| File name: | اختراق.bat |
| Full analysis: | https://app.any.run/tasks/a3f6911b-e62f-483f-8535-ffb13b6c2746 |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 14:22:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 3E41D0CF21489666CDC9BF5D77685471 |
| SHA1: | E0CFBF0598B147AAA420FE1E523428978D5D8213 |
| SHA256: | 94E0AD0B4219CC4AB9B6CF4E0DE35678CD33BC4B7DCC66D7C27328D520D4D2D9 |
| SSDEEP: | 48:m78uFW78n378RSbVKGT378jIqb378TCe1R1xAgxlxhjen:bu1nAcsbMdTCeLPPhO |
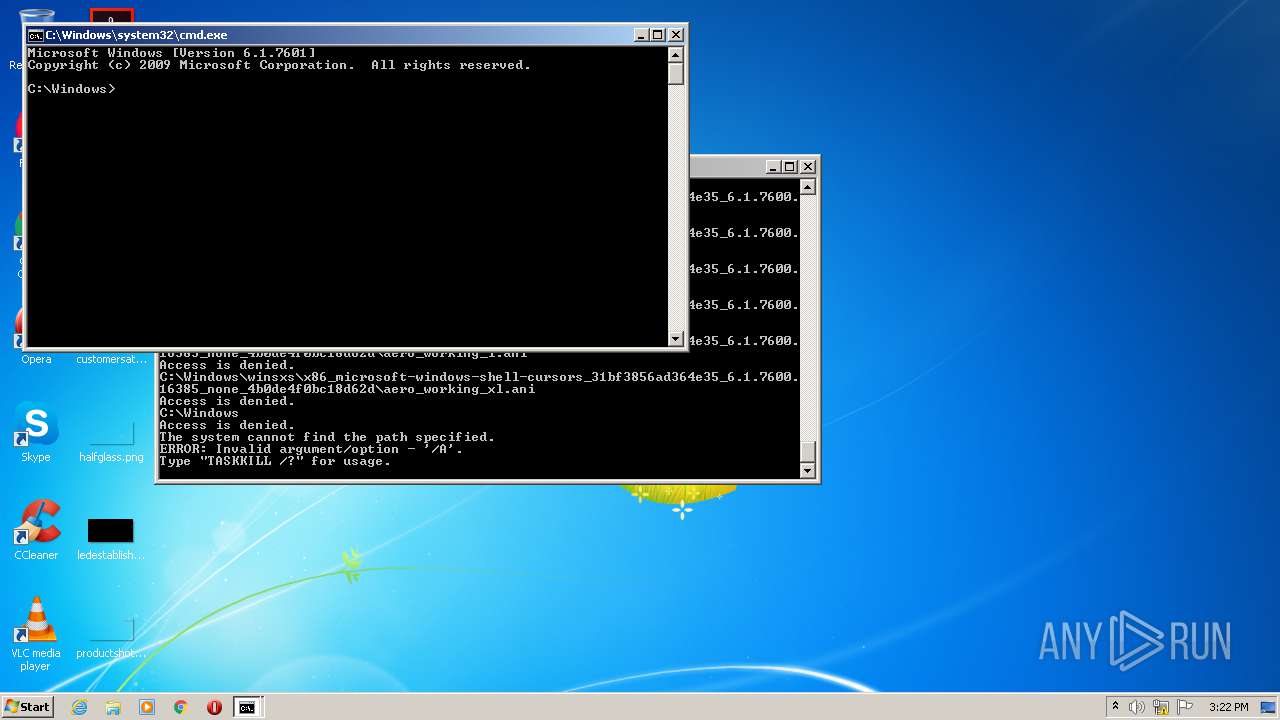
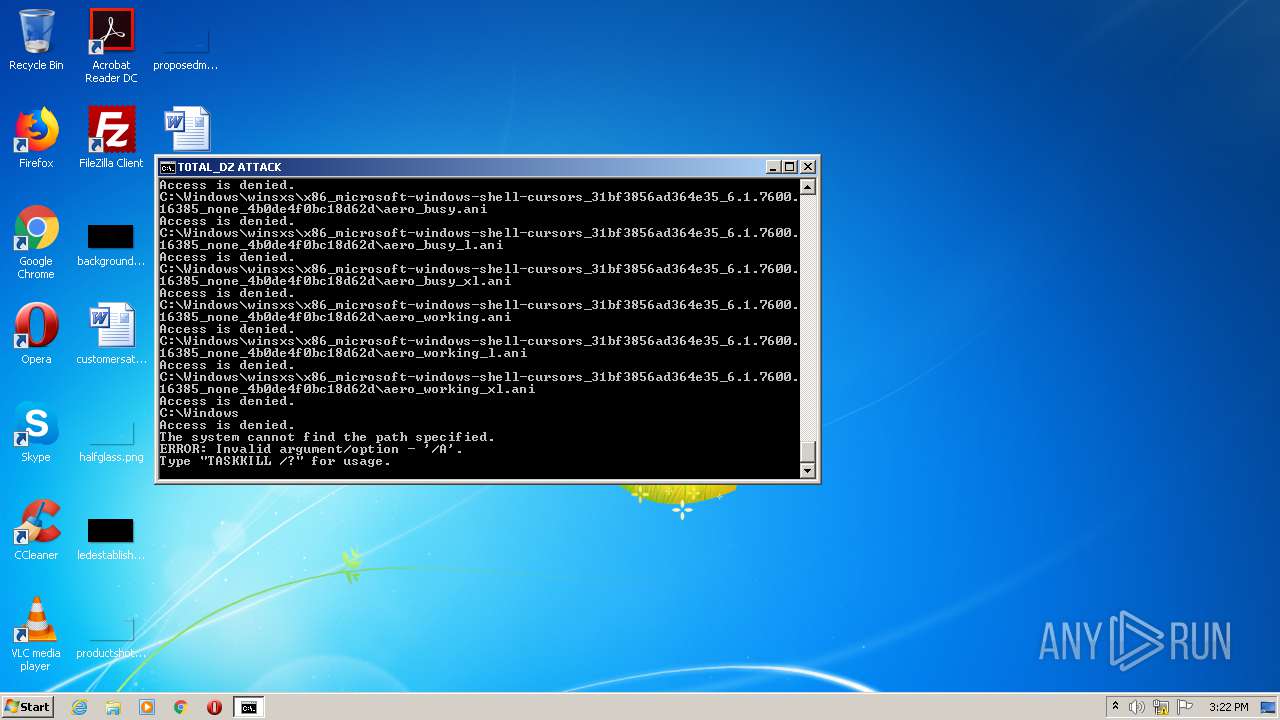
MALICIOUS
Writes to a start menu file
- cmd.exe (PID: 2144)
Runs app for hidden code execution
- cmd.exe (PID: 2144)
SUSPICIOUS
Creates files in the user directory
- cmd.exe (PID: 2144)
Application launched itself
- cmd.exe (PID: 2144)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2144)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2144)
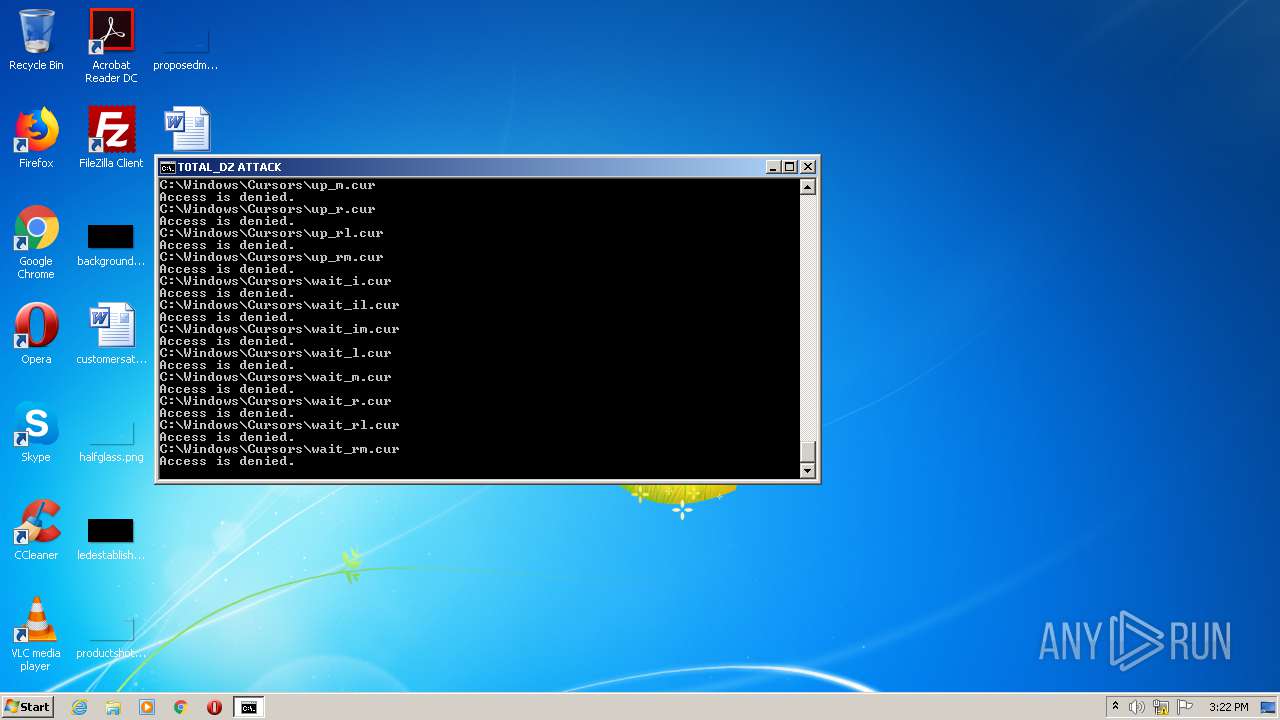
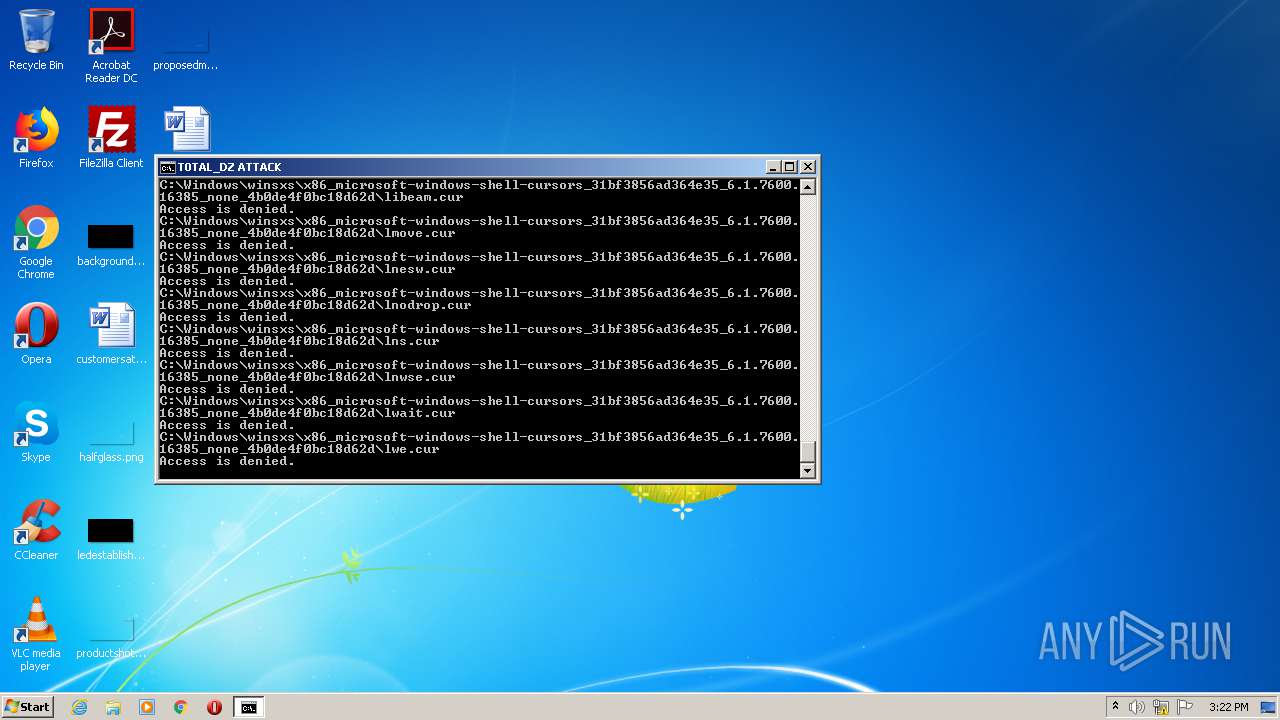
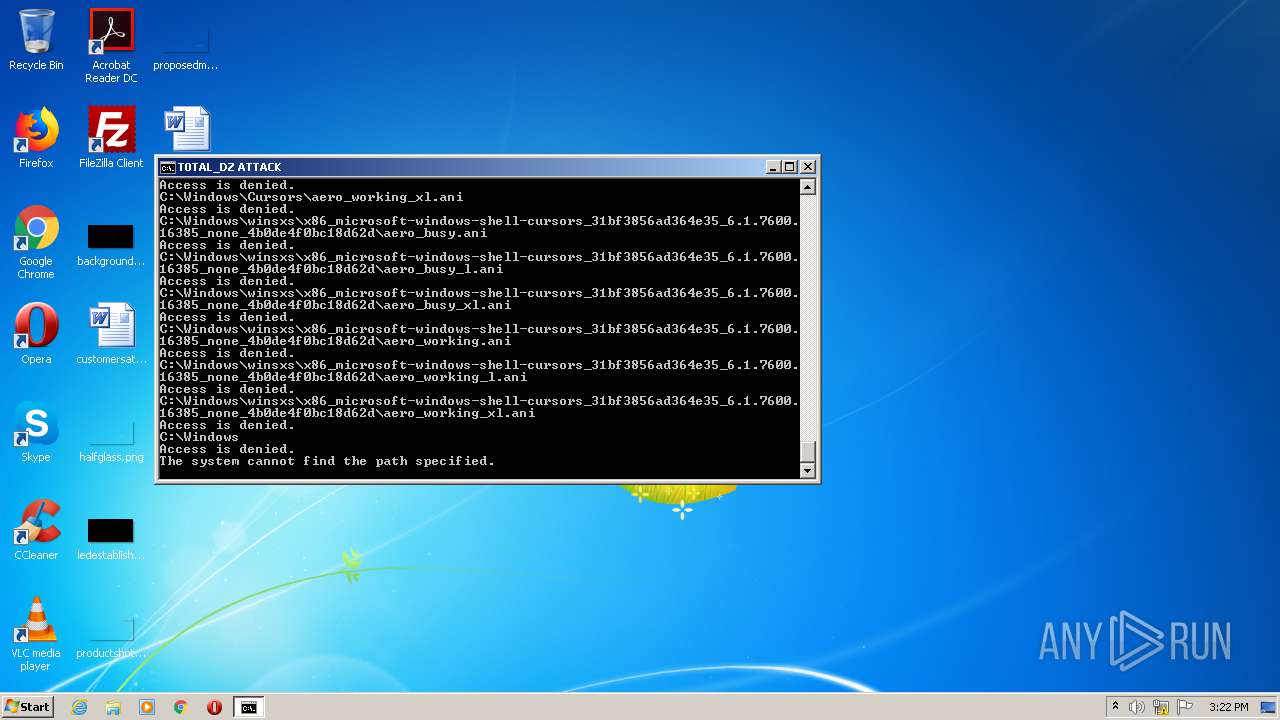
Removes files from Windows directory
- cmd.exe (PID: 2144)
Creates files in the program directory
- firefox.exe (PID: 4028)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2144)
INFO
Application launched itself
- firefox.exe (PID: 448)
- firefox.exe (PID: 4028)
Reads CPU info
- firefox.exe (PID: 4028)
Reads Internet Cache Settings
- pingsender.exe (PID: 2652)
- pingsender.exe (PID: 2404)
- firefox.exe (PID: 4028)
- pingsender.exe (PID: 2940)
Manual execution by user
- firefox.exe (PID: 448)
Creates files in the user directory
- firefox.exe (PID: 4028)
Changes settings of System certificates
- pingsender.exe (PID: 2404)
- pingsender.exe (PID: 2940)
- pingsender.exe (PID: 2652)
Adds / modifies Windows certificates
- pingsender.exe (PID: 2404)
- pingsender.exe (PID: 2652)
- pingsender.exe (PID: 2940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
17
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Cur rentVersion\Run" /v "virus2" /t REG_SZ /d "C:\Foldersaregettinguselesssoijustmade thisforfun\CF.bat" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1480 | reg add "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Ru n" /v "virus" /t REG_SZ /d "C:\Foldersaregettinguselesssoijustmade thisforfun\CF.bat" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
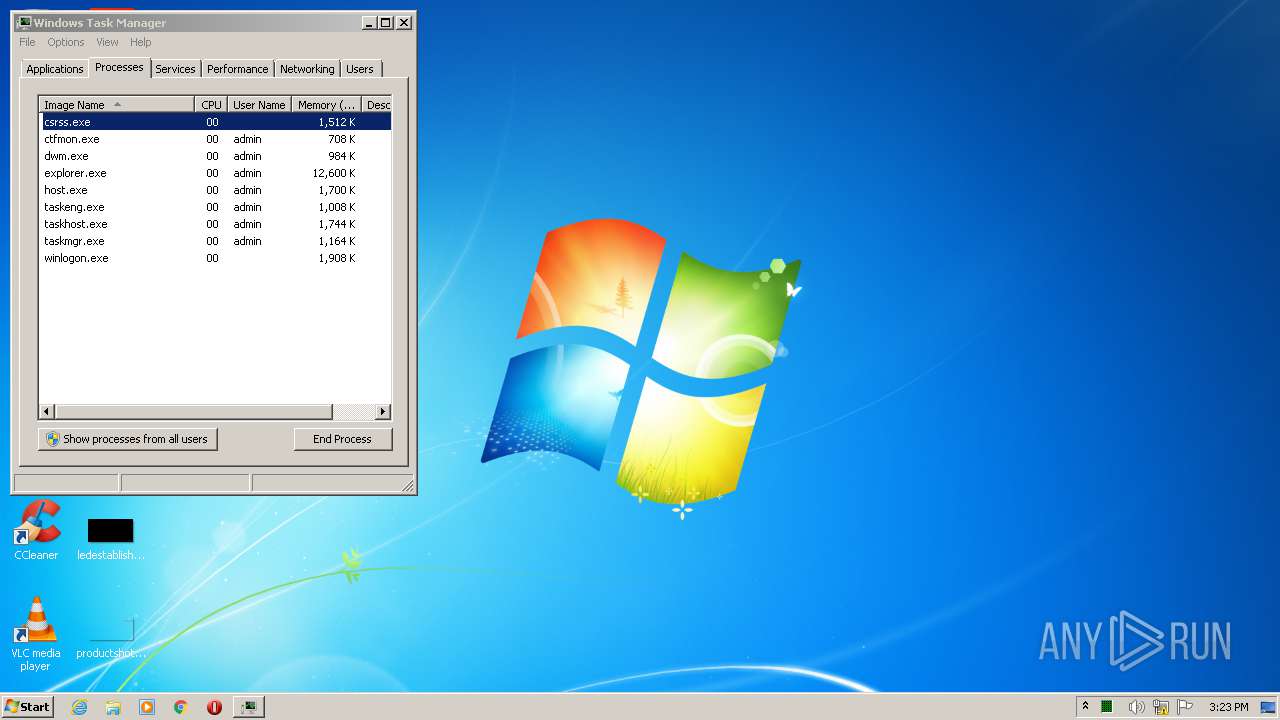
| 1516 | taskkill /A /IM taskmgr | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1752 | taskmgr | C:\Windows\system32\taskmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2144 | cmd /c ""C:\Users\admin\AppData\Local\Temp\اختراق.bat" " | C:\Windows\system32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4028.13.1491940249\593320021" -childID 2 -isForBrowser -prefsHandle 2880 -prefMapHandle 2884 -prefsLen 5997 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 4028 "\\.\pipe\gecko-crash-server-pipe.4028" 2896 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2236 | notepad | C:\Windows\notepad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4028.0.883883664\1288422782" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 4028 "\\.\pipe\gecko-crash-server-pipe.4028" 1192 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 68.0.1 Modules
| |||||||||||||||
| 2340 | cmd | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
616
Read events
539
Write events
74
Delete events
3
Modification events
| (PID) Process: | (2236) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 22 | |||
| (PID) Process: | (2236) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 22 | |||
| (PID) Process: | (2236) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (2236) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (448) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 0195ECCD08000000 | |||
| (PID) Process: | (4028) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 1495ECCD08000000 | |||
| (PID) Process: | (4028) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (4028) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4028) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2652) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
0
Suspicious files
7
Text files
12
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4028 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\favicons.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 4028 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\favicons.sqlite-wal | — | |
MD5:— | SHA256:— | |||
| 4028 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\favicons.sqlite | — | |
MD5:— | SHA256:— | |||
| 4028 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 4028 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\xulstore.json.tmp | — | |
MD5:— | SHA256:— | |||
| 4028 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\webappsstore.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 4028 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\webappsstore.sqlite-wal | — | |
MD5:— | SHA256:— | |||
| 4028 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 4028 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | — | |
MD5:— | SHA256:— | |||
| 4028 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
38
DNS requests
75
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
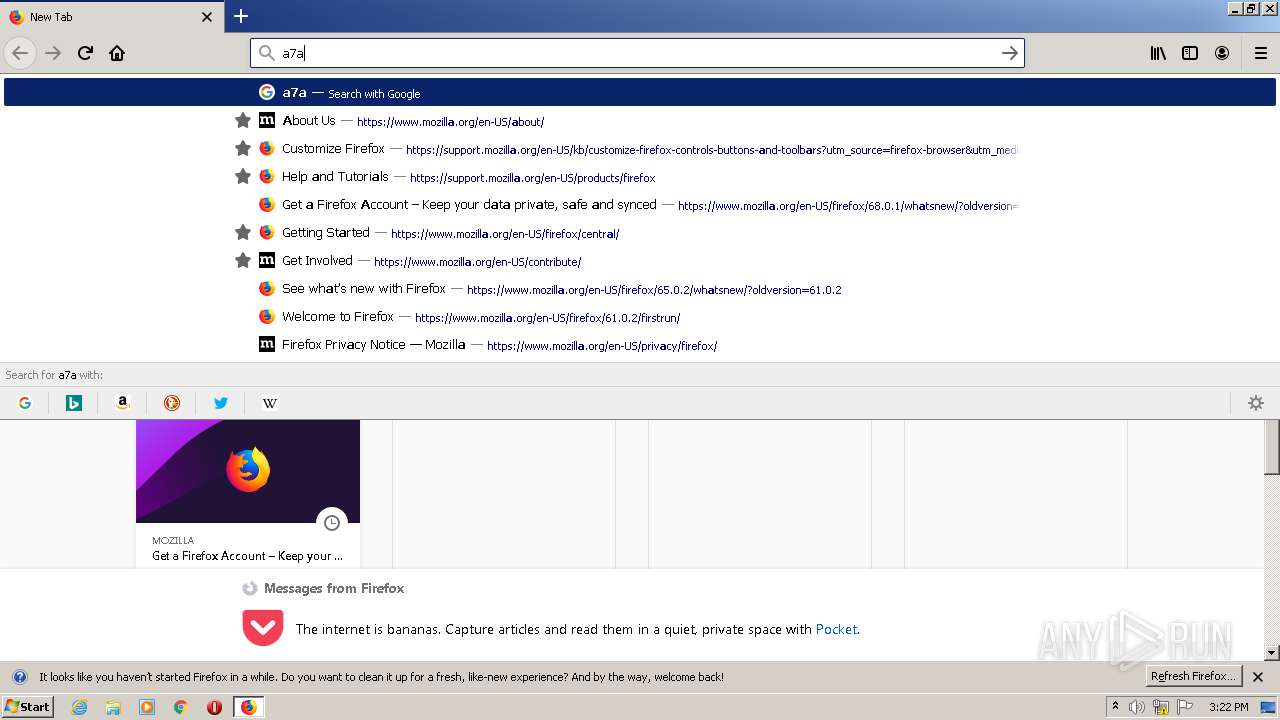
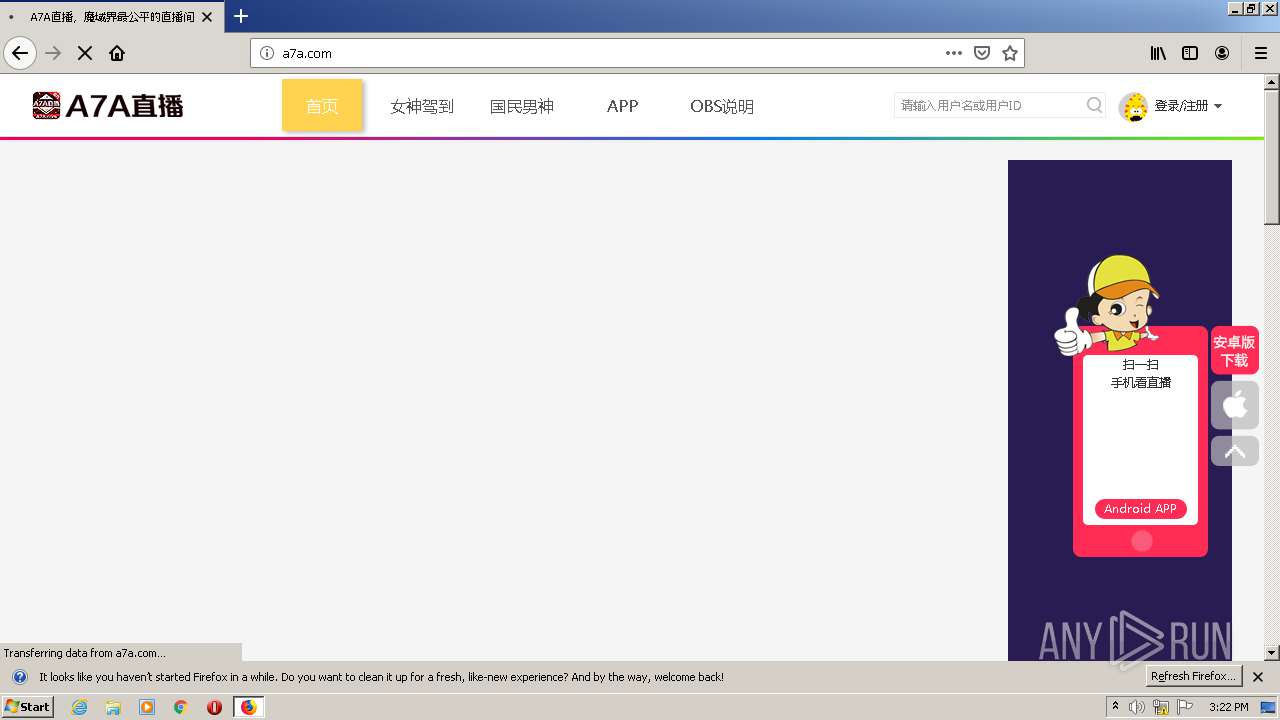
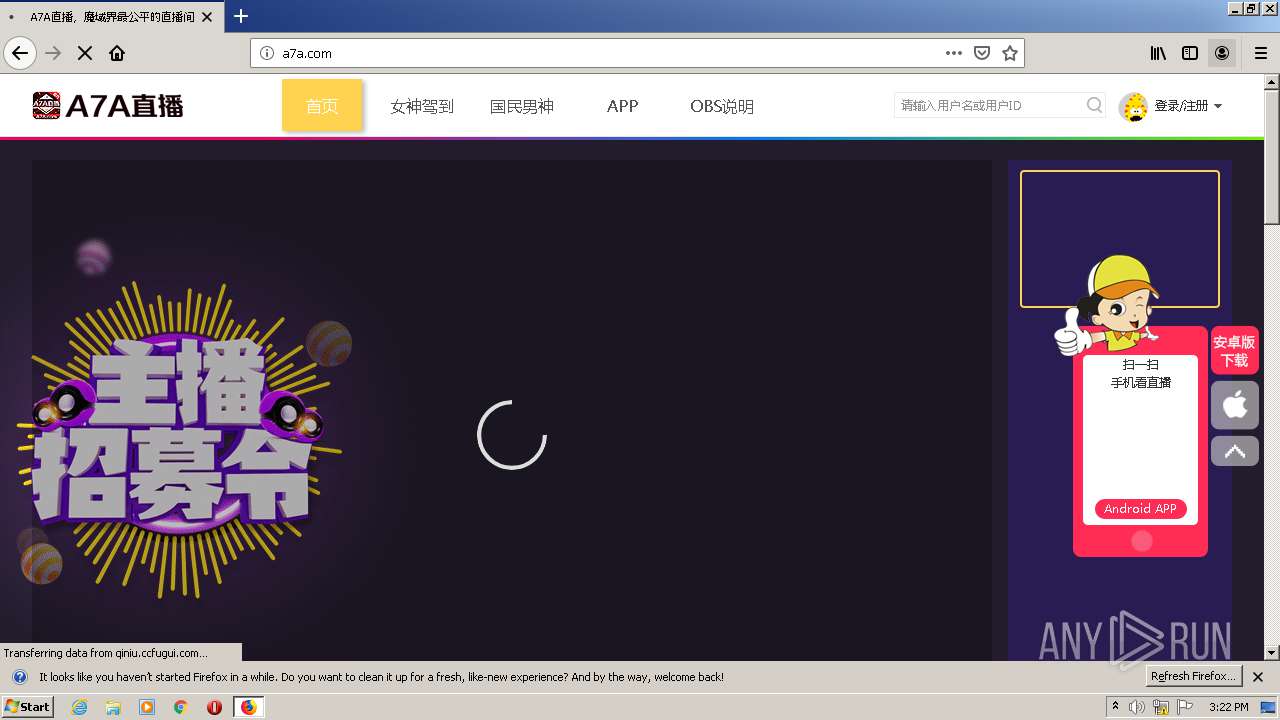
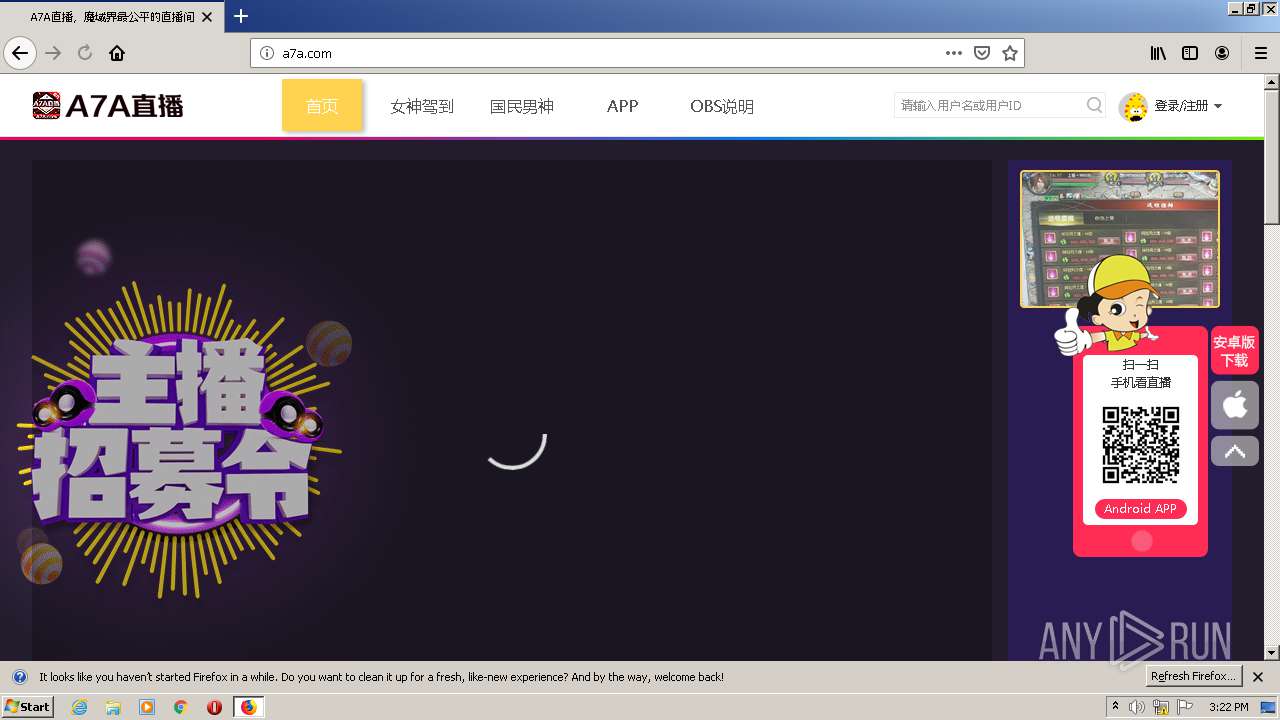
4028 | firefox.exe | GET | 200 | 47.246.50.229:80 | http://a7a.com/static/home/css/common.css?t=1542606716 | US | text | 16.9 Kb | suspicious |
4028 | firefox.exe | GET | 200 | 47.246.50.229:80 | http://a7a.com/ | US | html | 3.88 Kb | suspicious |
4028 | firefox.exe | GET | 200 | 47.246.50.229:80 | http://a7a.com/static/home/css/login.css | US | text | 7.32 Kb | suspicious |
4028 | firefox.exe | GET | 200 | 47.246.50.229:80 | http://a7a.com/static/home/js/login.js | US | text | 22.0 Kb | suspicious |
4028 | firefox.exe | GET | 200 | 47.246.50.229:80 | http://a7a.com/static/xigua/xgplayer.js?t=1574906138 | US | text | 217 Kb | suspicious |
4028 | firefox.exe | GET | 200 | 47.246.50.229:80 | http://a7a.com/static/xigua/xgplayer-flv.js.js | US | text | 169 Kb | suspicious |
4028 | firefox.exe | GET | 200 | 47.246.50.229:80 | http://a7a.com/static/home/js/jquery.lazyload.min.js | US | text | 3.30 Kb | suspicious |
4028 | firefox.exe | GET | 200 | 47.246.50.229:80 | http://a7a.com/static/js/jquery.js | US | text | 90.9 Kb | suspicious |
4028 | firefox.exe | GET | 200 | 47.246.50.229:80 | http://a7a.com/static/home/css/index.css | US | text | 28.4 Kb | suspicious |
4028 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4028 | firefox.exe | 2.16.177.18:80 | detectportal.firefox.com | Akamai International B.V. | — | unknown |
4028 | firefox.exe | 143.204.201.83:443 | snippets.cdn.mozilla.net | — | US | suspicious |
4028 | firefox.exe | 143.204.201.119:443 | snippets.cdn.mozilla.net | — | US | suspicious |
4028 | firefox.exe | 216.58.212.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
4028 | firefox.exe | 172.217.18.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
4028 | firefox.exe | 143.204.201.62:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
4028 | firefox.exe | 47.246.50.229:80 | a7a.com | — | US | unknown |
4028 | firefox.exe | 218.92.0.45:80 | qiniu.ccfugui.com | No.31,Jin-rong Street | CN | unknown |
2404 | pingsender.exe | 52.27.83.248:443 | incoming.telemetry.mozilla.org | Amazon.com, Inc. | US | unknown |
2404 | pingsender.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |