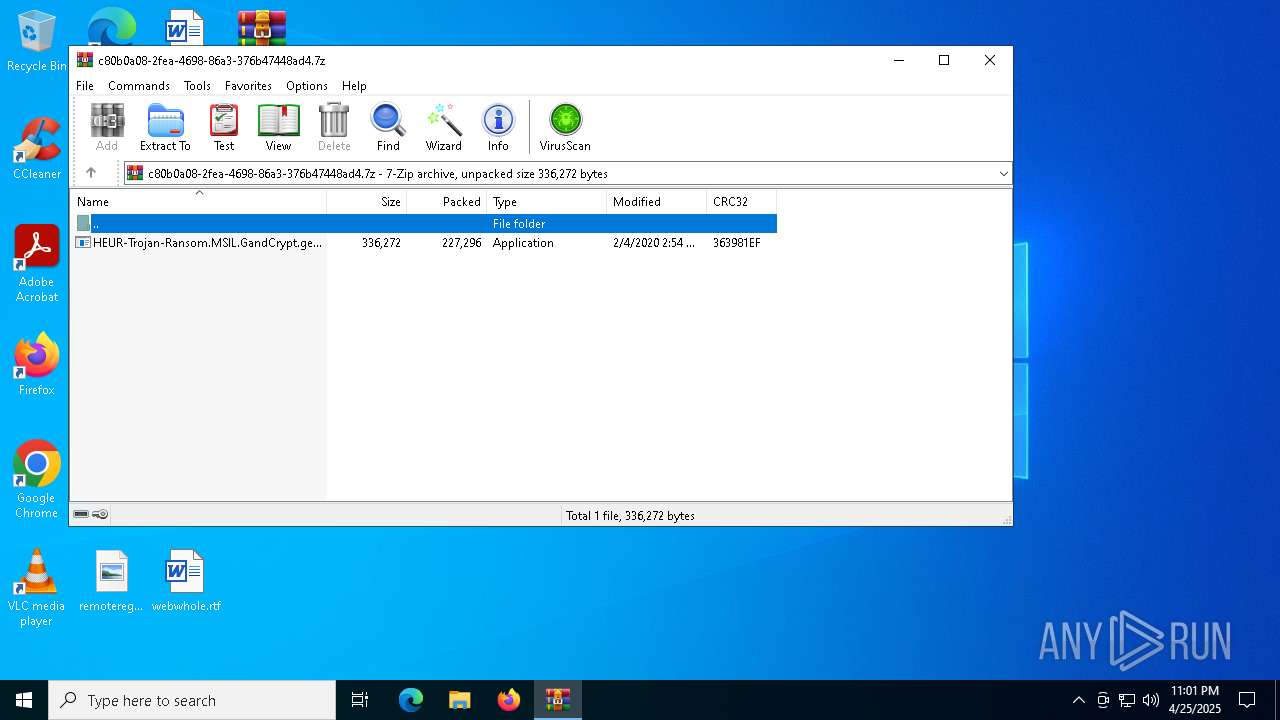
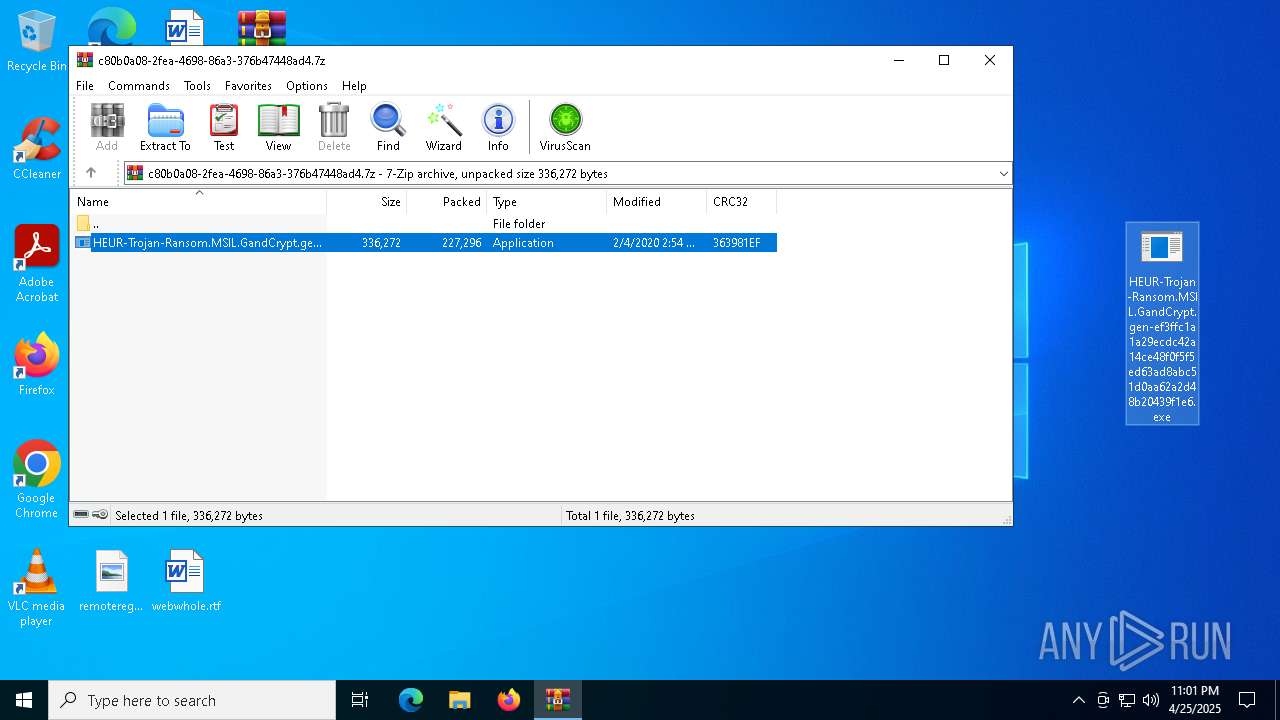
| File name: | HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.7z |
| Full analysis: | https://app.any.run/tasks/c80b0a08-2fea-4698-86a3-376b47448ad4 |
| Verdict: | Malicious activity |
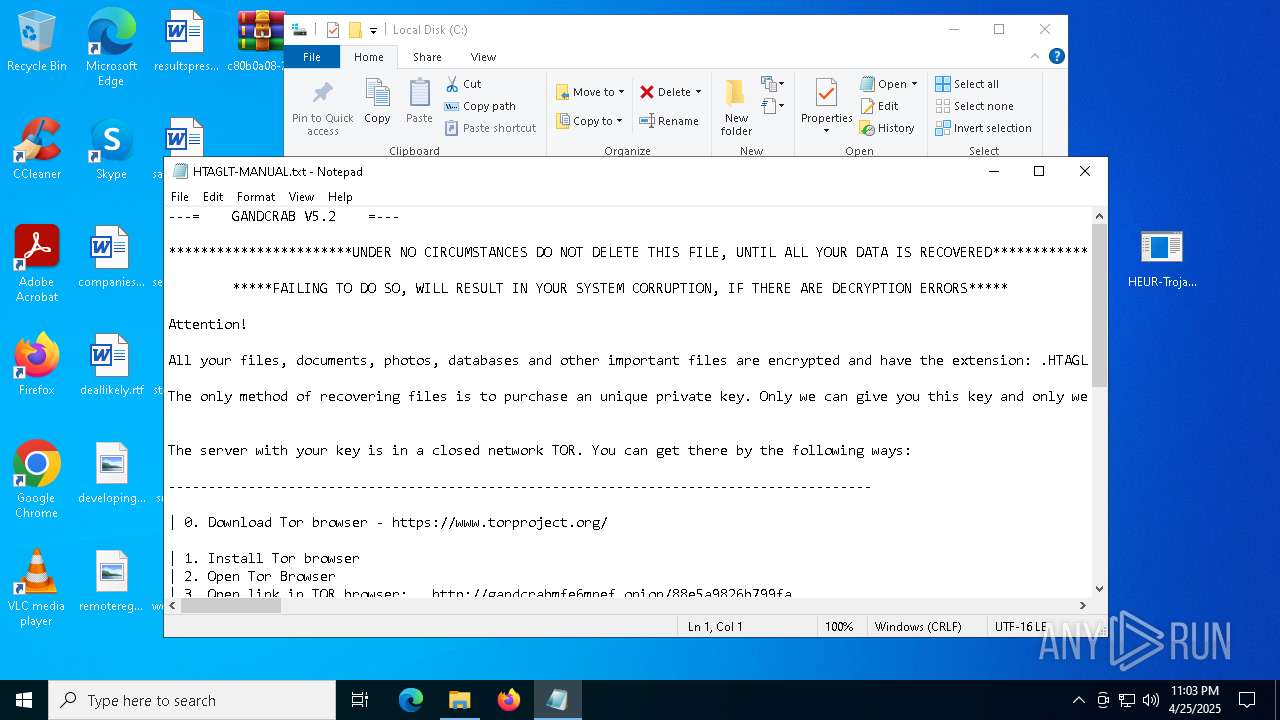
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | April 25, 2025, 23:01:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | EB3E9F3B4DFB13164F506D310BE523B4 |
| SHA1: | 8EEE83A38505419F9FD27B803E4F63D822D472D7 |
| SHA256: | 94ED82AA732CEEA43F6E1B28C80EC2A2C09AC37E4DA9089595468B1F16C9DB48 |
| SSDEEP: | 6144:dudkQ3TEDgi7GBH72cd5wTm2U0jIJQ8Wu:dudB6vaDqTm2sWu |
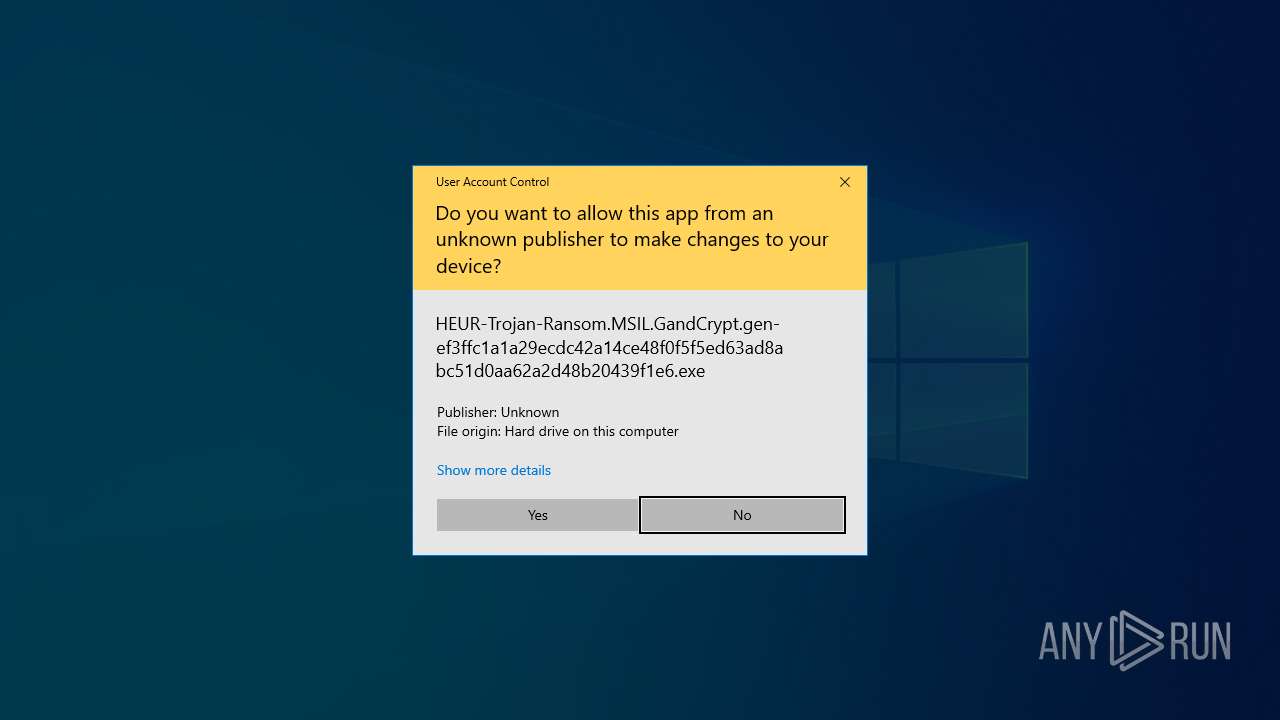
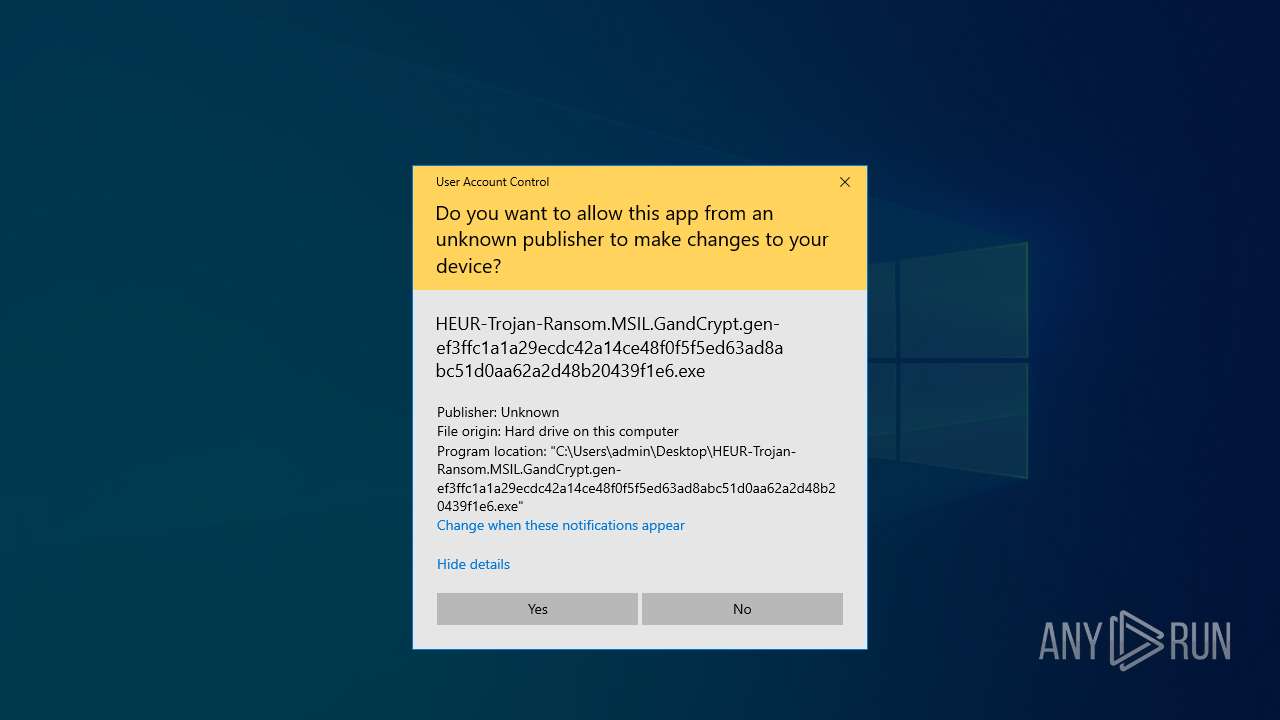
MALICIOUS
Executing a file with an untrusted certificate
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 7964)
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 4976)
GANDCRAB mutex has been found
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 4976)
RANSOMWARE has been detected
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 4976)
Renames files like ransomware
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 4976)
Writes a file to the Word startup folder
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 4976)
SUSPICIOUS
Reads security settings of Internet Explorer
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 7964)
Application launched itself
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 7964)
Starts CMD.EXE for commands execution
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 7964)
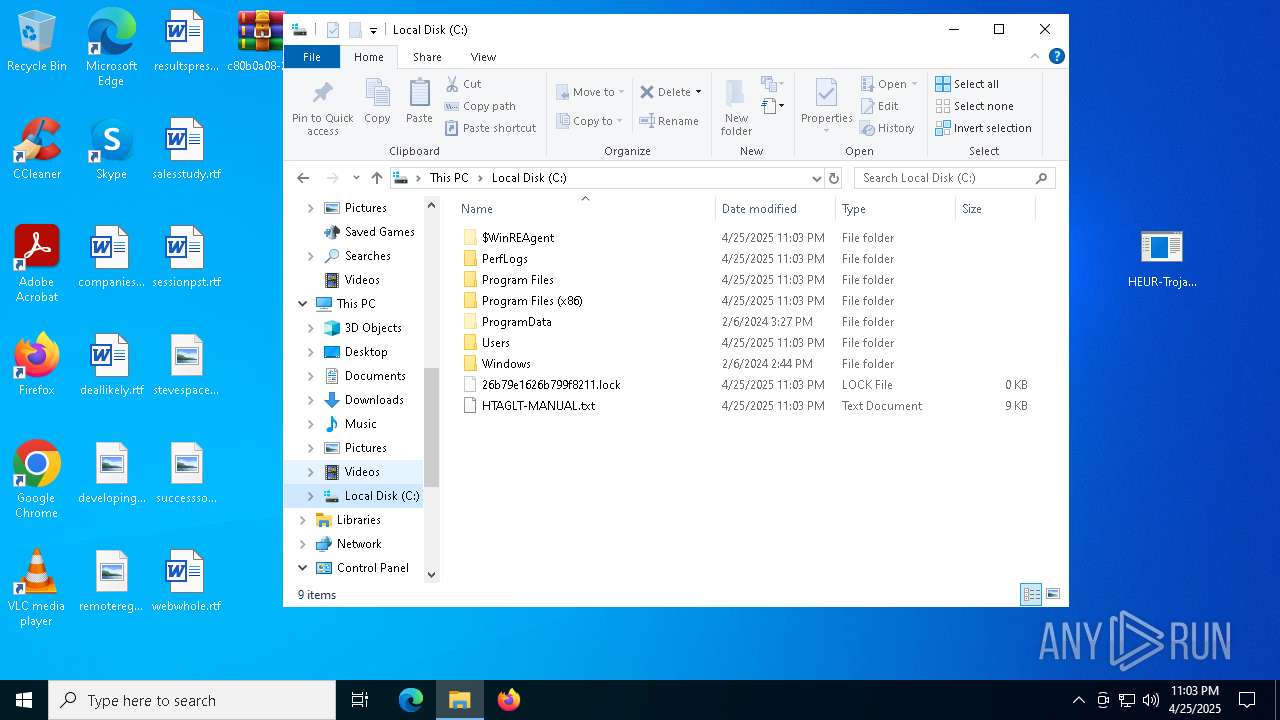
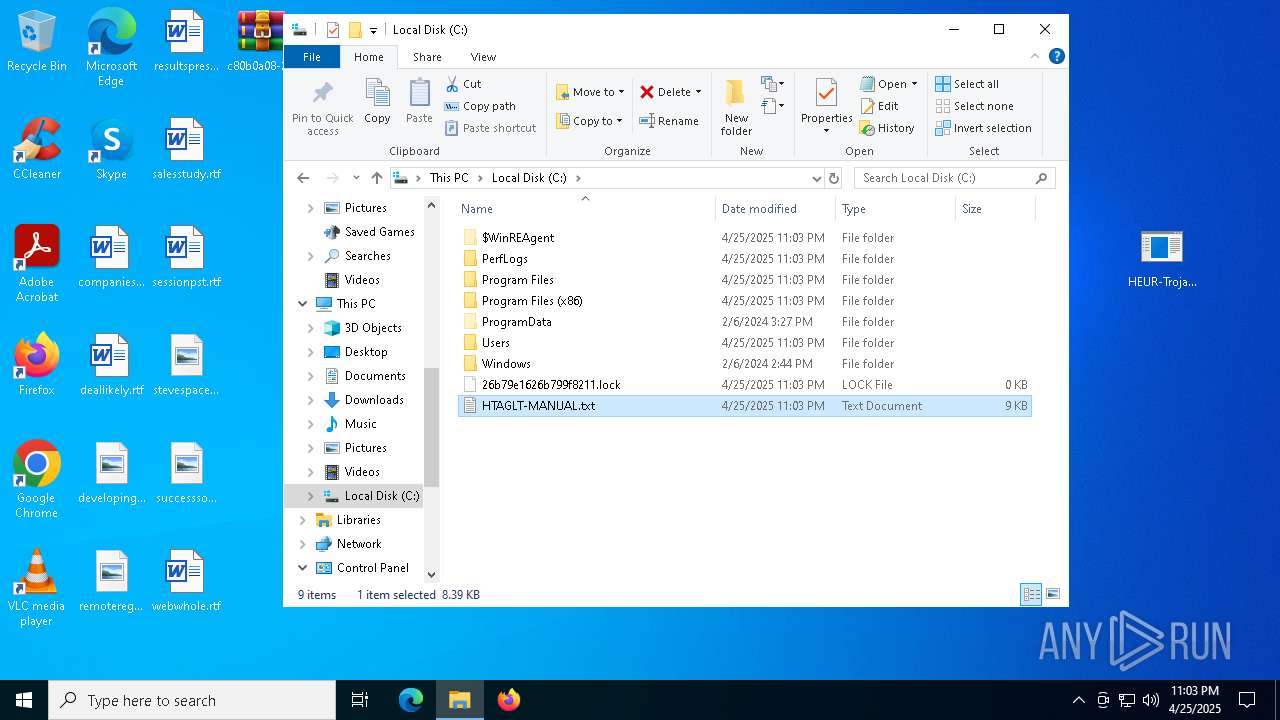
Creates file in the systems drive root
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 4976)
There is functionality for taking screenshot (YARA)
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 4976)
Executes application which crashes
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 7964)
INFO
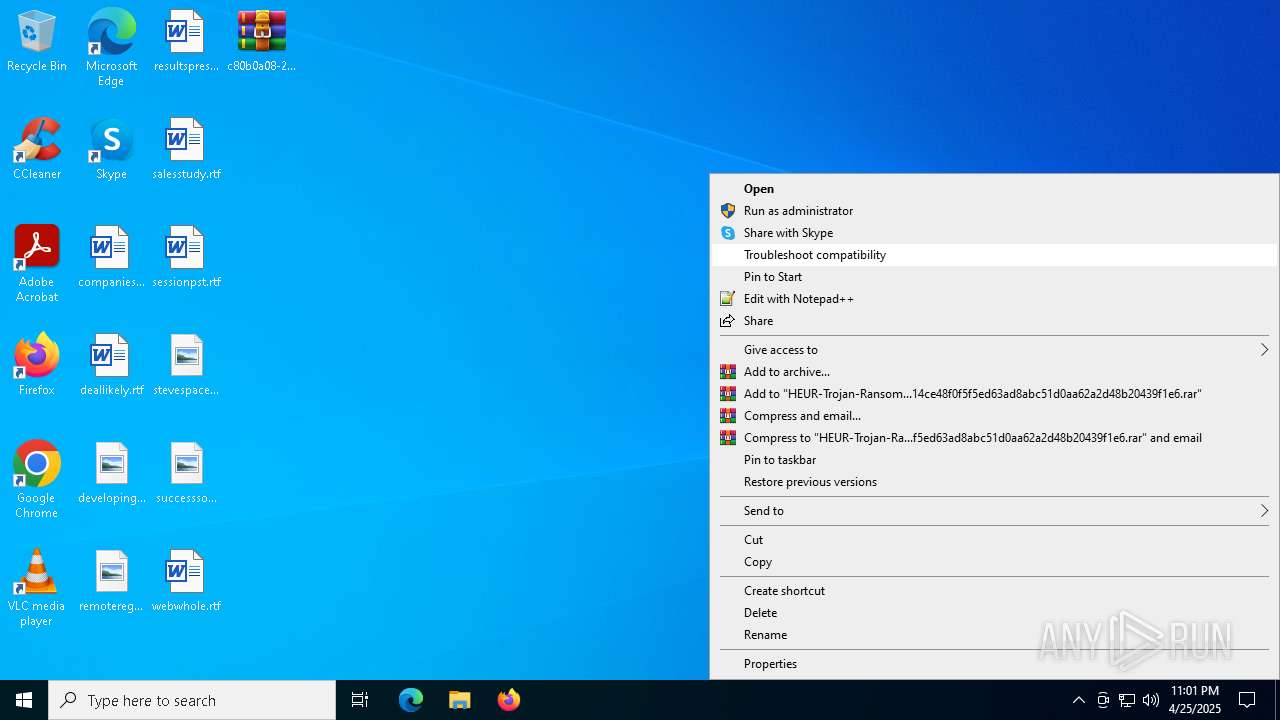
Manual execution by a user
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 7964)
- notepad.exe (PID: 5680)
Checks supported languages
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 7964)
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 4976)
Process checks computer location settings
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 7964)
Reads the computer name
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 7964)
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 4976)
Reads the machine GUID from the registry
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 7964)
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 4976)
Reads the software policy settings
- slui.exe (PID: 7328)
- slui.exe (PID: 6112)
Reads CPU info
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 4976)
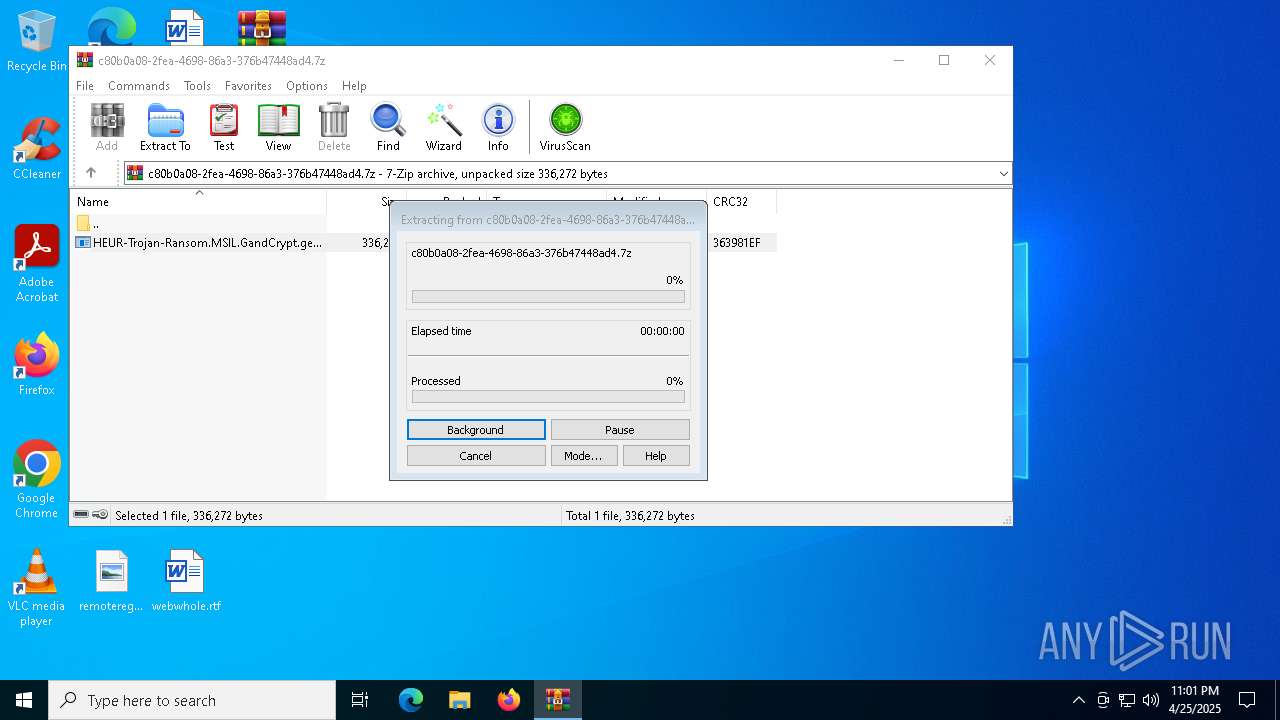
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5512)
Creates files or folders in the user directory
- WerFault.exe (PID: 7220)
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 4976)
Creates files in the program directory
- HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe (PID: 4976)
Checks proxy server information
- slui.exe (PID: 6112)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2020:02:04 14:54:48+00:00 |
| ArchivedFileName: | HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe |
Total processes
149
Monitored processes
12
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\Desktop\HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe:Zone.Identifier" | C:\Windows\SysWOW64\cmd.exe | — | HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3676 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4976 | "C:\Users\admin\Desktop\HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe" | C:\Users\admin\Desktop\HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe | HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe | ||||||||||||
User: admin Company: egulakamomunuhuq Integrity Level: HIGH Description: osayerel Version: 3.4.5.6 Modules
| |||||||||||||||
| 5512 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\c80b0a08-2fea-4698-86a3-376b47448ad4.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5680 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\HTAGLT-MANUAL.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6112 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6436 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\Desktop\HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe:Zone.Identifier" | C:\Windows\SysWOW64\cmd.exe | — | HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7220 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7964 -s 1764 | C:\Windows\SysWOW64\WerFault.exe | — | HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7280 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
Total events
20 407
Read events
20 382
Write events
22
Delete events
3
Modification events
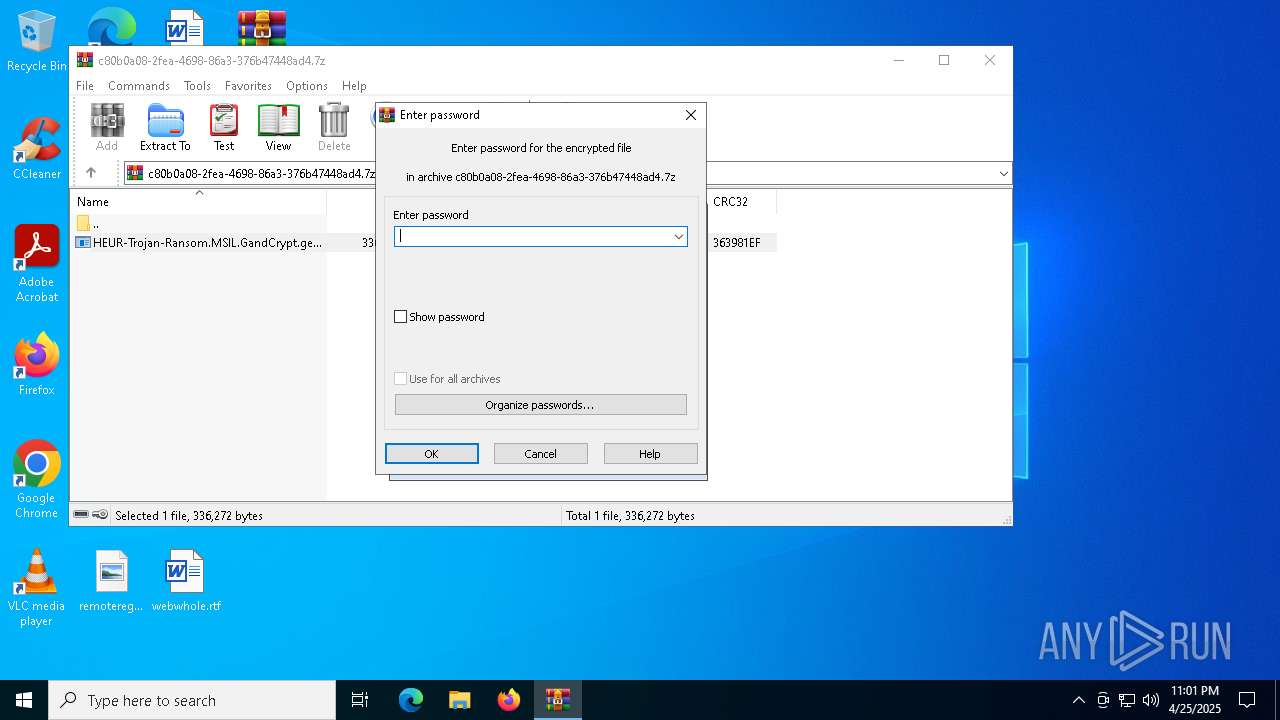
| (PID) Process: | (5512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\c80b0a08-2fea-4698-86a3-376b47448ad4.7z | |||
| (PID) Process: | (5512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (5512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
3
Suspicious files
984
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7220 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_5KCHKXZK0AOYM3RJ_c7fea7c043b4c260d17243e8e0ebd088f1a9a0c9_9811174d_3d6dd264-b3ec-4459-8192-e1f159e9bcff\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4976 | HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe | C:\$WinREAgent\Backup\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 4976 | HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe | C:\$WinREAgent\Backup\Winre.wim.htaglt | — | |
MD5:— | SHA256:— | |||
| 7220 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER5C04.tmp.WERInternalMetadata.xml | binary | |
MD5:408C0969356181E2AB6376C306D3B08A | SHA256:31BF545B457B20F2FDB920C7A36B127285BA6C741C7423C9C632C44D826BB1CD | |||
| 7220 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER5C43.tmp.xml | xml | |
MD5:C0BDF4916DAF88A1D6E48DE7C4A622C3 | SHA256:CF0F77957A4A29D0F7D365AA9857C20EC8709C2DEDC90C5DFFD431340F331E49 | |||
| 4976 | HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe | C:\$WinREAgent\Rollback.xml | binary | |
MD5:5549A55B21B3BFE155B5F53000C22180 | SHA256:DDF09B3815E5F80EE8DF263FBC999C3D71035BB3141013FF7B3C002AF6691488 | |||
| 4976 | HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe | C:\$Recycle.Bin\HTAGLT-MANUAL.txt | binary | |
MD5:2671D11C98A717EF06E9B4B9614DD9B7 | SHA256:978F00A3559E064750CF16F9AFB20154A904A98B1F9F5C287195FD35AB051BB5 | |||
| 4976 | HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1001\HTAGLT-MANUAL.txt | binary | |
MD5:2671D11C98A717EF06E9B4B9614DD9B7 | SHA256:978F00A3559E064750CF16F9AFB20154A904A98B1F9F5C287195FD35AB051BB5 | |||
| 4976 | HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe | C:\$WinREAgent\Scratch\update.wim | — | |
MD5:— | SHA256:— | |||
| 4976 | HEUR-Trojan-Ransom.MSIL.GandCrypt.gen-ef3ffc1a1a29ecdc42a14ce48f0f5f5ed63ad8abc51d0aa62a2d48b20439f1e6.exe | C:\$WinREAgent\Scratch\update.wim.htaglt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8088 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8088 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4024 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |