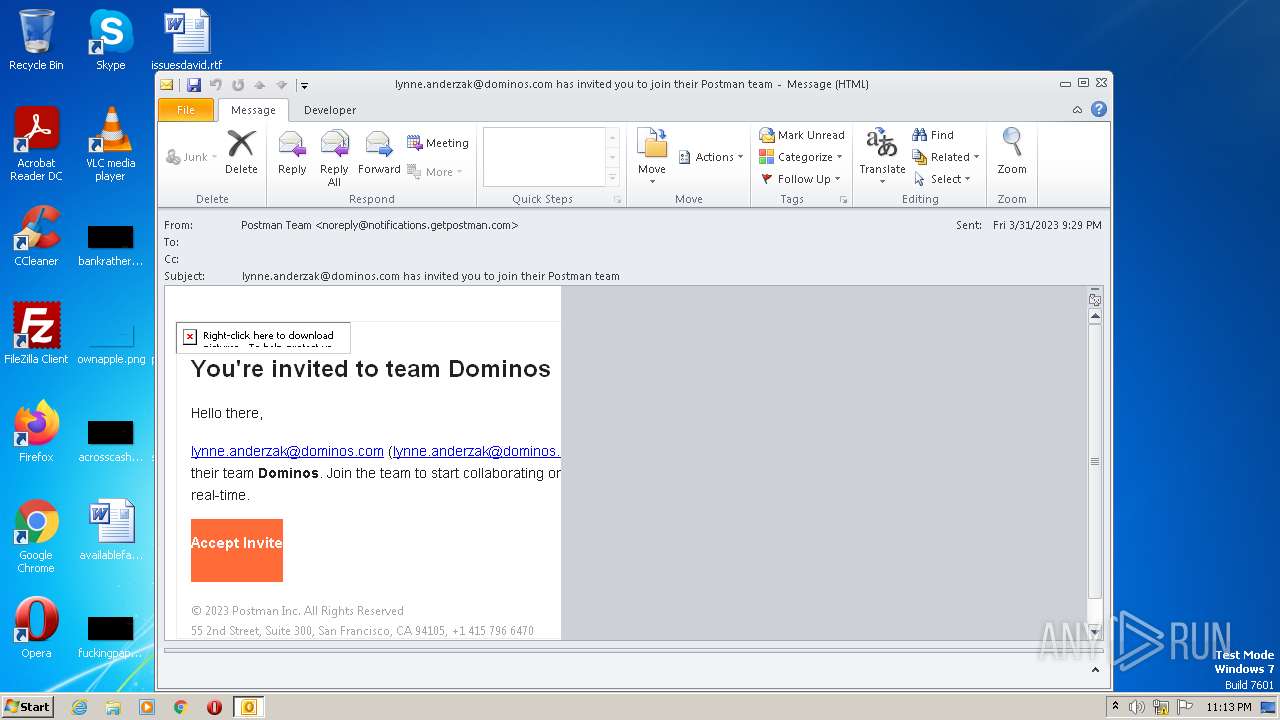
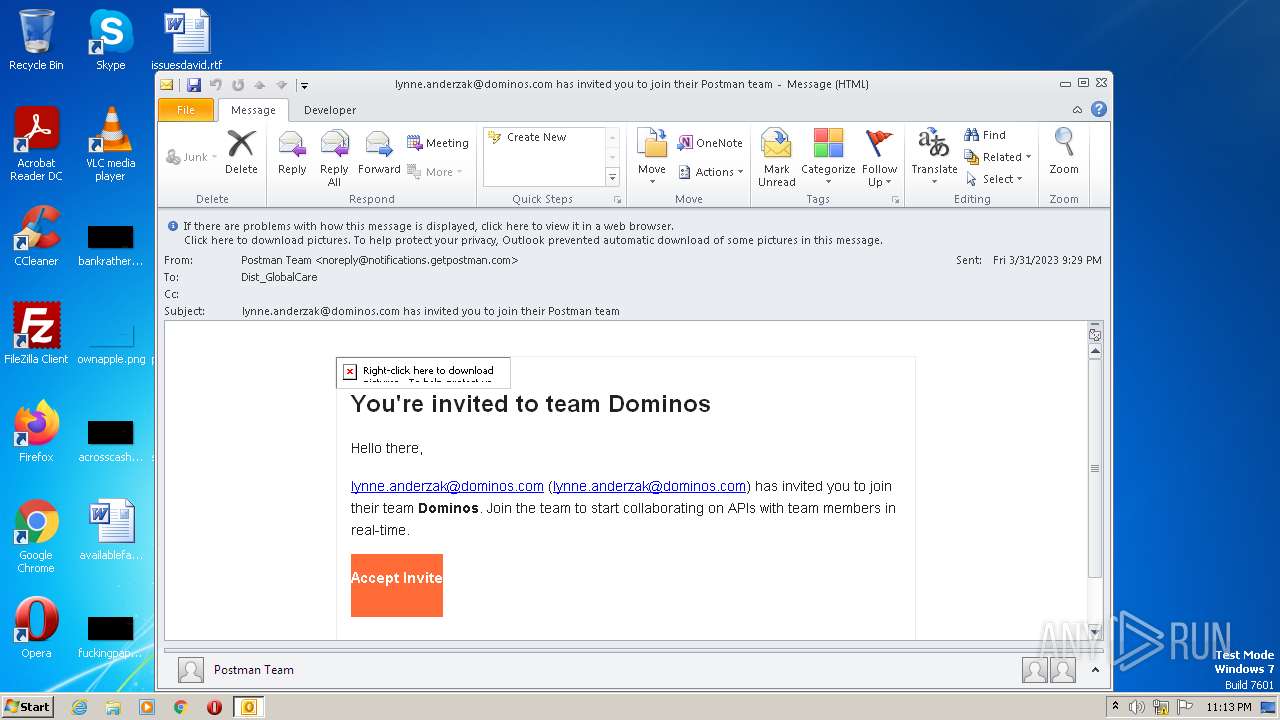
| File name: | phish_alert_sp2_2.0.0.0.eml |
| Full analysis: | https://app.any.run/tasks/ab72745a-36bc-4e08-a875-22fed0cbdd82 |
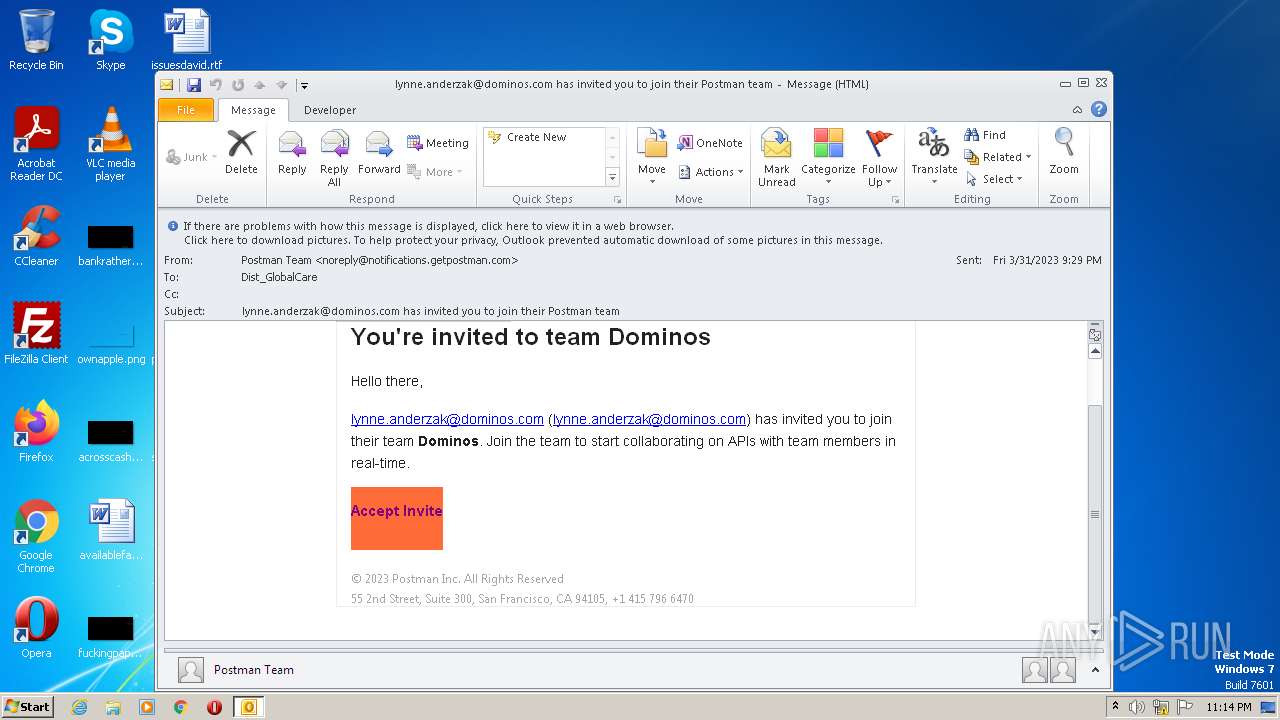
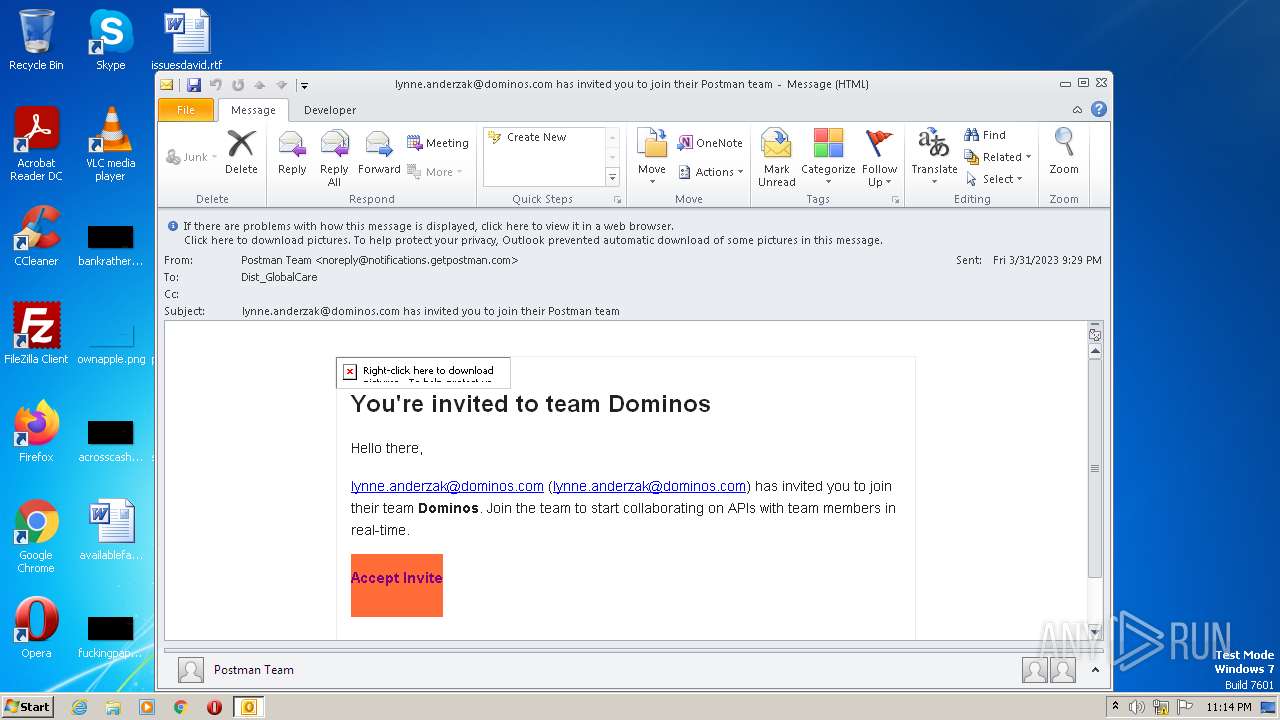
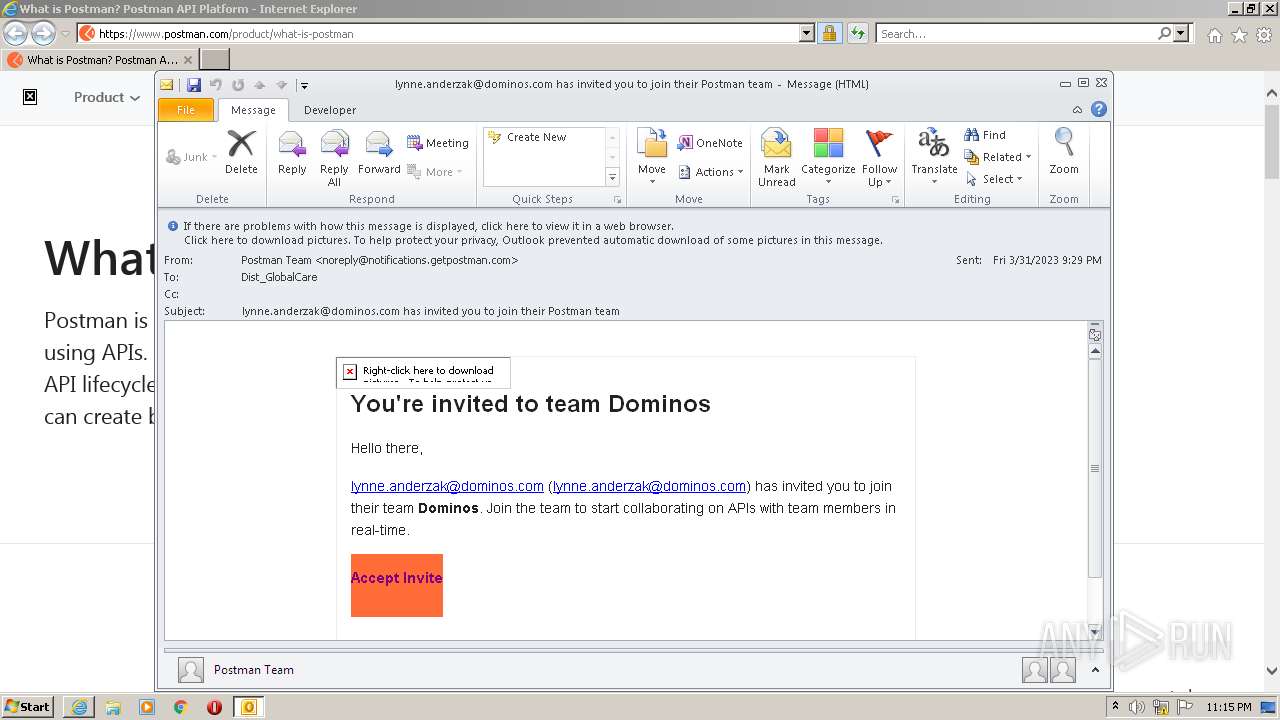
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2023, 22:13:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 10E7468E15DBA6C26BB964C899A9E6F1 |
| SHA1: | 00F4ED1530ACA34806F967B9760BC793CED4C49C |
| SHA256: | 94CD18A28FBC7E02D63AFAD65CA0F8AD41B18BB4D489794773729B52B574DBC4 |
| SSDEEP: | 384:1clMCer3yWKTlKphfyWP0cuoTC/T9Rw1Wf8/DH57:QMLrCW5DfyWMRoTQkWfgHd |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- OUTLOOK.EXE (PID: 2368)
Searches for installed software
- OUTLOOK.EXE (PID: 2368)
INFO
Checks supported languages
- OUTLOOK.EXE (PID: 2368)
The process checks LSA protection
- OUTLOOK.EXE (PID: 2368)
Reads the machine GUID from the registry
- OUTLOOK.EXE (PID: 2368)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2368)
