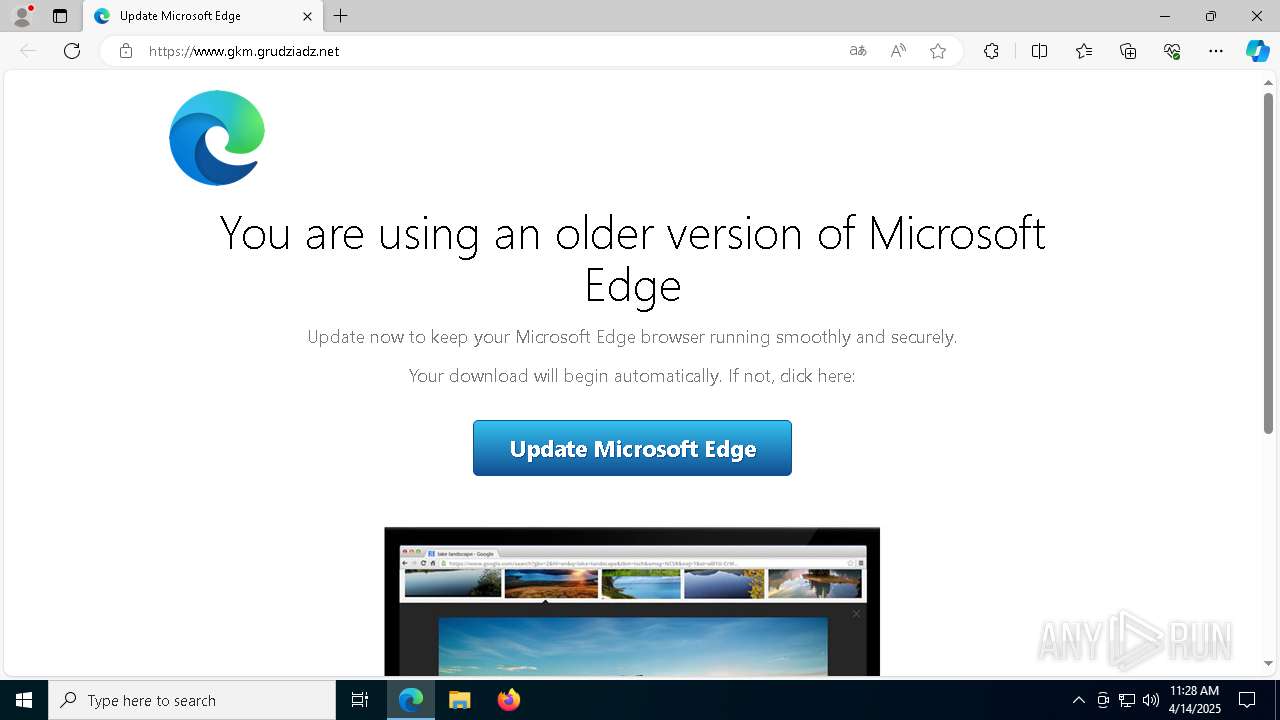
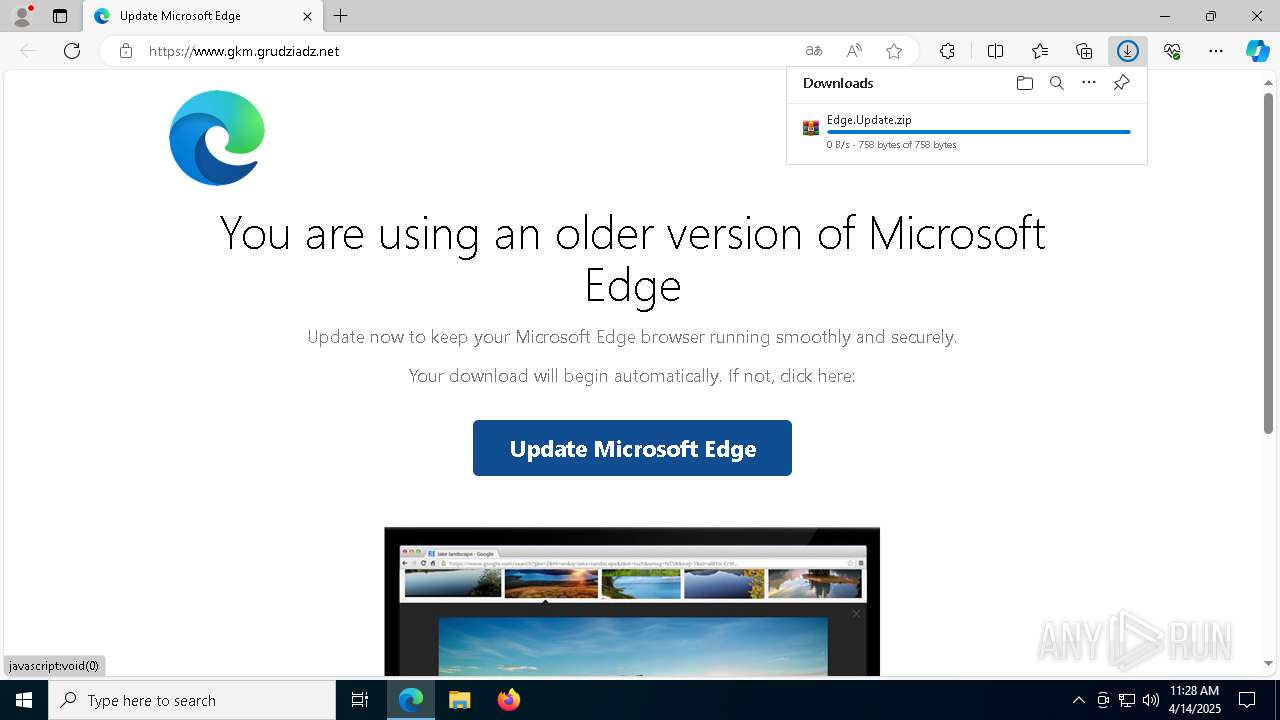
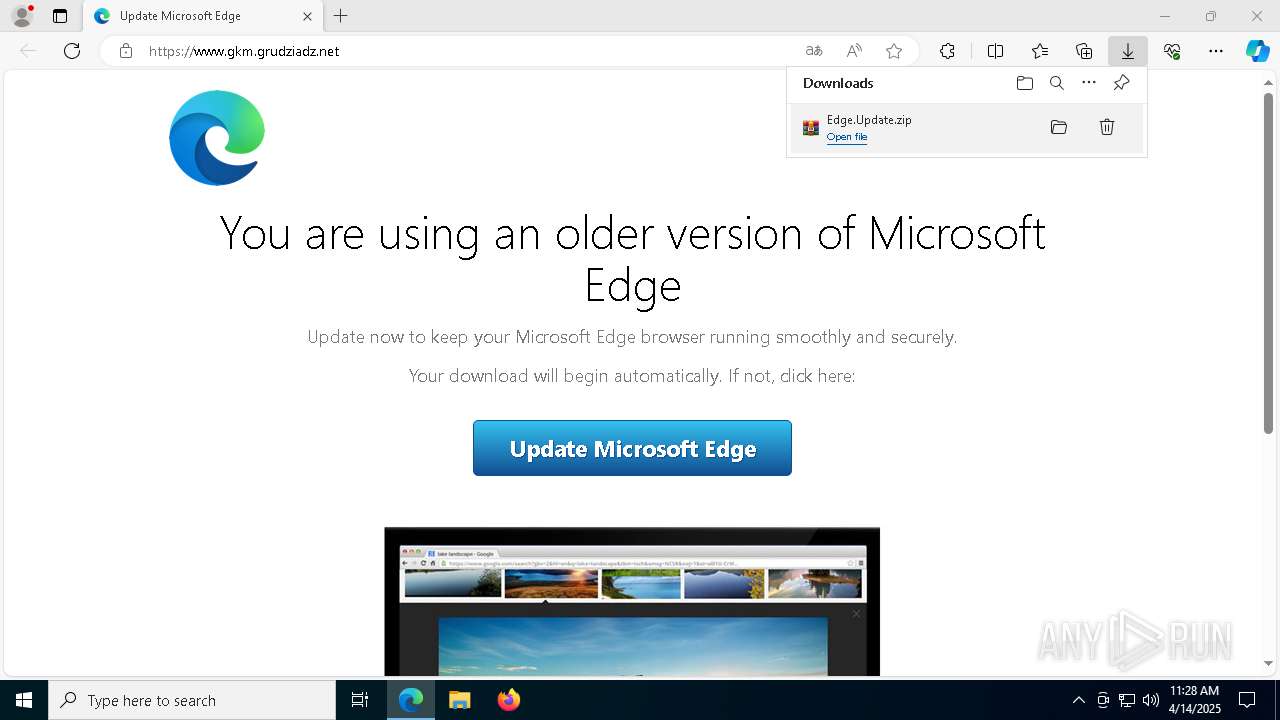
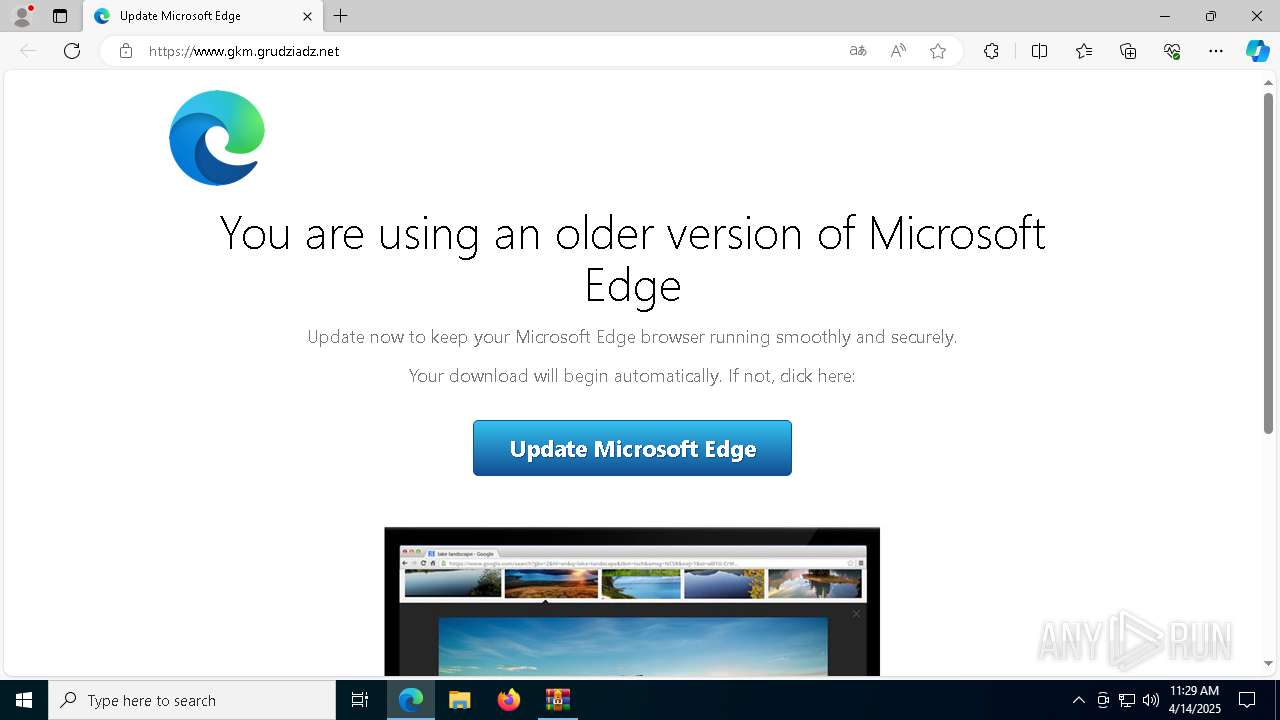
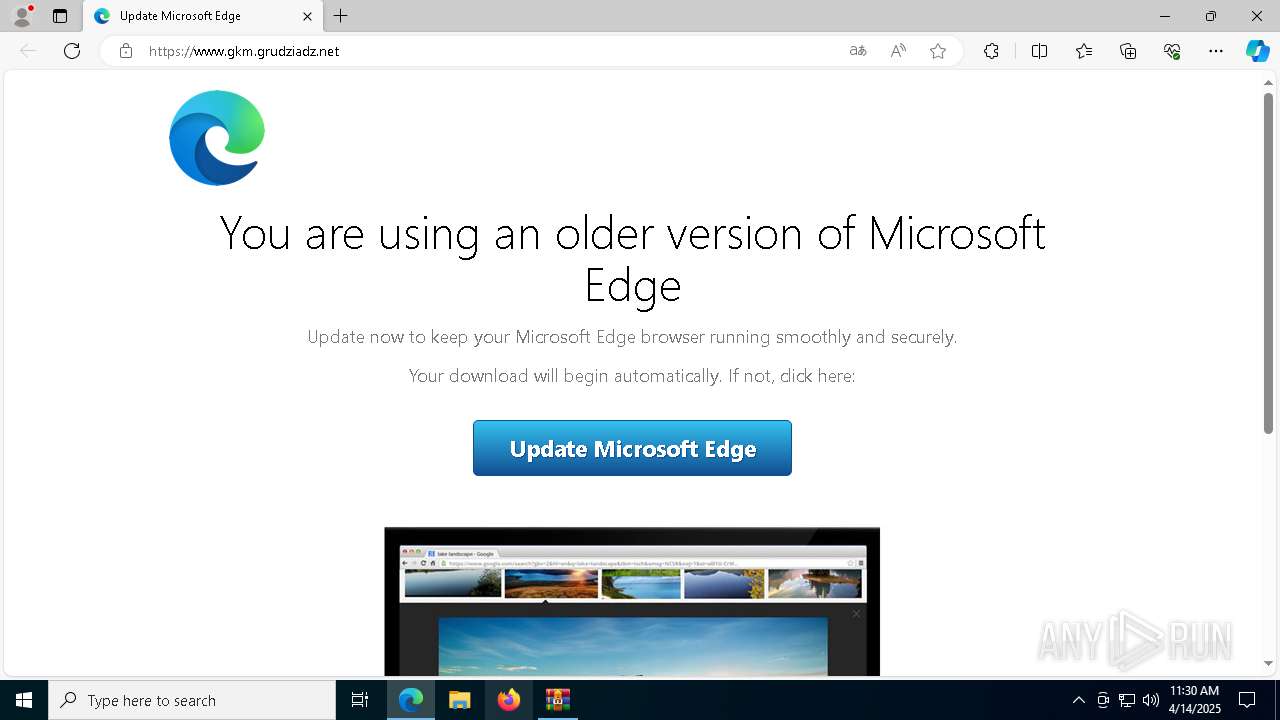
| URL: | http://www.gkm.grudziadz.net/ |
| Full analysis: | https://app.any.run/tasks/49077cc1-b2fd-4f10-8c5b-03262b872a59 |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2025, 11:27:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 31C60C0352DFAF825F41A1B7D75E14FC |
| SHA1: | 52CE8805D52F972FEF6123450C12C2439A7B7CF9 |
| SHA256: | 9537E3B3D38E05AB1B5533E898AA924D819DC01ED3055B03E0A87BB923DD8833 |
| SSDEEP: | 3:N1KJS4kfMEBf/As:Cc4kkC/z |
MALICIOUS
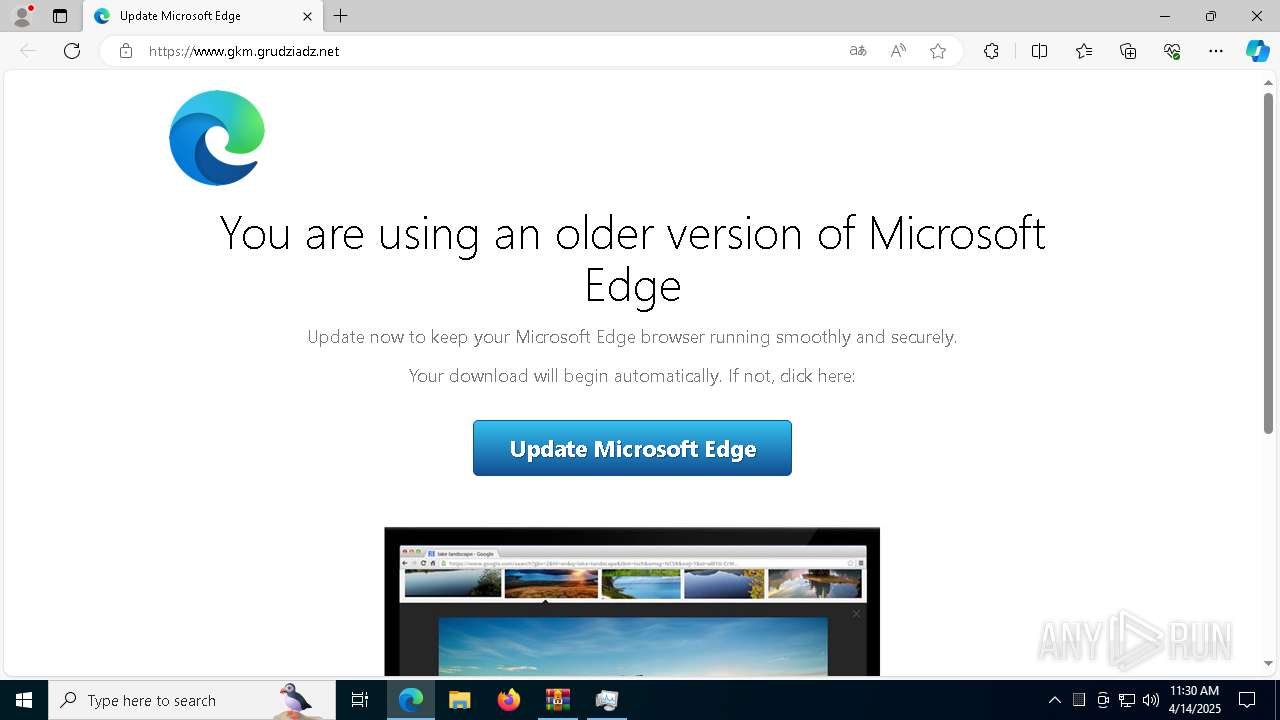
TDS has been detected (SURICATA)
- msedge.exe (PID: 7368)
SOCGHOLISH has been detected (SURICATA)
- msedge.exe (PID: 7368)
- wscript.exe (PID: 920)
- svchost.exe (PID: 2196)
Connects to the CnC server
- svchost.exe (PID: 2196)
- wscript.exe (PID: 920)
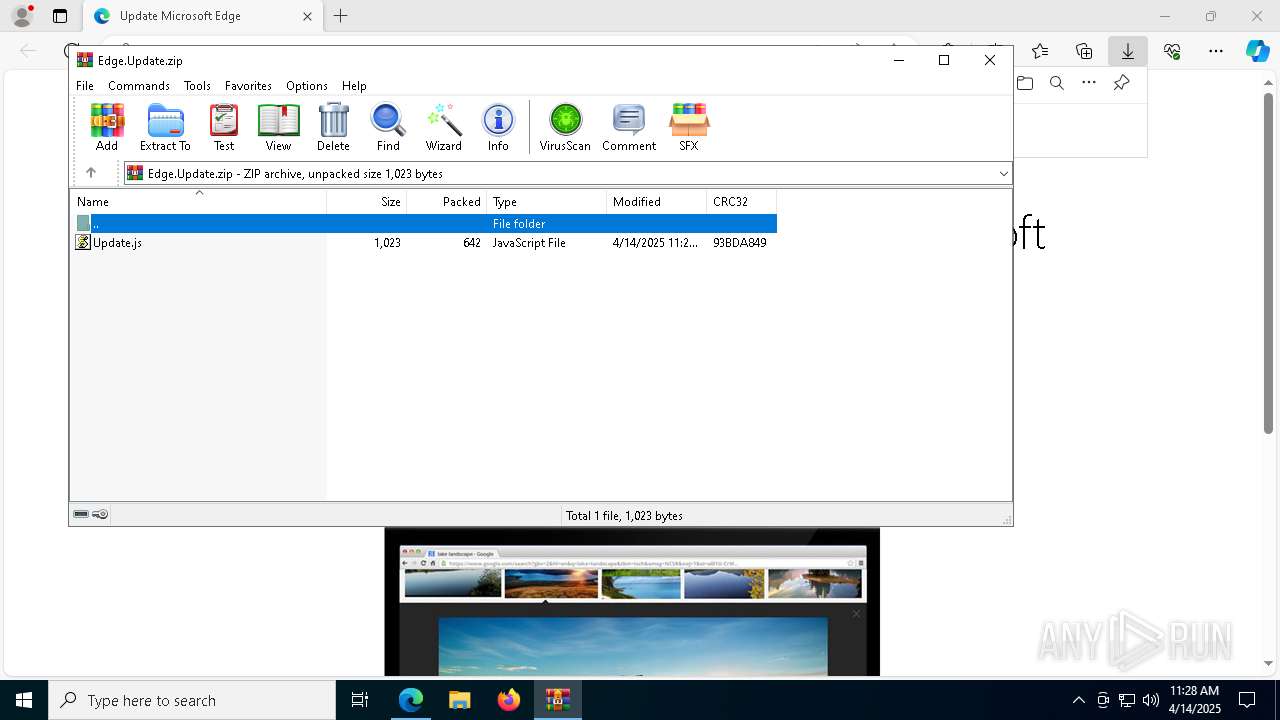
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 920)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 920)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 920)
Connecting to the Traffic Distribution System (TDS)
- msedge.exe (PID: 7368)
Accesses BIOS(Win32_BIOS, may evade sandboxes) via WMI (SCRIPT)
- wscript.exe (PID: 920)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 920)
Accesses information about the status of the installed antivirus(Win32_AntivirusProduct) via WMI (SCRIPT)
- wscript.exe (PID: 920)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 920)
FRAUD has been detected (SURICATA)
- msedge.exe (PID: 7368)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 920)
Accesses name of a computer manufacturer via WMI (SCRIPT)
- wscript.exe (PID: 920)
SUSPICIOUS
Contacting a server suspected of hosting an Exploit Kit
- msedge.exe (PID: 7368)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5084)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 920)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 920)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 920)
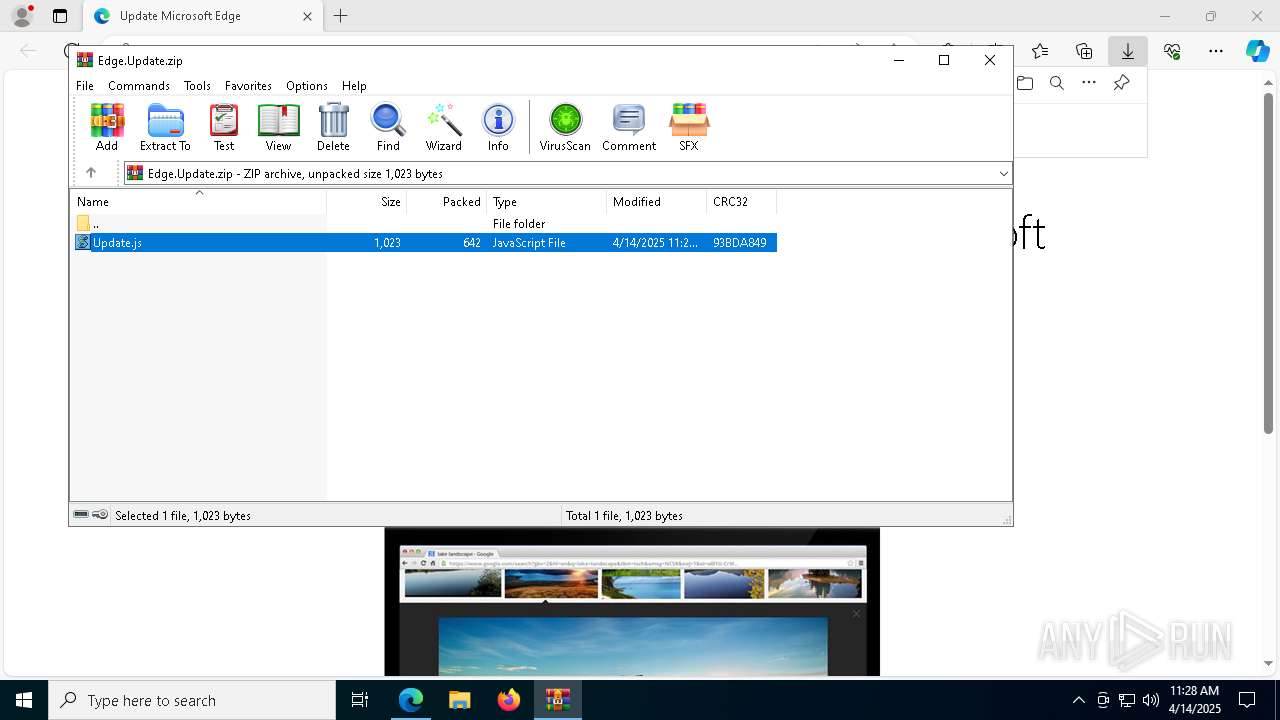
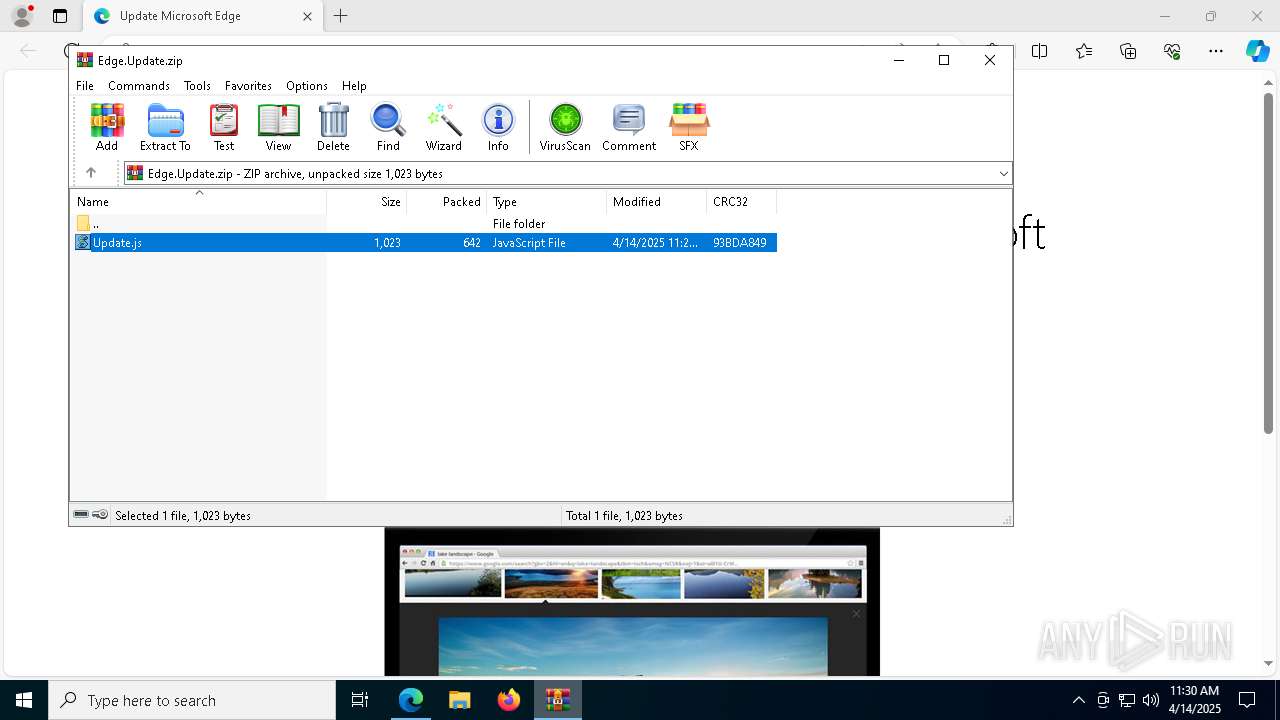
The process executes JS scripts
- WinRAR.exe (PID: 5084)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 920)
Access Product Name via WMI (SCRIPT)
- wscript.exe (PID: 920)
Accesses WMI object display name (SCRIPT)
- wscript.exe (PID: 920)
Accesses antivirus product name via WMI (SCRIPT)
- wscript.exe (PID: 920)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- wscript.exe (PID: 920)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 920)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 920)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 920)
Runs shell command (SCRIPT)
- wscript.exe (PID: 920)
Accesses ComputerSystem(Win32_ComputerSystem) via WMI (SCRIPT)
- wscript.exe (PID: 920)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 920)
INFO
Reads the computer name
- identity_helper.exe (PID: 5640)
Application launched itself
- msedge.exe (PID: 5280)
Reads Environment values
- identity_helper.exe (PID: 5640)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 5084)
- msedge.exe (PID: 5280)
Checks proxy server information
- wscript.exe (PID: 920)
- powershell.exe (PID: 5260)
- slui.exe (PID: 3956)
Checks supported languages
- identity_helper.exe (PID: 5640)
Reads the software policy settings
- slui.exe (PID: 8088)
- slui.exe (PID: 3956)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5260)
Disables trace logs
- powershell.exe (PID: 5260)
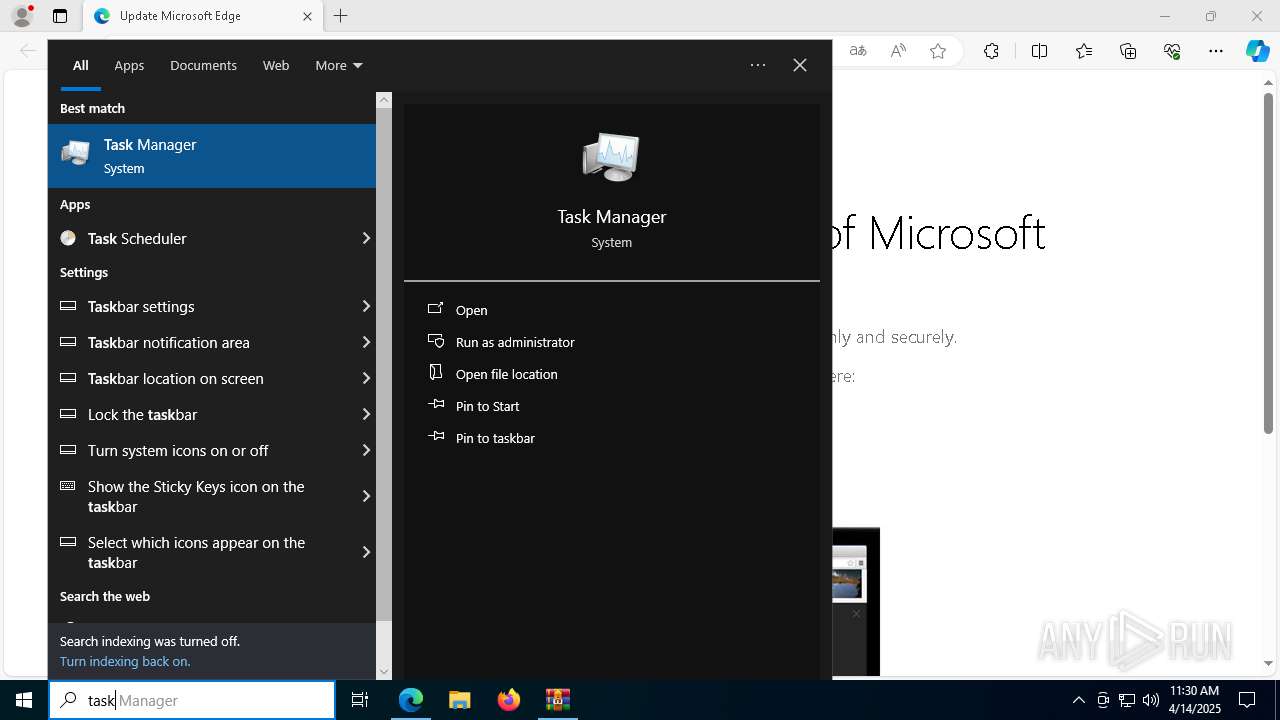
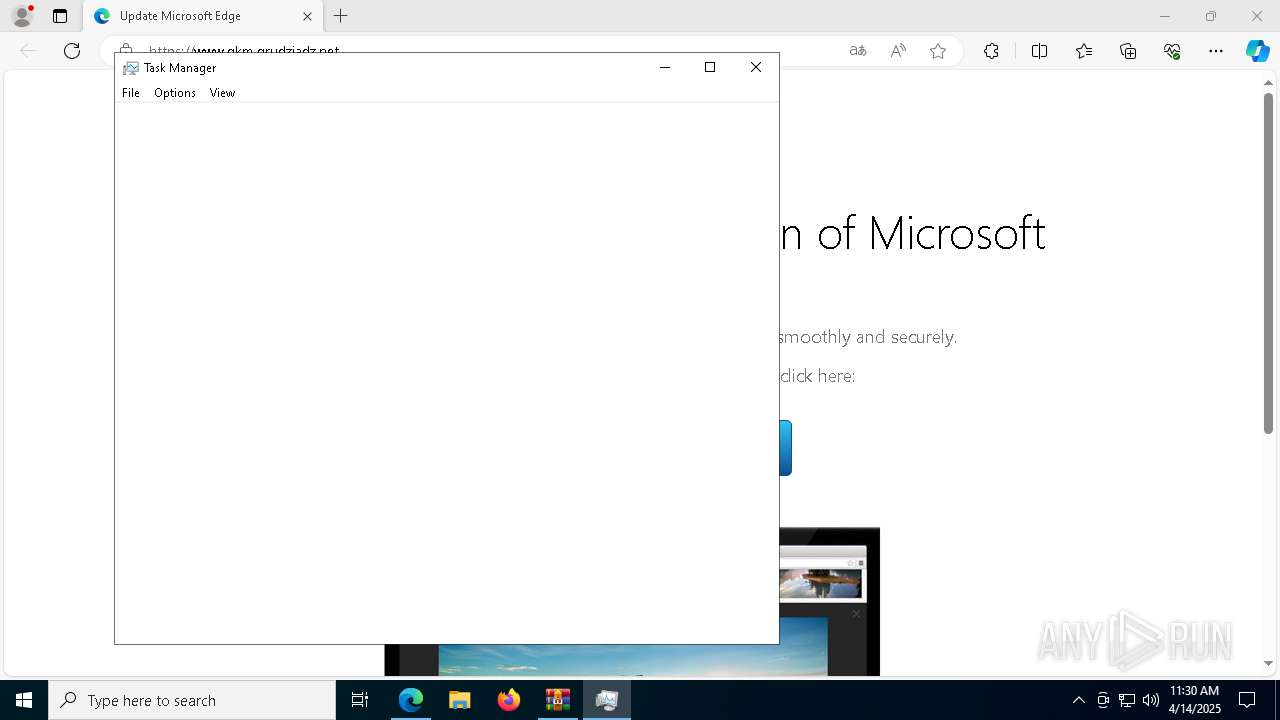
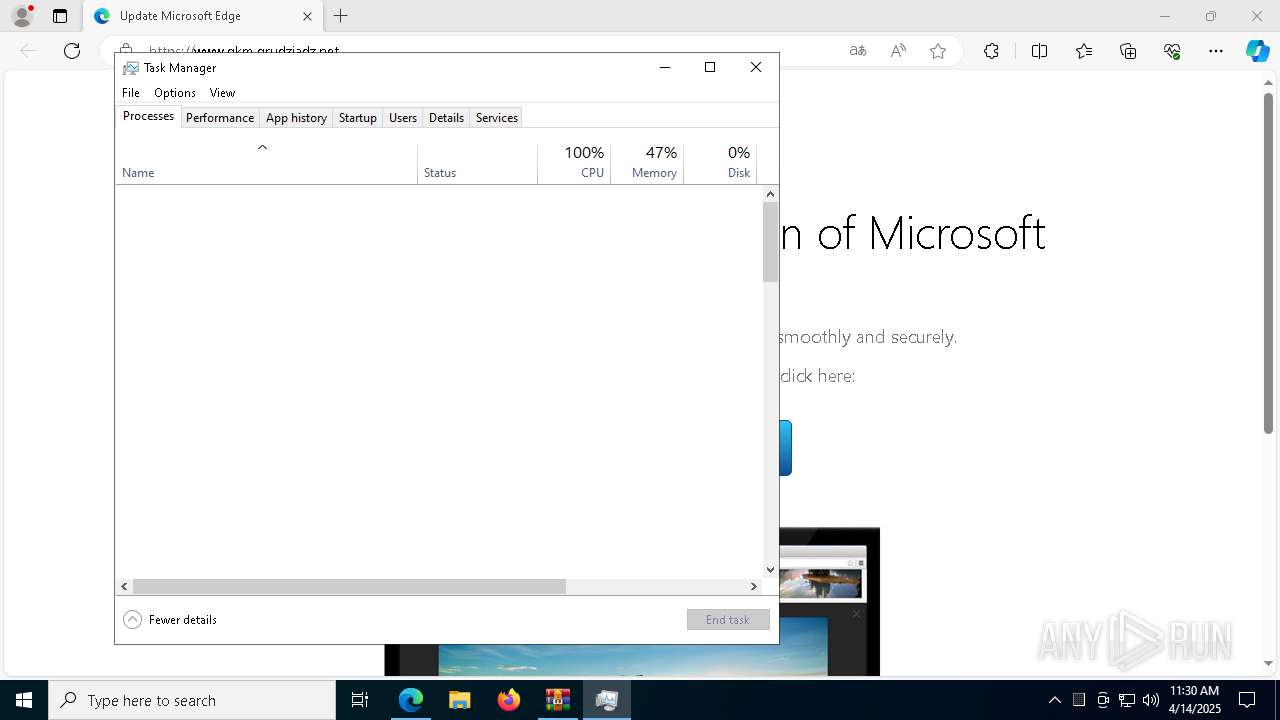
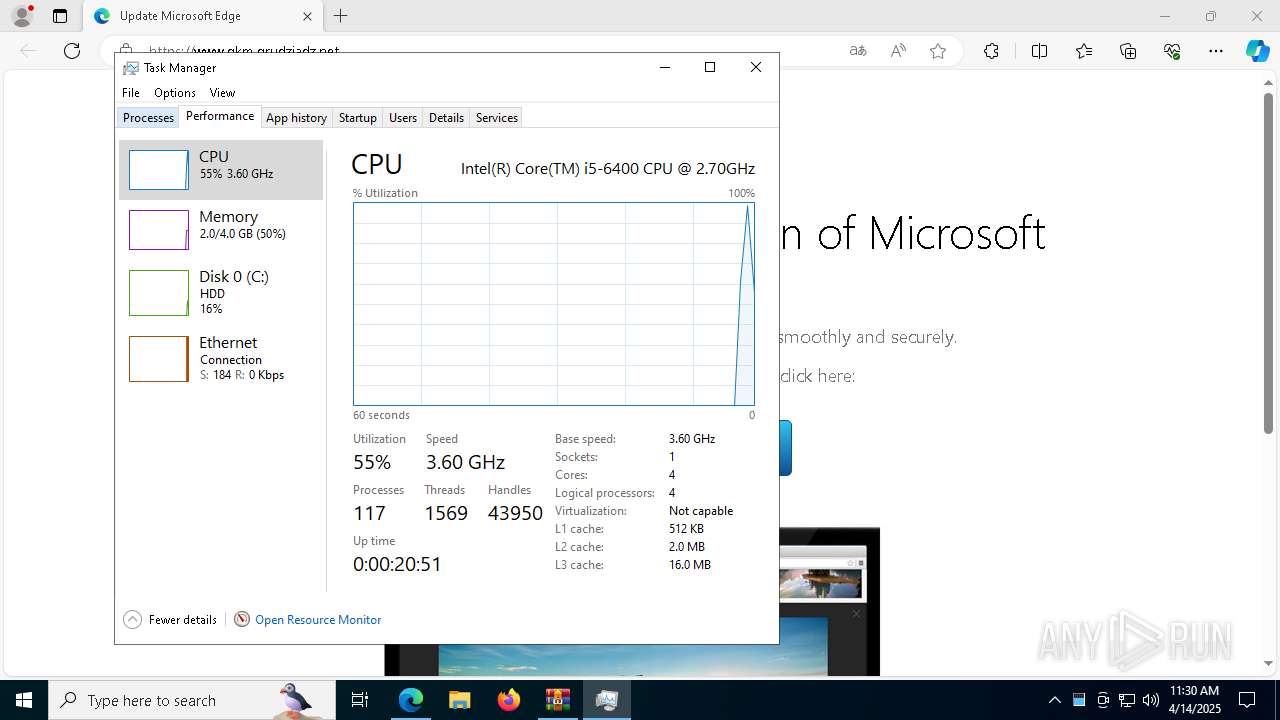
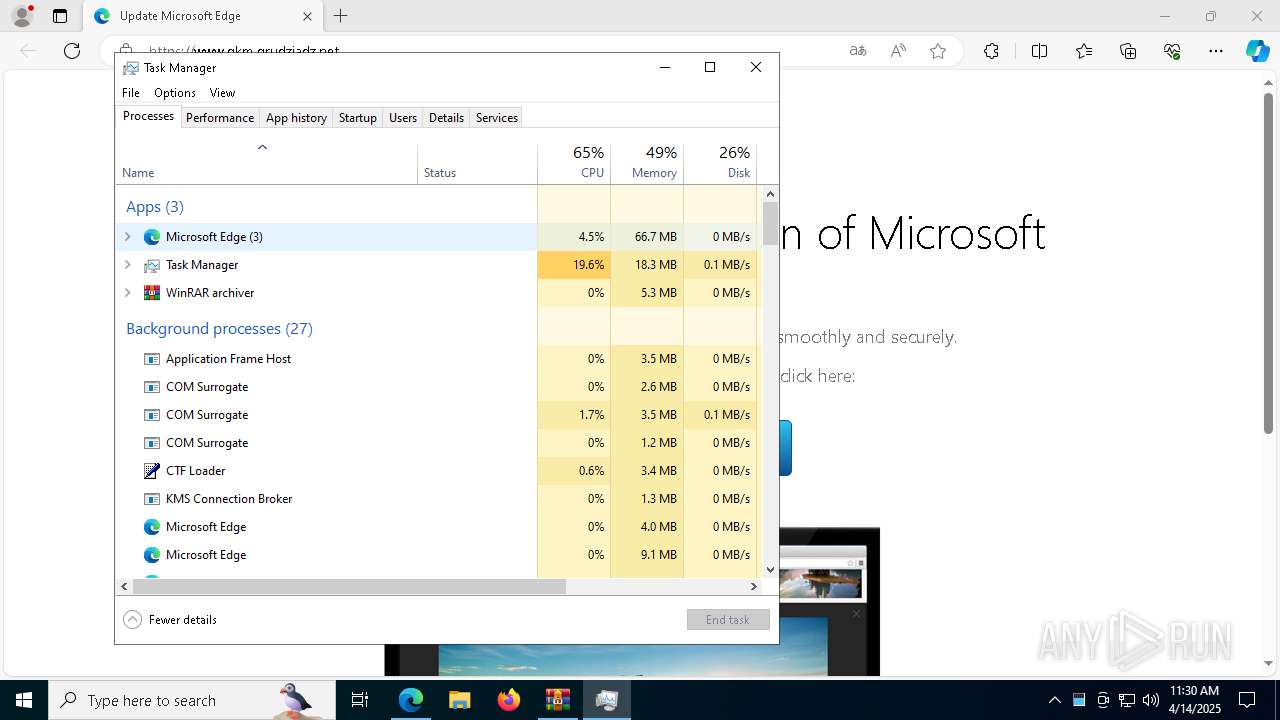
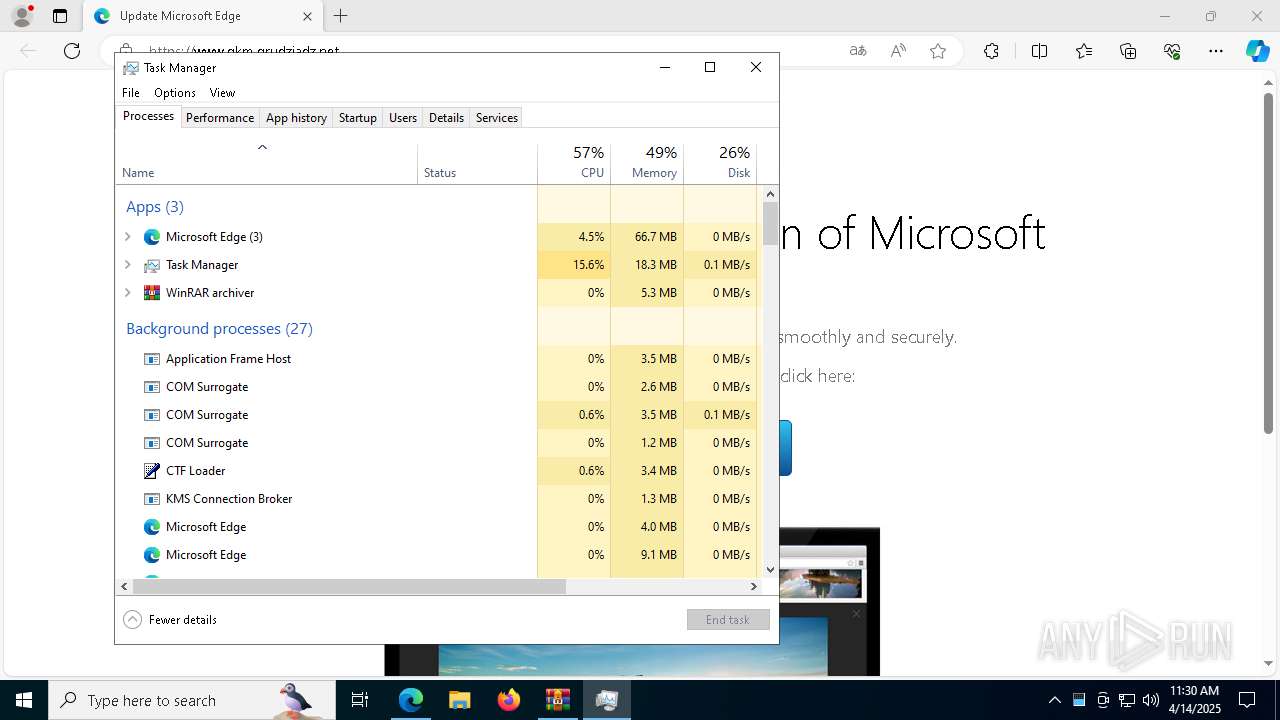
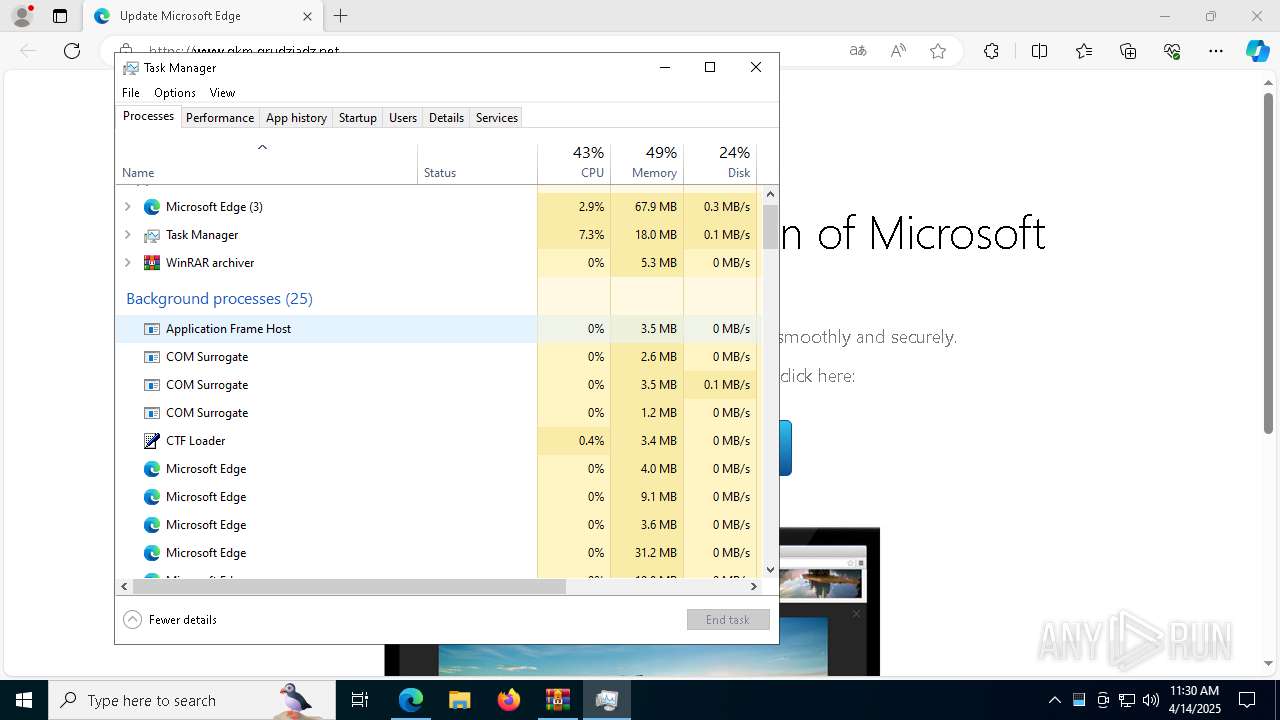
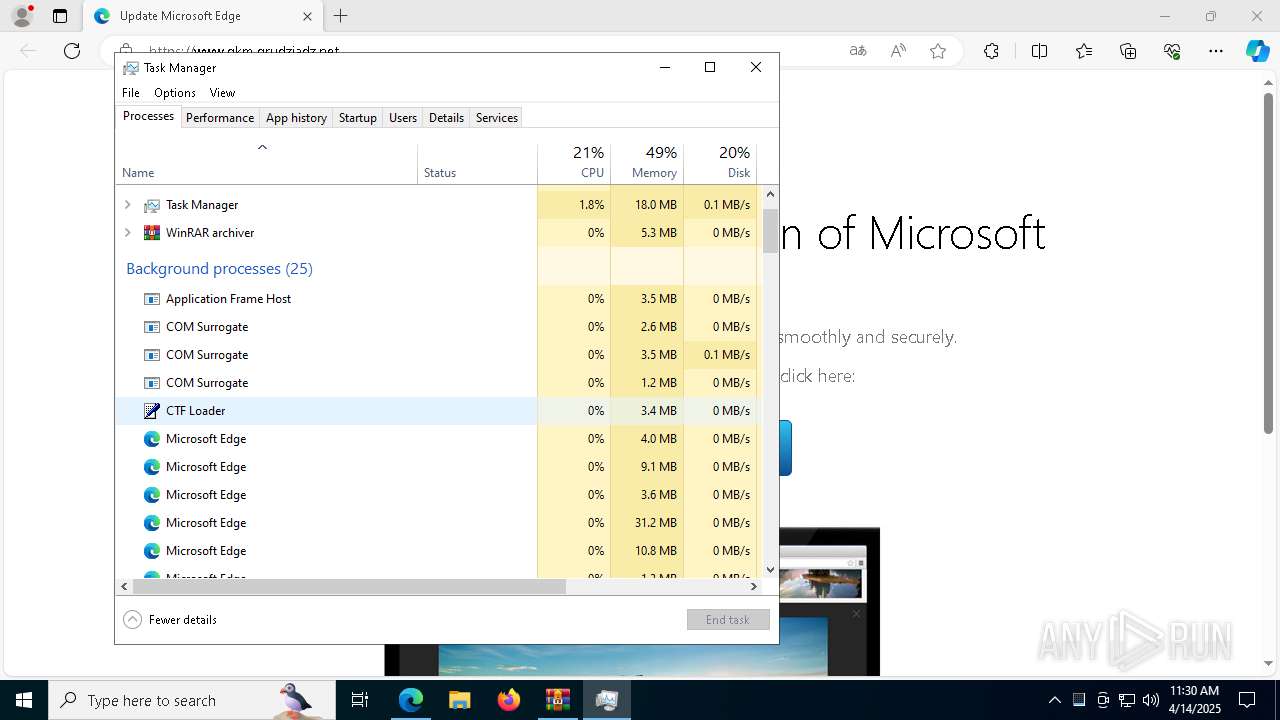
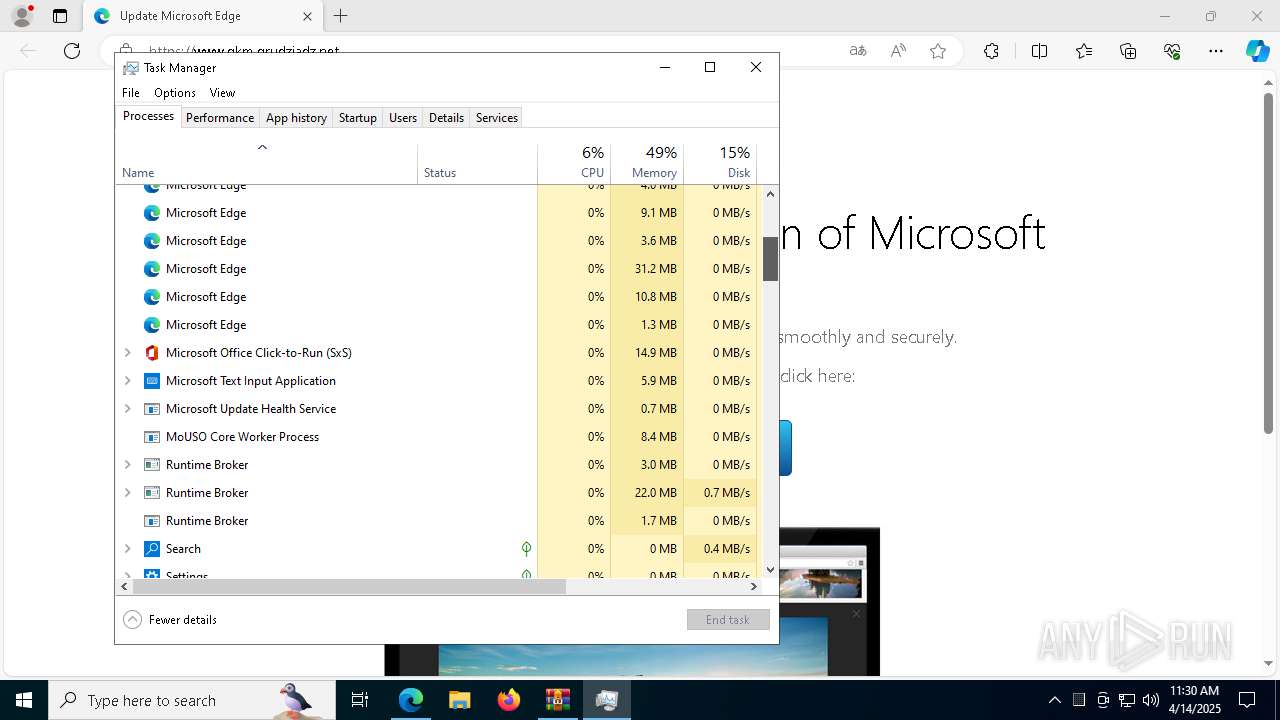
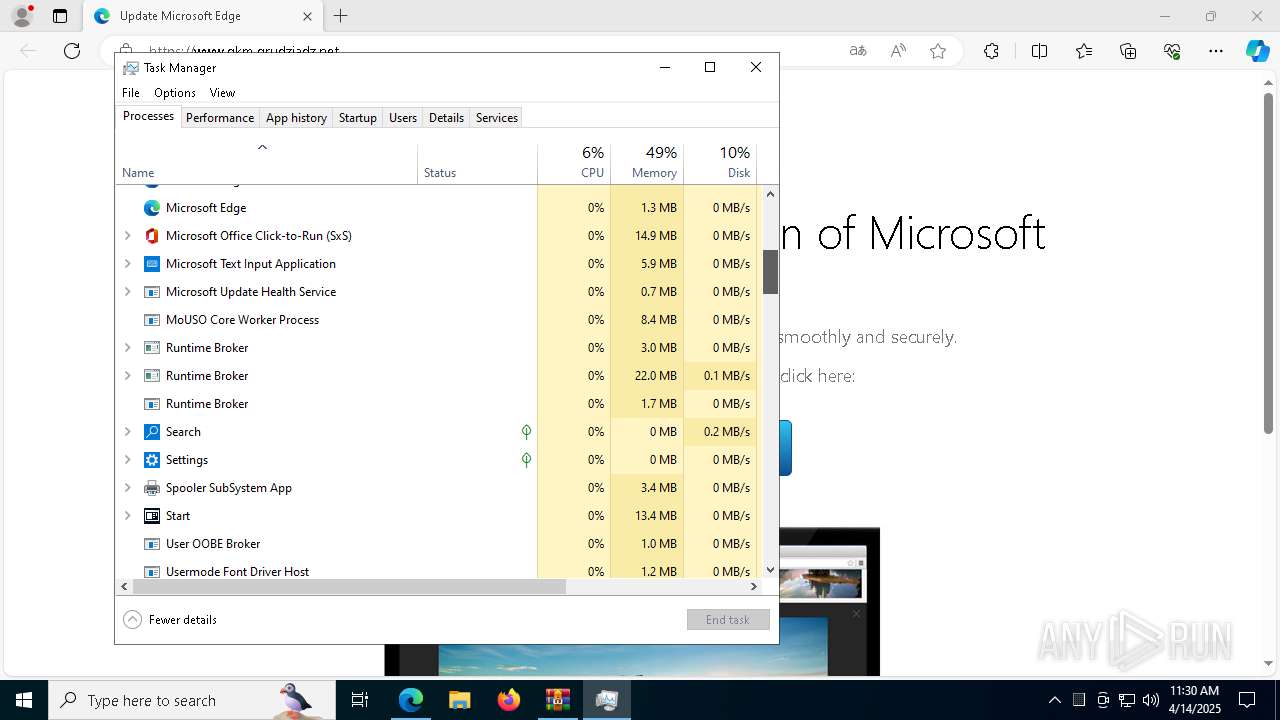
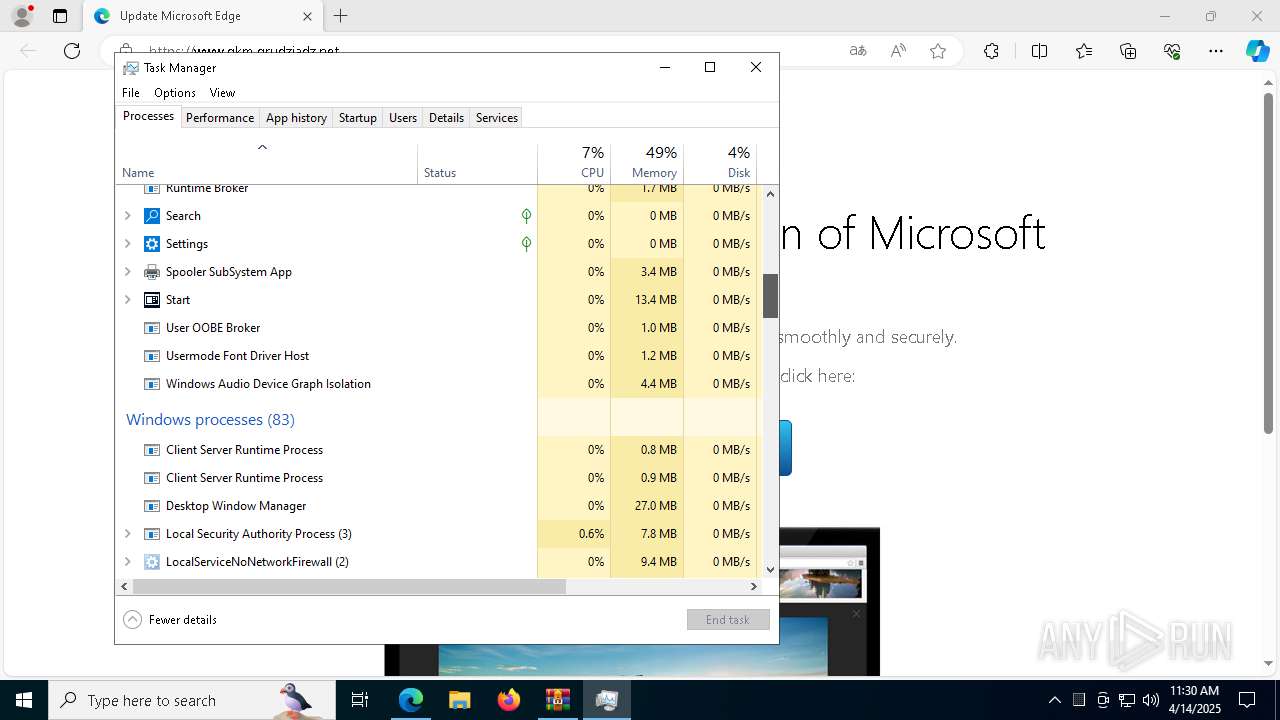
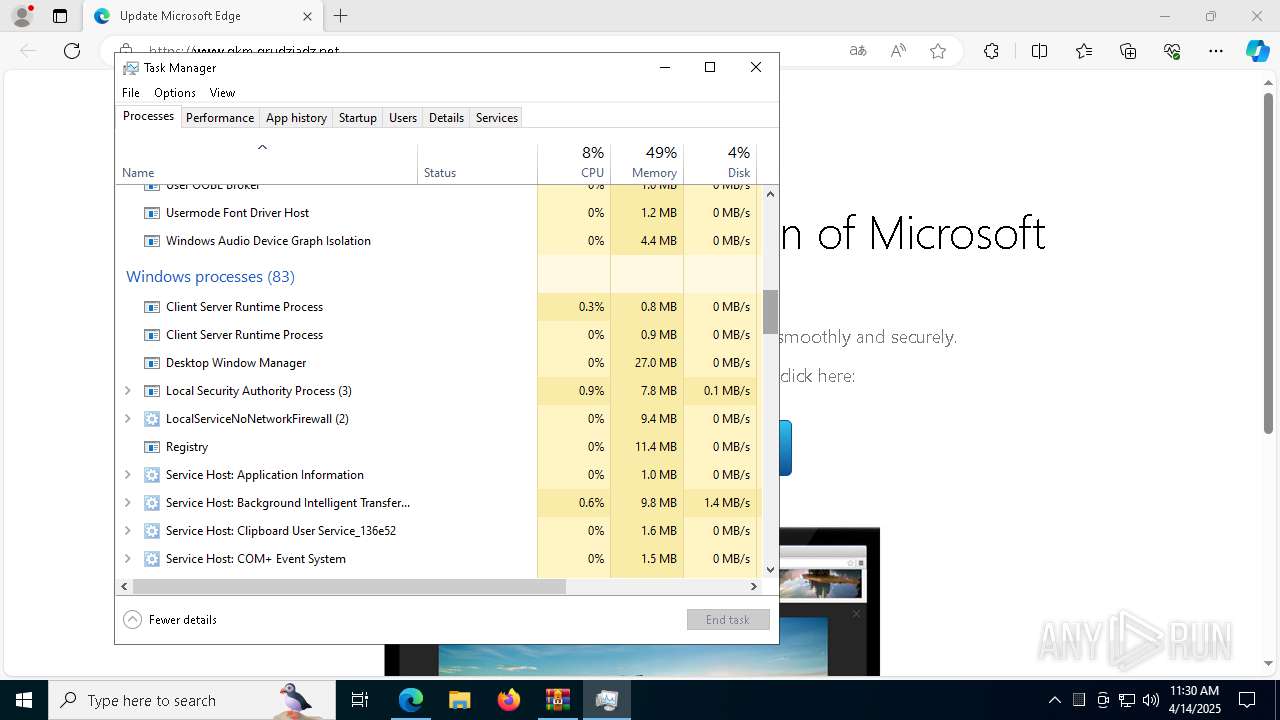
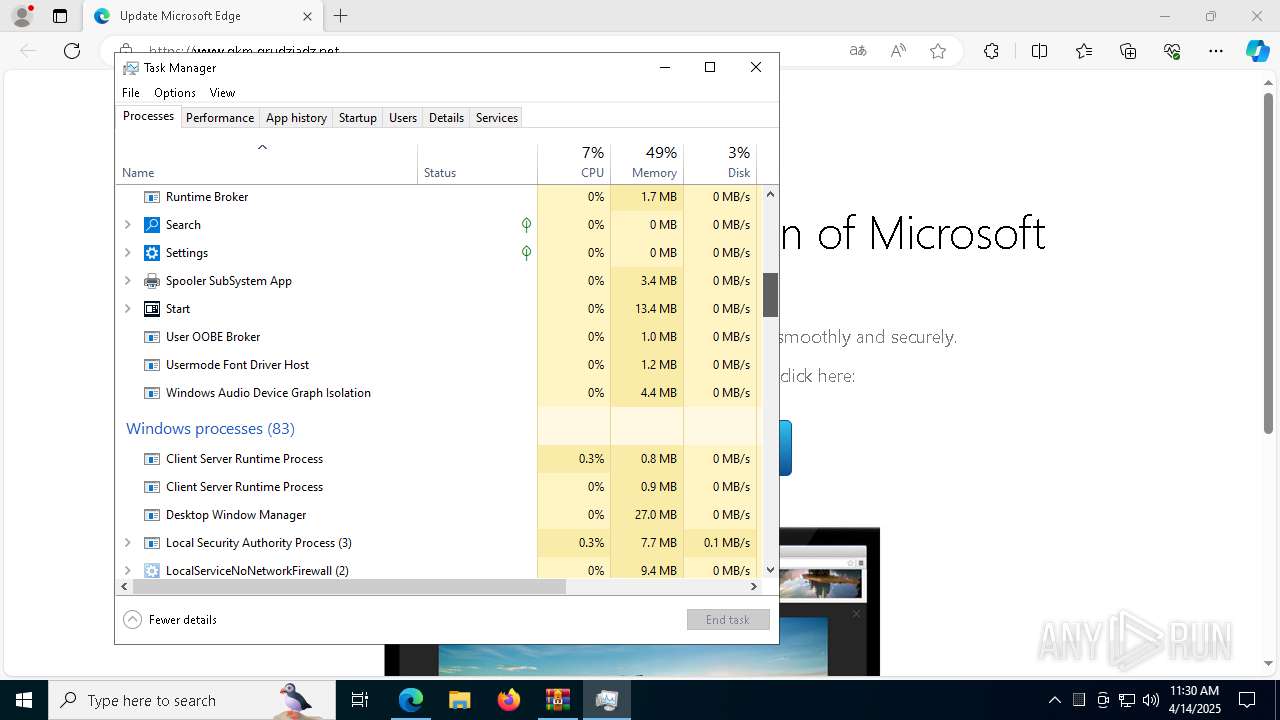
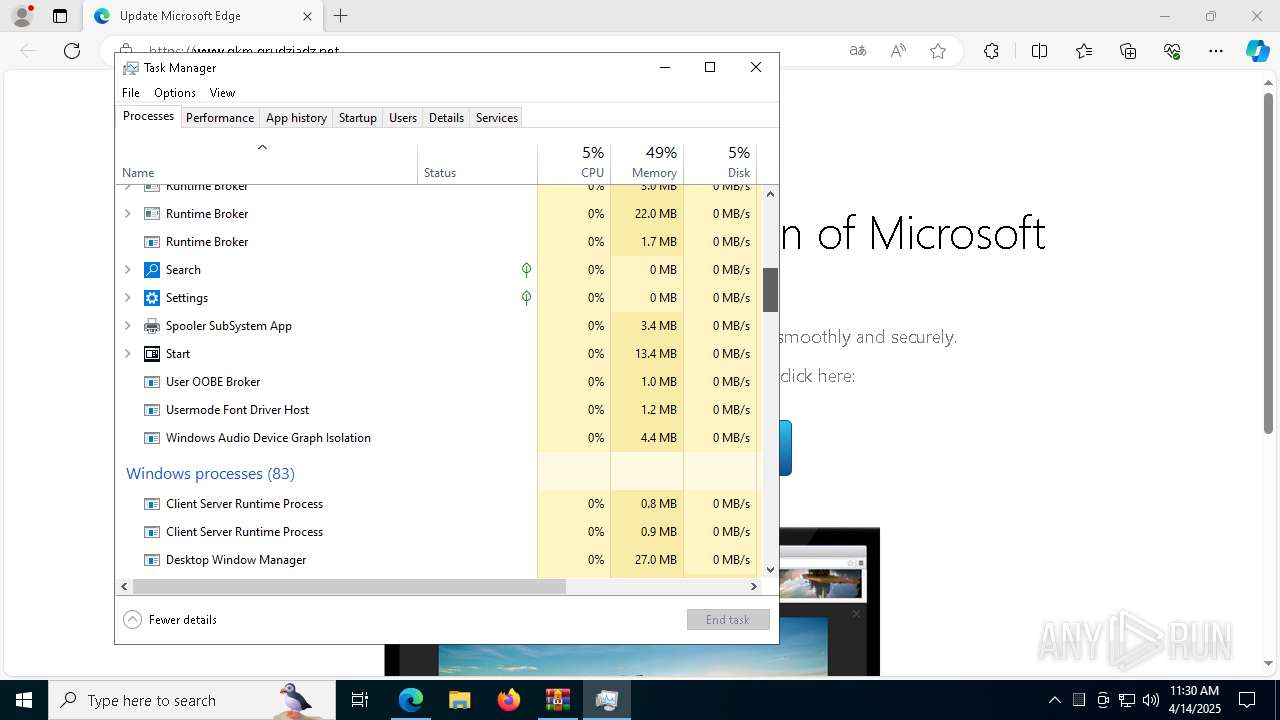
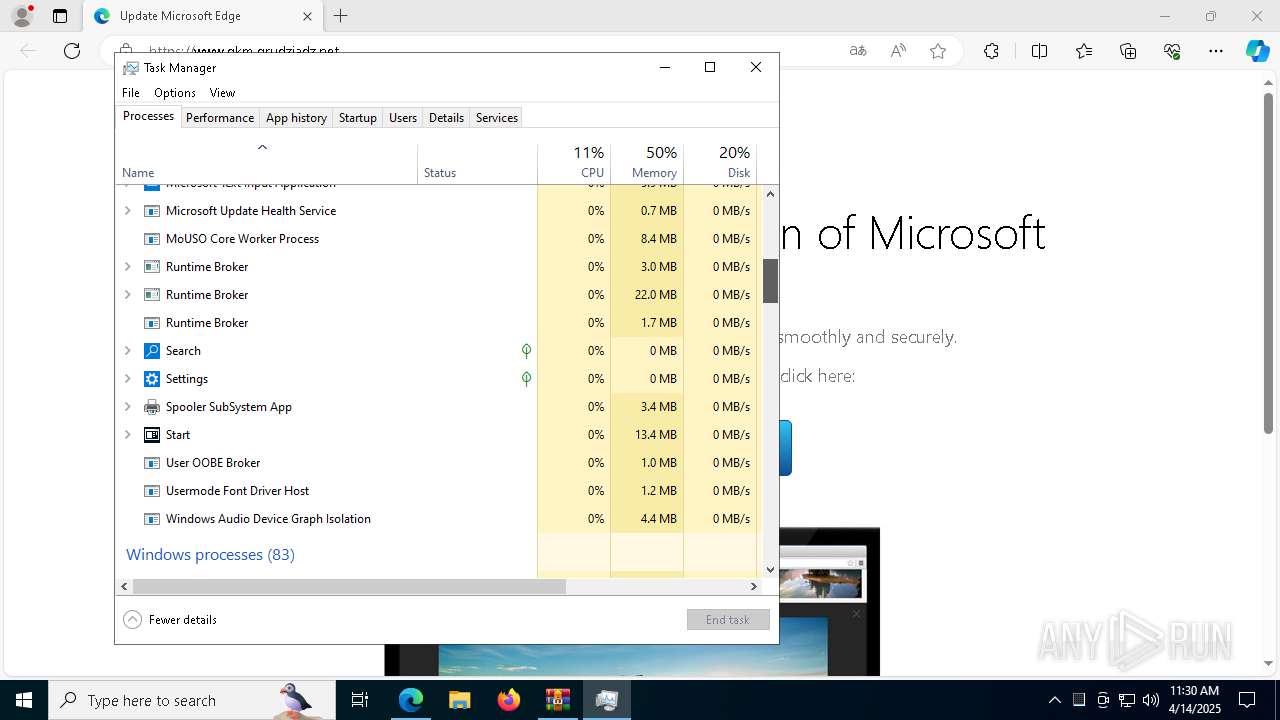
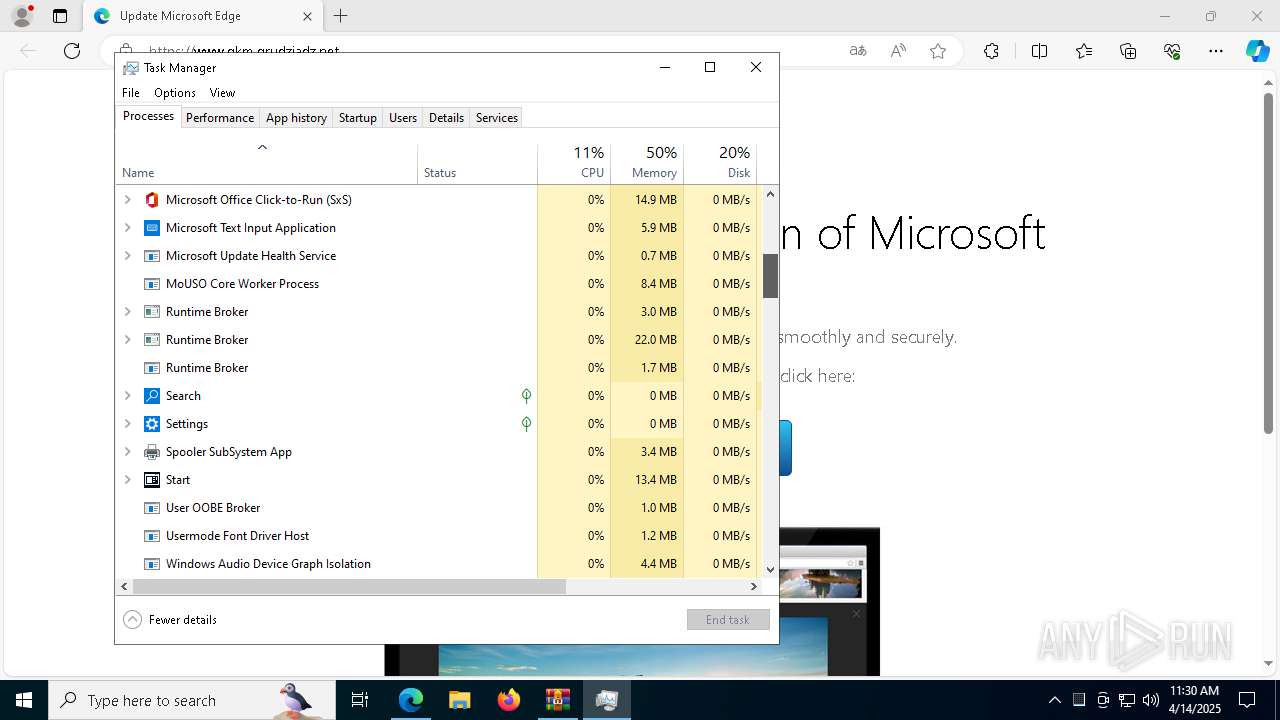
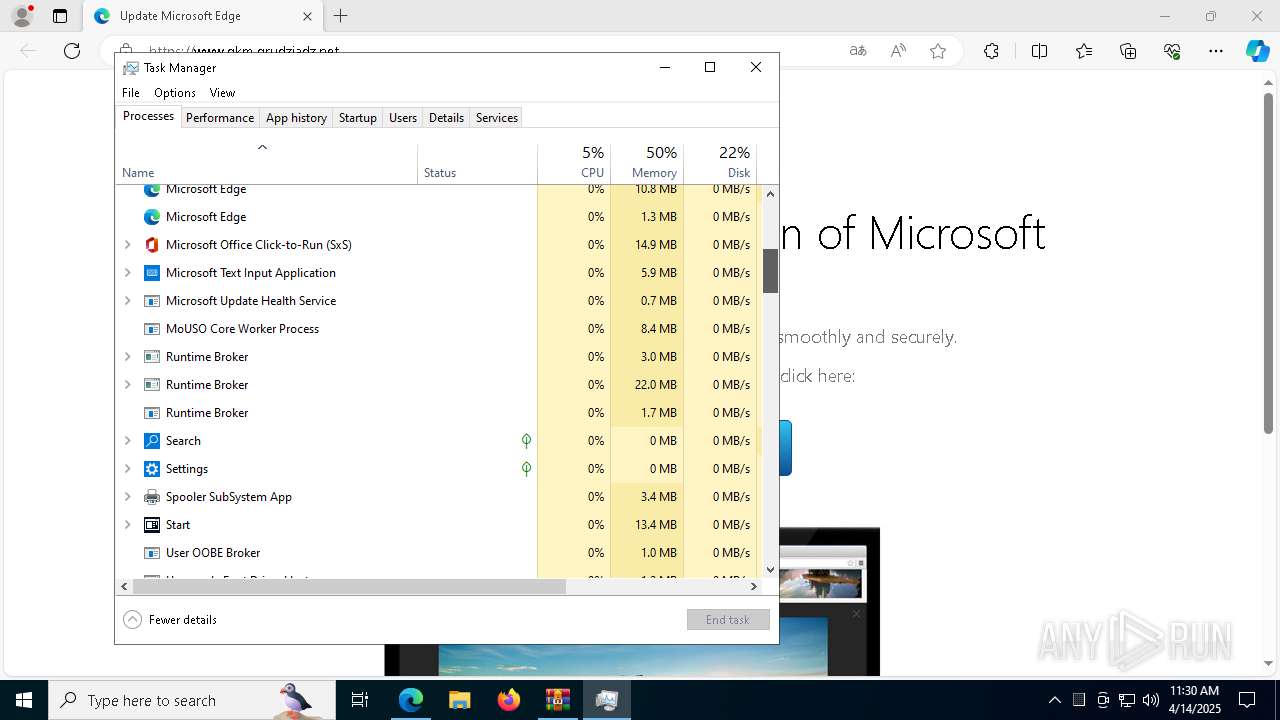
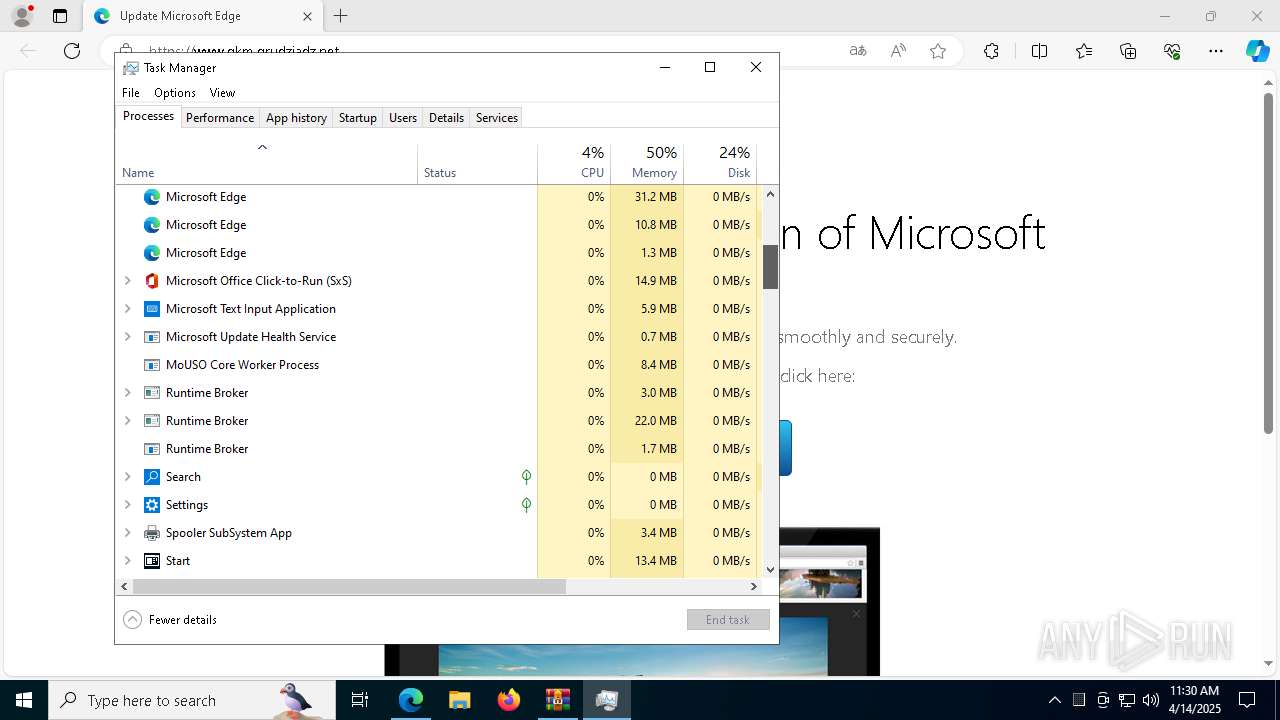
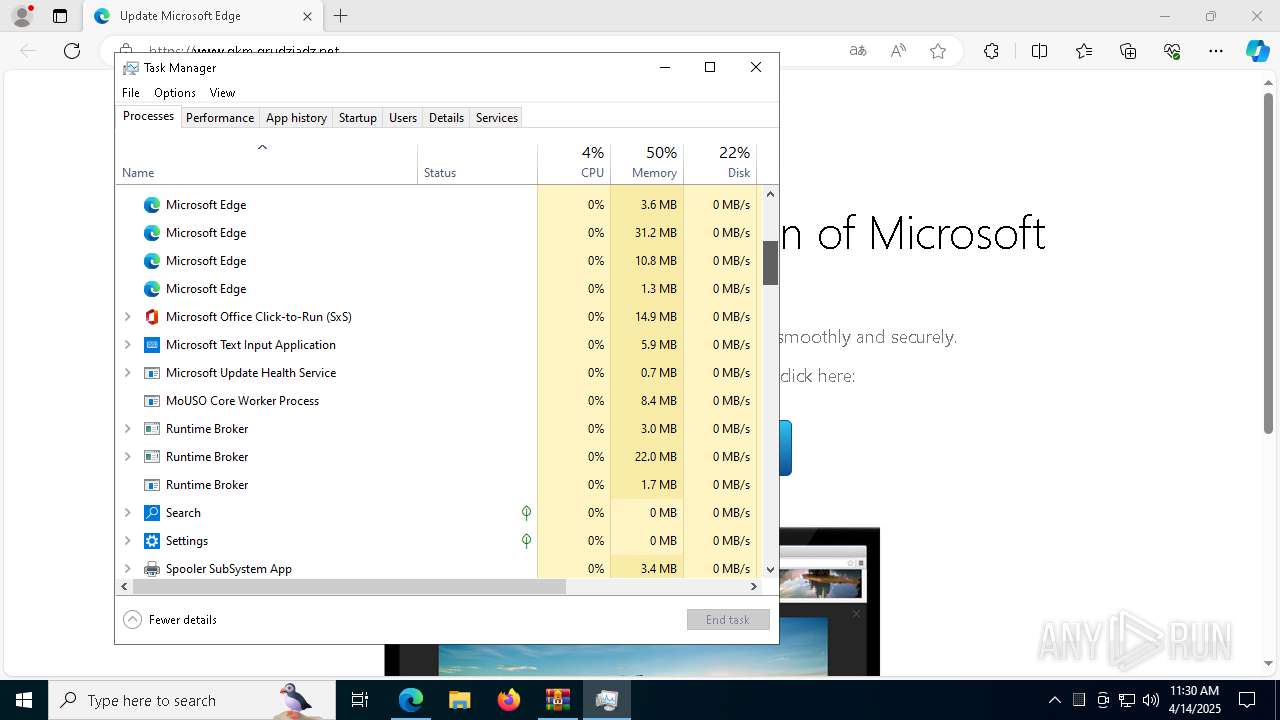
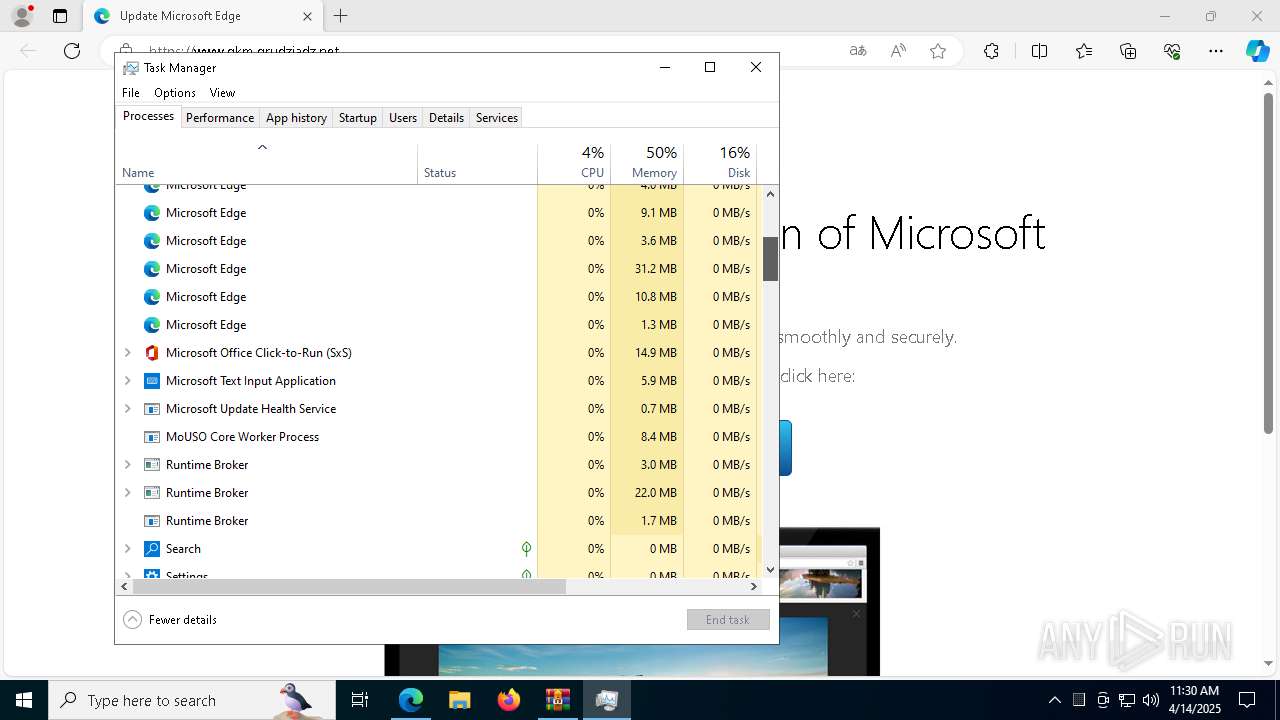
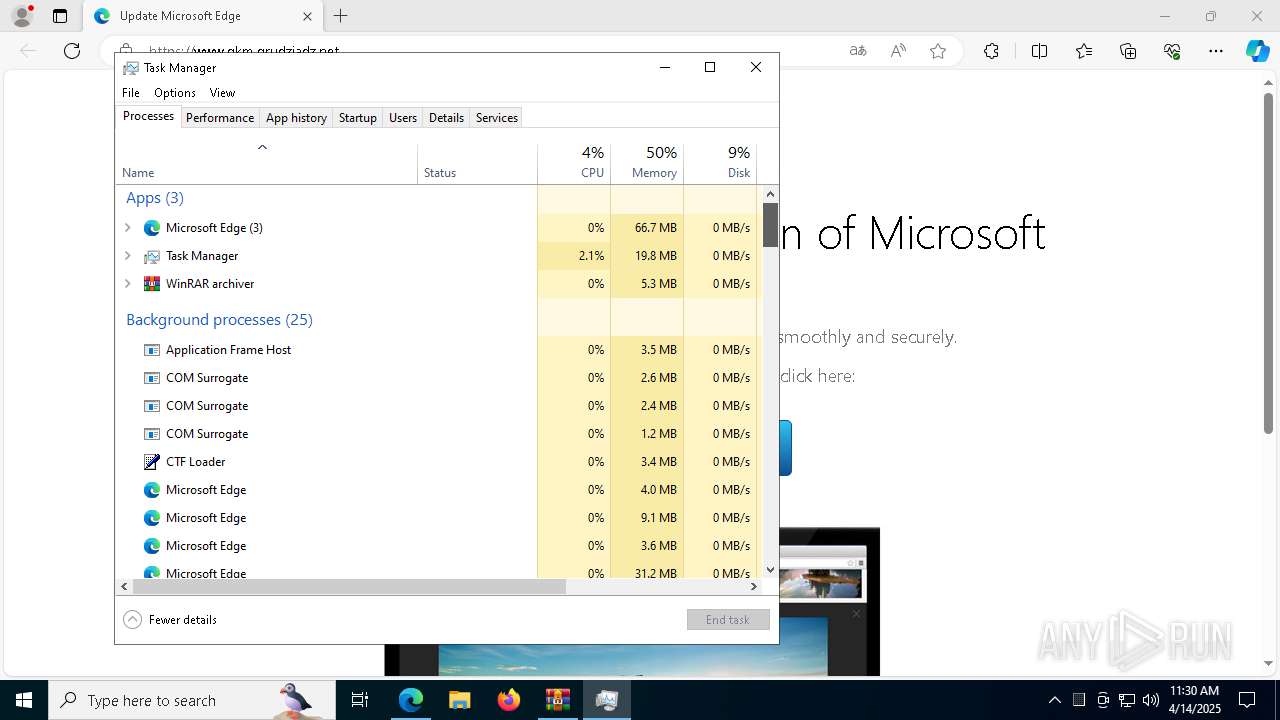
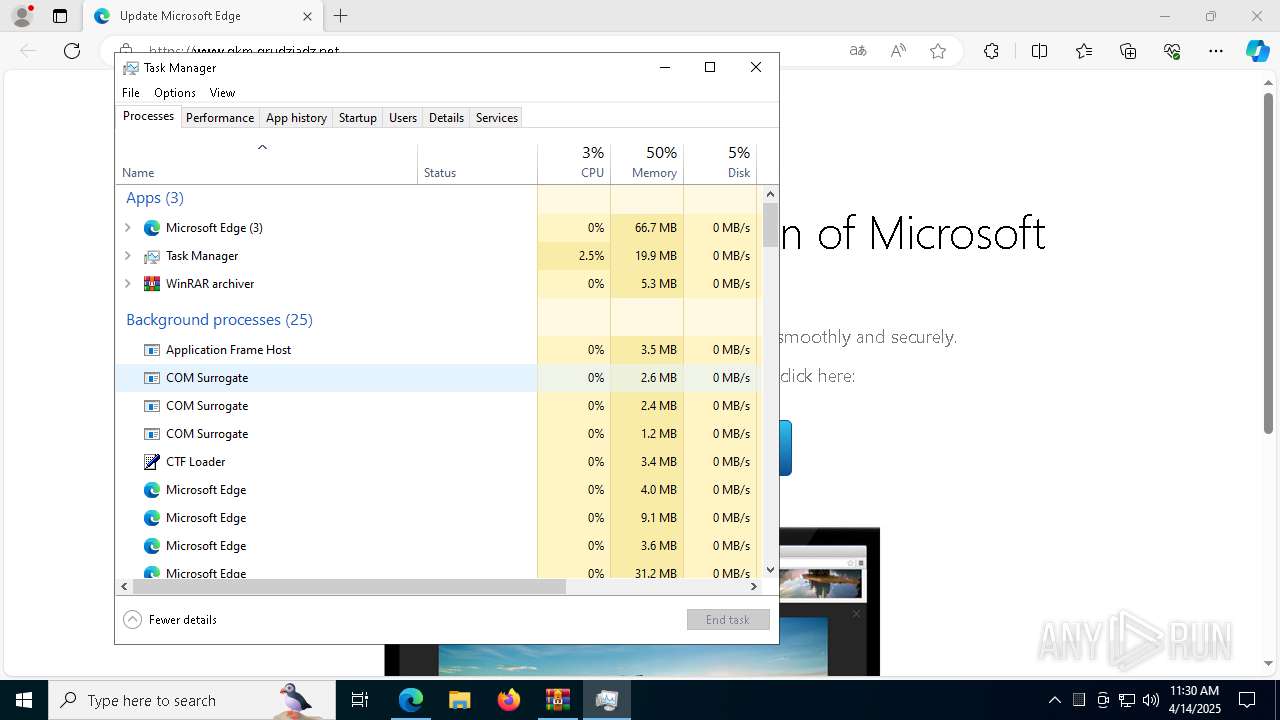
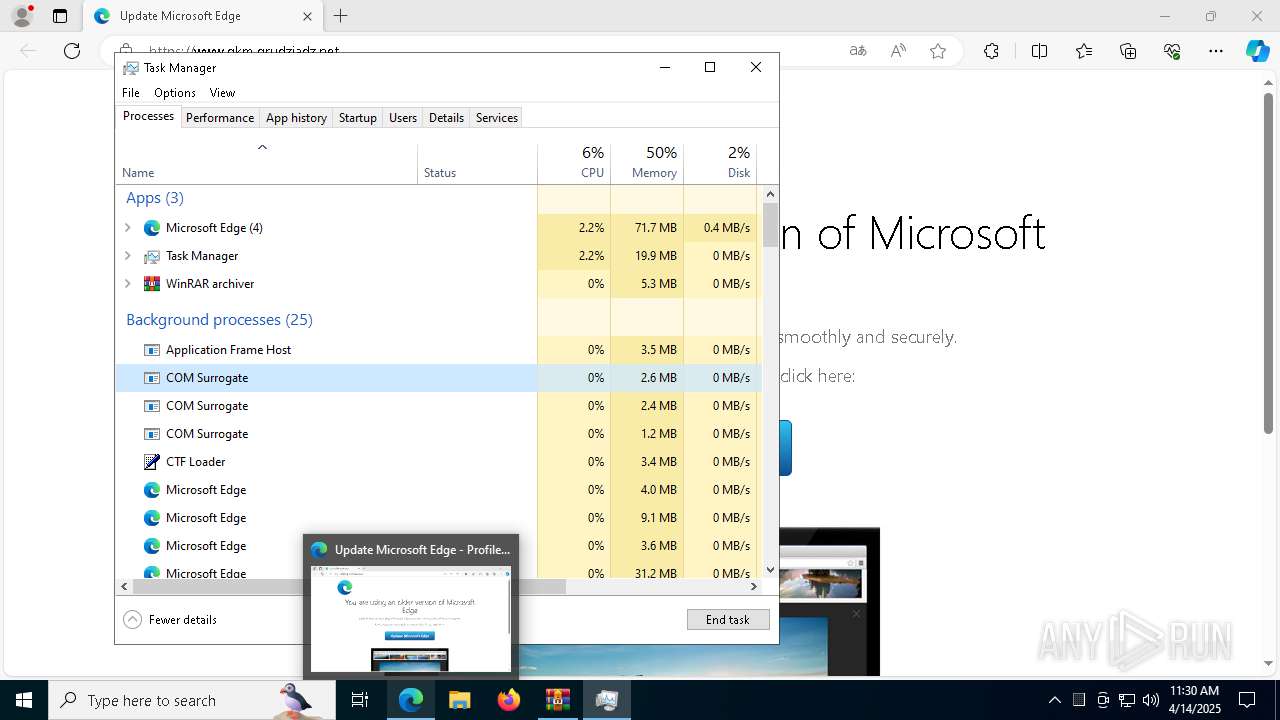
Manual execution by a user
- Taskmgr.exe (PID: 5332)
- Taskmgr.exe (PID: 8064)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 5332)
The sample compiled with english language support
- msedge.exe (PID: 5736)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 5260)
Executable content was dropped or overwritten
- msedge.exe (PID: 5736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
191
Monitored processes
58
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5576 --field-trial-handle=2384,i,16419622578657935013,8087586472593203752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3824 --field-trial-handle=2384,i,16419622578657935013,8087586472593203752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa5084.43545\Update.js" | C:\Windows\System32\wscript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6712 --field-trial-handle=2384,i,16419622578657935013,8087586472593203752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6476 --field-trial-handle=2384,i,16419622578657935013,8087586472593203752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6852 --field-trial-handle=2384,i,16419622578657935013,8087586472593203752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2392 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=4380 --field-trial-handle=2384,i,16419622578657935013,8087586472593203752,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2596 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6716 --field-trial-handle=2384,i,16419622578657935013,8087586472593203752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6192 --field-trial-handle=2384,i,16419622578657935013,8087586472593203752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
17 338
Read events
17 303
Write events
34
Delete events
1
Modification events
| (PID) Process: | (5280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5280) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A2E7EC9F51912F00 | |||
| (PID) Process: | (5280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8615760B-5D23-4846-8E2C-05EF4C8C8CB3} | |||
| (PID) Process: | (5280) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 52C4F49F51912F00 | |||
| (PID) Process: | (5280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (5280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (5280) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 327342A051912F00 | |||
Executable files
12
Suspicious files
381
Text files
190
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b7b9.TMP | — | |
MD5:— | SHA256:— | |||
| 5280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b7c9.TMP | — | |
MD5:— | SHA256:— | |||
| 5280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b7c9.TMP | — | |
MD5:— | SHA256:— | |||
| 5280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b7d8.TMP | — | |
MD5:— | SHA256:— | |||
| 5280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b7b9.TMP | — | |
MD5:— | SHA256:— | |||
| 5280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
110
DNS requests
104
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8132 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8132 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
920 | wscript.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCECO3bePBuysaUZYeCOq3ZOg%3D | unknown | — | — | whitelisted |
920 | wscript.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
3896 | svchost.exe | HEAD | 200 | 23.48.23.41:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744955548&P2=404&P3=2&P4=bI1JvJguLPtt7PUQ9BqfwHS7K7w%2b4rVB8PHwywzB4jioam2YeBTcHPU%2f48EUJXE65DqSnrBuytRYA6EjRKSpSA%3d%3d | unknown | — | — | whitelisted |
3896 | svchost.exe | GET | 206 | 23.48.23.41:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744955548&P2=404&P3=2&P4=bI1JvJguLPtt7PUQ9BqfwHS7K7w%2b4rVB8PHwywzB4jioam2YeBTcHPU%2f48EUJXE65DqSnrBuytRYA6EjRKSpSA%3d%3d | unknown | — | — | whitelisted |
5260 | powershell.exe | GET | 504 | 173.44.141.44:80 | http://aszze4rggizue.top/f79.svg | unknown | — | — | unknown |
3896 | svchost.exe | GET | 206 | 23.48.23.41:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744955548&P2=404&P3=2&P4=gvvcx8XRNdDlx9IhFgrxrSzVUUTXwEOp0Wh18ozWeCxaKxuz9B7OvvRBjMR5hZhRw1L%2bWjXxWMYIuqp4l6cnXw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7368 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5280 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7368 | msedge.exe | 150.171.30.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7368 | msedge.exe | 185.144.174.7:80 | www.gkm.grudziadz.net | Perfect-net Jaroslaw Dziubek | PL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.gkm.grudziadz.net |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7368 | msedge.exe | Potentially Bad Traffic | ET INFO Referrer-Policy set to unsafe-url |
7368 | msedge.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT Malicious TA2726 TDS Domain in DNS Lookup (blacksaltys .com) |
7368 | msedge.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT Malicious TA2726 TDS Domain in DNS Lookup (blacksaltys .com) |
7368 | msedge.exe | Possible Social Engineering Attempted | FRAUD [ANY.RUN] Suspected Fraud domain by CrossDomain (blacksaltys .com) |
7368 | msedge.exe | Possible Social Engineering Attempted | FRAUD [ANY.RUN] Suspected Fraud domain by CrossDomain (blacksaltys .com) |
7368 | msedge.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT Malicious TA2726 TDS Domain in TLS SNI (blacksaltys .com) |
7368 | msedge.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in DNS Lookup (virtual .urban-orthodontics .com) |
7368 | msedge.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in DNS Lookup (virtual .urban-orthodontics .com) |
7368 | msedge.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in TLS SNI (virtual .urban-orthodontics .com) |
7368 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |