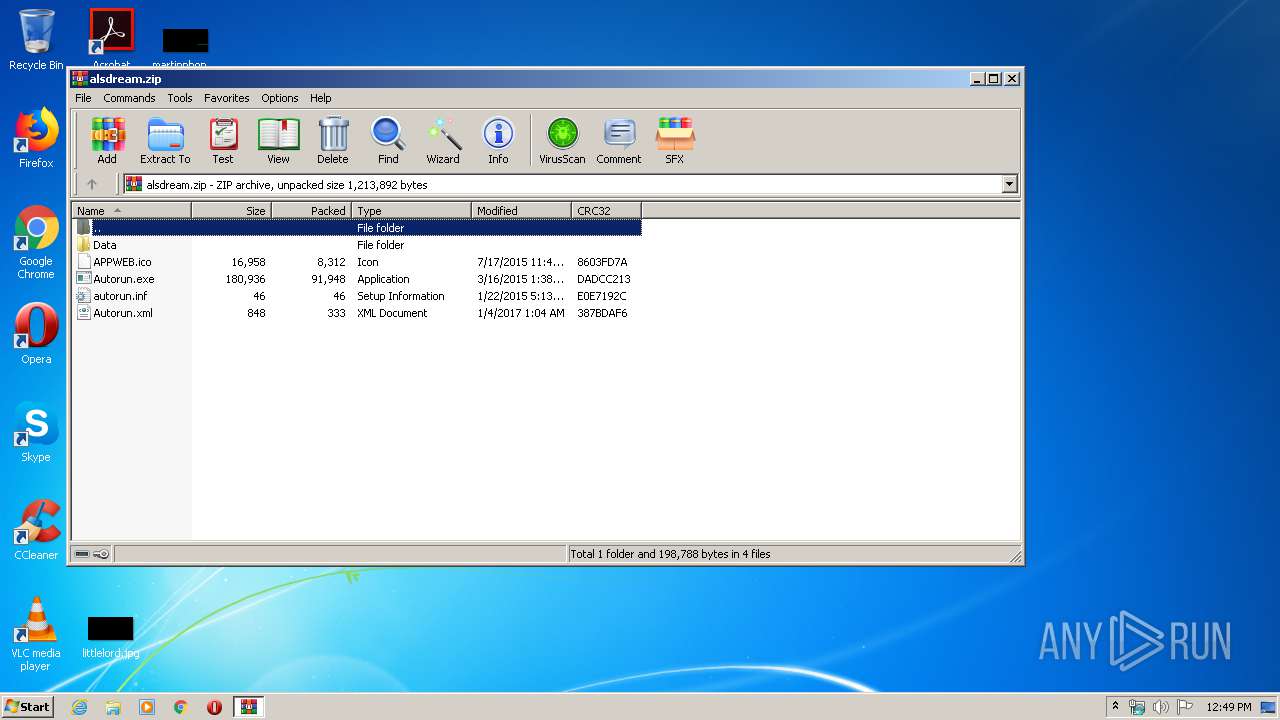
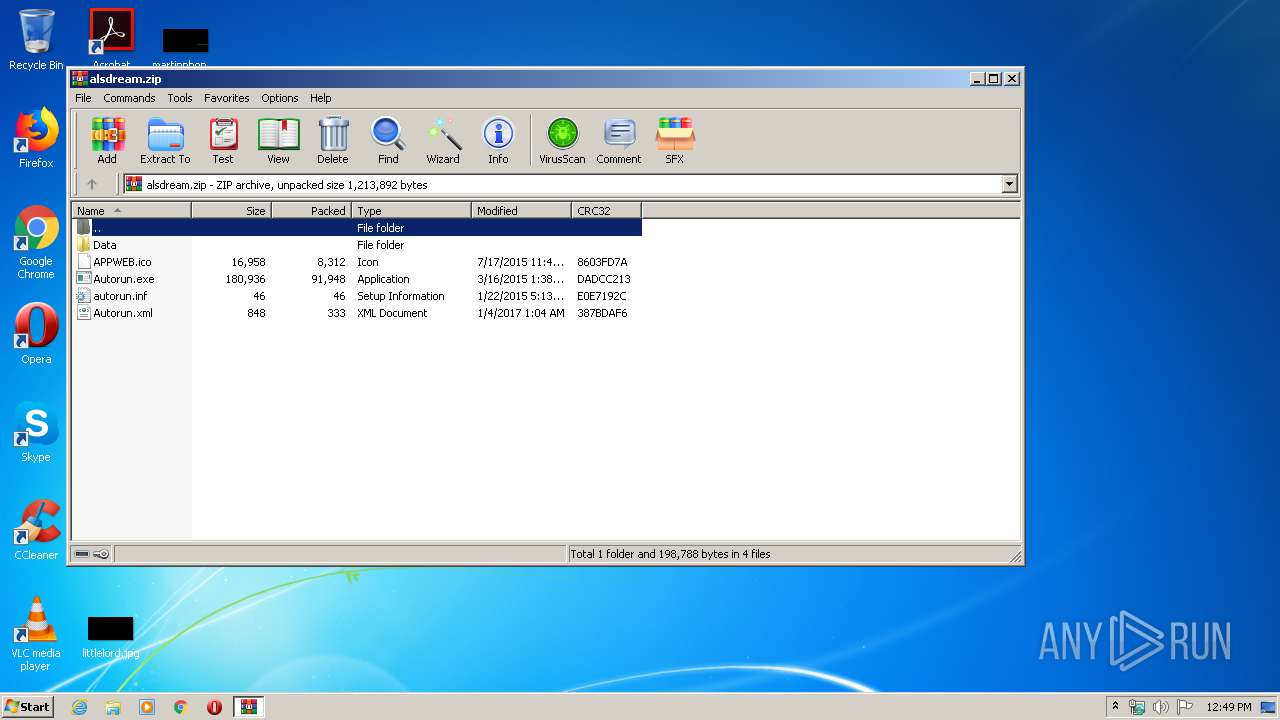
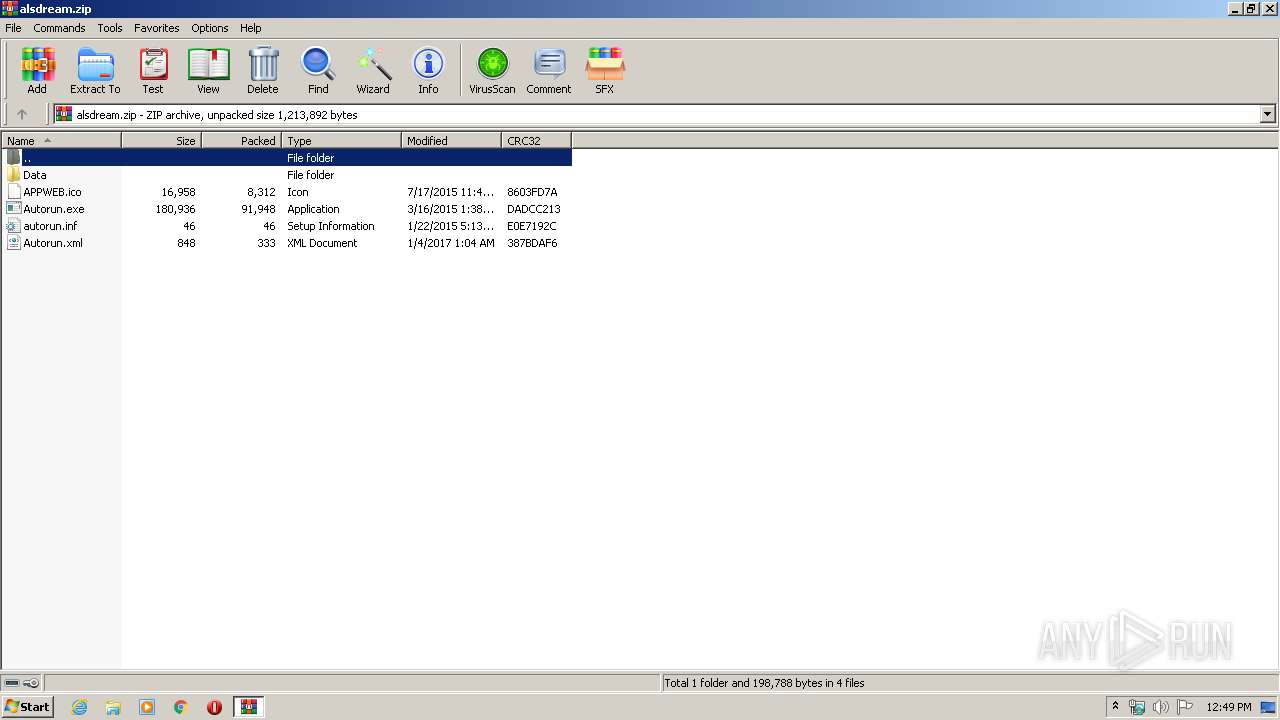
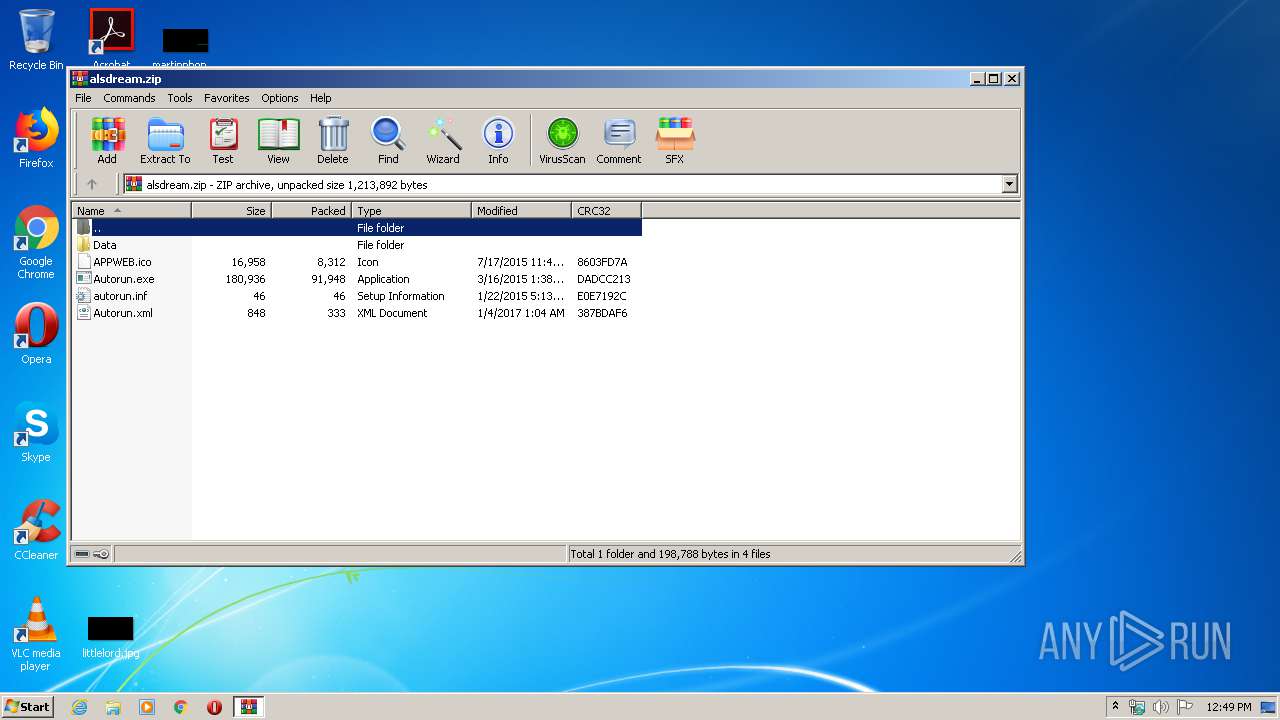
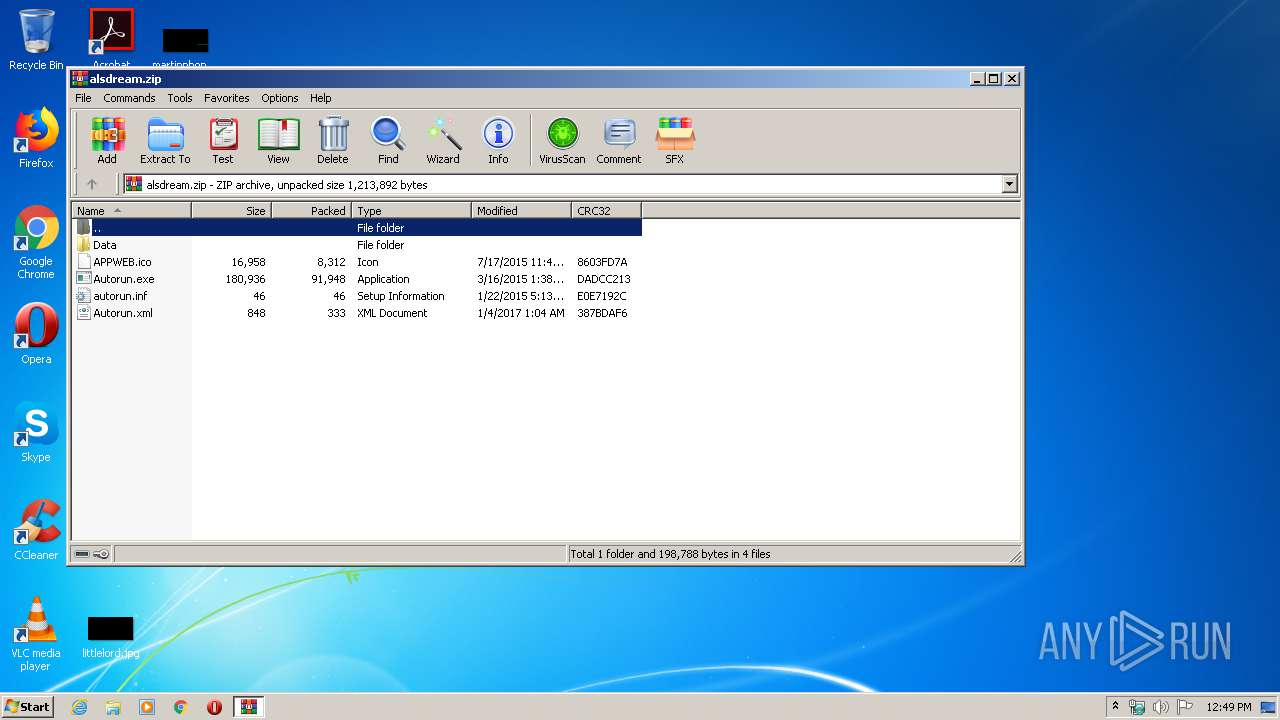
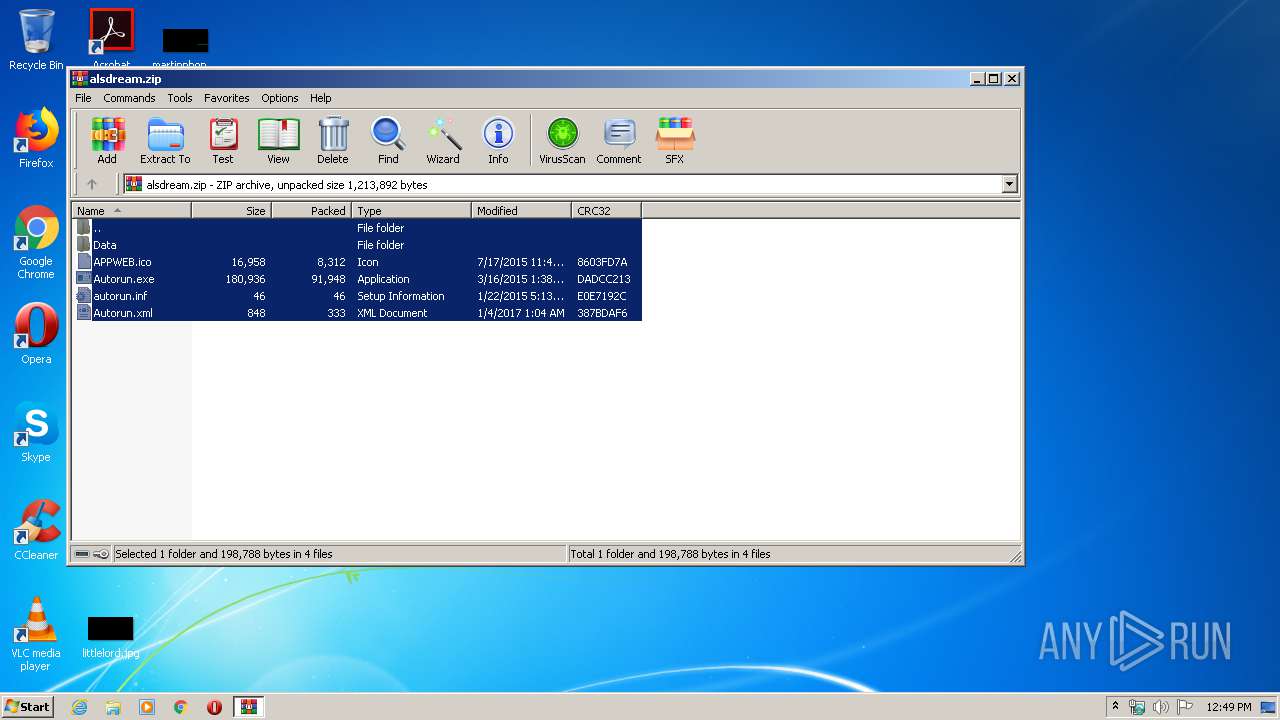
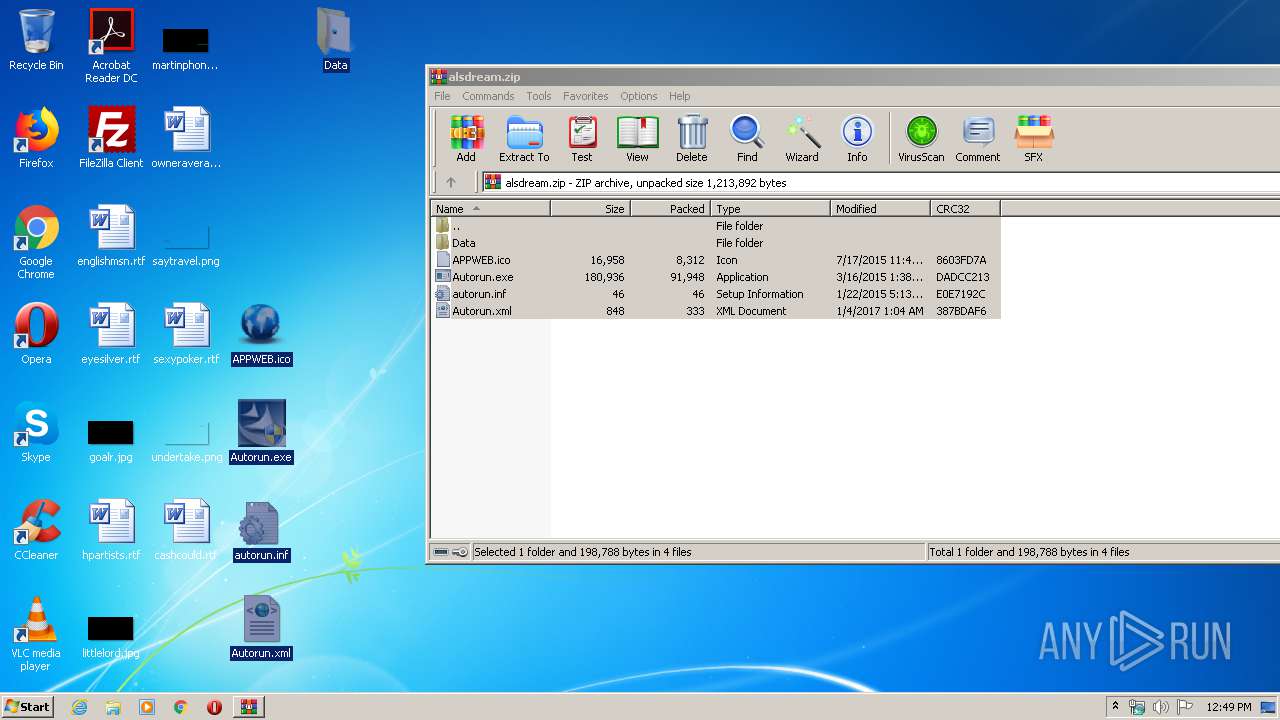
| File name: | alsdream.zip |
| Full analysis: | https://app.any.run/tasks/08e1e87b-dee2-4e64-929c-a2256880b097 |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2020, 11:48:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 158A6CEE849F0DBC91223839D4E9ACE2 |
| SHA1: | 20934D1E89FECE8CA339E0BC7C6235A5ABD13951 |
| SHA256: | 94AB457FC650DDF6C8220CF086FCEAE67AA5CB04E48508CEFFF247B4A92BF60E |
| SSDEEP: | 24576:2MrlI2qrSmzagaPiwnfEx0au9HxjKJdL9T67dv:eagMfnfIFmxj85mdv |
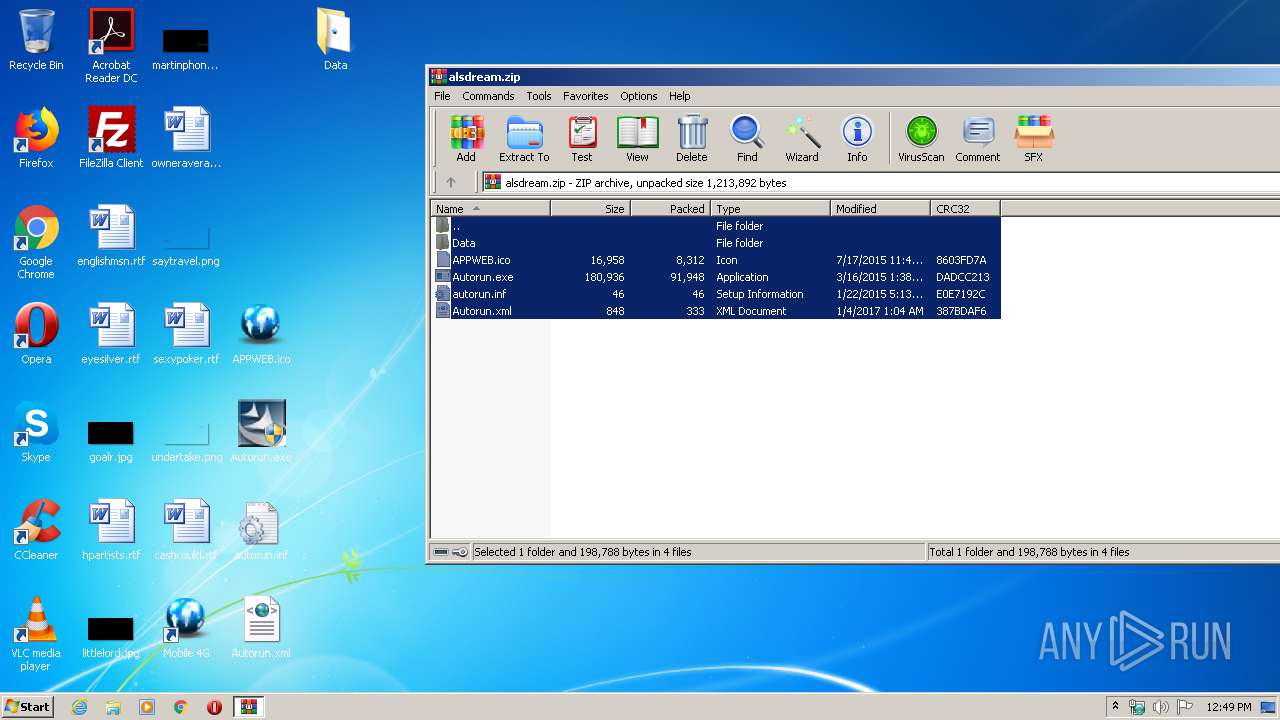
MALICIOUS
Application was dropped or rewritten from another process
- Autorun.exe (PID: 2864)
- Autorun.exe (PID: 2676)
- Setup.exe (PID: 3508)
- CertMgr.exe (PID: 884)
- setup.exe (PID: 3272)
- DrvInst_x86.exe (PID: 1172)
- EjectDisk_x86.exe (PID: 792)
- StartWebUI.exe (PID: 884)
- CertMgr.exe (PID: 3808)
Actions looks like stealing of personal data
- Autorun.exe (PID: 2676)
- Setup.tmp (PID: 2480)
Changes settings of System certificates
- CertMgr.exe (PID: 884)
- CertMgr.exe (PID: 3808)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3848)
- Setup.exe (PID: 3508)
- Setup.tmp (PID: 2480)
Creates files in the Windows directory
- Autorun.exe (PID: 2676)
- DrvInst_x86.exe (PID: 1172)
- setup.exe (PID: 3272)
- EjectDisk_x86.exe (PID: 792)
- StartWebUI.exe (PID: 884)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3848)
- Setup.tmp (PID: 2480)
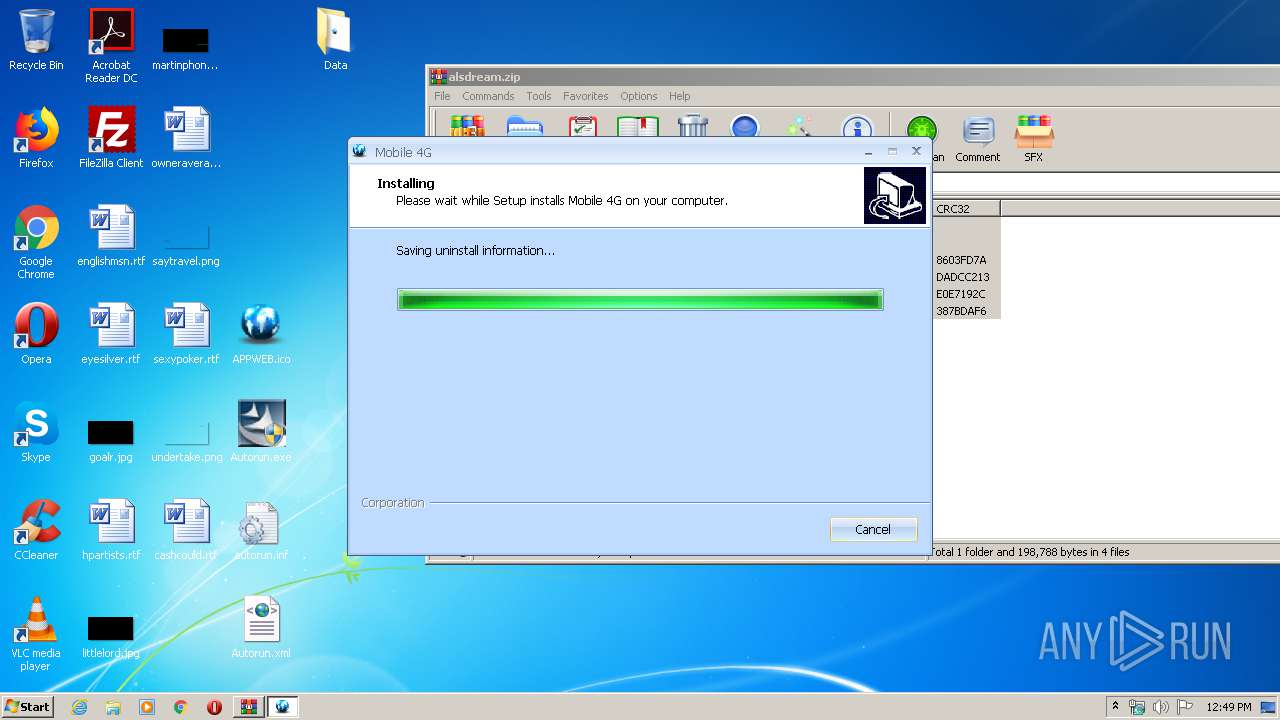
Manual execution by user
- Autorun.exe (PID: 2864)
- Autorun.exe (PID: 2676)
Creates files in the program directory
- Setup.tmp (PID: 2480)
Application was dropped or rewritten from another process
- Setup.tmp (PID: 2480)
Loads dropped or rewritten executable
- Setup.tmp (PID: 2480)
Creates a software uninstall entry
- Setup.tmp (PID: 2480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2015:01:23 02:13:26 |
| ZipCRC: | 0xe0e7192c |
| ZipCompressedSize: | 46 |
| ZipUncompressedSize: | 46 |
| ZipFileName: | autorun.inf |
Total processes
54
Monitored processes
11
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 792 | "C:\Program Files\Mobile 4G\EjectDisk_x86.exe" "Pid_0557&Rev_0101" "NOREINSTALL" | C:\Program Files\Mobile 4G\EjectDisk_x86.exe | Setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: EjectDisk program Exit code: 0 Version: 1, 0, 0, 2 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Mobile 4G\StartWebUI.exe" "USB\Vid_19d2&Pid_0558&Rev_0101&MI_00" "http://m.home/" | C:\Program Files\Mobile 4G\StartWebUI.exe | Setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: StartWeb Application Exit code: 0 Version: 1, 0, 0, 3 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Mobile 4G\OTHERS\x86\CertMgr.exe" /add zte.cer /s /r localMachine trustedpublisher | C:\Program Files\Mobile 4G\OTHERS\x86\CertMgr.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Mobile 4G\OTHERS\DrvInst_x86.exe" /i | C:\Program Files\Mobile 4G\OTHERS\DrvInst_x86.exe | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: DrvInst Application Exit code: 0 Version: 1, 1, 0, 7 Modules
| |||||||||||||||
| 2480 | "C:\Users\admin\AppData\Local\Temp\is-N4A9O.tmp\Setup.tmp" /SL5="$F0150,721234,69120,C:\Users\admin\Desktop\Data\Setup.exe" /SILENT | C:\Users\admin\AppData\Local\Temp\is-N4A9O.tmp\Setup.tmp | Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 安装/卸载 Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2676 | "C:\Users\admin\Desktop\Autorun.exe" | C:\Users\admin\Desktop\Autorun.exe | explorer.exe | ||||||||||||
User: admin Company: Corporation Integrity Level: HIGH Description: Autorun Application Exit code: 0 Version: 1, 1, 0, 3 Modules
| |||||||||||||||
| 2864 | "C:\Users\admin\Desktop\Autorun.exe" | C:\Users\admin\Desktop\Autorun.exe | — | explorer.exe | |||||||||||
User: admin Company: Corporation Integrity Level: MEDIUM Description: Autorun Application Exit code: 3221226540 Version: 1, 1, 0, 3 Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Mobile 4G\setup.exe" /i | C:\Program Files\Mobile 4G\setup.exe | — | Setup.tmp | |||||||||||
User: admin Company: Integrity Level: HIGH Description: setup Exit code: 0 Version: 1.00.00.0002 built by: WinDDK Modules
| |||||||||||||||
| 3508 | "C:\Users\admin\Desktop\Data\Setup.exe" /SILENT | C:\Users\admin\Desktop\Data\Setup.exe | Autorun.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 1, 0, 0, 2 Modules
| |||||||||||||||
| 3808 | "C:\Program Files\Mobile 4G\OTHERS\x86\CertMgr.exe" /add zte.cer /s /r localMachine root | C:\Program Files\Mobile 4G\OTHERS\x86\CertMgr.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
654
Read events
608
Write events
39
Delete events
7
Modification events
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\alsdream.zip | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\setupapi.dll,-2000 |
Value: Setup Information | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msxml3r.dll,-1 |
Value: XML Document | |||
Executable files
20
Suspicious files
2
Text files
201
Unknown types
7
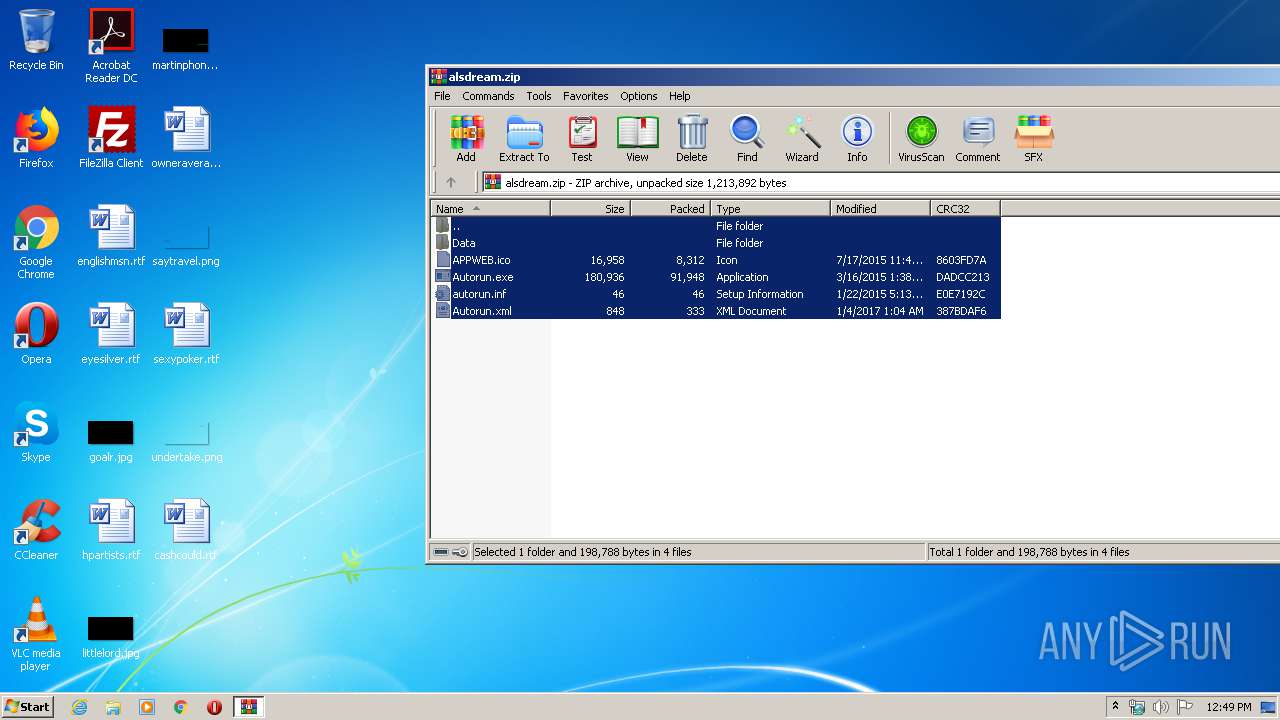
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
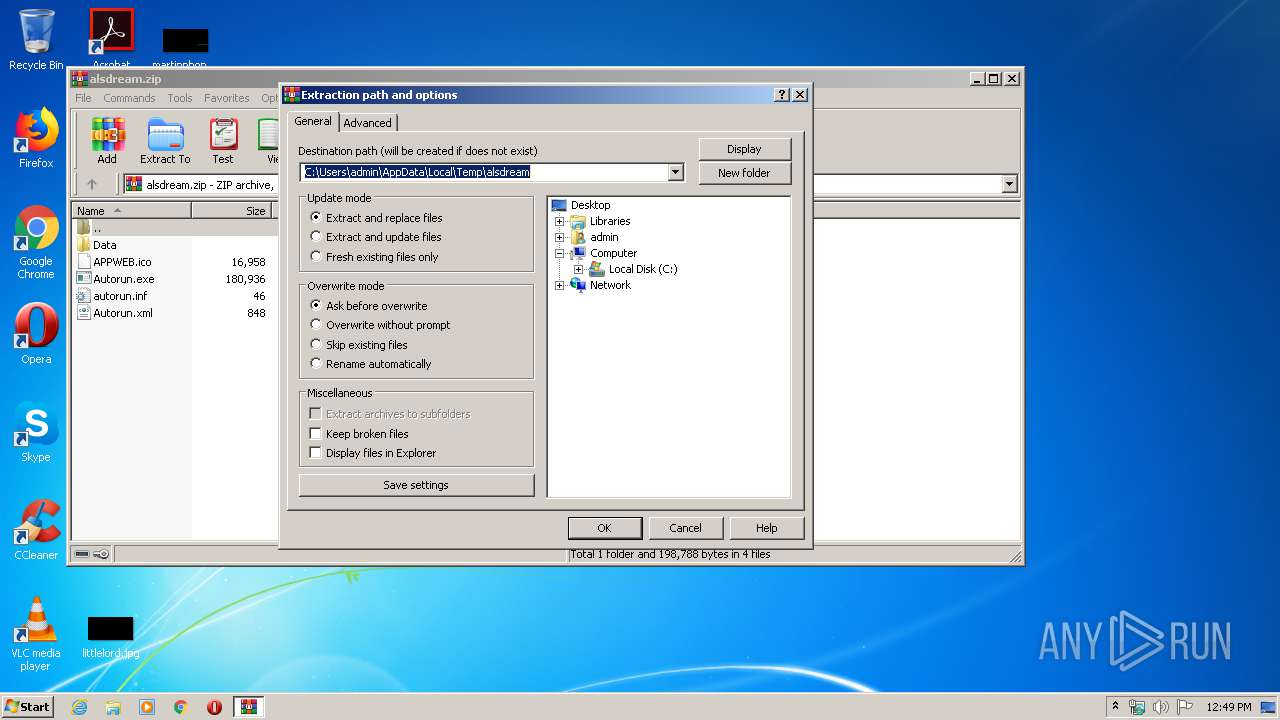
| 3848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3848.30977\autorun.inf | — | |
MD5:— | SHA256:— | |||
| 3848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3848.30977\Autorun.xml | — | |
MD5:— | SHA256:— | |||
| 3848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3848.30977\Data\Setup.exe | — | |
MD5:— | SHA256:— | |||
| 3848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3848.30977\APPWEB.ico | — | |
MD5:— | SHA256:— | |||
| 3848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3848.30977\Autorun.exe | — | |
MD5:— | SHA256:— | |||
| 2480 | Setup.tmp | C:\Program Files\Mobile 4G\is-2NC9T.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | Setup.tmp | C:\Program Files\Mobile 4G\is-SB101.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | Setup.tmp | C:\Program Files\Mobile 4G\is-I4AGS.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | Setup.tmp | C:\Program Files\Mobile 4G\is-K0CGC.tmp | — | |
MD5:— | SHA256:— | |||
| 2480 | Setup.tmp | C:\Program Files\Mobile 4G\is-NJQ61.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
Autorun.exe | [2020-5-14 12:49:44.861] <WinMain>: #68 @ .\Autorun.cpp
Complete reading XML configuration file
|
Autorun.exe | [2020-5-14 12:49:44.861] <LogActions>: #553 @ .\Actions.cpp
Action 0:
ActionType:Setup
ActionExecutive:Process
ShowUI:FALSE
Tips:Install Driver
Param:/SILENT
CurrentVersion:1.0.0.2
|
Autorun.exe | [2020-5-14 12:49:44.861] <WinMain>: #38 @ .\Autorun.cpp
OS:WIN_00000601, 32bits
|
Autorun.exe | [2020-5-14 12:49:44.861] <WinMain>: #66 @ .\Autorun.cpp
Begin to read XML configuration file
|
Autorun.exe | [2020-5-14 12:49:44.861] <DoAction>: #501 @ .\Actions.cpp
Start action 0, "C:\Users\admin\Desktop\Data\Setup.exe" /SILENT, Wait: 1
|
Autorun.exe | [2020-5-14 12:49:44.861] <WinMain>: #63 @ .\Autorun.cpp
Run in Silent mode
|
DrvInst_x86.exe | [2020-5-14 12:49:46.986] <GetInstallInfoFromXML>: #365 @ Install.cpp
OS:WIN_00000600_32bit, Dir: Drivers\
|
DrvInst_x86.exe | [2020-5-14 12:49:46.986] <GetInstallInfoFromXML>: #365 @ Install.cpp
OS:WIN_00000502_64bit, Dir: Drivers\
|
DrvInst_x86.exe | [2020-5-14 12:49:46.986] <GetInstallInfoFromXML>: #365 @ Install.cpp
OS:WIN_00000602_64bit, Dir: Drivers\
|
DrvInst_x86.exe | [2020-5-14 12:49:46.986] <GetInstallInfoFromXML>: #365 @ Install.cpp
OS:WIN_00000602_32bit, Dir: Drivers\
|