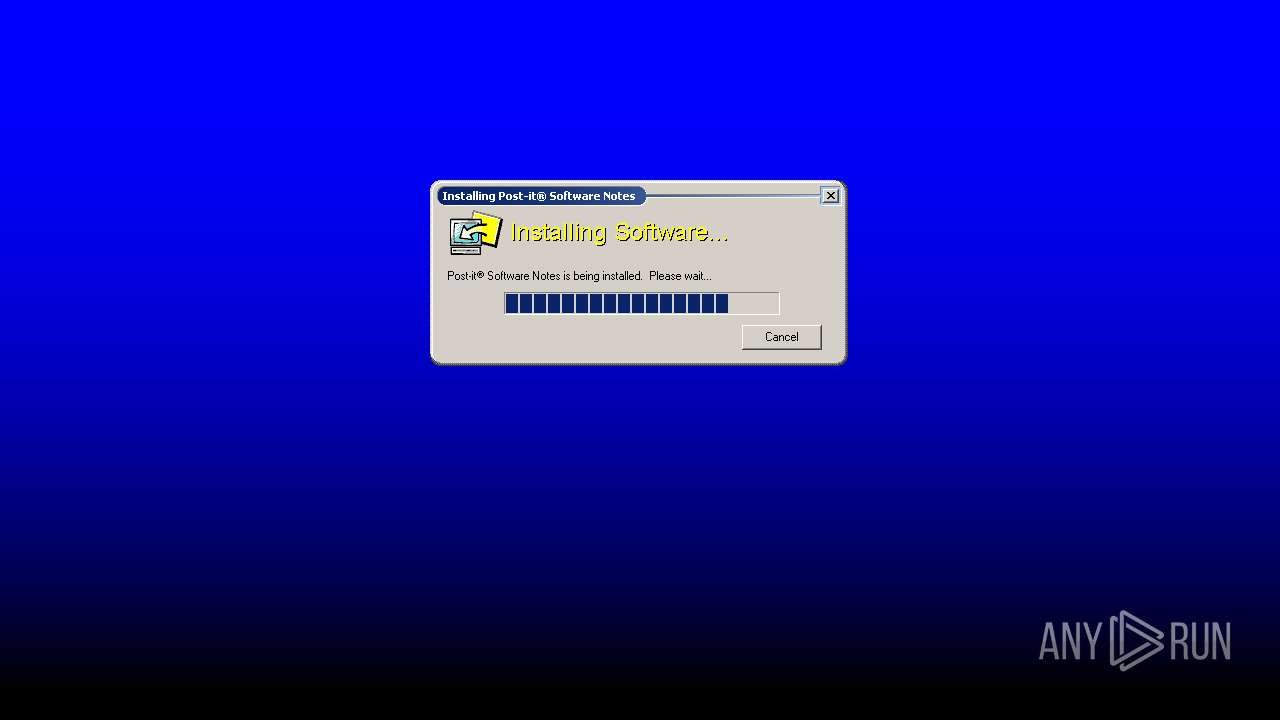
Total processes
46
Monitored processes
9
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Users\admin\Downloads\pn31lous_74.cynet.exe" | C:\Users\admin\Downloads\pn31lous_74.cynet.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 600 | "C:\Program Files\3M\PSNLite\PSNGive.exe" -RegServer | C:\Program Files\3M\PSNLite\PSNGive.exe | — | setup.exe | |||||||||||
User: admin Company: 3M Integrity Level: HIGH Description: Post-it(R) Software Notes: GiveNote Exit code: 0 Version: 3, 1, 2, 2073 Modules
| |||||||||||||||
| 2348 | cmd /c ""C:\Users\admin\AppData\Local\Temp\~psn.bat"" | C:\Windows\system32\cmd.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2608 | "C:\Program Files\3M\PSNLite\PsnLite.exe" -RegRun | C:\Program Files\3M\PSNLite\PsnLite.exe | — | setup.exe | |||||||||||
User: admin Company: 3M Integrity Level: HIGH Description: Post-it(R) Software Notes: System Exit code: 0 Version: 3, 1, 1, 1073 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\3M\PSNLite\FauxNote.exe" -RegServer | C:\Program Files\3M\PSNLite\FauxNote.exe | — | setup.exe | |||||||||||
User: admin Integrity Level: HIGH Description: FauxPSNotes Module Exit code: 0 Version: 1, 5, 320, 700 Modules
| |||||||||||||||
| 3136 | "C:\PROGRA~1\3M\PSNLite\PSNGive.exe" | C:\PROGRA~1\3M\PSNLite\PSNGive.exe | PsnLite.exe | ||||||||||||
User: admin Company: 3M Integrity Level: HIGH Description: Post-it(R) Software Notes: GiveNote Exit code: 0 Version: 3, 1, 2, 2073 Modules
| |||||||||||||||
| 3140 | "C:\Users\admin\Downloads\pn31lous_74.cynet.exe" | C:\Users\admin\Downloads\pn31lous_74.cynet.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4028 | "C:\Program Files\3M\PSNLite\PsnLite.exe" -RegServer | C:\Program Files\3M\PSNLite\PsnLite.exe | — | setup.exe | |||||||||||
User: admin Company: 3M Integrity Level: HIGH Description: Post-it(R) Software Notes: System Exit code: 0 Version: 3, 1, 1, 1073 Modules
| |||||||||||||||
| 4092 | setup.exe | C:\Users\admin\AppData\Local\Temp\WZSAEC8.tmp\setup.exe | pn31lous_74.cynet.exe | ||||||||||||
User: admin Company: 3M Integrity Level: HIGH Exit code: 0 Version: 3, 1, 0, 73 Modules
| |||||||||||||||
Total events
901
Read events
323
Write events
501
Delete events
77
Modification events
| (PID) Process: | (4092) setup.exe | Key: | HKEY_CURRENT_USER\Software\3M\Support |
| Operation: | write | Name: | A |
Value: 10/28/2019 3:09 PM:(m_bInit) in UtilVer.cpp at 98 | |||
| (PID) Process: | (4092) setup.exe | Key: | HKEY_CURRENT_USER\Software\3M\Support |
| Operation: | write | Name: | B |
Value: 10/28/2019 3:09 PM:(m_bInit) in UtilVer.cpp at 98 | |||
| (PID) Process: | (4092) setup.exe | Key: | HKEY_CURRENT_USER\Software\3M\Support |
| Operation: | write | Name: | A |
Value: 10/28/2019 3:09 PM:(m_bInit) in UtilVer.cpp at 82 | |||
| (PID) Process: | (4092) setup.exe | Key: | HKEY_CURRENT_USER\Software\3M\Support |
| Operation: | write | Name: | C |
Value: 10/28/2019 3:09 PM:(m_bInit) in UtilVer.cpp at 98 | |||
| (PID) Process: | (4092) setup.exe | Key: | HKEY_CURRENT_USER\Software\3M\Support |
| Operation: | write | Name: | B |
Value: 10/28/2019 3:09 PM:(m_bInit) in UtilVer.cpp at 82 | |||
| (PID) Process: | (4092) setup.exe | Key: | HKEY_CURRENT_USER\Software\3M\Support |
| Operation: | write | Name: | A |
Value: 10/28/2019 3:09 PM:(m_bInit) in UtilVer.cpp at 90 | |||
| (PID) Process: | (4092) setup.exe | Key: | HKEY_CURRENT_USER\Software\3M\Support |
| Operation: | write | Name: | D |
Value: 10/28/2019 3:09 PM:(m_bInit) in UtilVer.cpp at 98 | |||
| (PID) Process: | (4092) setup.exe | Key: | HKEY_CURRENT_USER\Software\3M\Support |
| Operation: | write | Name: | C |
Value: 10/28/2019 3:09 PM:(m_bInit) in UtilVer.cpp at 82 | |||
| (PID) Process: | (4092) setup.exe | Key: | HKEY_CURRENT_USER\Software\3M\Support |
| Operation: | write | Name: | B |
Value: 10/28/2019 3:09 PM:(m_bInit) in UtilVer.cpp at 90 | |||
| (PID) Process: | (4092) setup.exe | Key: | HKEY_CURRENT_USER\Software\3M\Support |
| Operation: | write | Name: | A |
Value: 10/28/2019 3:09 PM:(m_bInit) in UtilVer.cpp at 74 | |||
Executable files
26
Suspicious files
2
Text files
75
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 252 | pn31lous_74.cynet.exe | C:\Users\admin\AppData\Local\Temp\WZSAEC8.tmp\psn3lite.inf | binary | |
MD5:— | SHA256:— | |||
| 252 | pn31lous_74.cynet.exe | C:\Users\admin\AppData\Local\Temp\WZSAEC8.tmp\psnapp\Help\psnotes.cnt | text | |
MD5:— | SHA256:— | |||
| 252 | pn31lous_74.cynet.exe | C:\Users\admin\AppData\Local\Temp\WZSAEC8.tmp\psnapp\clock.wav | wav | |
MD5:— | SHA256:— | |||
| 252 | pn31lous_74.cynet.exe | C:\Users\admin\AppData\Local\Temp\WZSAEC8.tmp\psnapp\psnlite.exe | executable | |
MD5:— | SHA256:— | |||
| 252 | pn31lous_74.cynet.exe | C:\Users\admin\AppData\Local\Temp\WZSAEC8.tmp\psnapp\psnalarm.dll | executable | |
MD5:— | SHA256:— | |||
| 252 | pn31lous_74.cynet.exe | C:\Users\admin\AppData\Local\Temp\WZSAEC8.tmp\psnapp\rolldown.wav | wav | |
MD5:— | SHA256:— | |||
| 252 | pn31lous_74.cynet.exe | C:\Users\admin\AppData\Local\Temp\WZSAEC8.tmp\psnapp\whizpop.wav | wav | |
MD5:— | SHA256:— | |||
| 252 | pn31lous_74.cynet.exe | C:\Users\admin\AppData\Local\Temp\WZSAEC8.tmp\psnapp\uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 252 | pn31lous_74.cynet.exe | C:\Users\admin\AppData\Local\Temp\WZSAEC8.tmp\psnapp\siren.wav | wav | |
MD5:— | SHA256:— | |||
| 252 | pn31lous_74.cynet.exe | C:\Users\admin\AppData\Local\Temp\WZSAEC8.tmp\psnapp\uninst.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3136 | PSNGive.exe | POST | — | 192.28.32.56:80 | http://pmb001.3M.com/psnmsgr/PSNNews?server=psnnews2 | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3136 | PSNGive.exe | 192.28.32.56:80 | pmb001.3M.com | 3M Company | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pmb001.3M.com |
| unknown |