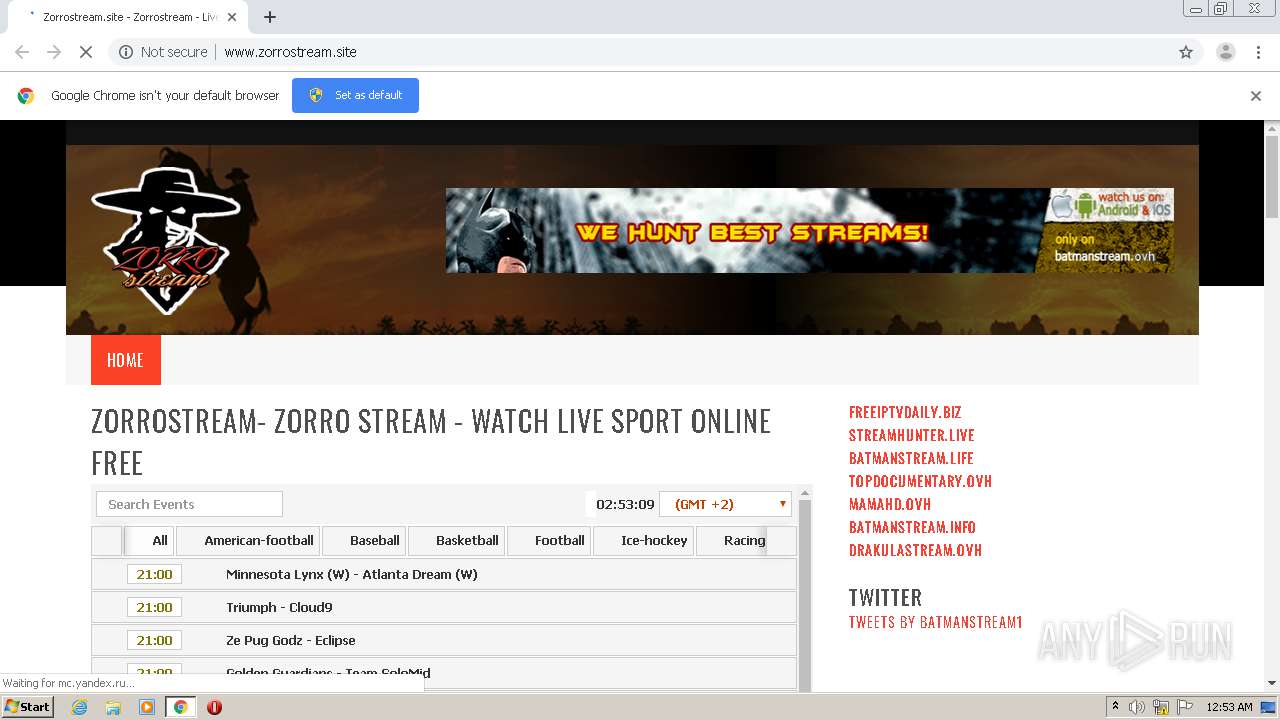
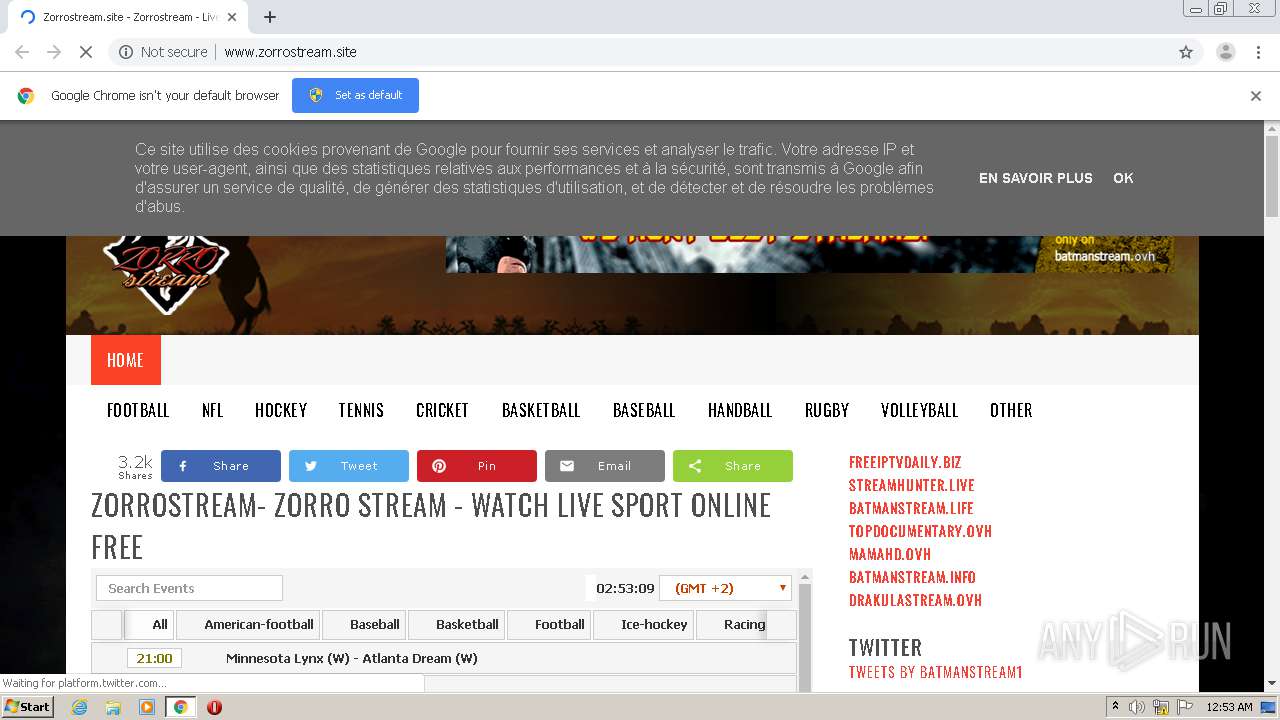
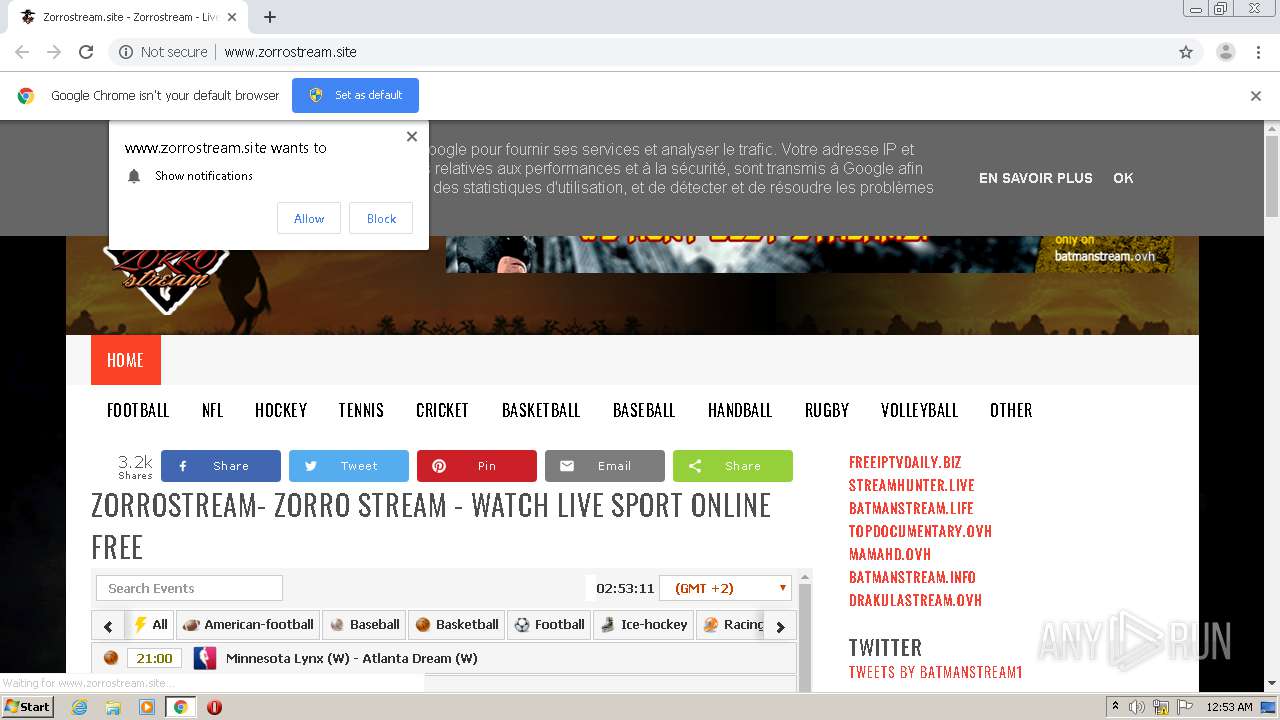
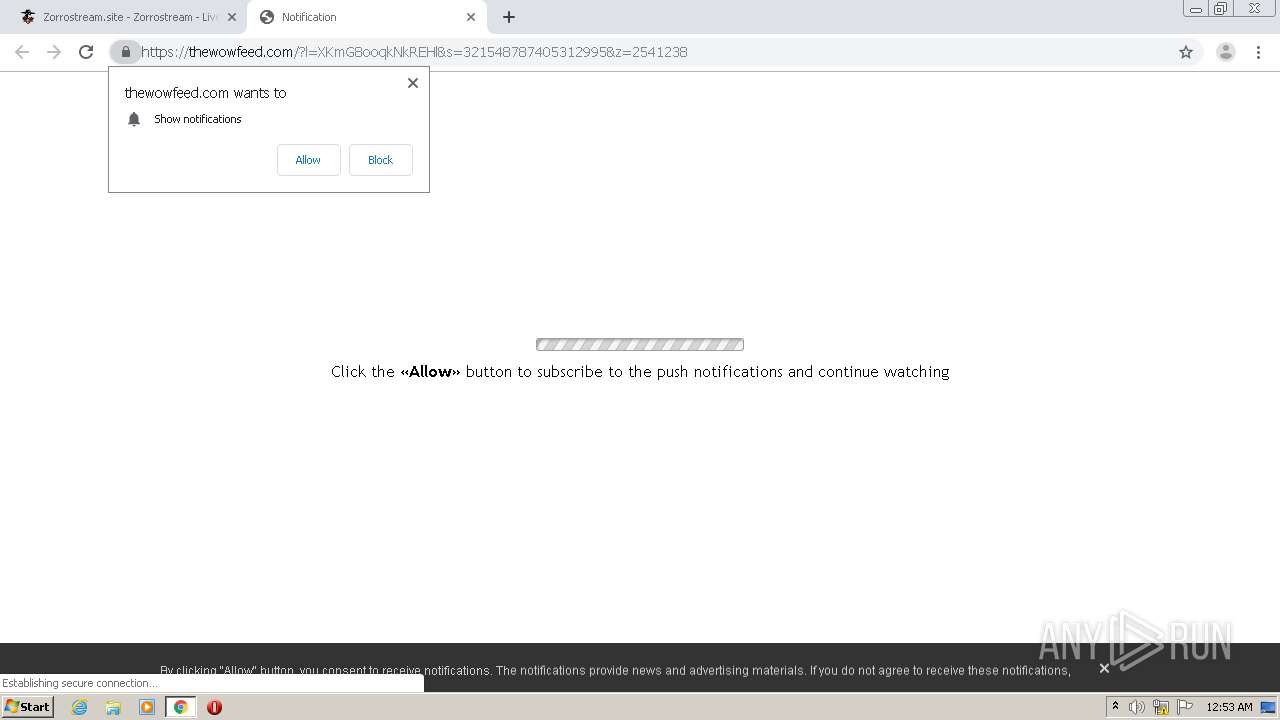
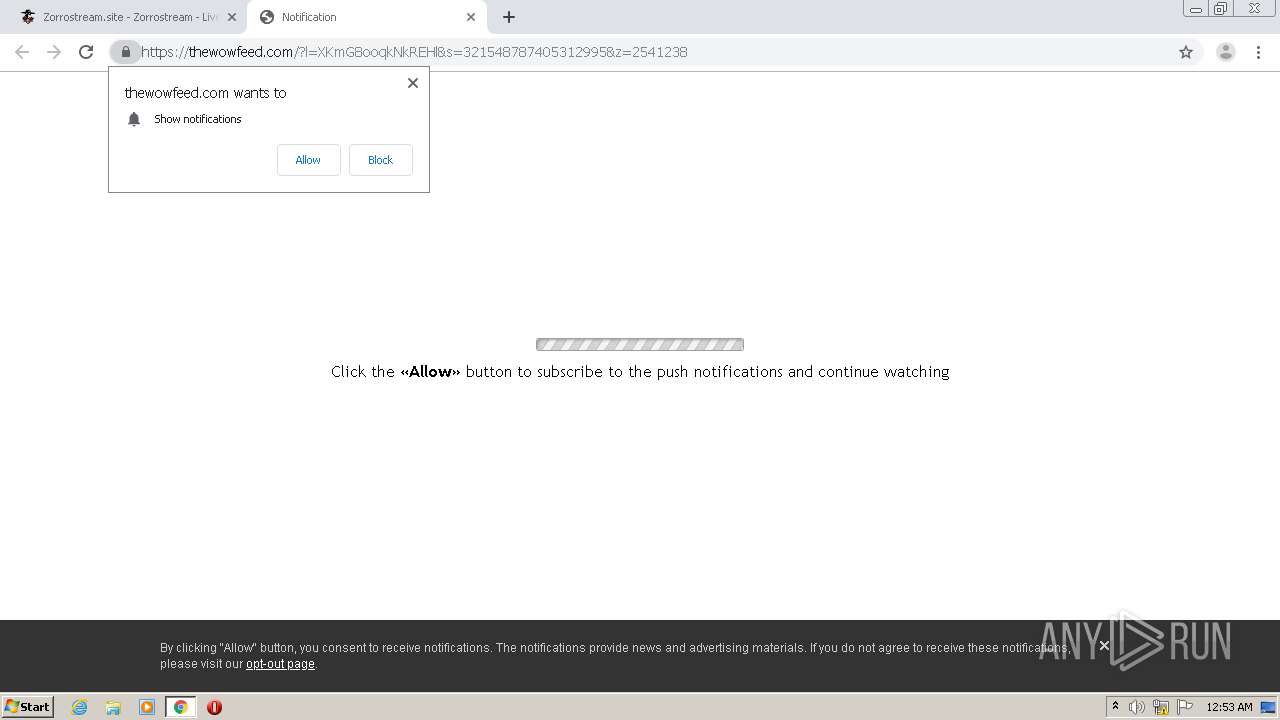
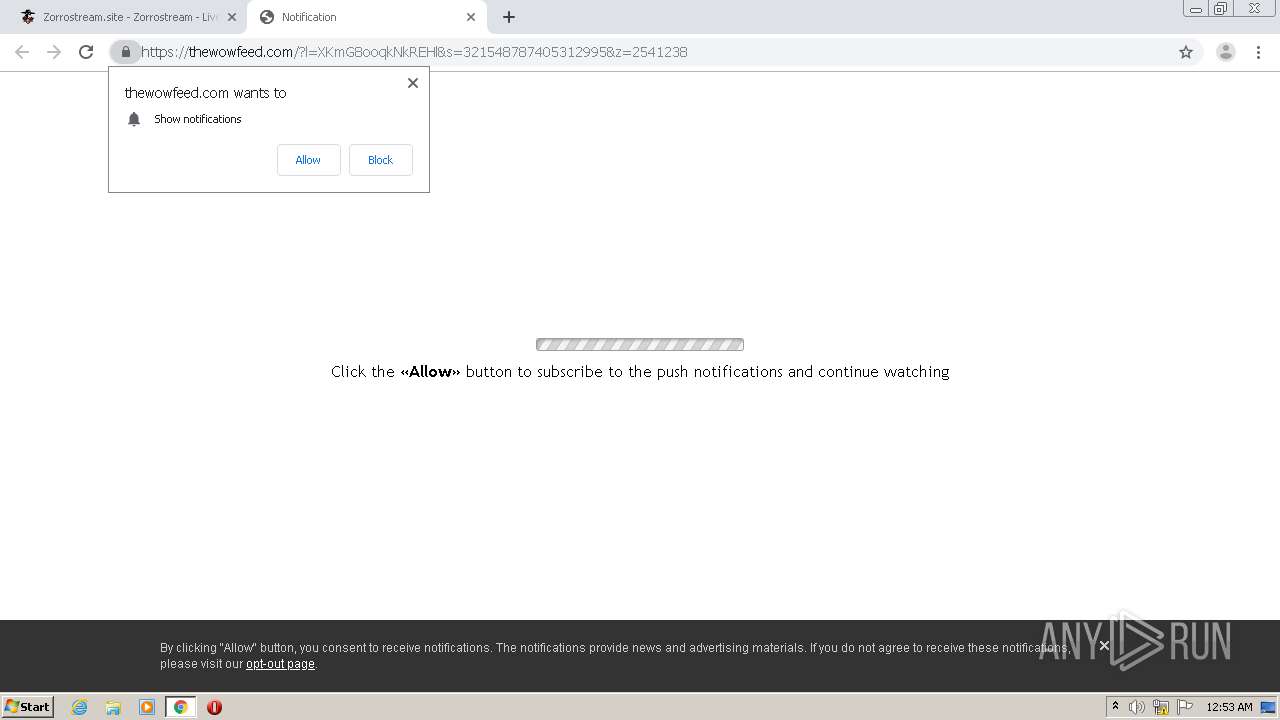
| URL: | http://www.zorrostream.site/ |
| Full analysis: | https://app.any.run/tasks/ef63e282-a76c-43a8-9301-87e528a1ef81 |
| Verdict: | Malicious activity |
| Analysis date: | August 23, 2020, 23:52:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6F7EFB4BA17CBD1E37A1C88F183B8B90 |
| SHA1: | 61D1625580FA5667F5EBDEC14ED003D6B9019278 |
| SHA256: | 958AFCDEF3D9FDEA14CF00F4E37366F2CD0016AF2CE51AF11A1ED9A188332723 |
| SSDEEP: | 3:N1KJS4iqWRNK:Cc4ipK |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 1756)
- chrome.exe (PID: 1488)
Application launched itself
- chrome.exe (PID: 1756)
Reads settings of System Certificates
- chrome.exe (PID: 1488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
20
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,12975533882844249381,18009699525736435719,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10016549069179899485 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4612 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,12975533882844249381,18009699525736435719,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8909164605765235056 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,12975533882844249381,18009699525736435719,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13022103581703822416 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3300 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,12975533882844249381,18009699525736435719,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7658741508344444694 --mojo-platform-channel-handle=1560 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,12975533882844249381,18009699525736435719,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9832270587719091478 --mojo-platform-channel-handle=4984 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,12975533882844249381,18009699525736435719,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7808119921536938322 --mojo-platform-channel-handle=4528 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,12975533882844249381,18009699525736435719,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15623037795275610910 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.zorrostream.site/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,12975533882844249381,18009699525736435719,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6514350615697383754 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,12975533882844249381,18009699525736435719,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1829730123524764453 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
635
Read events
553
Write events
78
Delete events
4
Modification events
| (PID) Process: | (1756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1756-13242700384718500 |
Value: 259 | |||
| (PID) Process: | (1756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (1756) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
67
Text files
86
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d2fef9a4-f7a9-4c80-9cb1-689a0339351c.tmp | — | |
MD5:— | SHA256:— | |||
| 1756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF157c6d.TMP | text | |
MD5:— | SHA256:— | |||
| 1756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF157bd1.TMP | text | |
MD5:— | SHA256:— | |||
| 1756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF157da5.TMP | — | |
MD5:— | SHA256:— | |||
| 1756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF157c0f.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
77
DNS requests
67
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1488 | chrome.exe | GET | 200 | 216.58.206.19:80 | http://www.zorrostream.site/ | US | html | 50.4 Kb | malicious |
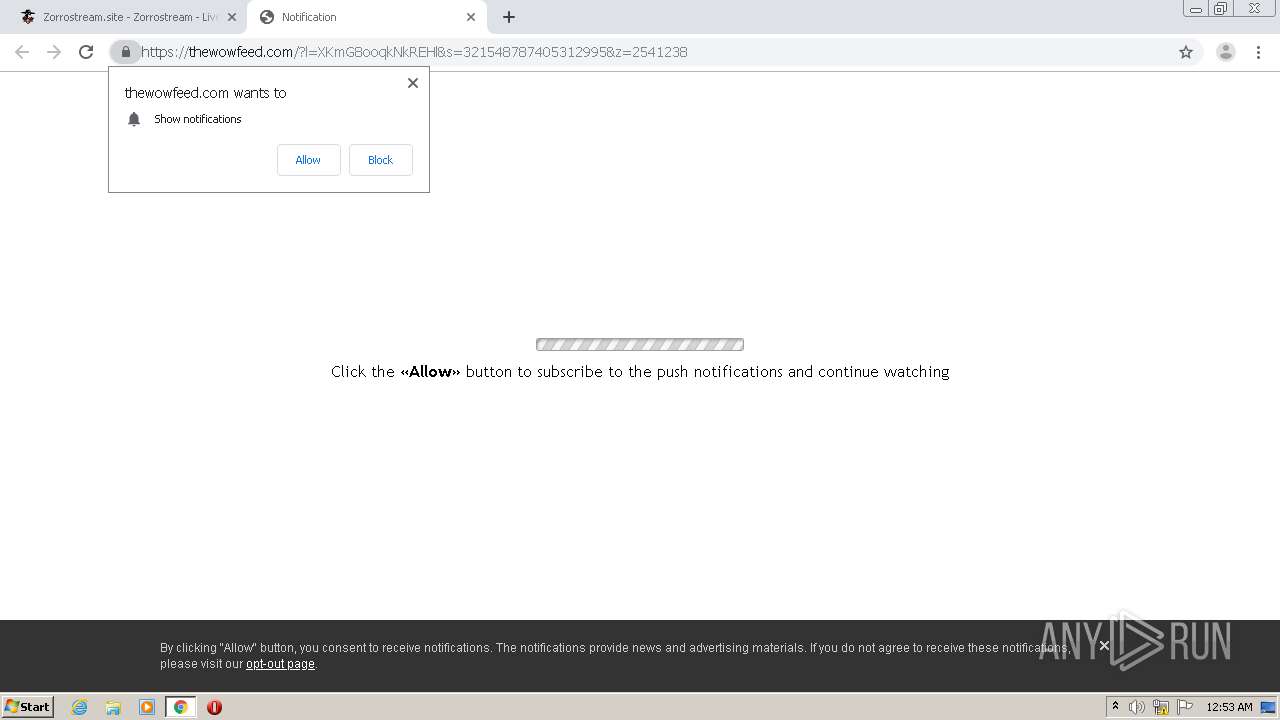
1488 | chrome.exe | GET | 200 | 139.45.196.146:80 | http://pushmejs.com/ntfc.php?p=2541246 | US | text | 12.1 Kb | whitelisted |
1488 | chrome.exe | GET | 200 | 216.58.206.19:80 | http://www.zorrostream.site/feeds/posts/summary?max-results=1&alt=json-in-script&callback=hitungtotaldata | US | text | 718 b | malicious |
1488 | chrome.exe | GET | 200 | 216.58.206.1:80 | http://2.bp.blogspot.com/-u7ON6QEUxuc/WmUHlUPh0YI/AAAAAAAAAFA/5Pz4z1rUVVIslSI1jT1g_pl4Q7OUyZmhgCK4BGAYYCw/s1600/hunt-best-streams.png | US | image | 119 Kb | whitelisted |
1488 | chrome.exe | POST | 200 | 81.171.10.215:80 | http://deloplen.com/options?option_args=CLaNmwESIDE2NzJhMTJmMzIwZTQ3NjE4NzI2MGU5YzZmNzRjYTliGipodHRwOi8vZGVsb3BsZW4uY29tL2FwdS5waHA/em9uZWlkPTI1NDEyMzgiHGh0dHA6Ly93d3cuem9ycm9zdHJlYW0uc2l0ZS8= | NL | — | — | whitelisted |
1488 | chrome.exe | GET | 200 | 216.58.206.1:80 | http://4.bp.blogspot.com/-DPxl6X_uufs/WmUTNw9dvfI/AAAAAAAAAG0/MTtigLXLPIcQjO_dy8CPK8X47wh14N5qgCK4BGAYYCw/s1600/zorrostream%2Blogo.png | US | image | 22.8 Kb | whitelisted |
1488 | chrome.exe | GET | 200 | 143.204.202.110:80 | http://platform-api.sharethis.com/js/sharethis.js | US | text | 30.1 Kb | whitelisted |
1488 | chrome.exe | GET | 200 | 81.171.10.215:80 | http://deloplen.com/?rb=PsDrqvQYZtuYVpIicVachQTS_66iyYq5b0gj8gD5vVFpoiA9CMKKrcfp7_cHykN3jCH5G5xQJSMEu3cJqbmQBemcL7_BC-aAfELA0Z5w65E0N5uP0UW6DBFN-sQv2YMni21zHpD4FmxdXK5VJlnevltDc4Kq_Fi7ai25aujXk5hFi2guLJjcCt3SVt7qUKBrRRM0ajyLQL9BOd180LoWYjjbXeDI_GFQceHozW26Yg5ujWBGJ82TF_UhsvPigktO4hSXsMpcVOw%3D&zoneid=2541238&fs=0&cf=0&sw=1280&sh=720&sah=692&wx=0&wy=0&ww=1280&wh=692&cw=1264&wiw=1280&wih=572&wfc=3&pl=http%3A%2F%2Fwww.zorrostream.site%2F&drf=&np=1&pt=0&nb=1&ng=1&ix=0&nw=0&tb=false | NL | html | 713 b | whitelisted |
1488 | chrome.exe | GET | 200 | 216.58.206.19:80 | http://www.zorrostream.site/favicon.ico | US | image | 662 b | malicious |
1488 | chrome.exe | GET | 200 | 81.171.10.215:80 | http://deloplen.com/fac.php | NL | html | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1488 | chrome.exe | 216.58.212.169:443 | www.blogger.com | Google Inc. | US | whitelisted |
1488 | chrome.exe | 139.45.196.146:80 | pushmejs.com | — | US | suspicious |
1488 | chrome.exe | 216.58.205.227:80 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1488 | chrome.exe | 23.210.248.44:80 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
1488 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1488 | chrome.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1488 | chrome.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
1488 | chrome.exe | 143.204.202.110:80 | platform-api.sharethis.com | — | US | suspicious |
1488 | chrome.exe | 172.217.23.138:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
1488 | chrome.exe | 216.58.206.1:80 | 2.bp.blogspot.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.zorrostream.site |
| malicious |
accounts.google.com |
| shared |
www.blogger.com |
| shared |
maxcdn.bootstrapcdn.com |
| whitelisted |
platform-api.sharethis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
pushmejs.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
resources.blogblog.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1488 | chrome.exe | A Network Trojan was detected | SUSPICIOUS [PTsecurity] JS obfuscation (obfuscator.io) |