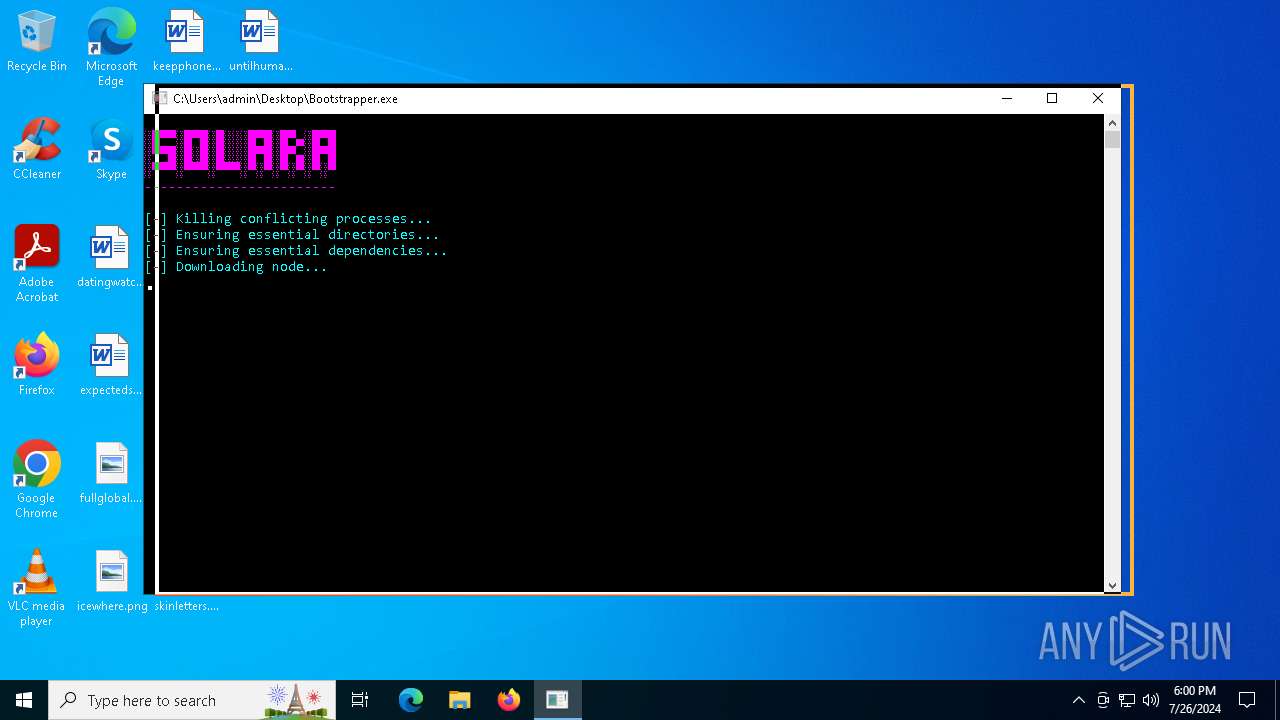
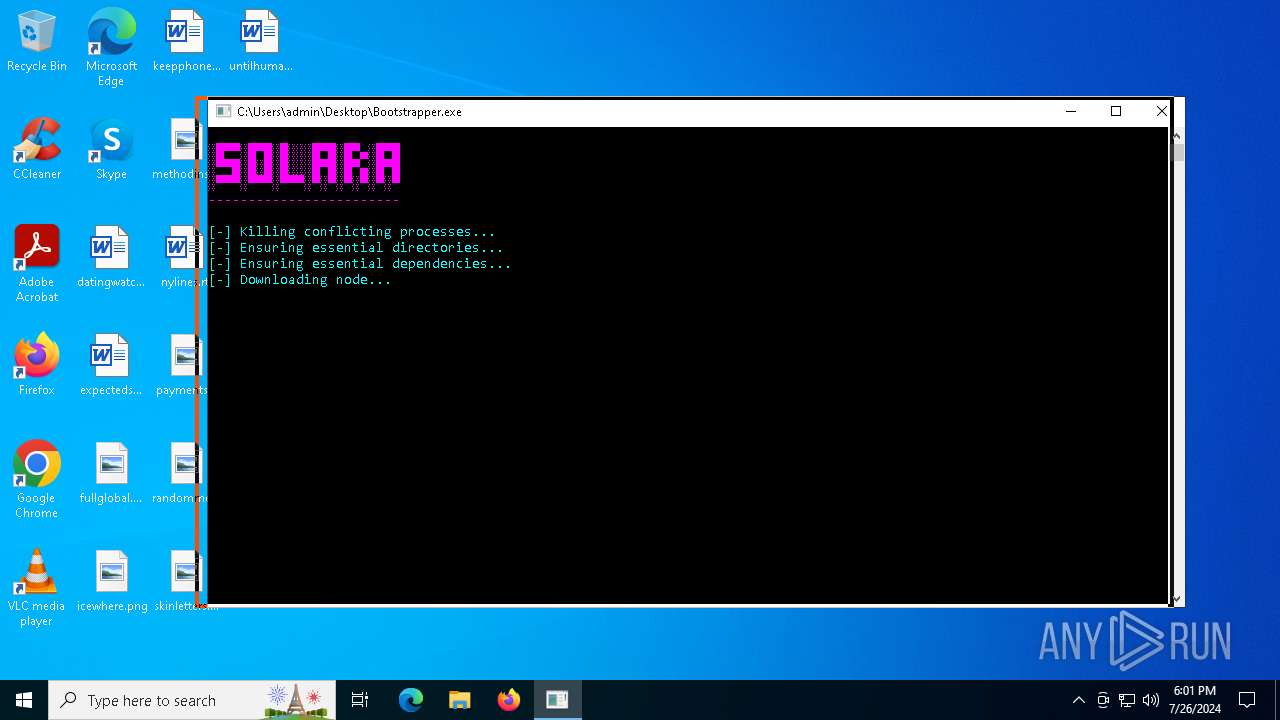
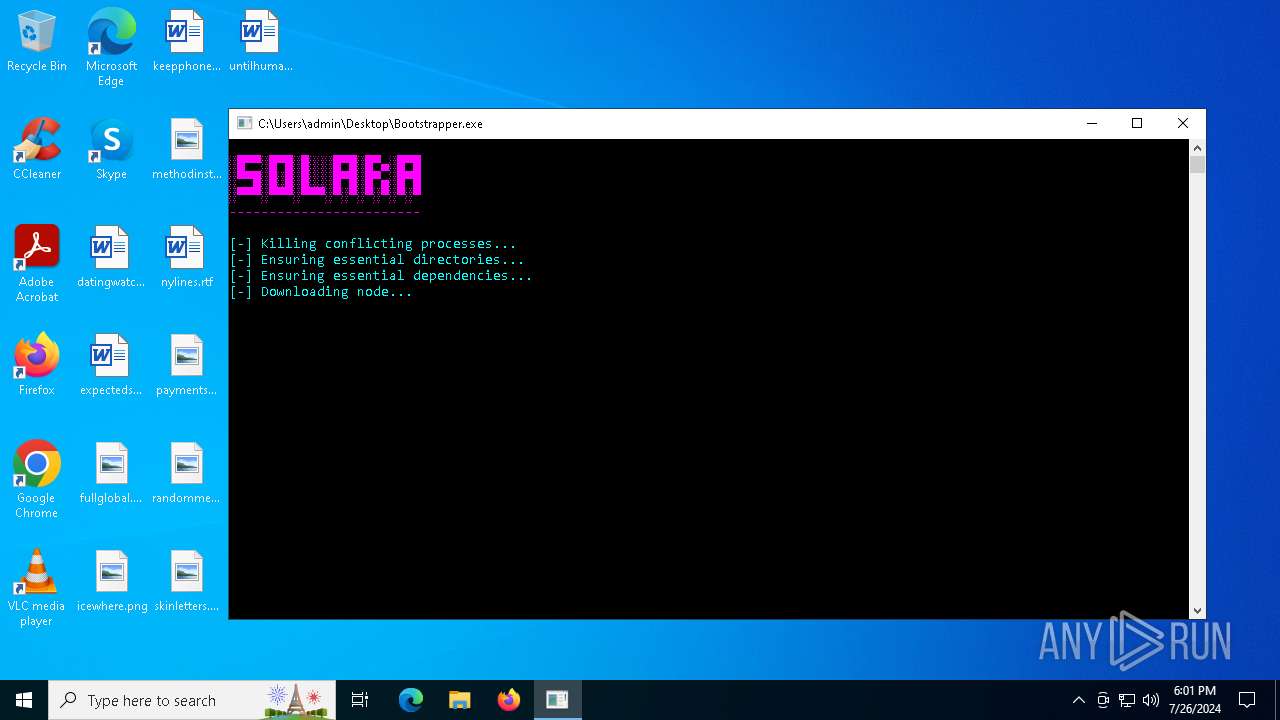
| download: | /cmd-softworks/solara/raw/main/Bootstrapper.exe |
| Full analysis: | https://app.any.run/tasks/2ef7271a-b868-4d23-900e-fdd2ae1e1c92 |
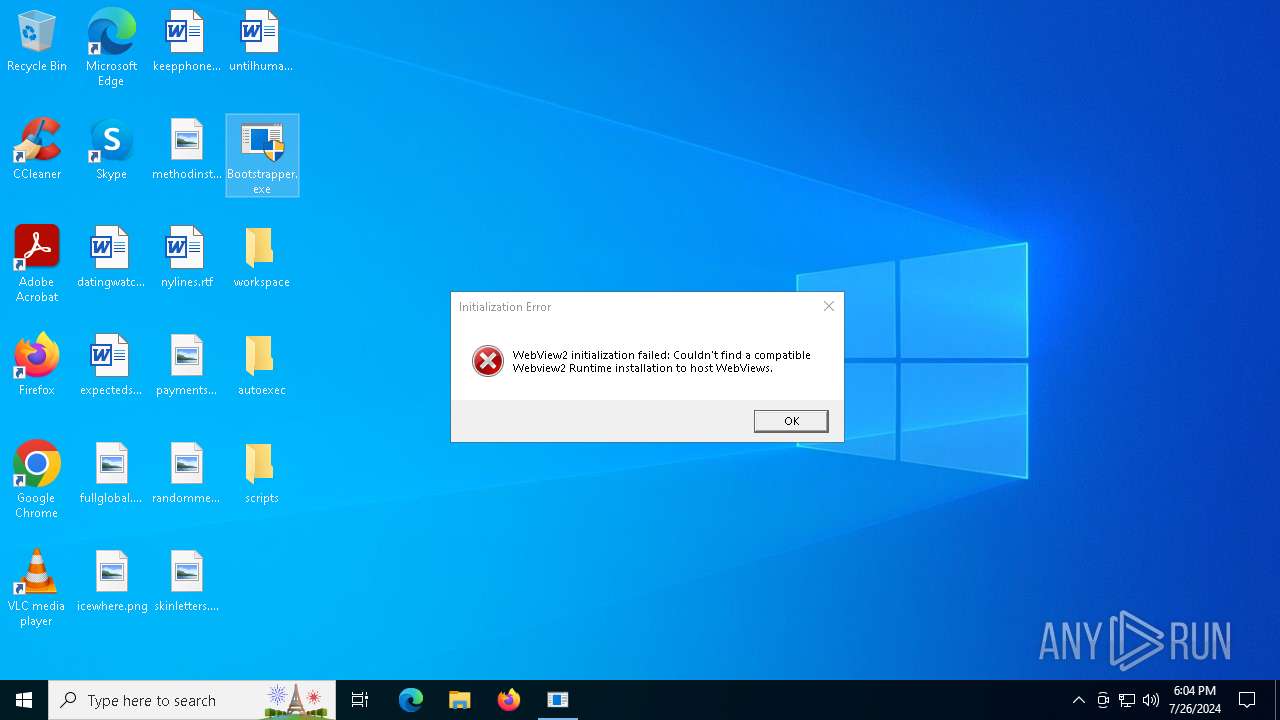
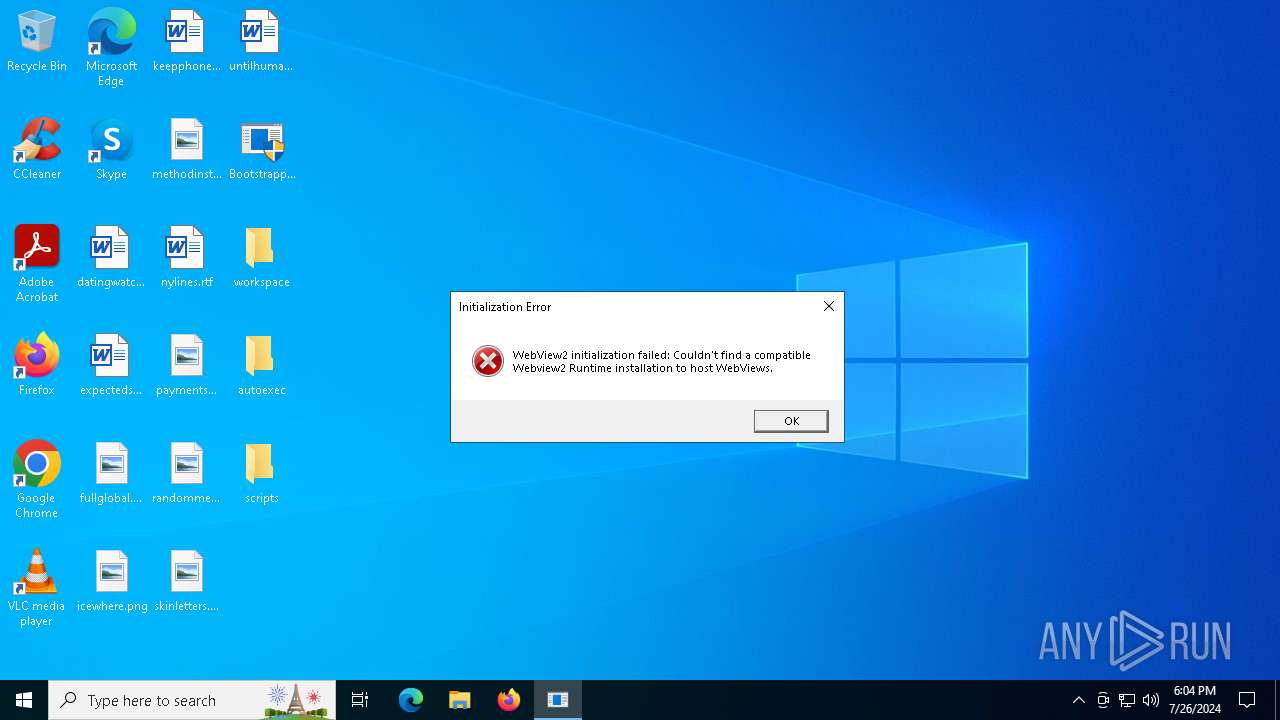
| Verdict: | Malicious activity |
| Analysis date: | July 26, 2024, 18:00:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | D674B62B359B2EC81398348904F8BEE9 |
| SHA1: | 609D29C3D5503BC382AB55188E67E002EB8270A7 |
| SHA256: | 95486D06DB5126EB557C563B5597E08B236634F75853A6491C485CB64CF28AE2 |
| SSDEEP: | 12288:M/YtlkXGfqKBwQjocHXhwZ0oRy7btb6U9Aubfh/dYl03n:M/VXGfqKB1jocHXhwgyubfh/dYl0 |
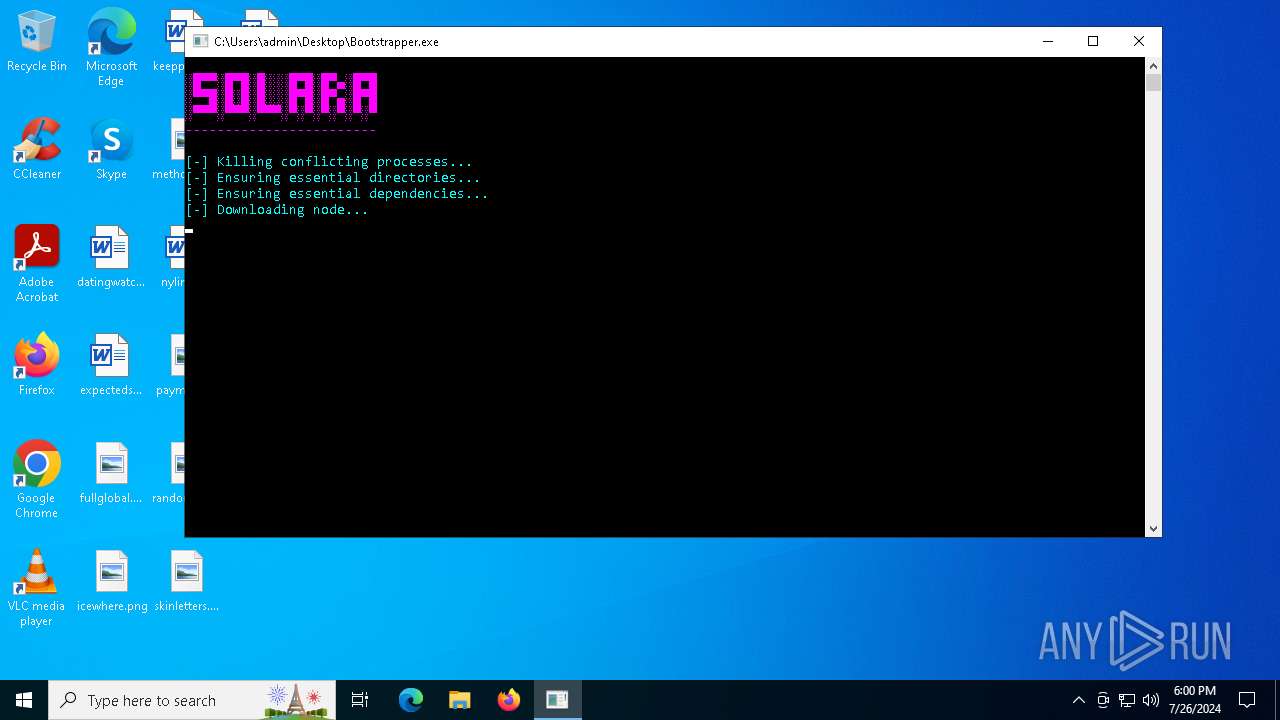
MALICIOUS
Drops the executable file immediately after the start
- Bootstrapper.exe (PID: 2508)
- msiexec.exe (PID: 3980)
SUSPICIOUS
Reads security settings of Internet Explorer
- Bootstrapper.exe (PID: 2508)
- msiexec.exe (PID: 6164)
- msiexec.exe (PID: 5396)
- Bootstrapper.exe (PID: 3816)
- Solara.exe (PID: 6124)
Reads the date of Windows installation
- Bootstrapper.exe (PID: 2508)
- Bootstrapper.exe (PID: 3816)
Checks Windows Trust Settings
- msiexec.exe (PID: 3980)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3980)
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- msiexec.exe (PID: 5396)
- wevtutil.exe (PID: 3720)
Executable content was dropped or overwritten
- Bootstrapper.exe (PID: 2508)
The process drops C-runtime libraries
- Bootstrapper.exe (PID: 2508)
Process drops legitimate windows executable
- Bootstrapper.exe (PID: 2508)
Reads the BIOS version
- Solara.exe (PID: 6124)
Executes script using NodeJS
- node.exe (PID: 6112)
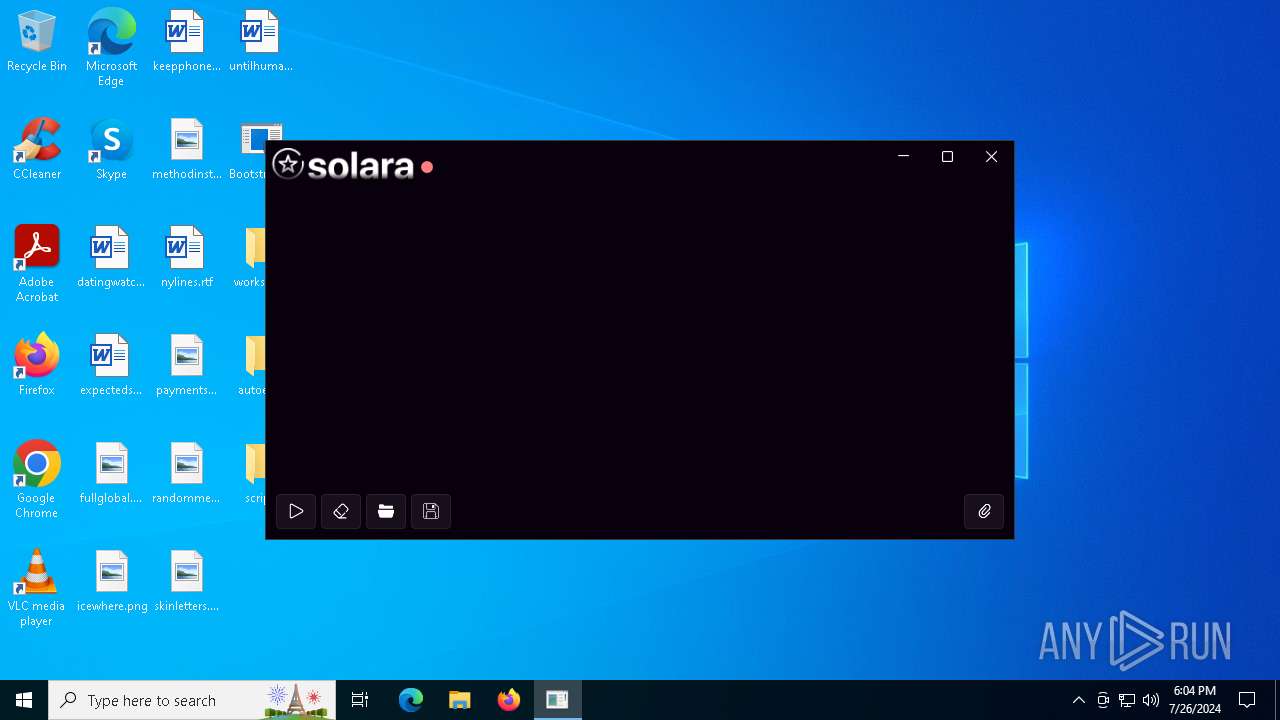
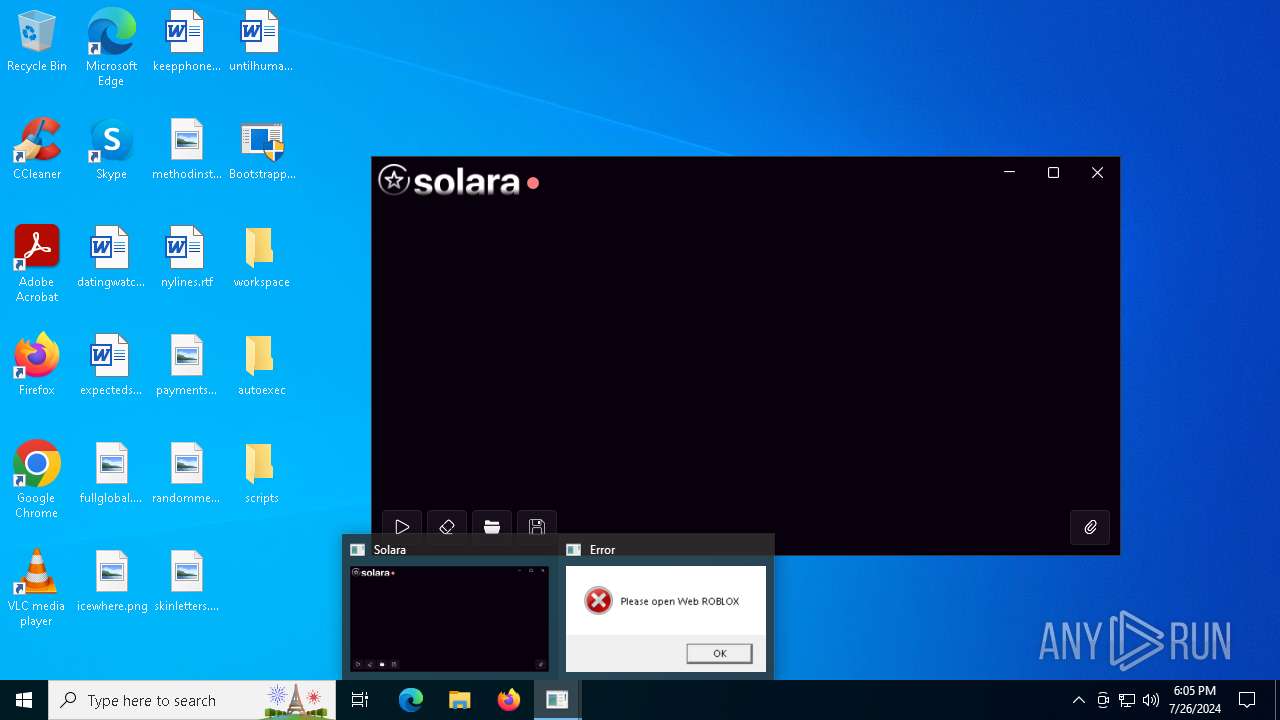
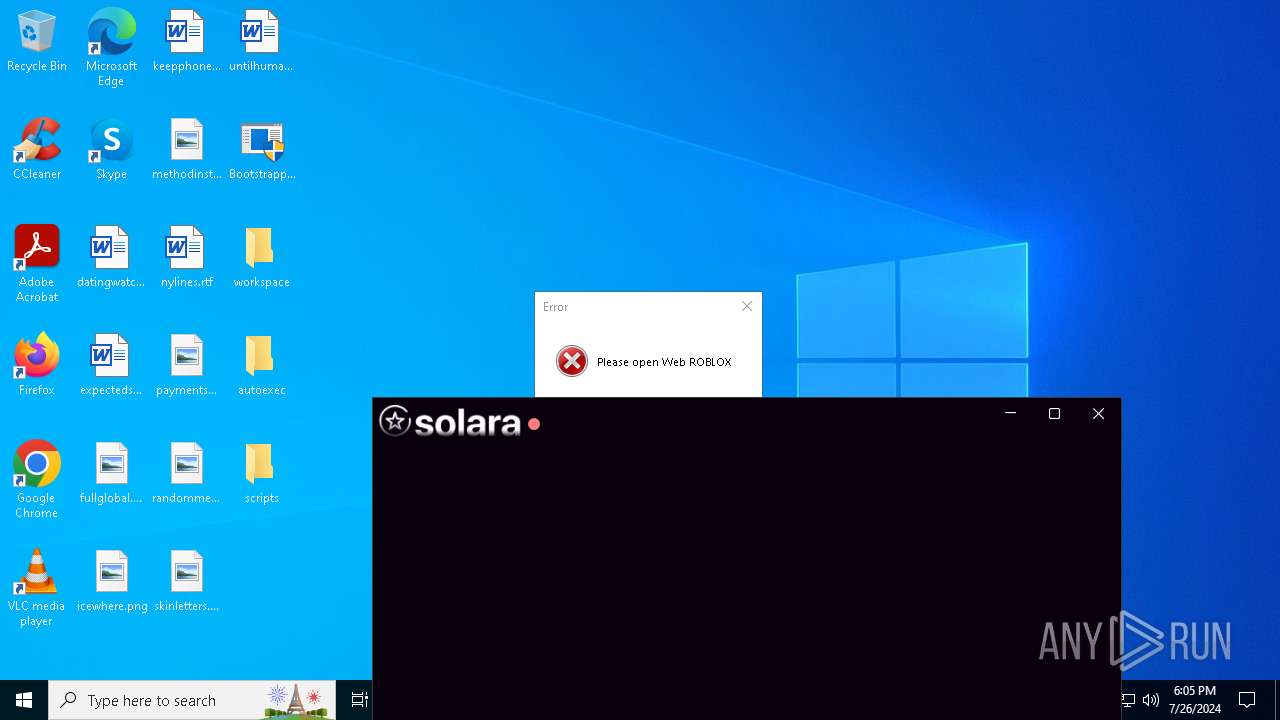
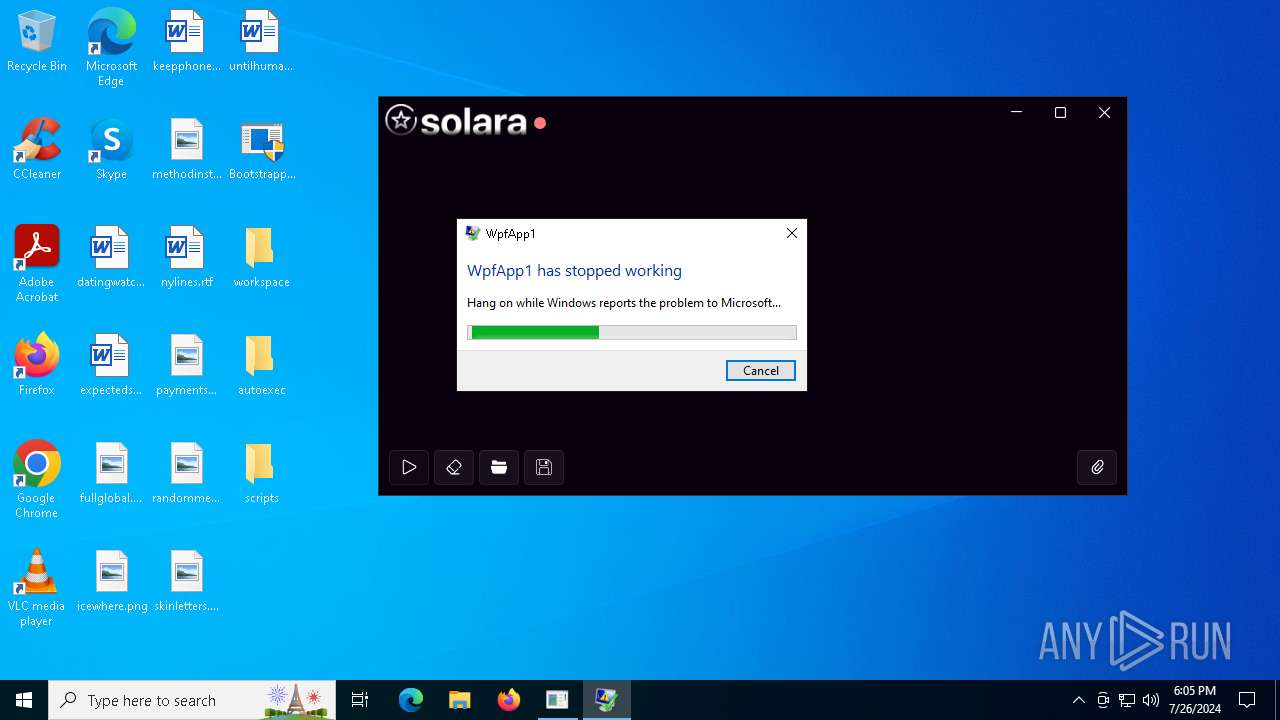
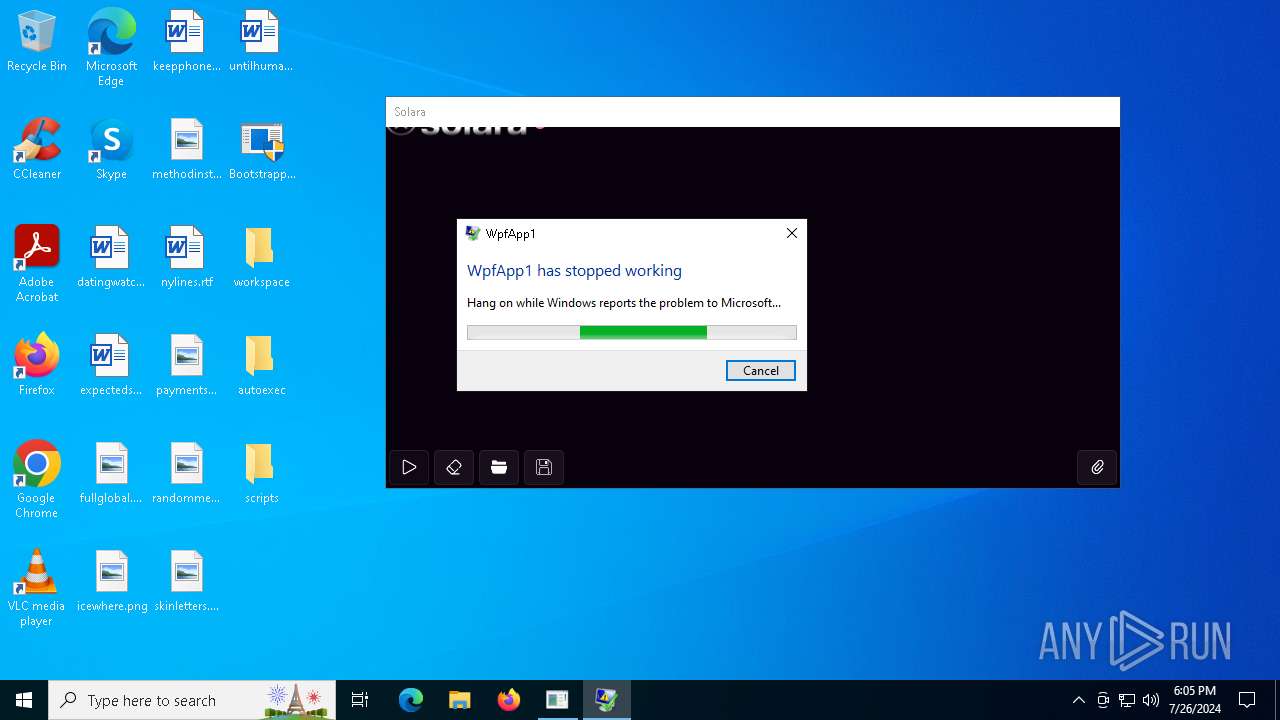
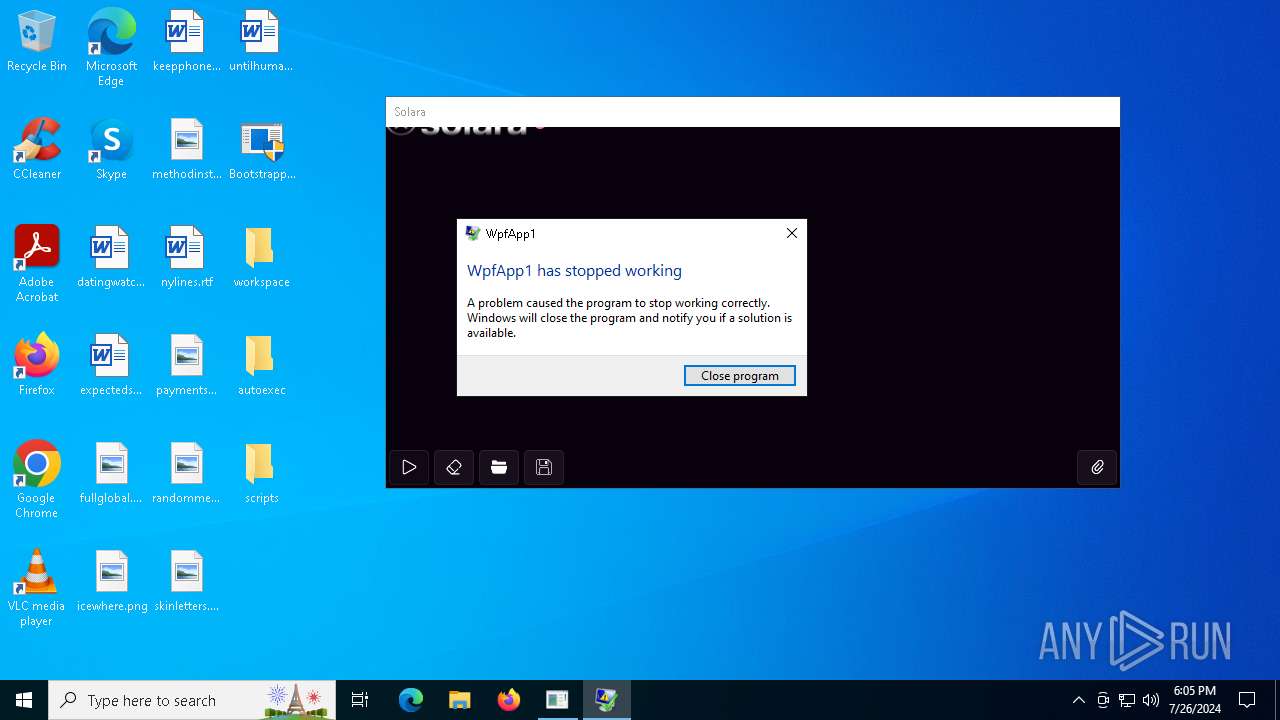
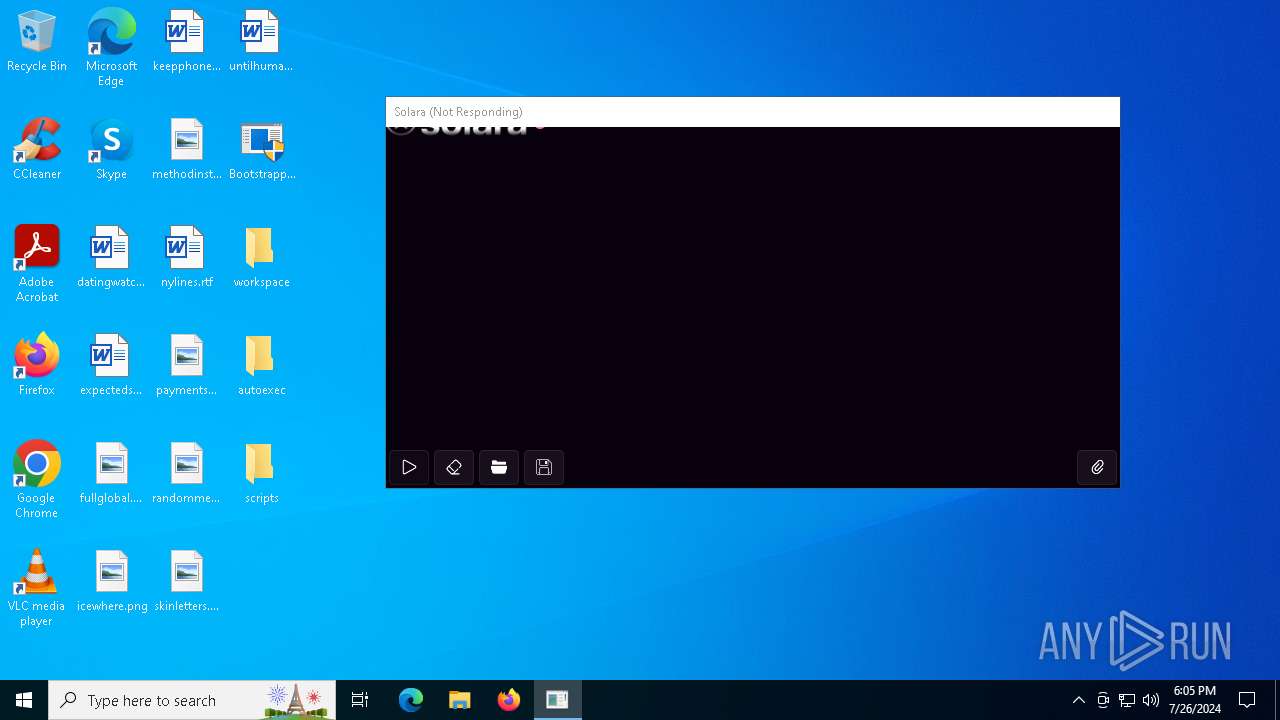
Executes application which crashes
- Solara.exe (PID: 6124)
INFO
Reads Environment values
- Bootstrapper.exe (PID: 2508)
- Bootstrapper.exe (PID: 3816)
- Solara.exe (PID: 6124)
- node.exe (PID: 6112)
Checks supported languages
- Bootstrapper.exe (PID: 2508)
- msiexec.exe (PID: 3980)
- msiexec.exe (PID: 6200)
- msiexec.exe (PID: 6164)
- msiexec.exe (PID: 5396)
- Bootstrapper.exe (PID: 3816)
- Solara.exe (PID: 6124)
- node.exe (PID: 1476)
- node.exe (PID: 6112)
Reads the computer name
- Bootstrapper.exe (PID: 2508)
- msiexec.exe (PID: 3980)
- msiexec.exe (PID: 6200)
- msiexec.exe (PID: 6164)
- msiexec.exe (PID: 5396)
- Bootstrapper.exe (PID: 3816)
- Solara.exe (PID: 6124)
Disables trace logs
- Bootstrapper.exe (PID: 2508)
- Bootstrapper.exe (PID: 3816)
- Solara.exe (PID: 6124)
Reads the machine GUID from the registry
- Bootstrapper.exe (PID: 2508)
- msiexec.exe (PID: 3980)
- Bootstrapper.exe (PID: 3816)
- Solara.exe (PID: 6124)
Checks proxy server information
- Bootstrapper.exe (PID: 2508)
- Bootstrapper.exe (PID: 3816)
- Solara.exe (PID: 6124)
- WerFault.exe (PID: 3488)
Create files in a temporary directory
- Bootstrapper.exe (PID: 2508)
Creates files or folders in the user directory
- msiexec.exe (PID: 3980)
- WerFault.exe (PID: 3488)
Process checks computer location settings
- Bootstrapper.exe (PID: 2508)
- Bootstrapper.exe (PID: 3816)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3980)
Reads the software policy settings
- msiexec.exe (PID: 3980)
- Bootstrapper.exe (PID: 2508)
- Bootstrapper.exe (PID: 3816)
- Solara.exe (PID: 6124)
- WerFault.exe (PID: 3488)
Application launched itself
- msiexec.exe (PID: 3980)
Manual execution by a user
- Bootstrapper.exe (PID: 3152)
- Bootstrapper.exe (PID: 3816)
Creates a software uninstall entry
- msiexec.exe (PID: 3980)
Creates files in the program directory
- Bootstrapper.exe (PID: 2508)
Dropped object may contain TOR URL's
- Bootstrapper.exe (PID: 2508)
Process checks whether UAC notifications are on
- Solara.exe (PID: 6124)
Reads product name
- node.exe (PID: 6112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:07:26 16:54:51+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 809984 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc7ade |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | SolaraBootstrapper |
| FileVersion: | 1.0.0.0 |
| InternalName: | SolaraBootstrapper.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | SolaraBootstrapper.exe |
| ProductName: | SolaraBootstrapper |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
172
Monitored processes
22
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1476 | "node" -v | C:\Program Files\nodejs\node.exe | — | Bootstrapper.exe | |||||||||||
User: admin Company: Node.js Integrity Level: HIGH Description: Node.js JavaScript Runtime Exit code: 0 Version: 18.16.0 Modules
| |||||||||||||||
| 1584 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2116 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Bootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2508 | "C:\Users\admin\Desktop\Bootstrapper.exe" | C:\Users\admin\Desktop\Bootstrapper.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SolaraBootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3152 | "C:\Users\admin\Desktop\Bootstrapper.exe" | C:\Users\admin\Desktop\Bootstrapper.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: SolaraBootstrapper Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3488 | C:\WINDOWS\system32\WerFault.exe -u -p 6124 -s 2936 | C:\Windows\System32\WerFault.exe | Solara.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3720 | "wevtutil.exe" im "C:\Program Files\nodejs\node_etw_provider.man" | C:\Windows\SysWOW64\wevtutil.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Eventing Command Line Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3816 | "C:\Users\admin\Desktop\Bootstrapper.exe" | C:\Users\admin\Desktop\Bootstrapper.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SolaraBootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3980 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 731
Read events
20 743
Write events
2 973
Delete events
15
Modification events
| (PID) Process: | (2508) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2508) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2508) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2508) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2508) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2508) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2508) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2508) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2508) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2508) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
33
Suspicious files
852
Text files
1 608
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2508 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\node-v18.16.0-x64.msi | — | |
MD5:— | SHA256:— | |||
| 3980 | msiexec.exe | C:\Windows\Installer\1c8091.msi | — | |
MD5:— | SHA256:— | |||
| 3980 | msiexec.exe | C:\Windows\Installer\MSI8ECE.tmp | executable | |
MD5:7A86CE1A899262DD3C1DF656BFF3FB2C | SHA256:B8F2D0909D7C2934285A8BE010D37C0609C7854A36562CBFCBCE547F4F4C7B0C | |||
| 3980 | msiexec.exe | C:\Windows\Installer\MSI8F0E.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 3980 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\66AE3BFDF94A732B262342AD2154B86E_CEA48AEE703922244E2530F7A011BBC6 | binary | |
MD5:A8B01B26B90019F5C46FF11C459BD527 | SHA256:E5200EC3479E33D030A4C0AB40D79309C20D8A598E57BFD8290350E5C7A9F3E7 | |||
| 3980 | msiexec.exe | C:\Windows\Installer\MSI8381.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 3980 | msiexec.exe | C:\Windows\Installer\MSI8361.tmp | executable | |
MD5:9FE9B0ECAEA0324AD99036A91DB03EBB | SHA256:E2CCE64916E405976A1D0C522B44527D12B1CBA19DE25DA62121CF5F41D184C9 | |||
| 3980 | msiexec.exe | C:\Windows\Installer\MSI8312.tmp | executable | |
MD5:9FE9B0ECAEA0324AD99036A91DB03EBB | SHA256:E2CCE64916E405976A1D0C522B44527D12B1CBA19DE25DA62121CF5F41D184C9 | |||
| 3980 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\66AE3BFDF94A732B262342AD2154B86E_CEA48AEE703922244E2530F7A011BBC6 | binary | |
MD5:29B5E357112B24202A67EB0A5A7CC9A6 | SHA256:2EEB36ABA1D9A8292CD2E004E3089B923CCAEFA1C0FE4B9E40522D1ED767042F | |||
| 3980 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\42B9A473B4DAF01285A36B4D3C7B1662_178C086B699FD6C56B804AF3EF759CB5 | binary | |
MD5:769506A95135705777D93F25F53D77E9 | SHA256:EBCAAEC1EB32262C85DEE9C4CE4B0881248DEE9E345903EA2C76A174E3E9B691 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
63
DNS requests
33
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | US | binary | 471 b | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | US | binary | 471 b | whitelisted |
760 | lsass.exe | GET | 200 | 142.250.184.195:80 | http://c.pki.goog/r/gsr1.crl | US | binary | 1.70 Kb | whitelisted |
760 | lsass.exe | GET | 200 | 142.250.184.195:80 | http://c.pki.goog/r/r4.crl | US | binary | 436 b | whitelisted |
3980 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | US | binary | 471 b | whitelisted |
1516 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
3980 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAOO2y%2FG5AVzGnYPFRYUTIU%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
204 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4436 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 2.20.142.138:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4560 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6012 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t-ring-fdv2.msedge.net |
| unknown |
a-ring-fallback.msedge.net |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
pastebin.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2284 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2284 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |