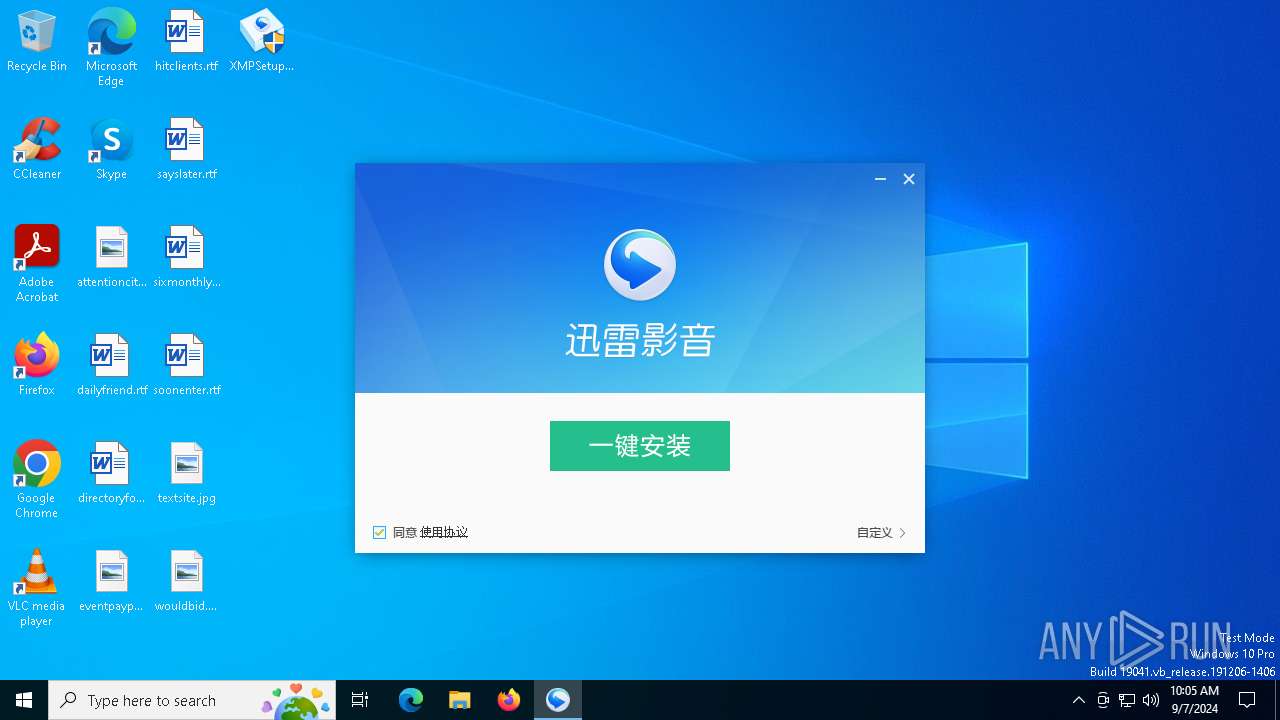
| File name: | XMPSetupKankan.exe |
| Full analysis: | https://app.any.run/tasks/6844e1e6-9f82-488b-af0b-ee42f304d4a5 |
| Verdict: | Malicious activity |
| Analysis date: | September 07, 2024, 10:05:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1233C6ABAA32971CA49597373485F6F0 |
| SHA1: | 339B7E979BDB64AFF037BE8FB2982BB88E78371D |
| SHA256: | 94D6A3E72E8E3479FCF2B3D71ED0E2B91B483C60BE298144B41089A61F296055 |
| SSDEEP: | 196608:gmTaTPgmdViv/bUbwuuljNPmiX2ghz1PBU+vE9vcidTaBMV:gmebk/gbtmhmiX2gz589vcUa2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- XMPSetupKankan.exe (PID: 6984)
Process drops legitimate windows executable
- XMPSetupKankan.exe (PID: 6984)
The process drops C-runtime libraries
- XMPSetupKankan.exe (PID: 6984)
Executable content was dropped or overwritten
- XMPSetupKankan.exe (PID: 6984)
INFO
Creates files in the program directory
- XMPSetupKankan.exe (PID: 6984)
Checks proxy server information
- XMPSetupKankan.exe (PID: 6984)
Creates files or folders in the user directory
- XMPSetupKankan.exe (PID: 6984)
Create files in a temporary directory
- XMPSetupKankan.exe (PID: 6984)
Reads the computer name
- XMPSetupKankan.exe (PID: 6984)
Checks supported languages
- XMPSetupKankan.exe (PID: 6984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (54.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (34.8) |
| .exe | | | Win32 Executable (generic) (5.6) |
| .exe | | | Generic Win/DOS Executable (2.5) |
| .exe | | | DOS Executable Generic (2.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:05:04 02:54:31+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 238080 |
| InitializedDataSize: | 29401600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x232ae |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.2.18.5894 |
| ProductVersionNumber: | 5.2.18.5894 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileDescription: | 迅雷影音 安装程序 |
| FileVersion: | 5, 2, 18, 5894 |
| InternalName: | XMPSetup |
| LegalCopyright: | Copyright (c) 2003-2017 深圳市迅雷网络技术有限公司 |
| OriginalFileName: | XMPSetup.exe |
| ProductName: | 迅雷影音 安装程序 |
| ProductVersion: | 5, 2, 18, 5894 |
| CompanyName: | 深圳市迅雷网络技术有限公司 |
| LegalTrademarks: | Xunlei |
Total processes
113
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4784 | "C:\Users\admin\Desktop\XMPSetupKankan.exe" | C:\Users\admin\Desktop\XMPSetupKankan.exe | — | explorer.exe | |||||||||||
User: admin Company: 深圳市迅雷网络技术有限公司 Integrity Level: MEDIUM Description: 迅雷影音 安装程序 Exit code: 3221226540 Version: 5, 2, 18, 5894 Modules
| |||||||||||||||
| 6984 | "C:\Users\admin\Desktop\XMPSetupKankan.exe" | C:\Users\admin\Desktop\XMPSetupKankan.exe | explorer.exe | ||||||||||||
User: admin Company: 深圳市迅雷网络技术有限公司 Integrity Level: HIGH Description: 迅雷影音 安装程序 Version: 5, 2, 18, 5894 Modules
| |||||||||||||||
Total events
478
Read events
471
Write events
7
Delete events
0
Modification events
| (PID) Process: | (6984) XMPSetupKankan.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Compatibility Assistant\Persisted |
| Operation: | write | Name: | C:\Users\admin\Desktop\XMPSetupKankan.exe |
Value: 1 | |||
| (PID) Process: | (6984) XMPSetupKankan.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Compatibility Assistant\Persisted |
| Operation: | write | Name: | SIGN.IE=01C48E90 XMPSetupKankan.exe |
Value: 1 | |||
| (PID) Process: | (6984) XMPSetupKankan.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Compatibility Assistant\Persisted |
| Operation: | write | Name: | SIGN.MEDIA=10C1A20 XMPSetupKankan.exe |
Value: 1 | |||
| (PID) Process: | (6984) XMPSetupKankan.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6984) XMPSetupKankan.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6984) XMPSetupKankan.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6984) XMPSetupKankan.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Thunder Network\Xmp |
| Operation: | write | Name: | allowplaysubtype |
Value: | |||
Executable files
135
Suspicious files
66
Text files
59
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6984 | XMPSetupKankan.exe | C:\Users\admin\AppData\Local\Temp\XMPSetupKankan\5.2.18.5894\SetupUI.cab | — | |
MD5:— | SHA256:— | |||
| 6984 | XMPSetupKankan.exe | C:\Users\admin\AppData\Local\Temp\XMPSetupKankan\5.2.18.5894\atl71.dll | executable | |
MD5:4EDD8D74EA48F58D3ECA7E9297F19221 | SHA256:D422497FEBAA2FBB83A8A2EC342E08884C5A77FBDDABDE7BEC4E21884F56D0CE | |||
| 6984 | XMPSetupKankan.exe | C:\ProgramData\Thunder Network\DownloadLib\pub_store.dat | text | |
MD5:F79C563BC47D7920DD680E84D5702346 | SHA256:5AFC59CCD82D6312D396E1923A910C645785C497E3CD0BD8CD545FE8FEC2E182 | |||
| 6984 | XMPSetupKankan.exe | C:\Users\admin\AppData\Local\Temp\XMPSetupKankan\5.2.18.5894\msvcp90.dll | executable | |
MD5:6DE5C66E434A9C1729575763D891C6C2 | SHA256:4F7ED27B532888CE72B96E52952073EAB2354160D1156924489054B7FA9B0B1A | |||
| 6984 | XMPSetupKankan.exe | C:\Users\admin\AppData\Local\Temp\XMPSetupKankan\5.2.18.5894\Microsoft.VC90.CRT.manifest | xml | |
MD5:4F9ED5EFA4F7B75BCFE0F36C36EE5CB6 | SHA256:FF718390133B400EE679177B2902BBB918DB148BBB4ABABA03D0A1DF325B3303 | |||
| 6984 | XMPSetupKankan.exe | C:\Users\admin\AppData\Local\Temp\XMPSetupKankan\5.2.18.5894\mini_unzip_dll.dll | executable | |
MD5:FCF06CE8023FDD59074FA557416D9DB8 | SHA256:B80A73C17946C6827A91F7A5B3B8155C240517160E6A8D97B751B9E9B3293C06 | |||
| 6984 | XMPSetupKankan.exe | C:\Users\admin\AppData\Local\Temp\XMPSetupKankan\5.2.18.5894\minizip.dll | executable | |
MD5:6C49EEA477828B88C4DF95BFD508B64C | SHA256:E5B5238CDC5C0F68F259C0C6793B0BCC3C38E1B6C4BD80186FE783C1A287C3FA | |||
| 6984 | XMPSetupKankan.exe | C:\Users\admin\AppData\Local\Temp\XMPSetupKankan\5.2.18.5894\libexpat.dll | executable | |
MD5:61E0F581F2330ABF707590AF01A6CAF3 | SHA256:8E7465EDD50EAFF7F1A2236A9FF2BAD7D0FB1220B0AC3855ADE24EBE9BC9D136 | |||
| 6984 | XMPSetupKankan.exe | C:\Users\admin\AppData\Local\Temp\XMPSetupKankan\5.2.18.5894\msvcr90.dll | executable | |
MD5:E7D91D008FE76423962B91C43C88E4EB | SHA256:ED0170D3DE86DA33E02BFA1605EEC8FF6010583481B1C530843867C1939D2185 | |||
| 6984 | XMPSetupKankan.exe | C:\Users\admin\AppData\Local\Temp\XMPSetupKankan\5.2.18.5894\zlib1.dll | executable | |
MD5:DDDC416F84AC8276620ED3100C22EFC5 | SHA256:563516479ADBA55646A691D43EECE6E3FE90380DCC51DA1855605B8739BE3C30 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
21
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
6984 | XMPSetupKankan.exe | GET | 200 | 39.104.21.243:80 | http://conf.v.xunlei.com/setup/xmp5/onlineindex.lua | CN | binary | 49.8 Kb | unknown |
6984 | XMPSetupKankan.exe | GET | 200 | 39.104.21.243:80 | http://conf.v.xunlei.com/setup/xmp5/onlineindex_config.lua | CN | text | 179 b | unknown |
6984 | XMPSetupKankan.exe | GET | — | 39.104.21.243:80 | http://conf.v.xunlei.com/setup/xmp5/startpageonline.lua | CN | — | — | unknown |
6984 | XMPSetupKankan.exe | GET | — | 39.104.21.243:80 | http://conf.v.xunlei.com/setup/xmp5/shortcutonline.lua | CN | — | — | unknown |
6012 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6012 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6984 | XMPSetupKankan.exe | 39.104.21.243:80 | conf.v.xunlei.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
user.stat.v.xunlei.com |
| unknown |
setup.stat.v.xunlei.com |
| unknown |
conf.v.xunlei.com |
| unknown |
02.rcv.sandai.net |
| whitelisted |
zone.xmp.kankan.xunlei.com |
| unknown |