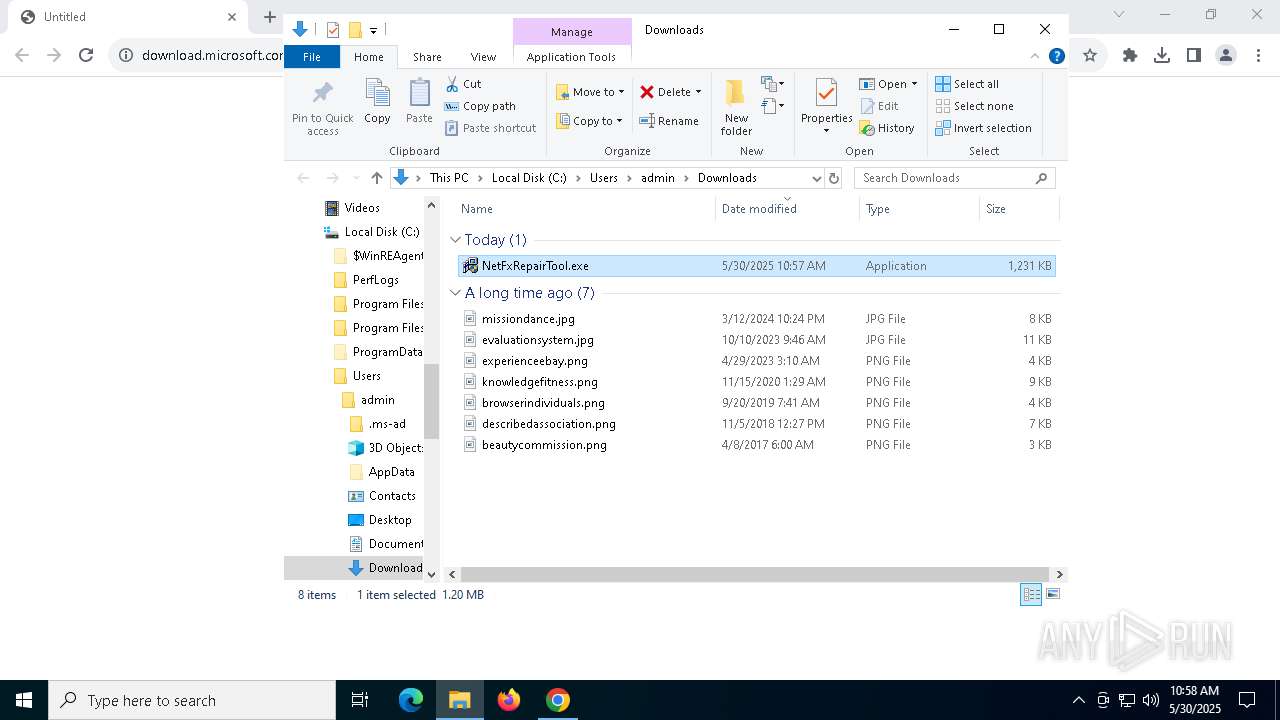
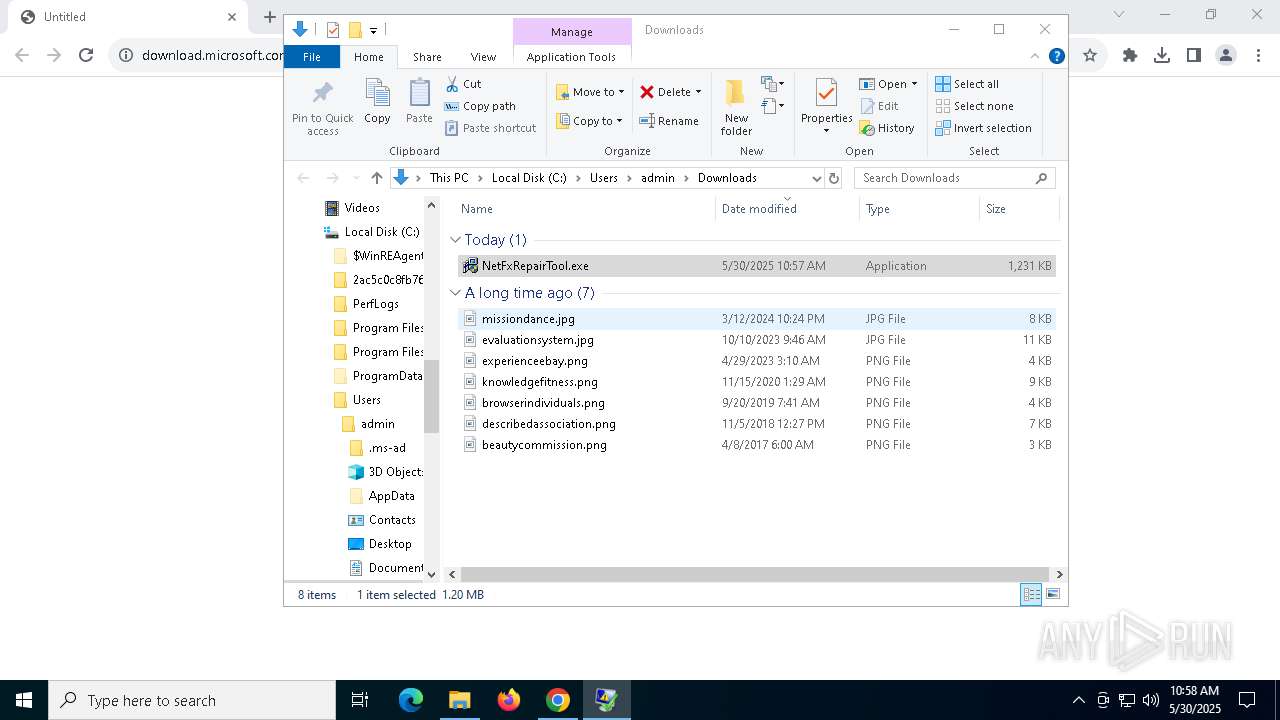
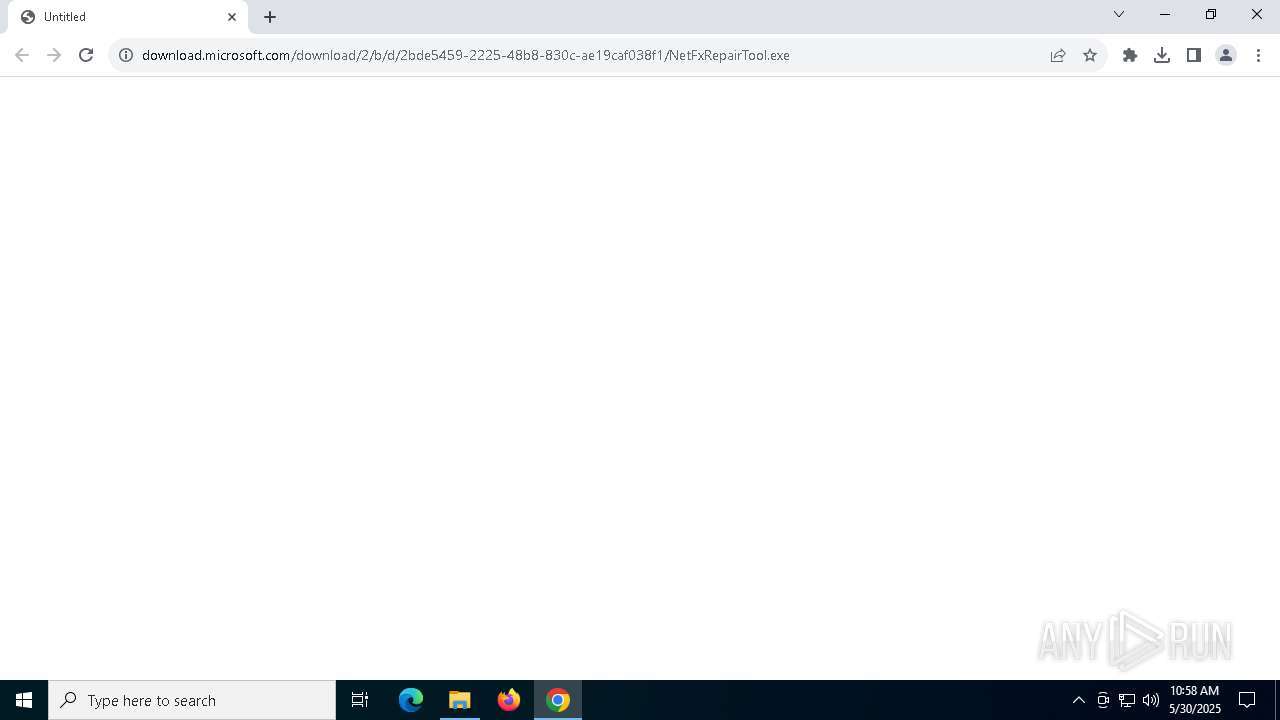
| URL: | https://download.microsoft.com/download/2/b/d/2bde5459-2225-48b8-830c-ae19caf038f1/NetFxRepairTool.exe |
| Full analysis: | https://app.any.run/tasks/37d3ec6a-7829-4205-aa41-97916f090553 |
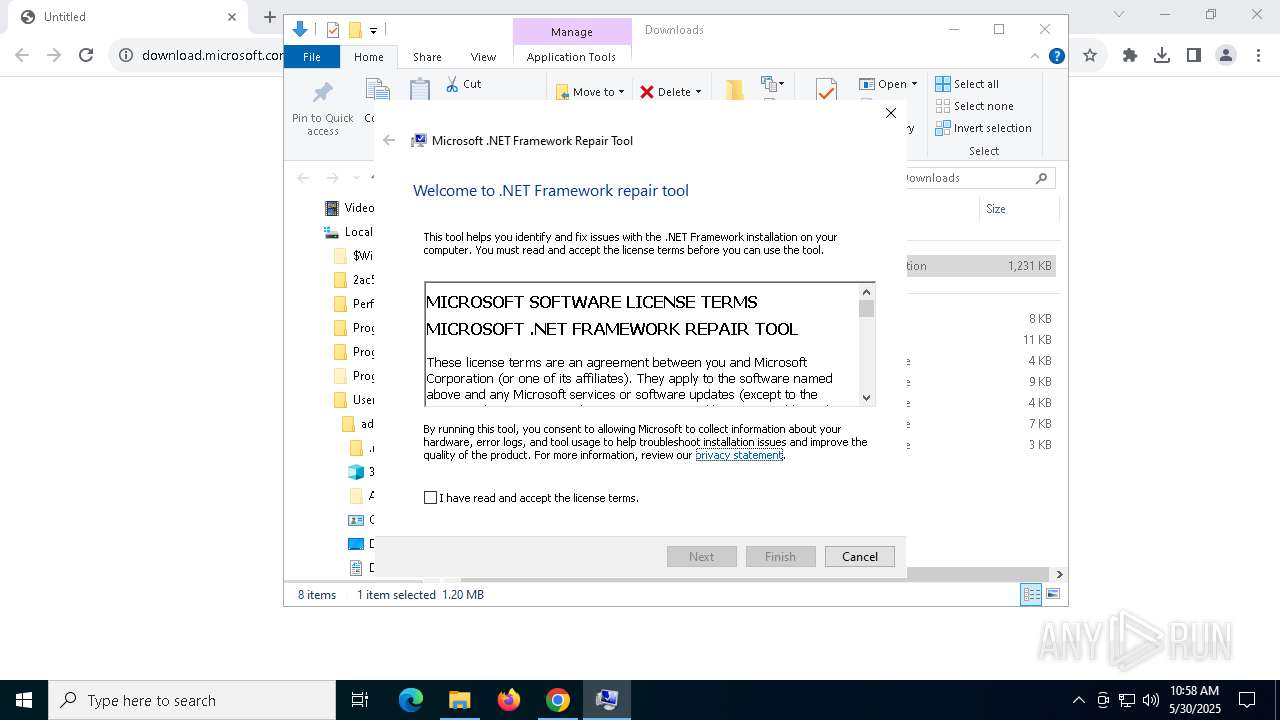
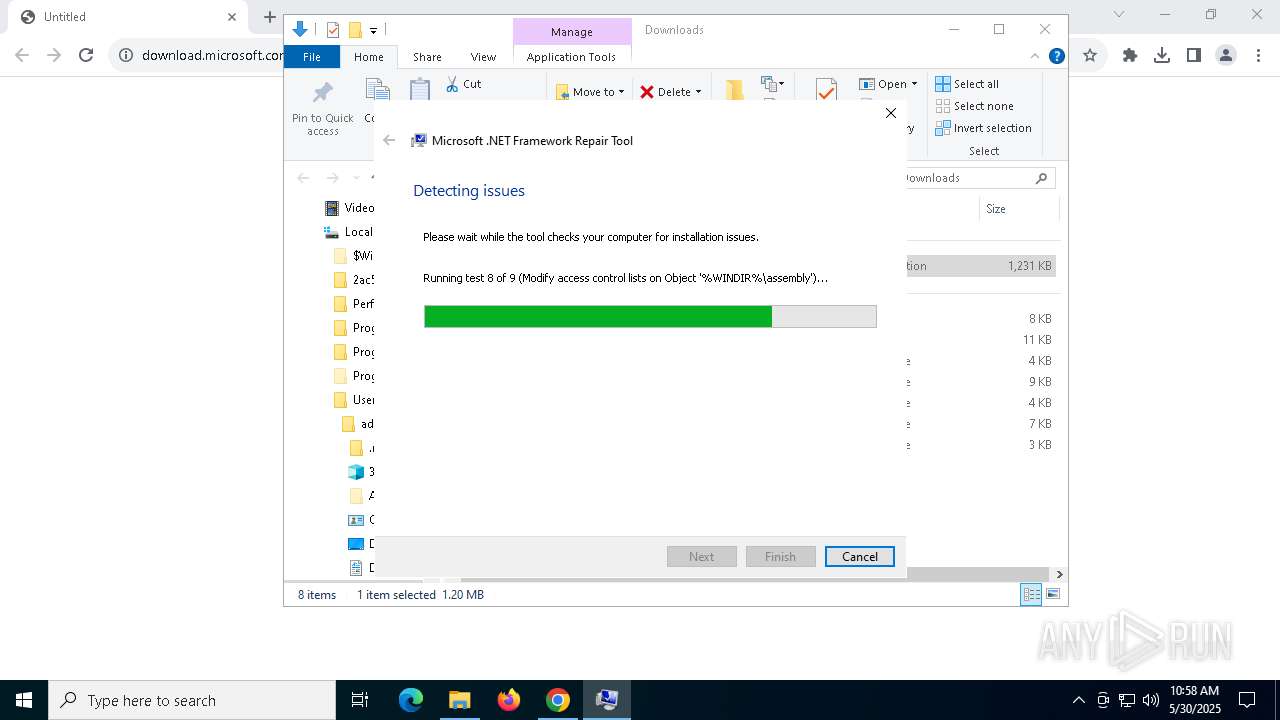
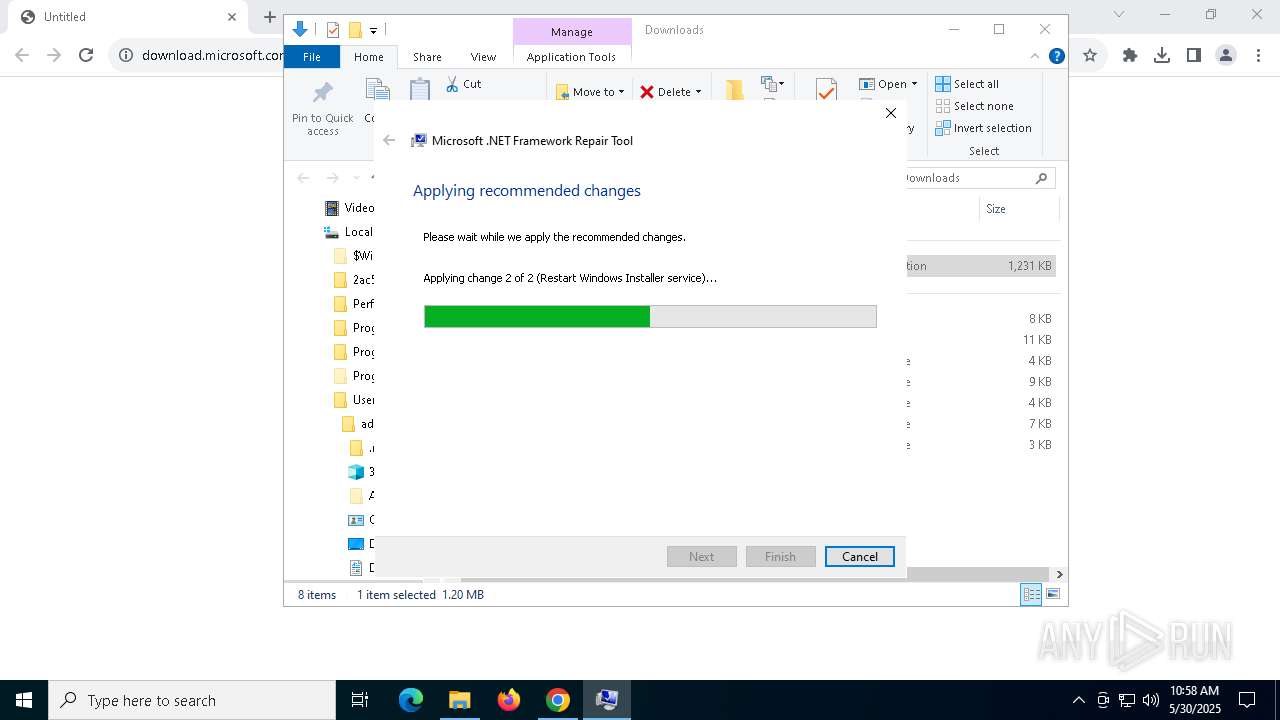
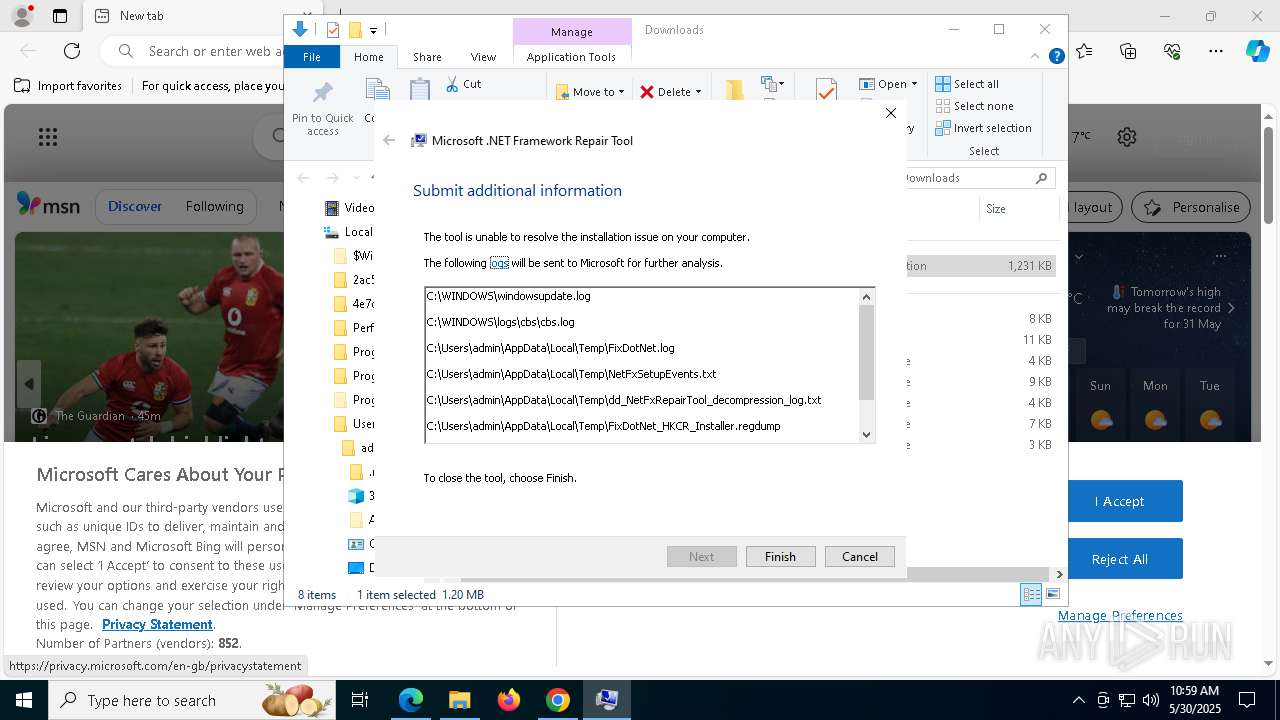
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2025, 10:57:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | B25A9564E67ECFDD663AB0F6A6404217 |
| SHA1: | 2A9D07AE859E83B3CB1AC8E9FF3182D89D7A0A17 |
| SHA256: | 9583F899805C1F6E3312C6561E71CDBE53F414582CCC6AE180BE57C06BAC1713 |
| SSDEEP: | 3:N8SElyKRtR8LXwX3ERId1IpUcGqCUbhAD7J0dAn:2SKTD8UnERg1L6Ct7n |
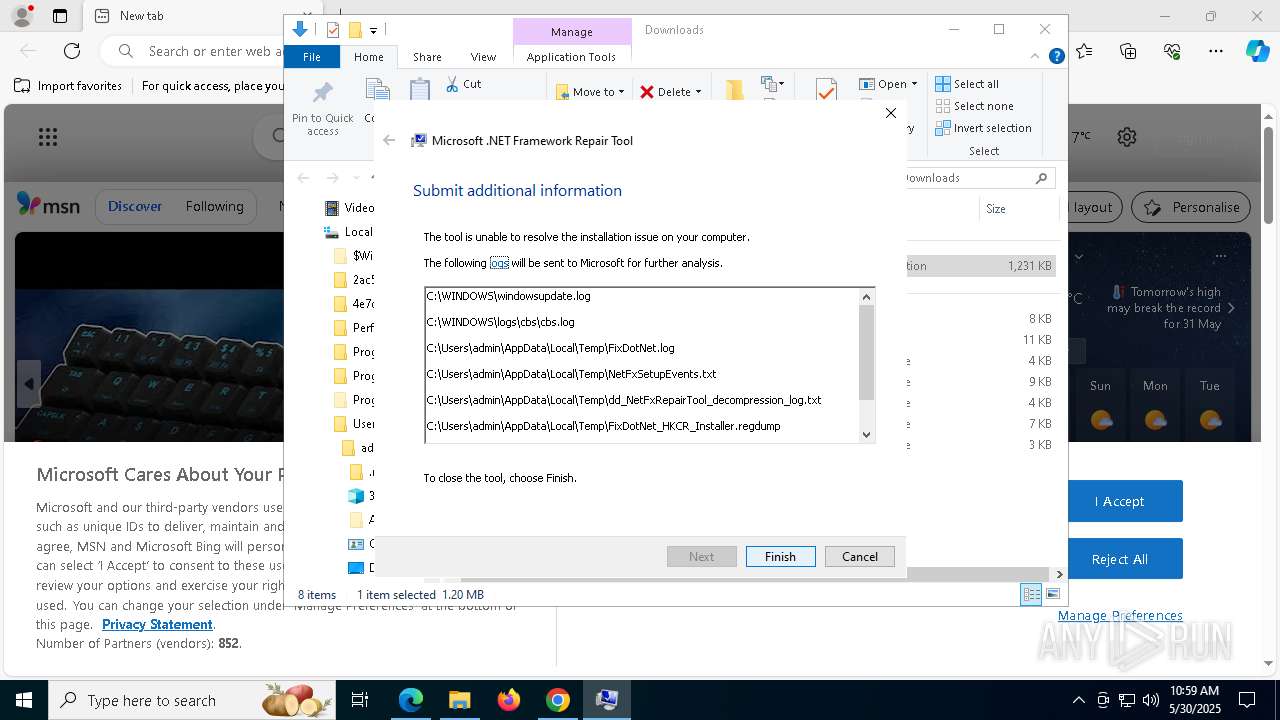
MALICIOUS
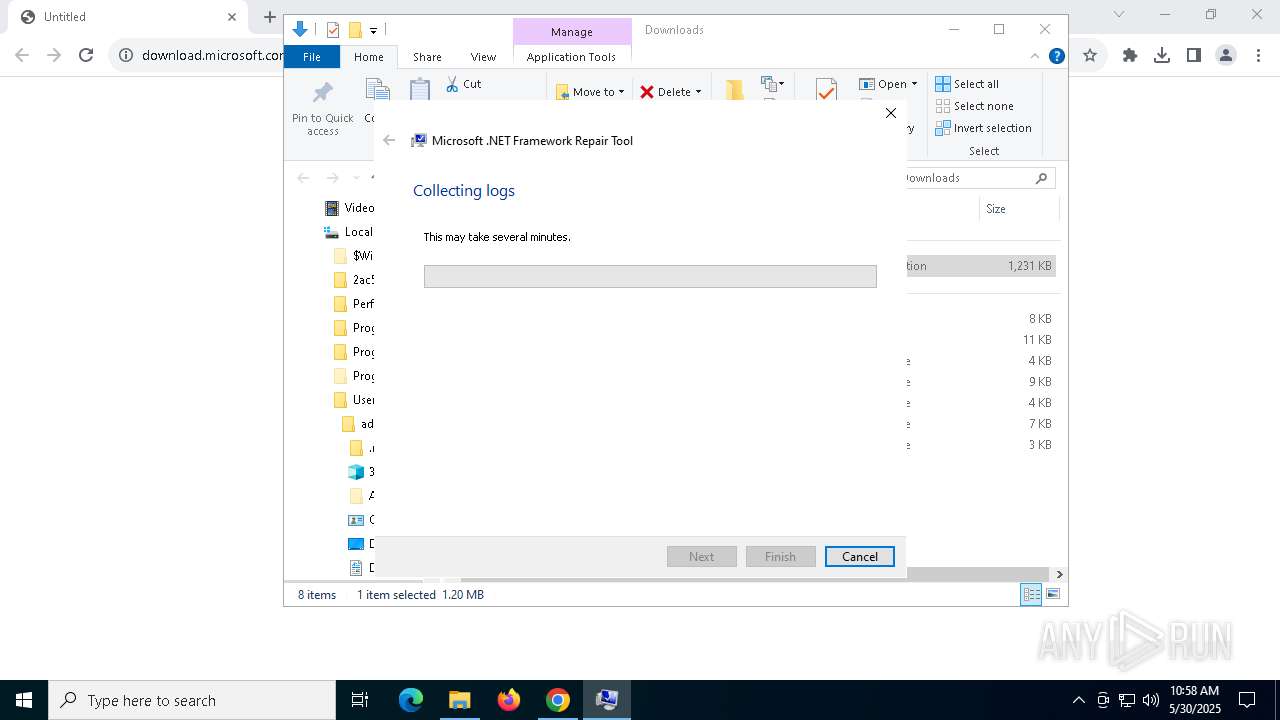
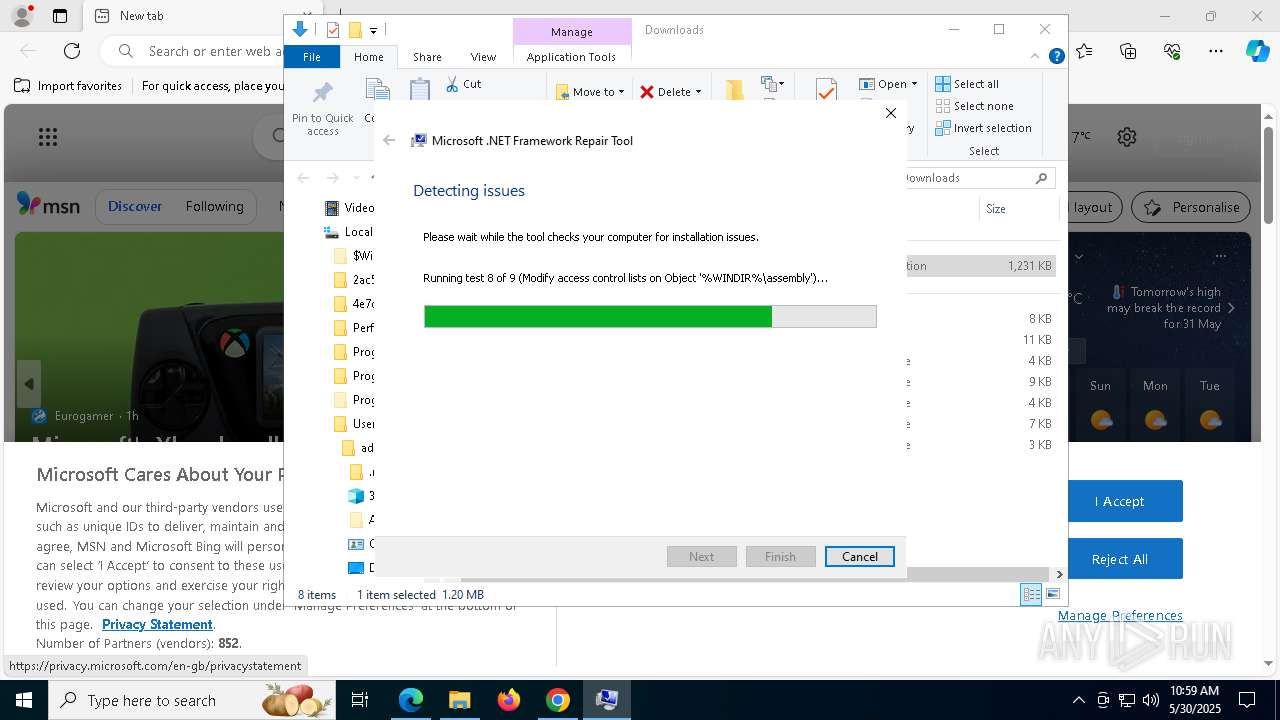
Starts NET.EXE for service management
- FixDotNet.exe (PID: 2560)
- net.exe (PID: 6268)
- net.exe (PID: 4448)
- FixDotNet.exe (PID: 7748)
- net.exe (PID: 8416)
- net.exe (PID: 8324)
SUSPICIOUS
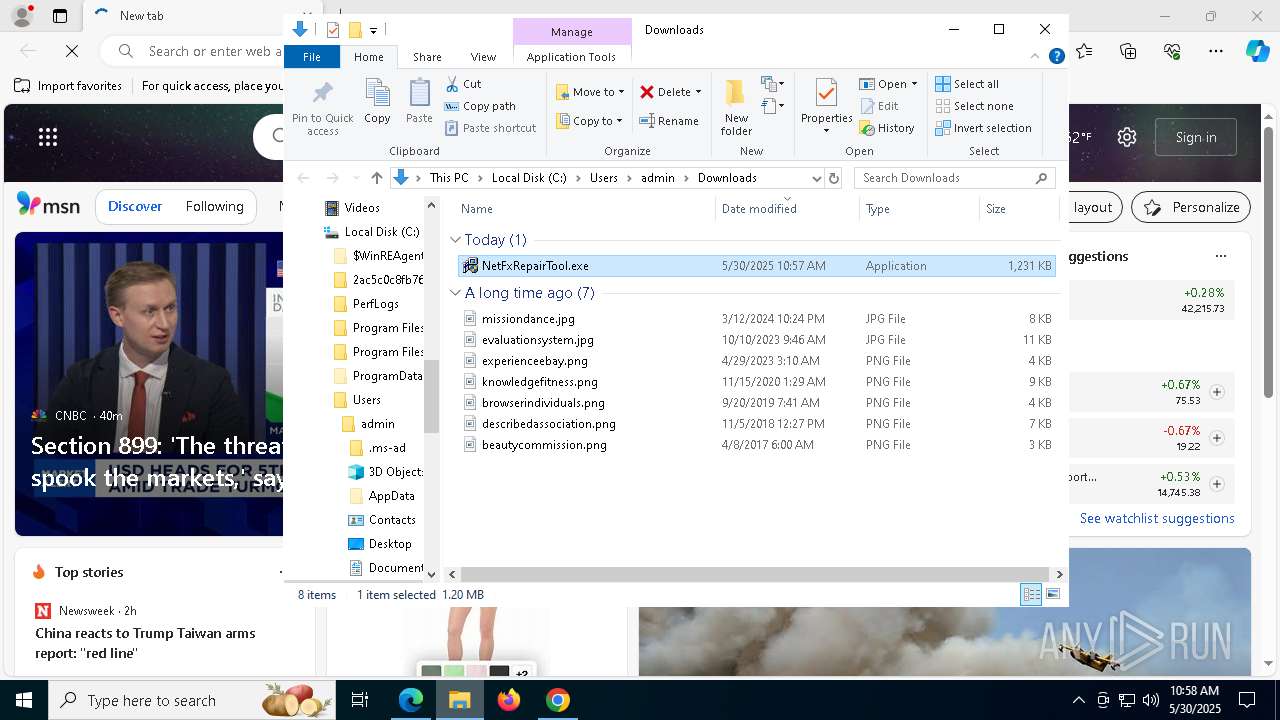
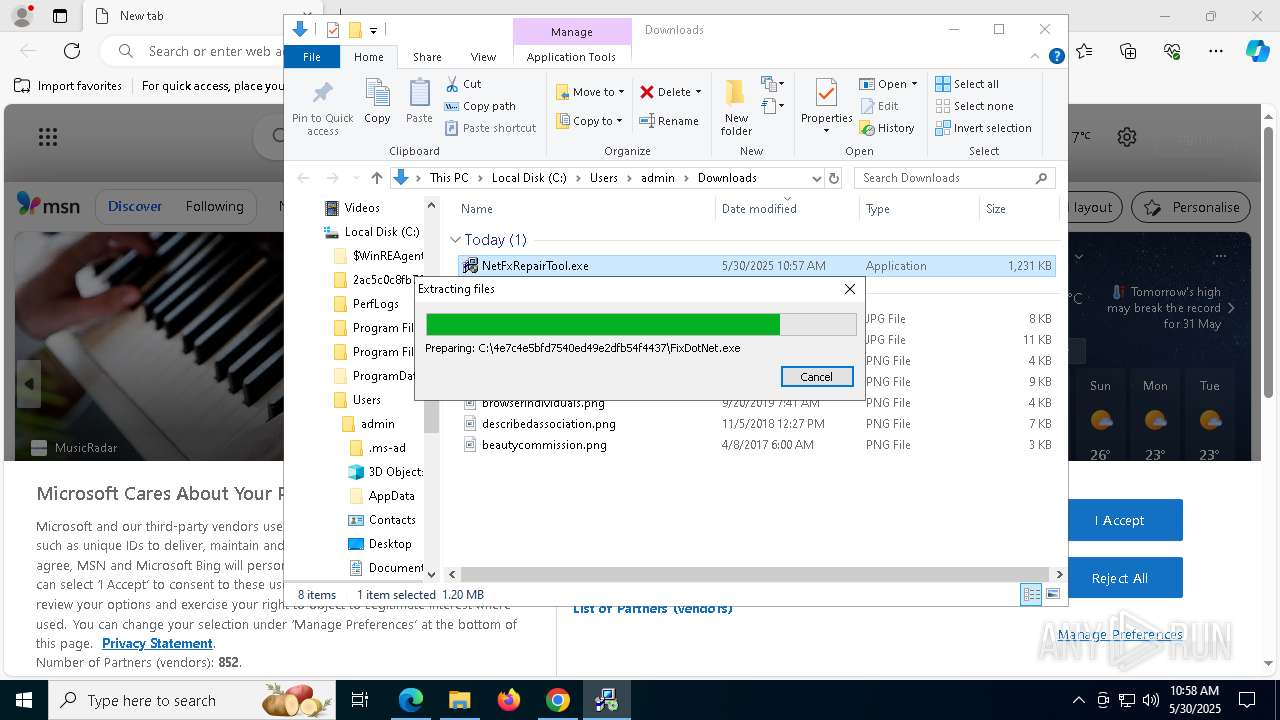
Executable content was dropped or overwritten
- NetFxRepairTool.exe (PID: 7728)
- NetFxRepairTool.exe (PID: 7784)
Process drops legitimate windows executable
- NetFxRepairTool.exe (PID: 7728)
- NetFxRepairTool.exe (PID: 7784)
- chrome.exe (PID: 6620)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 6620)
Application launched itself
- chrome.exe (PID: 6620)
- msedge.exe (PID: 3332)
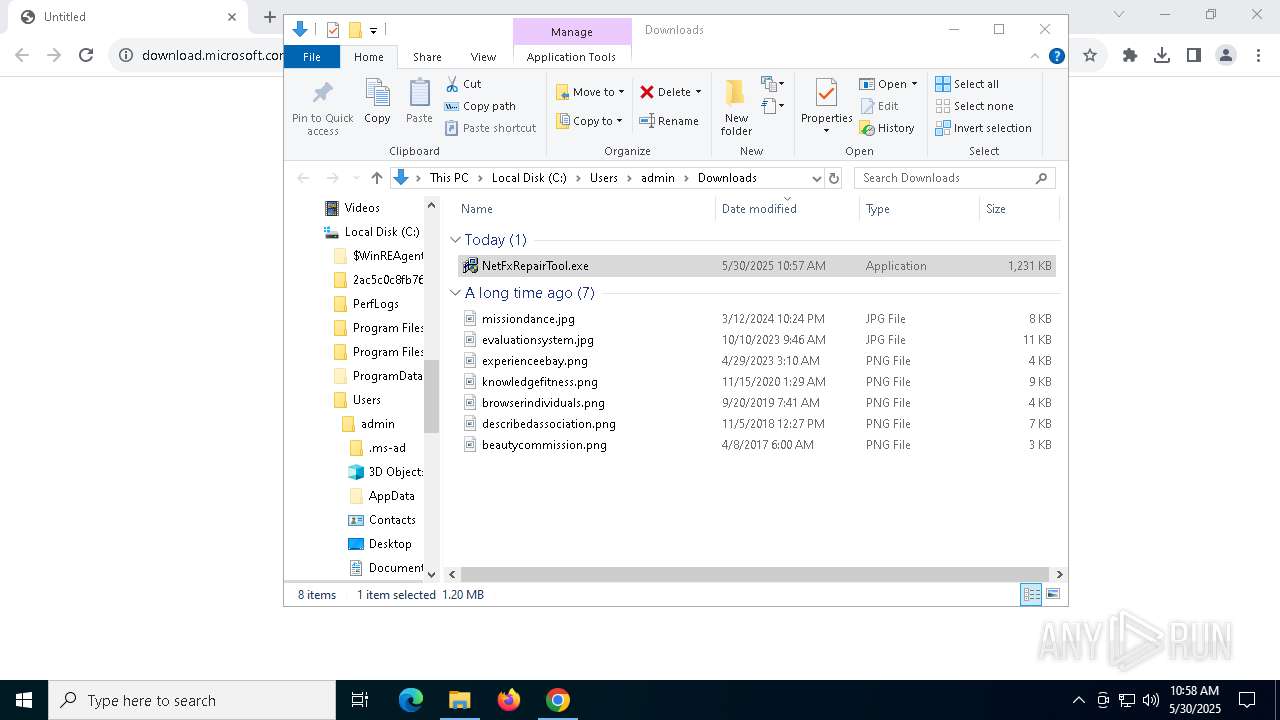
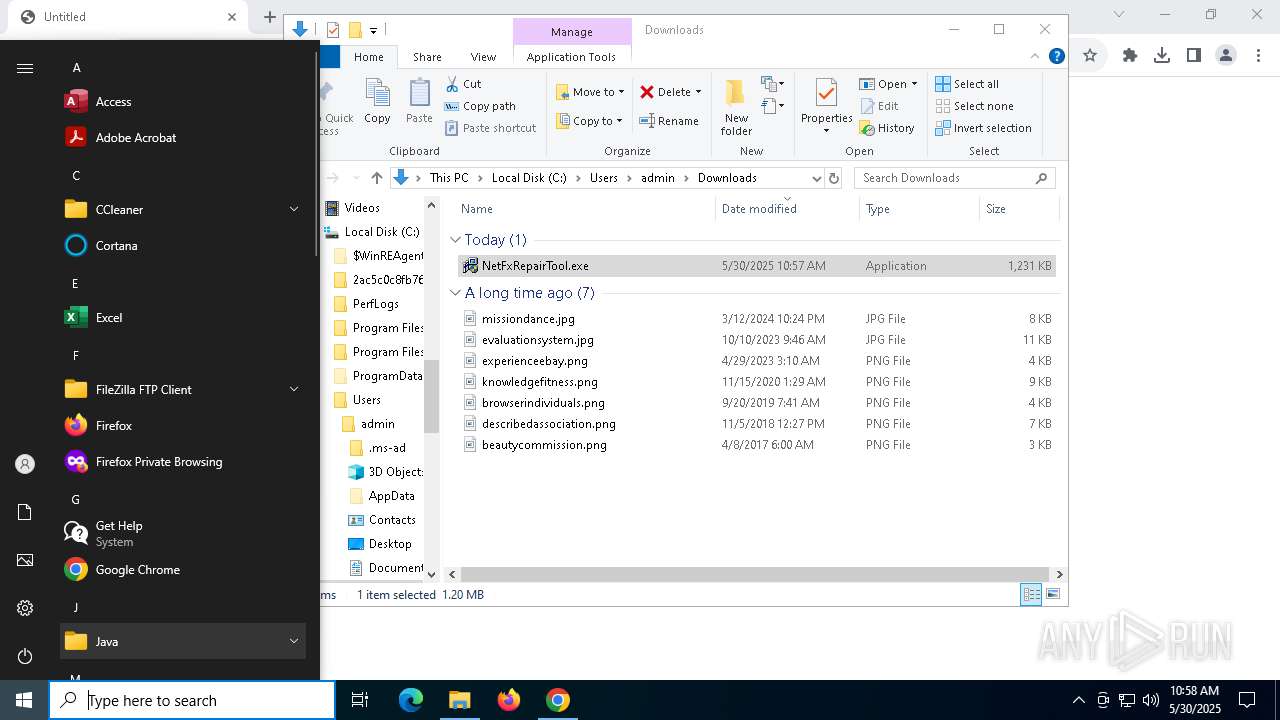
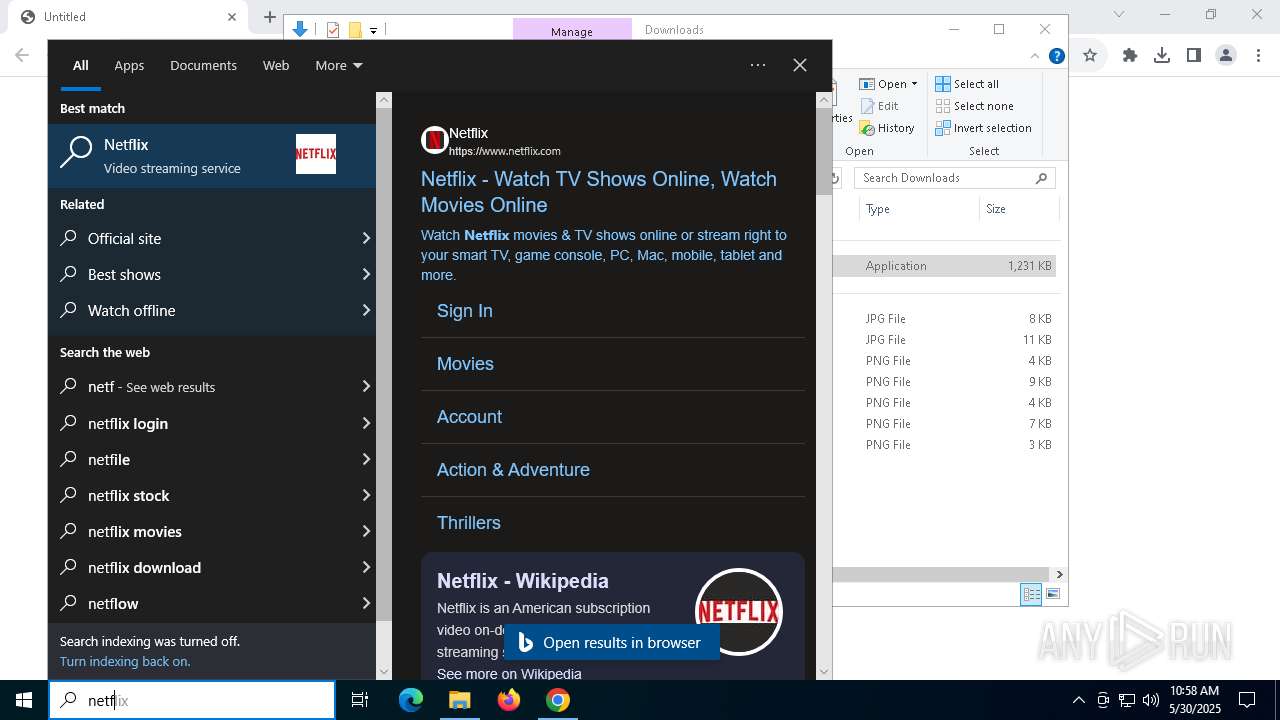
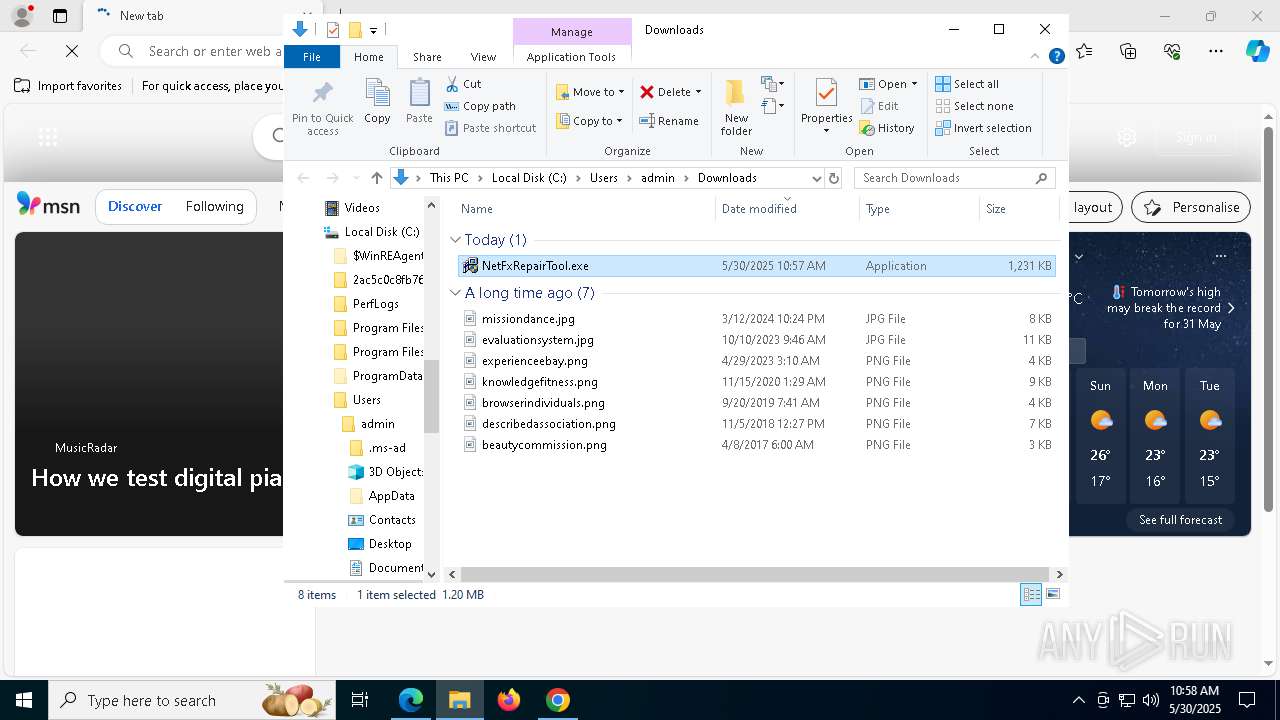
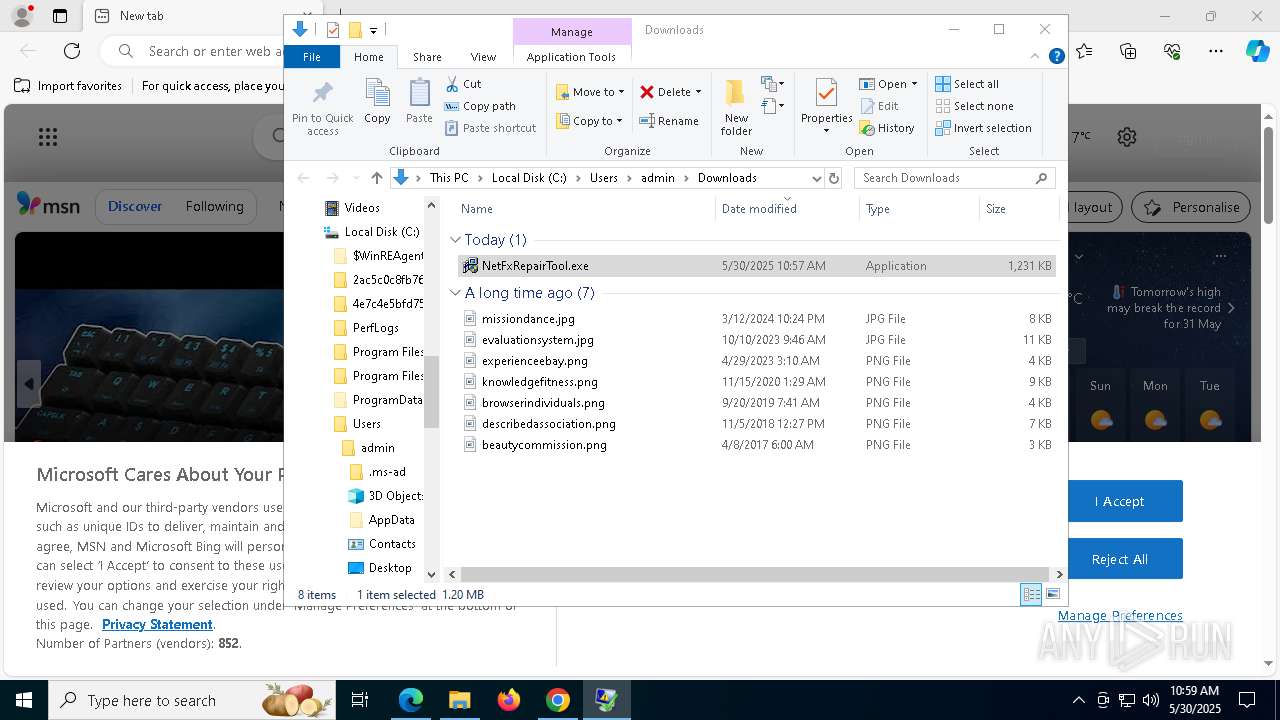
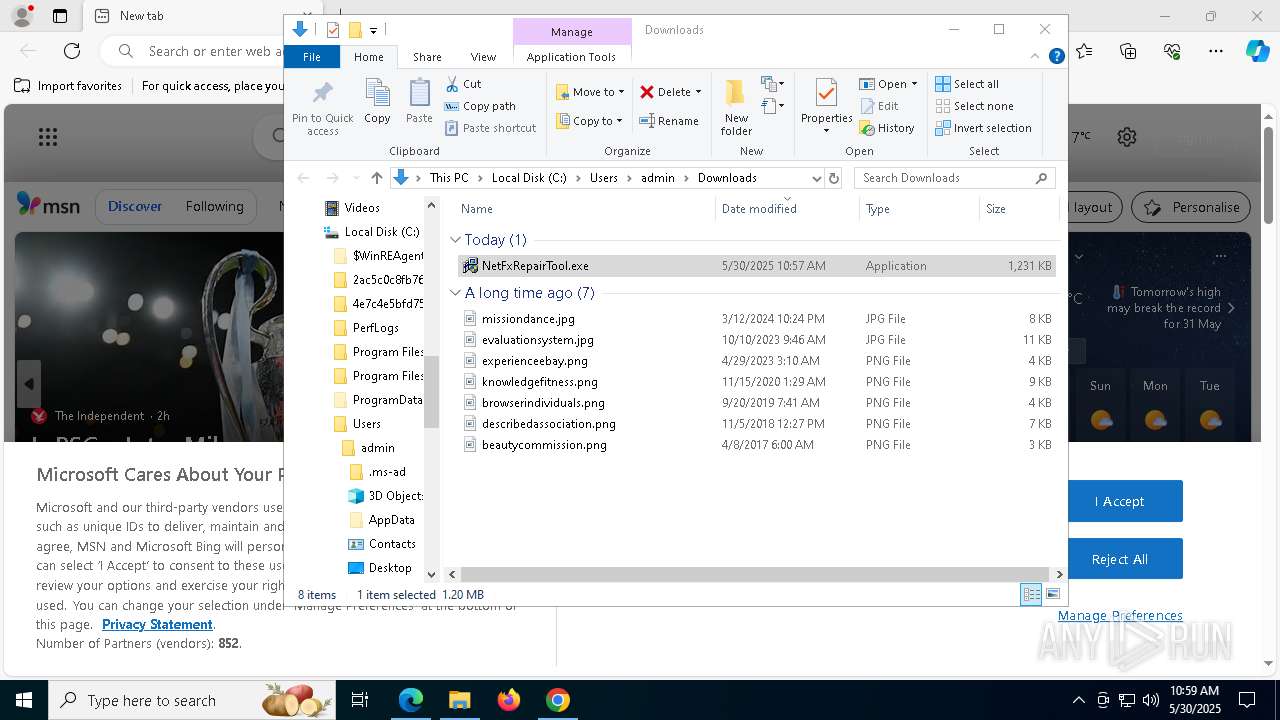
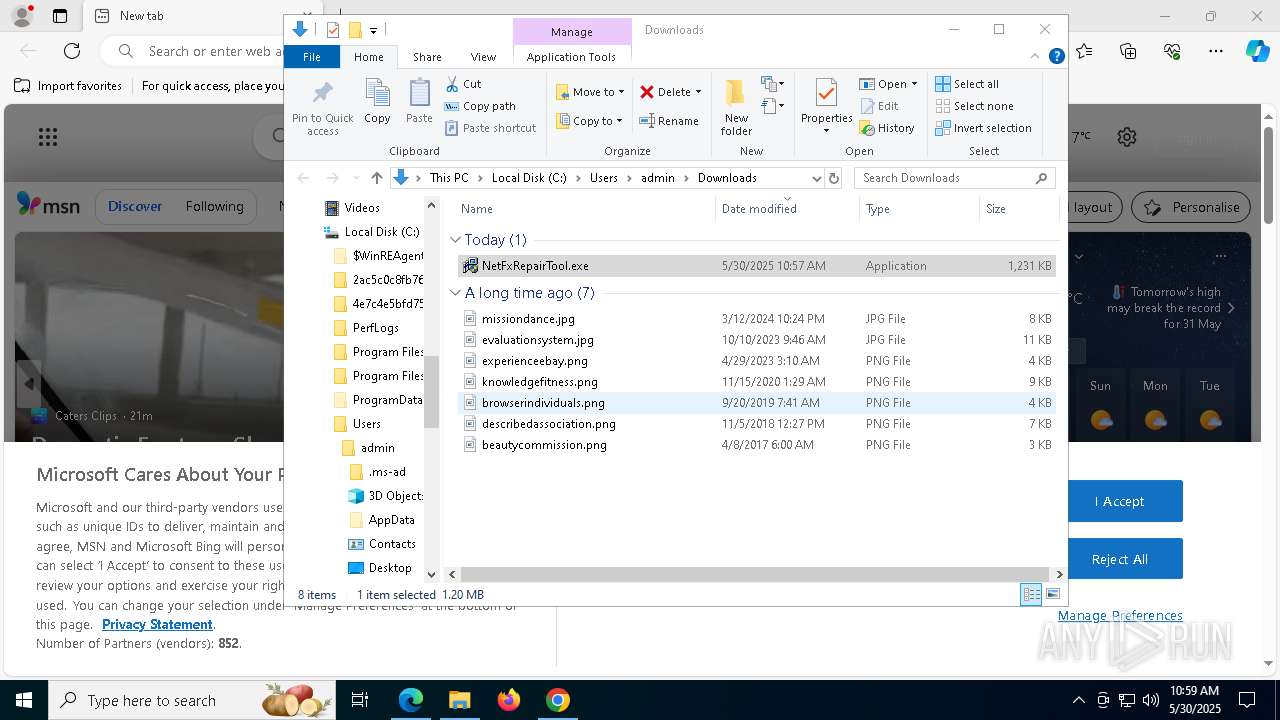
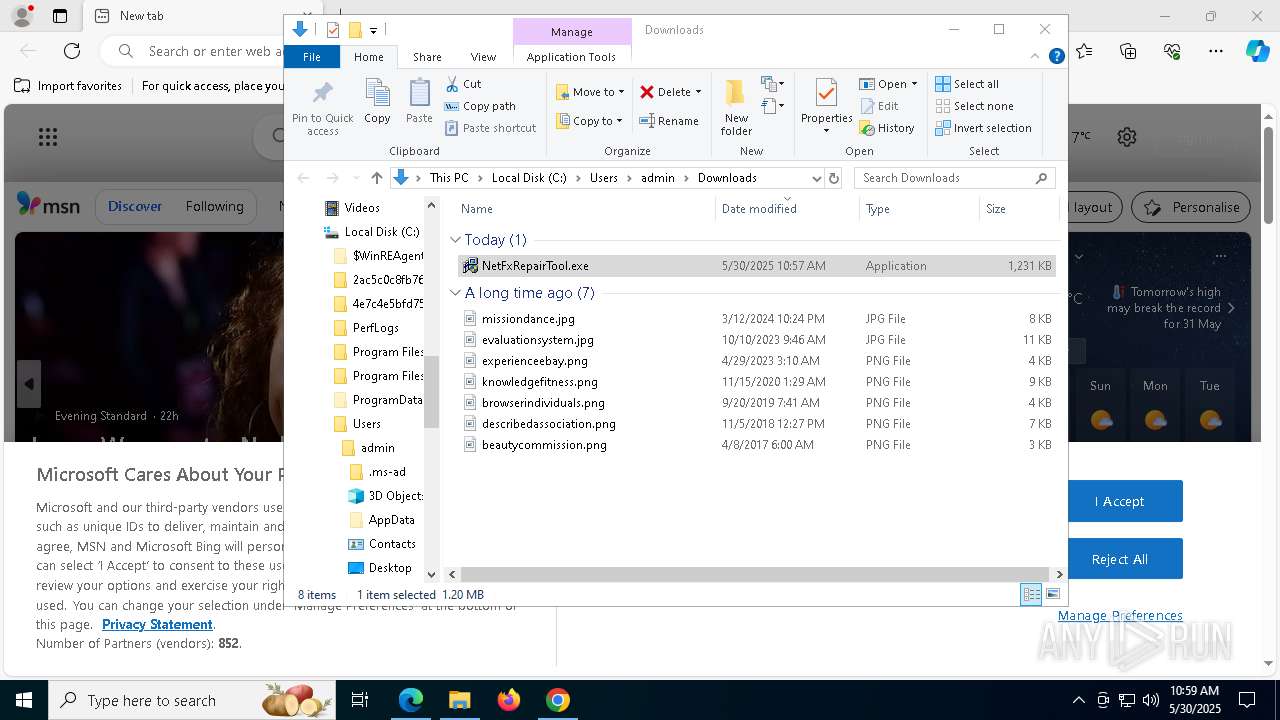
Launch of the file from Downloads directory
- chrome.exe (PID: 6620)
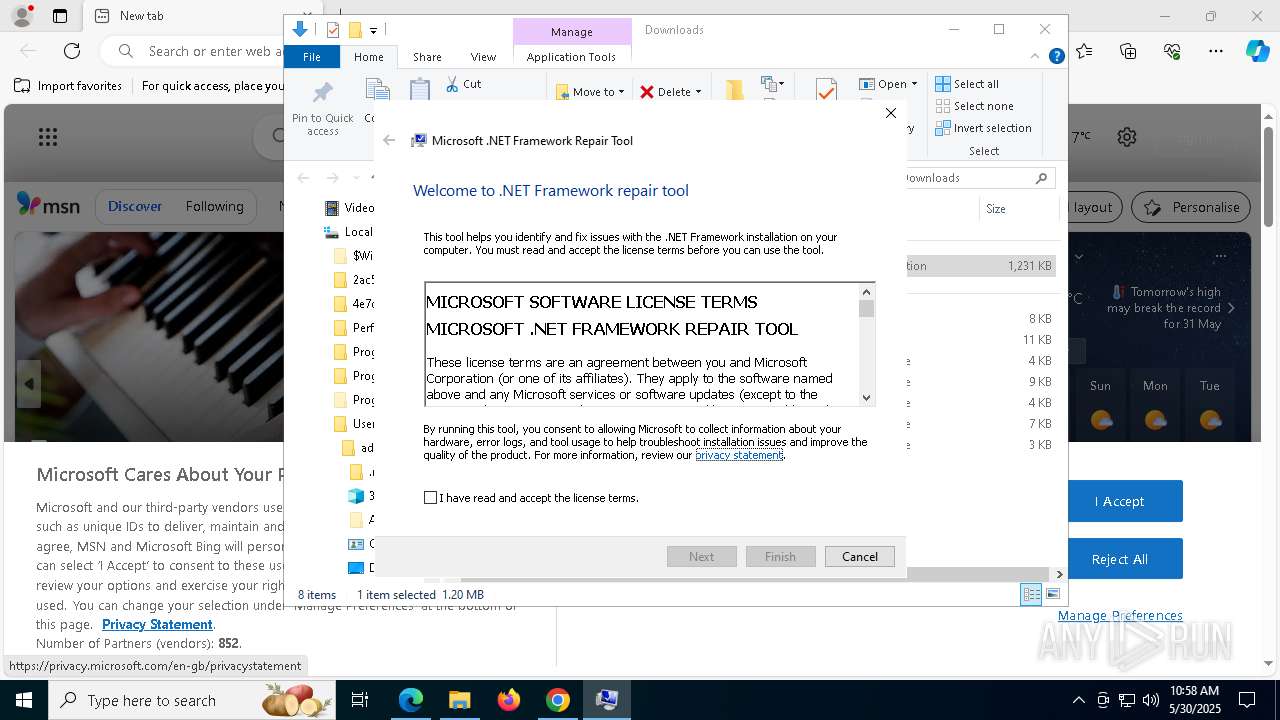
Checks supported languages
- NetFxRepairTool.exe (PID: 7728)
- msiexec.exe (PID: 5588)
- FixDotNet.exe (PID: 2560)
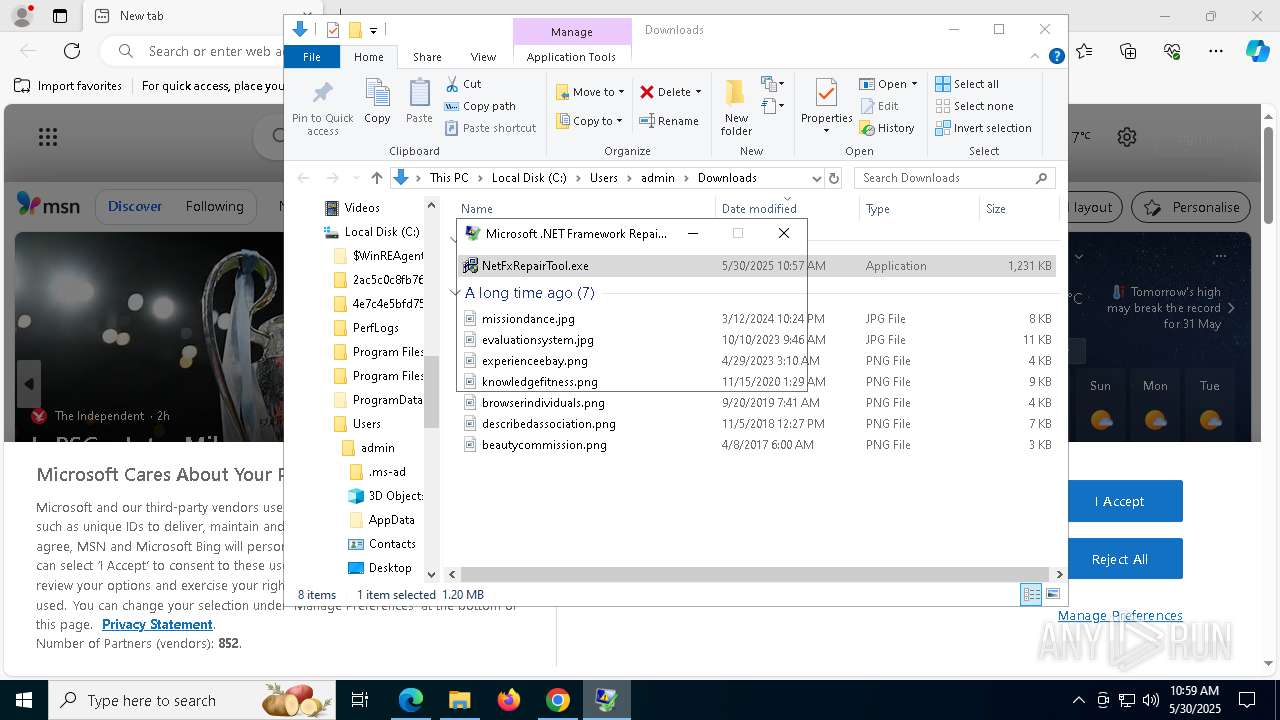
Manual execution by a user
- NetFxRepairTool.exe (PID: 7804)
- NetFxRepairTool.exe (PID: 7452)
- msedge.exe (PID: 3332)
- NetFxRepairTool.exe (PID: 7784)
- NetFxRepairTool.exe (PID: 7728)
Reads the computer name
- NetFxRepairTool.exe (PID: 7728)
- FixDotNet.exe (PID: 2560)
- msiexec.exe (PID: 5588)
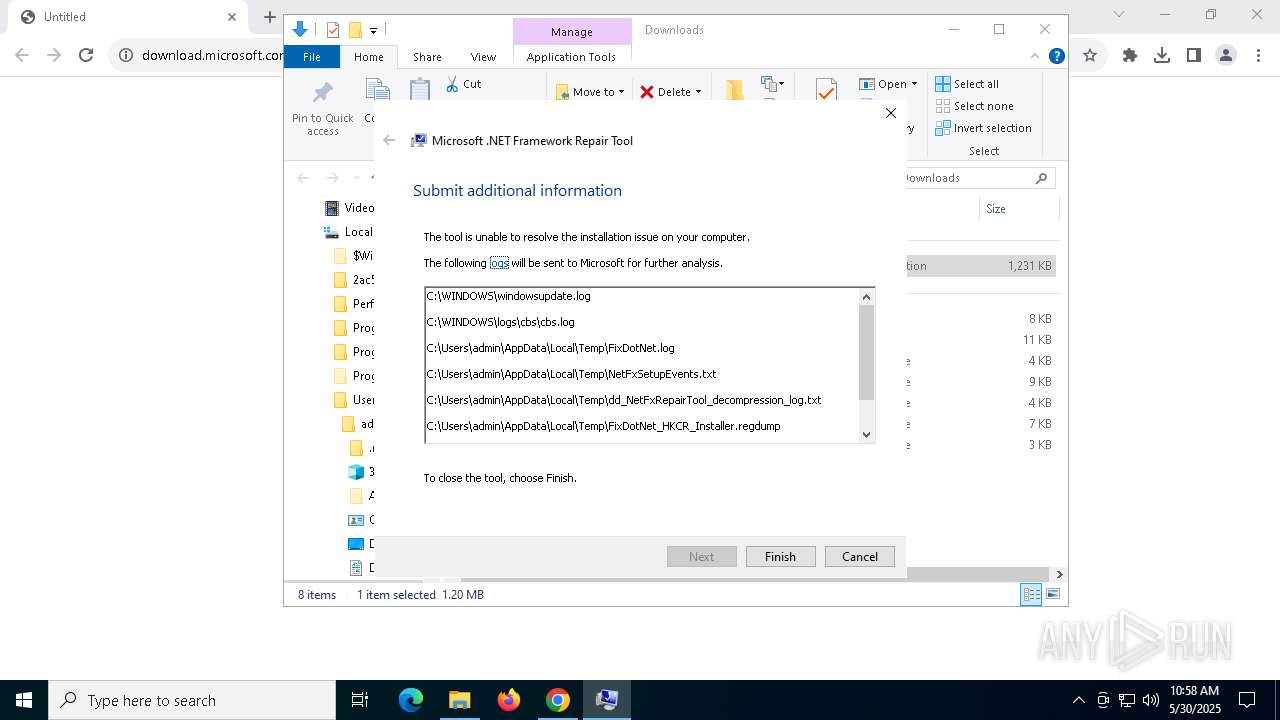
Create files in a temporary directory
- NetFxRepairTool.exe (PID: 7728)
- FixDotNet.exe (PID: 2560)
The sample compiled with english language support
- NetFxRepairTool.exe (PID: 7728)
- NetFxRepairTool.exe (PID: 7784)
- chrome.exe (PID: 6620)
Reads the machine GUID from the registry
- NetFxRepairTool.exe (PID: 7728)
- FixDotNet.exe (PID: 2560)
Creates files in the program directory
- FixDotNet.exe (PID: 2560)
Process checks computer location settings
- FixDotNet.exe (PID: 2560)
Reads the software policy settings
- wermgr.exe (PID: 2268)
- slui.exe (PID: 7932)
Creates files or folders in the user directory
- wermgr.exe (PID: 2268)
Checks proxy server information
- wermgr.exe (PID: 2268)
Reads Environment values
- FixDotNet.exe (PID: 2560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
210
Monitored processes
69
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6680 --field-trial-handle=2368,i,10833302987036239257,17259145638261440666,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6396 --field-trial-handle=2368,i,10833302987036239257,17259145638261440666,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1004 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6664 --field-trial-handle=2368,i,10833302987036239257,17259145638261440666,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6480 --field-trial-handle=2368,i,10833302987036239257,17259145638261440666,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1616 | C:\WINDOWS\system32\msiexec.exe /unreg | C:\Windows\System32\msiexec.exe | — | FixDotNet.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1912 | C:\WINDOWS\system32\msiexec.exe /regserver | C:\Windows\System32\msiexec.exe | — | FixDotNet.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "2560" "1228" "1176" "1240" "0" "0" "0" "0" "0" "0" "0" "0" | C:\Windows\SysWOW64\wermgr.exe | FixDotNet.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5328 --field-trial-handle=1856,i,72949376079482937,13505445457925673066,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2560 | C:\2ac5c0c8fb7674a50c68a2\FixDotNet.exe | C:\2ac5c0c8fb7674a50c68a2\FixDotNet.exe | — | NetFxRepairTool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework Repair Tool Exit code: 0 Version: 14.8.4072.0 built by: NET48REL1 Modules
| |||||||||||||||
| 3100 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6396 --field-trial-handle=2368,i,10833302987036239257,17259145638261440666,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
19 038
Read events
18 945
Write events
83
Delete events
10
Modification events
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000052AA55AA51D1DB01 | |||
| (PID) Process: | (2560) FixDotNet.exe | Key: | \REGISTRY\A\{d992798f-f68b-c22b-b2ae-940dd107af81}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (2560) FixDotNet.exe | Key: | \REGISTRY\A\{d992798f-f68b-c22b-b2ae-940dd107af81}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2560) FixDotNet.exe | Key: | \REGISTRY\A\{d992798f-f68b-c22b-b2ae-940dd107af81}\Root\InventoryApplicationFile\fixdotnet.exe|b102dfa87454ec16 |
| Operation: | write | Name: | ProgramId |
Value: 0006d6ee62214fe9042dc089ab66c86daaf100000904 | |||
| (PID) Process: | (2560) FixDotNet.exe | Key: | \REGISTRY\A\{d992798f-f68b-c22b-b2ae-940dd107af81}\Root\InventoryApplicationFile\fixdotnet.exe|b102dfa87454ec16 |
| Operation: | write | Name: | FileId |
Value: 0000da39a3ee5e6b4b0d3255bfef95601890afd80709 | |||
Executable files
42
Suspicious files
500
Text files
143
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c15e.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c15e.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c15e.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c15e.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c15e.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c16d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
91
DNS requests
89
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7736 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7736 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2268 | wermgr.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2268 | wermgr.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4408 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
4408 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
4408 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6620 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7300 | chrome.exe | 23.58.110.83:443 | download.microsoft.com | AKAMAI-AS | IN | whitelisted |
7300 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7300 | chrome.exe | 142.250.186.78:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
download.microsoft.com |
| whitelisted |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8172 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
8172 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
8172 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
8172 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
8172 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
8172 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |