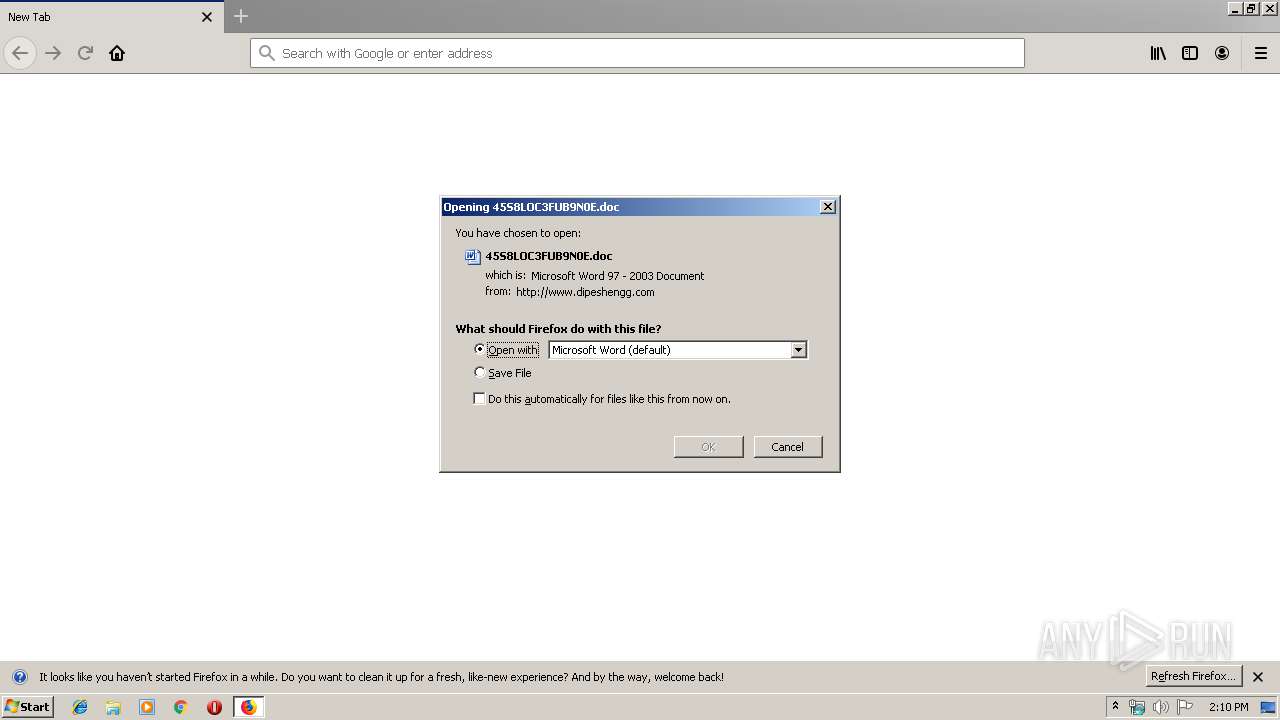
| URL: | http://www.dipeshengg.com/customers/paclm/cxDXknmMpgJCGLrsXOHGoicZqWSiwT/ |
| Full analysis: | https://app.any.run/tasks/961e9cfd-cc34-4b6f-b746-b01b3326896b |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 13:09:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8A7B6171BA0C39D19389CCD367D3127D |
| SHA1: | 70286D083D90C2B12CA562BED284069D93BCF281 |
| SHA256: | 959023257BC6321333170D1A16AFA8FE1643EA2D6C3D0BACCDEA91423C17AD62 |
| SSDEEP: | 3:N1KJS4zLBLGRQNIAUaGj9BnmMbiKj29K:Cc4zRGRY9UaGjzi39K |
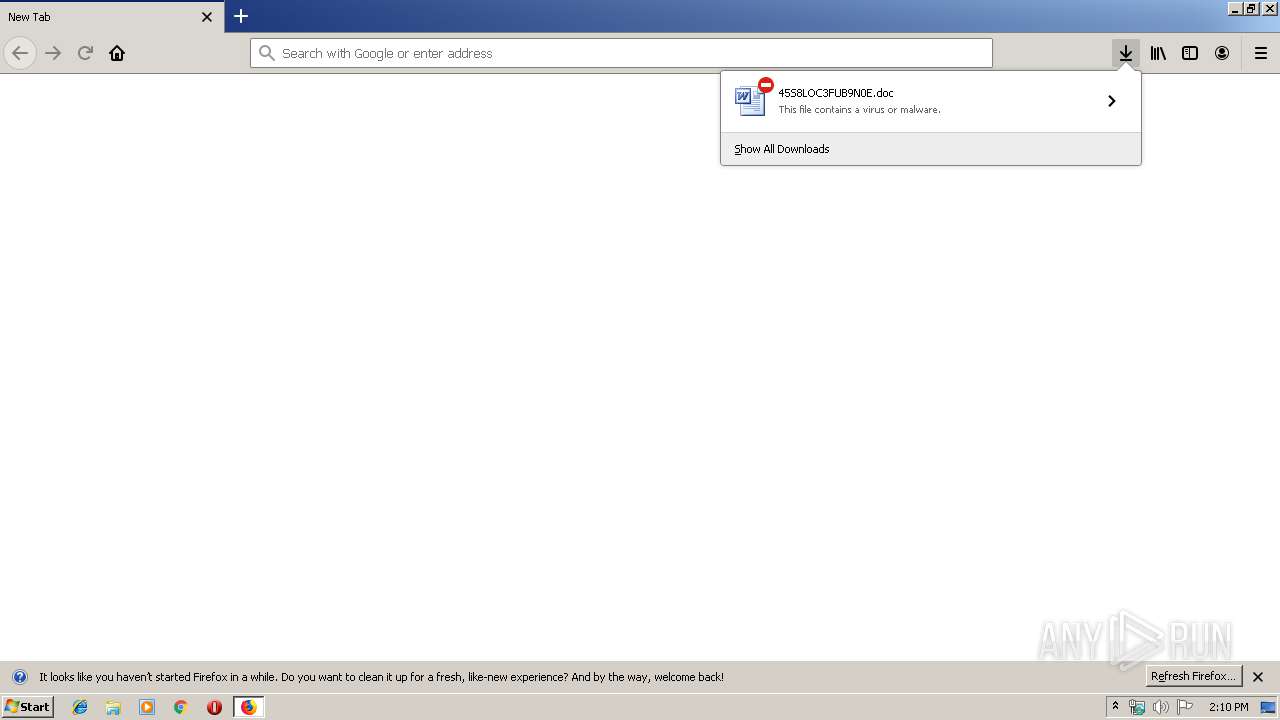
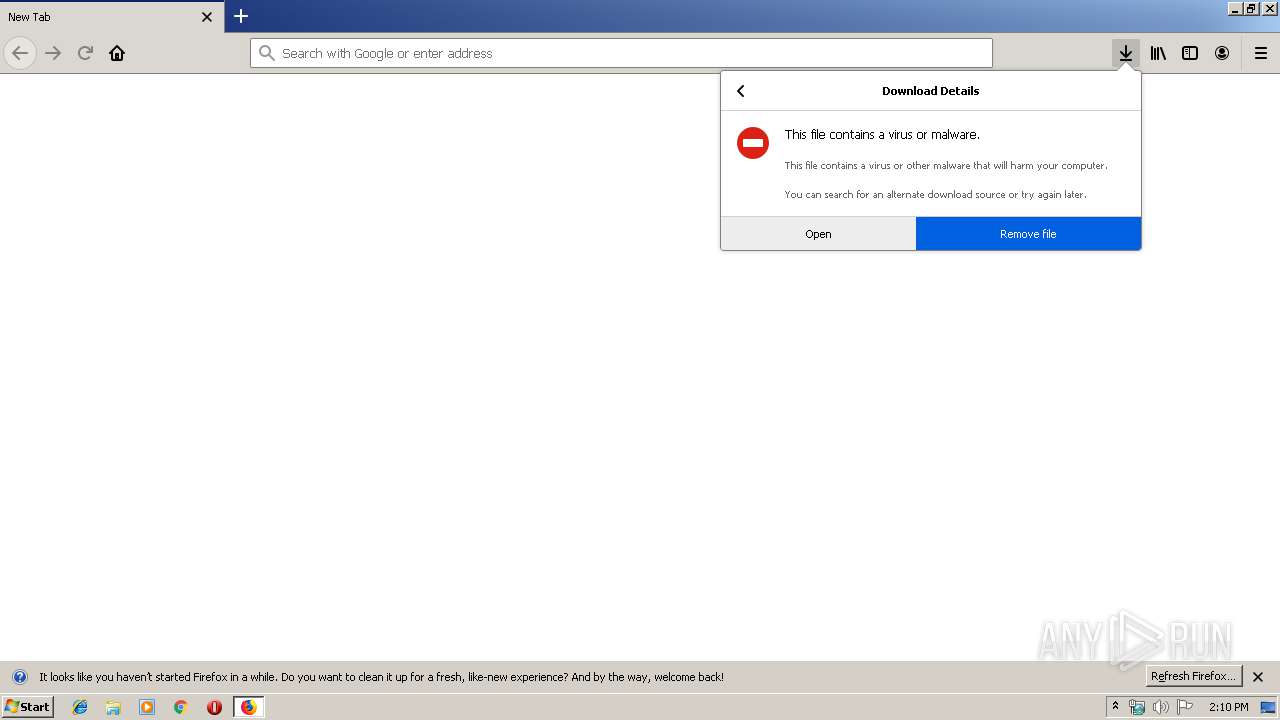
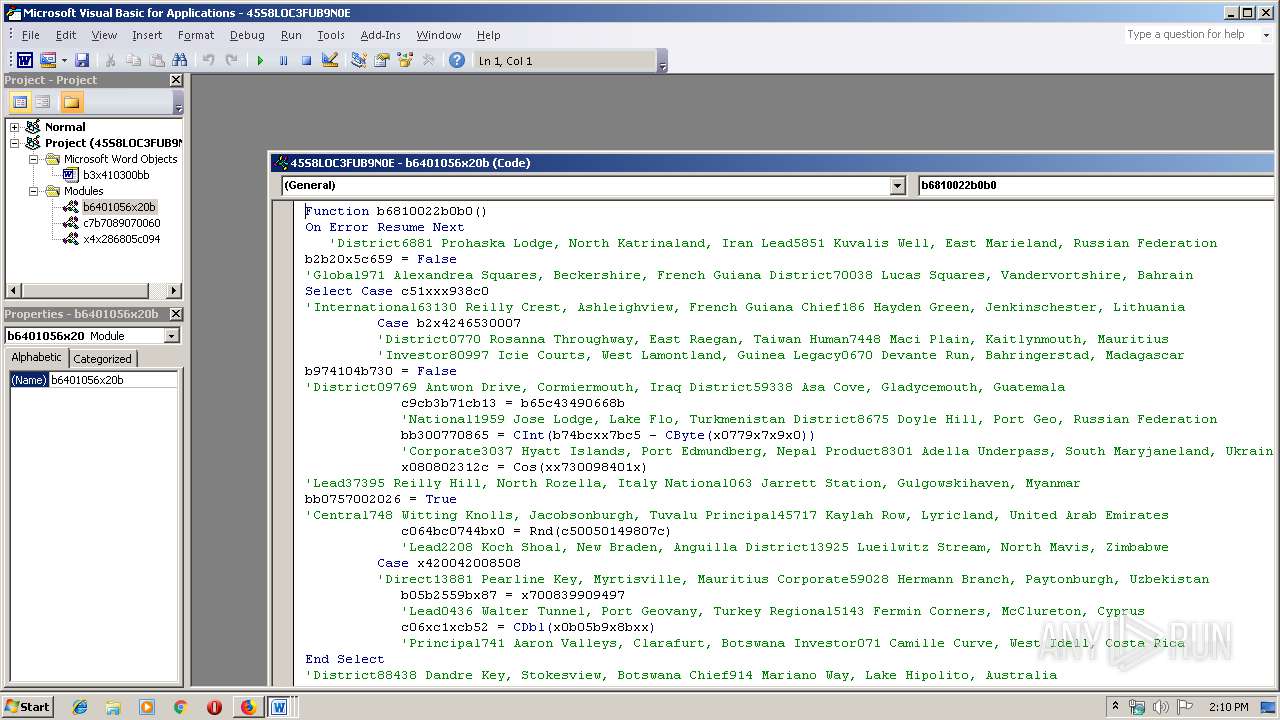
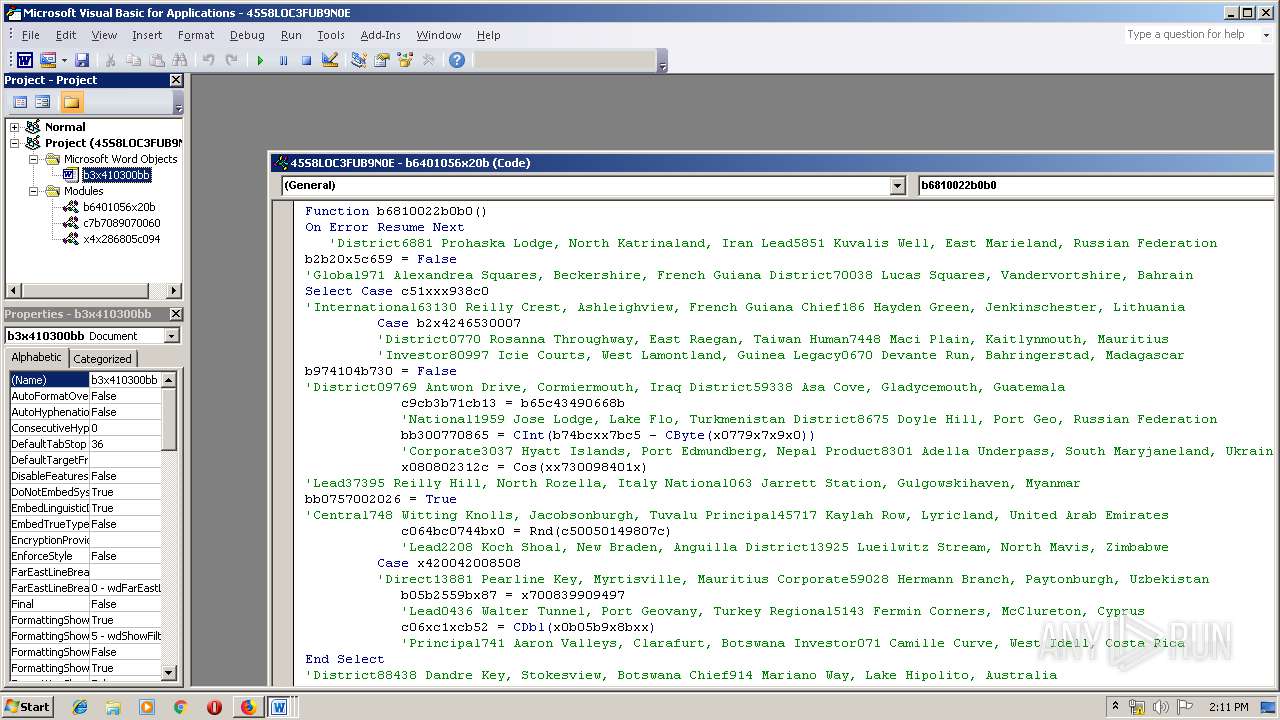
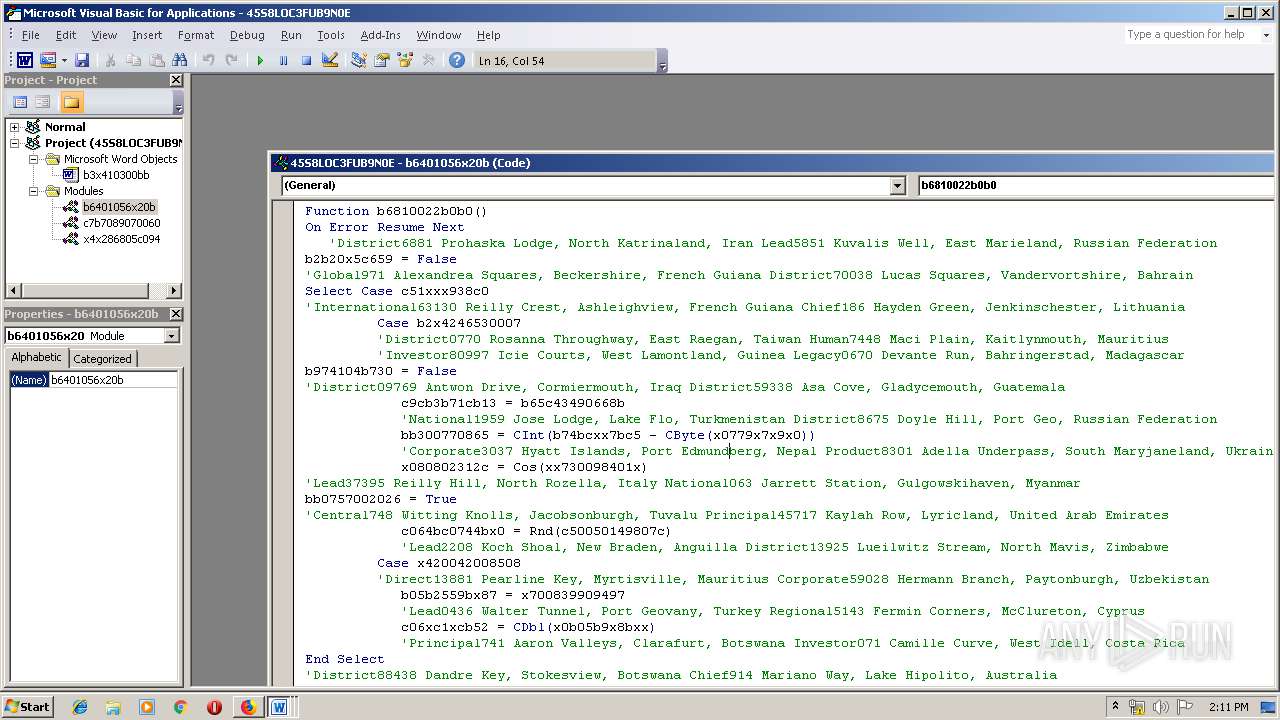
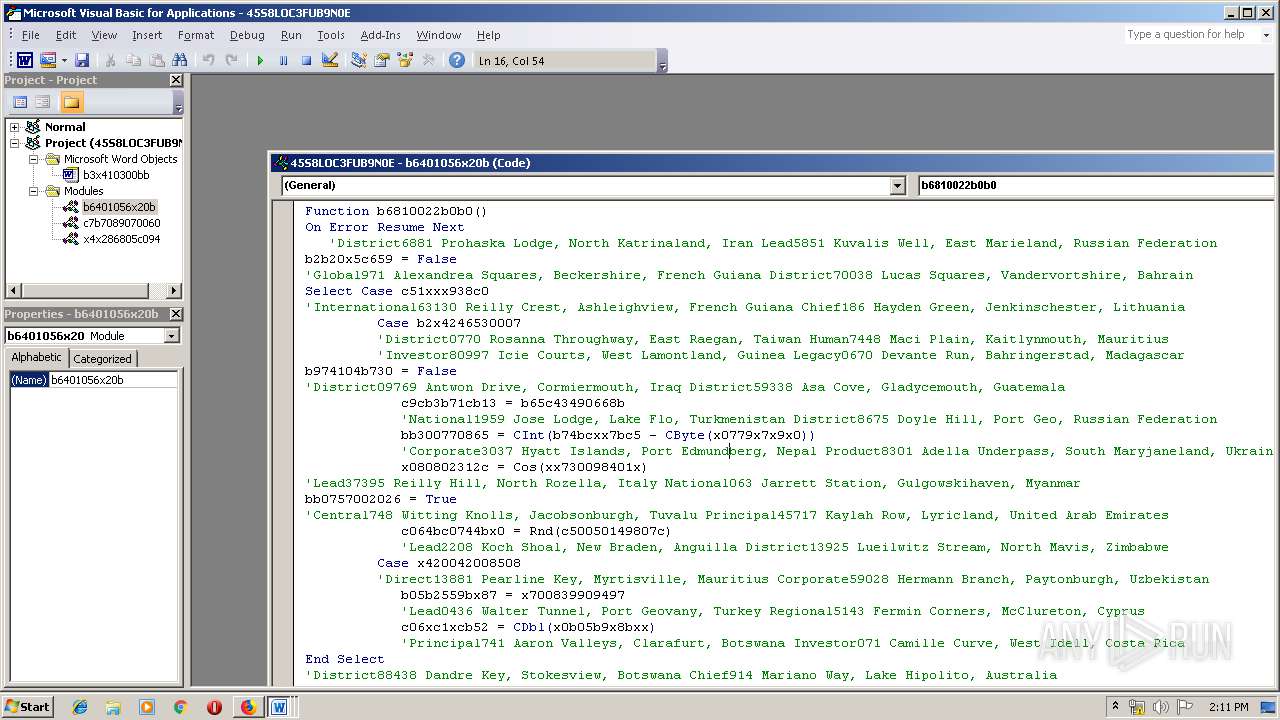
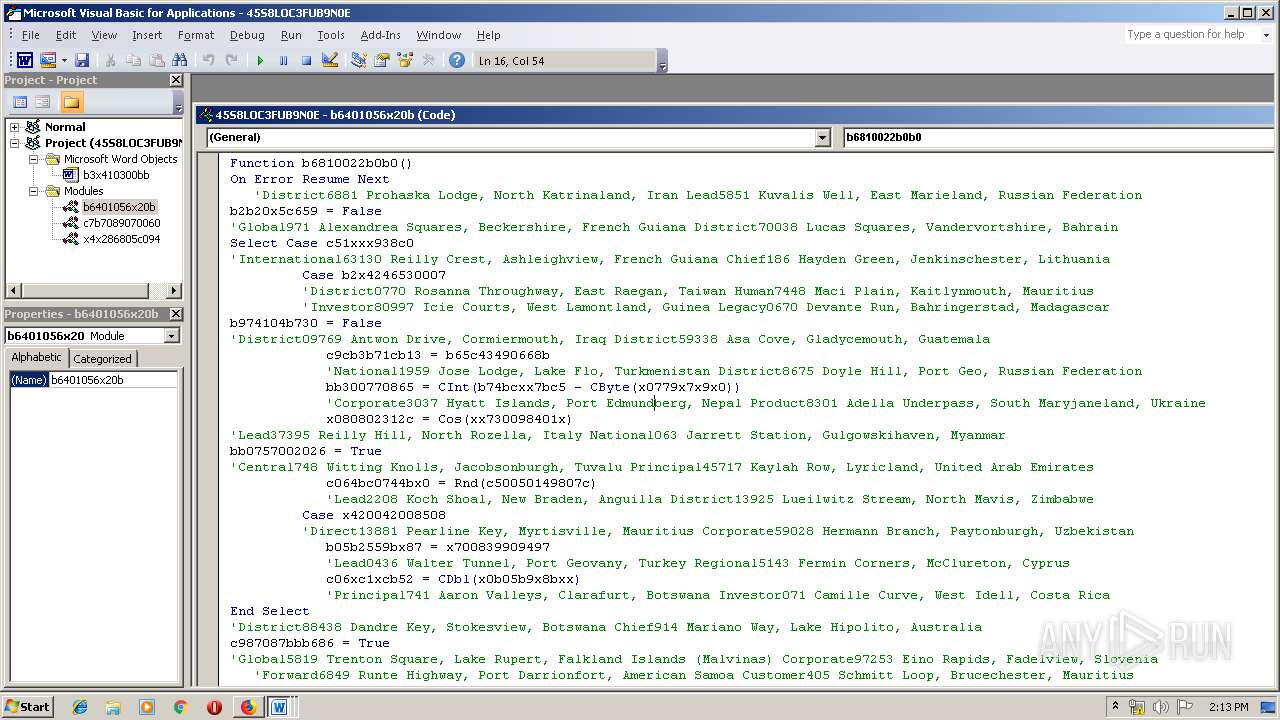
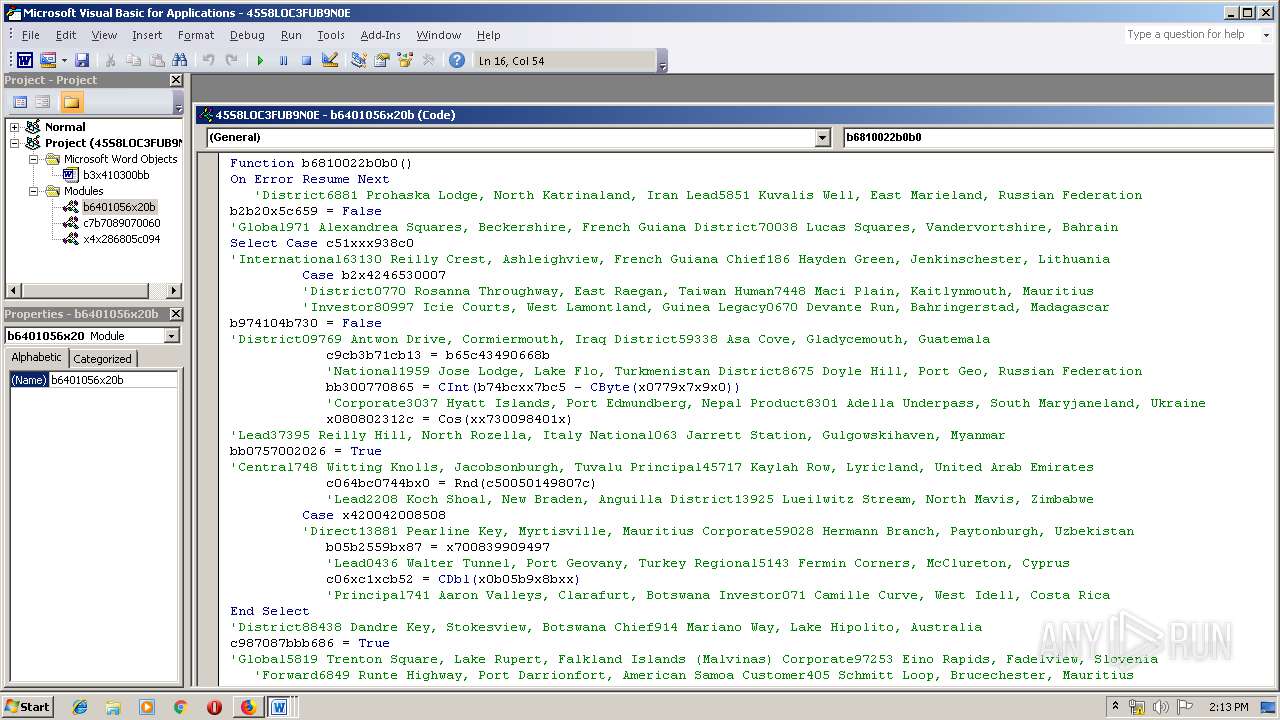
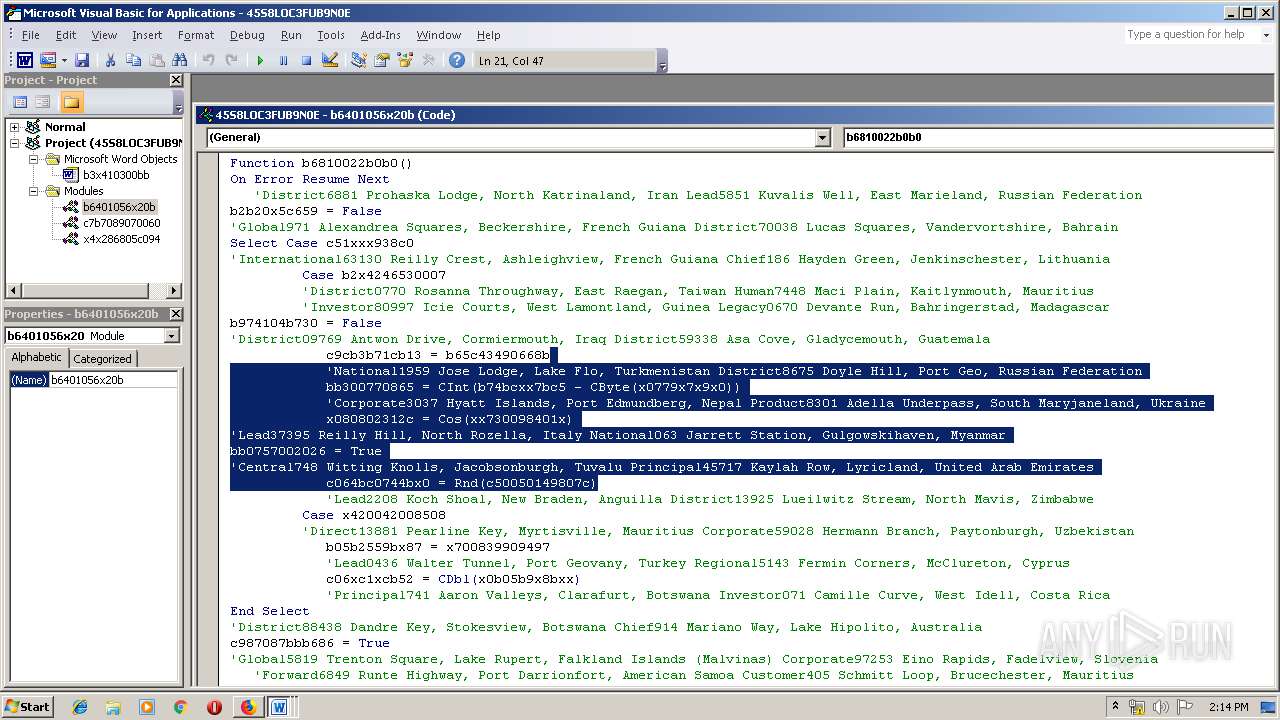
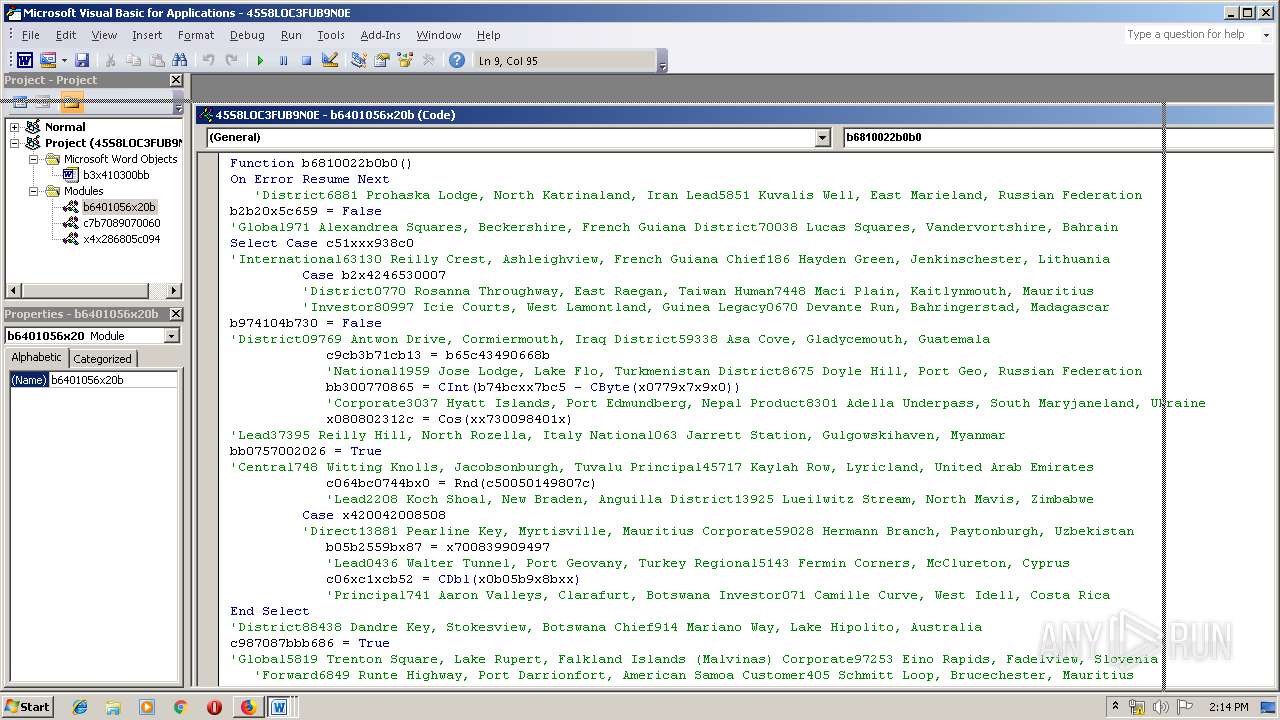
MALICIOUS
Drops known malicious document
- firefox.exe (PID: 2236)
- WINWORD.EXE (PID: 2180)
- WINWORD.EXE (PID: 1704)
Application was dropped or rewritten from another process
- 178.exe (PID: 2704)
- msptermsizes.exe (PID: 2784)
- msptermsizes.exe (PID: 1500)
- 178.exe (PID: 1524)
Emotet process was detected
- 178.exe (PID: 1524)
EMOTET was detected
- msptermsizes.exe (PID: 1500)
Connects to CnC server
- msptermsizes.exe (PID: 1500)
Changes the autorun value in the registry
- msptermsizes.exe (PID: 1500)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2236)
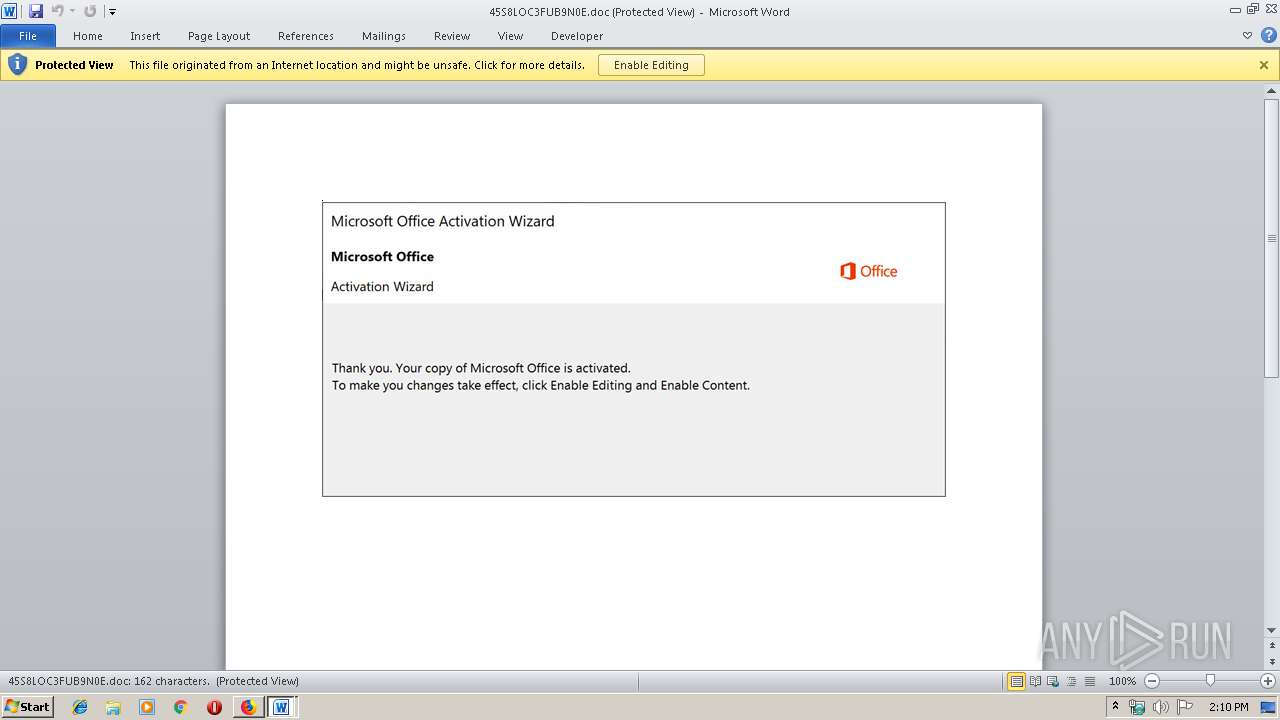
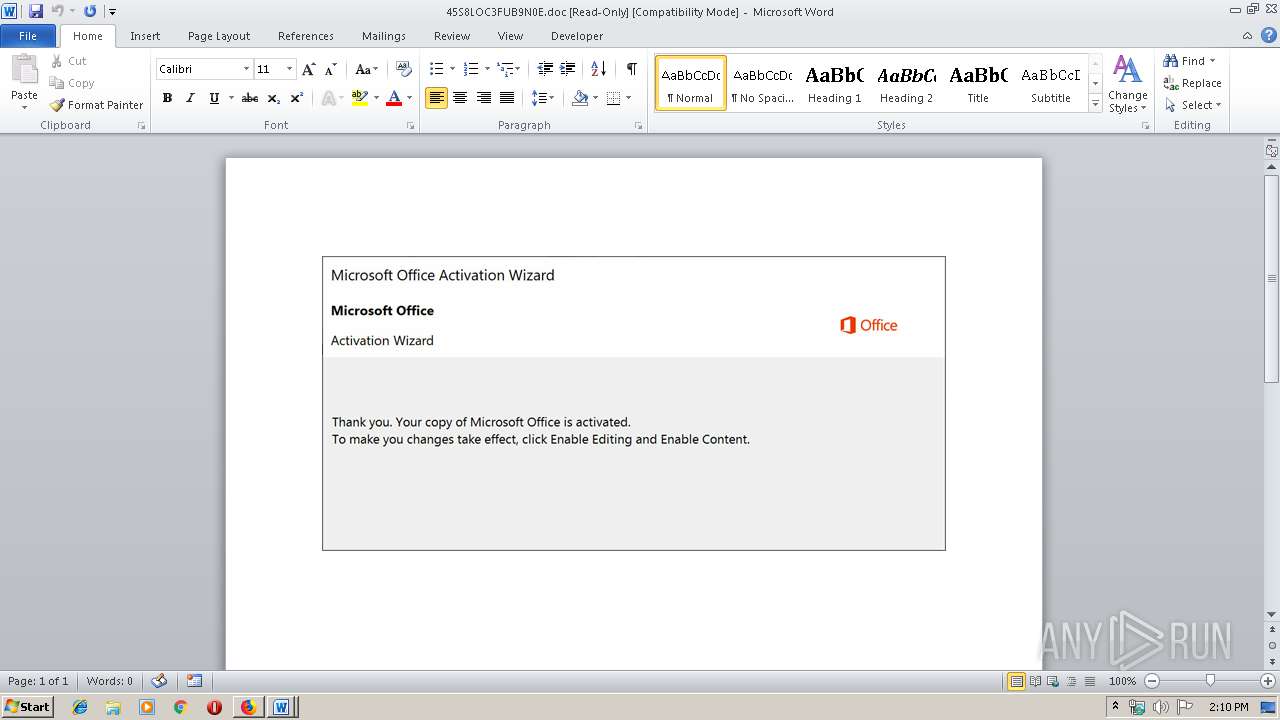
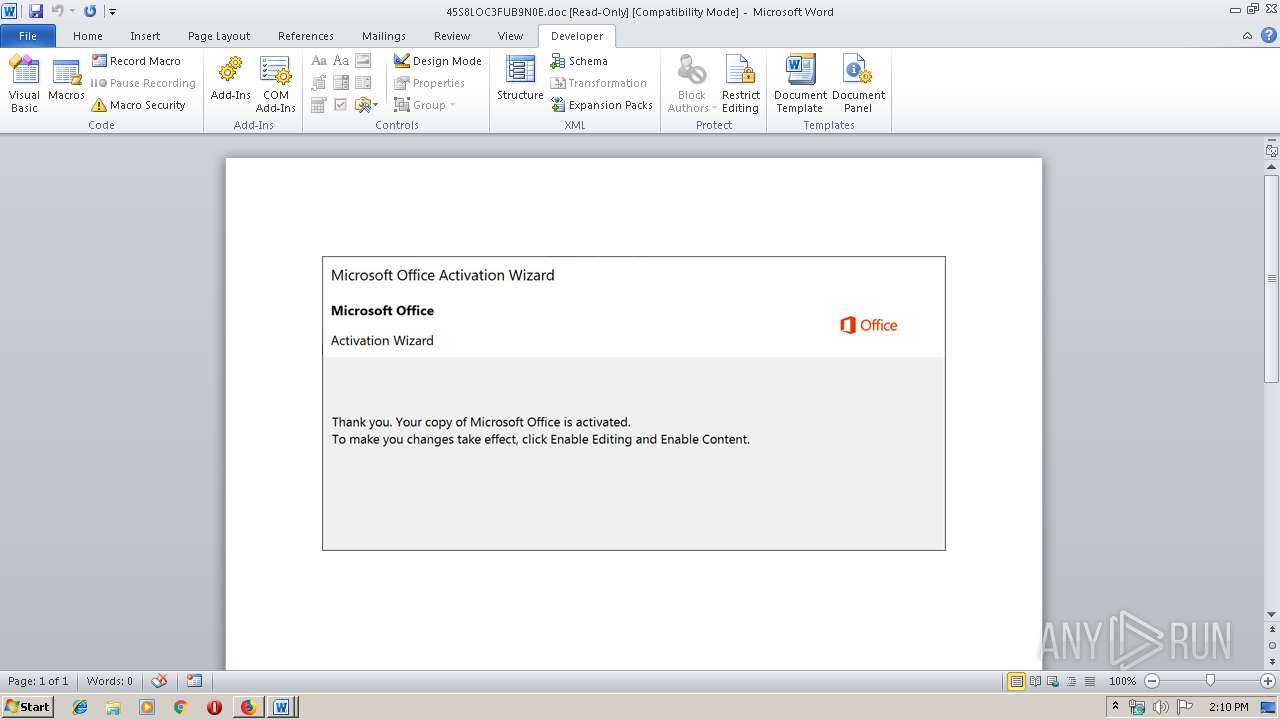
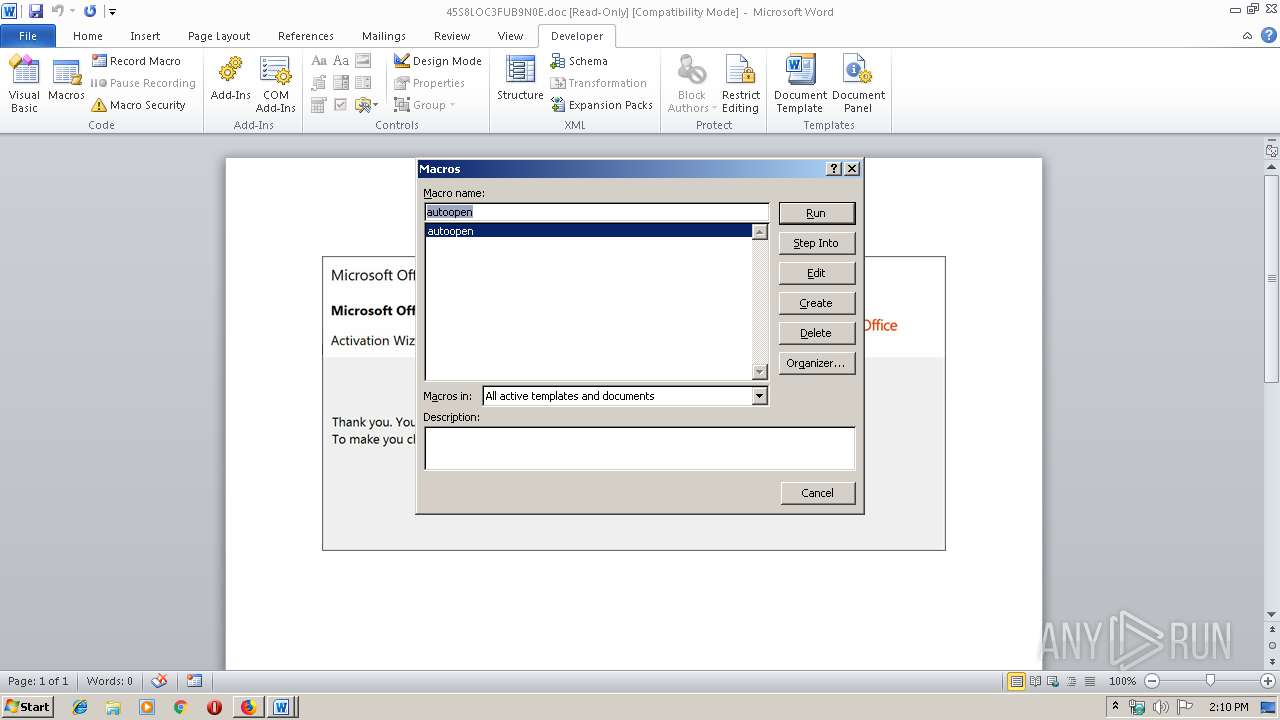
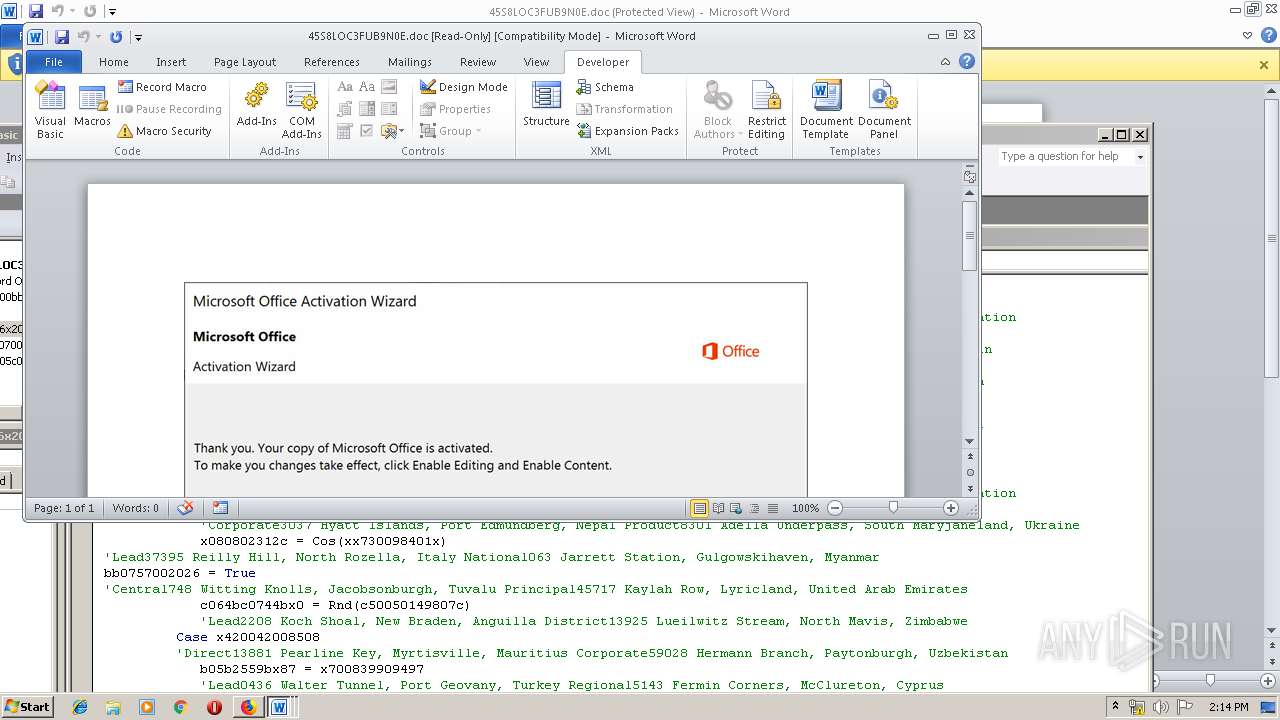
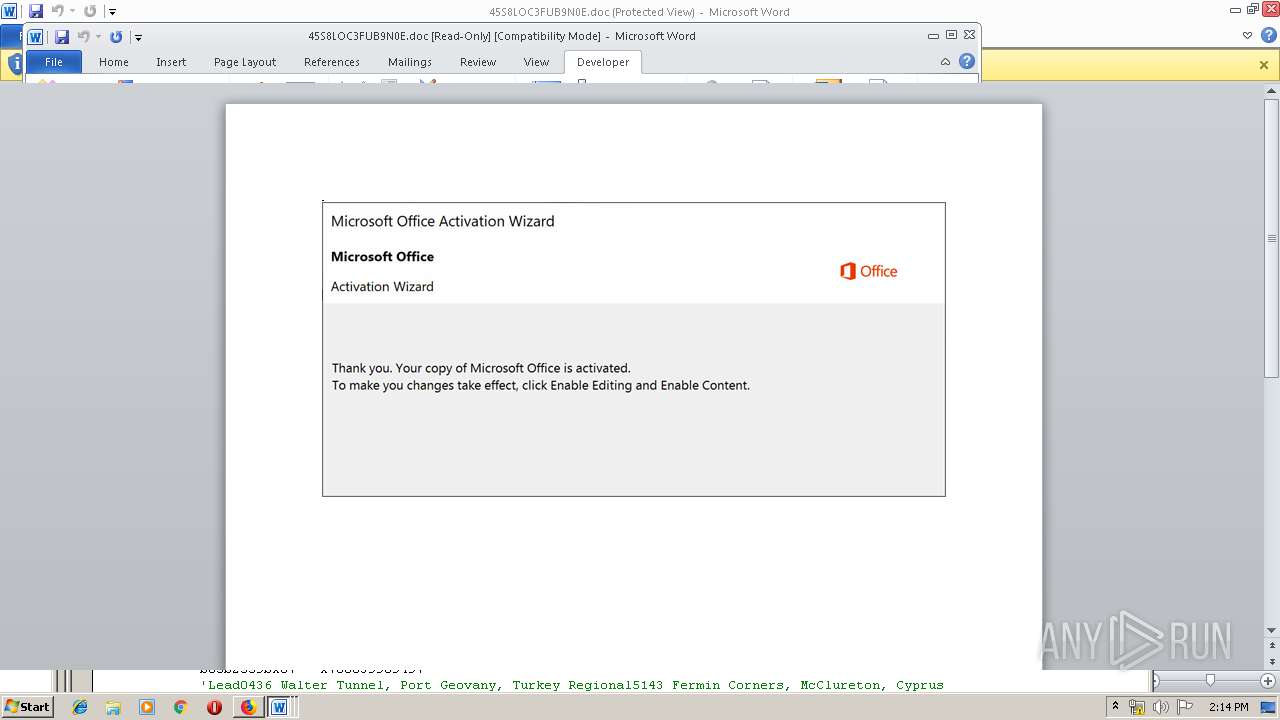
Starts Microsoft Office Application
- WINWORD.EXE (PID: 1704)
- firefox.exe (PID: 2236)
- WINWORD.EXE (PID: 2180)
Application launched itself
- WINWORD.EXE (PID: 1704)
- WINWORD.EXE (PID: 2180)
- 178.exe (PID: 2704)
Creates files in the user directory
- powershell.exe (PID: 3324)
- powershell.exe (PID: 2868)
Executed via WMI
- powershell.exe (PID: 3324)
- powershell.exe (PID: 2868)
PowerShell script executed
- powershell.exe (PID: 3324)
- powershell.exe (PID: 2868)
Executable content was dropped or overwritten
- powershell.exe (PID: 3324)
- 178.exe (PID: 1524)
Starts itself from another location
- 178.exe (PID: 1524)
INFO
Reads CPU info
- firefox.exe (PID: 2236)
Creates files in the user directory
- WINWORD.EXE (PID: 1704)
- firefox.exe (PID: 2236)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2700)
- WINWORD.EXE (PID: 1704)
- WINWORD.EXE (PID: 2420)
- WINWORD.EXE (PID: 2180)
Application launched itself
- firefox.exe (PID: 2236)
Reads settings of System Certificates
- powershell.exe (PID: 3324)
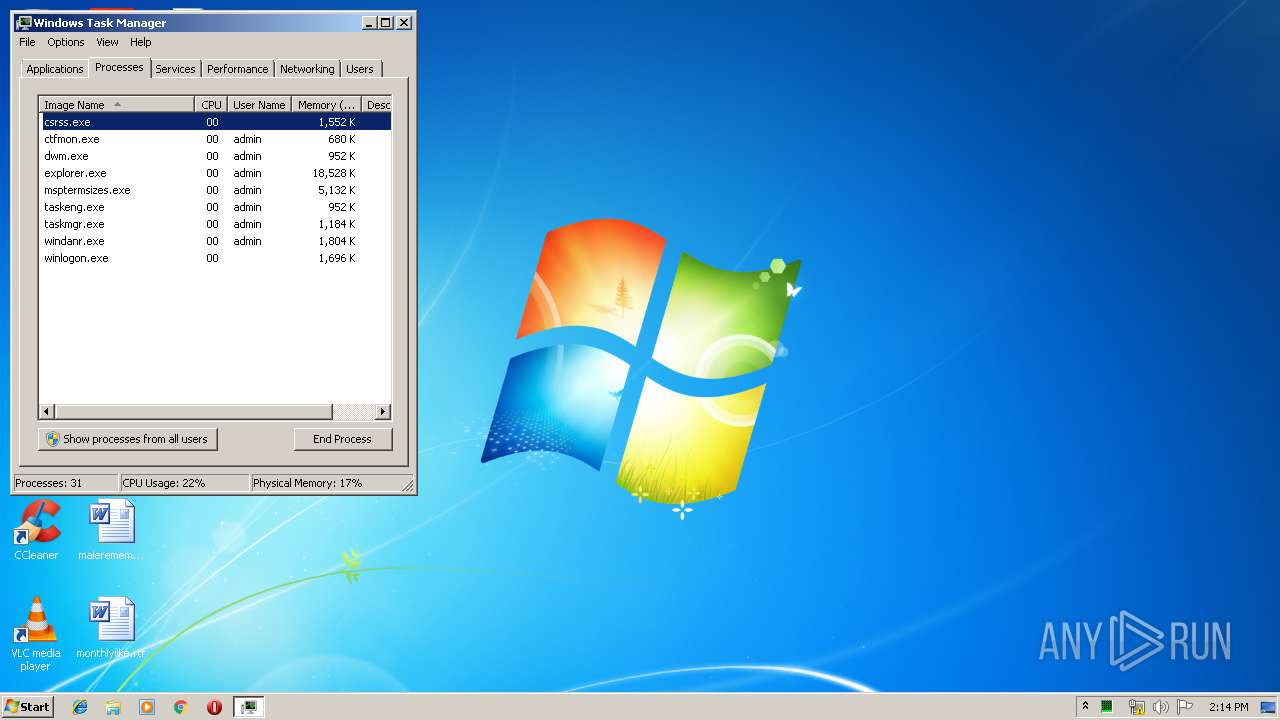
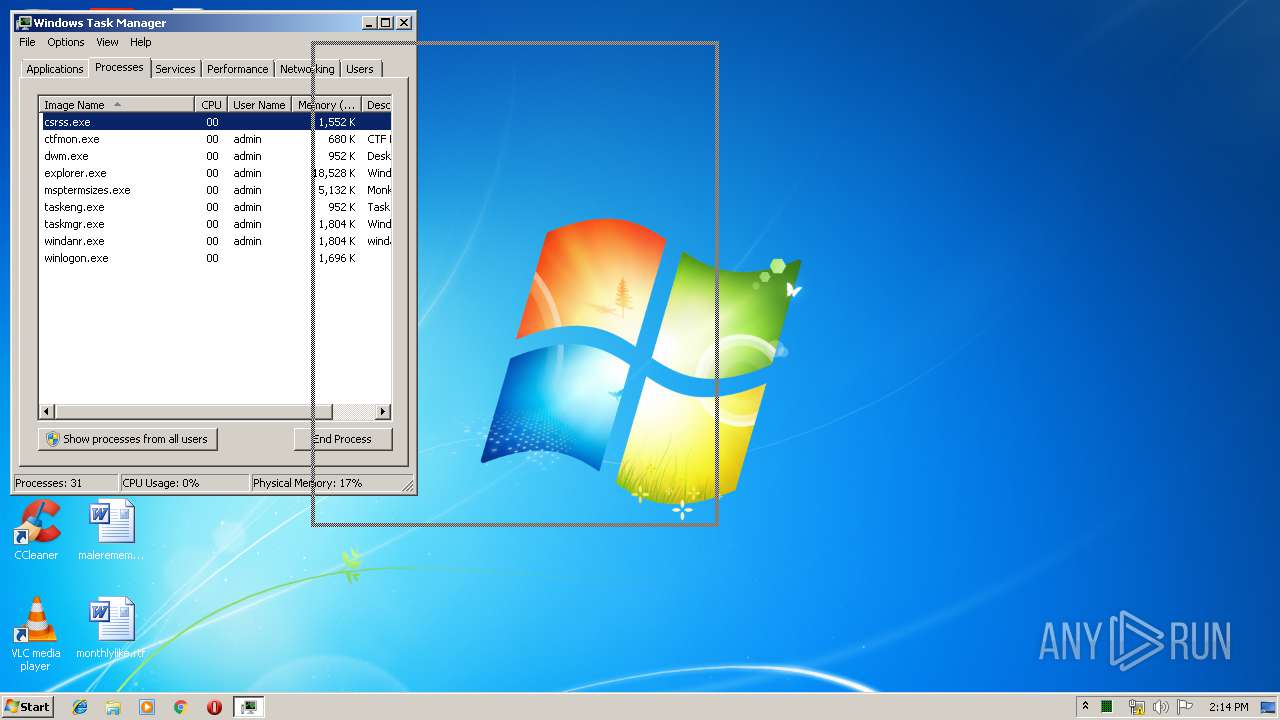
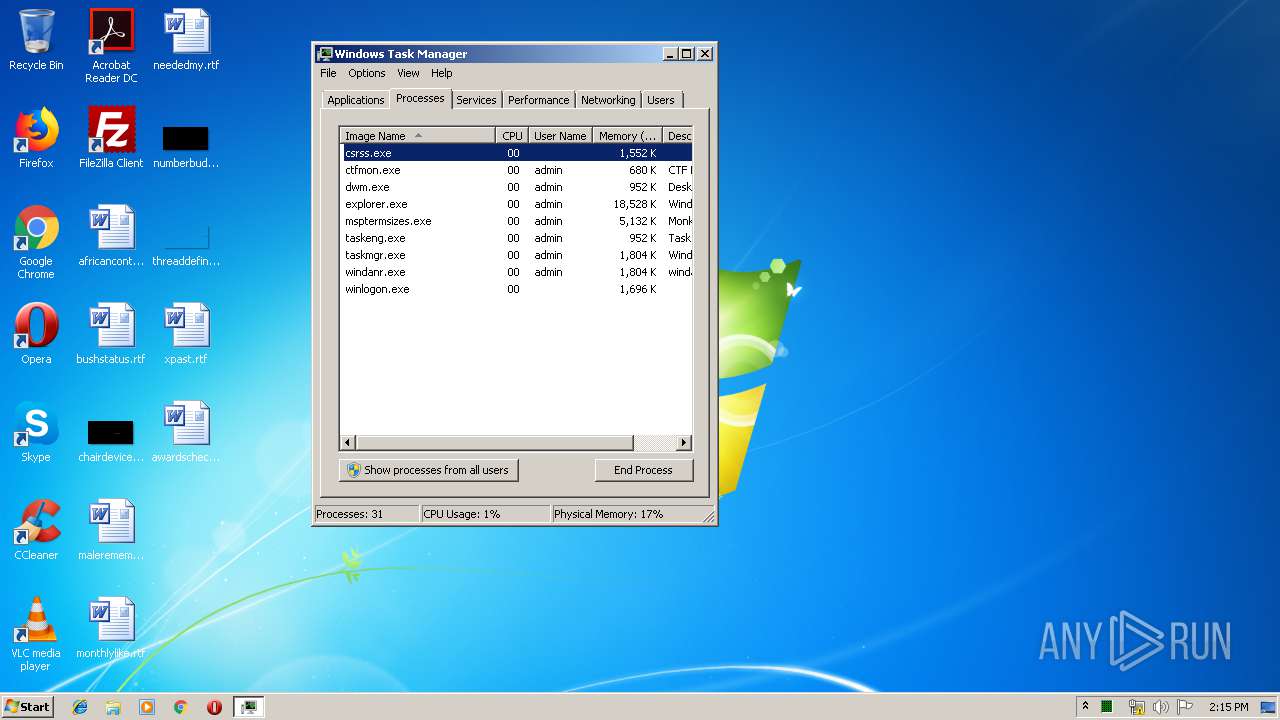
Manual execution by user
- taskmgr.exe (PID: 3644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
18
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 712 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/8341ce32-39bf-4a18-8f2b-9a822ed35b26/main/Firefox/68.0.1/release/20190717172542?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\8341ce32-39bf-4a18-8f2b-9a822ed35b26 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2236.13.1342477499\910973419" -childID 2 -isForBrowser -prefsHandle 2732 -prefMapHandle 2736 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2236 "\\.\pipe\gecko-crash-server-pipe.2236" 2752 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2236.3.1519844913\545445150" -childID 1 -isForBrowser -prefsHandle 784 -prefMapHandle 800 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2236 "\\.\pipe\gecko-crash-server-pipe.2236" 1676 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1500 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1524 | --3a2e7ef0 | C:\Users\admin\178.exe | 178.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
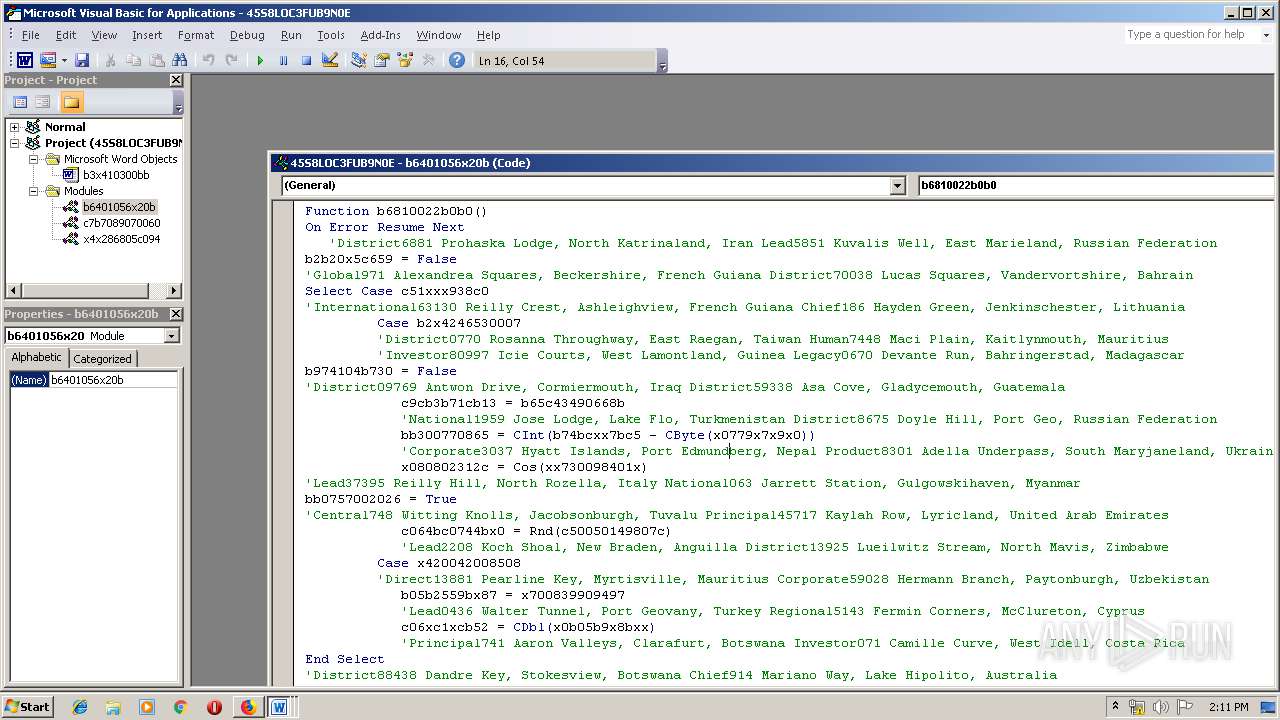
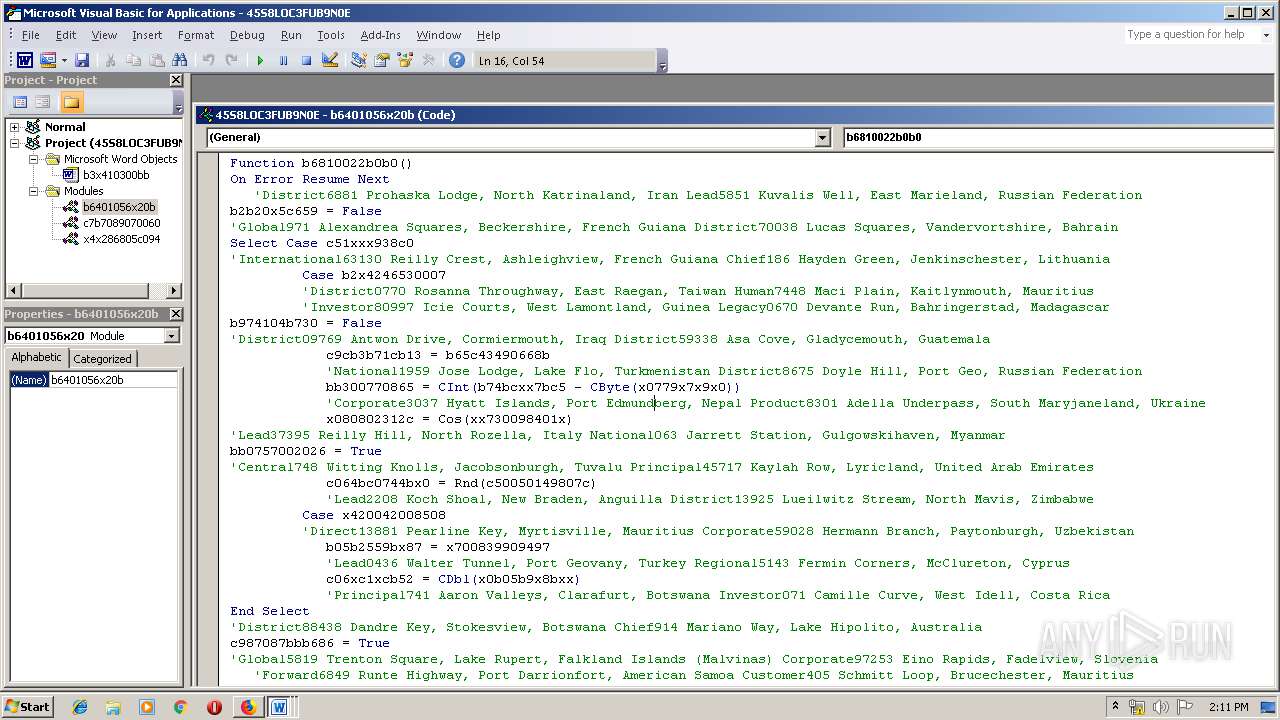
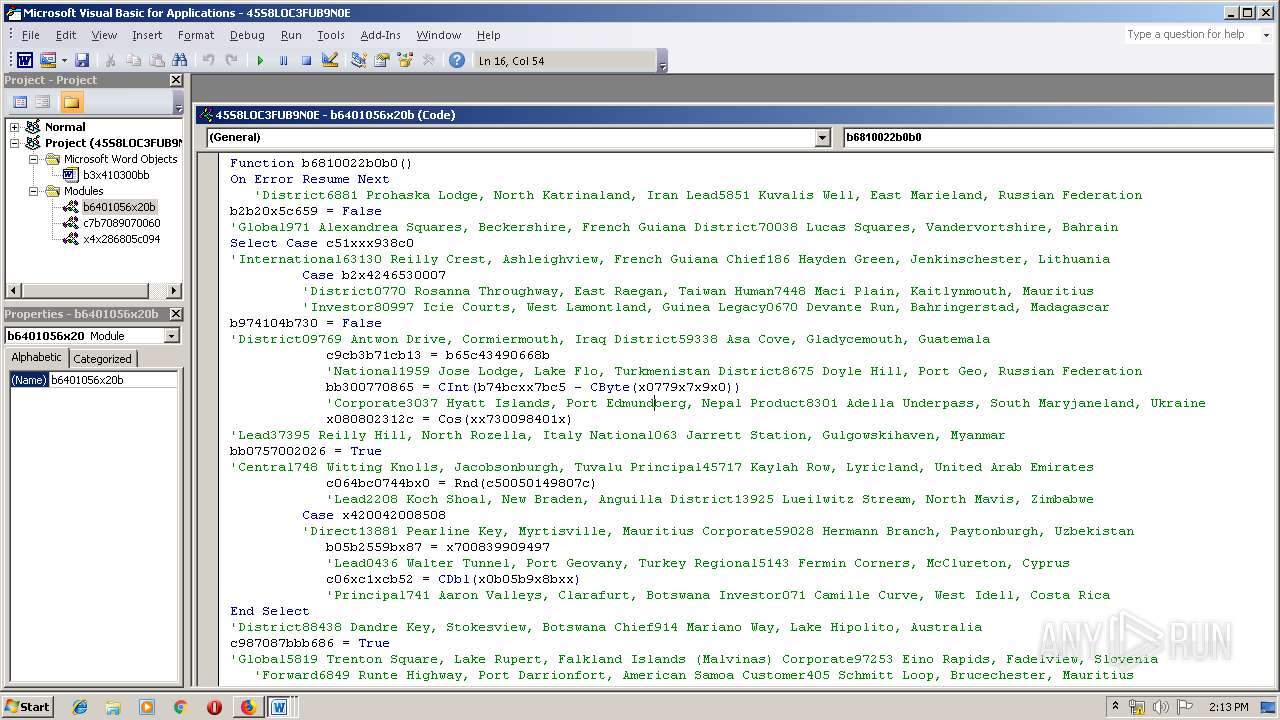
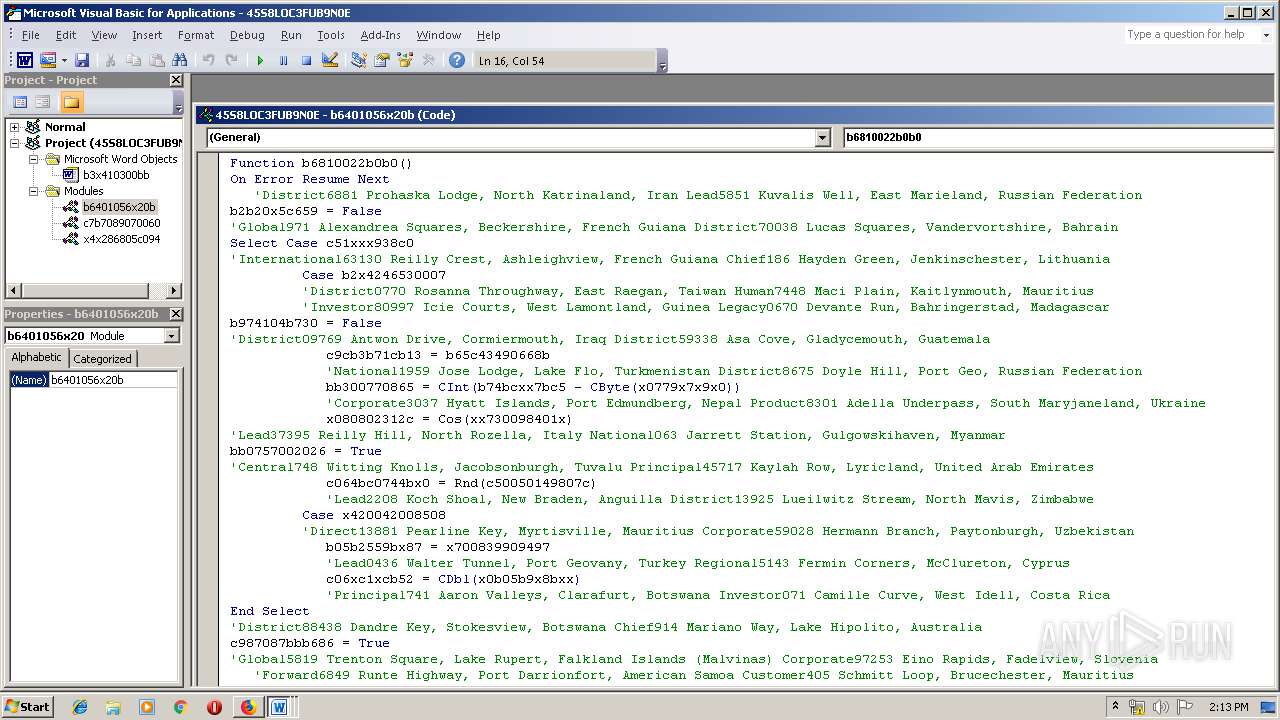
| 1704 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\45S8LOC3FUB9N0E.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | firefox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\45S8LOC3FUB9N0E.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | firefox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://www.dipeshengg.com/customers/paclm/cxDXknmMpgJCGLrsXOHGoicZqWSiwT/ | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
5 407
Read events
4 431
Write events
935
Delete events
41
Modification events
| (PID) Process: | (2236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 7B68ECC300000000 | |||
| (PID) Process: | (3240) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: F01AE9C300000000 | |||
| (PID) Process: | (2236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (2236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000093000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2236) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.doc\OpenWithProgids |
| Operation: | write | Name: | Word.Document.8 |
Value: | |||
| (PID) Process: | (2236) firefox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330184243 | |||
| (PID) Process: | (2236) firefox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330184244 | |||
Executable files
2
Suspicious files
83
Text files
43
Unknown types
83
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2236 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flashsubdoc-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 2236 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flashsubdoc-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 2236 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flash-digest256.pset | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
33
DNS requests
84
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1500 | msptermsizes.exe | POST | 200 | 23.239.29.211:443 | http://23.239.29.211:443/site/walk/ | US | binary | 148 b | malicious |
1500 | msptermsizes.exe | POST | 200 | 23.253.207.142:8080 | http://23.253.207.142:8080/free/ | US | binary | 132 b | malicious |
1500 | msptermsizes.exe | GET | 200 | 23.253.207.142:8080 | http://23.253.207.142:8080/news.php | US | text | 11 b | malicious |
2236 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1500 | msptermsizes.exe | POST | 200 | 23.239.29.211:443 | http://23.239.29.211:443/arizona/teapot/ringin/merge/ | US | binary | 789 Kb | malicious |
2236 | firefox.exe | POST | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
2236 | firefox.exe | POST | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2236 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2236 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2236 | firefox.exe | GET | 200 | 166.62.28.86:80 | http://www.dipeshengg.com/customers/paclm/cxDXknmMpgJCGLrsXOHGoicZqWSiwT/ | US | document | 146 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2236 | firefox.exe | 52.36.193.139:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2236 | firefox.exe | 2.16.186.112:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
2236 | firefox.exe | 52.32.239.48:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2236 | firefox.exe | 52.89.51.22:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2236 | firefox.exe | 172.217.23.110:443 | www.youtube.com | Google Inc. | US | whitelisted |
2236 | firefox.exe | 172.217.22.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2236 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2236 | firefox.exe | 143.204.214.45:443 | firefox.settings.services.mozilla.com | — | US | unknown |
2236 | firefox.exe | 52.222.157.203:443 | content-signature-2.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
2236 | firefox.exe | 166.62.28.86:80 | www.dipeshengg.com | GoDaddy.com, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
www.dipeshengg.com |
| malicious |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1500 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
1500 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1500 | msptermsizes.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
1500 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1500 | msptermsizes.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
1500 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
5 ETPRO signatures available at the full report