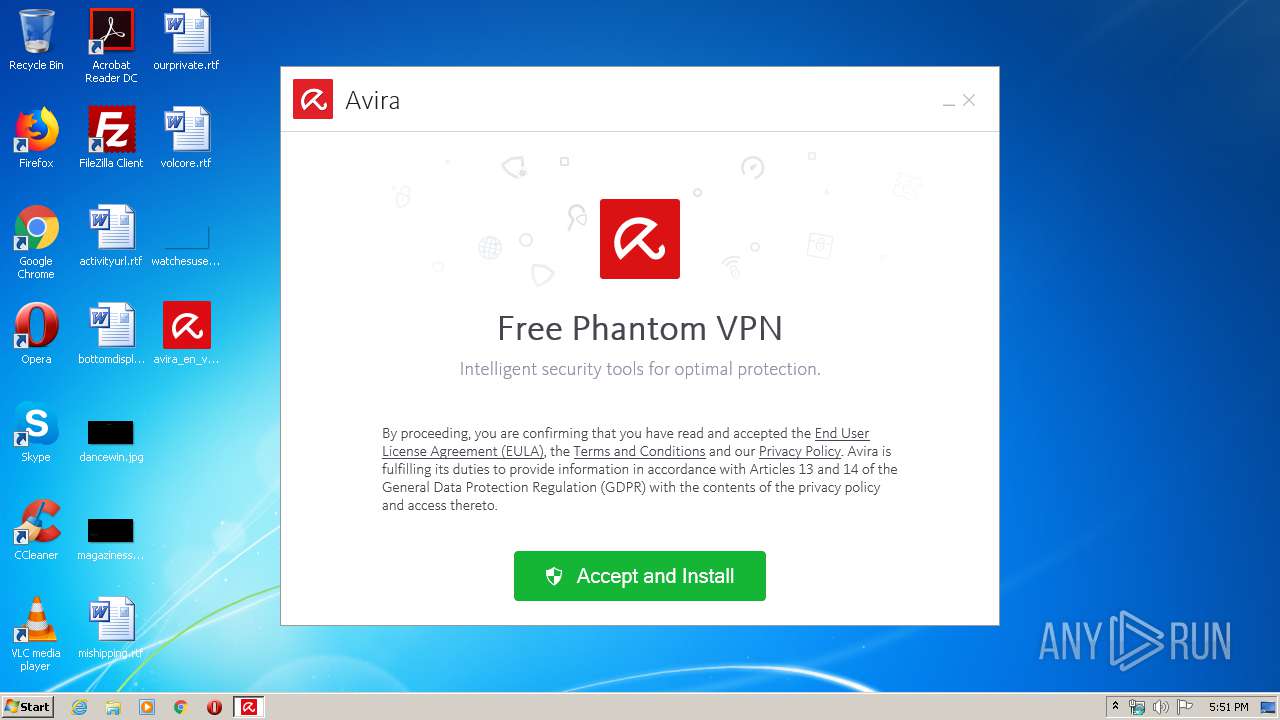
| File name: | avira_en_vpnb0___pvpnws.exe |
| Full analysis: | https://app.any.run/tasks/d07e1d66-1ca4-4590-a30d-e422aa38da3e |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 16:50:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 60395DE4A177237F92584433B9E1EF18 |
| SHA1: | 15BCAB4D1198F50BF148993DB8D86F9182B219D1 |
| SHA256: | 956180895B6E50747B905E98718618C87A9A5007C582EAD563A37A53EB57D9B7 |
| SSDEEP: | 196608:4hfUU8Z9Z0/v6YC83CzZ+pC+JDsKlbpP43:4RUjzZ0/v68OgpjZsgV43 |
MALICIOUS
Application was dropped or rewritten from another process
- avira_en_vpnb0___pvpnws.exe (PID: 3052)
- Avira.OE.Setup.Bundle.exe (PID: 1800)
- Avira.OE.Setup.Prerequisites.exe (PID: 1920)
- Avira.OE.Setup.Prerequisites.exe (PID: 3808)
- Avira.ServiceHost.exe (PID: 2988)
- Avira.Systray.exe (PID: 4040)
- Avira.Systray.exe (PID: 3376)
Loads dropped or rewritten executable
- avira_en_vpnb0___pvpnws.exe (PID: 3052)
- rundll32.exe (PID: 2844)
- rundll32.exe (PID: 3376)
- rundll32.exe (PID: 2092)
- rundll32.exe (PID: 3720)
- rundll32.exe (PID: 3168)
- rundll32.exe (PID: 3804)
- rundll32.exe (PID: 1920)
- rundll32.exe (PID: 3072)
- rundll32.exe (PID: 3528)
- rundll32.exe (PID: 2636)
- rundll32.exe (PID: 3728)
- rundll32.exe (PID: 3760)
- rundll32.exe (PID: 3068)
- rundll32.exe (PID: 1248)
- rundll32.exe (PID: 1268)
- Avira.Systray.exe (PID: 4040)
- Avira.ServiceHost.exe (PID: 2988)
- rundll32.exe (PID: 2348)
- Avira.Systray.exe (PID: 3376)
- rundll32.exe (PID: 3040)
- rundll32.exe (PID: 1456)
Changes the autorun value in the registry
- Avira.OE.Setup.Bundle.exe (PID: 1800)
Uses Task Scheduler to run other applications
- MsiExec.exe (PID: 2948)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 272)
Changes settings of System certificates
- Avira.ServiceHost.exe (PID: 2988)
- rundll32.exe (PID: 3168)
SUSPICIOUS
Reads Internet Cache Settings
- avira_en_vpnb0___pvpnws.exe (PID: 3052)
Changes IE settings (feature browser emulation)
- avira_en_vpnb0___pvpnws.exe (PID: 3052)
- Avira.Systray.exe (PID: 4040)
- Avira.Systray.exe (PID: 3376)
Executable content was dropped or overwritten
- avira_en_vpnb0___pvpnws.exe (PID: 2828)
- avira_en_vpnb0___pvpnws.exe (PID: 3052)
- Avira.OE.Setup.Bundle.exe (PID: 1800)
- rundll32.exe (PID: 2844)
- rundll32.exe (PID: 3376)
- rundll32.exe (PID: 3168)
- rundll32.exe (PID: 3072)
- msiexec.exe (PID: 3076)
- rundll32.exe (PID: 3528)
- rundll32.exe (PID: 1248)
- rundll32.exe (PID: 1268)
- rundll32.exe (PID: 1456)
Reads internet explorer settings
- avira_en_vpnb0___pvpnws.exe (PID: 3052)
Starts itself from another location
- avira_en_vpnb0___pvpnws.exe (PID: 3052)
Creates files in the program directory
- Avira.OE.Setup.Bundle.exe (PID: 1800)
- rundll32.exe (PID: 3720)
- rundll32.exe (PID: 3528)
- rundll32.exe (PID: 1268)
- Avira.ServiceHost.exe (PID: 2988)
Creates a software uninstall entry
- Avira.OE.Setup.Bundle.exe (PID: 1800)
- rundll32.exe (PID: 3072)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 2948)
Changes the autorun value in the registry
- msiexec.exe (PID: 3076)
Executed as Windows Service
- Avira.ServiceHost.exe (PID: 2988)
