| File name: | HskDDNS_5.0.0.21724.exe |
| Full analysis: | https://app.any.run/tasks/38391ed1-0860-42fc-9de3-b0194ff903f0 |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 07:53:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 78FC0052D63A8B68D7000F47F9AA81D8 |
| SHA1: | 9567F025A68EFF7D22503A98101177505EA26FEF |
| SHA256: | 950E4BCF1841481B53E2C8C7774BE2F1A09C20BE5F8AEDCEB8AC65B05D6CBB70 |
| SSDEEP: | 98304:9rC2JcwApx3vqm5h0wCqNo3alPapkk37i86ZRlR+X22aCffy4aO8JOQjhVXtd5uA:kRTN5h01qN4a9aZIZNvhXpOQjpdIJ0h5 |
MALICIOUS
Changes the autorun value in the registry
- HskDDNS_5.0.0.21724.exe (PID: 3896)
- HskDDNS.exe (PID: 1972)
Application was dropped or rewritten from another process
- phtunnel.exe (PID: 2284)
- HskDDNSMaint.exe (PID: 3196)
Loads dropped or rewritten executable
- HskDDNSMaint.exe (PID: 3196)
- WerFault.exe (PID: 3064)
SUSPICIOUS
Creates files in the program directory
- HskDDNS_5.0.0.21724.exe (PID: 3896)
- phtunnel.exe (PID: 2284)
- HskDDNS.exe (PID: 1972)
- WerFault.exe (PID: 3064)
Executed as Windows Service
- phtunnel.exe (PID: 2284)
Application launched itself
- HskDDNS_5.0.0.21724.exe (PID: 3048)
Creates a software uninstall entry
- HskDDNS_5.0.0.21724.exe (PID: 3896)
Executable content was dropped or overwritten
- HskDDNS_5.0.0.21724.exe (PID: 3896)
Creates files in the Windows directory
- phtunnel.exe (PID: 2284)
- HskDDNS.exe (PID: 3732)
- WerFault.exe (PID: 3064)
Starts itself from another location
- HskDDNS_5.0.0.21724.exe (PID: 3896)
Removes files from Windows directory
- WerFault.exe (PID: 3064)
INFO
Application was crashed
- HskDDNS.exe (PID: 3732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:24 22:27:10+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 5787648 |
| InitializedDataSize: | 462848 |
| UninitializedDataSize: | 5349376 |
| EntryPoint: | 0xa9fbd0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.0.21724 |
| ProductVersionNumber: | 5.0.0.21724 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
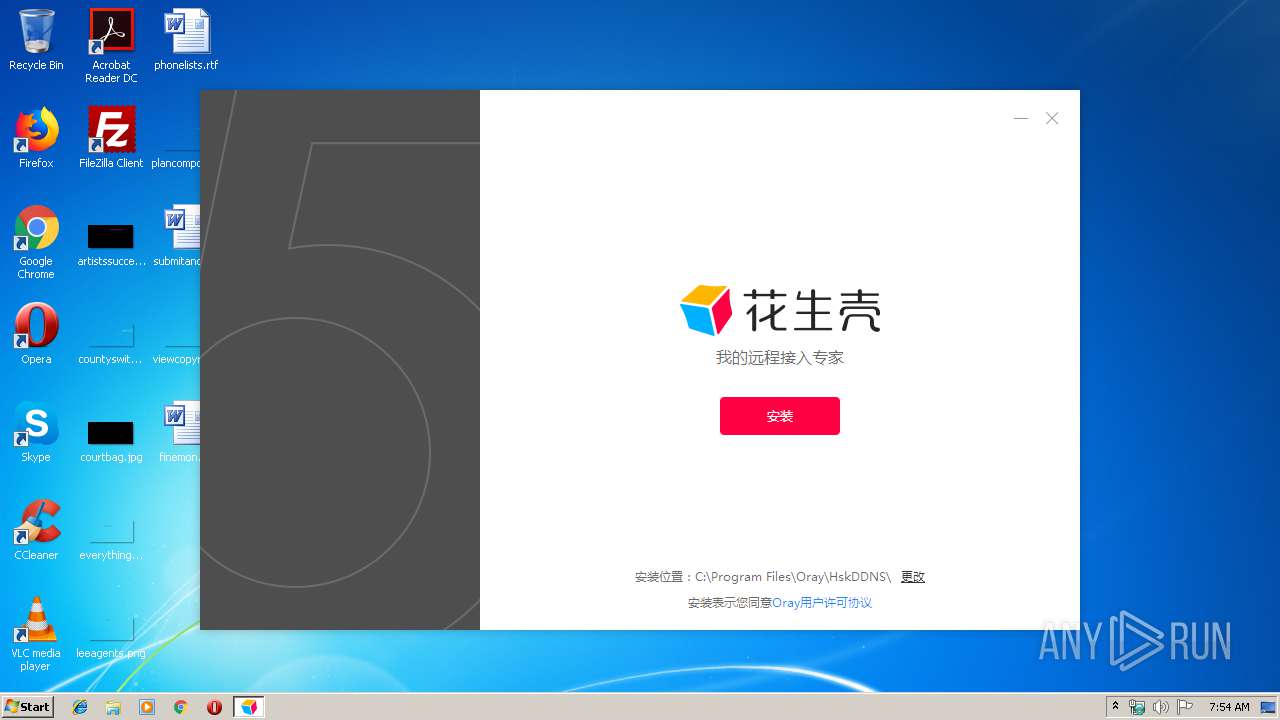
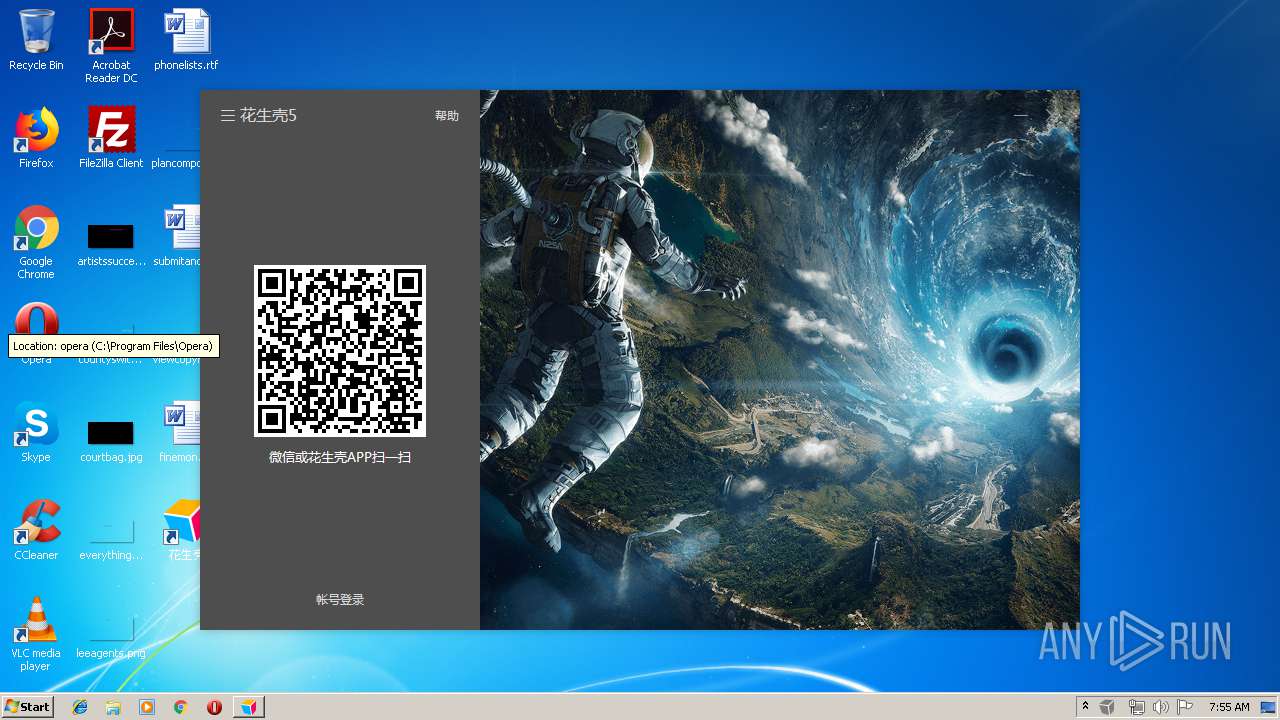
| Comments: | 花生壳程序 |
| CompanyName: | 上海贝锐信息科技股份有限公司 |
| FileDescription: | 花生壳程序 |
| FileVersion: | 5.0.0.21724 |
| InternalName: | HskDDNS.exe |
| LegalCopyright: | 上海贝锐 版权所有 |
| OriginalFileName: | HskDDNS.exe |
| ProductName: | 花生壳动态域名 |
| ProductVersion: | 5.0.0.21724 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Jun-2019 20:27:10 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000140 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 24-Jun-2019 20:27:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0051A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0051B000 | 0x00585000 | 0x00585000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.85281 |
.rsrc | 0x00AA0000 | 0x00071000 | 0x00070400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.44856 |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSIMG32.dll |
OLEAUT32.dll |
SHELL32.dll |
Total processes
47
Monitored processes
7
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1972 | "C:\Program Files\Oray\HskDDNS\HskDDNS.exe" | C:\Program Files\Oray\HskDDNS\HskDDNS.exe | HskDDNS_5.0.0.21724.exe | ||||||||||||
User: admin Company: 上海贝锐信息科技股份有限公司 Integrity Level: HIGH Description: 花生壳程序 Exit code: 0 Version: 5.0.0.21724 Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Oray\HskDDNS\phtunnel.exe" -S -v | C:\Program Files\Oray\HskDDNS\phtunnel.exe | services.exe | ||||||||||||
User: SYSTEM Company: 上海贝锐信息科技股份有限公司 Integrity Level: SYSTEM Description: 花生壳程序 Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3048 | "C:\Users\admin\AppData\Local\Temp\HskDDNS_5.0.0.21724.exe" | C:\Users\admin\AppData\Local\Temp\HskDDNS_5.0.0.21724.exe | — | explorer.exe | |||||||||||
User: admin Company: 上海贝锐信息科技股份有限公司 Integrity Level: MEDIUM Description: 花生壳程序 Exit code: 0 Version: 5.0.0.21724 Modules
| |||||||||||||||
| 3064 | C:\Windows\system32\WerFault.exe -u -p 3732 -s 1088 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3196 | "C:\Program Files\Oray\HskDDNS\HskDDNSMaint.exe" 2284 0 HskService | C:\Program Files\Oray\HskDDNS\HskDDNSMaint.exe | phtunnel.exe | ||||||||||||
User: SYSTEM Company: Shanghai Best Oray Integrity Level: SYSTEM Description: SunLogin Clients Maintainence Process Exit code: 0 Version: 3, 5, 18, 18283 Modules
| |||||||||||||||
| 3732 | "C:\Program Files\Oray\HskDDNS\HskDDNS.exe" --mod=localscan -i 0 -w 85.203.20.11 | C:\Program Files\Oray\HskDDNS\HskDDNS.exe | phtunnel.exe | ||||||||||||
User: SYSTEM Company: 上海贝锐信息科技股份有限公司 Integrity Level: SYSTEM Description: 花生壳程序 Exit code: 255 Version: 5.0.0.21724 Modules
| |||||||||||||||
| 3896 | "C:\Users\admin\AppData\Local\Temp\HskDDNS_5.0.0.21724.exe" "C:\Users\admin\AppData\Local\Temp\HskDDNS_5.0.0.21724.exe" | C:\Users\admin\AppData\Local\Temp\HskDDNS_5.0.0.21724.exe | HskDDNS_5.0.0.21724.exe | ||||||||||||
User: admin Company: 上海贝锐信息科技股份有限公司 Integrity Level: HIGH Description: 花生壳程序 Exit code: 0 Version: 5.0.0.21724 Modules
| |||||||||||||||
Total events
647
Read events
605
Write events
42
Delete events
0
Modification events
| (PID) Process: | (3048) HskDDNS_5.0.0.21724.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3048) HskDDNS_5.0.0.21724.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3896) HskDDNS_5.0.0.21724.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HskDDNS_5_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3896) HskDDNS_5.0.0.21724.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HskDDNS_5_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3896) HskDDNS_5.0.0.21724.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HskDDNS_5_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3896) HskDDNS_5.0.0.21724.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HskDDNS_5_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3896) HskDDNS_5.0.0.21724.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HskDDNS_5_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3896) HskDDNS_5.0.0.21724.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HskDDNS_5_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3896) HskDDNS_5.0.0.21724.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HskDDNS_5_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3896) HskDDNS_5.0.0.21724.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HskDDNS_5_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
4
Suspicious files
1
Text files
97
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3896 | HskDDNS_5.0.0.21724.exe | C:\Program Files\Oray\HskDDNS\oraylog.dll | executable | |
MD5:— | SHA256:— | |||
| 3896 | HskDDNS_5.0.0.21724.exe | C:\ProgramData\HskDDNS\collectdata\equipment_id | text | |
MD5:— | SHA256:— | |||
| 2284 | phtunnel.exe | C:\Windows\system32\config\systemprofile\phtunnel.pid | text | |
MD5:— | SHA256:— | |||
| 3896 | HskDDNS_5.0.0.21724.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\花生壳\花生壳.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2284 | phtunnel.exe | C:\Program Files\Oray\HskDDNS\phtunnel.json | text | |
MD5:— | SHA256:— | |||
| 3896 | HskDDNS_5.0.0.21724.exe | C:\Program Files\Oray\HskDDNS\phtunnel.exe | executable | |
MD5:— | SHA256:— | |||
| 3896 | HskDDNS_5.0.0.21724.exe | C:\Users\Public\Desktop\花生壳.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3896 | HskDDNS_5.0.0.21724.exe | C:\Program Files\Oray\HskDDNS\HskDDNS.exe | executable | |
MD5:— | SHA256:— | |||
| 3896 | HskDDNS_5.0.0.21724.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\花生壳\卸载花生壳.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1972 | HskDDNS.exe | C:\Users\admin\AppData\Local\Temp\sapisvr.48x48.png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
8
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3896 | HskDDNS_5.0.0.21724.exe | GET | 200 | 222.73.7.11:80 | http://client.oray.net/feedback/install?isgreen=0&track=oray.com&r=1573890871&version=5.0.0.21724&key=6311a6471a6072b349c1f10ec549e40c&client=ddns | CN | text | 7 b | unknown |
3896 | HskDDNS_5.0.0.21724.exe | POST | 200 | 114.55.209.149:80 | http://ph-tk.oray.com/track | CN | text | 50 b | unknown |
3896 | HskDDNS_5.0.0.21724.exe | POST | 200 | 114.55.209.149:80 | http://ph-tk.oray.com/track | CN | text | 50 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3896 | HskDDNS_5.0.0.21724.exe | 114.55.209.149:80 | ph-tk.oray.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3896 | HskDDNS_5.0.0.21724.exe | 222.73.7.11:80 | client.oray.net | China Telecom (Group) | CN | unknown |
1972 | HskDDNS.exe | 118.31.225.247:443 | hsk-api.oray.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2284 | phtunnel.exe | 47.99.166.140:6061 | phsle5-std01.oray.net | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2284 | phtunnel.exe | 118.31.225.247:443 | hsk-api.oray.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3896 | HskDDNS_5.0.0.21724.exe | 172.217.21.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ph-tk.oray.com |
| unknown |
client.oray.net |
| unknown |
hsk-api.oray.com |
| unknown |
phsle5-std01.oray.net |
| unknown |
www.google-analytics.com |
| whitelisted |
2.100.168.192.in-addr.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2284 | phtunnel.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
Process | Message |
|---|---|
HskDDNSMaint.exe | load oraylog.dll
|
HskDDNSMaint.exe | CreateFileMapping oraylog file mapping ok, |
HskDDNSMaint.exe | Global\764F2066-E3C5-4108-A748-B7D2D1003748C__PROGRA~1_Oray_HskDDNS_oraylog.dll.sd.share |
HskDDNSMaint.exe | |
HskDDNSMaint.exe | oraylog MapViewOfFile ok
|
HskDDNS.exe | 2019-11-16 07:54:44.524 - Info - [interface] now status is 4
|
HskDDNS.exe | [string "..."]:4547: attempt to index a nil value (global 'password_edit') |
HskDDNS.exe | [string "..."]:4547: attempt to index a nil value (global 'password_edit') |