Creates files or folders in the user directory
- OUTLOOK.EXE (PID: 2368)
Reads the computer name
- OUTLOOK.EXE (PID: 2368)
Create files in a temporary directory
- OUTLOOK.EXE (PID: 2368)
- iexplore.exe (PID: 2460)
- iexplore.exe (PID: 664)
Application launched itself
- iexplore.exe (PID: 2460)
- iexplore.exe (PID: 664)
Checks proxy server information
- OUTLOOK.EXE (PID: 2368)
Process checks computer location settings
- OUTLOOK.EXE (PID: 2368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
46
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
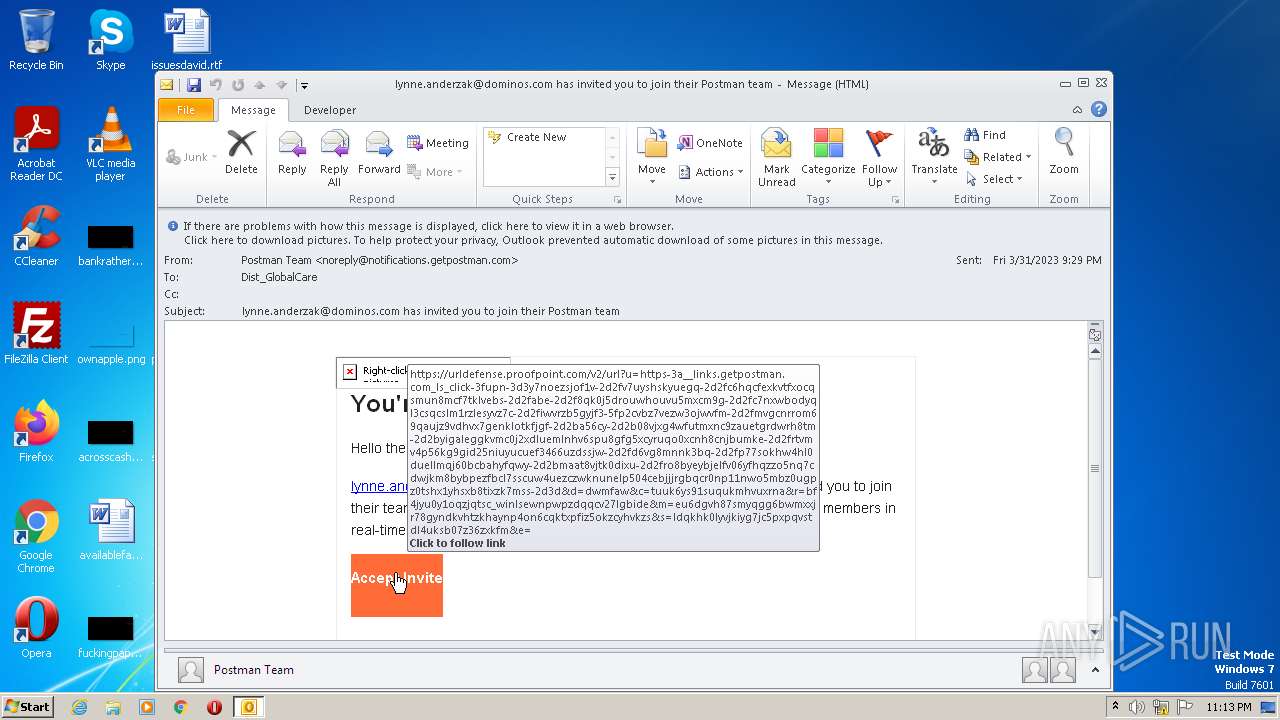
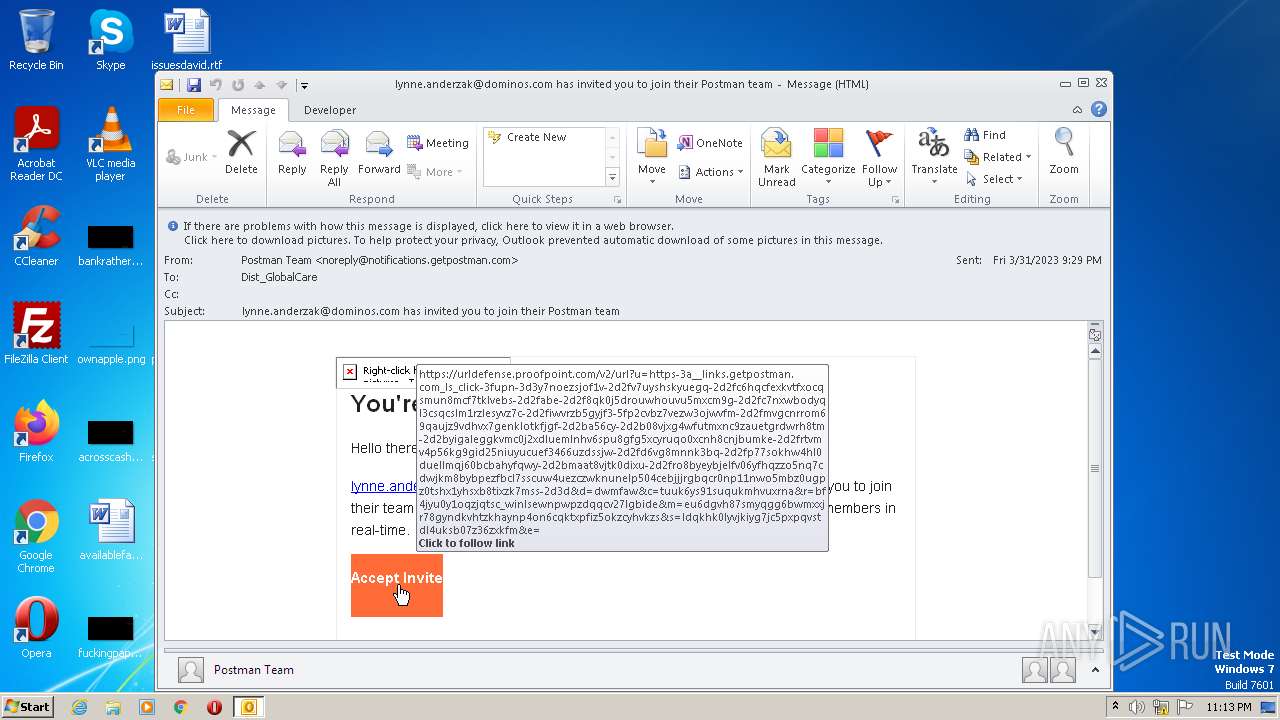
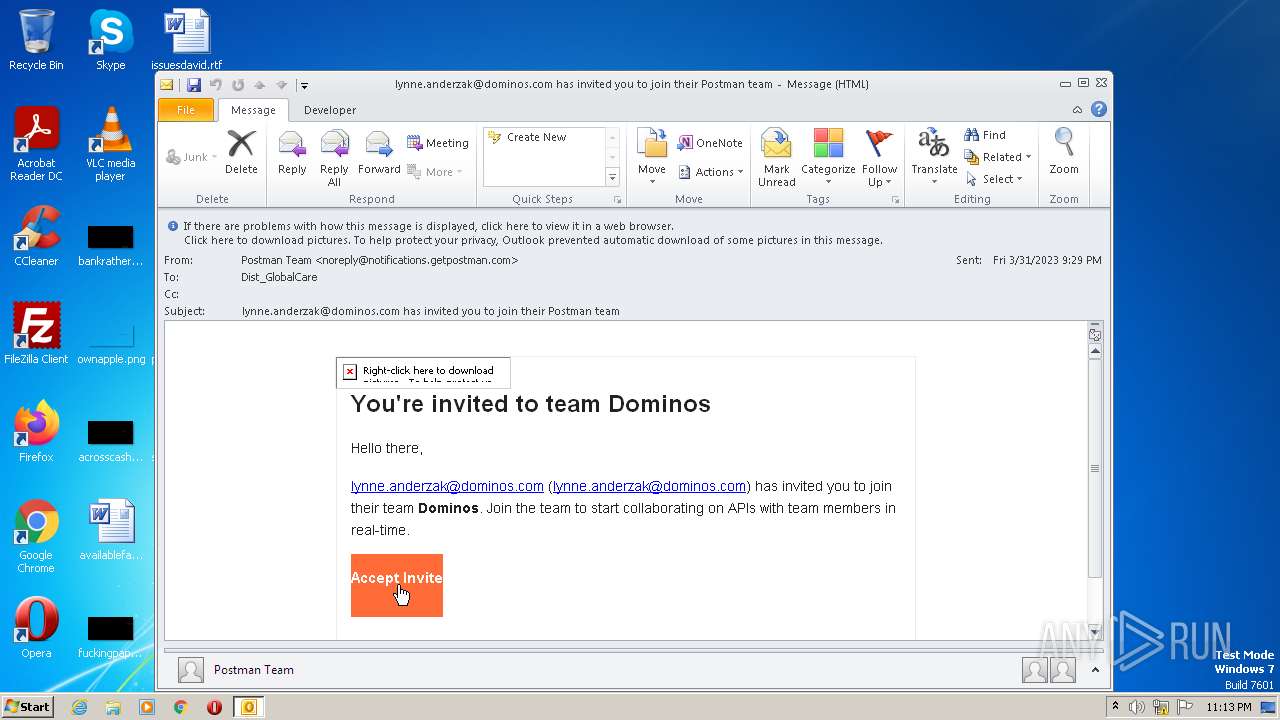
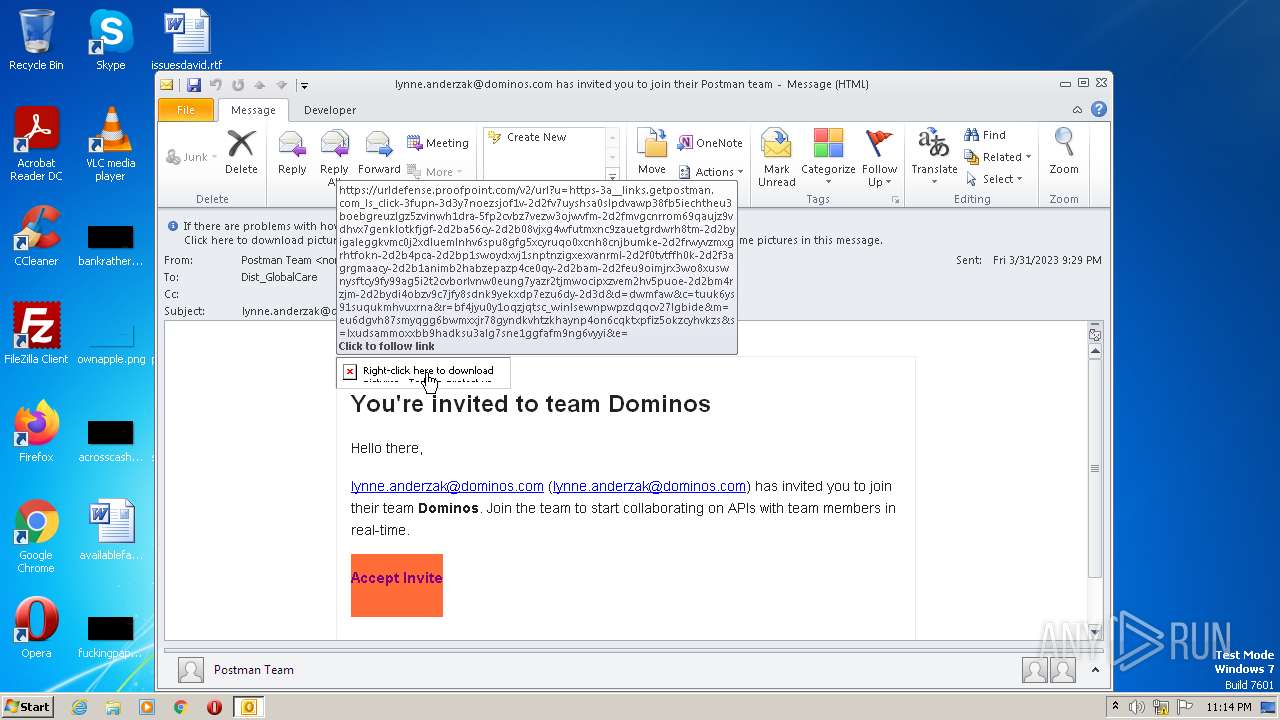
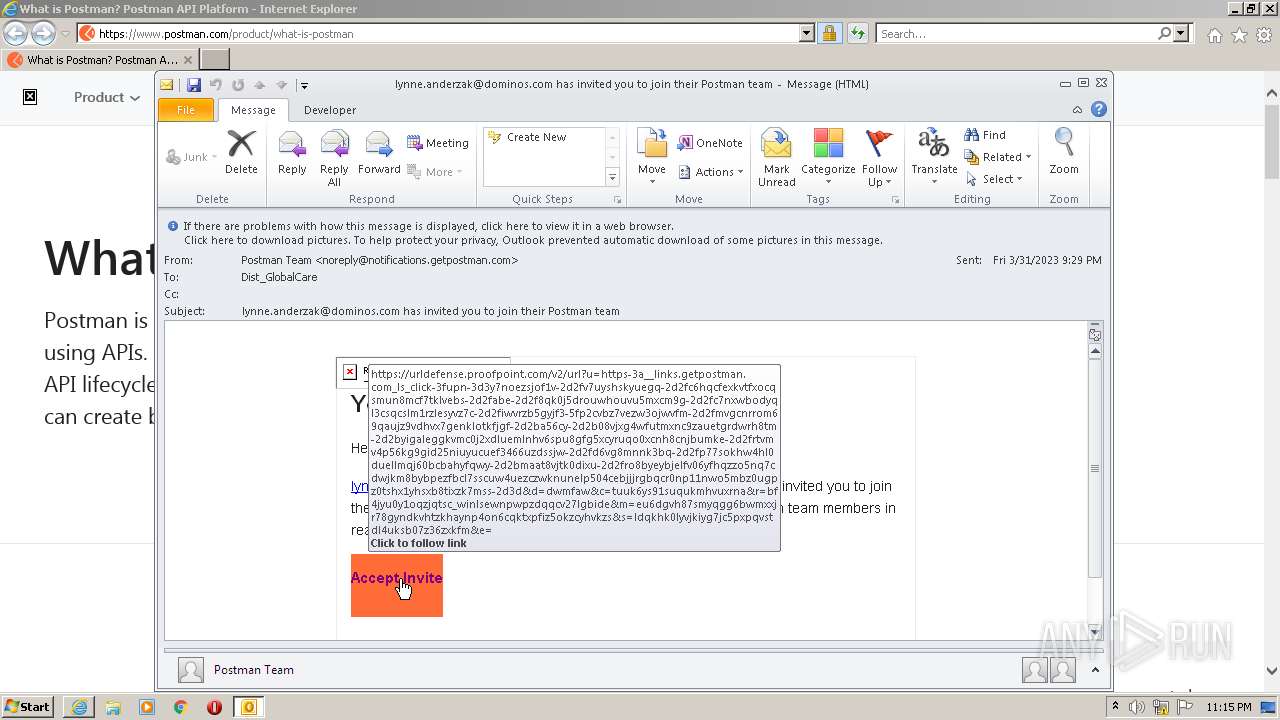
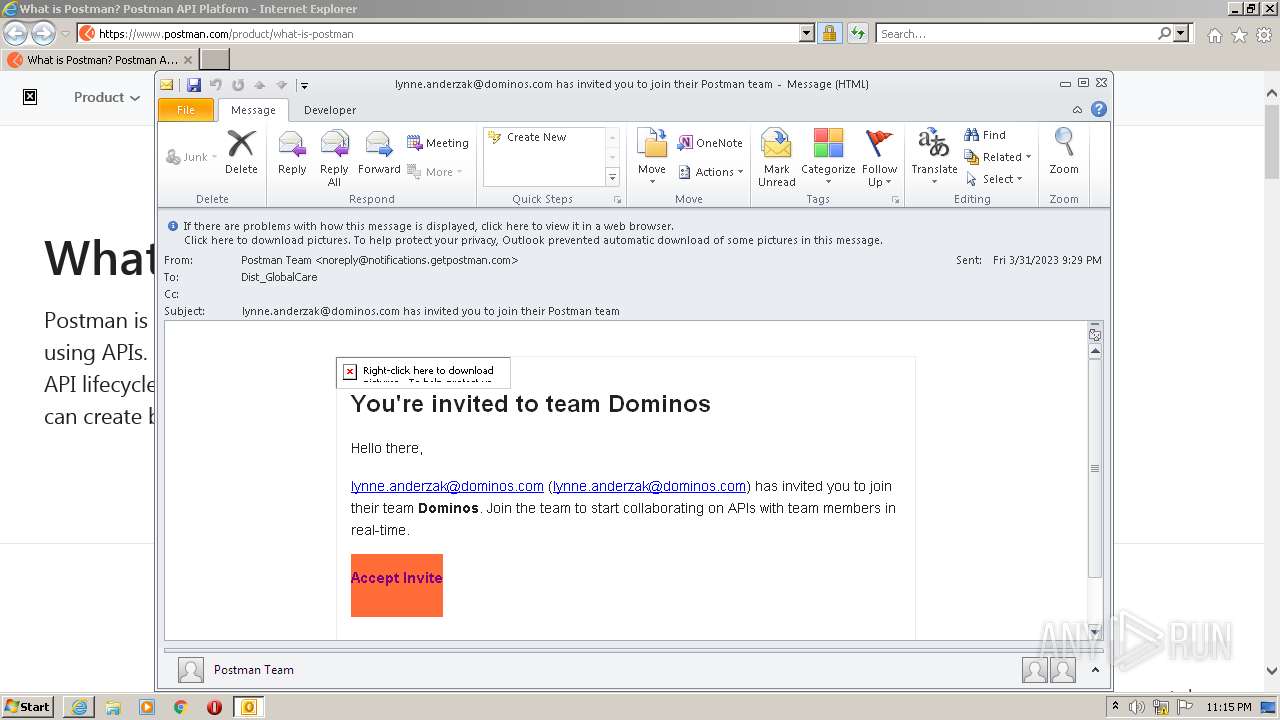
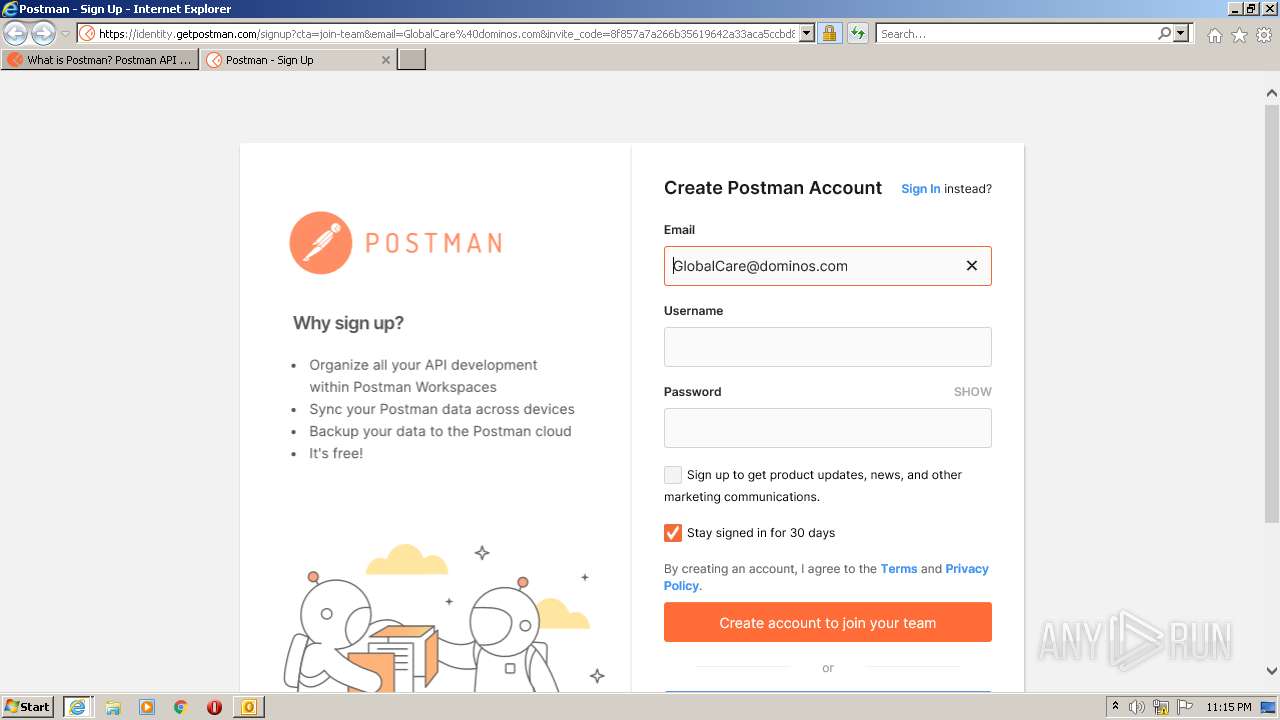
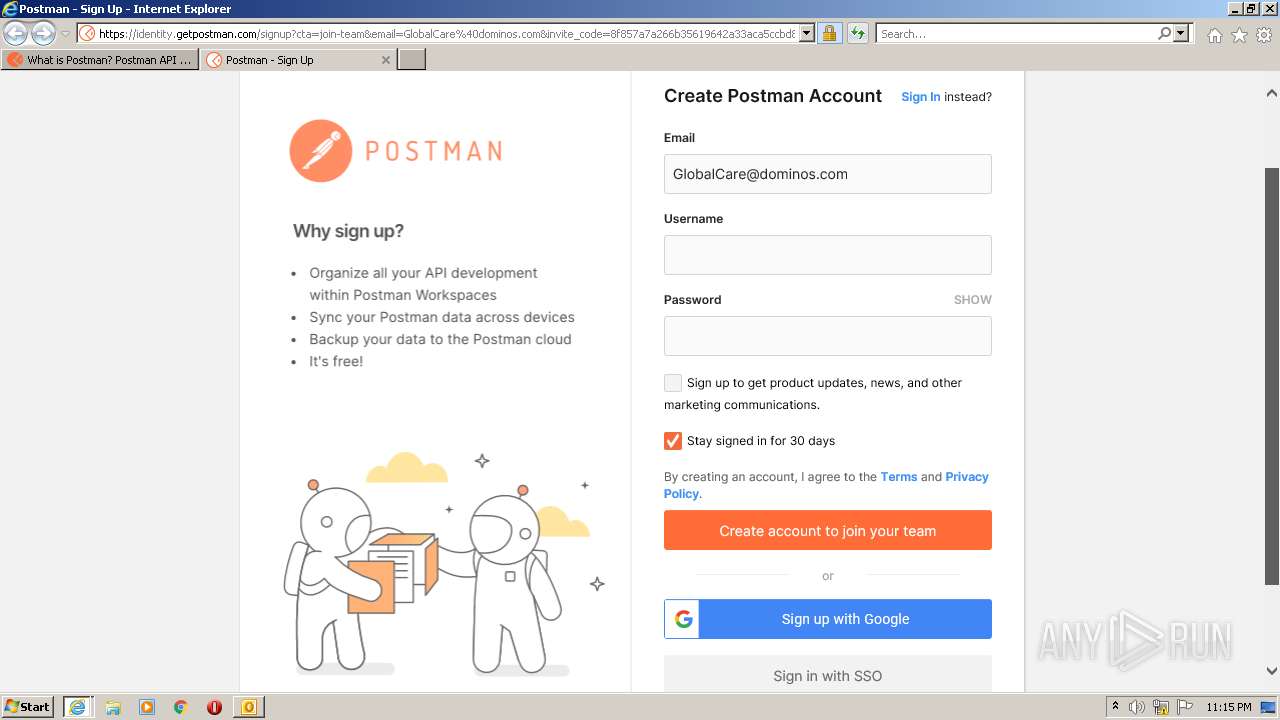
| 664 | "C:\Program Files\Internet Explorer\iexplore.exe" https://urldefense.proofpoint.com/v2/url?u=https-3A__links.getpostman.com_ls_click-3Fupn-3D3y7nOEZSJOF1v-2D2Fv7UyshsA0slPDVAWp38fB5IEChtheu3bOEbgreuzlgz5zViNwH1dRA-5FP2CVbZ7VEZW3OJwvfm-2D2FmVgcnRROM69QAuJZ9vDHvX7genKlOTKFjgF-2D2BA56cy-2D2B08vJXg4wFuTmXNc9zAUeTgRDWRH8tm-2D2BYiGAleggKVmc0j2XdlUemLNhv6Spu8GFG5XcyrUqo0Xcnh8cnjbUmKe-2D2FRWYVzMXgRhTFoKN-2D2B4Pca-2D2Bp1SwOYdxVj1SnptnziGxExvaNrML-2D2F0TvtfFH0K-2D2F3AgrgMaacY-2D2B1ANimb2hAbZEpaZp4CE0QY-2D2Bam-2D2FeU9OIMJRX3wo8XuswnysftCY9FY99AG5I2T2CvbOrLvnw0eUNg7YazR2TJmwocIpXZvem2hV5PuOE-2D2BM4RZJm-2D2BYDI4oBzV9c7jfY8sdnK9yEKxDP7ezU6dY-2D3D&d=DwMFAw&c=tuuk6YS91SuQukMhvUXrnA&r=BF4JyU0Y1oQZJQTsc_wInLSEwNpwPZdQqCv27lGbiDE&m=eu6dgvh87SMyqGg6bwMXXjR78gyNdkvHtzKHaYNp4oN6cqktXPFiZ5OkZcYHvkZS&s=LxudsAMMOXXbB9HAdKsu3alG7SNe1gGFAfm9Ng6VyYI&e= | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2368 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\phish_alert_sp2_2.0.0.0.eml" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Internet Explorer\iexplore.exe" https://urldefense.proofpoint.com/v2/url?u=https-3A__links.getpostman.com_ls_click-3Fupn-3D3y7nOEZSJOF1v-2D2Fv7UyshsKYUegQ-2D2FC6hQcfExkvtFxOCQSmun8mCf7tKlvebS-2D2FAbE-2D2F8Qk0J5DROuWHOuvU5MXcm9g-2D2Fc7NXWboDyqL3CsqCsLM1rzLeSyvz7c-2D2FIWvrzB5GyjF3-5FP2CVbZ7VEZW3OJwvfm-2D2FmVgcnRROM69QAuJZ9vDHvX7genKlOTKFjgF-2D2BA56cy-2D2B08vJXg4wFuTmXNc9zAUeTgRDWRH8tm-2D2BYiGAleggKVmc0j2XdlUemLNhv6Spu8GFG5XcyrUqo0Xcnh8cnjbUmKe-2D2FRTvMv4P56kG9GiD25NiUyucUef3466uZDssjw-2D2Fd6vG8mNNk3BQ-2D2FP77sokHW4Hl0dUelLMqj60BCBahYFqwy-2D2BmaAT8VjTk0dIXU-2D2FRo8BYeybjelFv06yfHqZZo5NQ7cDwjKm8bybpEzfBcL7SsCuw4UEZCzwKnUnElp504CEBJjjrGBqcr0NP11NwO5MbZ0UGpz0TShx1YhsXB8tixZk7MSs-2D3D&d=DwMFAw&c=tuuk6YS91SuQukMhvUXrnA&r=BF4JyU0Y1oQZJQTsc_wInLSEwNpwPZdQqCv27lGbiDE&m=eu6dgvh87SMyqGg6bwMXXjR78gyNdkvHtzKHaYNp4oN6cqktXPFiZ5OkZcYHvkZS&s=LDQkHk0lyVJKiyg7jc5PXpqvSTDL4UKSb07Z36zxKfM&e= | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2900 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:664 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3224 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2460 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3712 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:664 CREDAT:660768 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
120 438
Read events
119 186
Write events
1 208
Delete events
44
Modification events
| (PID) Process: | (2368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (2368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (2368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (2368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (2368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (2368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (2368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (2368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (2368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
0
Suspicious files
60
Text files
132
Unknown types
56
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2368 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRFD4C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2368 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2368 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2368 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3224 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:— | SHA256:— | |||
| 3224 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3224 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 3224 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 3224 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | der | |
MD5:— | SHA256:— | |||
| 3224 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
128
DNS requests
50
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2368 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3224 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 1.42 Kb | whitelisted |
3224 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 2.18 Kb | whitelisted |
3224 | iexplore.exe | GET | 200 | 108.138.2.173:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3224 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCEAtkAeQNBc8Mrt%2B1FY0cY%2Bg%3D | US | der | 471 b | whitelisted |
2460 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3224 | iexplore.exe | GET | 200 | 52.222.226.205:80 | http://ocsp.r2m02.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRmbQtwnInkvkvr7BNFR%2BS2lTYPjAQUwDFSzVpQw4J8dHHOy%2Bmc%2BXrrguICEAO2%2FCXty0krWayEwEKjsAQ%3D | US | der | 471 b | whitelisted |
2900 | iexplore.exe | GET | 200 | 52.222.226.205:80 | http://ocsp.r2m02.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRmbQtwnInkvkvr7BNFR%2BS2lTYPjAQUwDFSzVpQw4J8dHHOy%2Bmc%2BXrrguICEA5lV5%2FJdwsdaivGBcBMPn8%3D | US | der | 471 b | whitelisted |
3224 | iexplore.exe | GET | 200 | 52.222.250.42:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | US | der | 1.39 Kb | shared |
3224 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2368 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
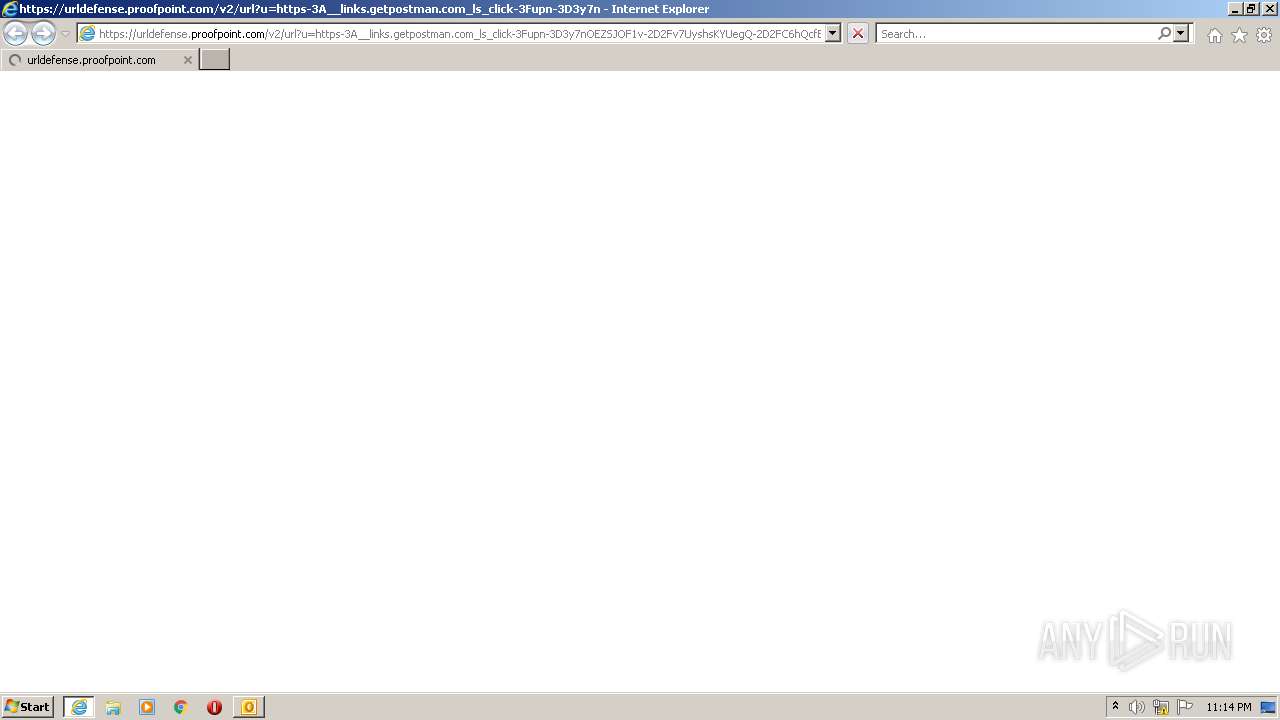
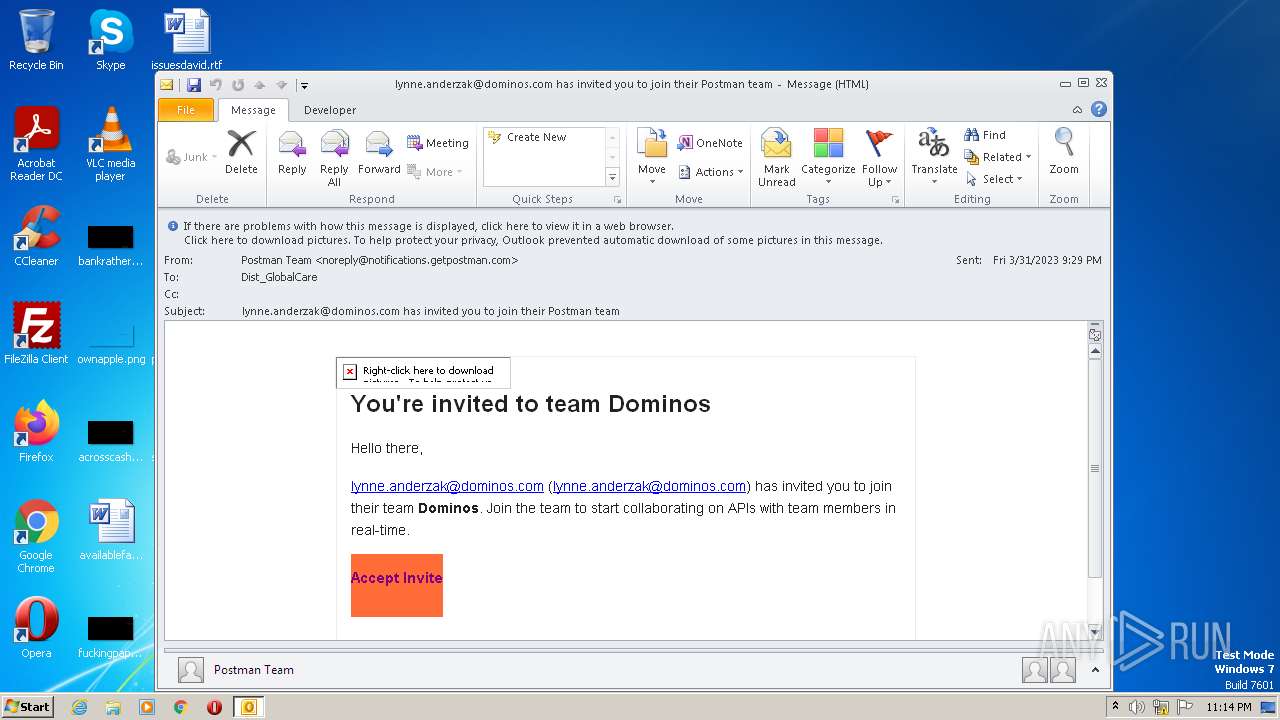
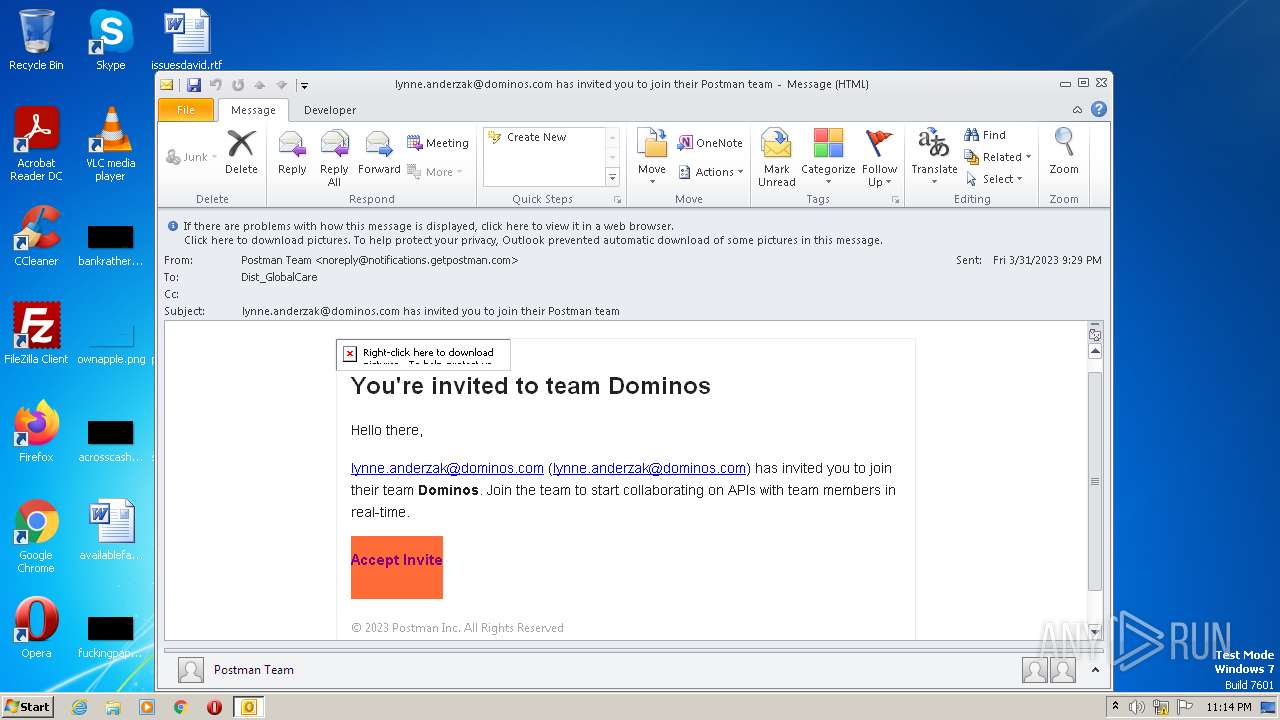
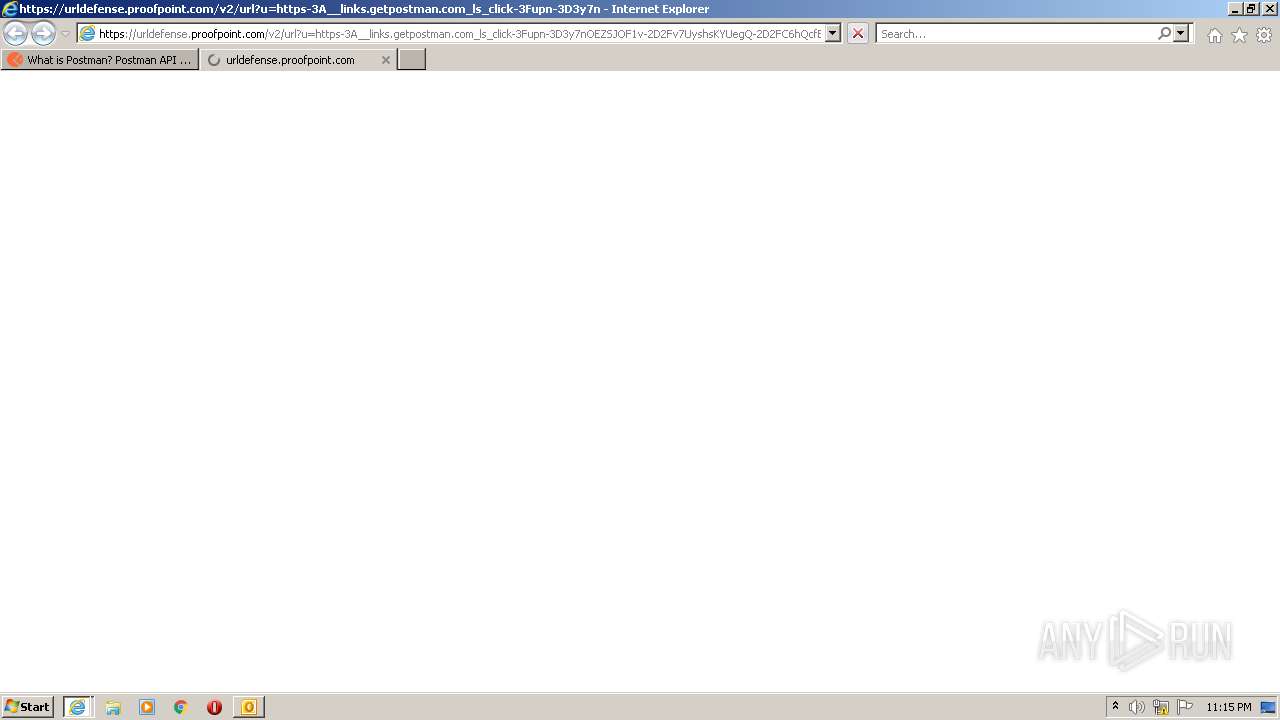
3224 | iexplore.exe | 67.231.146.66:443 | urldefense.proofpoint.com | PROOFPOINT-ASN-US-WEST | US | suspicious |
3224 | iexplore.exe | 34.194.89.64:443 | links.getpostman.com | AMAZON-AES | US | unknown |
3224 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | CLOUDFLARENET | US | suspicious |
3224 | iexplore.exe | 108.138.2.173:80 | o.ss2.us | AMAZON-02 | US | unknown |
3224 | iexplore.exe | 52.222.250.112:80 | ocsp.rootg2.amazontrust.com | AMAZON-02 | US | whitelisted |
3224 | iexplore.exe | 52.222.250.42:80 | ocsp.rootg2.amazontrust.com | AMAZON-02 | US | whitelisted |
3224 | iexplore.exe | 52.222.226.205:80 | ocsp.r2m02.amazontrust.com | AMAZON-02 | US | unknown |
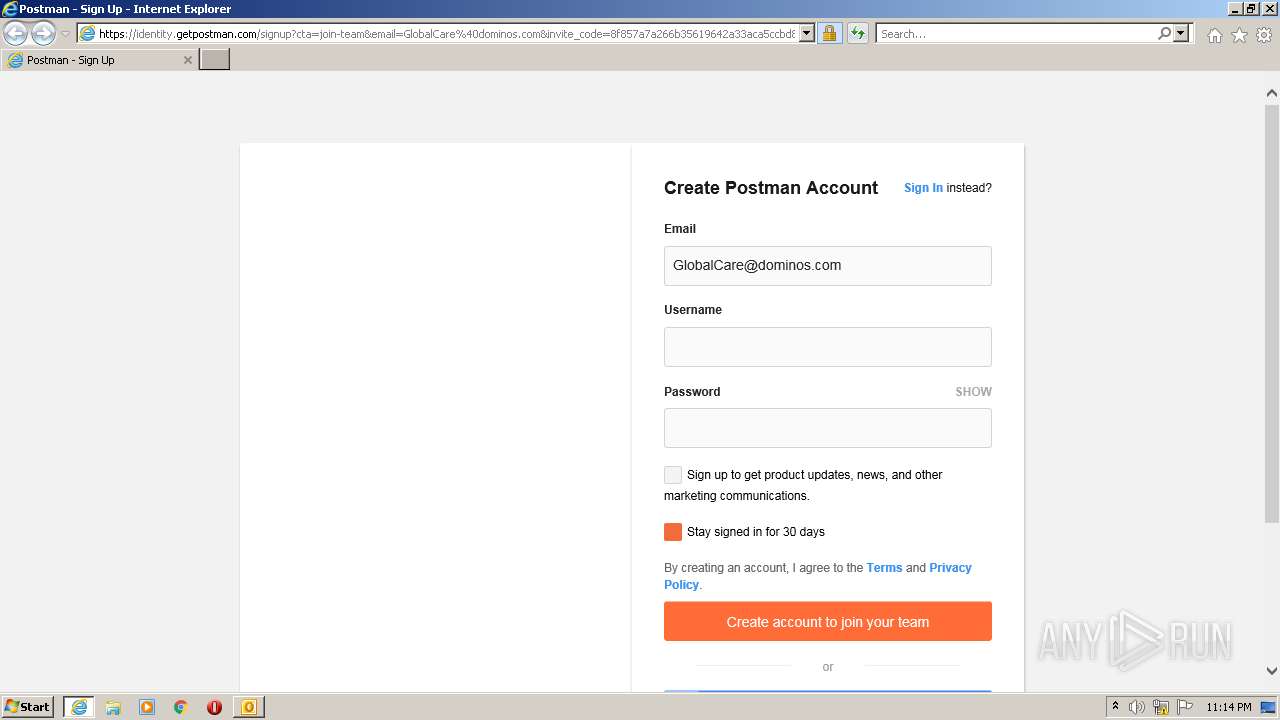
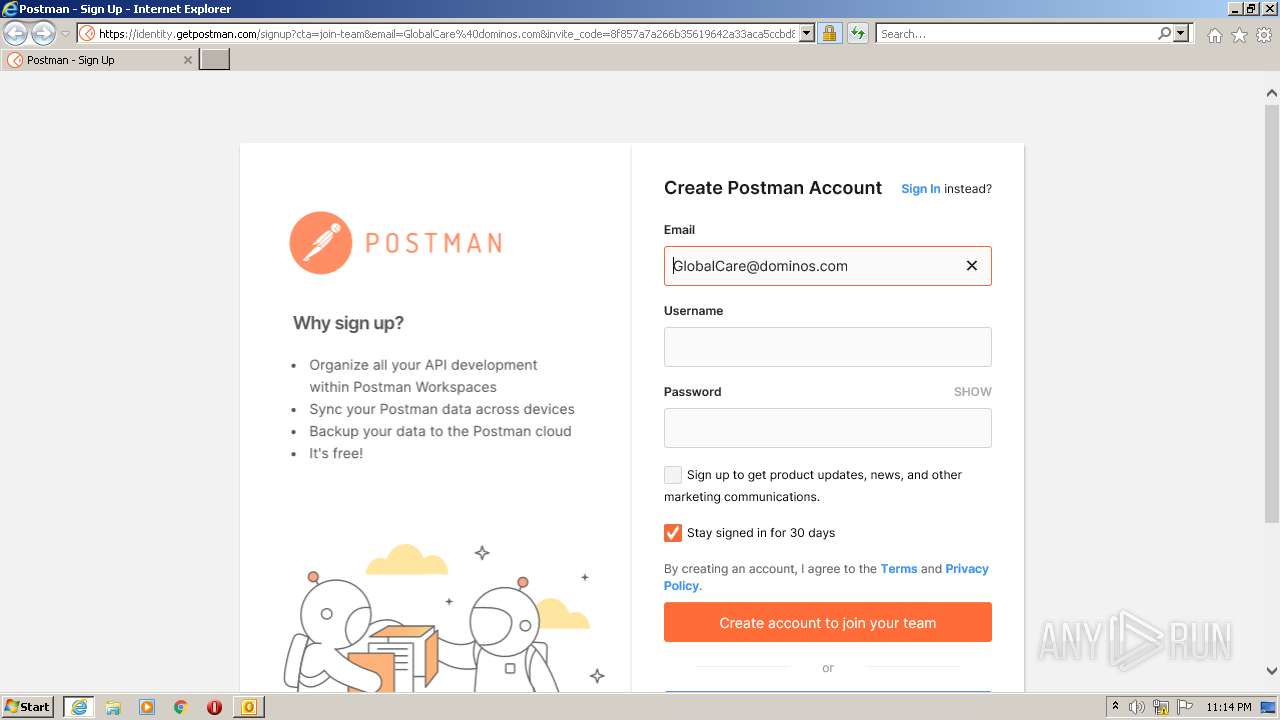
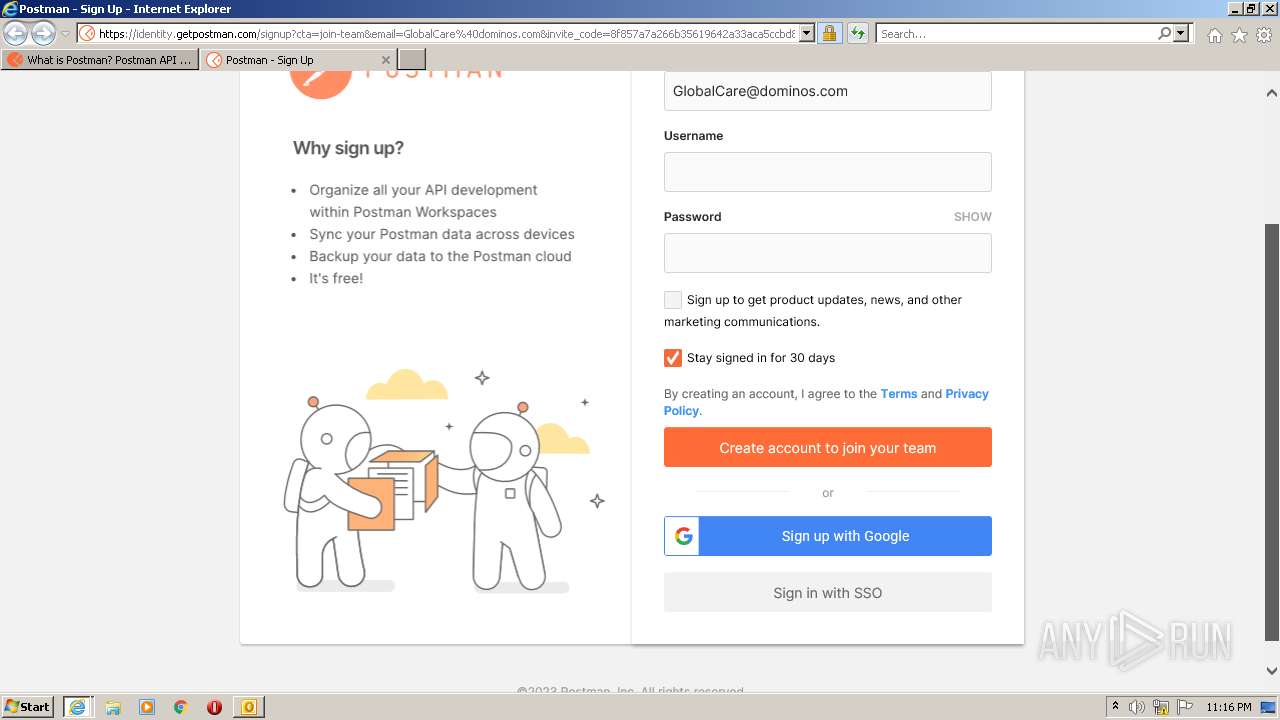
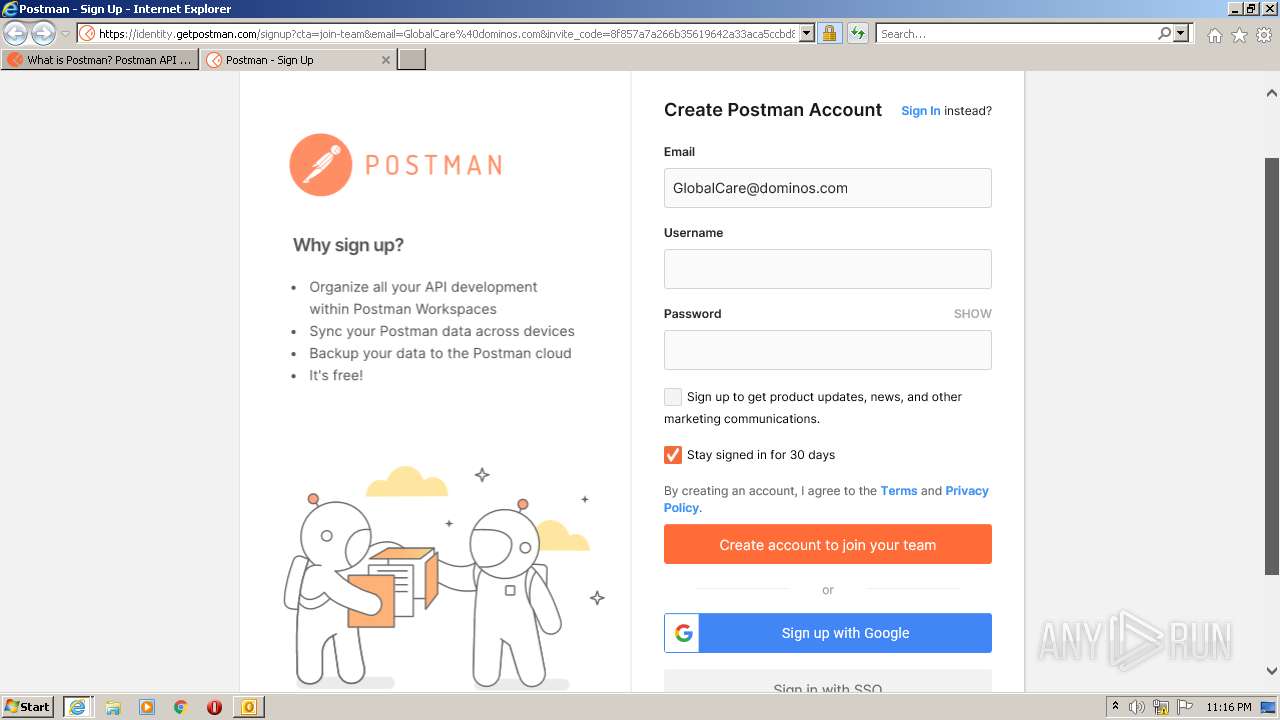
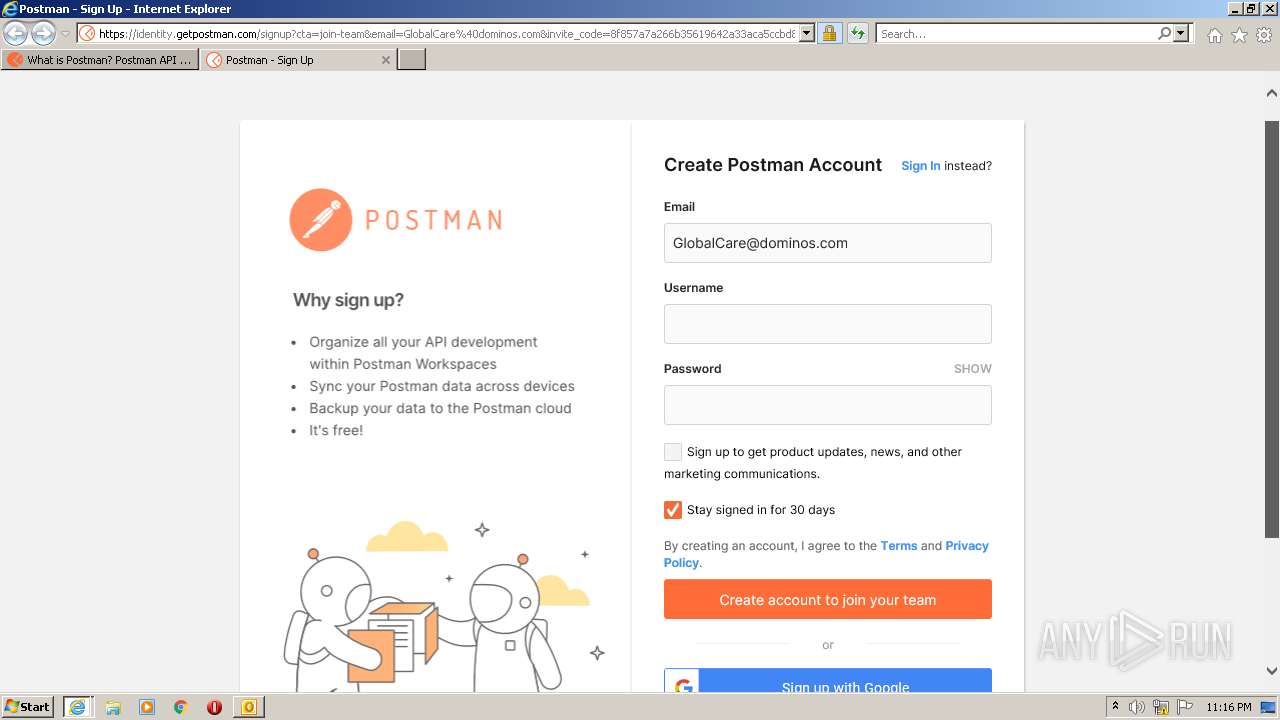
3224 | iexplore.exe | 54.236.151.127:443 | app.getpostman.com | AMAZON-AES | US | unknown |
3224 | iexplore.exe | 104.18.24.175:443 | identity.getpostman.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
urldefense.proofpoint.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
links.getpostman.com |
| unknown |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |