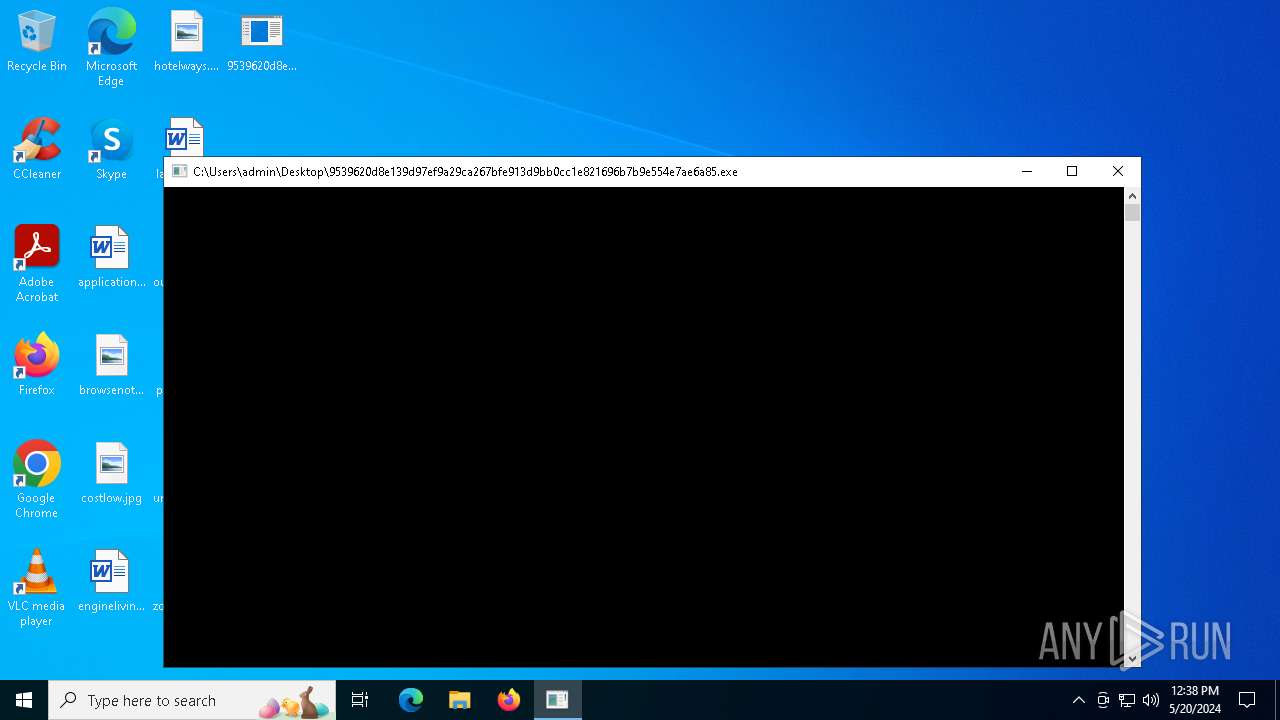
| File name: | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe |
| Full analysis: | https://app.any.run/tasks/36914c70-075a-46de-8d7f-538c8a06d8d4 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | May 20, 2024, 12:38:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64 (stripped to external PDB), for MS Windows |
| MD5: | D9B10475F33905DECB604C690E5D17C0 |
| SHA1: | 1728FDBF0AC8FAFF1F66902B0A5D5D8DD08C2544 |
| SHA256: | 9539620D8E139D97EF9A29CA267BFE913D9BB0CC1E821696B7B9E554E7AE6A85 |
| SSDEEP: | 49152:Rn8+gCN4iigiORdg5aIwC+AlcpfVEnmcKxY/O1u:18zW4kB6 |
MALICIOUS
Drops the executable file immediately after the start
- powershell.exe (PID: 6320)
- 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe (PID: 6708)
Connects to the CnC server
- 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe (PID: 6708)
SUSPICIOUS
Executable content was dropped or overwritten
- 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe (PID: 6708)
Starts itself from another location
- 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe (PID: 6708)
Potential Corporate Privacy Violation
- 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe (PID: 6708)
INFO
Checks supported languages
- SZnBlpj.exe (PID: 6812)
- vNKqfeQ.exe (PID: 6832)
- DpZcssX.exe (PID: 6788)
- 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe (PID: 6708)
- aMPTcXl.exe (PID: 6868)
- VUjDiUB.exe (PID: 6848)
- IZDFdLS.exe (PID: 6896)
- eQNEzGX.exe (PID: 6916)
- wXhsrKh.exe (PID: 6936)
- Meiqran.exe (PID: 6956)
- vEyoduB.exe (PID: 6980)
- JiqpOGJ.exe (PID: 7000)
- xYxfelF.exe (PID: 7020)
- oMaqAah.exe (PID: 7040)
- hpZyZSv.exe (PID: 7064)
- cNWJsHH.exe (PID: 7080)
- dZCvyjh.exe (PID: 7104)
- JCYBMbf.exe (PID: 2524)
- USVafTD.exe (PID: 7124)
- FOedSzY.exe (PID: 7144)
- XhwQKLX.exe (PID: 7164)
- uXQBYVX.exe (PID: 1172)
- lLaOxSi.exe (PID: 5004)
- XtRiqRq.exe (PID: 3640)
- RyqKzOS.exe (PID: 5180)
- urlBvIA.exe (PID: 2528)
- YDavLDh.exe (PID: 6100)
- nLyTfYV.exe (PID: 712)
- nIIJycr.exe (PID: 2472)
- jYpaIkn.exe (PID: 2736)
- rwZxgag.exe (PID: 5032)
- CXFSnXR.exe (PID: 472)
- jUGhBHC.exe (PID: 1712)
- BrhnqcJ.exe (PID: 3688)
- MqkpYDB.exe (PID: 5244)
- gvxkggY.exe (PID: 3728)
- dXnuMlA.exe (PID: 1492)
- nrwhorM.exe (PID: 3692)
- mabCvFW.exe (PID: 4708)
- iXtuCYZ.exe (PID: 4148)
- GHdvcAk.exe (PID: 6164)
- jWonddk.exe (PID: 6332)
- UoEDzTP.exe (PID: 4012)
- YXrSjoi.exe (PID: 5256)
- HDwFXsl.exe (PID: 4380)
- zFgWVDN.exe (PID: 6220)
- YuqzgmZ.exe (PID: 6056)
- gulRvMJ.exe (PID: 6152)
- aKmpcNc.exe (PID: 2592)
- lnxKElb.exe (PID: 1412)
- htLYYzn.exe (PID: 6256)
- tPBOKUJ.exe (PID: 6420)
- NVnuHaG.exe (PID: 1440)
- XSflXQx.exe (PID: 6688)
- PCktjiY.exe (PID: 2312)
- GZYGVin.exe (PID: 3040)
- XqmBhUw.exe (PID: 6576)
- TfAHtsL.exe (PID: 5784)
- jgOxgqS.exe (PID: 3172)
- ccfHJgr.exe (PID: 6488)
- JDvtwfA.exe (PID: 2396)
- nzVtFhh.exe (PID: 1116)
- ZApmMqL.exe (PID: 6660)
- gRmySgn.exe (PID: 6676)
- orKTeWe.exe (PID: 6388)
- qmRAKib.exe (PID: 6732)
- bMkoKOy.exe (PID: 6636)
- InkQBOU.exe (PID: 6620)
- hlnqBGk.exe (PID: 6440)
- rEIqHvP.exe (PID: 6500)
- nmYvLDW.exe (PID: 6416)
- PCdhuJs.exe (PID: 3732)
- LPDlqLg.exe (PID: 6892)
- gSEFWfg.exe (PID: 6452)
- FeaLUQt.exe (PID: 6464)
- YlOvIhn.exe (PID: 6368)
- gVhdUDp.exe (PID: 7268)
- uLRtfpM.exe (PID: 7208)
- CiuuugO.exe (PID: 7188)
- UXSKYkZ.exe (PID: 920)
- AaRLauz.exe (PID: 1276)
- TcQRfnC.exe (PID: 780)
- yrmGjcU.exe (PID: 7228)
- dnmnBzW.exe (PID: 7248)
- oyEZceY.exe (PID: 7308)
- kfQsJKj.exe (PID: 7328)
- pgacDDw.exe (PID: 7348)
- lxuWHqA.exe (PID: 7288)
- VrxQqfo.exe (PID: 7408)
- vxQKSeu.exe (PID: 7448)
- hJApecD.exe (PID: 7468)
- NdOFMhD.exe (PID: 7488)
- wxBZOMJ.exe (PID: 7508)
- kIYKaDr.exe (PID: 7528)
- lmXxmzj.exe (PID: 7368)
- uEyQivZ.exe (PID: 7388)
- FkWHFKd.exe (PID: 7428)
- mgDZJfq.exe (PID: 7576)
- MupicPy.exe (PID: 7556)
- LTFmOcE.exe (PID: 7596)
- jmlXpPc.exe (PID: 7616)
- sZXCJgL.exe (PID: 7636)
- ZUShdRI.exe (PID: 7652)
- LwZjglM.exe (PID: 7672)
- nkNHYHB.exe (PID: 7692)
- sAZlweh.exe (PID: 7712)
- TpIcRZl.exe (PID: 7732)
- dwhttWv.exe (PID: 7752)
- WHikqIl.exe (PID: 7772)
- ONtHMmF.exe (PID: 7792)
- ncjCGNd.exe (PID: 7812)
- QgNYtMj.exe (PID: 7832)
- yyufWkn.exe (PID: 7872)
- rClOylq.exe (PID: 7852)
- PPqjjXV.exe (PID: 7932)
- ZsTIDiE.exe (PID: 7912)
- gorihjh.exe (PID: 7892)
- VimwWvW.exe (PID: 7952)
- PjuFKvC.exe (PID: 7972)
- zkNcSbu.exe (PID: 7992)
- bTXWOSn.exe (PID: 8012)
- DHJuORf.exe (PID: 8032)
- tLCrPPB.exe (PID: 8052)
- mtfUIHK.exe (PID: 8092)
- bAPjvxd.exe (PID: 8072)
- CsDCSZT.exe (PID: 8256)
- nboORLd.exe (PID: 8112)
- JXDBhql.exe (PID: 8132)
- NFFyojX.exe (PID: 8172)
- aBUhXMO.exe (PID: 8196)
- RwKtUbp.exe (PID: 2680)
- WBMaHen.exe (PID: 8216)
- JCtiRmx.exe (PID: 8236)
- SuYJWqk.exe (PID: 8276)
- XsjlYmO.exe (PID: 8152)
- rtVNpHg.exe (PID: 8336)
- YDSslUz.exe (PID: 8356)
- JSYmeiL.exe (PID: 8396)
- lopbwbD.exe (PID: 8376)
- hMKyynu.exe (PID: 8488)
- MPpSeHc.exe (PID: 8416)
- PMDYyqW.exe (PID: 8436)
- nzxwdAa.exe (PID: 8464)
- CAdwYwa.exe (PID: 8664)
- KnTOrUU.exe (PID: 8512)
- hhSBiPg.exe (PID: 8544)
- Kwksosq.exe (PID: 8572)
- NTxnAAR.exe (PID: 8604)
- uxxLAWe.exe (PID: 8628)
- eVSoFTW.exe (PID: 8696)
- gjrTDTI.exe (PID: 8728)
- qGPoAdJ.exe (PID: 8756)
- AtGIvbL.exe (PID: 8296)
- DbkINyQ.exe (PID: 8316)
- JZqQGiW.exe (PID: 8884)
- JrxOlnL.exe (PID: 8820)
- RmLQmMX.exe (PID: 8852)
- URyHqNI.exe (PID: 9268)
- sdbkpDv.exe (PID: 9036)
- ujjPwpe.exe (PID: 8912)
- ZvKJtiP.exe (PID: 8944)
- NrNBUXD.exe (PID: 8972)
- CleeTod.exe (PID: 9004)
- yVlNnYK.exe (PID: 9100)
- pFqxveT.exe (PID: 9068)
- LcuBPjk.exe (PID: 9128)
- FMSIipn.exe (PID: 9152)
- TtJzoTu.exe (PID: 9188)
- wPYSMDS.exe (PID: 4340)
- uKKRxjZ.exe (PID: 9244)
- vpdHZxi.exe (PID: 9296)
- cLCkjkg.exe (PID: 9352)
- nYRaslJ.exe (PID: 9328)
- jQOQHni.exe (PID: 8788)
- yxYwxPg.exe (PID: 9380)
- LVkTzAU.exe (PID: 9404)
- iRJWXTR.exe (PID: 9432)
- kjXeICj.exe (PID: 9608)
- vKHcVdf.exe (PID: 9460)
- vkQxJpR.exe (PID: 9488)
- pYnpyUf.exe (PID: 9512)
- PNqBXdb.exe (PID: 9532)
- XECmrTg.exe (PID: 9560)
- asXVYeS.exe (PID: 9584)
- DzubiLP.exe (PID: 9680)
- zJvVLge.exe (PID: 9640)
- CvplAOi.exe (PID: 9660)
- ythCQXq.exe (PID: 9704)
- QyWFtBa.exe (PID: 9776)
- cgkhPkh.exe (PID: 9728)
- VcSDxAC.exe (PID: 9752)
- ZWoBZGJ.exe (PID: 9800)
- PbdCouz.exe (PID: 9820)
- YDCCBtB.exe (PID: 9844)
- jUBDbjk.exe (PID: 9892)
- ejBNFkQ.exe (PID: 9940)
- EcXXkpY.exe (PID: 9988)
- jCsklHr.exe (PID: 9964)
- UWZGcSh.exe (PID: 10208)
- KPDpowv.exe (PID: 10012)
- YBIYOHv.exe (PID: 10036)
- JWGKENG.exe (PID: 10060)
- cAfxoml.exe (PID: 10084)
- qRoKdpf.exe (PID: 10108)
- xoVRpYc.exe (PID: 10156)
- oWjJYbR.exe (PID: 10132)
- eXVJSnc.exe (PID: 1788)
- PRsMFxI.exe (PID: 10180)
- VgMMweN.exe (PID: 10232)
- hNRbnsf.exe (PID: 5556)
- qNkljED.exe (PID: 10248)
- UmggnWg.exe (PID: 10276)
- GXhSuXt.exe (PID: 9868)
- JBFtpQA.exe (PID: 9916)
- rmKUopX.exe (PID: 10296)
- uGJqXpV.exe (PID: 10324)
- OysXvDJ.exe (PID: 10344)
- dlzGlWm.exe (PID: 10488)
- xAZrvPg.exe (PID: 10392)
- kzxtWRO.exe (PID: 10372)
- ifaPJUh.exe (PID: 10440)
- xXORvhc.exe (PID: 10416)
- OztPCFB.exe (PID: 10464)
- spYIeVm.exe (PID: 10612)
- sBBCJDv.exe (PID: 10512)
- bYwImiW.exe (PID: 10536)
- ztmskTT.exe (PID: 10684)
- ChpPqwZ.exe (PID: 10564)
- HbsLbnk.exe (PID: 10588)
- TFplaXK.exe (PID: 10636)
- fKjnzSU.exe (PID: 10660)
- OiJBhsB.exe (PID: 10708)
- alDSrvI.exe (PID: 10828)
- CUKtnPo.exe (PID: 10808)
- AagaicD.exe (PID: 11068)
- XblExzu.exe (PID: 10852)
- uqWVKqr.exe (PID: 10924)
- cvIXNER.exe (PID: 10876)
- QqbzRun.exe (PID: 10900)
- OaoJUje.exe (PID: 10996)
- vnwzYvR.exe (PID: 10948)
- iezrkcf.exe (PID: 10972)
- SLRwkWl.exe (PID: 11016)
- iEnCrjt.exe (PID: 11044)
- neRnuAF.exe (PID: 11092)
- JlBsqLV.exe (PID: 11116)
- TrvhTGu.exe (PID: 11140)
- DdIUHZj.exe (PID: 11188)
- eyAFbbk.exe (PID: 11164)
- hXFdenL.exe (PID: 10732)
- nEvDzia.exe (PID: 10756)
- qvxJaSm.exe (PID: 10780)
- grKTgdK.exe (PID: 11236)
- KlzOkQF.exe (PID: 11272)
- XGEPCmB.exe (PID: 11256)
- WDpkqZO.exe (PID: 11316)
- mvaQami.exe (PID: 11296)
- MCcWsxA.exe (PID: 11344)
- ohwferF.exe (PID: 11368)
- Ikllelw.exe (PID: 11392)
- mTcWzkM.exe (PID: 11416)
- uTskepg.exe (PID: 11444)
- lPtrtVC.exe (PID: 11464)
- XcIkYyM.exe (PID: 11536)
- NcUtKee.exe (PID: 11488)
- dYHIMlj.exe (PID: 11512)
- HaXOrND.exe (PID: 11560)
- IgxYcWQ.exe (PID: 11584)
- JPbaqgh.exe (PID: 11608)
- UnZKgfO.exe (PID: 11212)
- ceBZAQX.exe (PID: 11684)
- mPjKQrS.exe (PID: 11824)
- UXbEMlg.exe (PID: 11756)
- vHTRimK.exe (PID: 11780)
- zyElUeR.exe (PID: 11800)
- aCKztPW.exe (PID: 11876)
- wTpQuey.exe (PID: 11852)
- pRVUOkh.exe (PID: 11900)
- ZKMPQrR.exe (PID: 11948)
- Fwhzato.exe (PID: 11972)
- fIisDPv.exe (PID: 11996)
- vDXGWys.exe (PID: 12020)
- yklsdyM.exe (PID: 12044)
- GvsqSOJ.exe (PID: 12072)
- yIDXhXz.exe (PID: 11636)
- dGTBpJU.exe (PID: 11660)
- ighLeWf.exe (PID: 11708)
- fmUtYzt.exe (PID: 11732)
- ZRaBFDp.exe (PID: 11924)
- PwMIQIR.exe (PID: 12116)
- QEJmJhn.exe (PID: 12164)
- HKNUOaE.exe (PID: 12192)
- YhmNajB.exe (PID: 12216)
- RFoUhqz.exe (PID: 12396)
- oKSyDTg.exe (PID: 12348)
- KigGOvu.exe (PID: 6264)
- yNISfGu.exe (PID: 12324)
- LZZfeel.exe (PID: 12372)
- IgRtXjA.exe (PID: 12420)
- GyhoXUV.exe (PID: 12444)
- JVdNRVr.exe (PID: 12092)
- LkARITM.exe (PID: 12140)
- LnYkDoD.exe (PID: 12236)
- TibSLgA.exe (PID: 12260)
- gohaALg.exe (PID: 12300)
- hXcgcby.exe (PID: 12588)
- ZNegNUY.exe (PID: 12612)
- qzkNghD.exe (PID: 12636)
- oLOSnnw.exe (PID: 12664)
- oLBSKTQ.exe (PID: 12716)
- rKxJxAQ.exe (PID: 12740)
- ghkyltP.exe (PID: 12764)
- xbHlqUn.exe (PID: 12812)
- sGhRAFG.exe (PID: 12788)
- pViNIyx.exe (PID: 12836)
- VQYykpE.exe (PID: 12472)
- qiUMSmG.exe (PID: 12496)
- vKIUJao.exe (PID: 12520)
- kRbkGxe.exe (PID: 12544)
- JPuqCoC.exe (PID: 12568)
- dbXTeTF.exe (PID: 12688)
- SOAXEIB.exe (PID: 12864)
- aUQBIPe.exe (PID: 12888)
- eBkybAZ.exe (PID: 12912)
- WkcaAPy.exe (PID: 12936)
- aLWzzDA.exe (PID: 12960)
Reads the computer name
- 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe (PID: 6708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (39.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (26.3) |
| .exe | | | UPX compressed Win32 Executable (25.8) |
| .exe | | | Win32 Executable (generic) (4.3) |
| .exe | | | Generic Win/DOS Executable (1.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:08:29 00:43:41+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 14.22 |
| CodeSize: | 278528 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 3190784 |
| EntryPoint: | 0x9a338 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
445
Monitored processes
330
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | C:\Windows\System\CXFSnXR.exe | C:\Windows\System\CXFSnXR.exe | — | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 712 | C:\Windows\System\nLyTfYV.exe | C:\Windows\System\nLyTfYV.exe | — | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 780 | C:\Windows\System\TcQRfnC.exe | C:\Windows\System\TcQRfnC.exe | — | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 920 | C:\Windows\System\UXSKYkZ.exe | C:\Windows\System\UXSKYkZ.exe | — | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1116 | C:\Windows\System\nzVtFhh.exe | C:\Windows\System\nzVtFhh.exe | — | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1172 | C:\Windows\System\uXQBYVX.exe | C:\Windows\System\uXQBYVX.exe | — | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1276 | C:\Windows\System\AaRLauz.exe | C:\Windows\System\AaRLauz.exe | — | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1412 | C:\Windows\System\lnxKElb.exe | C:\Windows\System\lnxKElb.exe | — | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1440 | C:\Windows\System\NVnuHaG.exe | C:\Windows\System\NVnuHaG.exe | — | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1492 | C:\Windows\System\dXnuMlA.exe | C:\Windows\System\dXnuMlA.exe | — | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
15 967
Read events
15 959
Write events
8
Delete events
0
Modification events
| (PID) Process: | (6320) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6320) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6320) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6320) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
325
Suspicious files
5
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6320 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | — | |
MD5:— | SHA256:— | |||
| 6708 | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | C:\Windows\System\JiqpOGJ.exe | executable | |
MD5:F3BD3D33D2DB57DC7698BEB60A210473 | SHA256:BCBC7FA9F13AF4E9D41D6C0C71BB9AFA03B6AD61C4CFB337D67DDAB7D34FED05 | |||
| 6320 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:D61E70D758CA1ABD092826F8F8FB6591 | SHA256:DFC6E2A9BD85F12ACD1B5B86A4F00806965D0E4A1CB62B6DCD5355A2F836BF64 | |||
| 6320 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fnxcgm5l.f2n.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6708 | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | C:\Windows\System\IZDFdLS.exe | executable | |
MD5:0C9F31D7AA8DF88E90AA0AEC565BD5C6 | SHA256:9EFAA6EB158E7FD4BACAD4FB9DE878942F44FEE64A68AA75B6F8FA05E338664D | |||
| 6708 | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | C:\Windows\System\VUjDiUB.exe | executable | |
MD5:738A8970626746C6226E637ABF9DA76E | SHA256:926C1061D0EEE06047D7B58939BCC51476198DE658A1B0FAB24F76817C6627BB | |||
| 6708 | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | C:\Windows\System\DpZcssX.exe | executable | |
MD5:7FE8A7BB25EA2898B7EEF8DD9F4AF0E3 | SHA256:DB02F1E3DC8629EEEF2E5ED405E96C1387D2BF970498F6D1DA976D5B2BB35EFF | |||
| 6708 | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | C:\Windows\System\eQNEzGX.exe | executable | |
MD5:072D4213CDE340CB675428682D497CAE | SHA256:9B923D1215644DEF4F9584C77668237170196F20FBF929D4076B2144DB1BE7B1 | |||
| 6708 | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | C:\Windows\System\vNKqfeQ.exe | executable | |
MD5:D85649165C01124024723F03C29D08EF | SHA256:B38454A9BB4B5C3E4E6C70ABF5AE3FDA0124F89995DEBAC8C7B5BE741394F530 | |||
| 6708 | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | C:\Windows\System\aMPTcXl.exe | executable | |
MD5:4ECF2CF8C0BFC123EFAB1158EBD8416B | SHA256:4C128525D0B6BA0E115CC243292BF43C76050EADF23093F6E1B6BD17570BE06B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
26
DNS requests
5
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5140 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.24:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1744 | svchost.exe | GET | 200 | 2.16.164.24:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5524 | RUXIMICS.exe | GET | 200 | 2.16.164.24:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5524 | RUXIMICS.exe | GET | 200 | 2.18.97.123:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1744 | svchost.exe | GET | 200 | 2.18.97.123:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 2.18.97.123:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
2908 | OfficeClickToRun.exe | POST | 200 | 13.89.179.9:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5524 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5140 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5140 | MoUsoCoreWorker.exe | 2.16.164.24:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
5524 | RUXIMICS.exe | 2.16.164.24:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
1744 | svchost.exe | 2.16.164.24:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
5524 | RUXIMICS.exe | 2.18.97.123:80 | www.microsoft.com | Akamai International B.V. | FR | unknown |
5140 | MoUsoCoreWorker.exe | 2.18.97.123:80 | www.microsoft.com | Akamai International B.V. | FR | unknown |
1744 | svchost.exe | 2.18.97.123:80 | www.microsoft.com | Akamai International B.V. | FR | unknown |
1744 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6708 | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
— | — | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
6708 | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
— | — | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
6708 | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
— | — | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
6708 | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
— | — | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
6708 | 9539620d8e139d97ef9a29ca267bfe913d9bb0cc1e821696b7b9e554e7ae6a85.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |