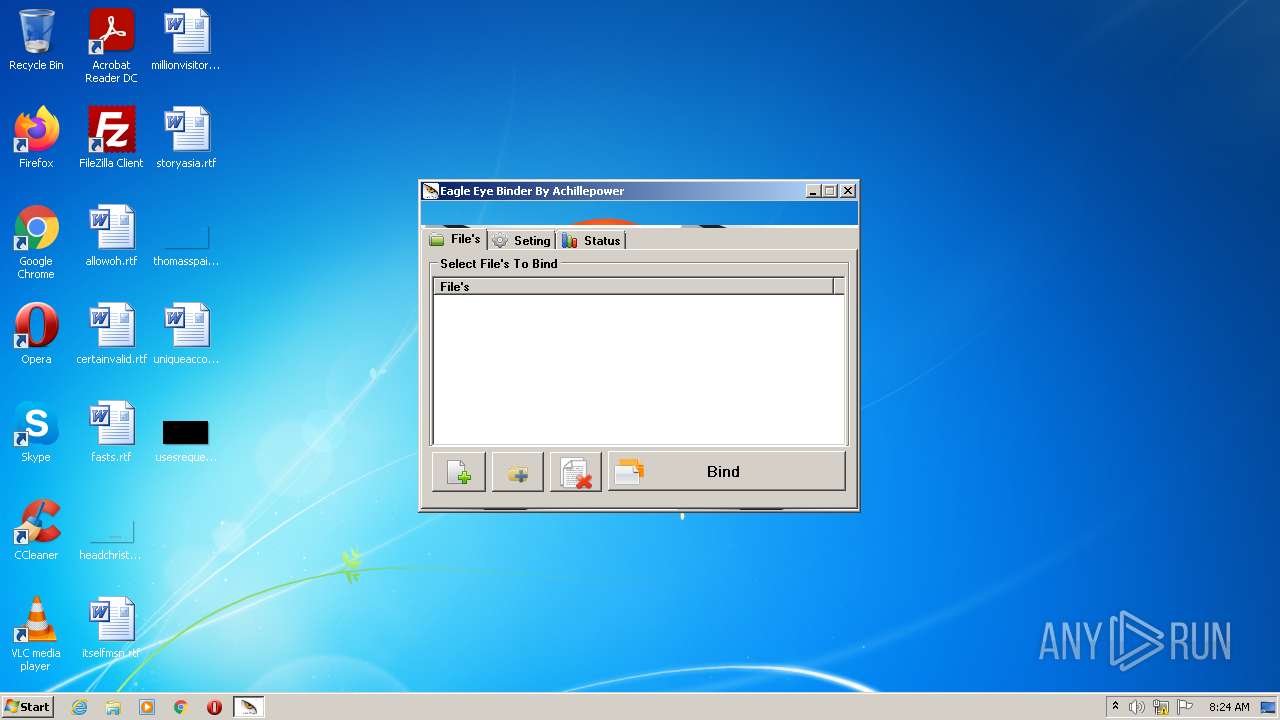
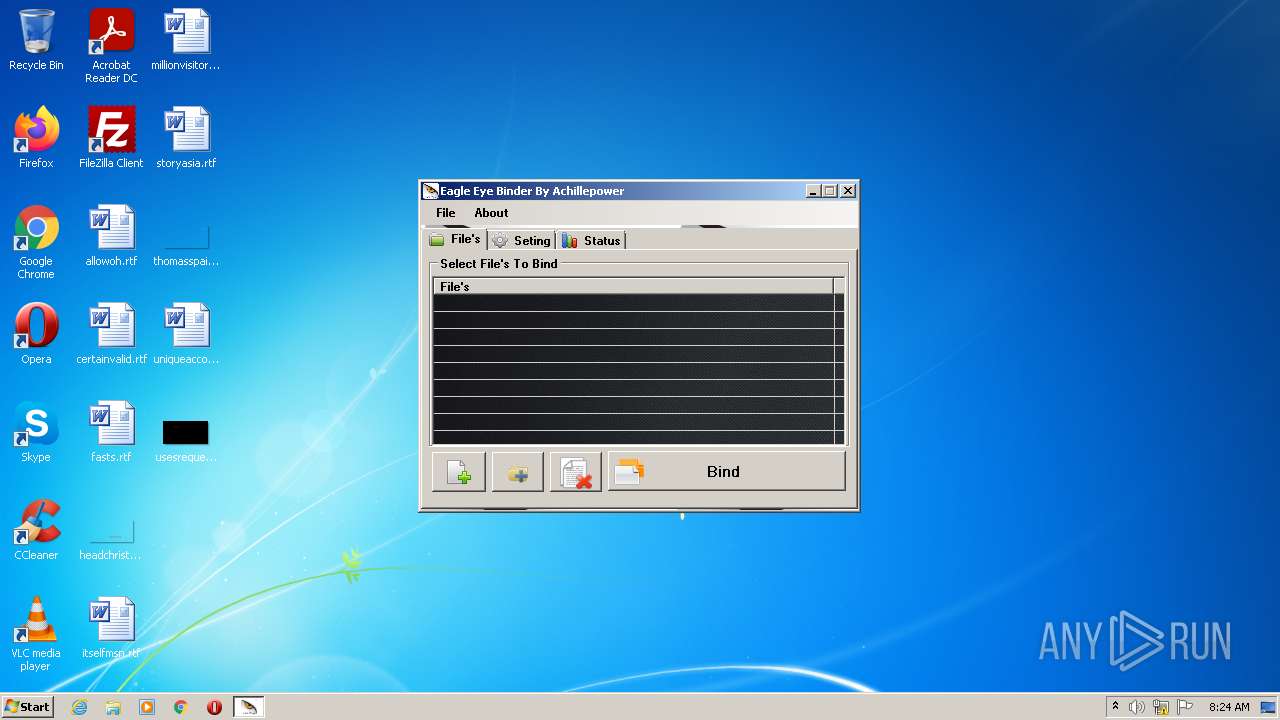
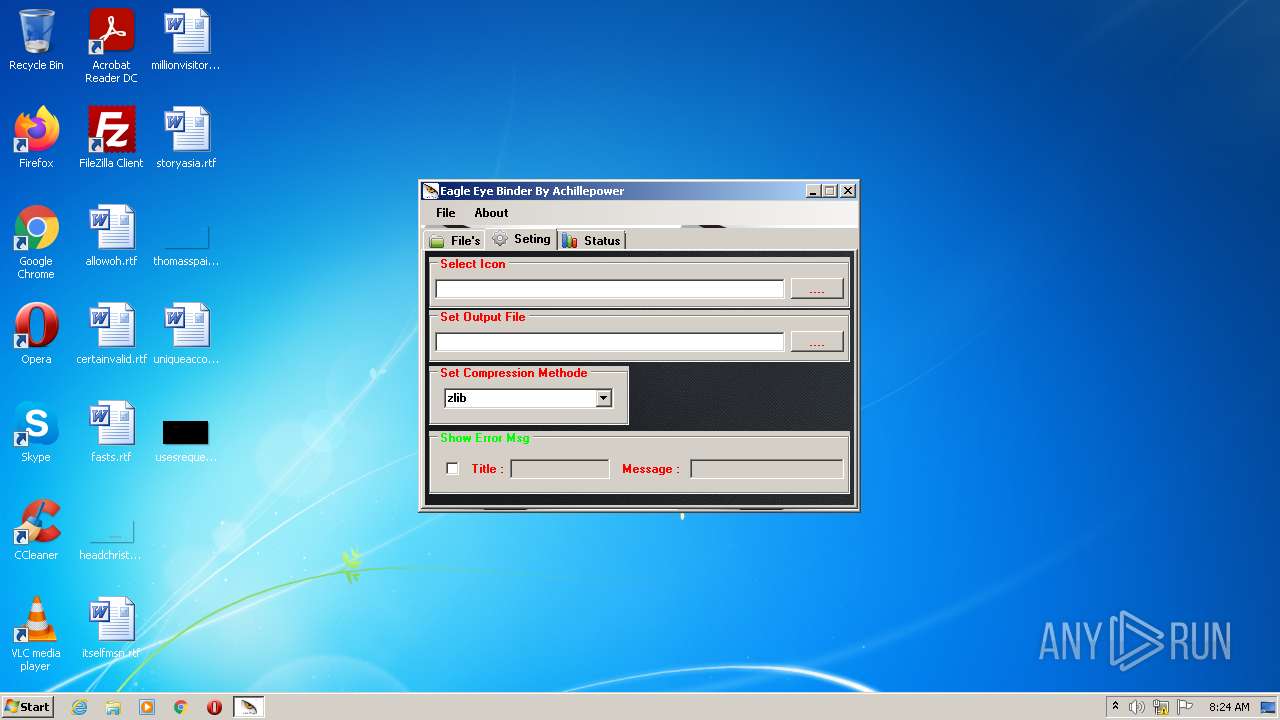
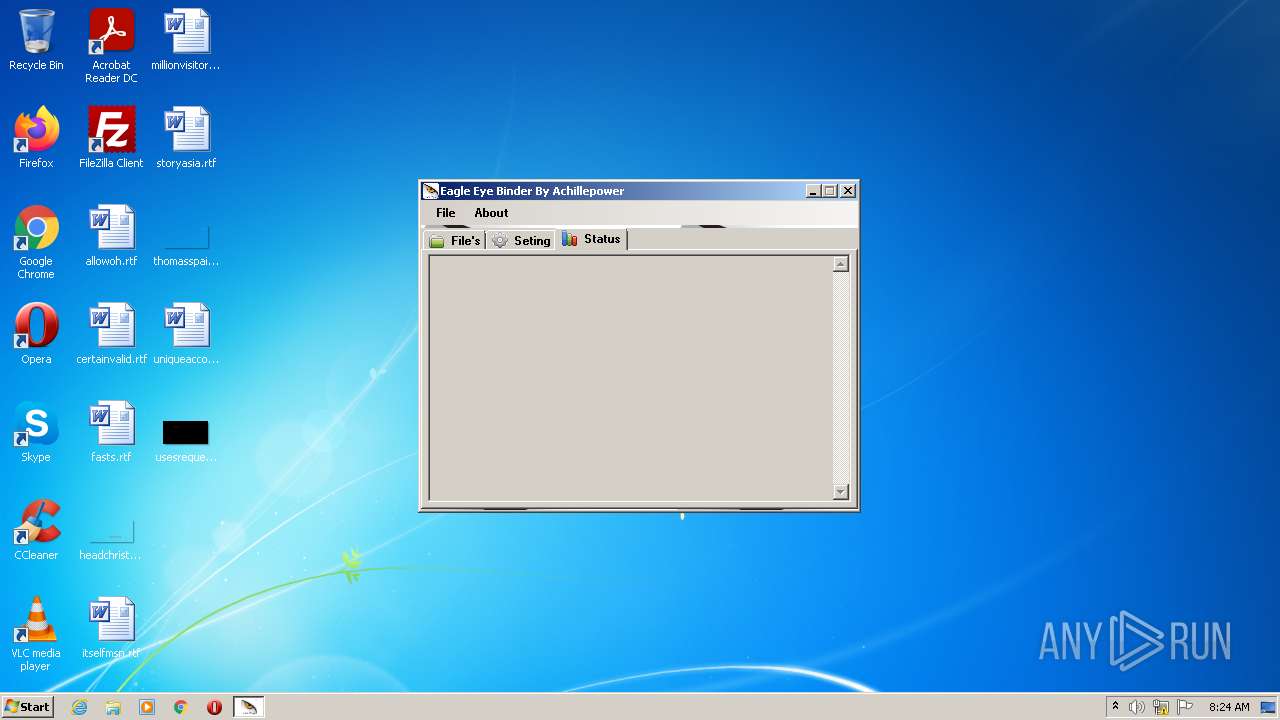
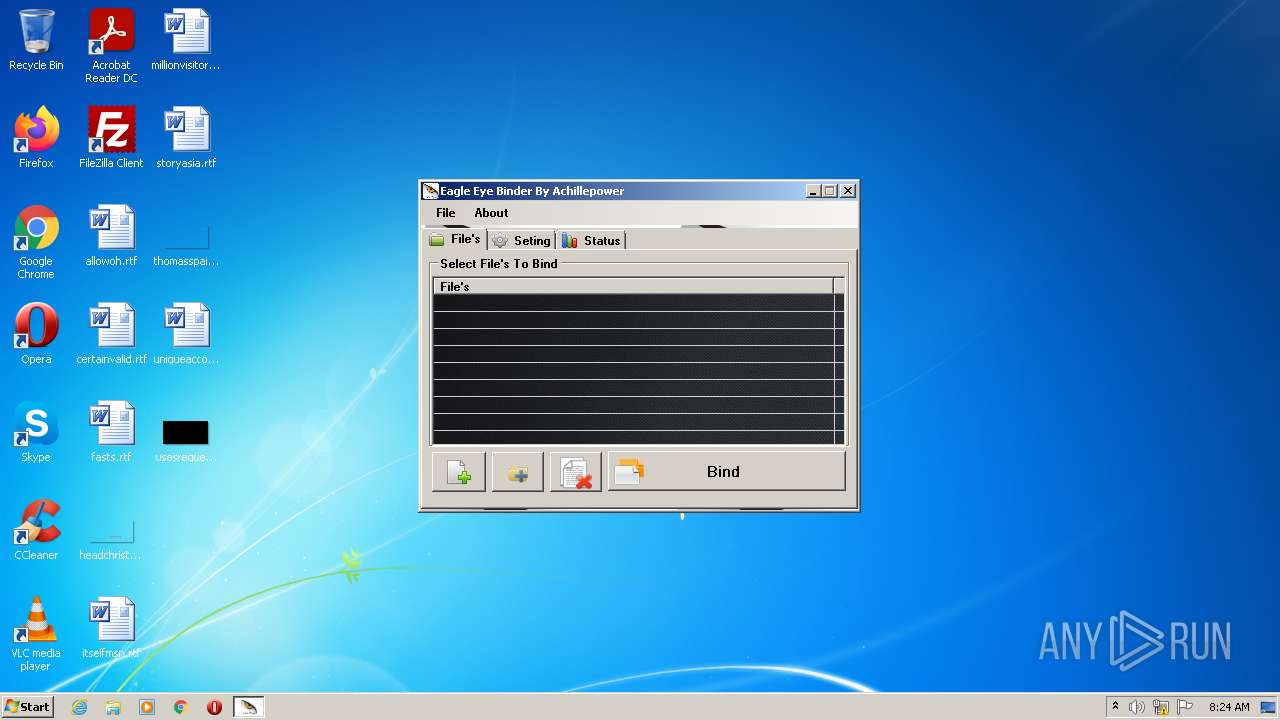
| File name: | Eagle Eye Binder.exe |
| Full analysis: | https://app.any.run/tasks/b87b0b64-feac-44df-9547-445d351c6ea6 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2022, 07:23:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 9BFF19AA79D69F19782BB3D7381AE8B6 |
| SHA1: | 1273288C6DD4DFBE883923289FFD19352C439D4C |
| SHA256: | 94F07062A84BC731FC2C92F7DE7954872006A67D806990EEAC7B8F1CAFAFAB11 |
| SSDEEP: | 98304:i2gR9ael9A9vcrzjZFFgYxGdchj9ixCSYgYj66GOs49Pj3tWA27AQk:+Pael9Avcrzj3Fg/dc+CSYgYj66GSPji |
MALICIOUS
Drops executable file immediately after starts
- Eagle Eye Binder.exe (PID: 1836)
- temp.exe (PID: 240)
Application was dropped or rewritten from another process
- temp.exe (PID: 240)
SUSPICIOUS
Reads the computer name
- Eagle Eye Binder.exe (PID: 1836)
Reads Microsoft Outlook installation path
- Eagle Eye Binder.exe (PID: 1836)
Checks supported languages
- Eagle Eye Binder.exe (PID: 1836)
- temp.exe (PID: 240)
Executable content was dropped or overwritten
- temp.exe (PID: 240)
- Eagle Eye Binder.exe (PID: 1836)
Drops a file with a compile date too recent
- temp.exe (PID: 240)
- Eagle Eye Binder.exe (PID: 1836)
Creates files in the Windows directory
- temp.exe (PID: 240)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (45.1) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (19.2) |
| .exe | | | Win64 Executable (generic) (17) |
| .scr | | | Windows screen saver (8) |
| .dll | | | Win32 Dynamic Link Library (generic) (4) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | Eagle Eye Binder |
| OriginalFileName: | Eagle Eye Binder.exe |
| LegalCopyright: | Copyright © 2015 AchillepowerGeek |
| InternalName: | Eagle Eye Binder.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Eagle Eye Binder |
| Comments: | By AchillepowerGeek |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x32037e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 22016 |
| CodeSize: | 3269632 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| TimeStamp: | 2015:09:23 02:17:12+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Sep-2015 00:17:12 |
| Debug artifacts: |
|
| Comments: | By AchillepowerGeek |
| FileDescription: | Eagle Eye Binder |
| FileVersion: | 1.0.0.0 |
| InternalName: | Eagle Eye Binder.exe |
| LegalCopyright: | Copyright © 2015 AchillepowerGeek |
| OriginalFilename: | Eagle Eye Binder.exe |
| ProductName: | Eagle Eye Binder |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 23-Sep-2015 00:17:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0031E384 | 0x0031E400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.96657 |
.sdata | 0x00322000 | 0x00000138 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.21092 |
.rsrc | 0x00324000 | 0x00005130 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.64631 |
.reloc | 0x0032A000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.01561 | 2672 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 1.83321 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
38
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Users\admin\AppData\Local\Temp\temp.exe" | C:\Users\admin\AppData\Local\Temp\temp.exe | Eagle Eye Binder.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1836 | "C:\Users\admin\AppData\Local\Temp\Eagle Eye Binder.exe" | C:\Users\admin\AppData\Local\Temp\Eagle Eye Binder.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: Eagle Eye Binder Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2976 | "C:\Users\admin\AppData\Local\Temp\Eagle Eye Binder.exe" | C:\Users\admin\AppData\Local\Temp\Eagle Eye Binder.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Eagle Eye Binder Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
896
Read events
888
Write events
8
Delete events
0
Modification events
| (PID) Process: | (1836) Eagle Eye Binder.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1836) Eagle Eye Binder.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1836) Eagle Eye Binder.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1836) Eagle Eye Binder.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
34
Suspicious files
0
Text files
74
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1836 | Eagle Eye Binder.exe | C:\Users\admin\AppData\Local\Temp\584DBE0.tmp | — | |
MD5:— | SHA256:— | |||
| 1836 | Eagle Eye Binder.exe | C:\Users\admin\AppData\Local\Temp\temp.exe | executable | |
MD5:DF21207322BB1E8511A824107E852E16 | SHA256:5EAB7CBC6741AEE4FE457138732E8F07751CE360ABA25F973E41CF96A6B880B5 | |||
| 240 | temp.exe | C:\Windows\EasyBind\Contrib\Language files\Basque.nlf | text | |
MD5:58818A07E83C360E46B142CC5B7CBCF1 | SHA256:7CD4C534482A093C0A09487E3941ABFA915F3E1E57FD929265D93B2A8FD48F90 | |||
| 240 | temp.exe | C:\Windows\EasyBind\Contrib\Language files\Albanian.nlf | text | |
MD5:34339C9F8C631649BCE80B92A7652789 | SHA256:9F27DD0CB82CA73F7C308BDFCA8C2BFADD743B457E97629B7A89DE2F0CF52DD6 | |||
| 240 | temp.exe | C:\Windows\EasyBind\Contrib\Language files\Belarusian.nlf | text | |
MD5:79446F3CB05B14D0E0D41ACD8CCE8B78 | SHA256:F798ADC22B26F8887CE80264E70F8C10FFA9448F5797212311D4E02FBD4234FA | |||
| 240 | temp.exe | C:\Windows\EasyBind\Contrib\Language files\Breton.nlf | text | |
MD5:E896187D248EE1357CC00AE6BF9B5BA3 | SHA256:C60767A1E9AF91FC1AFDDE71187E0CF62F70BA4C57666D3174775EB531938044 | |||
| 240 | temp.exe | C:\Windows\EasyBind\Contrib\Language files\Catalan.nlf | text | |
MD5:107088288877B4BBB013726C998CA824 | SHA256:C9E6DF7FACAA0C35309057BF1A3C8670EB1586C0B90761A7C8B4353AE1C72645 | |||
| 240 | temp.exe | C:\Windows\EasyBind\Contrib\Language files\Bulgarian.nlf | text | |
MD5:9179B1FF3AA76719C234A8DF574FD3FA | SHA256:3D224763D6F210FFEC24604810BDB8613584D253F829C35F3701BC4B90B0FCC3 | |||
| 240 | temp.exe | C:\Windows\EasyBind\Contrib\Language files\Bosnian.nlf | text | |
MD5:0F05012A476852635E4CA84EA9A63B31 | SHA256:6D9DF735BF635D10DEBA274B57ED43AC22A3289A76964DA488EFB712C987DF2F | |||
| 240 | temp.exe | C:\Windows\EasyBind\Contrib\Language files\Arabic.nlf | text | |
MD5:718D99271DF0F80A25EE4C51998AC864 | SHA256:91BD8CA772C7126C2EA968A72E04790EEC72952BF536082011C4A0814FBEDDF1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report