Reads Environment values
- Avira.ServiceHost.exe (PID: 2988)
Reads the cookies of Google Chrome
- Avira.ServiceHost.exe (PID: 2988)
Reads the cookies of Mozilla Firefox
- Avira.ServiceHost.exe (PID: 2988)
Removes files from Windows directory
- Avira.ServiceHost.exe (PID: 2988)
Creates files in the Windows directory
- Avira.ServiceHost.exe (PID: 2988)
Creates files in the user directory
- Avira.ServiceHost.exe (PID: 2988)
Adds / modifies Windows certificates
- rundll32.exe (PID: 3168)
- Avira.ServiceHost.exe (PID: 2988)
Searches for installed software
- Avira.ServiceHost.exe (PID: 2988)
INFO
Application launched itself
- msiexec.exe (PID: 3076)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2948)
- msiexec.exe (PID: 3076)
- MsiExec.exe (PID: 2644)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3076)
Creates a software uninstall entry
- msiexec.exe (PID: 3076)
Reads settings of System Certificates
- Avira.ServiceHost.exe (PID: 2988)
- rundll32.exe (PID: 3168)
Creates files in the program directory
- msiexec.exe (PID: 3076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:26 17:49:16+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 288768 |
| InitializedDataSize: | 306176 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x37f09 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.144.30330 |
| ProductVersionNumber: | 1.2.144.30330 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Avira Operations GmbH & Co. KG |
| FileDescription: | Avira |
| FileVersion: | 1.2.144.30330 |
| InternalName: | setup |
| LegalCopyright: | Copyright © 2019 Avira Operations GmbH & Co. KG and its Licensors |
| OriginalFileName: | Avira.OE.Setup.Bundle.exe |
| ProductName: | Avira |
| ProductVersion: | 1.2.144.30330 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Feb-2020 16:49:16 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Avira Operations GmbH & Co. KG |
| FileDescription: | Avira |
| FileVersion: | 1.2.144.30330 |
| InternalName: | setup |
| LegalCopyright: | Copyright © 2019 Avira Operations GmbH & Co. KG and its Licensors |
| OriginalFilename: | Avira.OE.Setup.Bundle.exe |
| ProductName: | Avira |
| ProductVersion: | 1.2.144.30330 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 26-Feb-2020 16:49:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004660E | 0x00046800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54363 |
.rdata | 0x00048000 | 0x0001D86C | 0x0001DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.93956 |
.data | 0x00066000 | 0x000035E0 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.58198 |
.wixburn8 | 0x0006A000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.742974 |
.tls | 0x0006B000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0006C000 | 0x00027610 | 0x00027800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.55843 |
.reloc | 0x00094000 | 0x00003E3C | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.73 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.39986 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.49457 | 38056 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.65675 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.80124 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.07284 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.46786 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.88962 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll (delay-loaded) |
ole32.dll |
Total processes
73
Monitored processes
30
Malicious processes
24
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Windows\system32\schtasks.exe" /Delete /TN "Avira SystrayStartTrigger" /F | C:\Windows\system32\schtasks.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | rundll32.exe "C:\Windows\Installer\MSIEE5C.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_10940000 201 Avira.OE.Setup.CustomActions!Avira.OE.Setup.CustomActions.DesktopShortcut.CreateDesktopShortcut | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1268 | rundll32.exe "C:\Windows\Installer\MSIF40A.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_10941421 208 Avira.OE.Setup.CustomActions!Avira.OE.Setup.CustomActions.DesktopShortcut.CreateStartMenuShortcut | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1456 | rundll32.exe "C:\Windows\Installer\MSI258E.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_10954109 233 Avira.OE.Setup.CustomActions!Avira.OE.Setup.CustomActions.InstallFinalization.WaitUntilLauncherIsReady | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1800 | "C:\Users\admin\AppData\Local\Temp\{9F05649F-F2BB-4812-B6A5-73D69B3BF7A1}\.be\Avira.OE.Setup.Bundle.exe" -q -burn.elevated BurnPipe.{23D49202-E153-4EA2-8681-521C0293319A} {24AEAE96-D177-47D9-9B04-DF9E3F0381F6} 3052 | C:\Users\admin\AppData\Local\Temp\{9F05649F-F2BB-4812-B6A5-73D69B3BF7A1}\.be\Avira.OE.Setup.Bundle.exe | avira_en_vpnb0___pvpnws.exe | ||||||||||||
User: admin Company: Avira Operations GmbH & Co. KG Integrity Level: HIGH Description: Avira Exit code: 0 Version: 1.2.144.30330 Modules
| |||||||||||||||
| 1920 | "C:\ProgramData\Package Cache\03728D13C6B8152C05F3C44FA7C264A9F4C5D751\Avira.OE.Setup.Prerequisites.exe" /enableMsiService /checkRebootRequired | C:\ProgramData\Package Cache\03728D13C6B8152C05F3C44FA7C264A9F4C5D751\Avira.OE.Setup.Prerequisites.exe | — | Avira.OE.Setup.Bundle.exe | |||||||||||
User: admin Company: Avira Operations GmbH & Co. KG Integrity Level: HIGH Description: Avira.OE.Setup.Prerequisites Exit code: 0 Version: 1.2.144.30330 Modules
| |||||||||||||||
| 1920 | rundll32.exe "C:\Windows\Installer\MSID353.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_10933062 118 Avira.OE.Setup.CustomActions!Avira.OE.Setup.CustomActions.Configuration.SetTrackingId | C:\Windows\system32\rundll32.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2092 | rundll32.exe "C:\Windows\Installer\MSIC0CB.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_10928328 13 Avira.OE.Setup.CustomActions!Avira.OE.Setup.CustomActions.Migration.MigrateSettingsFile | C:\Windows\system32\rundll32.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2348 | rundll32.exe "C:\Windows\Installer\MSI21A3.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_10953109 215 Avira.OE.Setup.CustomActions!Avira.OE.Setup.CustomActions.StorageFilesAccess.SetStorageFilesAccess | C:\Windows\system32\rundll32.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2636 | rundll32.exe "C:\Windows\Installer\MSIE120.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_10936593 132 Avira.OE.Setup.CustomActions!Avira.OE.Setup.CustomActions.HtmlUiCustomActions.FixCssClassContentType | C:\Windows\system32\rundll32.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 546
Read events
1 881
Write events
1 654
Delete events
11
Modification events
| (PID) Process: | (3052) avira_en_vpnb0___pvpnws.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3052) avira_en_vpnb0___pvpnws.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3052) avira_en_vpnb0___pvpnws.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3052) avira_en_vpnb0___pvpnws.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3052) avira_en_vpnb0___pvpnws.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3052) avira_en_vpnb0___pvpnws.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3052) avira_en_vpnb0___pvpnws.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3052) avira_en_vpnb0___pvpnws.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3052) avira_en_vpnb0___pvpnws.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | avira_en_vpnb0___pvpnws.exe |
Value: 11001 | |||
| (PID) Process: | (1800) Avira.OE.Setup.Bundle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{7ff7e40a-a321-45a2-a6d4-2ab2ae8ce908} |
| Operation: | write | Name: | BundleCachePath |
Value: C:\ProgramData\Package Cache\{7ff7e40a-a321-45a2-a6d4-2ab2ae8ce908}\Avira.OE.Setup.Bundle.exe | |||
Executable files
152
Suspicious files
29
Text files
486
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3052 | avira_en_vpnb0___pvpnws.exe | C:\Users\admin\AppData\Local\Temp\{9F05649F-F2BB-4812-B6A5-73D69B3BF7A1}\.ba\WixStdBA.dll | executable | |
MD5:— | SHA256:— | |||
| 3052 | avira_en_vpnb0___pvpnws.exe | C:\Users\admin\AppData\Local\Temp\{9F05649F-F2BB-4812-B6A5-73D69B3BF7A1}\.ba\Avira.OE.Setup.InstallationCore.dll | executable | |
MD5:— | SHA256:— | |||
| 3052 | avira_en_vpnb0___pvpnws.exe | C:\Users\admin\AppData\Local\Temp\{9F05649F-F2BB-4812-B6A5-73D69B3BF7A1}\.ba\Ui\images\illustration_fss.png | image | |
MD5:F2D6D84DFDCA1507FE7BA84DDA886DD5 | SHA256:8B36218FB27E3931E8F7F465056C2CC84C6897D6A1B85F391352D765EAE0BDD8 | |||
| 3052 | avira_en_vpnb0___pvpnws.exe | C:\Users\admin\AppData\Local\Temp\{9F05649F-F2BB-4812-B6A5-73D69B3BF7A1}\.ba\Ui\fonts\KievitWeb-Light.woff | woff | |
MD5:A8A9D6AAF9F3940BADC66E2A2AA21047 | SHA256:A791ABA3842D3766494AD0AA2A1B9CDBD2BB8AA8B2235AEDEA82E993C851A1AB | |||
| 3052 | avira_en_vpnb0___pvpnws.exe | C:\Users\admin\AppData\Local\Temp\{9F05649F-F2BB-4812-B6A5-73D69B3BF7A1}\.ba\thm.xml | xml | |
MD5:EC0BDB2B232D6ACAD037CC13281CBD15 | SHA256:9AECD08839F1D3223188029DEBE49504D760314148EFFDA1520BCEE5CEA451F2 | |||
| 3052 | avira_en_vpnb0___pvpnws.exe | C:\Users\admin\AppData\Local\Temp\{9F05649F-F2BB-4812-B6A5-73D69B3BF7A1}\.ba\Ui\fonts\co-icon-font.eot | eot | |
MD5:DC7AF97FD125F09920BFBCF4E67A5779 | SHA256:FA3E72F29F73A8EE08FB6D2DD976AB9E2A91A7EF7470D0ED01B95742825FF55F | |||
| 3052 | avira_en_vpnb0___pvpnws.exe | C:\Users\admin\AppData\Local\Temp\{9F05649F-F2BB-4812-B6A5-73D69B3BF7A1}\.ba\Ui\scripts\main.js | text | |
MD5:B6E79CC5559A7D4AA15E607E6C9A4435 | SHA256:56EB30AD85DC6AC21258BF86DC38999B8EC181D6E695653605AFEE194C89A9E4 | |||
| 3052 | avira_en_vpnb0___pvpnws.exe | C:\Users\admin\AppData\Local\Temp\{9F05649F-F2BB-4812-B6A5-73D69B3BF7A1}\.ba\Ui\images\loading.ie8.gif | image | |
MD5:8039A24504716835C871673883E59820 | SHA256:362DEA985E7C5BDE02D65380C45CD37DB0CC5DDD10CD277D0E20B0E0C666FA9F | |||
| 3052 | avira_en_vpnb0___pvpnws.exe | C:\Users\admin\AppData\Local\Temp\{9F05649F-F2BB-4812-B6A5-73D69B3BF7A1}\.ba\Ui\scripts\jquery.min.js | text | |
MD5:F03E5A3BF534F4A738BC350631FD05BD | SHA256:AEC3D419D50F05781A96F223E18289AEB52598B5DB39BE82A7B71DC67D6A7947 | |||
| 3052 | avira_en_vpnb0___pvpnws.exe | C:\Users\admin\AppData\Local\Temp\{9F05649F-F2BB-4812-B6A5-73D69B3BF7A1}\.ba\Ui\images\mad.png | image | |
MD5:0CAEDA34B545EF1E40AE37CEBECB9845 | SHA256:62A9DFA30760763BE2BD3048F4DA0746D89EF5D780C96E91FCA8ADBE4F91906D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
7
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3052 | avira_en_vpnb0___pvpnws.exe | GET | 200 | 151.139.128.14:80 | http://crl.usertrust.com/AddTrustExternalCARoot.crl | US | der | 673 b | whitelisted |
3052 | avira_en_vpnb0___pvpnws.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEDaCXn%2B1pIGTfvbRc2u5PKY%3D | US | der | 727 b | whitelisted |
3052 | avira_en_vpnb0___pvpnws.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQLqIKj6Gi5thHaqKC1ECU9aXsCRQQUmvMr2s%2BtT7YvuypISCoStxtCwSQCEBLOxnPQyWHOCM2d3uZuQ04%3D | US | der | 471 b | whitelisted |
2988 | Avira.ServiceHost.exe | GET | 200 | 23.55.161.155:80 | http://www.msftncsi.com/ncsi.txt | US | text | 14 b | whitelisted |
2988 | Avira.ServiceHost.exe | GET | 200 | 23.55.161.155:80 | http://www.msftncsi.com/ncsi.txt | US | text | 14 b | whitelisted |
2988 | Avira.ServiceHost.exe | GET | 200 | 23.55.161.155:80 | http://www.msftncsi.com/ncsi.txt | US | text | 14 b | whitelisted |
2988 | Avira.ServiceHost.exe | GET | 200 | 23.55.161.155:80 | http://www.msftncsi.com/ncsi.txt | US | text | 14 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3052 | avira_en_vpnb0___pvpnws.exe | 18.196.112.115:443 | api.my.avira.com | Amazon.com, Inc. | DE | unknown |
3052 | avira_en_vpnb0___pvpnws.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
— | — | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
2988 | Avira.ServiceHost.exe | 18.153.6.21:443 | ssldev.oes.avira.com | — | US | unknown |
2988 | Avira.ServiceHost.exe | 23.55.161.155:80 | www.msftncsi.com | Akamai International B.V. | US | suspicious |
2988 | Avira.ServiceHost.exe | 130.211.34.183:443 | api.mixpanel.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.my.avira.com |
| unknown |
ocsp.usertrust.com |
| whitelisted |
crl.usertrust.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ssldev.oes.avira.com |
| unknown |
www.msftncsi.com |
| whitelisted |
api.mixpanel.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report