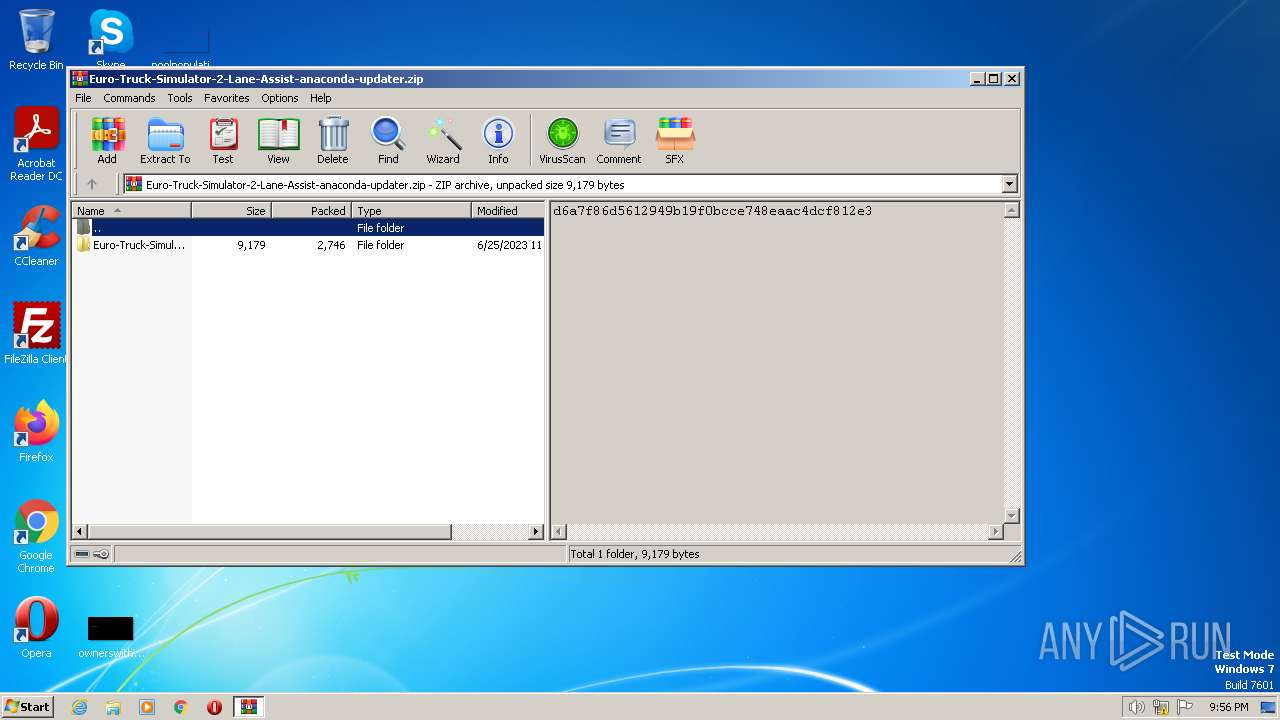
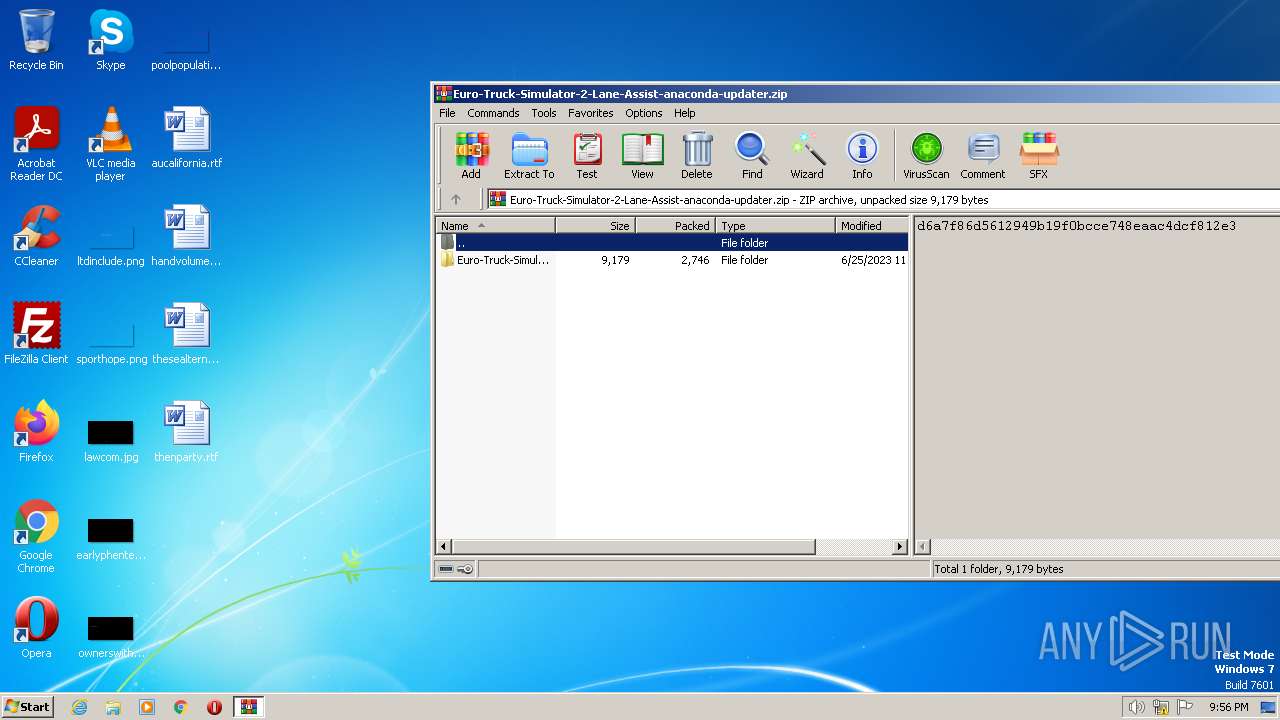
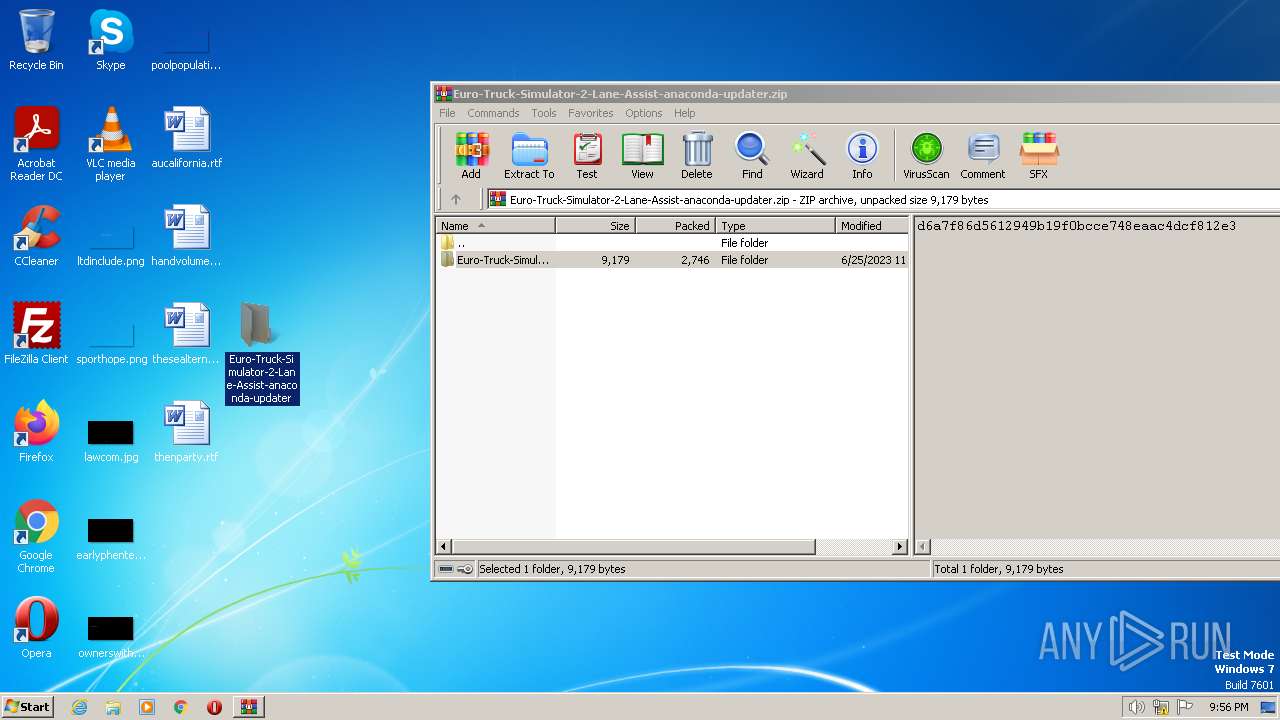
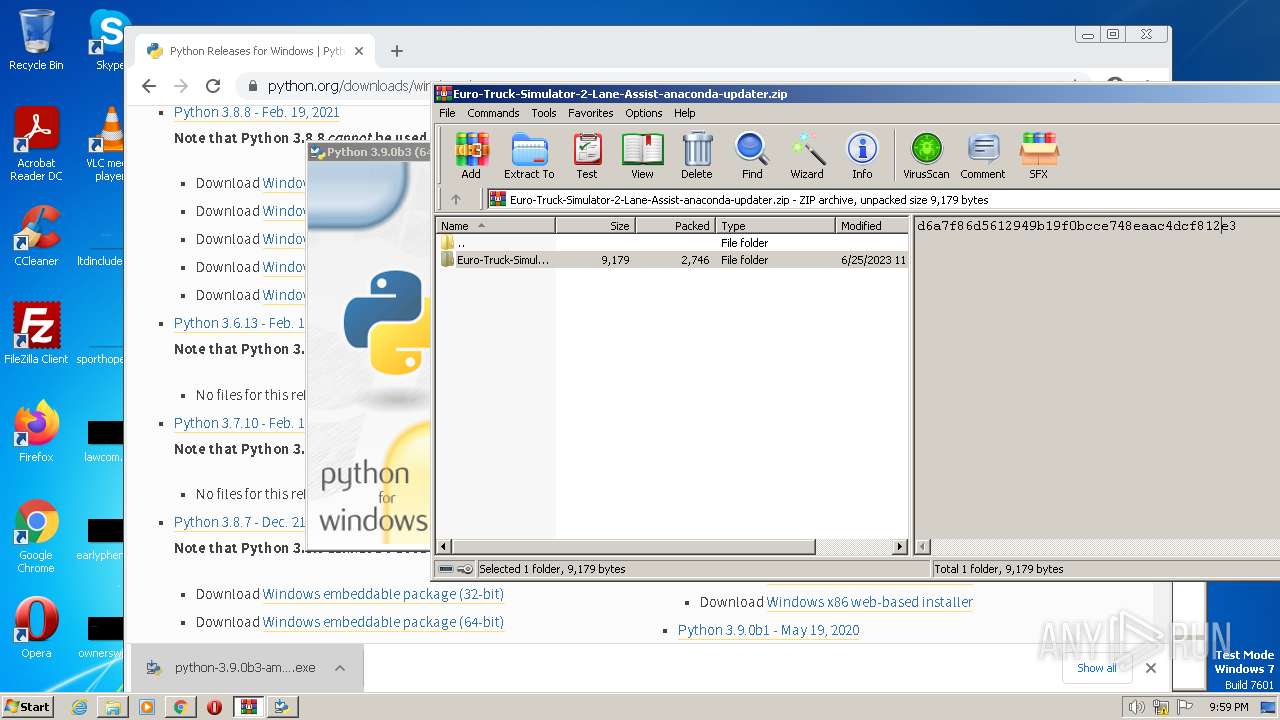
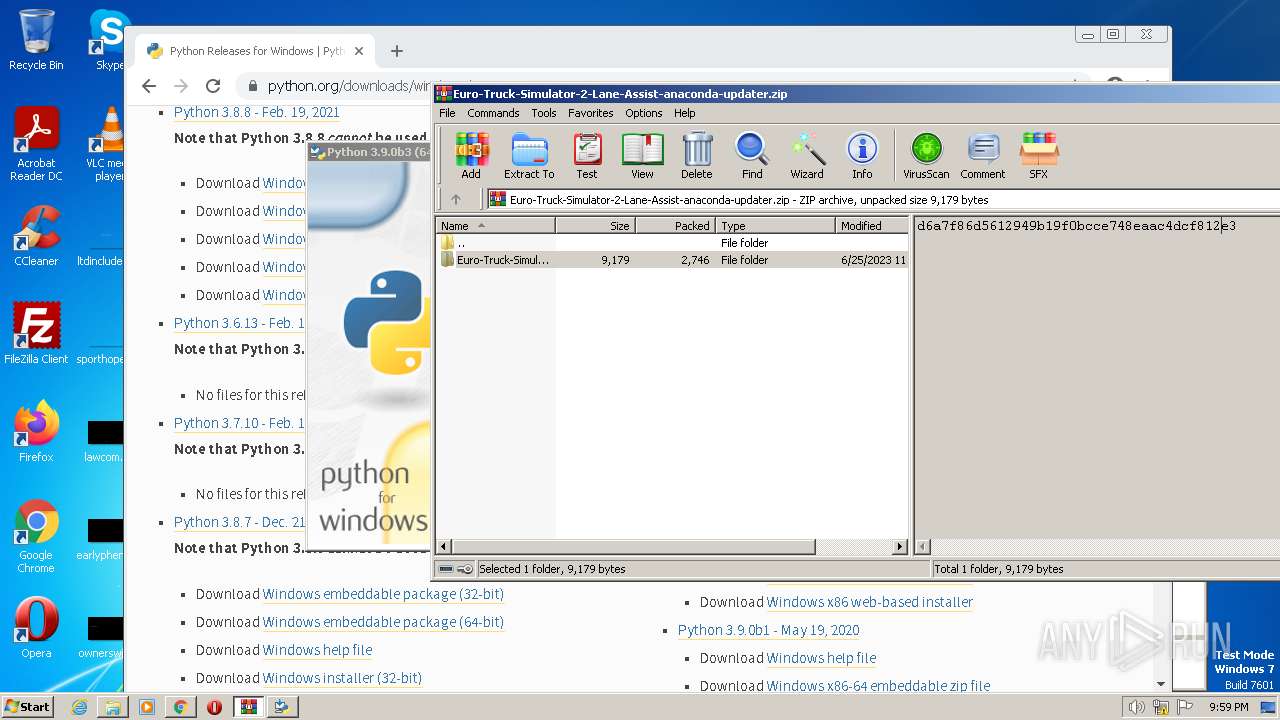
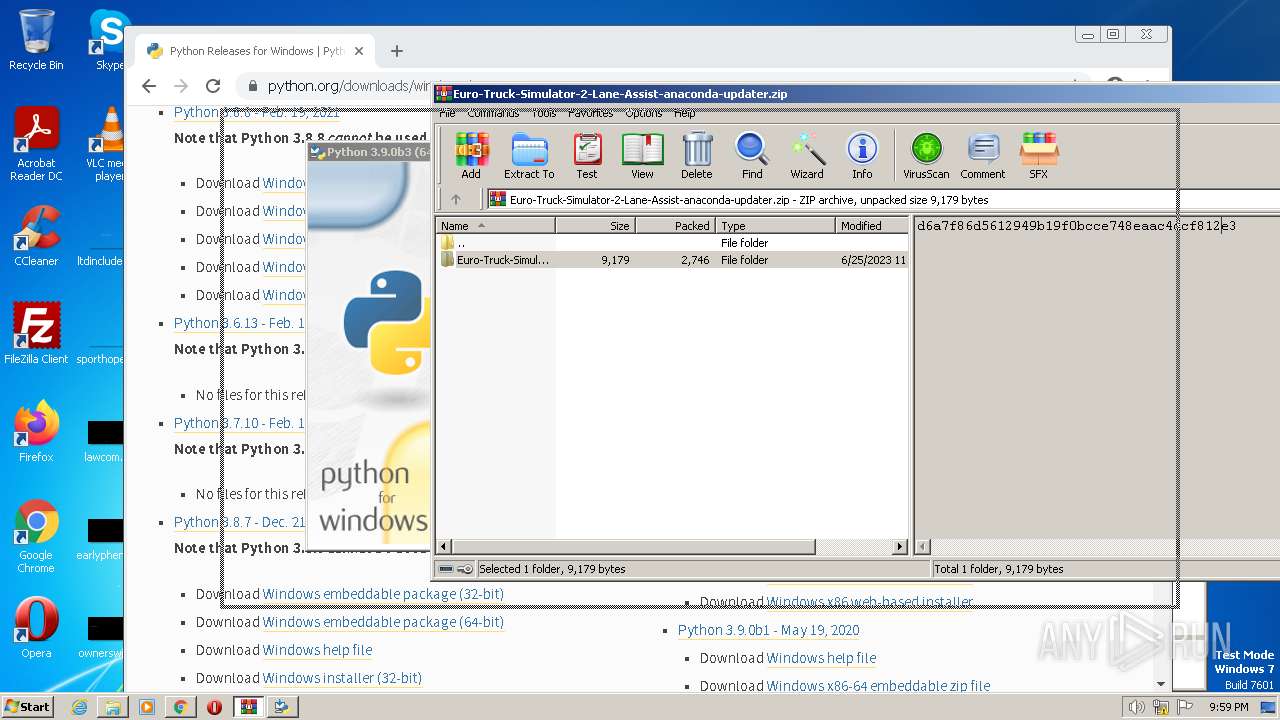
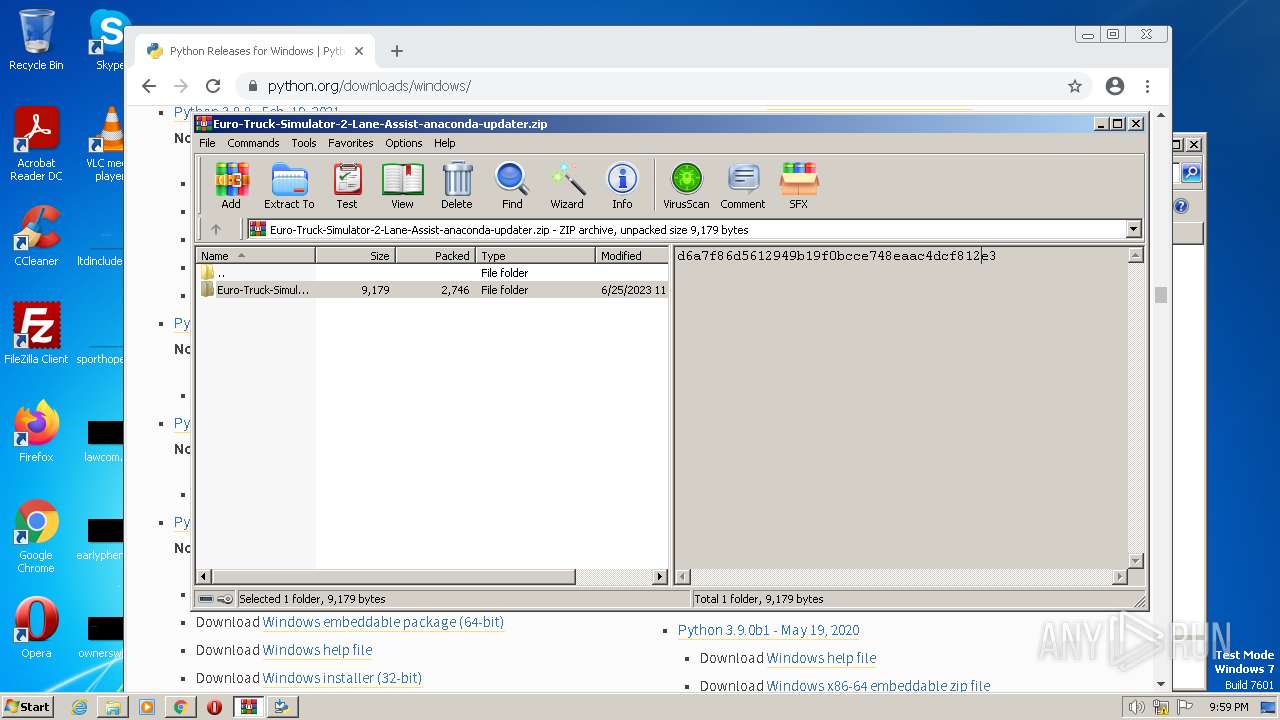
| File name: | Euro-Truck-Simulator-2-Lane-Assist-anaconda-updater.zip |
| Full analysis: | https://app.any.run/tasks/68ea1294-c6ab-4402-aee5-cb51a2d62389 |
| Verdict: | Malicious activity |
| Analysis date: | June 26, 2023, 20:56:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 9B296C04950F1ABB7C5D82EE3D25E8F0 |
| SHA1: | 3DA864F7AB103E586BD8D911AFF51BF8C7529154 |
| SHA256: | 959A4605065370D766B68BC6BEA5B320784DC369819DF28B585B3D021D8800C4 |
| SSDEEP: | 48:faxKFaPy6QvcUH3UUxccqaAdFzAHS0UQe7q6UqNYNDjVxywMgwNMkqBxK5h:faR9QBHfaeAdFTQuq6MowdBSh |
MALICIOUS
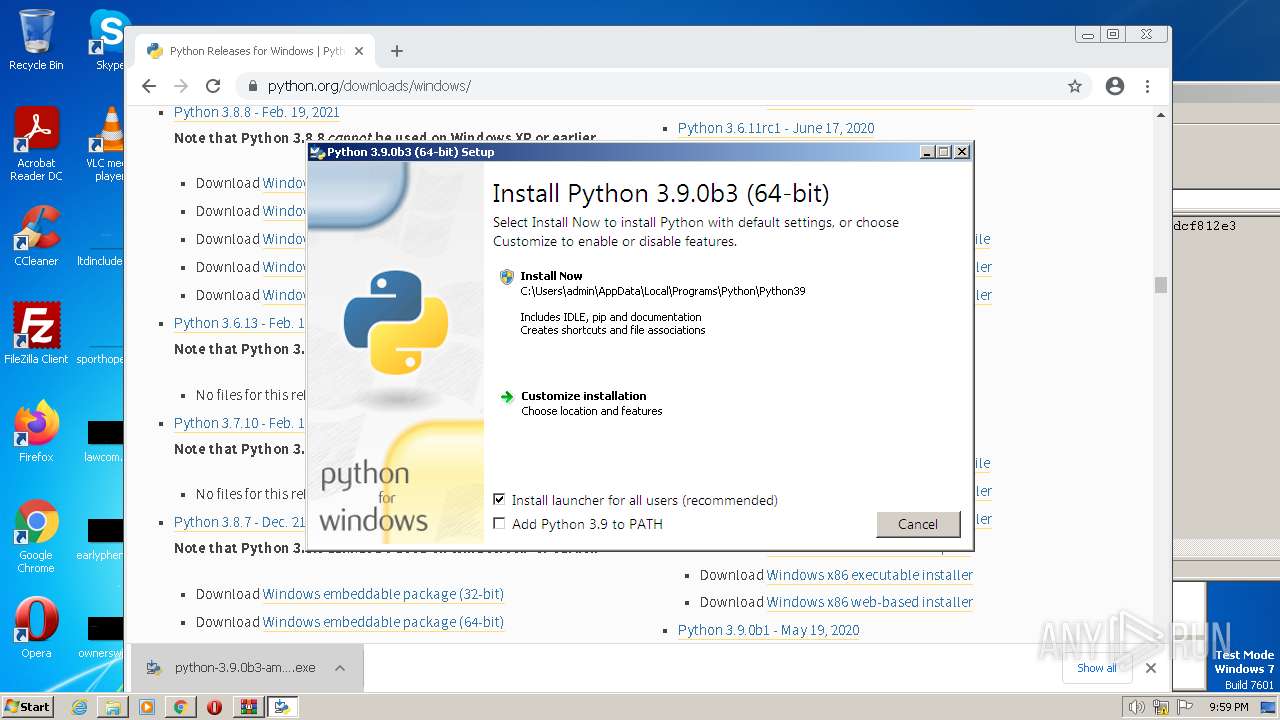
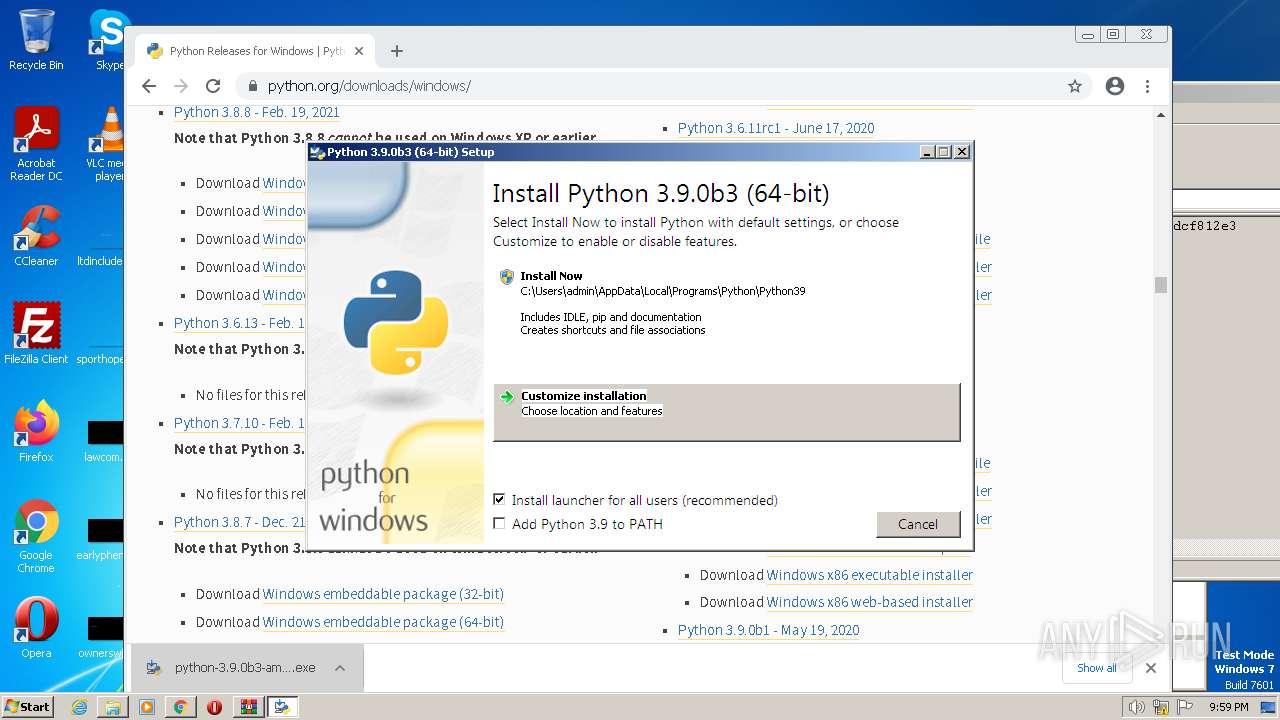
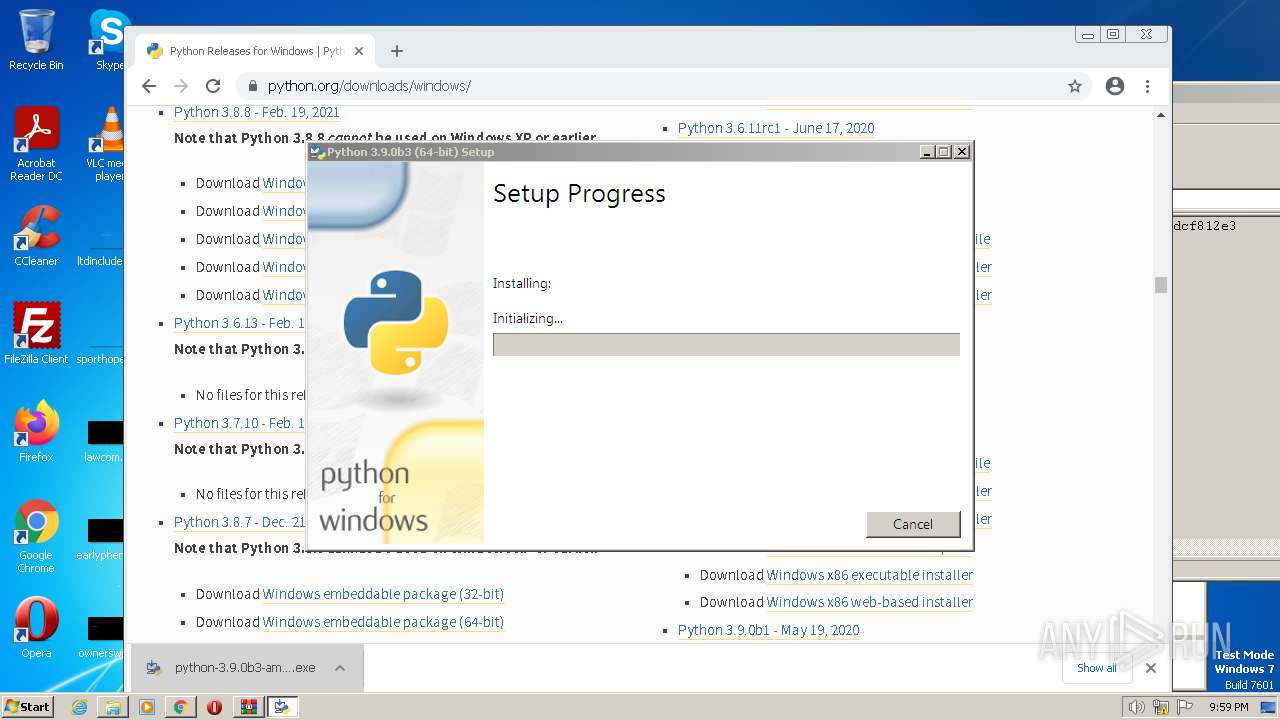
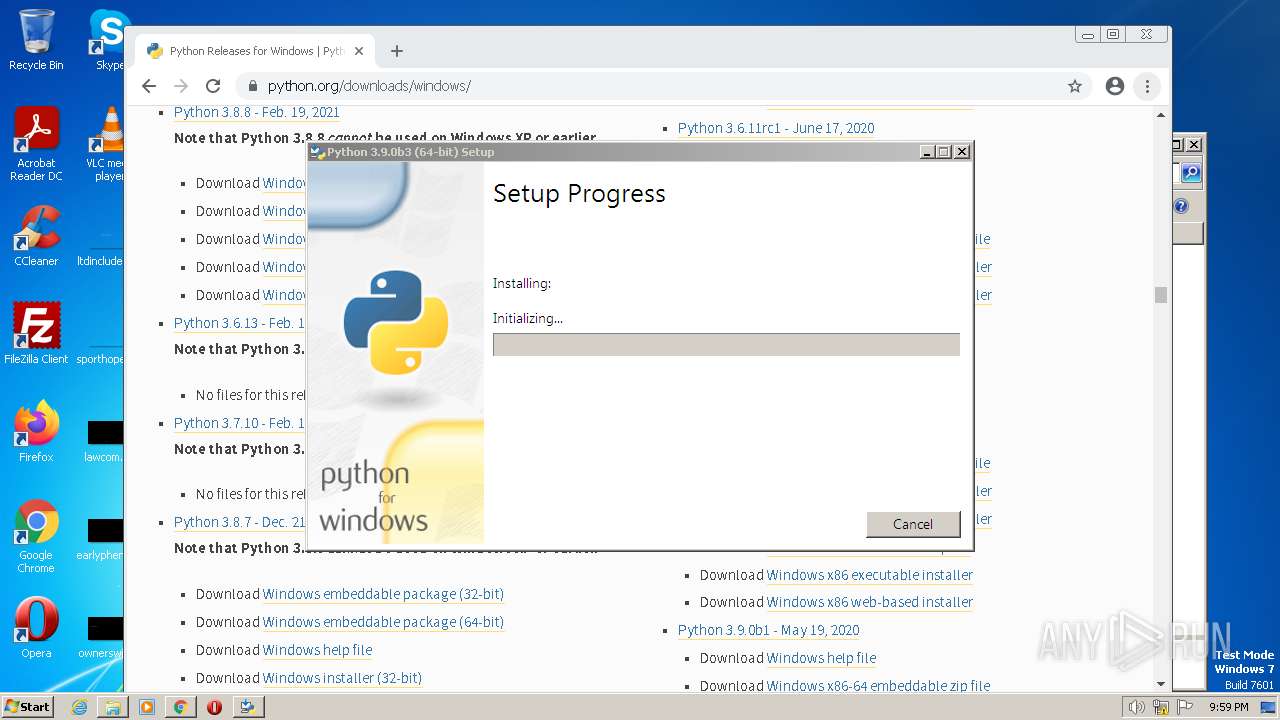
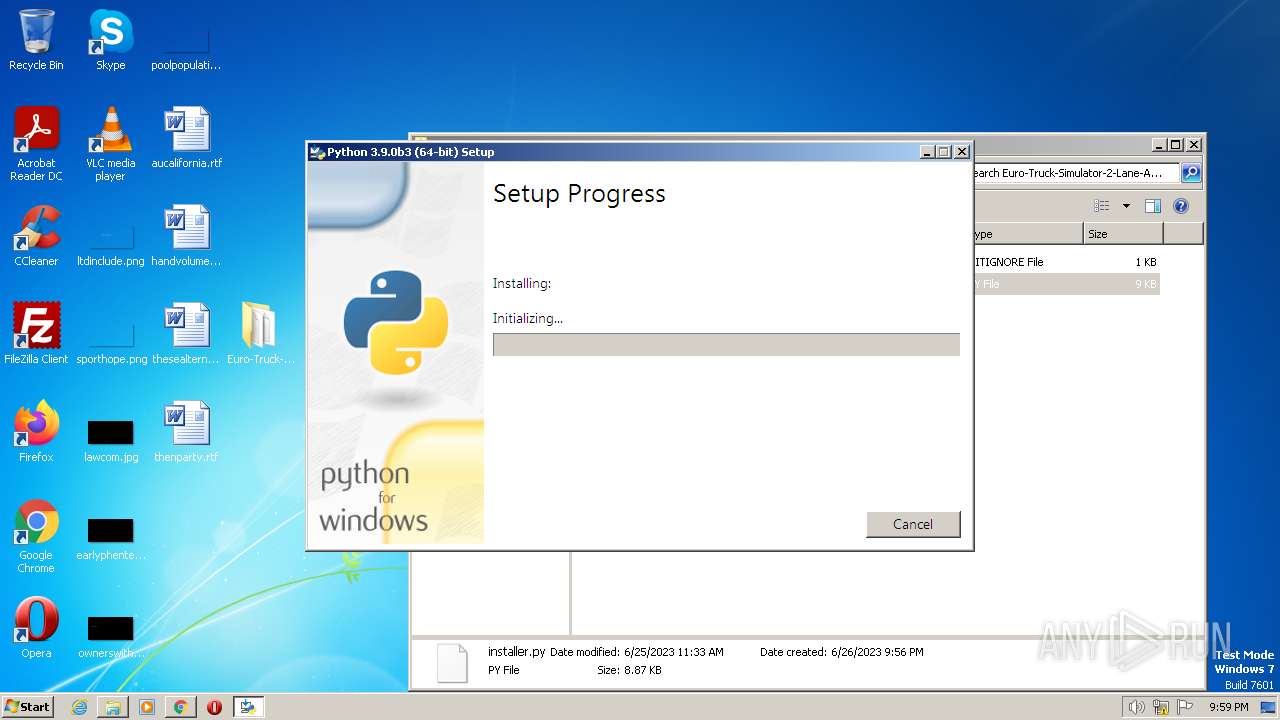
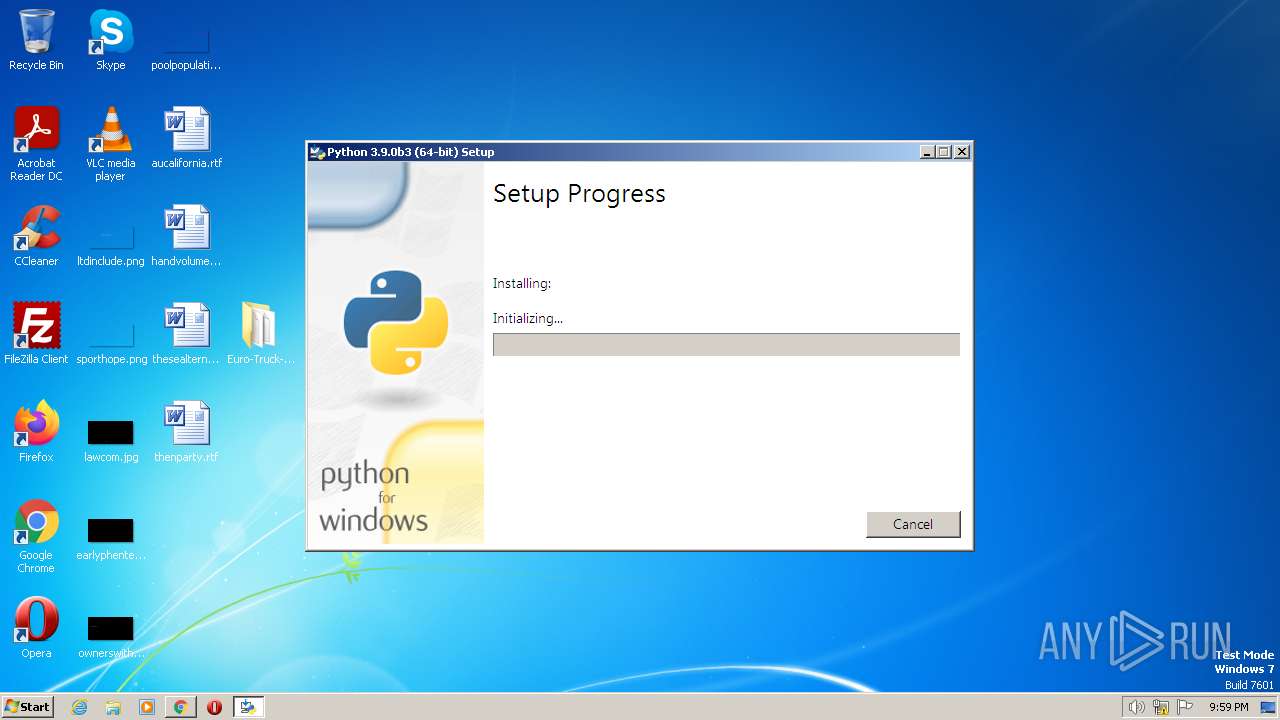
Application was dropped or rewritten from another process
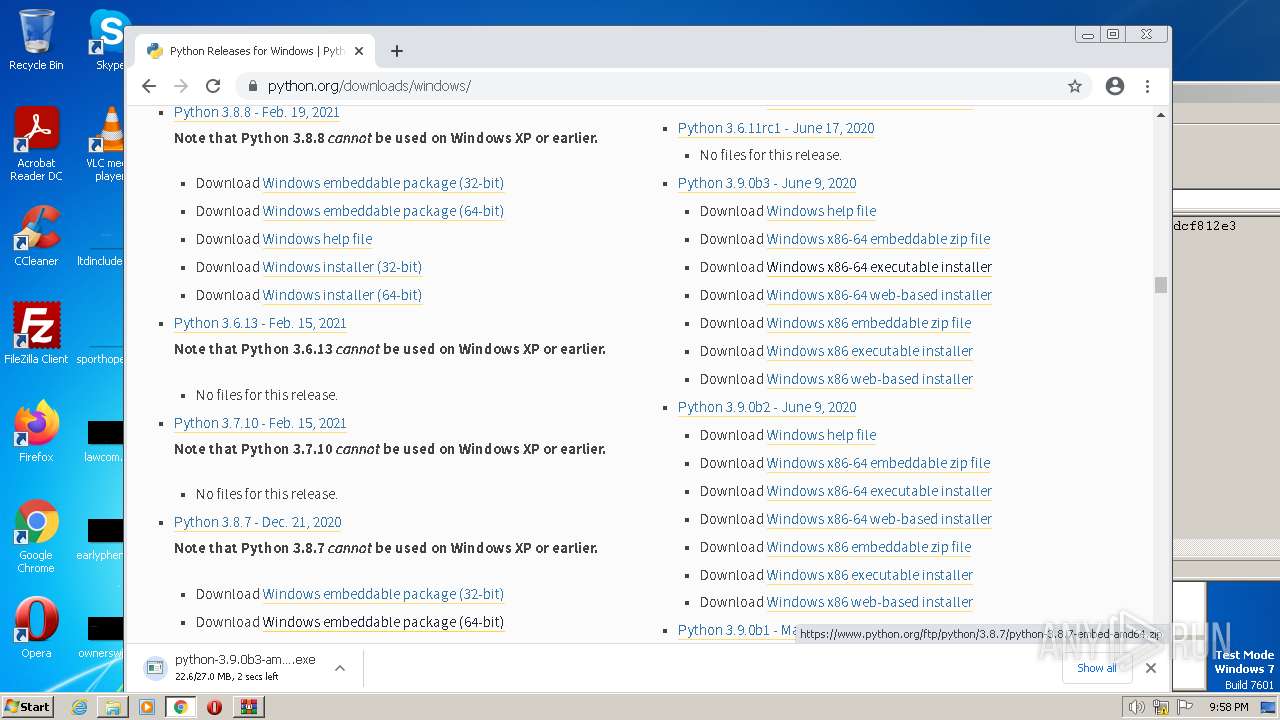
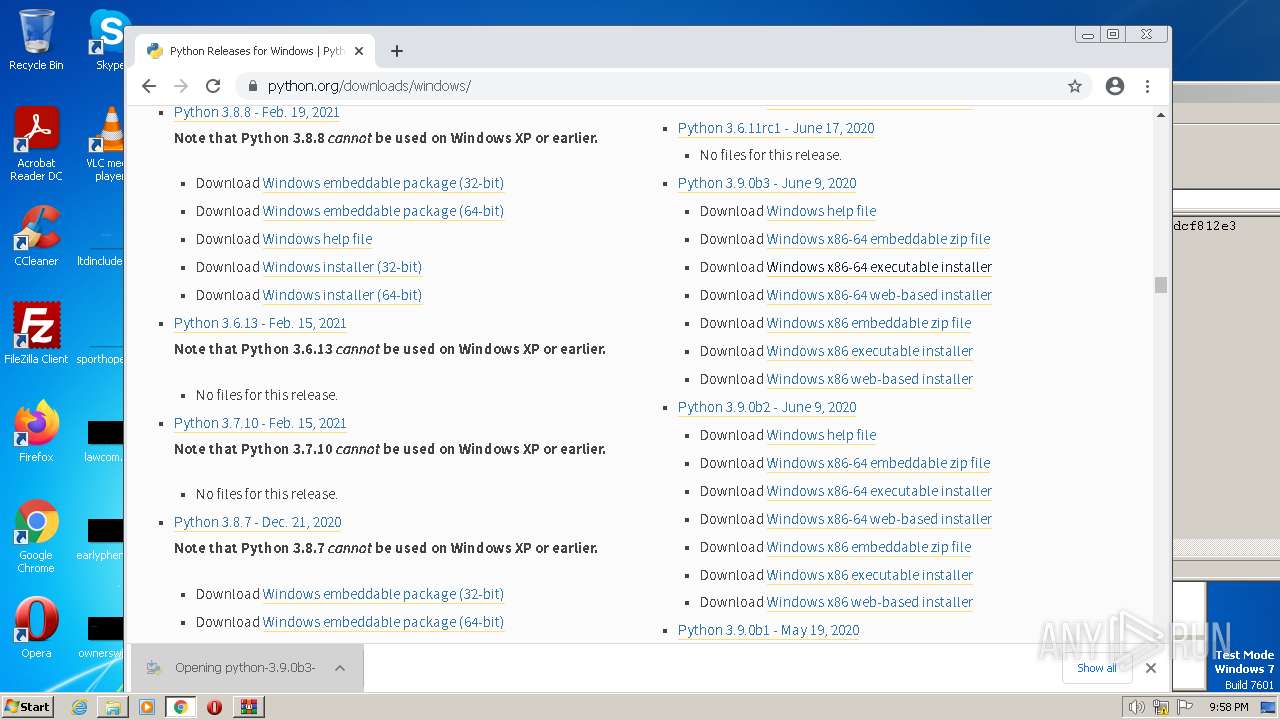
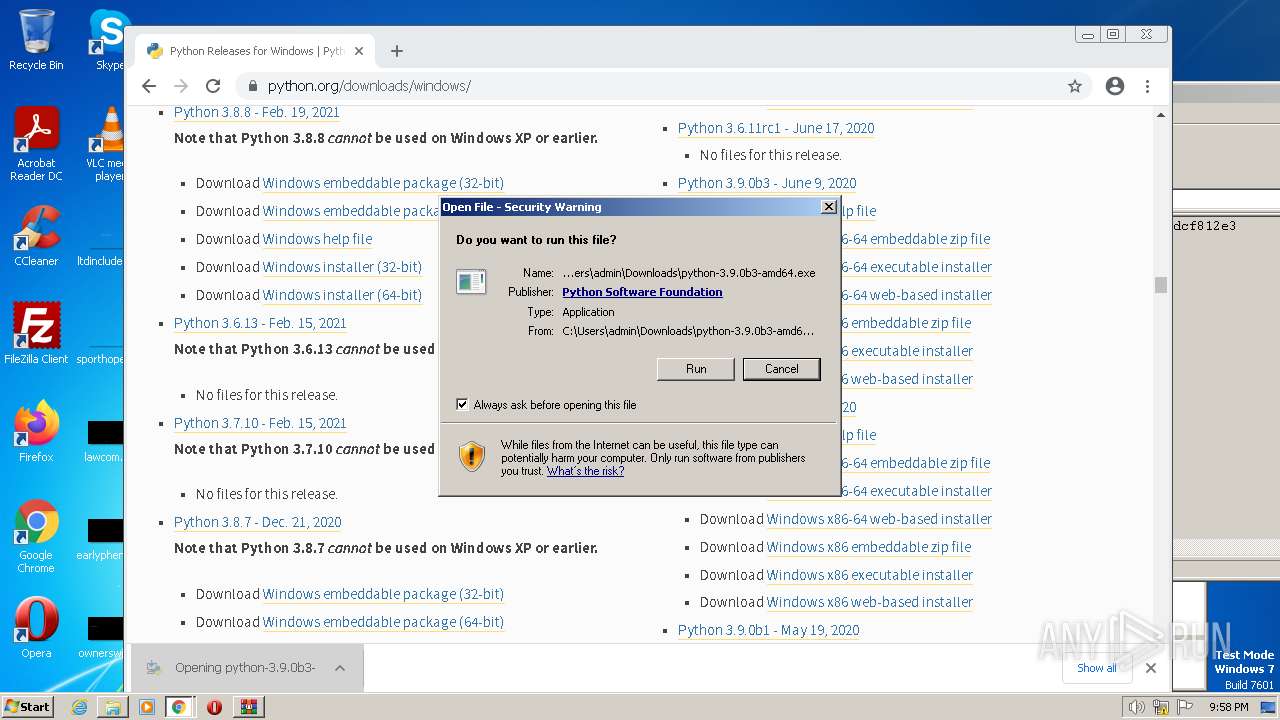
- python-3.9.0b3-amd64.exe (PID: 3604)
- python-3.9.0b3-amd64.exe (PID: 596)
- python-3.9.0b3-amd64.exe (PID: 3996)
SUSPICIOUS
Executable content was dropped or overwritten
- python-3.9.0b3-amd64.exe (PID: 596)
- python-3.9.0b3-amd64.exe (PID: 3604)
- python-3.9.0b3-amd64.exe (PID: 3996)
Loads Python modules
- python-3.9.0b3-amd64.exe (PID: 596)
Searches for installed software
- python-3.9.0b3-amd64.exe (PID: 596)
- python-3.9.0b3-amd64.exe (PID: 3996)
Reads the Internet Settings
- python-3.9.0b3-amd64.exe (PID: 596)
- rundll32.exe (PID: 2528)
Starts itself from another location
- python-3.9.0b3-amd64.exe (PID: 596)
Executes as Windows Service
- VSSVC.exe (PID: 3748)
Checks Windows Trust Settings
- msiexec.exe (PID: 2968)
INFO
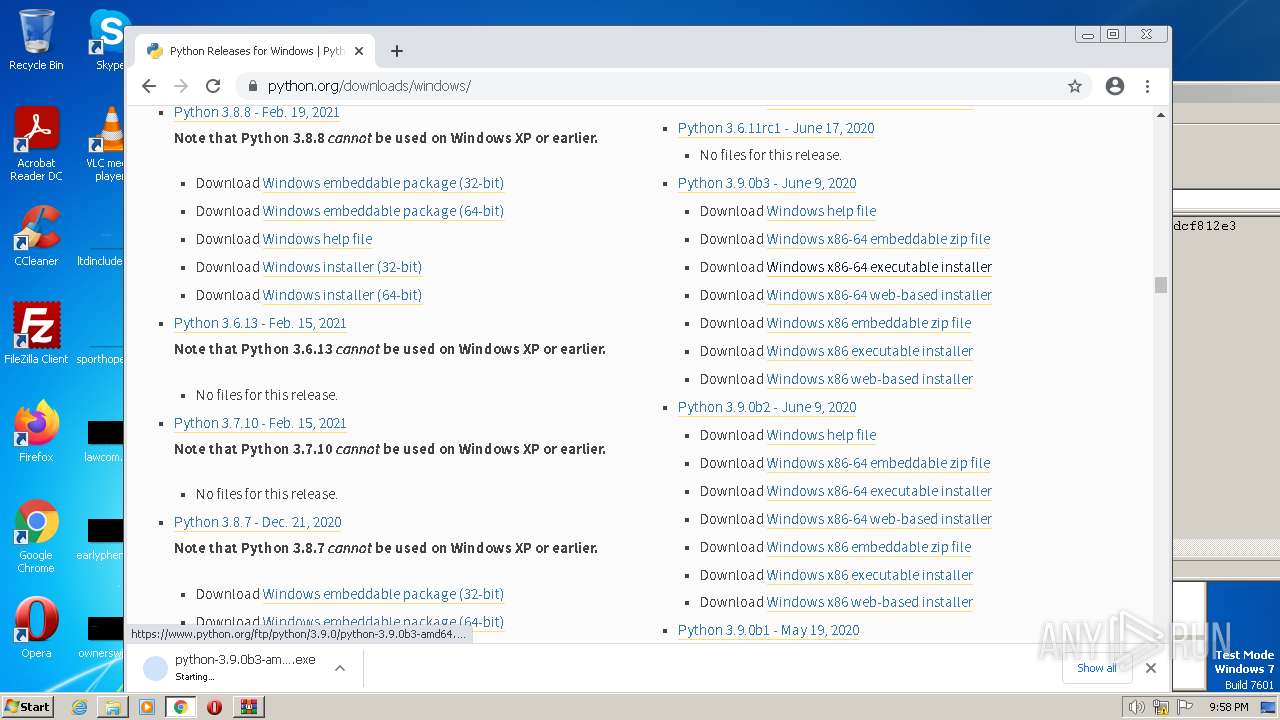
Manual execution by a user
- rundll32.exe (PID: 1144)
- chrome.exe (PID: 2056)
- rundll32.exe (PID: 2528)
- rundll32.exe (PID: 3984)
Checks supported languages
- python-3.9.0b3-amd64.exe (PID: 3604)
- python-3.9.0b3-amd64.exe (PID: 596)
- python-3.9.0b3-amd64.exe (PID: 3996)
- msiexec.exe (PID: 2968)
Create files in a temporary directory
- python-3.9.0b3-amd64.exe (PID: 3604)
- python-3.9.0b3-amd64.exe (PID: 596)
The process uses the downloaded file
- chrome.exe (PID: 3652)
- chrome.exe (PID: 2056)
Reads the computer name
- python-3.9.0b3-amd64.exe (PID: 596)
- python-3.9.0b3-amd64.exe (PID: 3996)
- msiexec.exe (PID: 2968)
The process checks LSA protection
- python-3.9.0b3-amd64.exe (PID: 596)
- python-3.9.0b3-amd64.exe (PID: 3996)
- VSSVC.exe (PID: 3748)
- msiexec.exe (PID: 2968)
Application launched itself
- chrome.exe (PID: 2056)
- iexplore.exe (PID: 3880)
Reads the machine GUID from the registry
- python-3.9.0b3-amd64.exe (PID: 596)
- msiexec.exe (PID: 2968)
- python-3.9.0b3-amd64.exe (PID: 3996)
Creates files or folders in the user directory
- python-3.9.0b3-amd64.exe (PID: 596)
Creates files in the program directory
- python-3.9.0b3-amd64.exe (PID: 3996)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2968)
- chrome.exe (PID: 908)
- chrome.exe (PID: 2056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
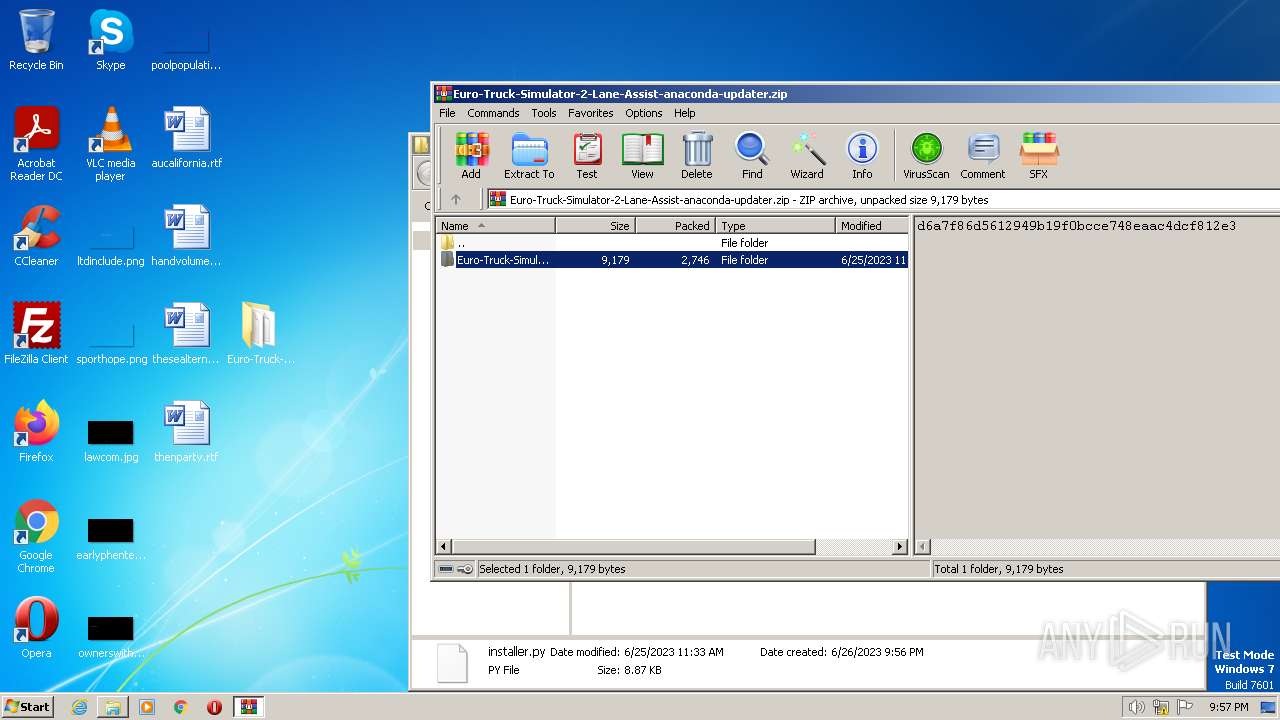
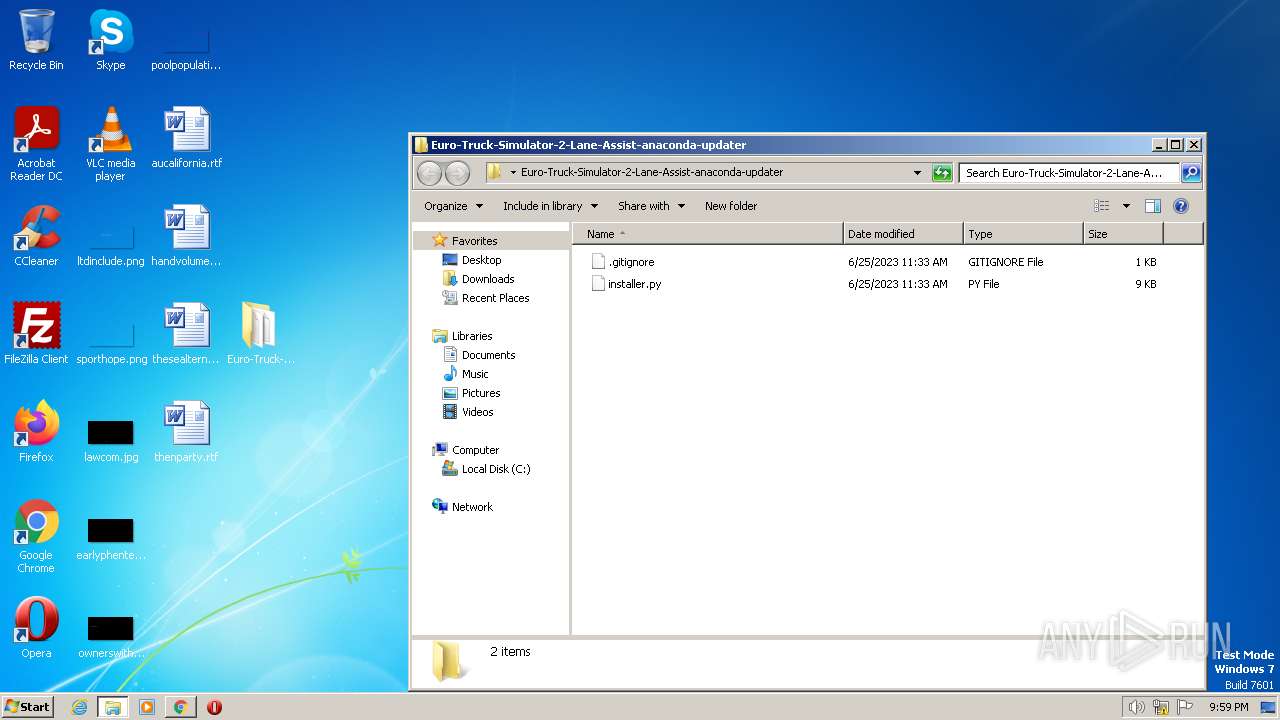
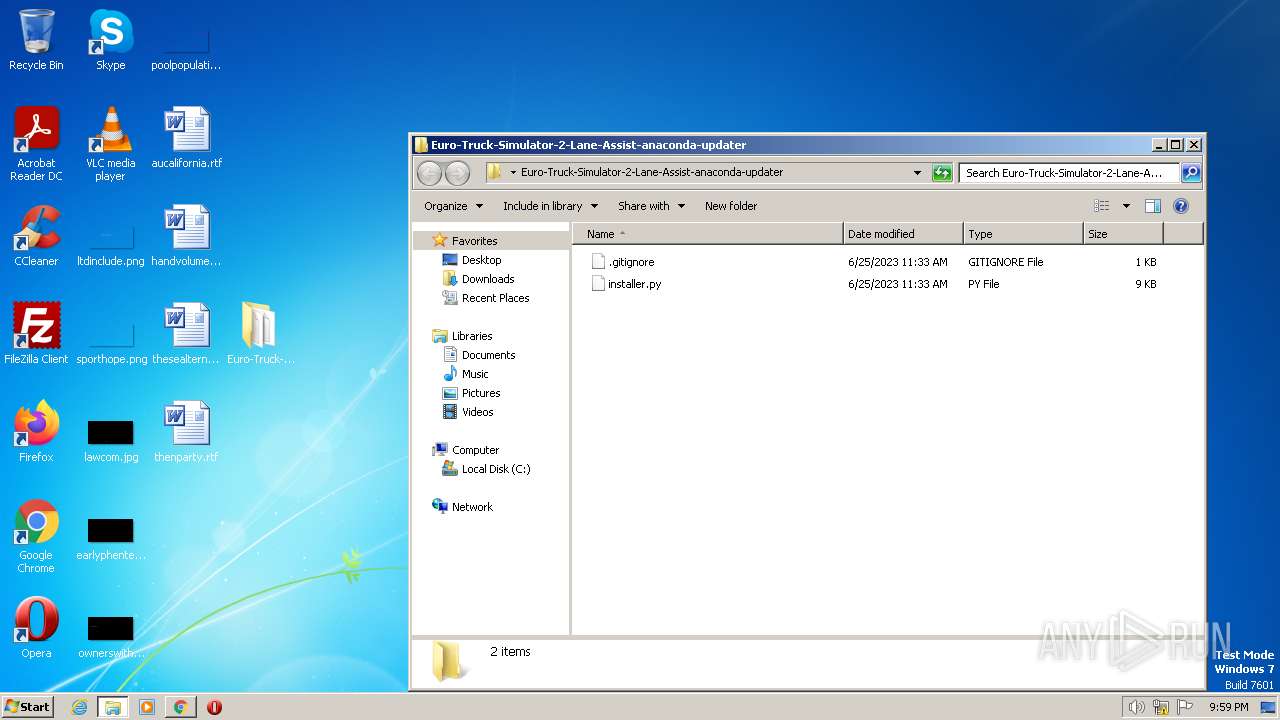
| ZipFileName: | Euro-Truck-Simulator-2-Lane-Assist-anaconda-updater/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2023:06:25 03:33:48 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 10 |
Total processes
83
Monitored processes
38
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1032,2571827114902905641,4846653215085047736,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=1484 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 596 | "C:\Users\admin\AppData\Local\Temp\{B176CD5C-F646-4484-93E5-F823C1A302BB}\.cr\python-3.9.0b3-amd64.exe" -burn.clean.room="C:\Users\admin\Downloads\python-3.9.0b3-amd64.exe" -burn.filehandle.attached=152 -burn.filehandle.self=160 | C:\Users\admin\AppData\Local\Temp\{B176CD5C-F646-4484-93E5-F823C1A302BB}\.cr\python-3.9.0b3-amd64.exe | python-3.9.0b3-amd64.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python 3.9.0b3 (64-bit) Exit code: 1633 Version: 3.9.113.0 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1032,2571827114902905641,4846653215085047736,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1292 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,2571827114902905641,4846653215085047736,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,2571827114902905641,4846653215085047736,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,2571827114902905641,4846653215085047736,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bbad988,0x6bbad998,0x6bbad9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
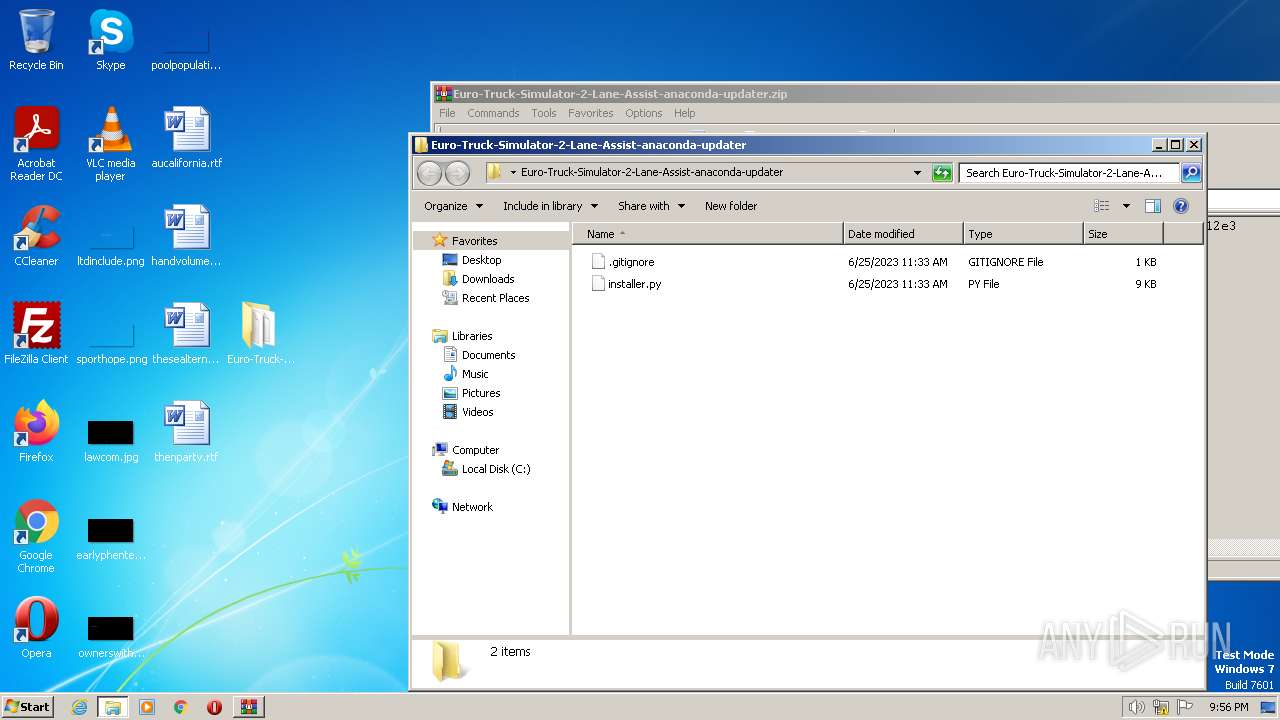
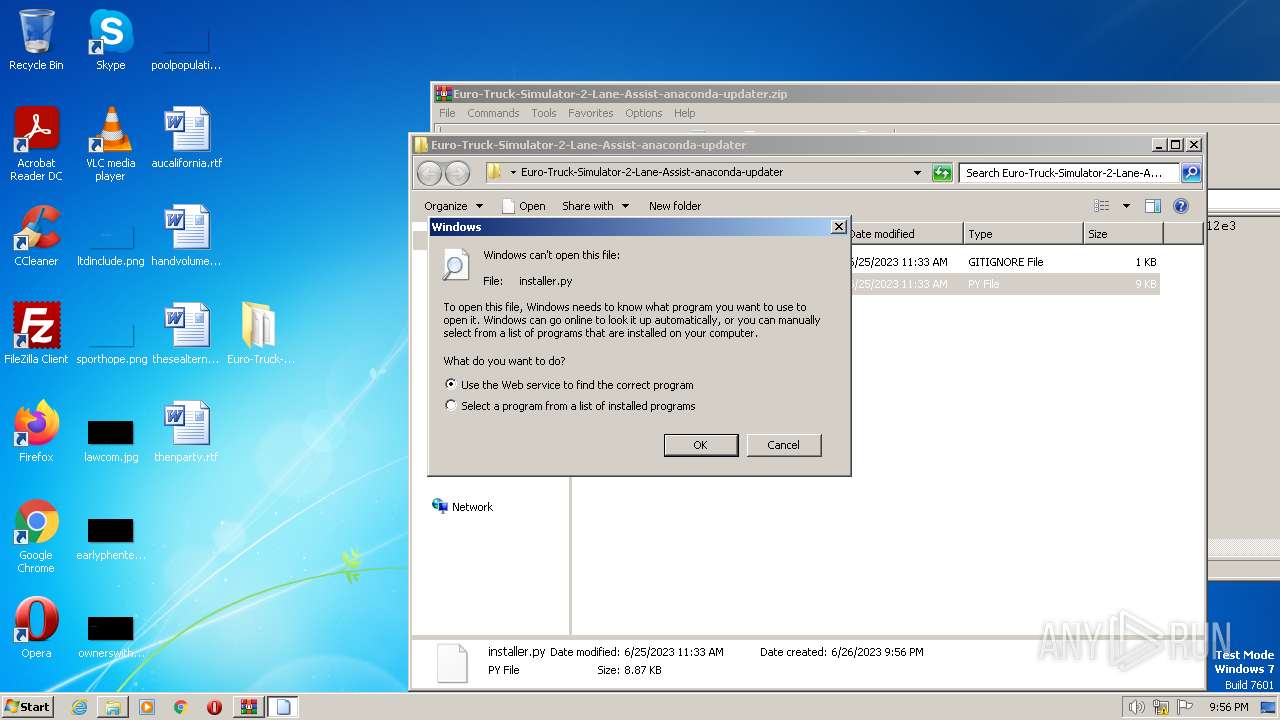
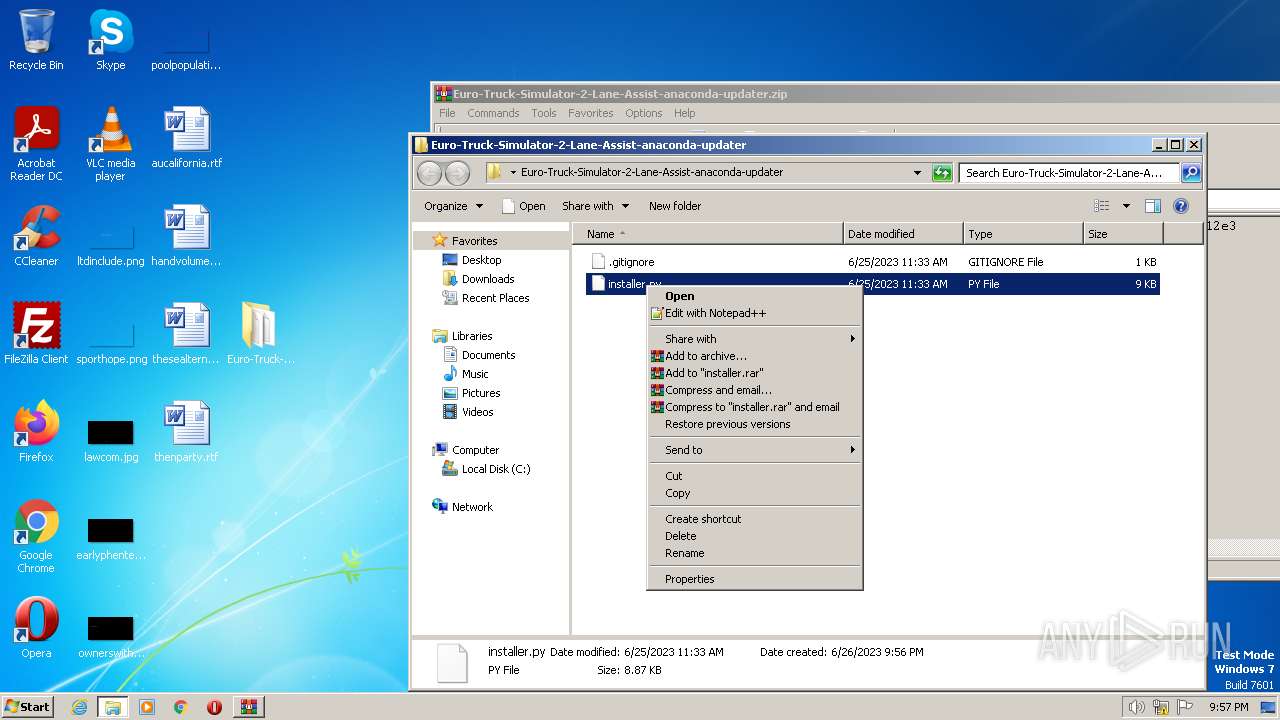
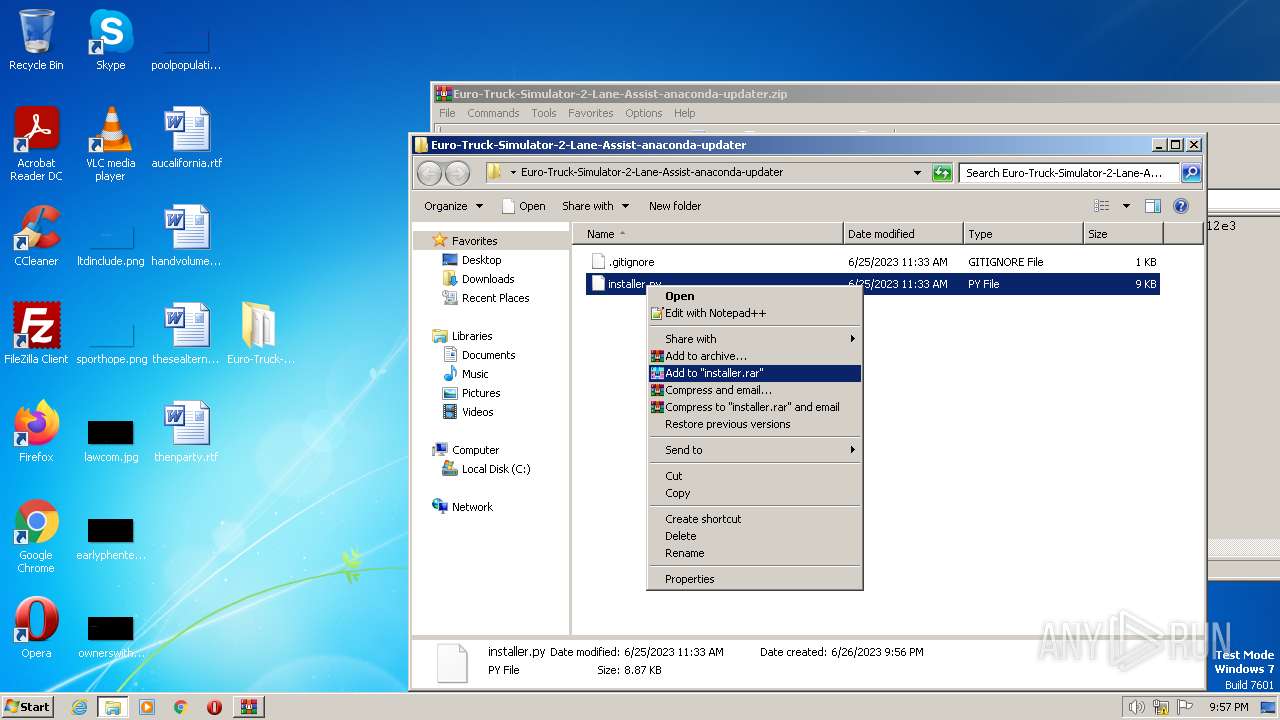
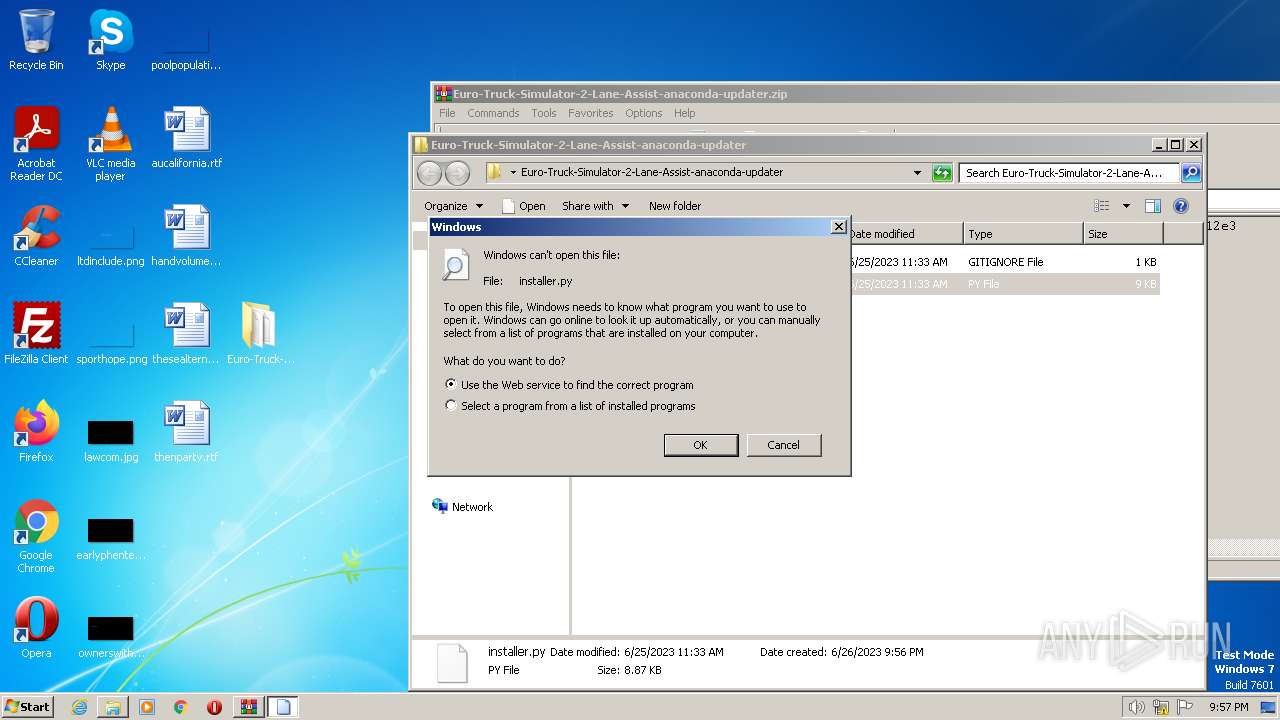
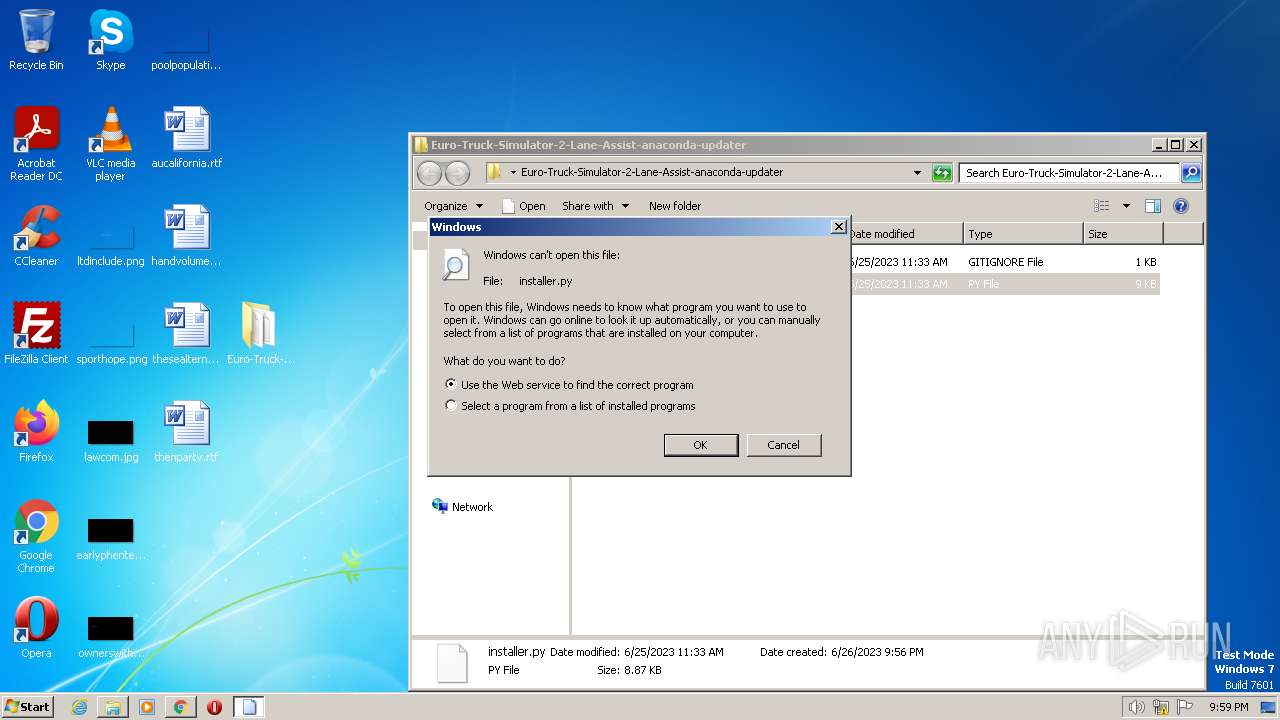
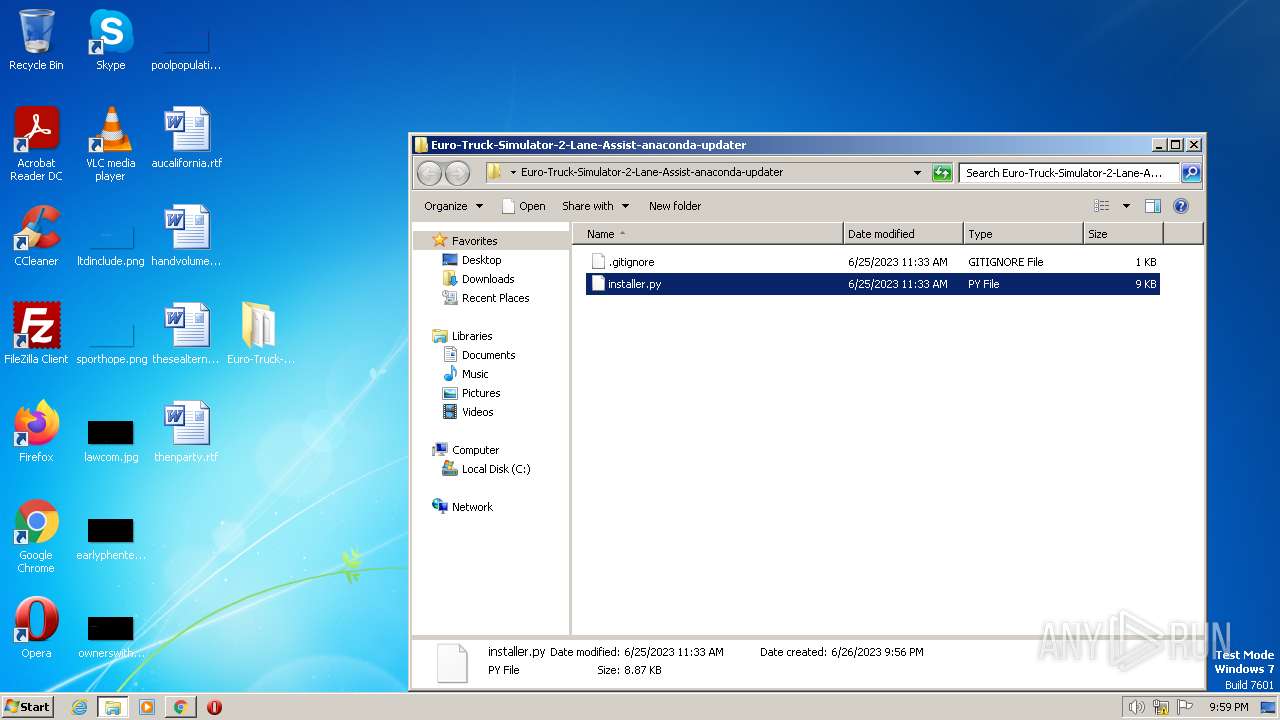
| 1144 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\Euro-Truck-Simulator-2-Lane-Assist-anaconda-updater\installer.py | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,2571827114902905641,4846653215085047736,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1572 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,2571827114902905641,4846653215085047736,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
26 659
Read events
26 386
Write events
260
Delete events
13
Modification events
| (PID) Process: | (2096) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2096) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
36
Suspicious files
65
Text files
114
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6499FBB0-808.pma | — | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF124a9e.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
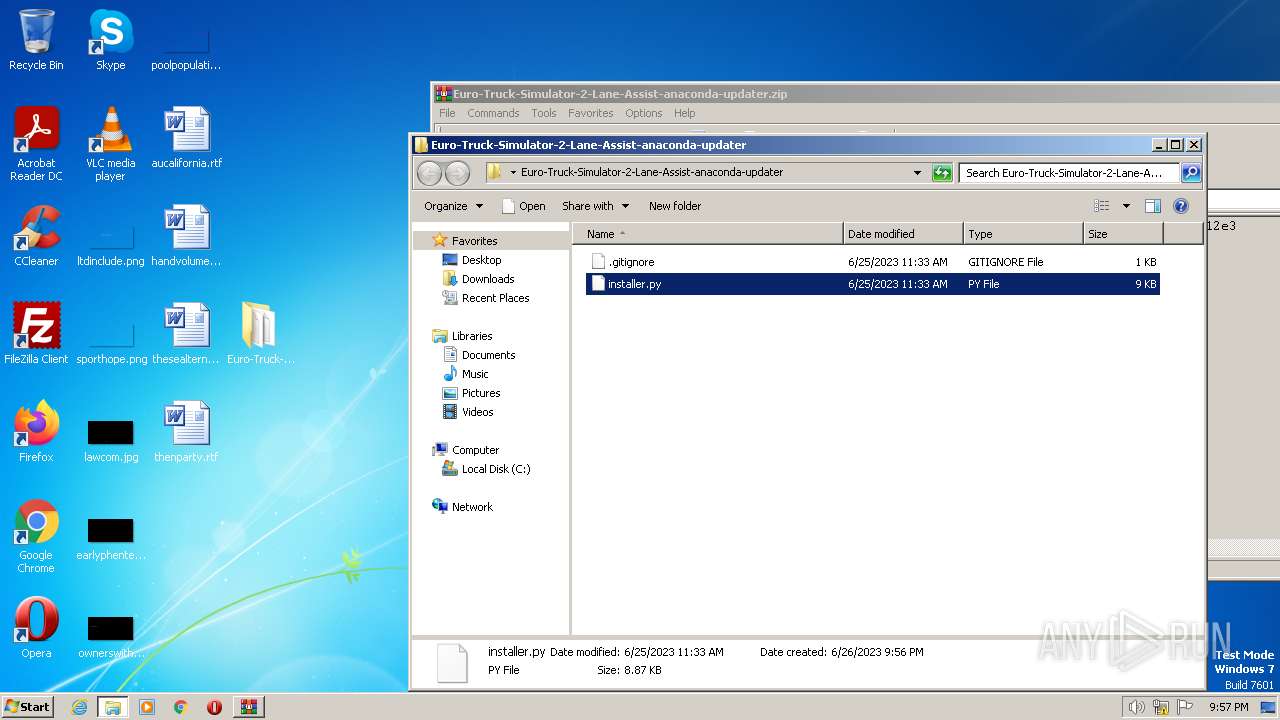
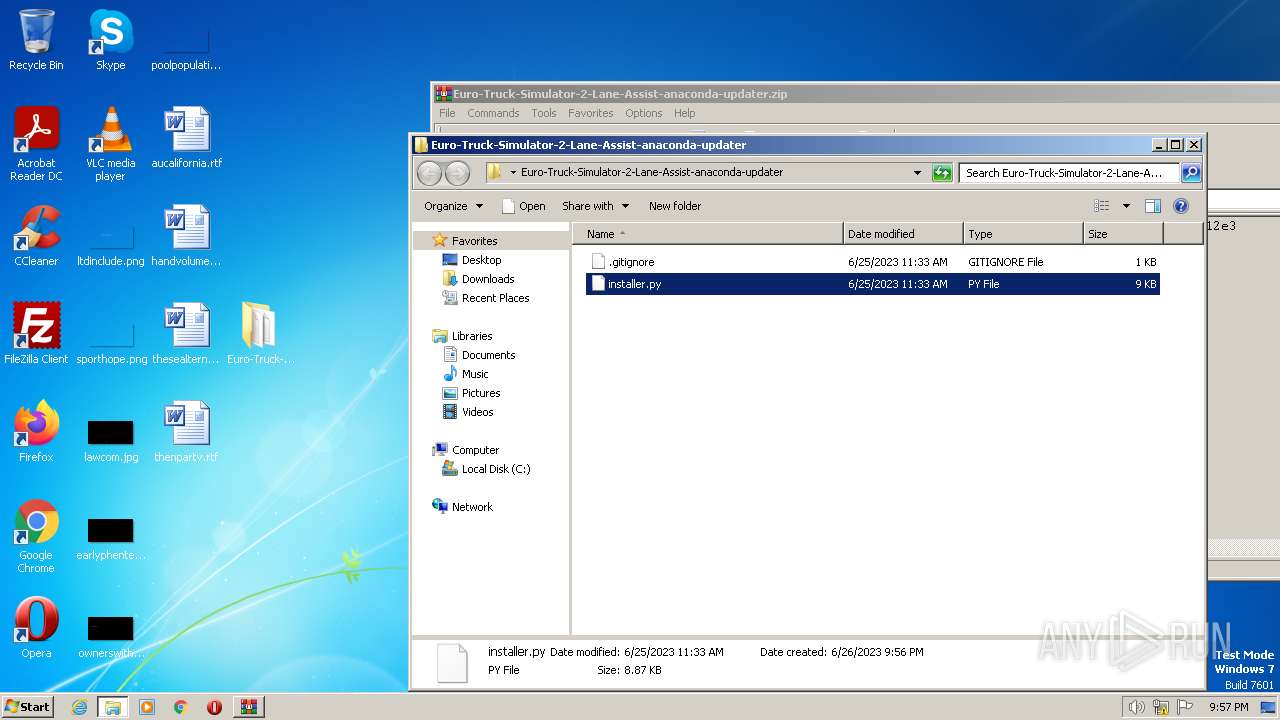
| 2096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2096.49857\Euro-Truck-Simulator-2-Lane-Assist-anaconda-updater\.gitignore | text | |
MD5:6ED6EF3EC0BF57233FB5EF86925F4E46 | SHA256:567963114D48651E70EFD7B22232877438F188D49BB0CB60BA8E222A4DBB898A | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2096.49857\Euro-Truck-Simulator-2-Lane-Assist-anaconda-updater\installer.py | text | |
MD5:AC8F7C5977CDC594734381ECB998068B | SHA256:EB4629233055731E3CB129EFD45FA47B2FC30BF9830DBA1B7DB4C9A567C73A8C | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF1249c3.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 1140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF124975.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
63
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
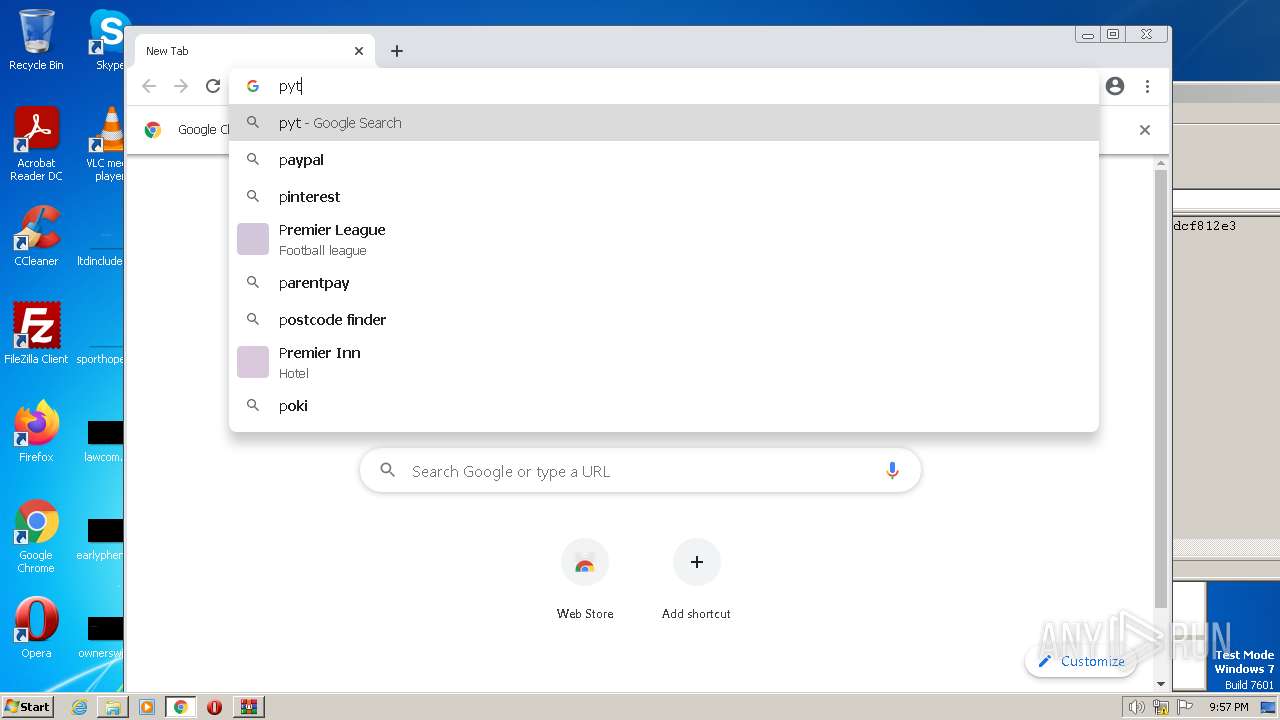
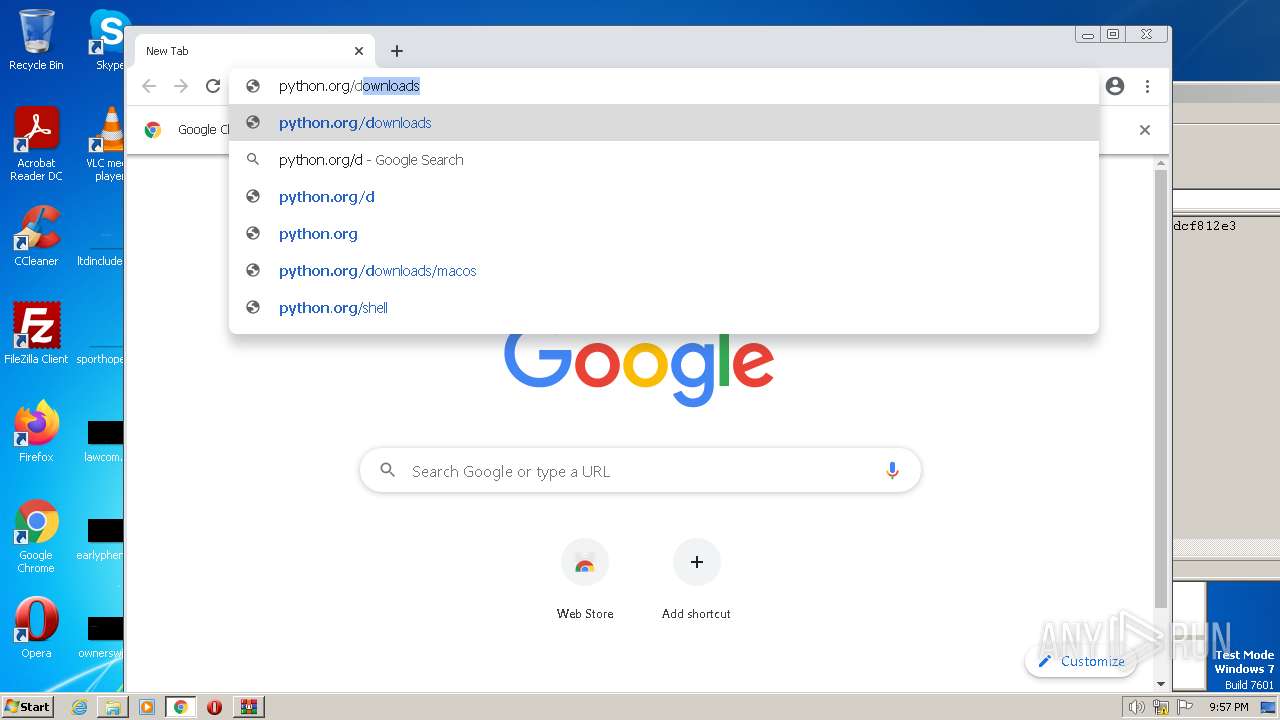
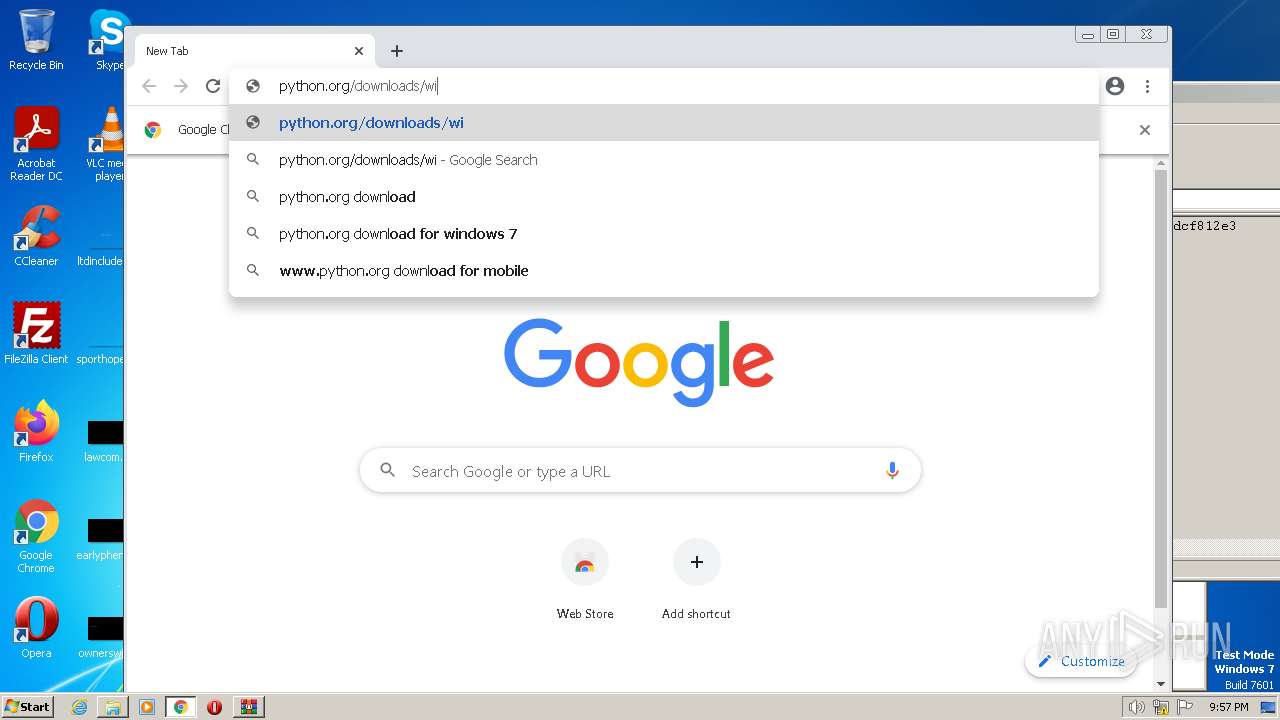
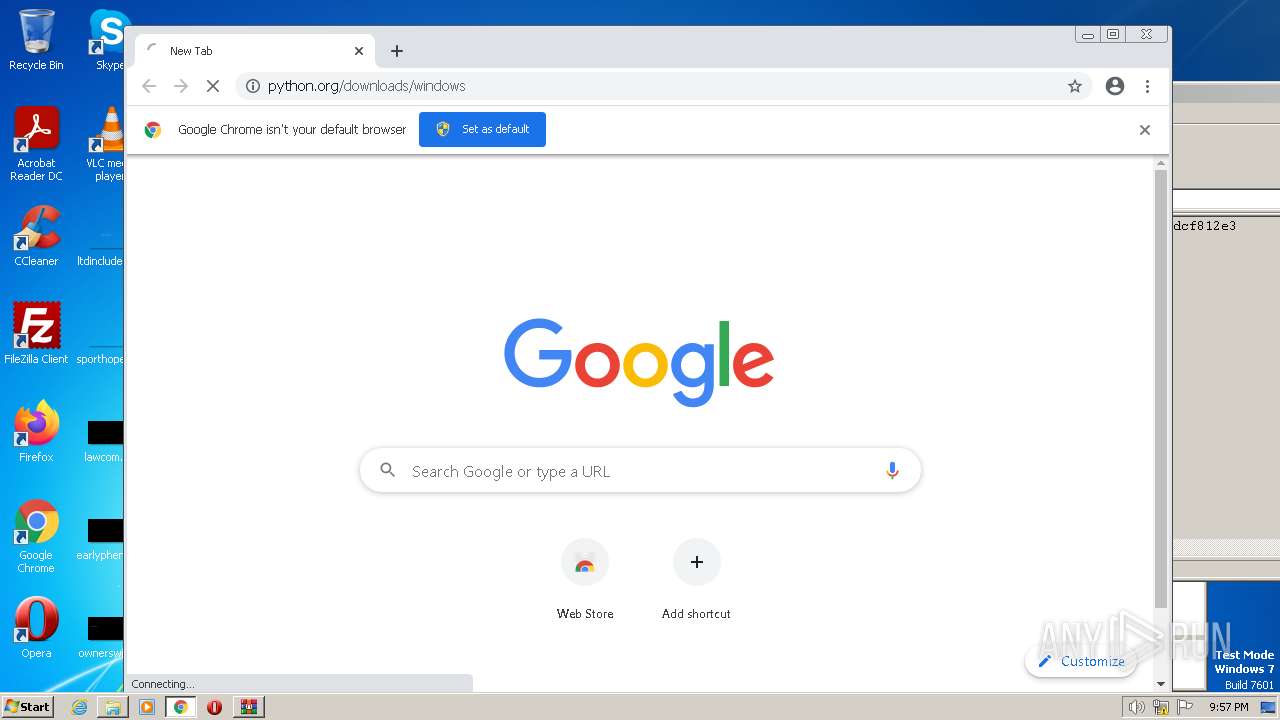
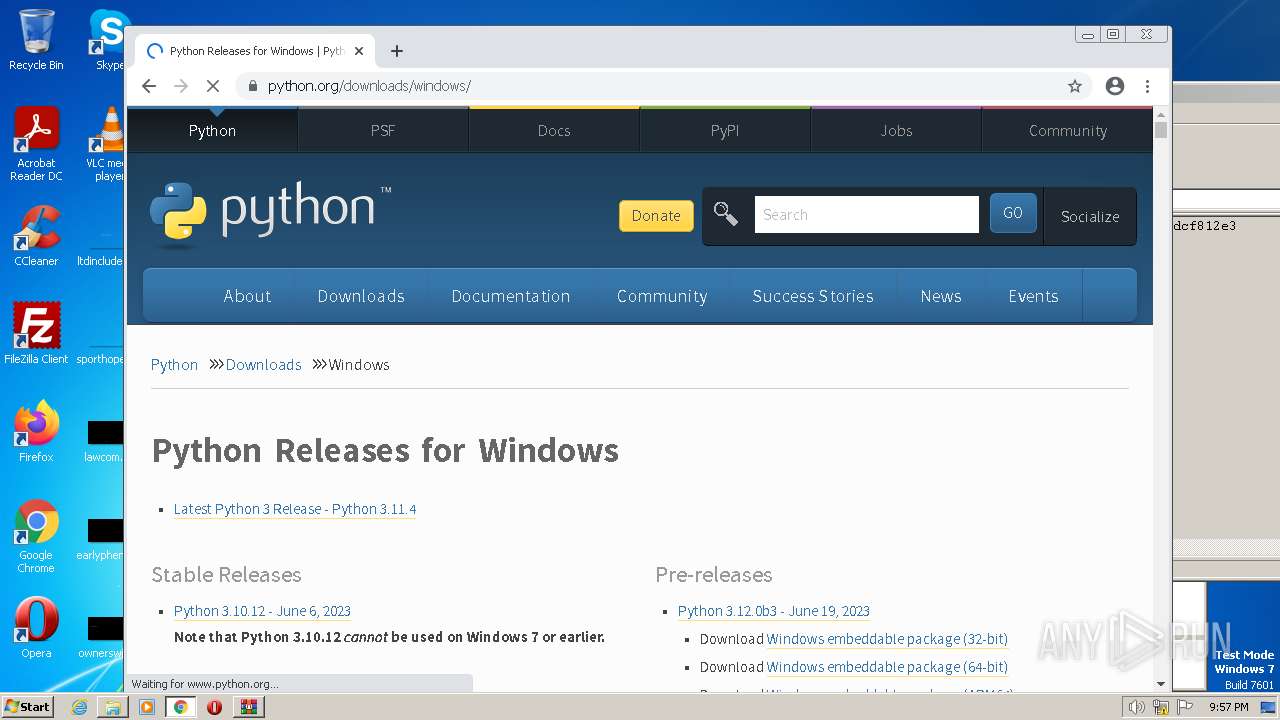
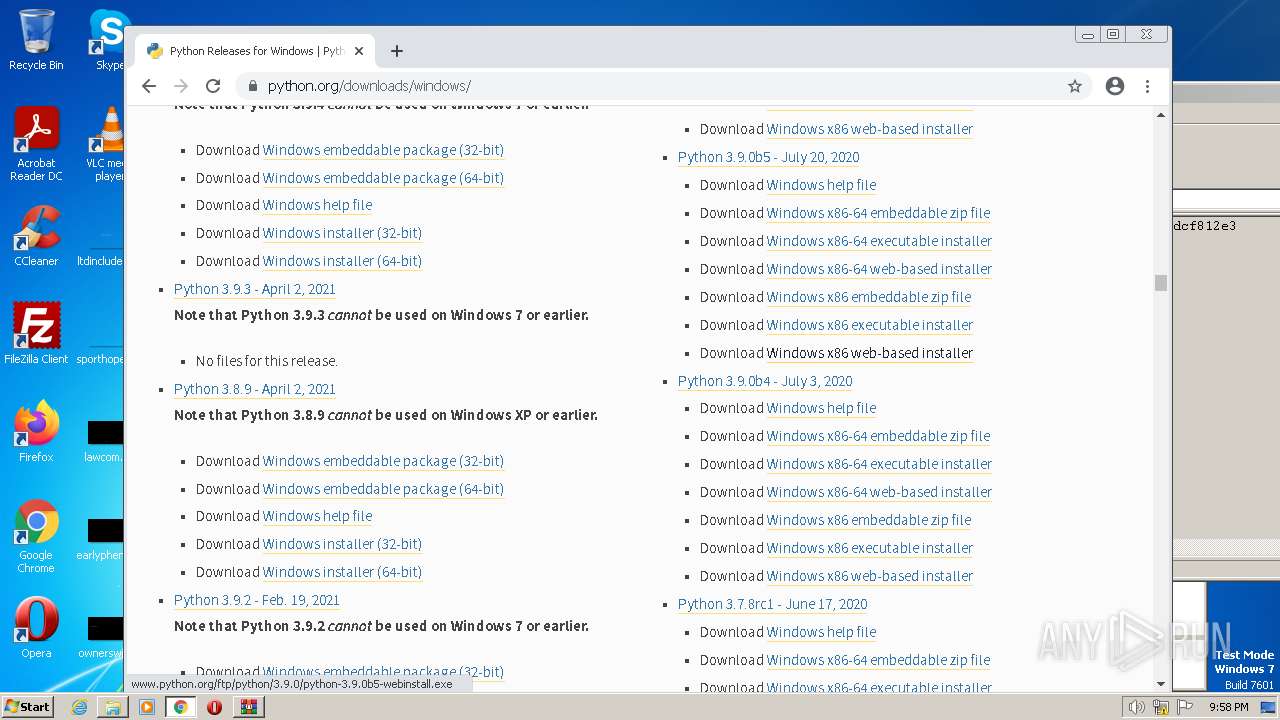
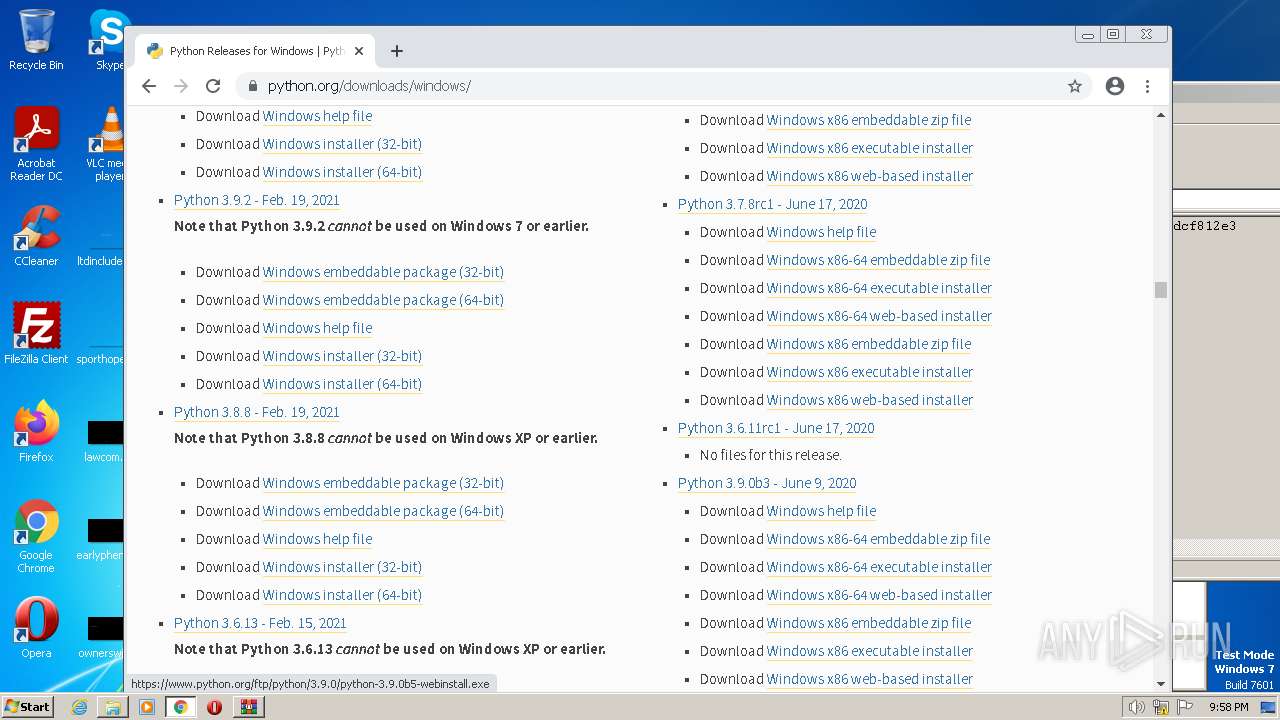
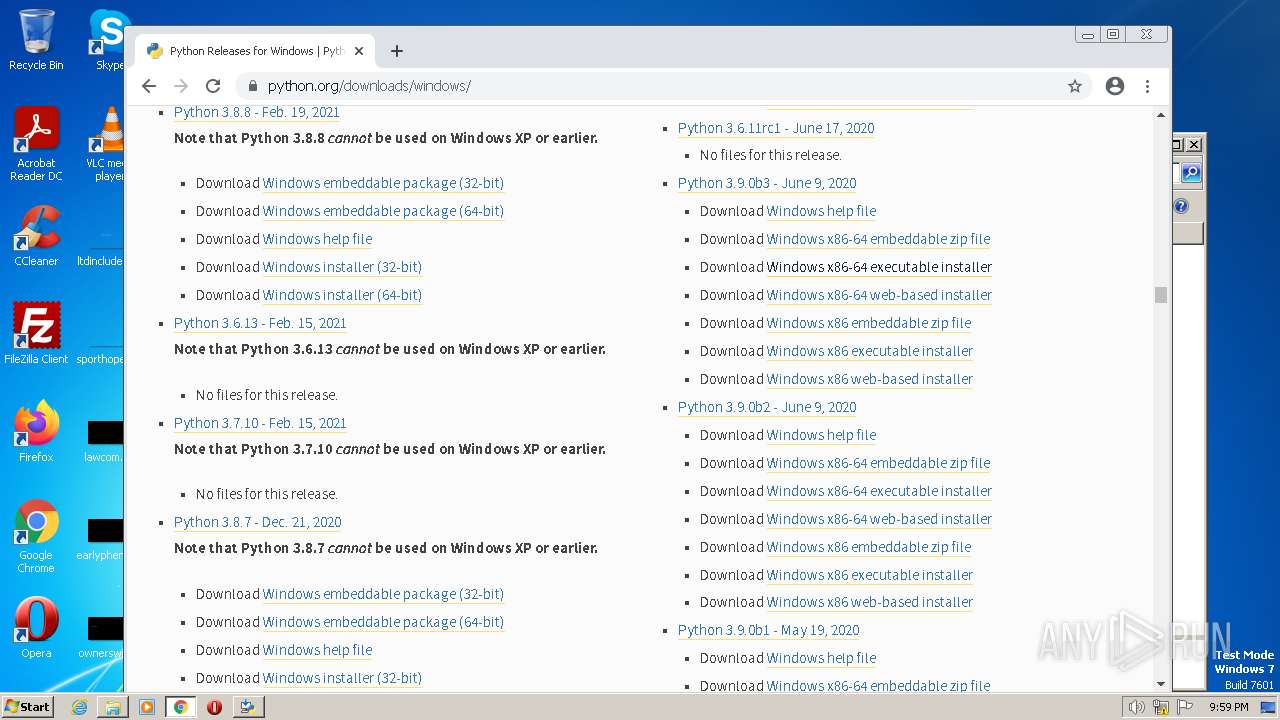
908 | chrome.exe | GET | 301 | 151.101.193.168:80 | http://python.org/downloads/windows | US | — | — | whitelisted |
852 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/YGkwa4MXjfWSuERyWQYP_A_4/aapLKTSZ439A-0g3nqJr3Q | US | — | — | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kggj3i32kib3f7ydpbj53gn3km_2968/jflookgnkcckhobaglndicnbbgbonegd_2968_all_i65jksxtophwtcqkuykfc4pmyi.crx3 | US | binary | 7.00 Kb | whitelisted |
852 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kggj3i32kib3f7ydpbj53gn3km_2968/jflookgnkcckhobaglndicnbbgbonegd_2968_all_i65jksxtophwtcqkuykfc4pmyi.crx3 | US | binary | 3.72 Kb | whitelisted |
852 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/YGkwa4MXjfWSuERyWQYP_A_4/aapLKTSZ439A-0g3nqJr3Q | US | binary | 3.72 Kb | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kggj3i32kib3f7ydpbj53gn3km_2968/jflookgnkcckhobaglndicnbbgbonegd_2968_all_i65jksxtophwtcqkuykfc4pmyi.crx3 | US | binary | 9.85 Kb | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kggj3i32kib3f7ydpbj53gn3km_2968/jflookgnkcckhobaglndicnbbgbonegd_2968_all_i65jksxtophwtcqkuykfc4pmyi.crx3 | US | binary | 21.1 Kb | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kggj3i32kib3f7ydpbj53gn3km_2968/jflookgnkcckhobaglndicnbbgbonegd_2968_all_i65jksxtophwtcqkuykfc4pmyi.crx3 | US | binary | 9.97 Kb | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kggj3i32kib3f7ydpbj53gn3km_2968/jflookgnkcckhobaglndicnbbgbonegd_2968_all_i65jksxtophwtcqkuykfc4pmyi.crx3 | US | binary | 10.4 Kb | whitelisted |
3592 | iexplore.exe | GET | 200 | 178.79.242.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?899dffb565387f3e | DE | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2056 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
908 | chrome.exe | 142.250.186.35:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
908 | chrome.exe | 142.250.186.141:443 | accounts.google.com | GOOGLE | US | whitelisted |
908 | chrome.exe | 142.250.184.196:443 | www.google.com | GOOGLE | US | whitelisted |
908 | chrome.exe | 142.250.181.238:443 | clients2.google.com | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
820 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
908 | chrome.exe | 172.217.16.195:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
python.org |
| whitelisted |
www.python.org |
| whitelisted |
www.googletagmanager.com |
| whitelisted |