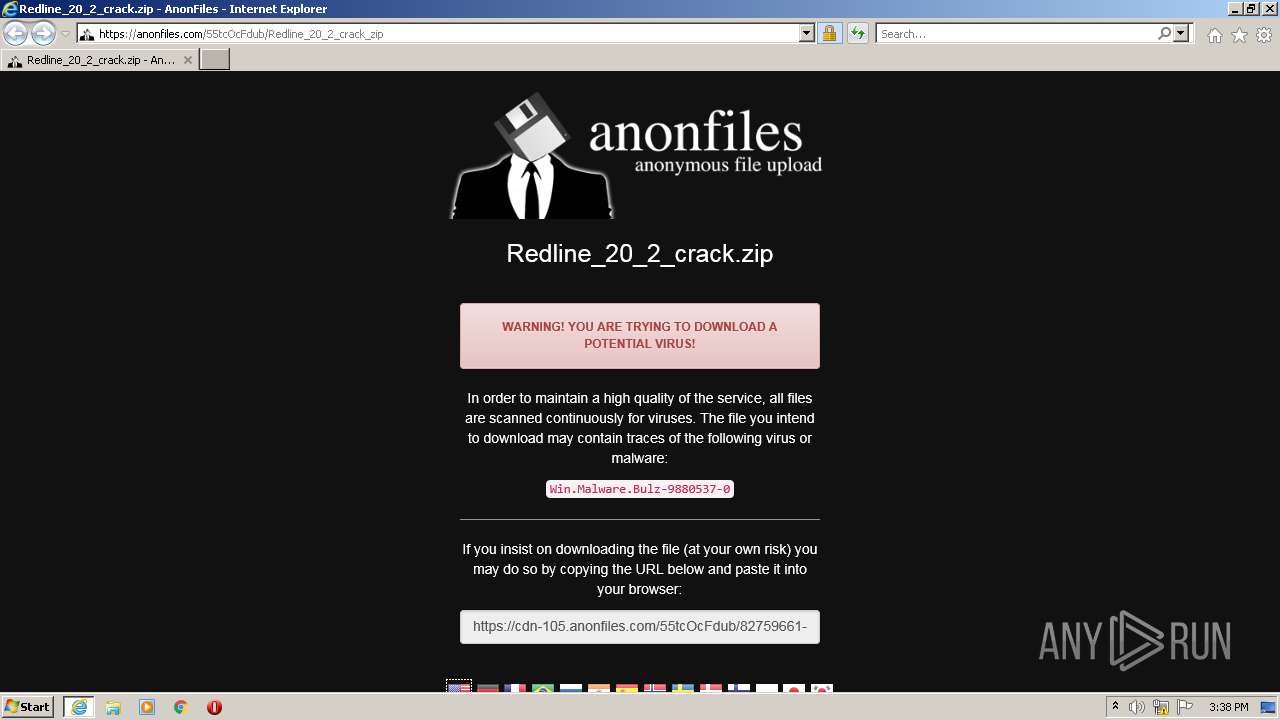
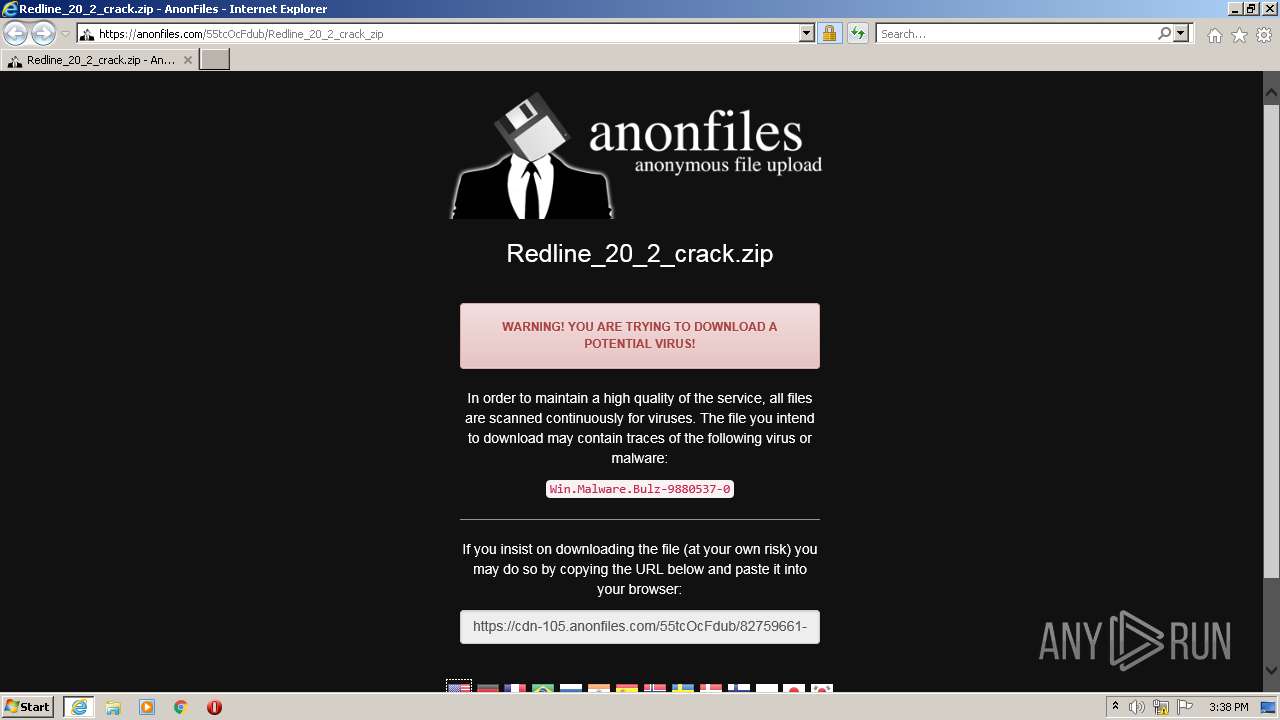
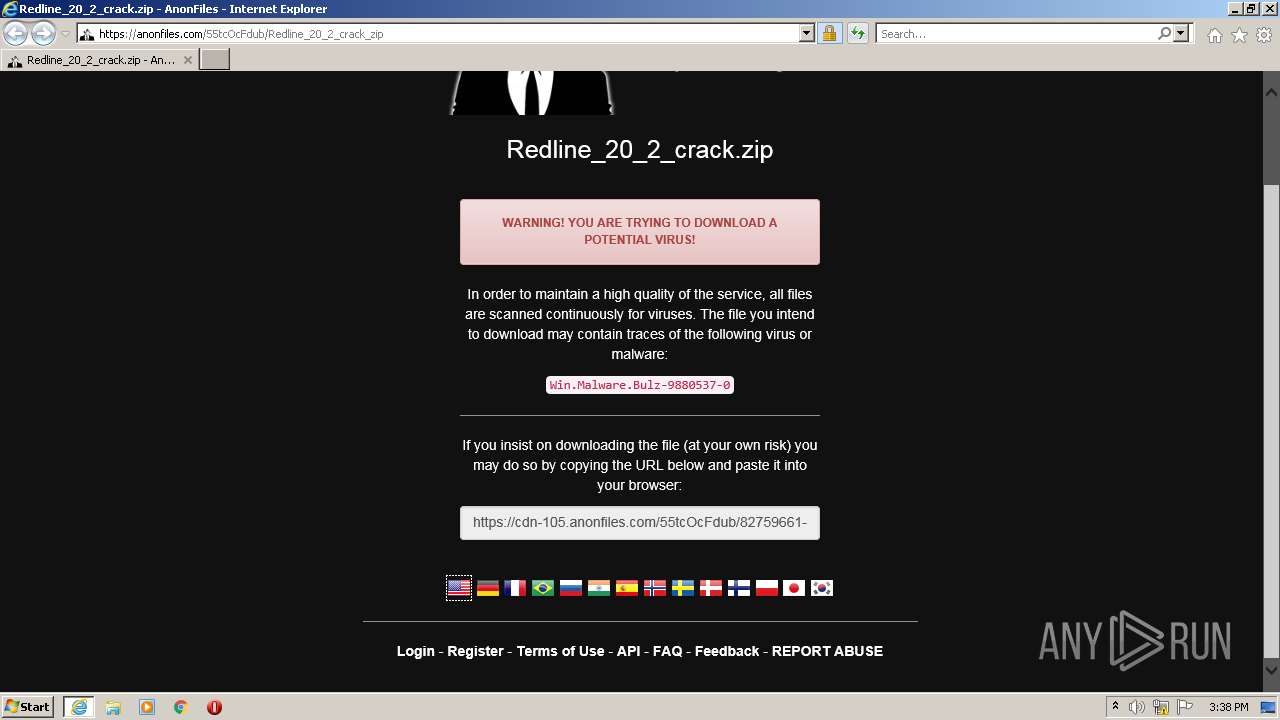
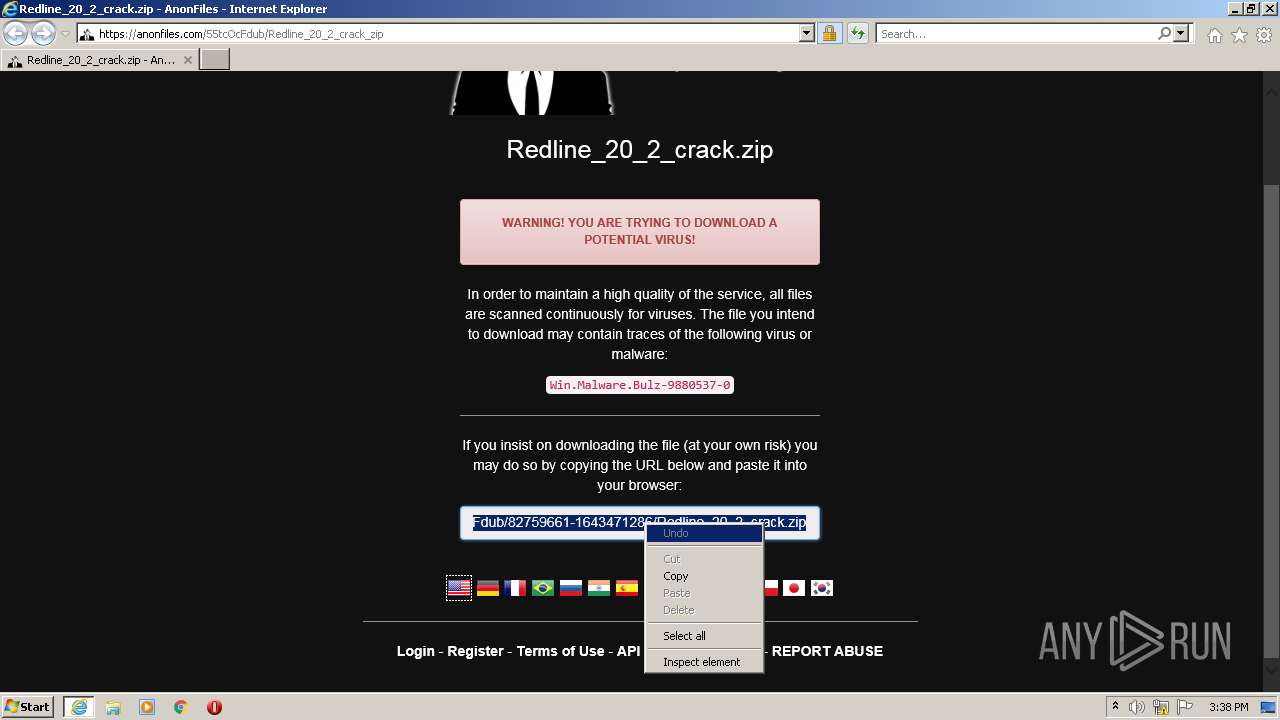
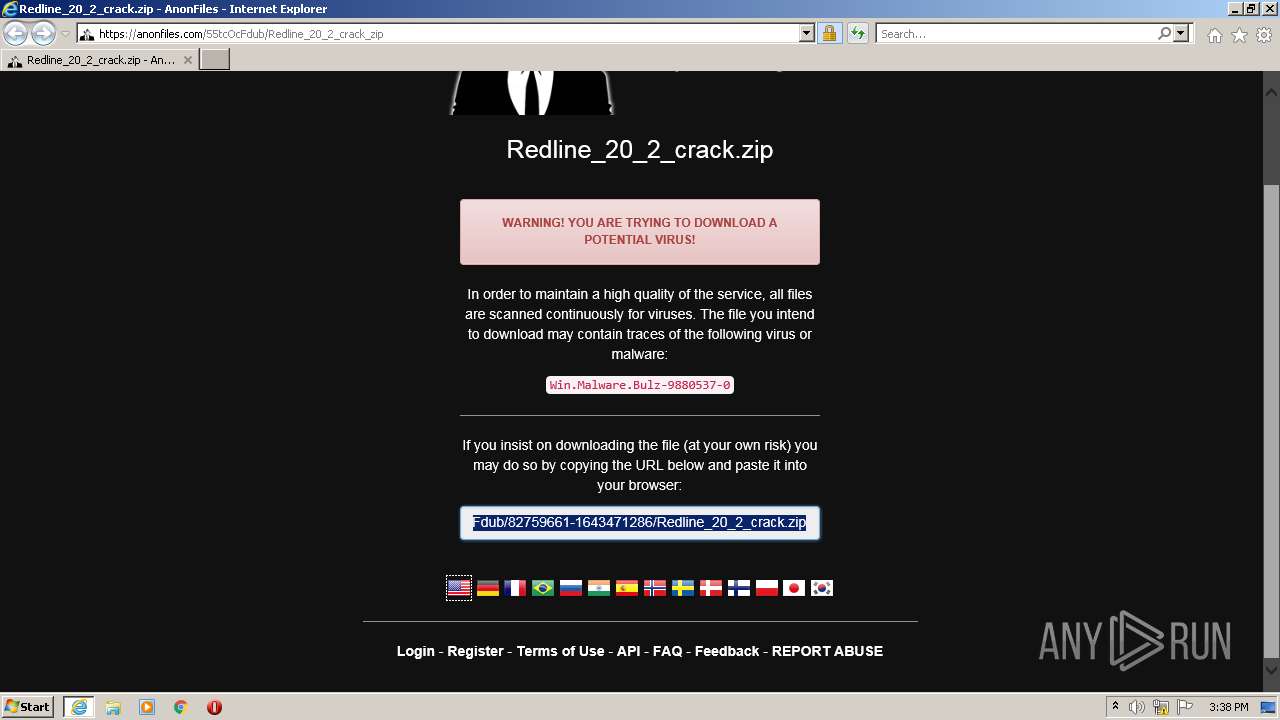
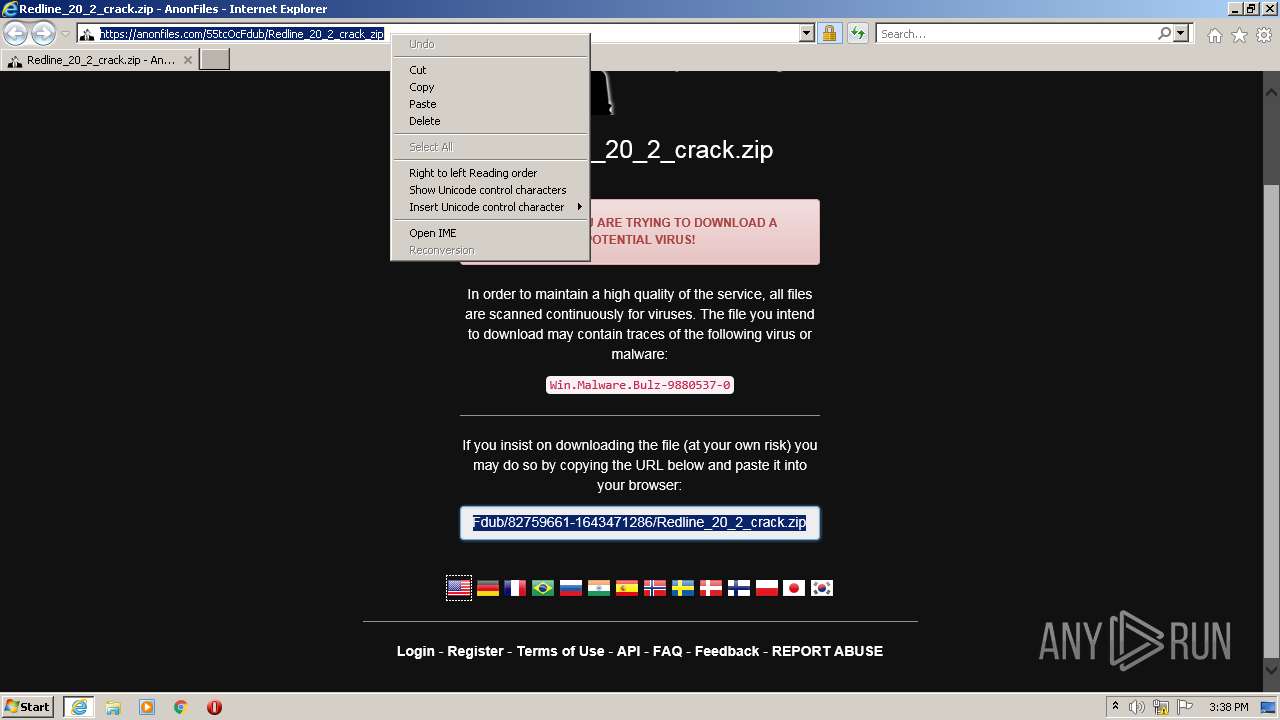
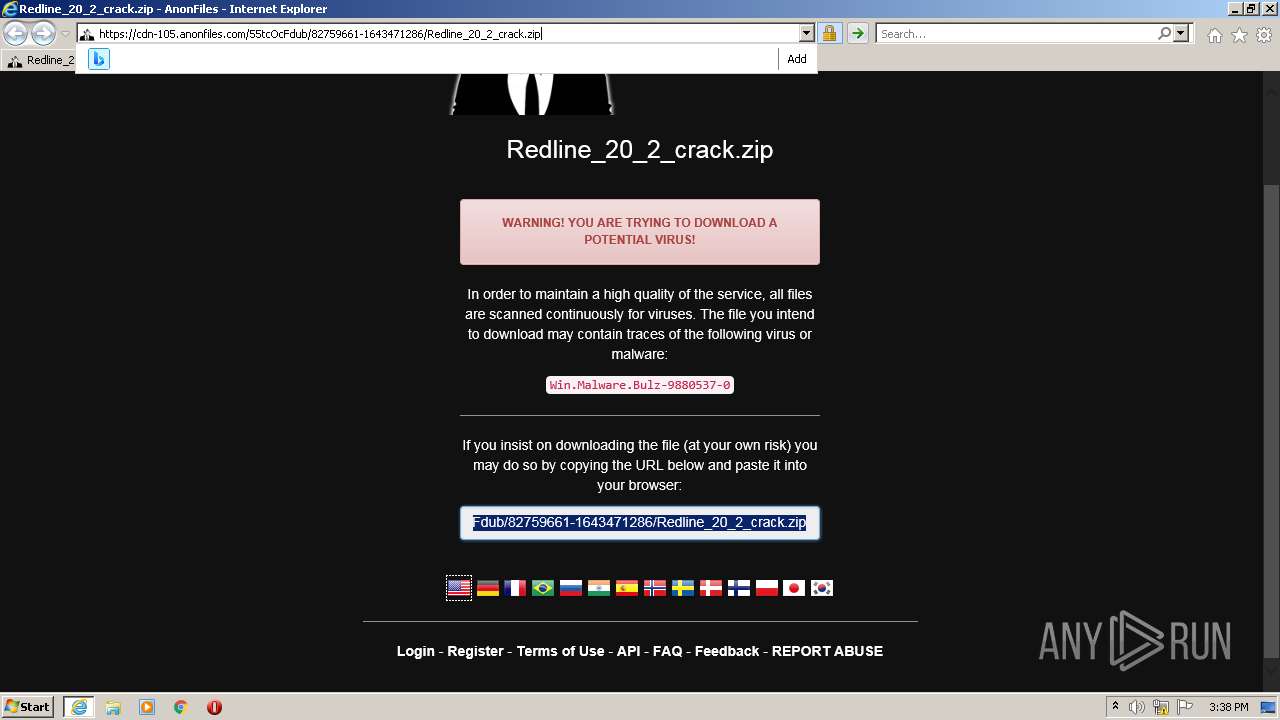
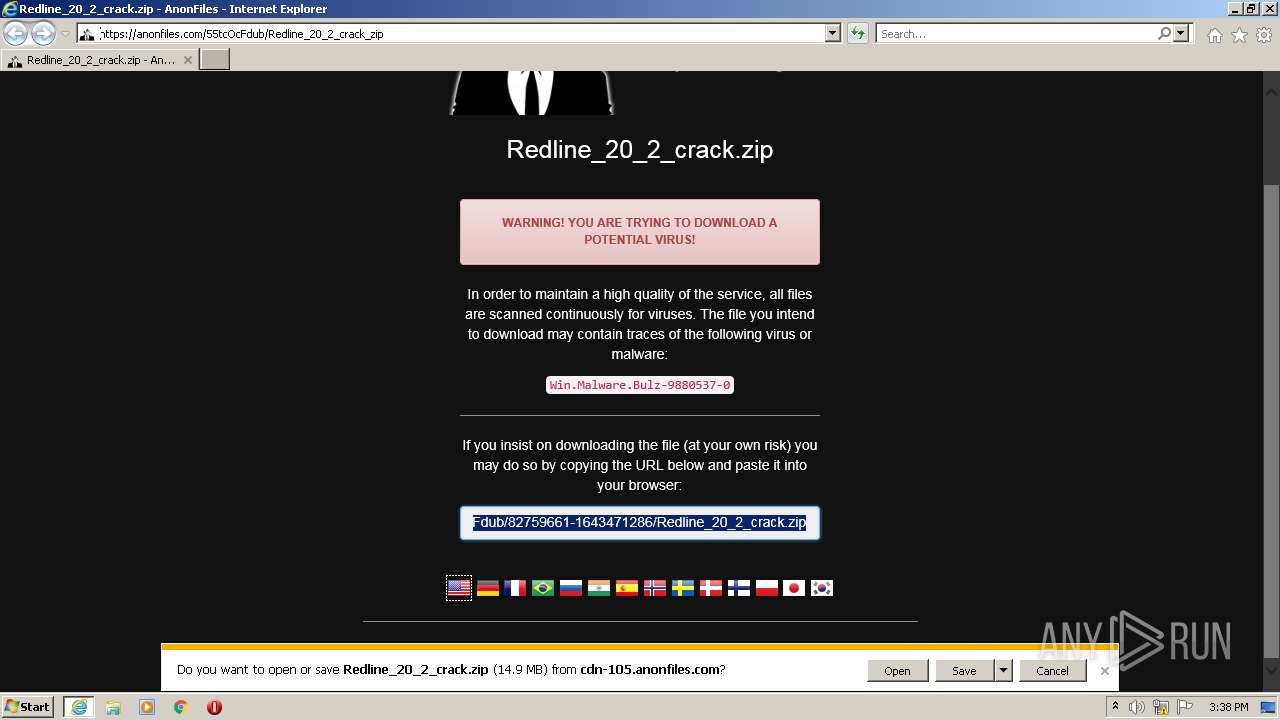
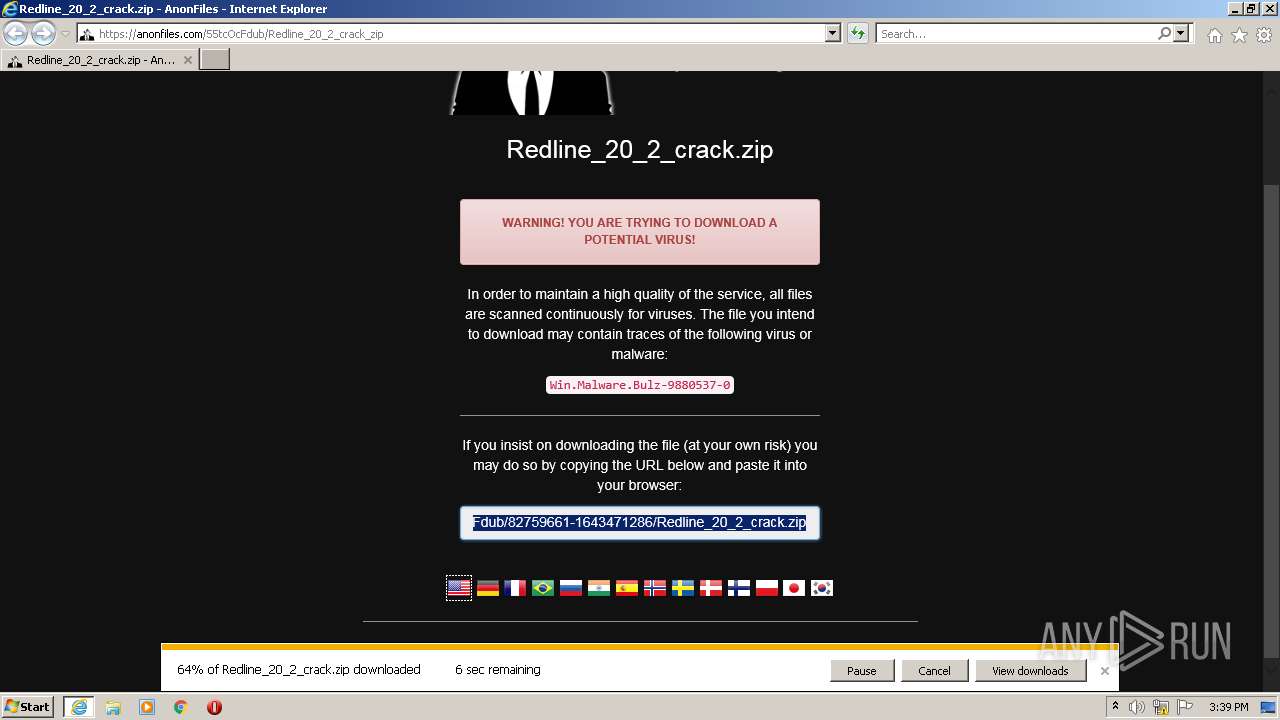
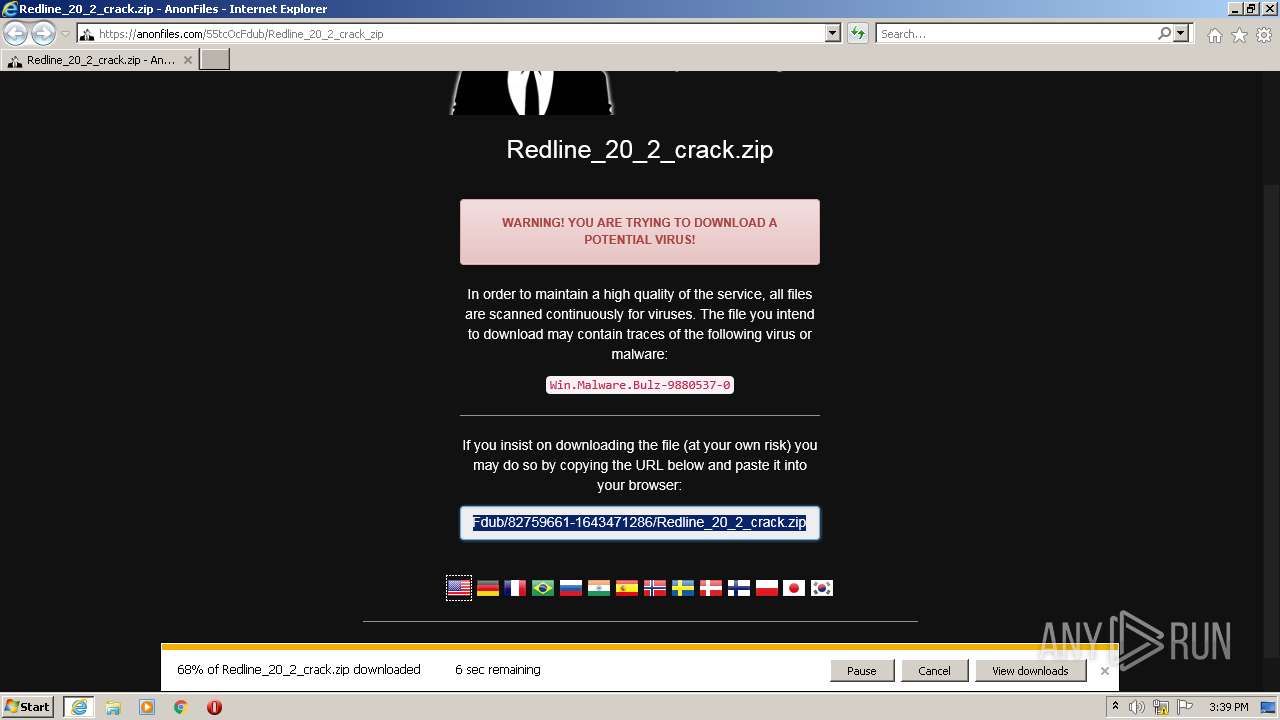
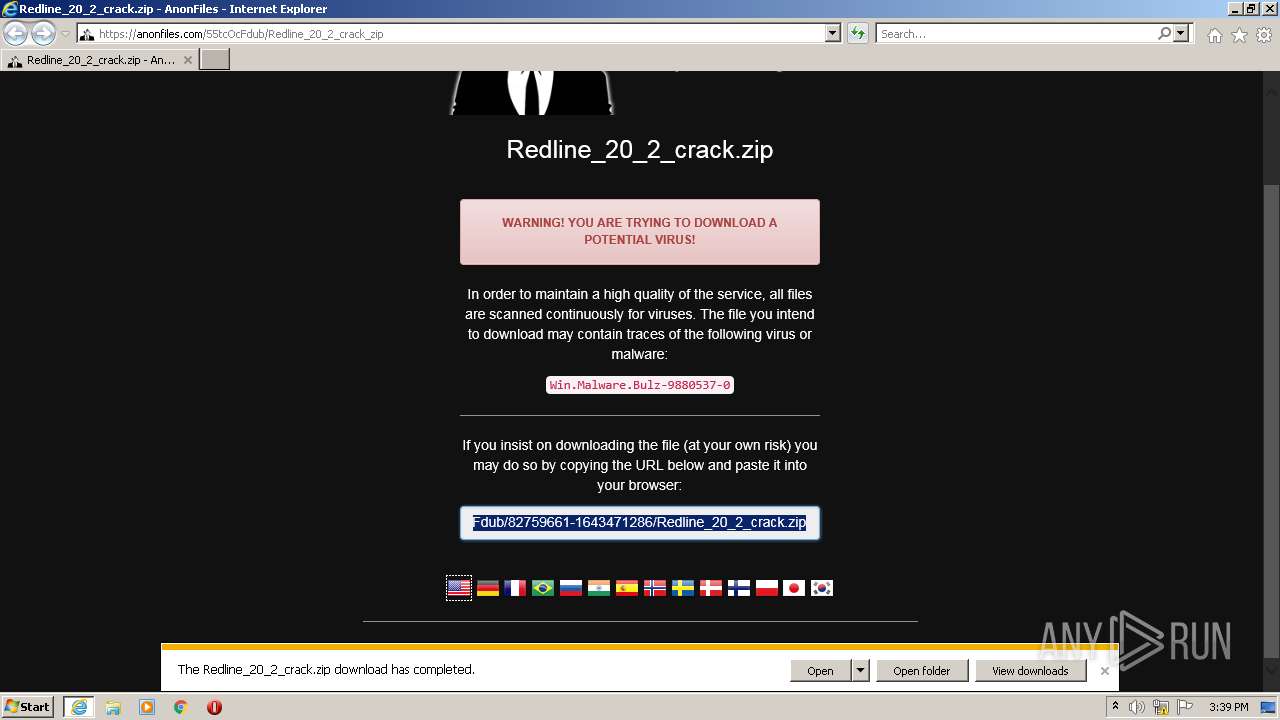
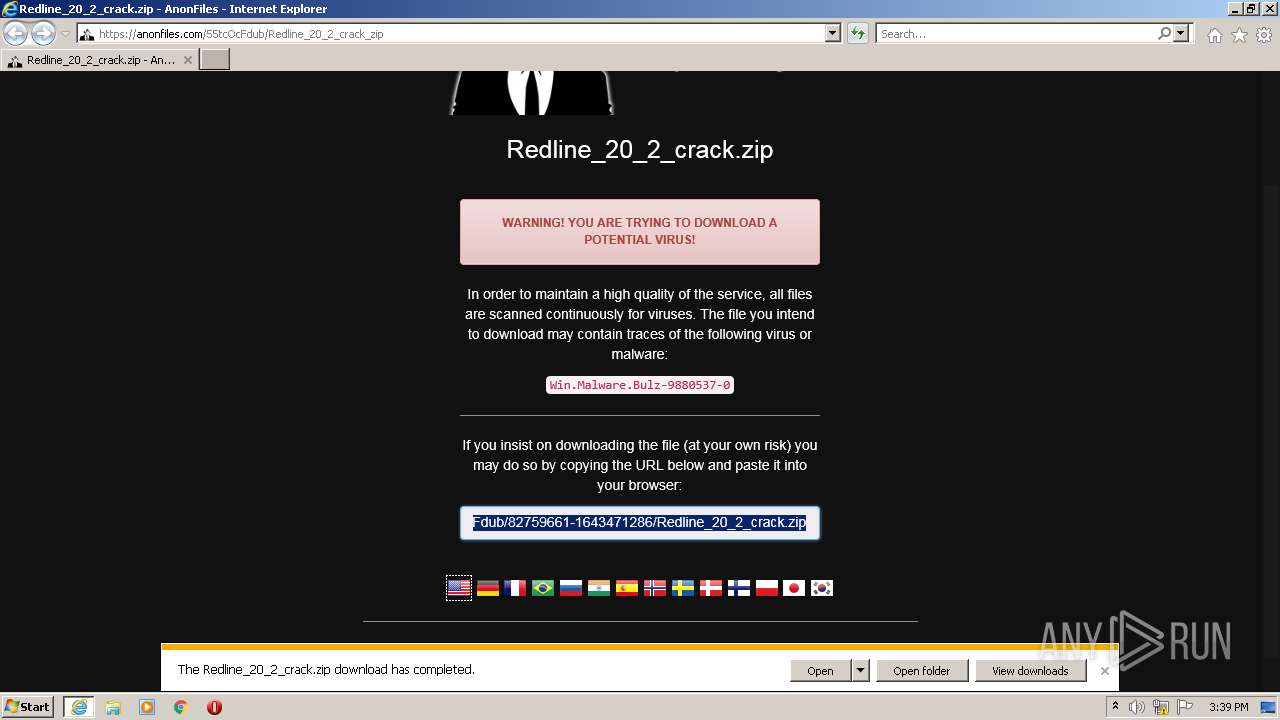
| URL: | https://anonfiles.com/55tcOcFdub/Redline_20_2_crack_zip |
| Full analysis: | https://app.any.run/tasks/256a0cf5-5213-4b7a-9718-7facdf5269a7 |
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2022, 15:38:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 34D420DA59E283F9C0F5F2CFA16891BA |
| SHA1: | 020A835EB40F99BDF8DBB6093C227A5B9CE47759 |
| SHA256: | 958CF6C58687970A2DE5F3D3E904D1FB198B2298E1C9E33B6718EF5BFFD717B9 |
| SSDEEP: | 3:N8M2keyHZMLfA9NMV:2M25ySLfoeV |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3204)
Application was dropped or rewritten from another process
- Kurome.Loader.exe (PID: 2428)
- Kurome.Host.exe (PID: 1276)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2968)
- Kurome.Loader.exe (PID: 2428)
- Kurome.Host.exe (PID: 1276)
Reads the computer name
- WinRAR.exe (PID: 2968)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2968)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3436)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2968)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2968)
INFO
Checks supported languages
- iexplore.exe (PID: 3928)
- iexplore.exe (PID: 3436)
Reads the computer name
- iexplore.exe (PID: 3928)
- iexplore.exe (PID: 3436)
Changes internet zones settings
- iexplore.exe (PID: 3928)
Reads settings of System Certificates
- iexplore.exe (PID: 3928)
- iexplore.exe (PID: 3436)
Application launched itself
- iexplore.exe (PID: 3928)
Checks Windows Trust Settings
- iexplore.exe (PID: 3928)
- iexplore.exe (PID: 3436)
Changes settings of System certificates
- iexplore.exe (PID: 3928)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3928)
Creates files in the user directory
- iexplore.exe (PID: 3928)
Reads internet explorer settings
- iexplore.exe (PID: 3436)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3928)
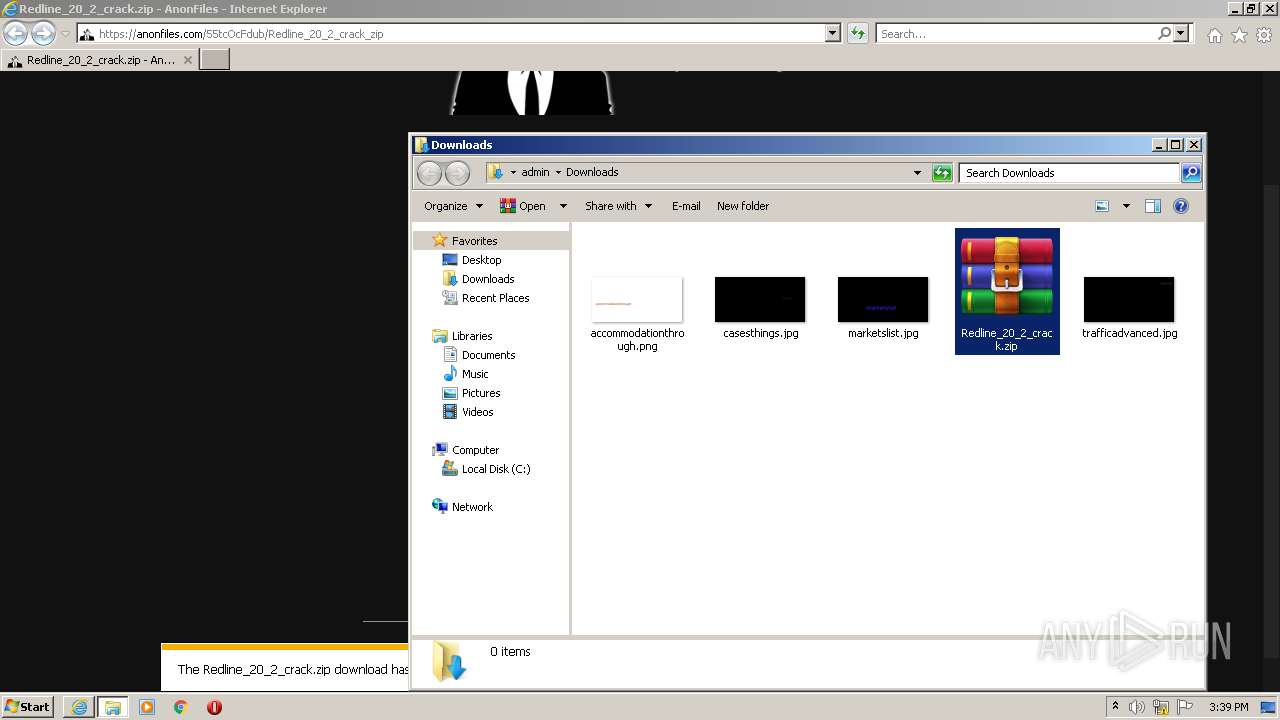
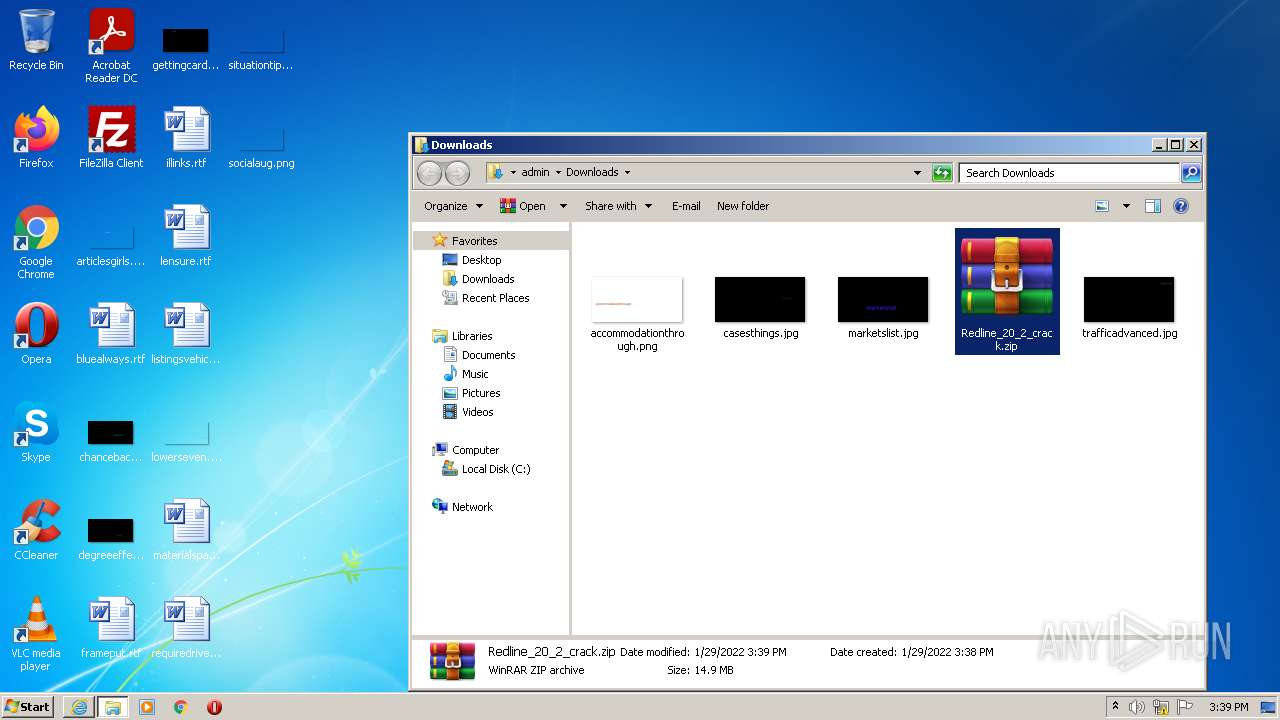
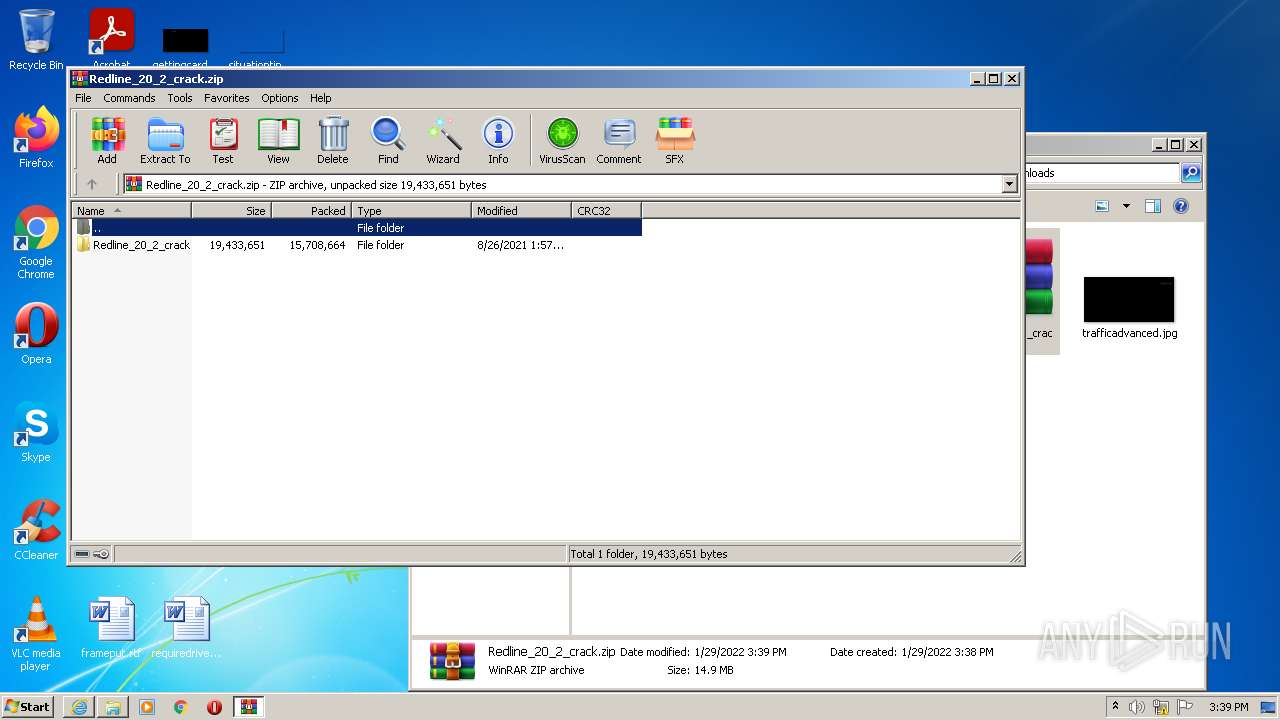
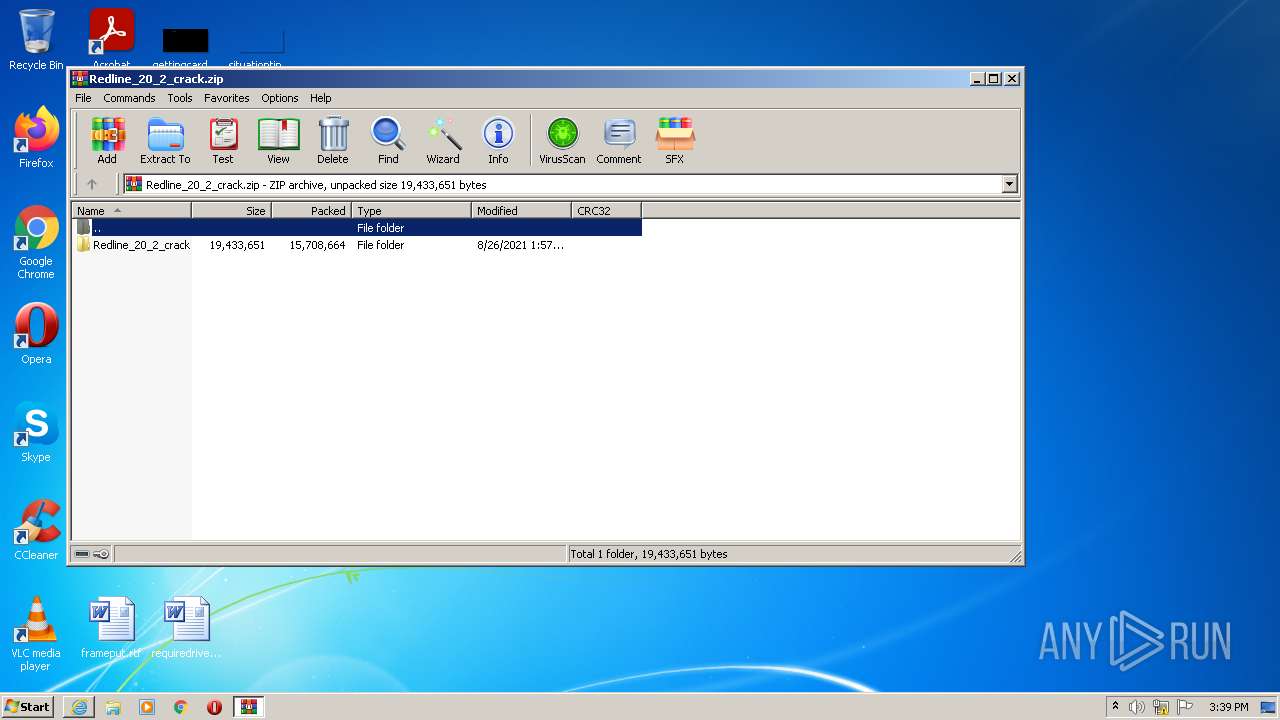
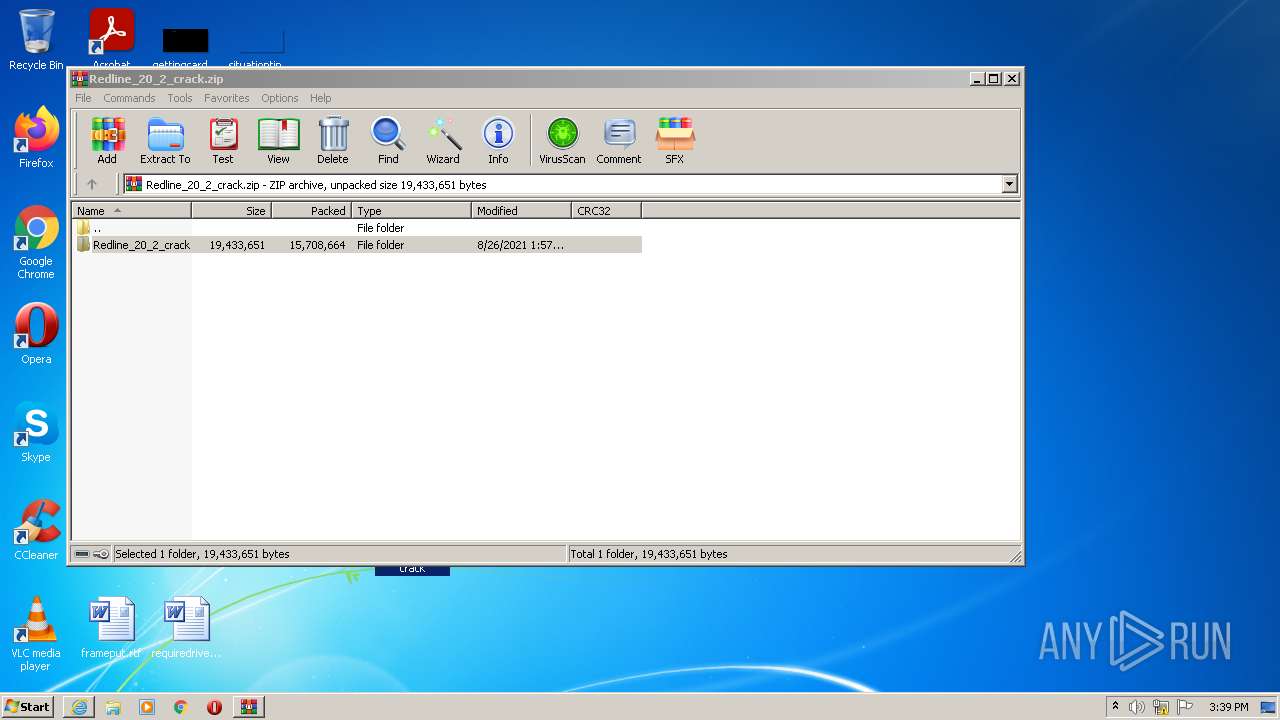
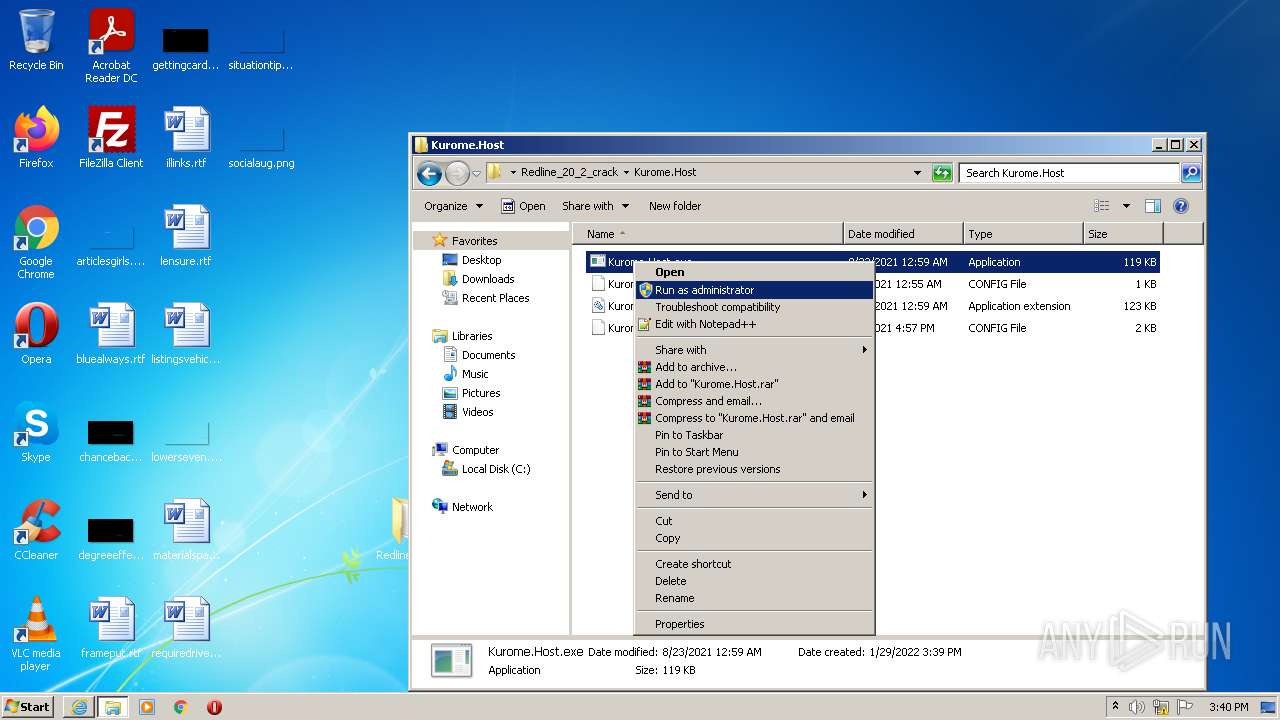
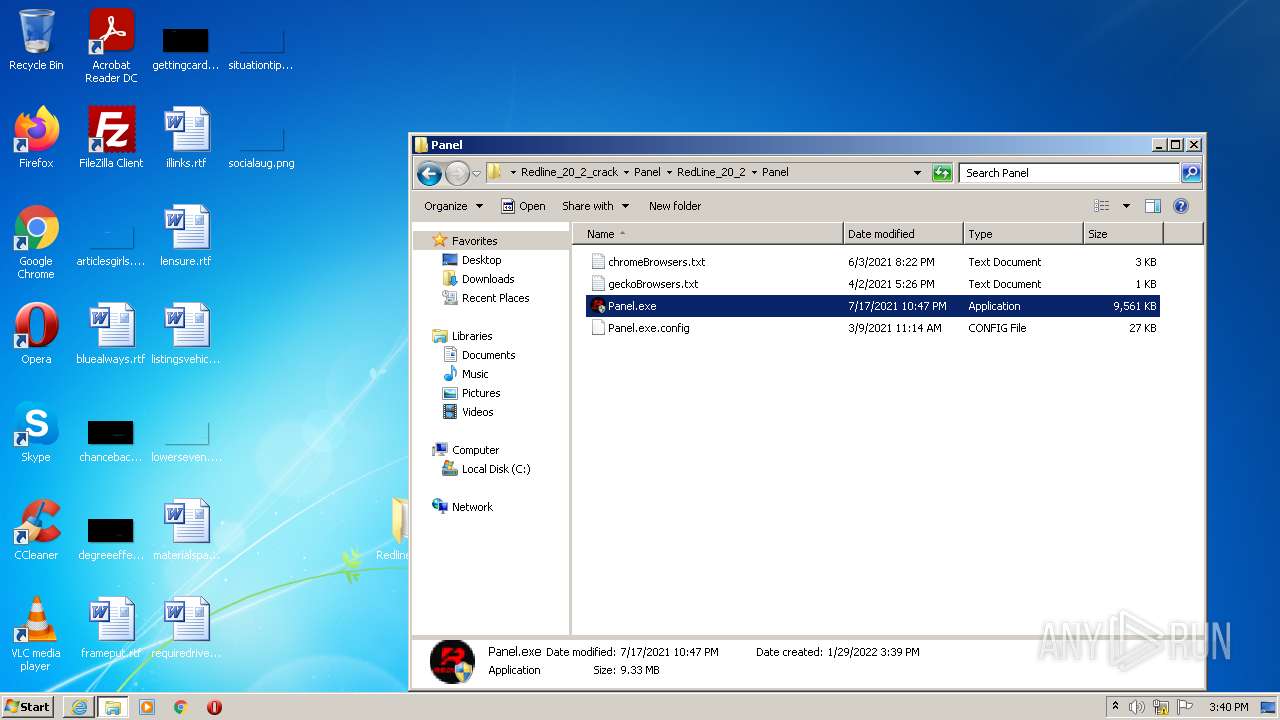
Manual execution by user
- WinRAR.exe (PID: 2968)
- Kurome.Host.exe (PID: 1276)
- Kurome.Loader.exe (PID: 2428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
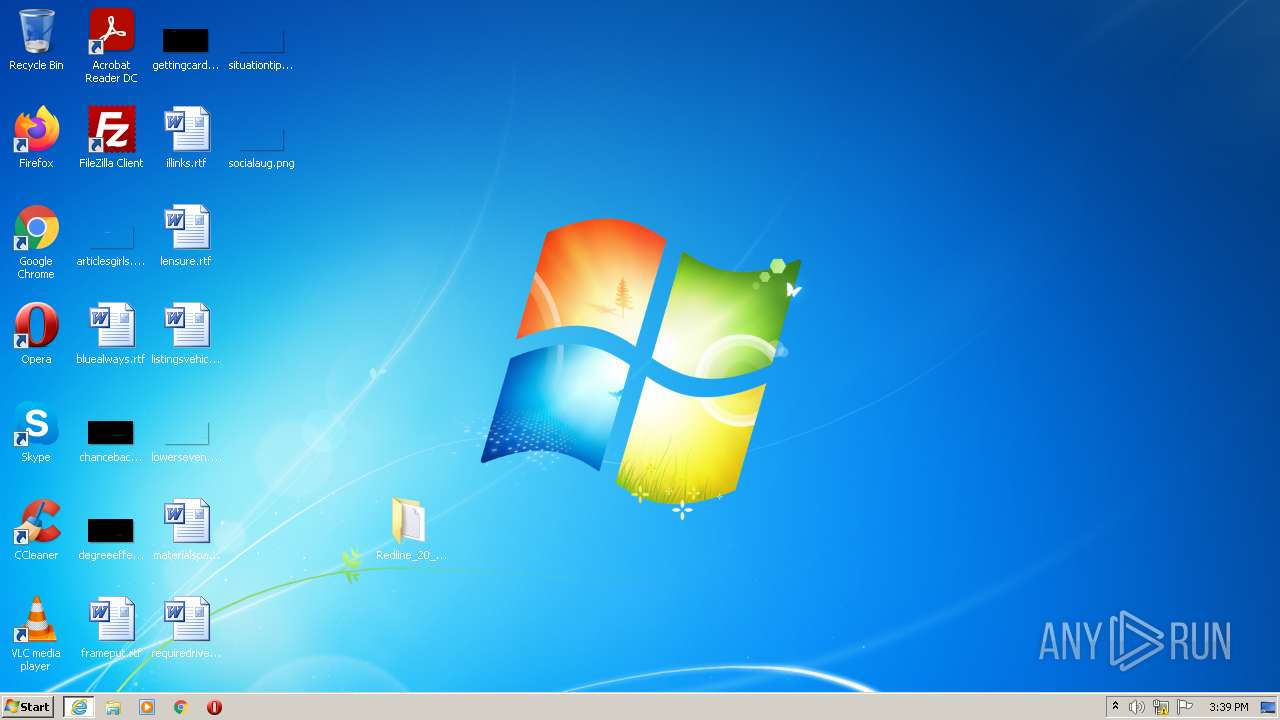
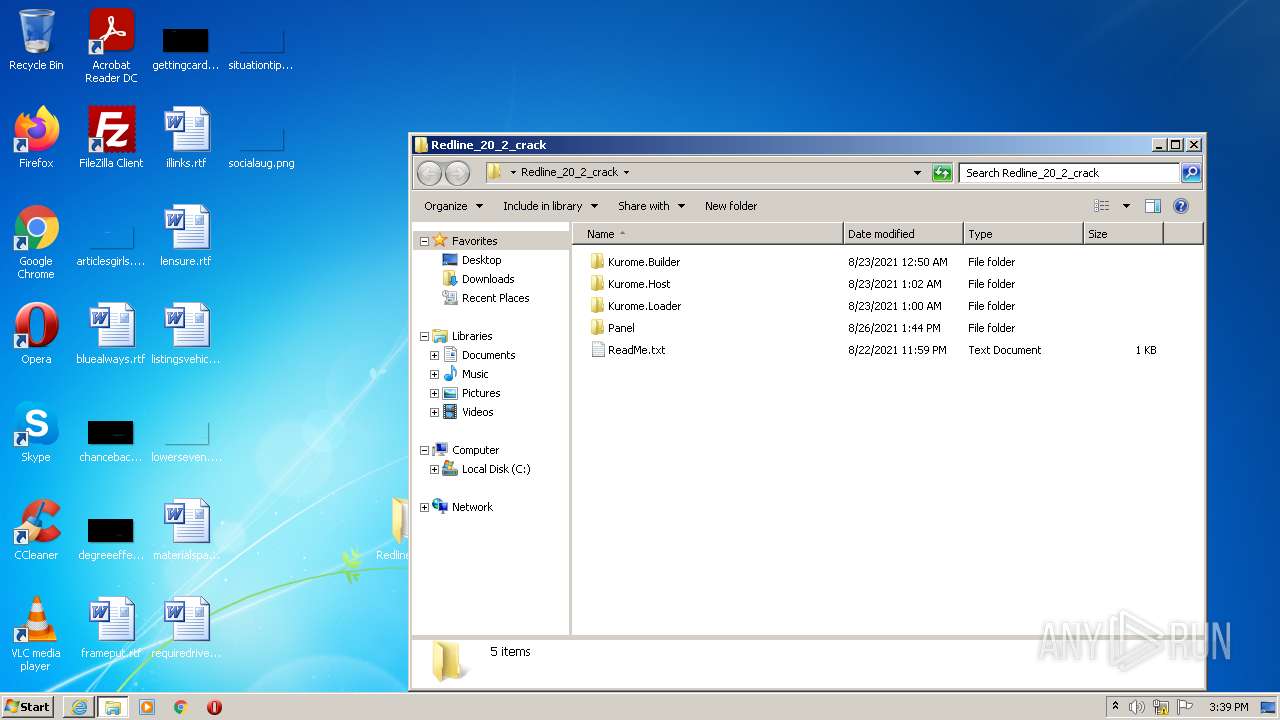
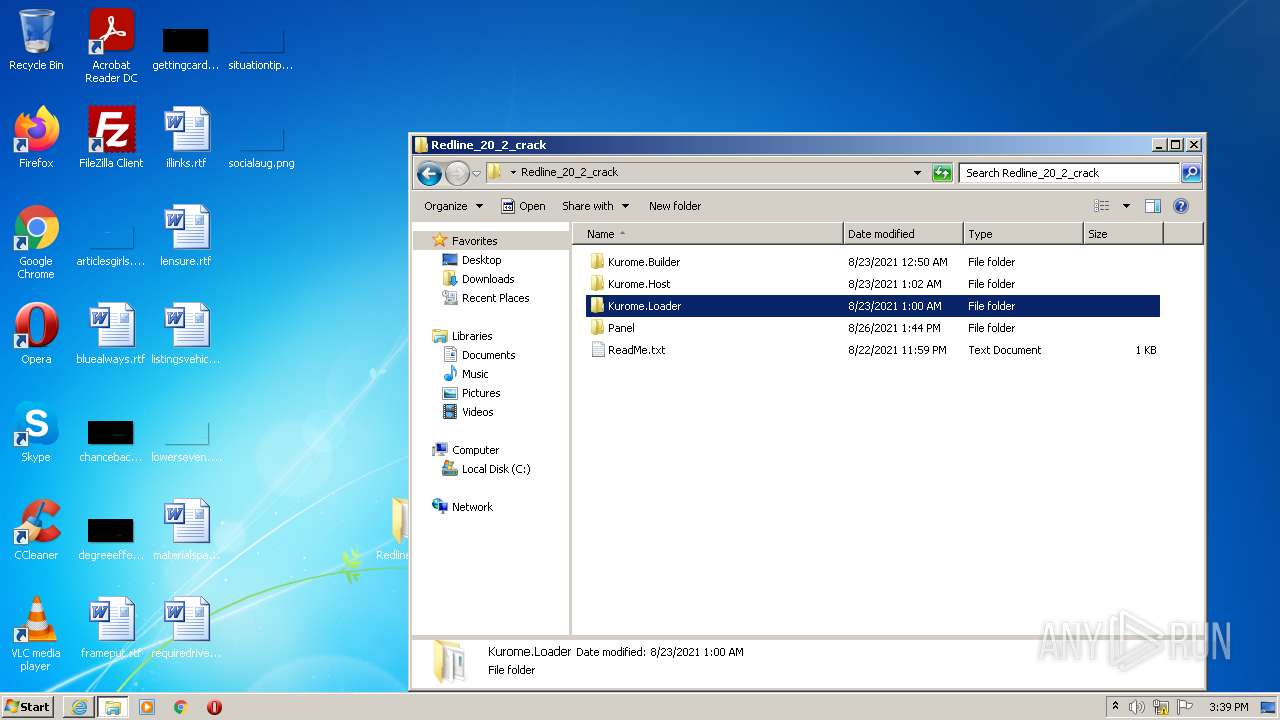
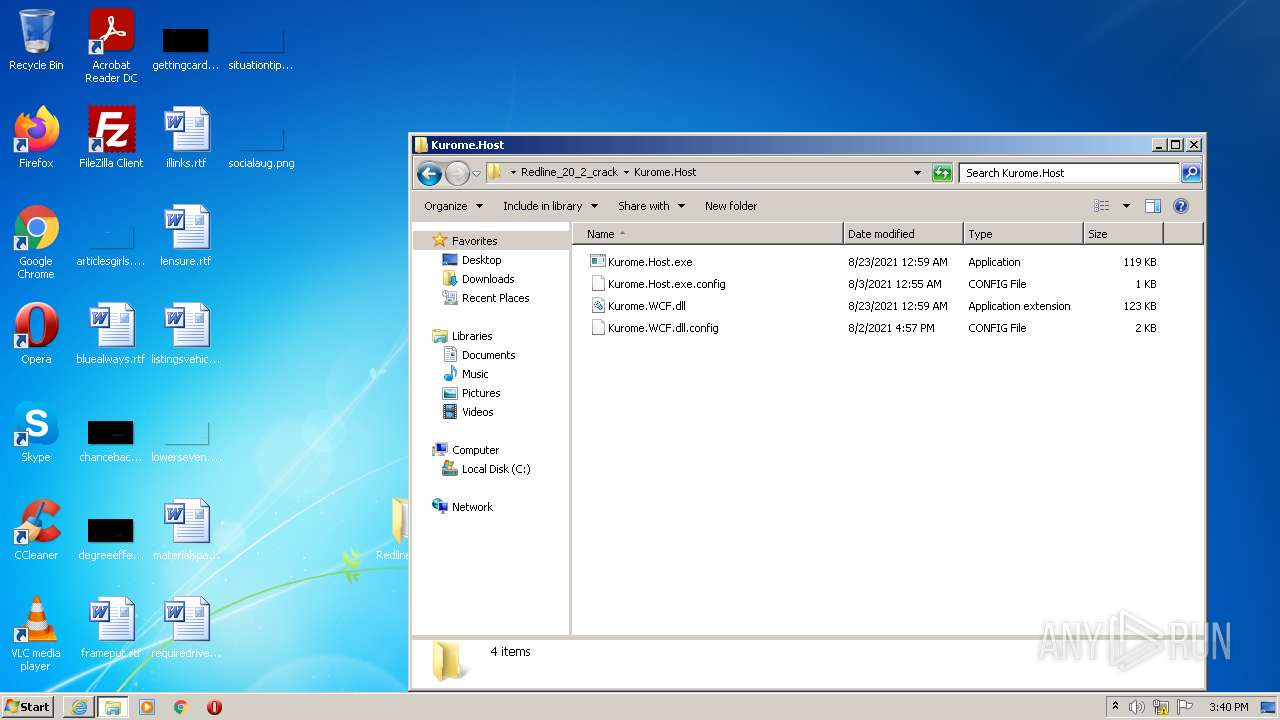
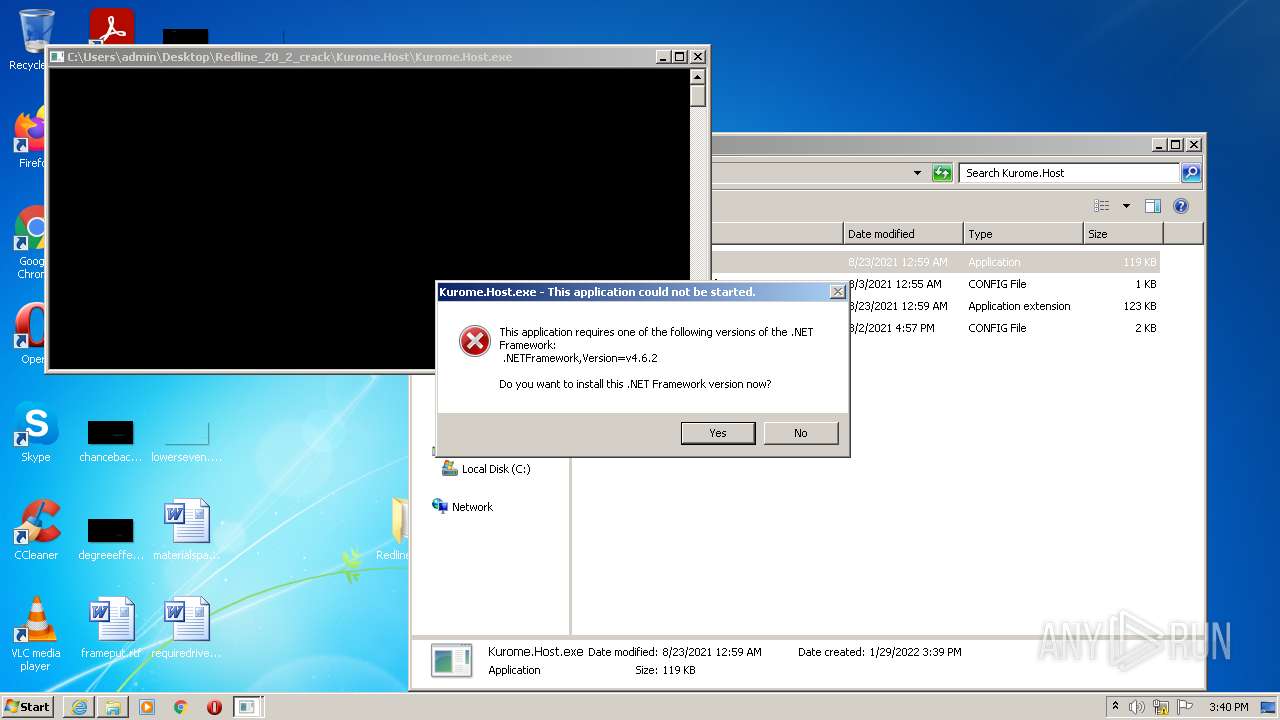
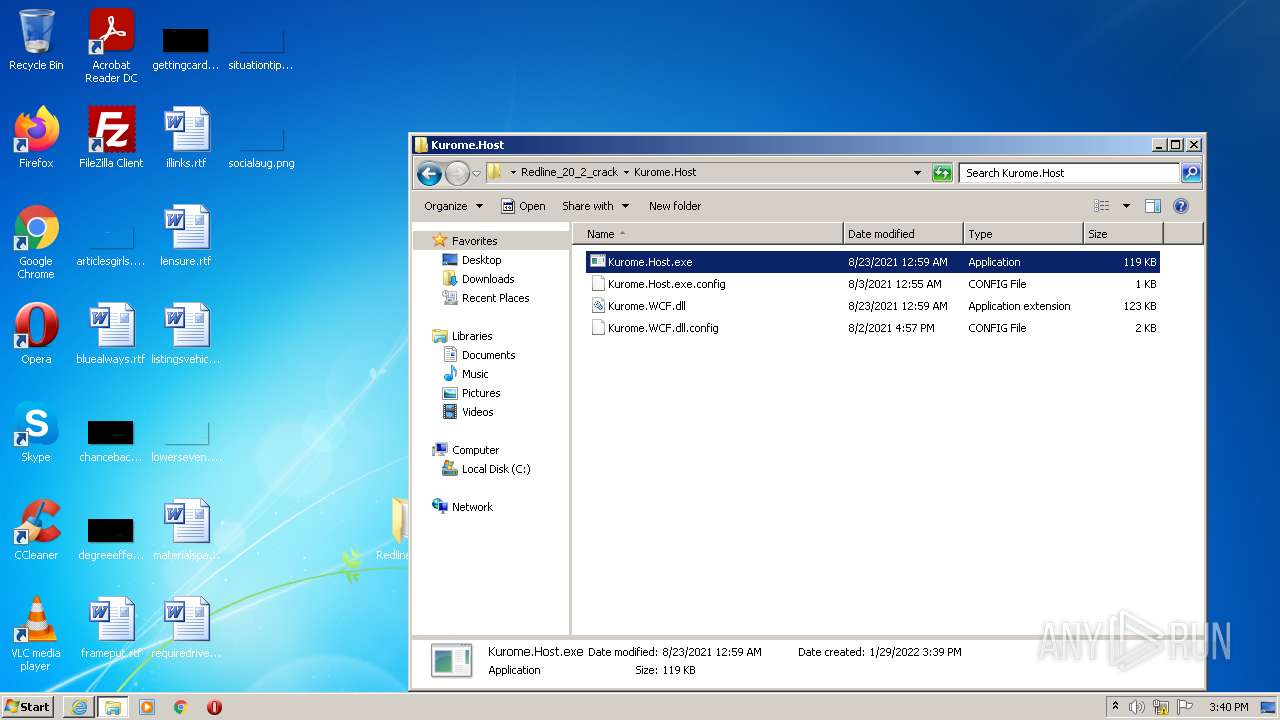
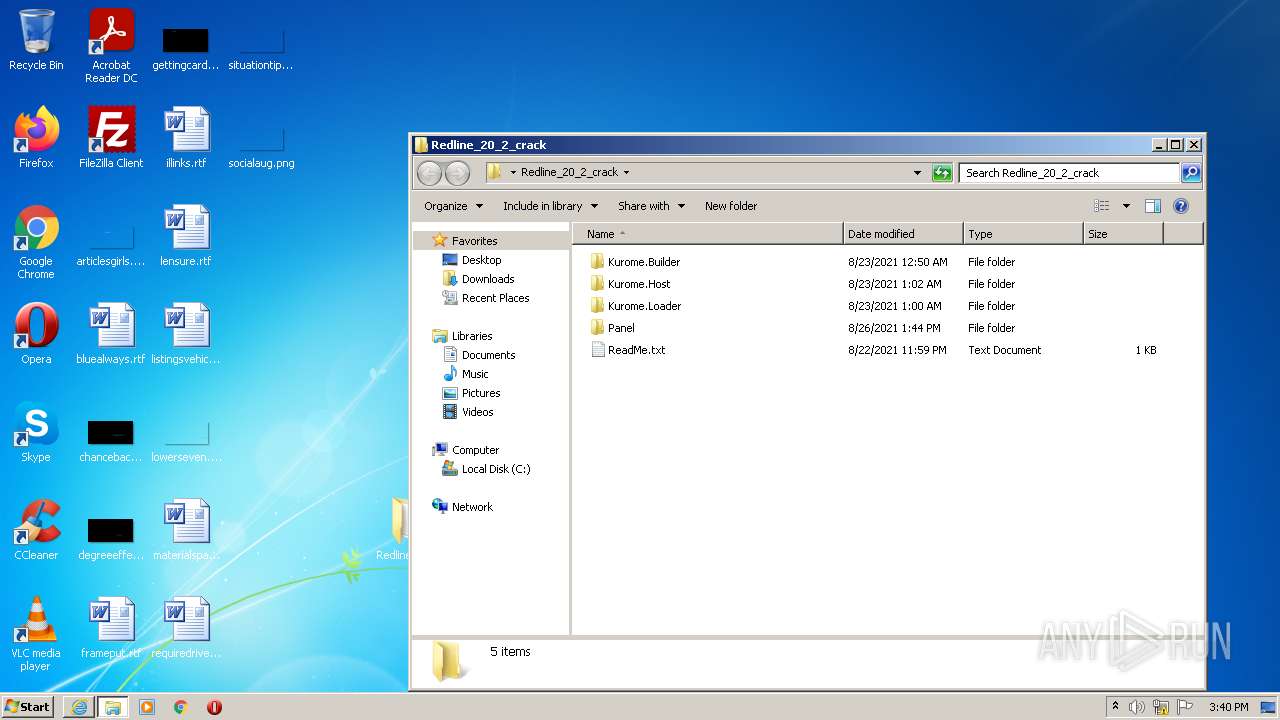
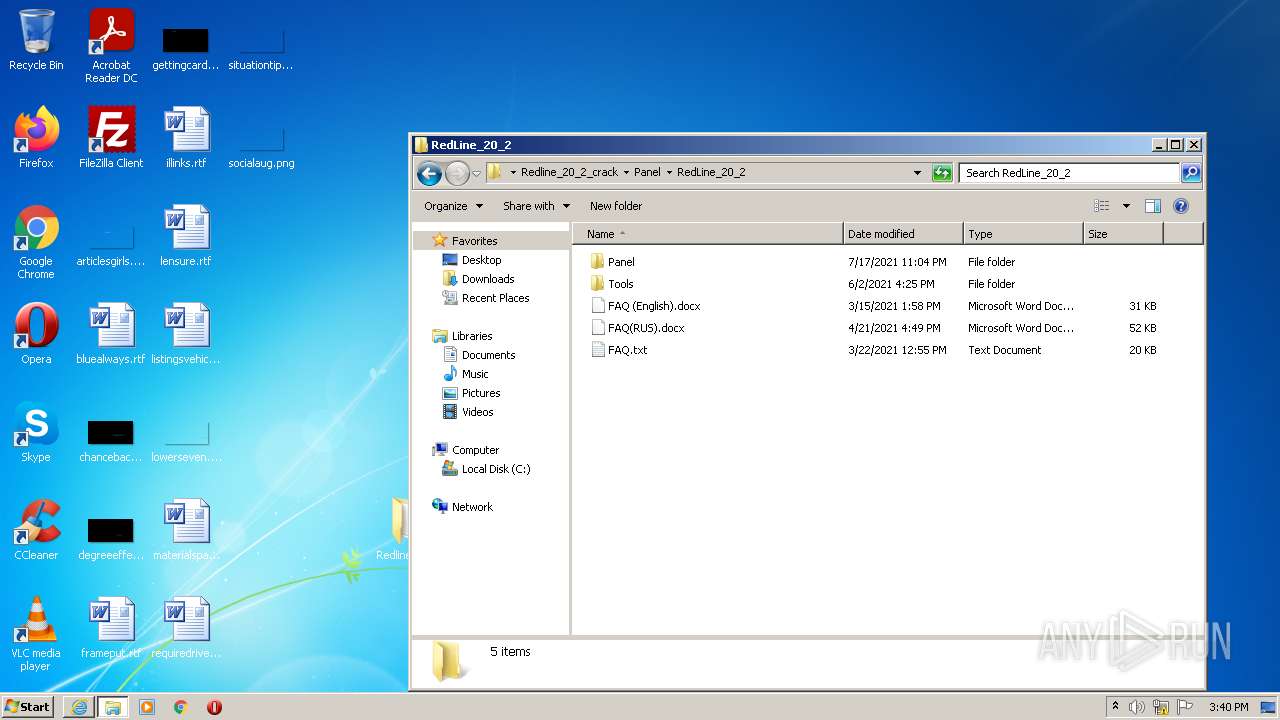
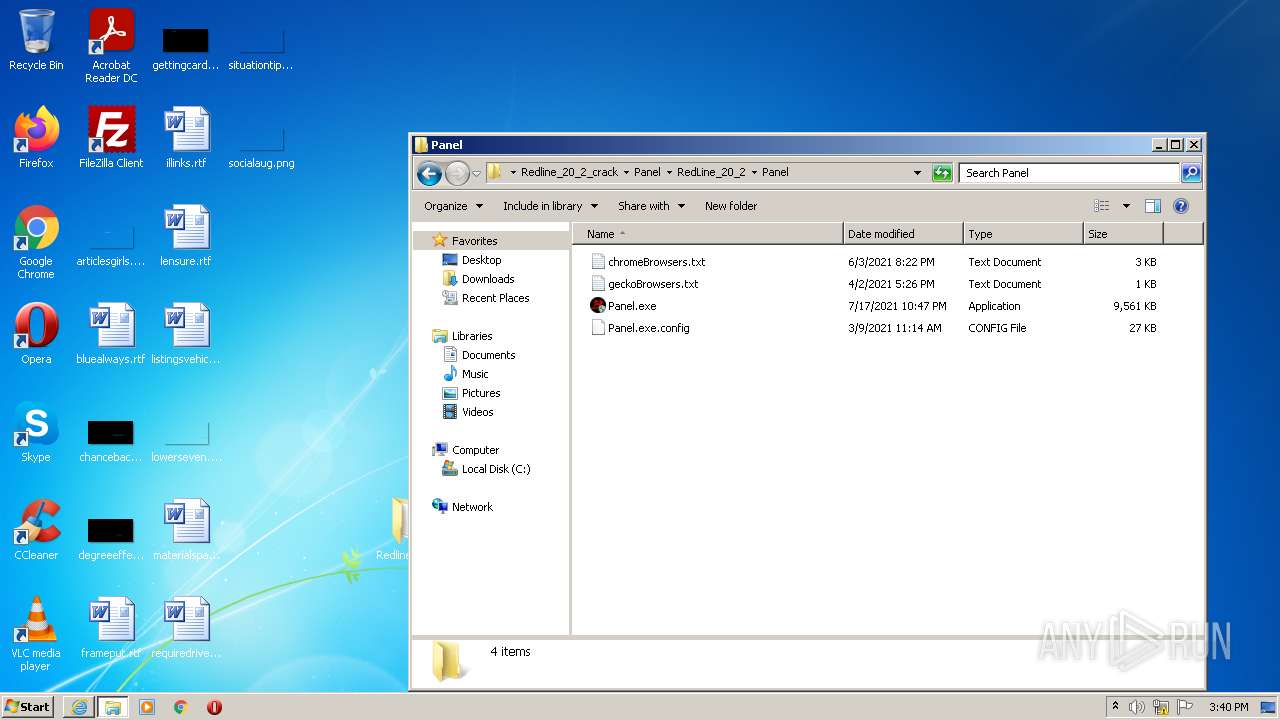
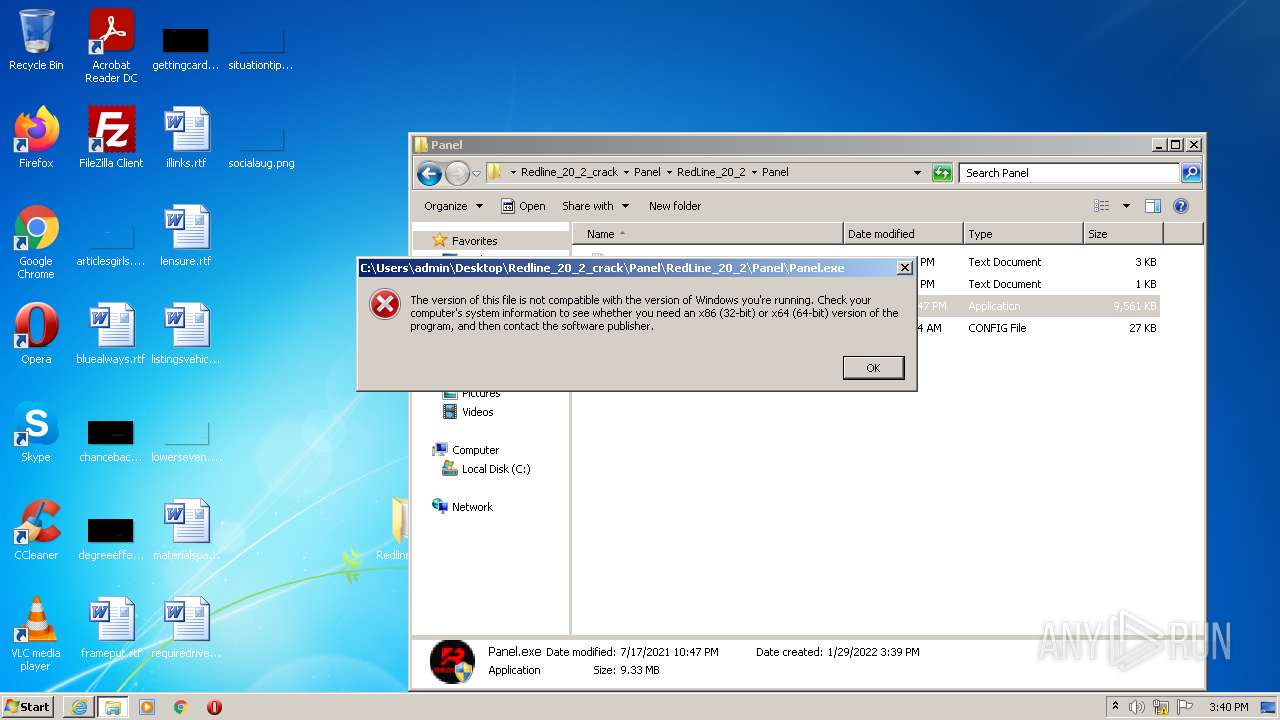
| 1276 | "C:\Users\admin\Desktop\Redline_20_2_crack\Kurome.Host\Kurome.Host.exe" | C:\Users\admin\Desktop\Redline_20_2_crack\Kurome.Host\Kurome.Host.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: Kurome.Host Exit code: 2148734720 Version: 1.0.0.0 Modules
| |||||||||||||||
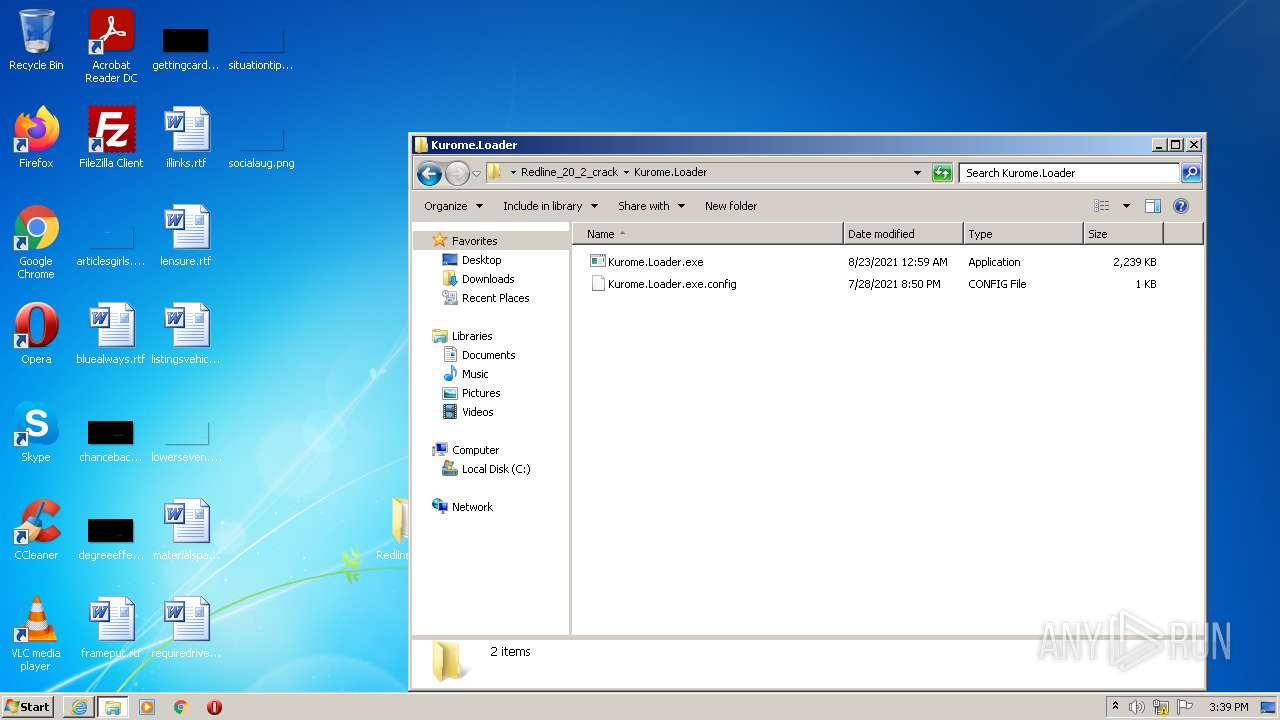
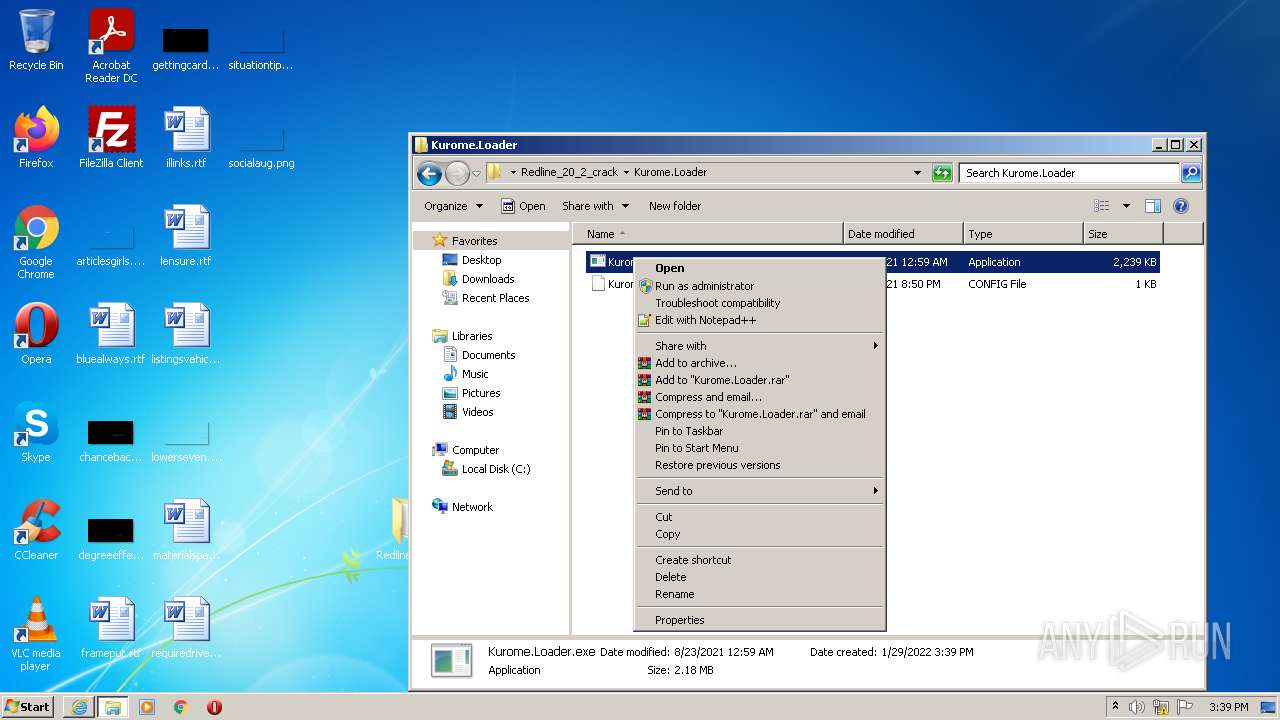
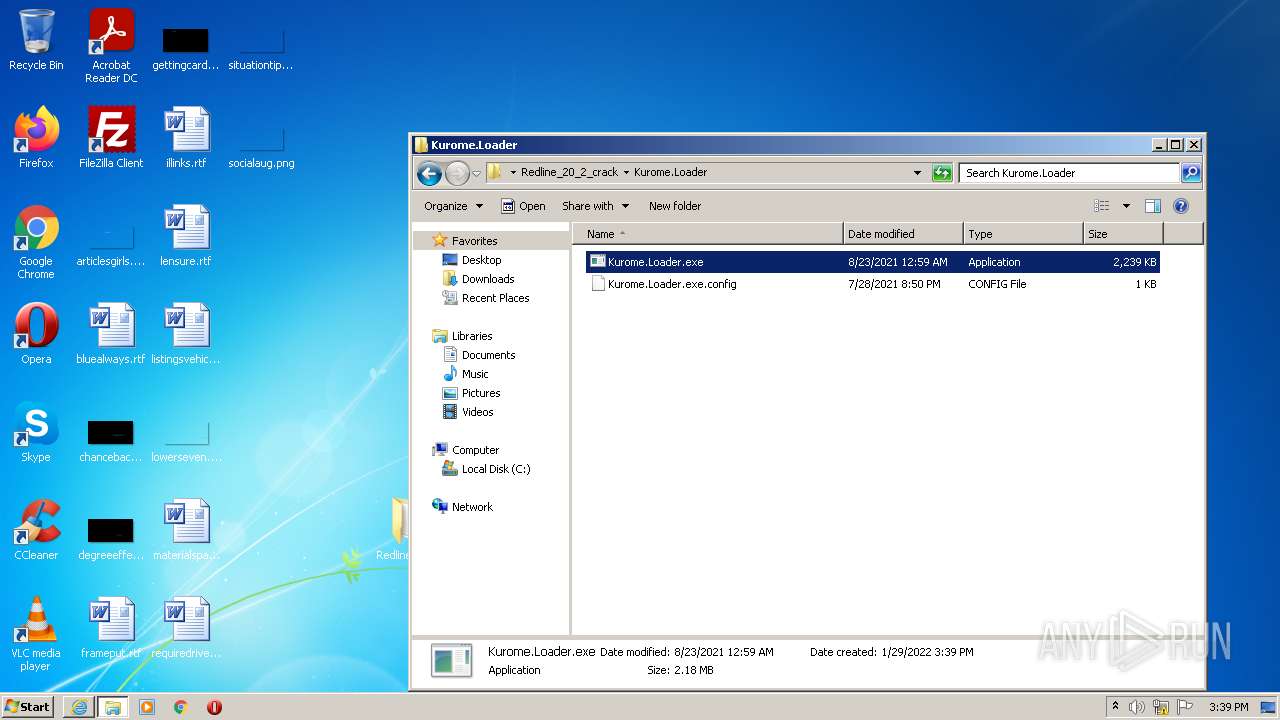
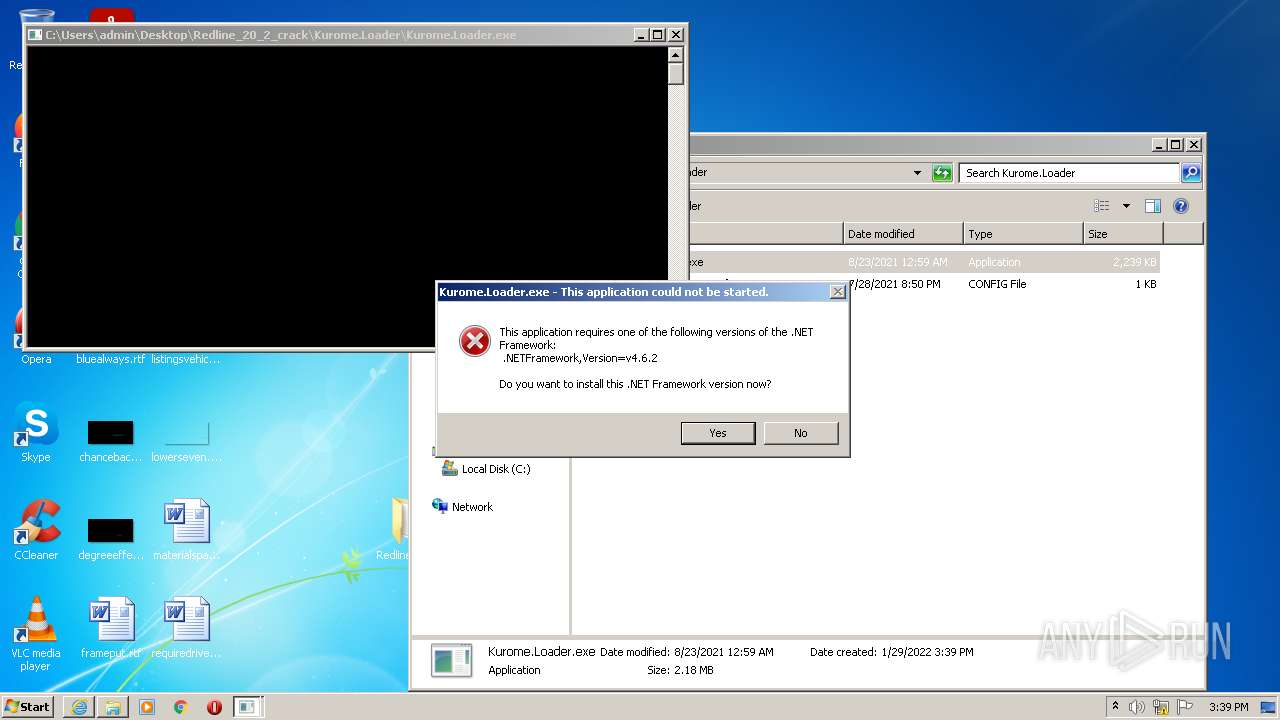
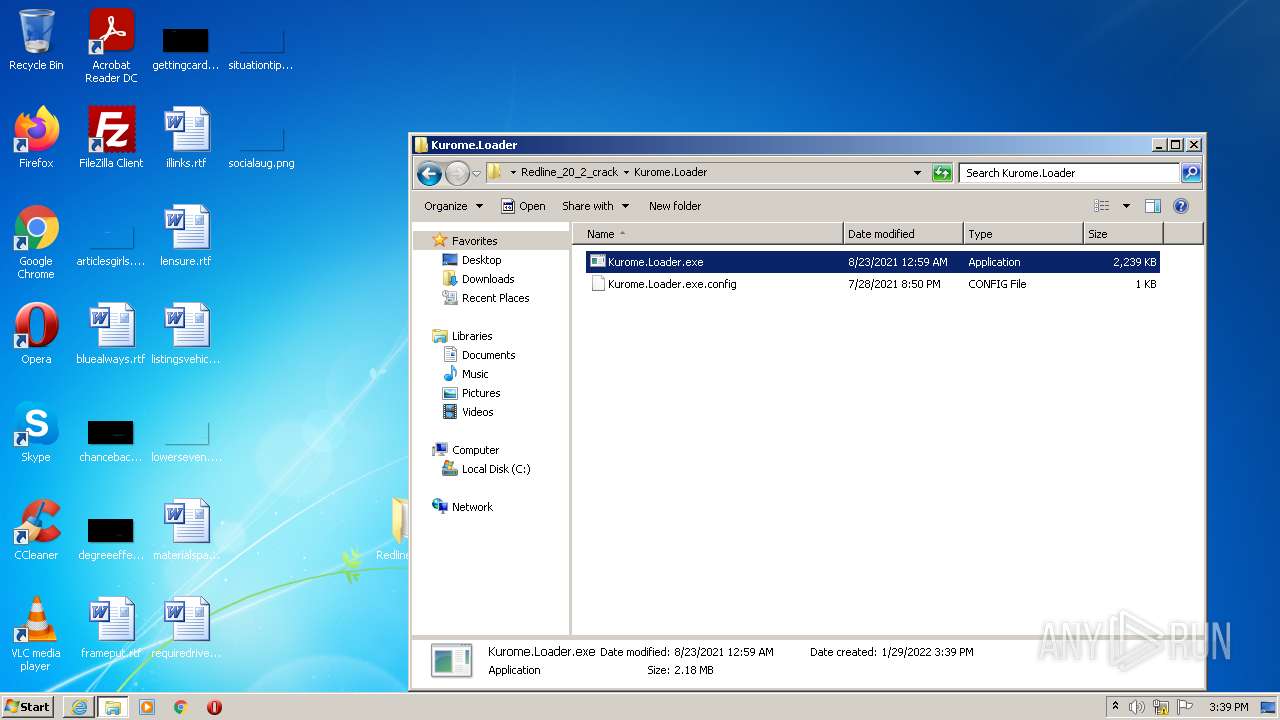
| 2428 | "C:\Users\admin\Desktop\Redline_20_2_crack\Kurome.Loader\Kurome.Loader.exe" | C:\Users\admin\Desktop\Redline_20_2_crack\Kurome.Loader\Kurome.Loader.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: Kurome.Loader Exit code: 2148734720 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2968 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Redline_20_2_crack.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3204 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 3436 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3928 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3928 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://anonfiles.com/55tcOcFdub/Redline_20_2_crack_zip" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
17 278
Read events
17 079
Write events
195
Delete events
4
Modification events
| (PID) Process: | (3928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 887639824 | |||
| (PID) Process: | (3928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30938406 | |||
| (PID) Process: | (3928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30938406 | |||
| (PID) Process: | (3928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
13
Suspicious files
26
Text files
49
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Redline_20_2_crack_zip[1].htm | html | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\app[1].js | text | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab3AAD.tmp | compressed | |
MD5:ACAEDA60C79C6BCAC925EEB3653F45E0 | SHA256:6B0CECCF0103AFD89844761417C1D23ACC41F8AEBF3B7230765209B61EEE5658 | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar3AAE.tmp | cat | |
MD5:D99661D0893A52A0700B8AE68457351A | SHA256:BDD5111162A6FA25682E18FA74E37E676D49CAFCB5B7207E98E5256D1EF0D003 | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:54E9306F95F32E50CCD58AF19753D929 | SHA256:45F94DCEB18A8F738A26DA09CE4558995A4FE02B971882E8116FC9B59813BB72 | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8CF5BD514FD3F41B9B84FC505B8DCD45 | der | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\anonfiles[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
37
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3436 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
3928 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
3436 | iexplore.exe | GET | 200 | 2.16.186.9:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgNP3fS5KI692THHXqQ23ICPyg%3D%3D | unknown | der | 503 b | shared |
3436 | iexplore.exe | GET | 200 | 18.66.92.28:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3436 | iexplore.exe | GET | 200 | 23.37.41.57:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
3436 | iexplore.exe | GET | 200 | 95.140.236.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bba66621feecf837 | GB | compressed | 4.70 Kb | whitelisted |
3436 | iexplore.exe | GET | 200 | 95.140.236.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?4c02cd1d150e1dbd | GB | compressed | 59.9 Kb | whitelisted |
3436 | iexplore.exe | GET | 200 | 52.222.206.202:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3436 | iexplore.exe | GET | 200 | 52.222.206.67:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3928 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3436 | iexplore.exe | 45.154.253.150:443 | anonfiles.com | — | — | suspicious |
3436 | iexplore.exe | 23.37.41.57:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
3436 | iexplore.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
3436 | iexplore.exe | 18.66.137.171:443 | djv99sxoqpv11.cloudfront.net | Massachusetts Institute of Technology | US | unknown |
3436 | iexplore.exe | 104.18.20.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
3436 | iexplore.exe | 18.66.92.28:80 | o.ss2.us | Massachusetts Institute of Technology | US | suspicious |
3436 | iexplore.exe | 52.222.206.202:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
3436 | iexplore.exe | 52.222.206.67:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
3436 | iexplore.exe | 95.140.236.0:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | GB | whitelisted |
3928 | iexplore.exe | 45.154.253.150:443 | anonfiles.com | — | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
o.ss2.us |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |