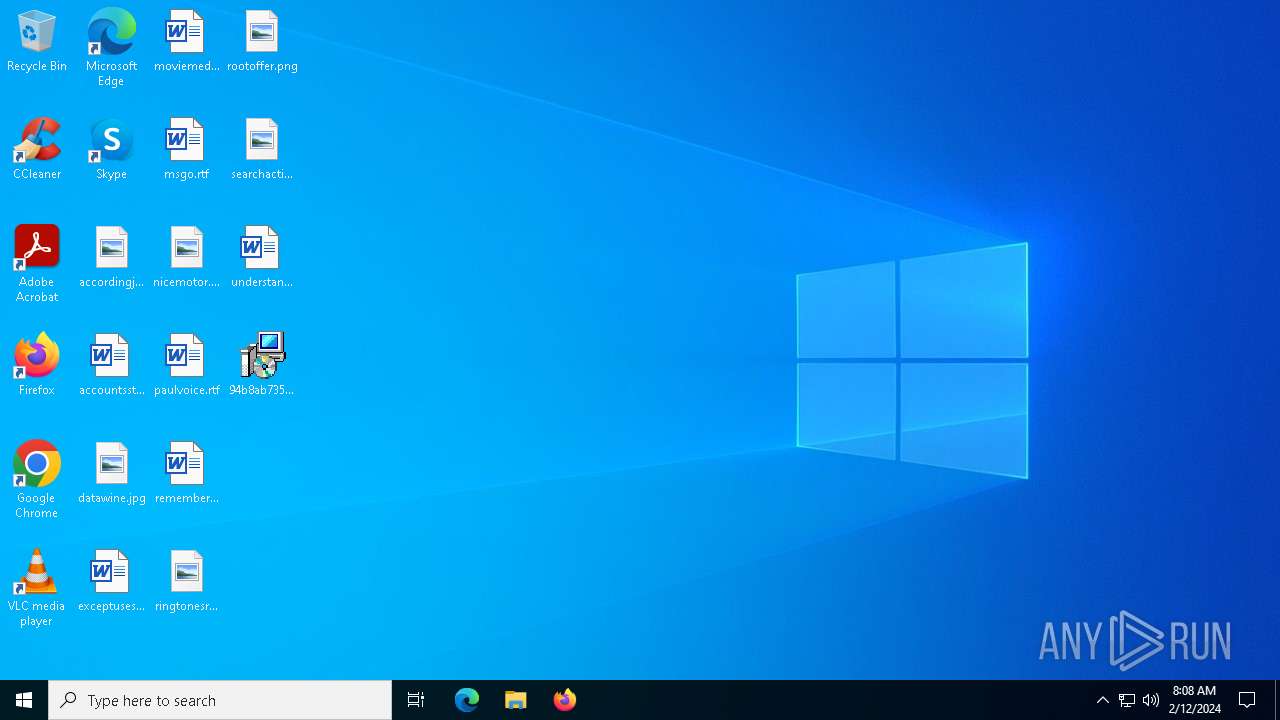
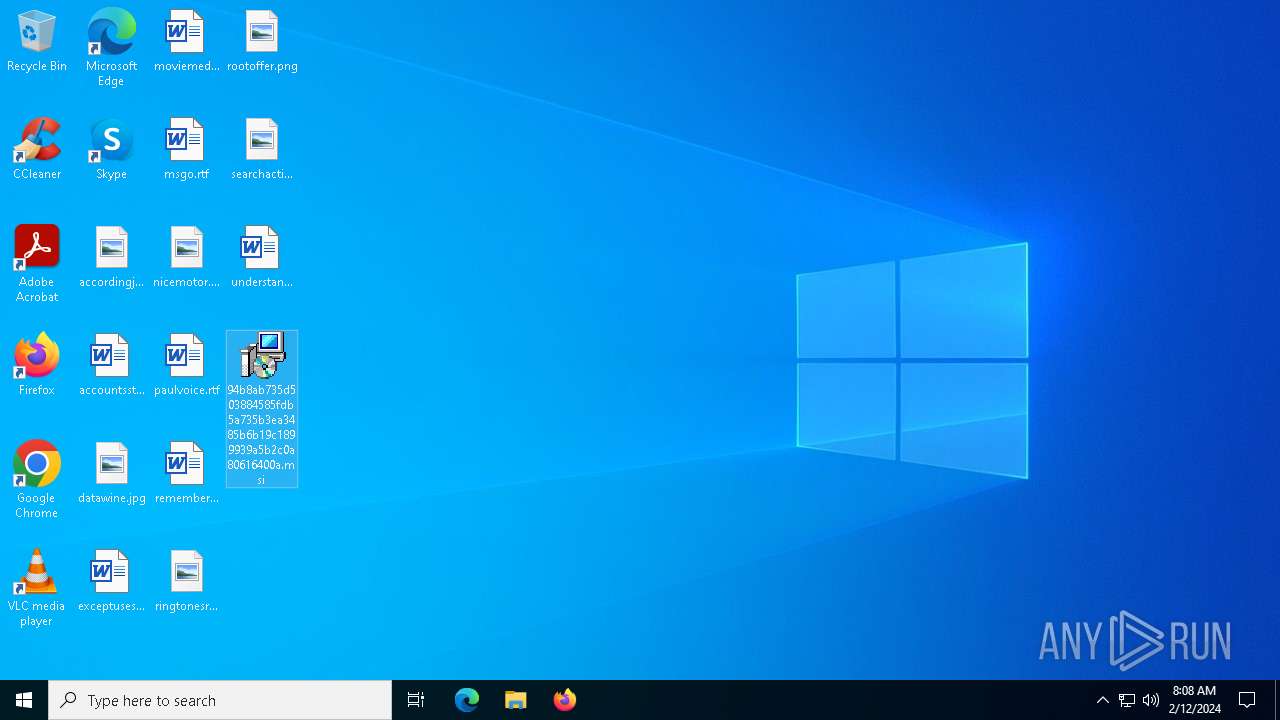
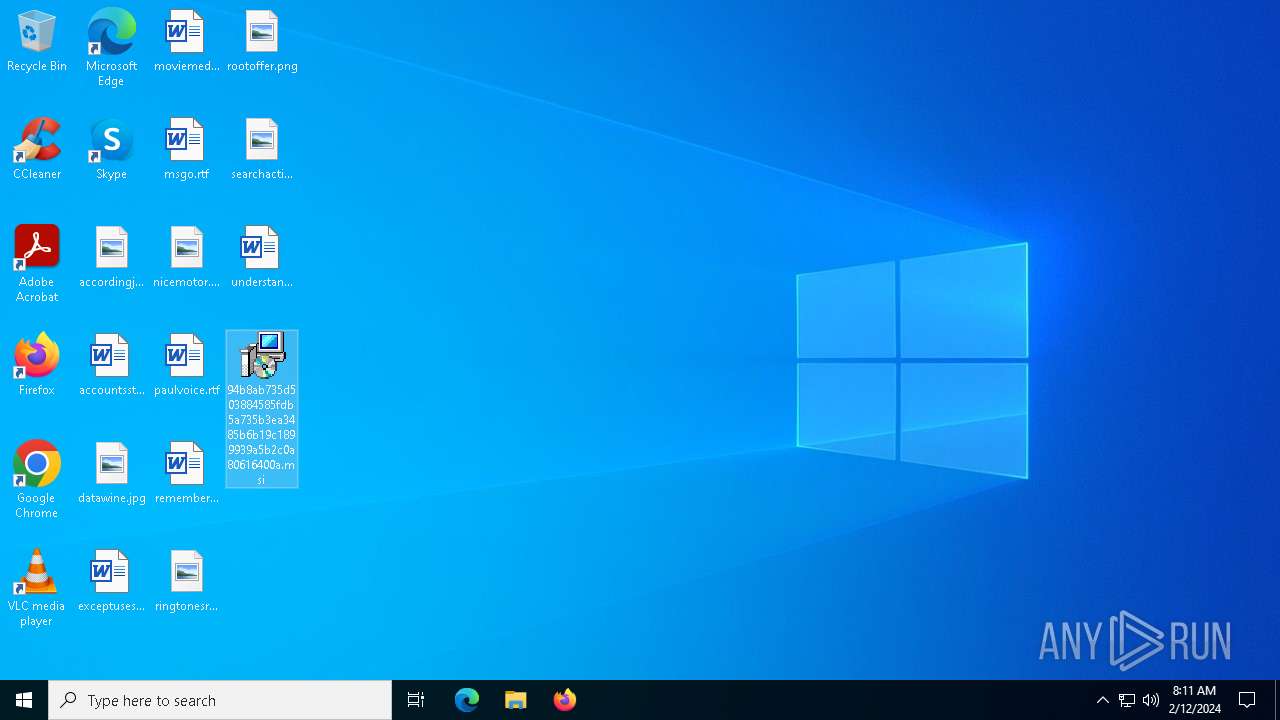
| File name: | 94b8ab735d503884585fdb5a735b3ea3485b6b19c1899939a5b2c0a80616400a |
| Full analysis: | https://app.any.run/tasks/0a91dc2a-c5bc-4358-8783-14880ff85dff |
| Verdict: | Malicious activity |
| Threats: | IcedID is a banking trojan-type malware which allows attackers to utilize it to steal banking credentials of the victims. IcedID aka BokBot mainly targets businesses and steals payment information, it also acts as a loader and can deliver another viruses or download additional modules. |
| Analysis date: | February 12, 2024, 08:08:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Sep 18 14:06:51 2020, Security: 0, Code page: 1252, Revision Number: {0A2ED818-E861-4525-BAB6-6132A30F2F0D}, Number of Words: 10, Subject: Holographsd, Author: Beatss, Name of Creating Application: Holographsd, Template: ;1033, Comments: This installer database contains the logic and data required to install Holographsd., Title: Installation Database, Keywords: Installer, MSI, Database, Number of Pages: 200 |
| MD5: | 9C8696DBB48ADD540A75737327C537D2 |
| SHA1: | 78B4EB7D363E017EB06E03408D7952BBB843F9A9 |
| SHA256: | 94B8AB735D503884585FDB5A735B3EA3485B6B19C1899939A5B2C0A80616400A |
| SSDEEP: | 49152:7Wn9IfHAotxmbqD+/GKIikt698ta5Q1gTeor8trZeeLxzfm0NTMhniez57vbC0:o9I4otWkt698t+Teor0Vm0NTMhrVb |
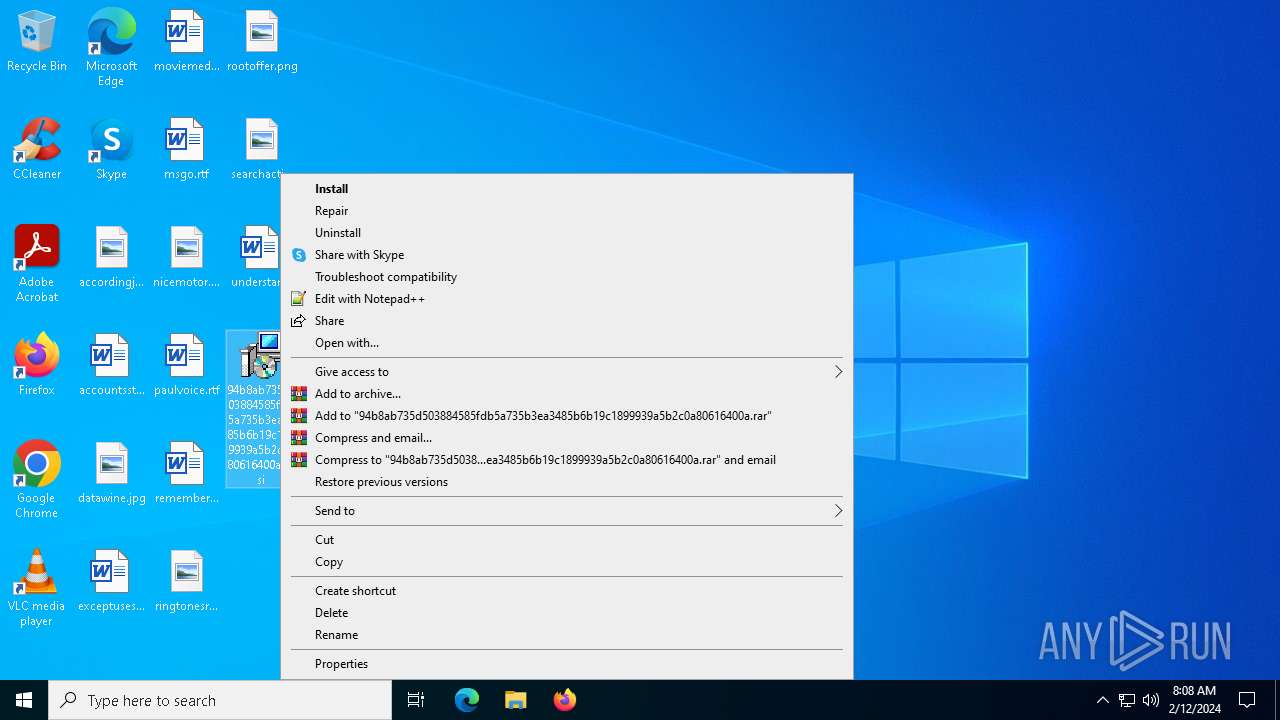
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 4516)
- msiexec.exe (PID: 4064)
ICEDID has been detected (YARA)
- rundll32.exe (PID: 6668)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 6844)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4064)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 6552)
- rundll32.exe (PID: 2460)
- rundll32.exe (PID: 4696)
Executable content was dropped or overwritten
- rundll32.exe (PID: 2460)
Application launched itself
- rundll32.exe (PID: 2460)
Reads security settings of Internet Explorer
- MSI693A.tmp (PID: 3492)
- MSI6047.tmp (PID: 3800)
Reads the date of Windows installation
- MSI693A.tmp (PID: 3492)
- MSI6047.tmp (PID: 3800)
INFO
Executable content was dropped or overwritten
- msiexec.exe (PID: 4516)
- msiexec.exe (PID: 4064)
- msiexec.exe (PID: 6344)
Reads the computer name
- msiexec.exe (PID: 4064)
- msiexec.exe (PID: 2696)
- msiexec.exe (PID: 5220)
- msiexec.exe (PID: 3180)
- msiexec.exe (PID: 4156)
- MSI693A.tmp (PID: 3492)
- MSI6047.tmp (PID: 3800)
Checks supported languages
- msiexec.exe (PID: 4064)
- msiexec.exe (PID: 2696)
- msiexec.exe (PID: 4156)
- MSI693A.tmp (PID: 3492)
- msiexec.exe (PID: 3180)
- MSI6047.tmp (PID: 3800)
- msiexec.exe (PID: 5220)
Reads Environment values
- msiexec.exe (PID: 2696)
- msiexec.exe (PID: 5220)
- msiexec.exe (PID: 4156)
- msiexec.exe (PID: 3180)
Starts application with an unusual extension
- msiexec.exe (PID: 4064)
Process checks computer location settings
- MSI6047.tmp (PID: 3800)
- MSI693A.tmp (PID: 3492)
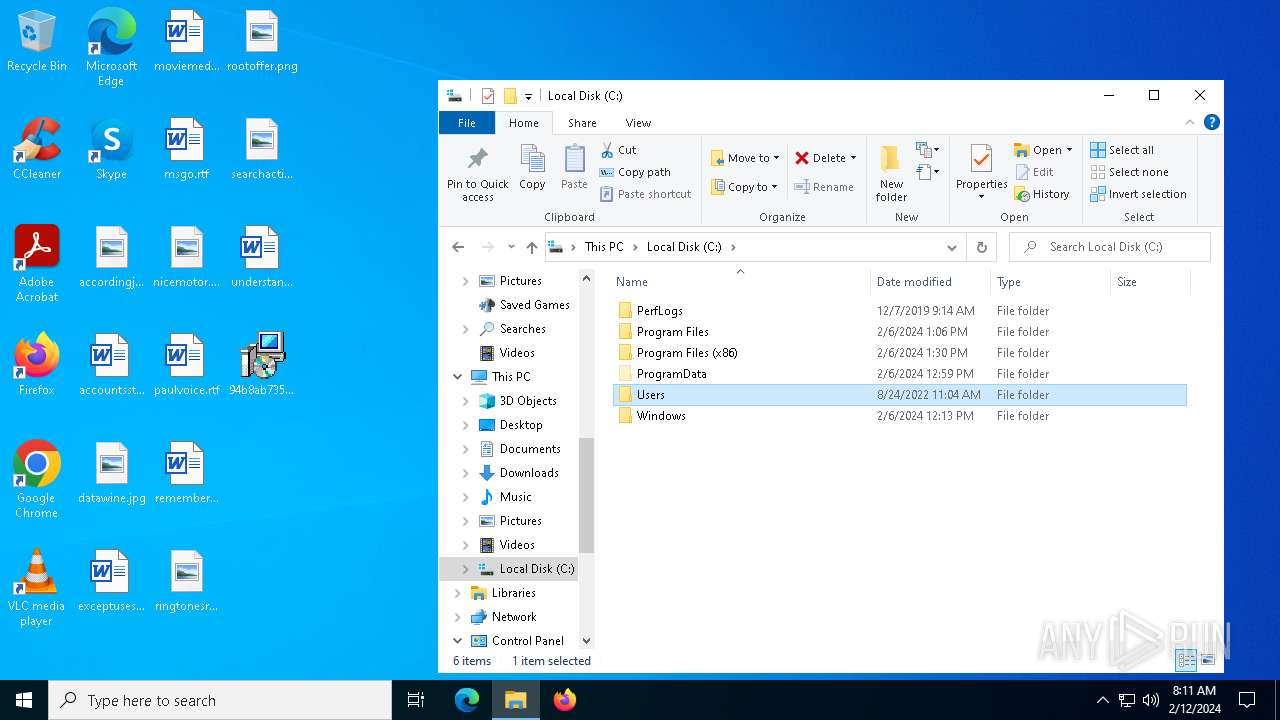
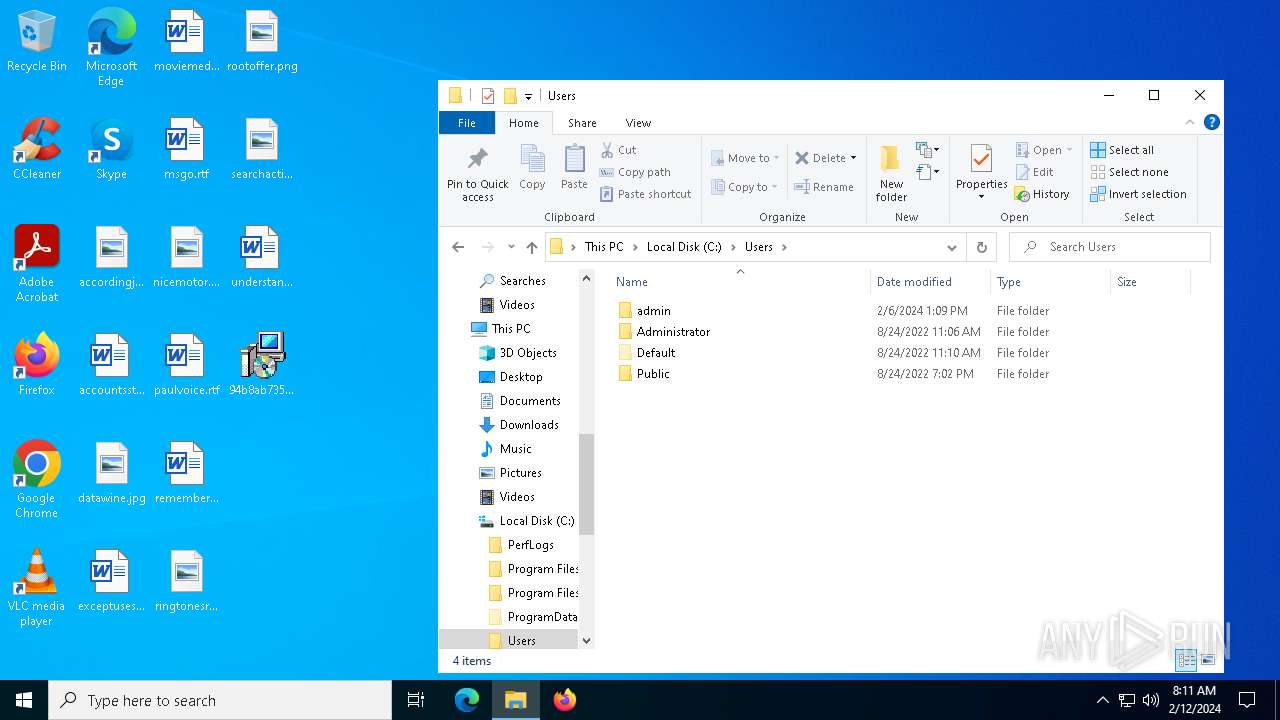
Creates files or folders in the user directory
- rundll32.exe (PID: 2460)
- msiexec.exe (PID: 4064)
Drops the executable file immediately after the start
- rundll32.exe (PID: 2460)
- msiexec.exe (PID: 6344)
Checks proxy server information
- slui.exe (PID: 6216)
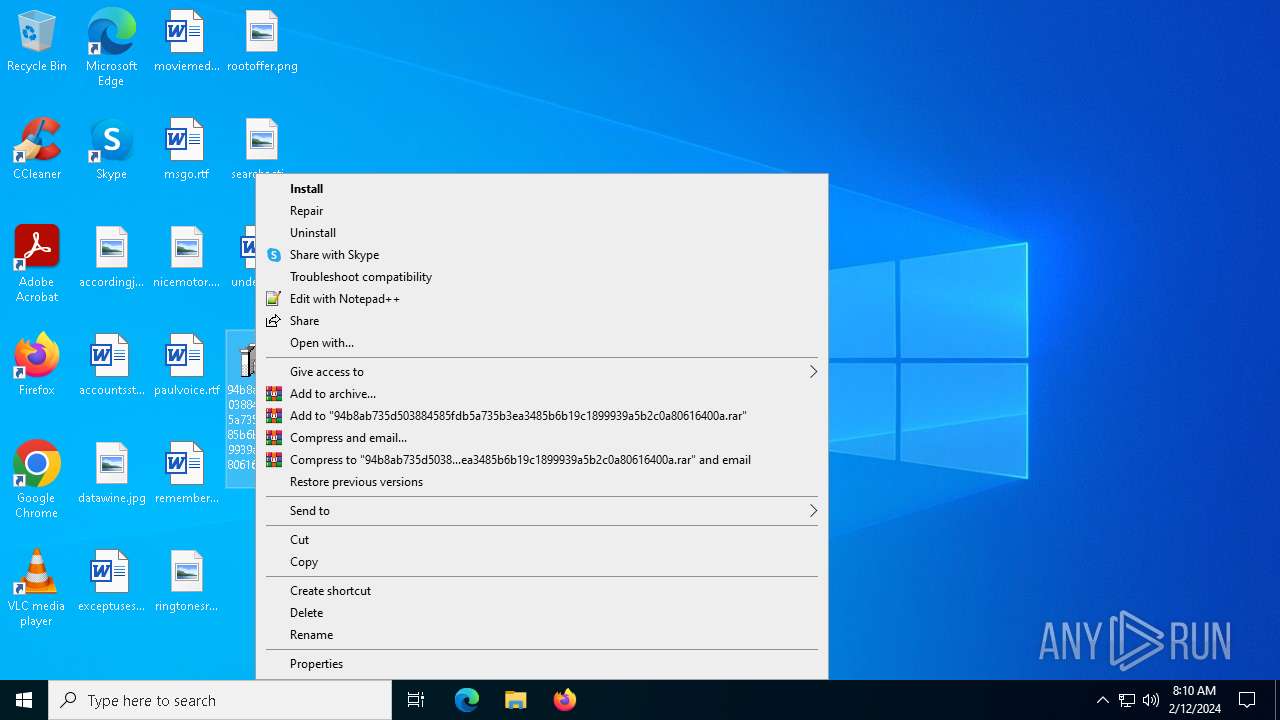
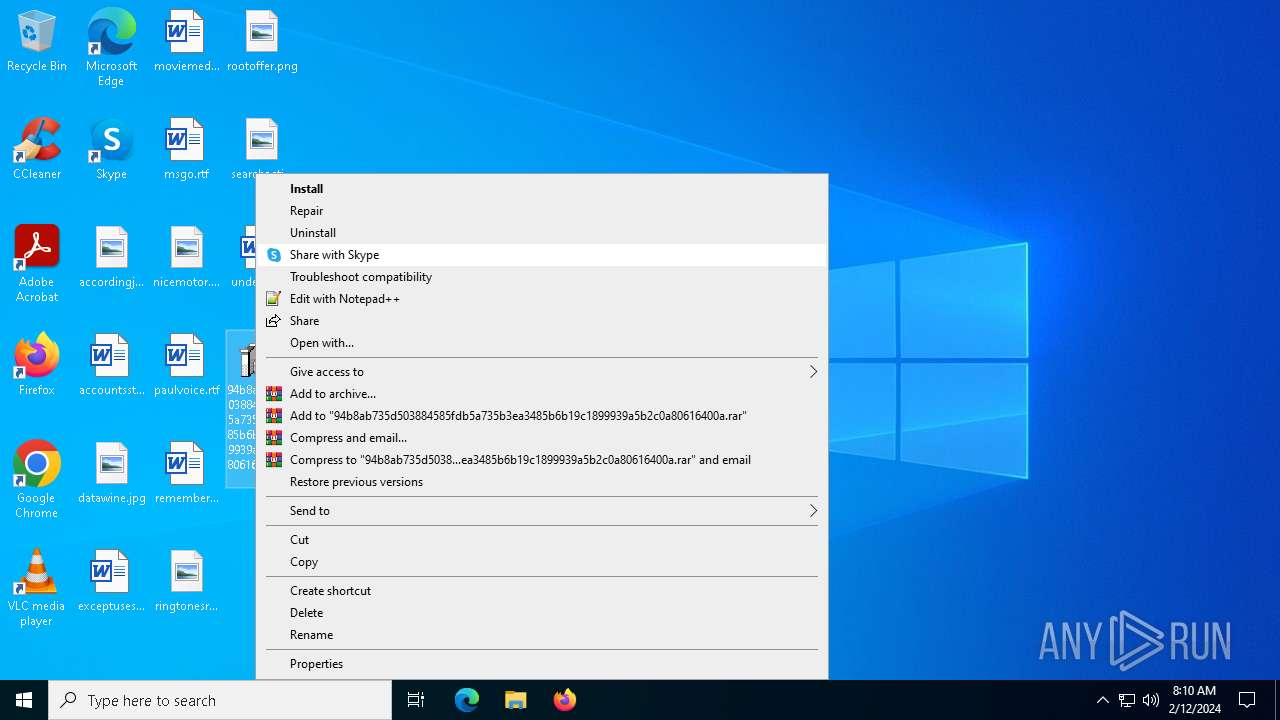
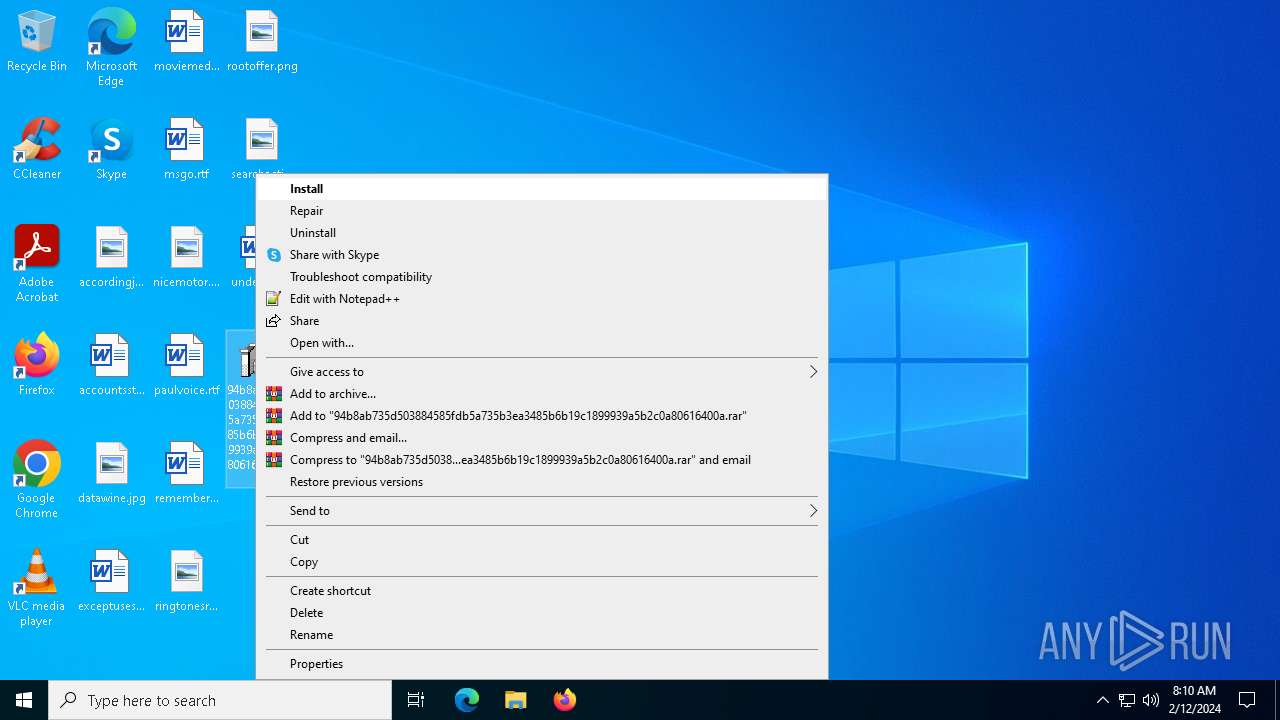
Manual execution by a user
- msiexec.exe (PID: 6344)
Reads the software policy settings
- slui.exe (PID: 6216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| LastPrinted: | 2009:12:11 11:47:44 |
|---|---|
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2020:09:18 14:06:51 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {0A2ED818-E861-4525-BAB6-6132A30F2F0D} |
| Words: | 10 |
| Subject: | Holographsd |
| Author: | Beatss |
| LastModifiedBy: | - |
| Software: | Holographsd |
| Template: | ;1033 |
| Comments: | This installer database contains the logic and data required to install Holographsd. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| Pages: | 200 |
Total processes
153
Monitored processes
21
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1936 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:6 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2460 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Local\Putty/setordinal.dll,bhuf | C:\Windows\System32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2596 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2696 | C:\Windows\syswow64\MsiExec.exe -Embedding E29A000D545CDD4AA157E80CA806C11C C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2912 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:5 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3180 | C:\Windows\syswow64\MsiExec.exe -Embedding C164C27A5C7CA5FBF253753E0F9B64C7 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3276 | C:\WINDOWS\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.546 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3492 | "C:\WINDOWS\Installer\MSI693A.tmp" /DontWait C:/Windows/System32/rundll32.exe C:\Users\admin\AppData\Local\Putty/setordinal.dll,bhuf | C:\Windows\Installer\MSI693A.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: File that launches another file Exit code: 0 Version: 19.1.0.0 Modules
| |||||||||||||||
| 3800 | "C:\WINDOWS\Installer\MSI6047.tmp" /DontWait C:/Windows/System32/rundll32.exe C:\Users\admin\AppData\Local\Putty/setordinal.dll,bhuf | C:\Windows\Installer\MSI6047.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: File that launches another file Exit code: 0 Version: 19.1.0.0 Modules
| |||||||||||||||
| 4064 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 149
Read events
11 710
Write events
401
Delete events
38
Modification events
| (PID) Process: | (4064) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000CBA8C7AE8A5DDA01E00F0000F4020000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4064) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000CBA8C7AE8A5DDA01E00F0000F4020000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4064) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000007129DDAE8A5DDA01E00F0000F4020000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4064) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000007129DDAE8A5DDA01E00F0000F4020000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4064) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000007129DDAE8A5DDA01E00F0000F4020000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4064) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000004B8CDFAE8A5DDA01E00F0000F4020000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4064) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 5 | |||
| (PID) Process: | (4064) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000C686F7AE8A5DDA01E00F0000F4020000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4064) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000C686F7AE8A5DDA01E00F00008C1B0000E8030000010000000000000000000000868A8281A511AE43BF6FCB1D0EE234AD00000000000000000000000000000000 | |||
| (PID) Process: | (6844) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000BA27FCAE8A5DDA01BC1A000040100000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
23
Suspicious files
14
Text files
0
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4064 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4516 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI44C2.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 4516 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI4480.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 4516 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI4421.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 4516 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI44B1.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 4064 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:913A7654926F3D4C605E52A04BA1A6A3 | SHA256:63EE7D7984520D96184AE8DF3B61E405B66AFFAD69F87A8DE9B5B829988478DB | |||
| 4064 | msiexec.exe | C:\Config.Msi\135f0c.rbs | binary | |
MD5:80410ADEB366F55A77DF80646A42C78A | SHA256:0D1EDB40CF3064A59DF84C6BDC09B6E591BFD30B902E75C70D6BC7BBA3378BFF | |||
| 4064 | msiexec.exe | C:\WINDOWS\TEMP\~DF9BF955831826783C.TMP | binary | |
MD5:C0F576D5EBED43F36DBA45EAA84AABEE | SHA256:5134D8B3FB34B58A8DC2D96AAF526177AADBD967CE1FC308B2A141D8DDB24A16 | |||
| 4064 | msiexec.exe | C:\WINDOWS\Installer\MSI6007.tmp | binary | |
MD5:524021806A9DFE0206787FAAA4AF7C79 | SHA256:B539DD1F8838FDDD7D5C84070D78B43F32A67A056AC9D122E0C944EF18BB1FCF | |||
| 4064 | msiexec.exe | C:\WINDOWS\Installer\inprogressinstallinfo.ipi | binary | |
MD5:C0F576D5EBED43F36DBA45EAA84AABEE | SHA256:5134D8B3FB34B58A8DC2D96AAF526177AADBD967CE1FC308B2A141D8DDB24A16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
28
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2464 | svchost.exe | GET | 200 | 184.51.233.5:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
1056 | svchost.exe | POST | 302 | 2.20.58.57:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | unknown |
3848 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
5928 | svchost.exe | 40.126.31.71:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6896 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
5928 | svchost.exe | 20.190.159.4:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6828 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
7040 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2052 | backgroundTaskHost.exe | 23.64.12.33:443 | www.bing.com | Akamai International B.V. | PL | unknown |
1020 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
go.microsoft.com |
| whitelisted |
dmd.metaservices.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |