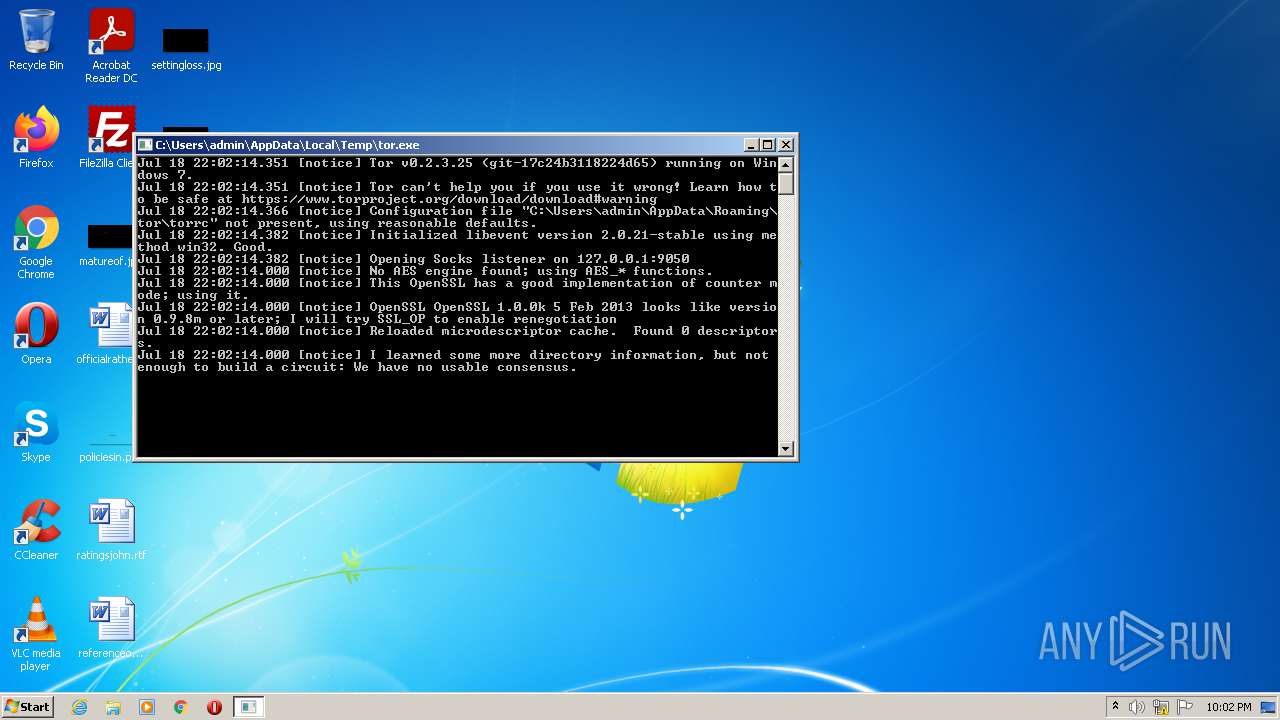
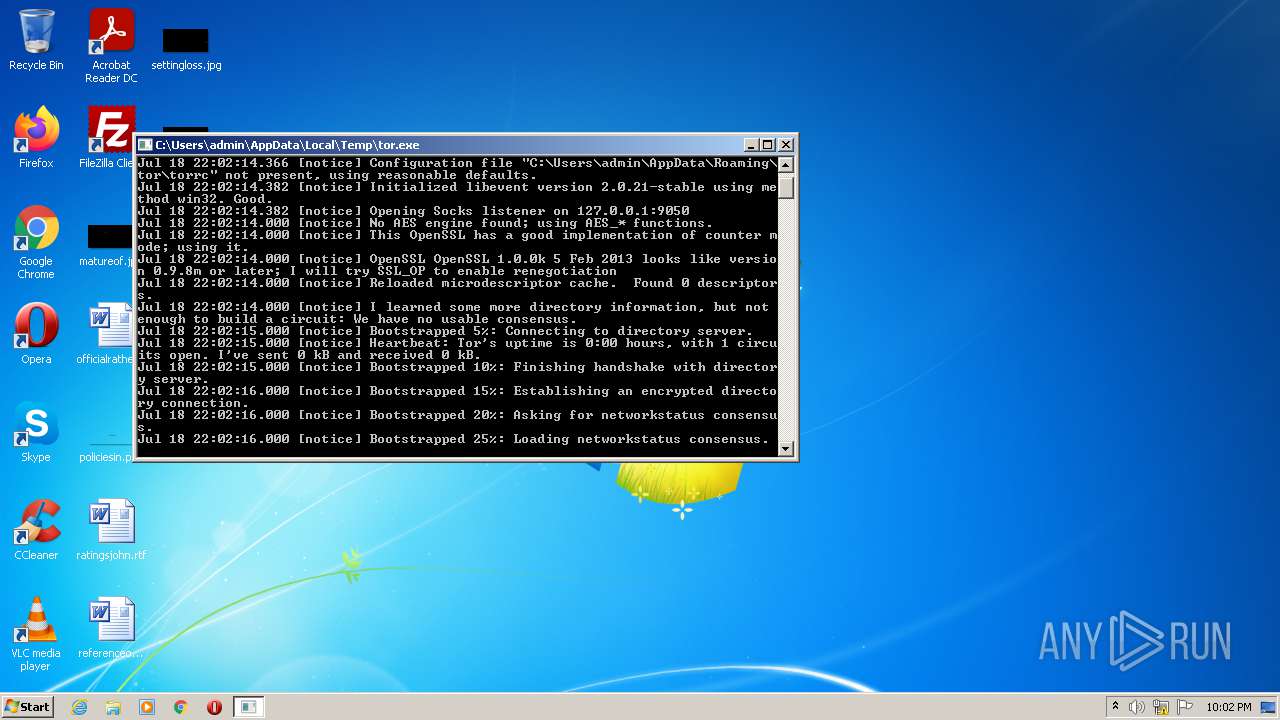
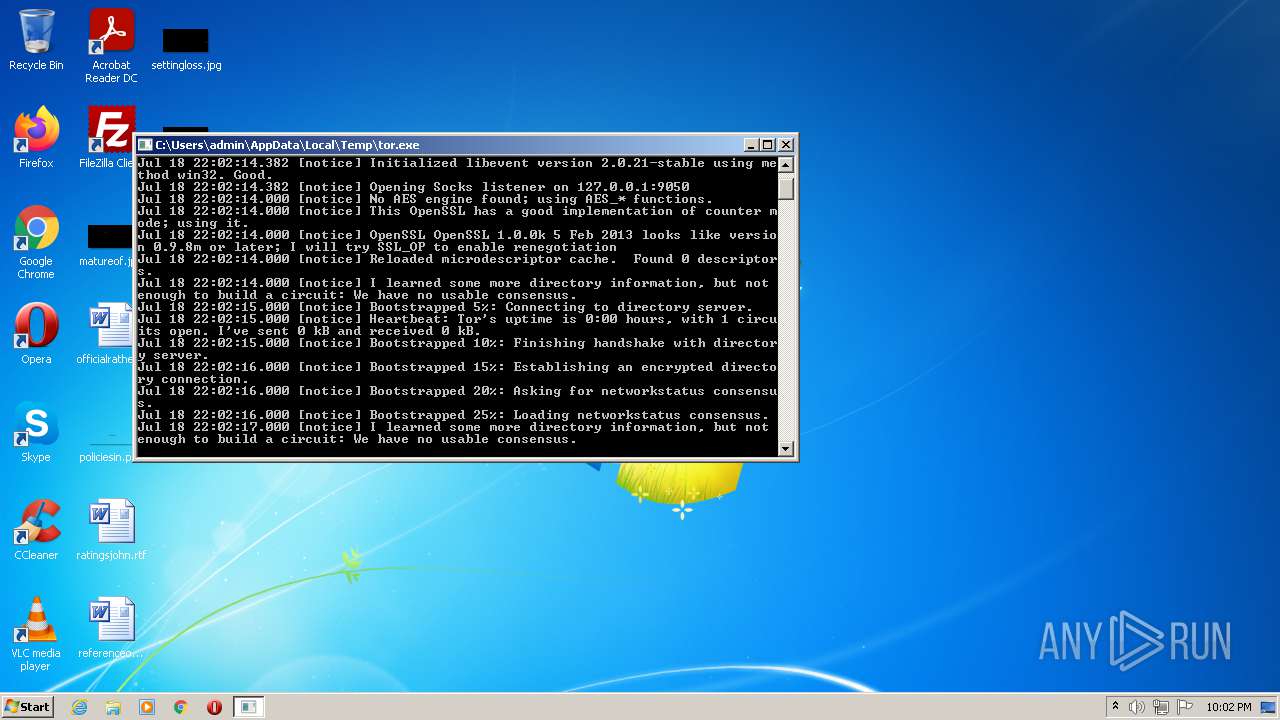
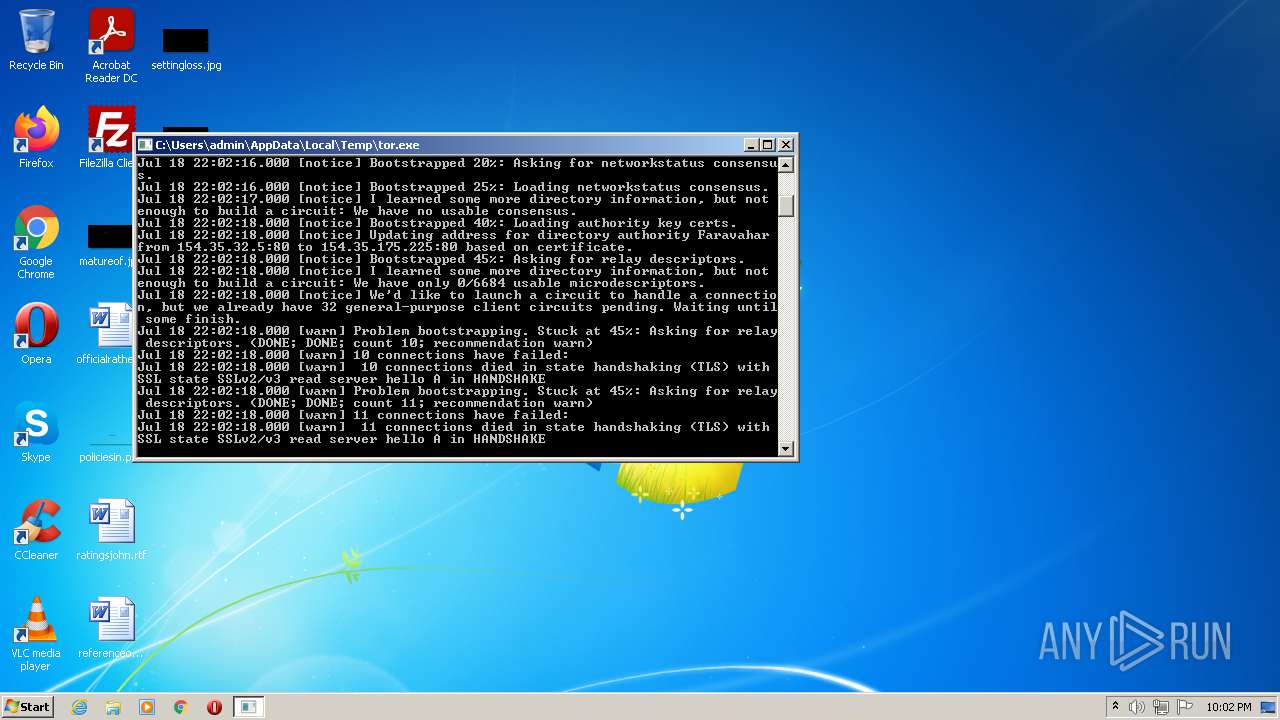
| File name: | tor.exe |
| Full analysis: | https://app.any.run/tasks/dd8483c9-251c-4c57-b116-f50d5b8bc2a5 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2021, 21:02:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 506B0B498216371D64ABB69145B70E4C |
| SHA1: | 71DA7037F29BF8AFE78D2A504350CDAF7CC6C9DA |
| SHA256: | 94FE0E8A61C506FBA45D14571A14DC259E1D52778CEF8366CE8CBDCD871E28DB |
| SSDEEP: | 98304:kaCvGxVNZJ3iE8pq1fAA+eWUwTpHyYaCtQEdaiTYcaKpxuV4D:kaCv4J3iE8pq1ojeWUw9HyY9QEdLYzKp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- tor.exe (PID: 2236)
Checks supported languages
- tor.exe (PID: 2236)
Reads the computer name
- tor.exe (PID: 2236)
INFO
Dropped object may contain Bitcoin addresses
- tor.exe (PID: 2236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x126c |
| UninitializedDataSize: | 24064 |
| InitializedDataSize: | 3232768 |
| CodeSize: | 2293760 |
| LinkerVersion: | 2.22 |
| PEType: | PE32 |
| TimeStamp: | 2013:02:27 15:38:02+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 27-Feb-2013 14:38:02 |
| TLS Callbacks: | 2 callback(s) detected. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 27-Feb-2013 14:38:02 |
| Pointer to Symbol Table: | 0x00315800 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0022FF58 | 0x00230000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.05803 |
.data | 0x00231000 | 0x0000AAE8 | 0x0000AC00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.25201 |
.rdata | 0x0023C000 | 0x0008B820 | 0x0008BA00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76372 |
/4 | 0x002C8000 | 0x0004D050 | 0x0004D200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92761 |
.bss | 0x00316000 | 0x00005E00 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0031C000 | 0x000017AC | 0x00001800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.34698 |
.CRT | 0x0031E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.114463 |
.tls | 0x0031F000 | 0x00000020 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.220914 |
Imports
ADVAPI32.DLL |
GDI32.dll |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
WS2_32.dll |
msvcrt.dll |
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2236 | "C:\Users\admin\AppData\Local\Temp\tor.exe" | C:\Users\admin\AppData\Local\Temp\tor.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
256
Read events
256
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2236 | tor.exe | C:\Users\admin\AppData\Roaming\tor\cached-certs | text | |
MD5:— | SHA256:— | |||
| 2236 | tor.exe | C:\Users\admin\AppData\Roaming\tor\state | text | |
MD5:— | SHA256:— | |||
| 2236 | tor.exe | C:\Users\admin\AppData\Roaming\tor\unverified-microdesc-consensus | text | |
MD5:— | SHA256:— | |||
| 2236 | tor.exe | C:\Users\admin\AppData\Roaming\tor\cached-microdesc-consensus.tmp | text | |
MD5:— | SHA256:— | |||
| 2236 | tor.exe | C:\Users\admin\AppData\Roaming\tor\unverified-microdesc-consensus.tmp | text | |
MD5:— | SHA256:— | |||
| 2236 | tor.exe | C:\Users\admin\AppData\Roaming\tor\cached-microdescs.new | text | |
MD5:— | SHA256:— | |||
| 2236 | tor.exe | C:\Users\admin\AppData\Roaming\tor\cached-microdesc-consensus | text | |
MD5:— | SHA256:— | |||
| 2236 | tor.exe | C:\Users\admin\AppData\Roaming\tor\state.tmp | text | |
MD5:— | SHA256:— | |||
| 2236 | tor.exe | C:\Users\admin\AppData\Roaming\tor\cached-certs.tmp | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
126
DNS requests
0
Threats
160
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2236 | tor.exe | 128.31.0.39:9101 | — | Massachusetts Institute of Technology | US | malicious |
2236 | tor.exe | 194.109.206.212:443 | — | Xs4all Internet BV | NL | malicious |
2236 | tor.exe | 171.25.193.9:80 | — | Foreningen for digitala fri- och rattigheter | SE | malicious |
2236 | tor.exe | 93.115.95.38:443 | — | Voxility S.R.L. | RO | malicious |
2236 | tor.exe | 147.135.4.38:9001 | — | OVH SAS | US | suspicious |
2236 | tor.exe | 185.225.19.204:9001 | — | — | — | suspicious |
2236 | tor.exe | 95.211.210.72:443 | — | LeaseWeb Netherlands B.V. | NL | suspicious |
2236 | tor.exe | 188.34.199.143:443 | — | Asre Enteghal Dadeha | IR | suspicious |
2236 | tor.exe | 51.38.80.214:9001 | — | — | GB | suspicious |
2236 | tor.exe | 188.165.212.152:9001 | — | OVH SAS | FR | suspicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2236 | tor.exe | Misc activity | ET POLICY TLS possible TOR SSL traffic |
2236 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 211 |
2236 | tor.exe | Misc activity | ET POLICY TLS possible TOR SSL traffic |
2236 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 810 |
2236 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 827 |
2236 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 233 |
2236 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 612 |
2236 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 653 |
2236 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 759 |
2236 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 640 |