| File name: | RemoveWAT 2.2.6.exe |
| Full analysis: | https://app.any.run/tasks/80362ed2-a4a6-4474-92df-18f49add6c35 |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 06:30:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | BFACF78644CA41FD6D4B23976E7574A1 |
| SHA1: | 6BDC28B673D25481A7A5828ACA6EFD87D2C90B14 |
| SHA256: | 94A1A26F61B015C2CED2FD50BDBA4070B6C9AEC7D2938FBF7EB9E99960D3B7A9 |
| SSDEEP: | 98304:G33yKMaL/eXV1i/kDxkmcL/eXV1i/kaRWYL/eXV1i/kmeM1qj4iwiANvSo2/CAyq:QyKnZrrLGA3PhsKPkG0tWu |
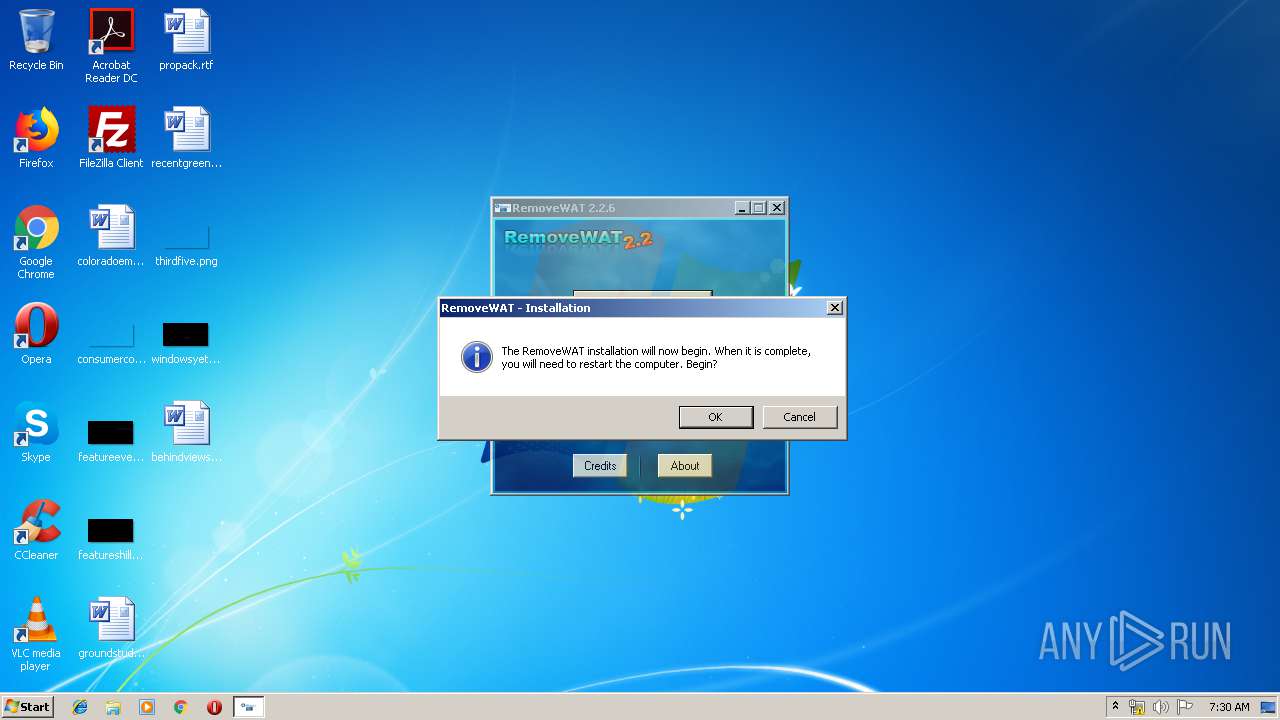
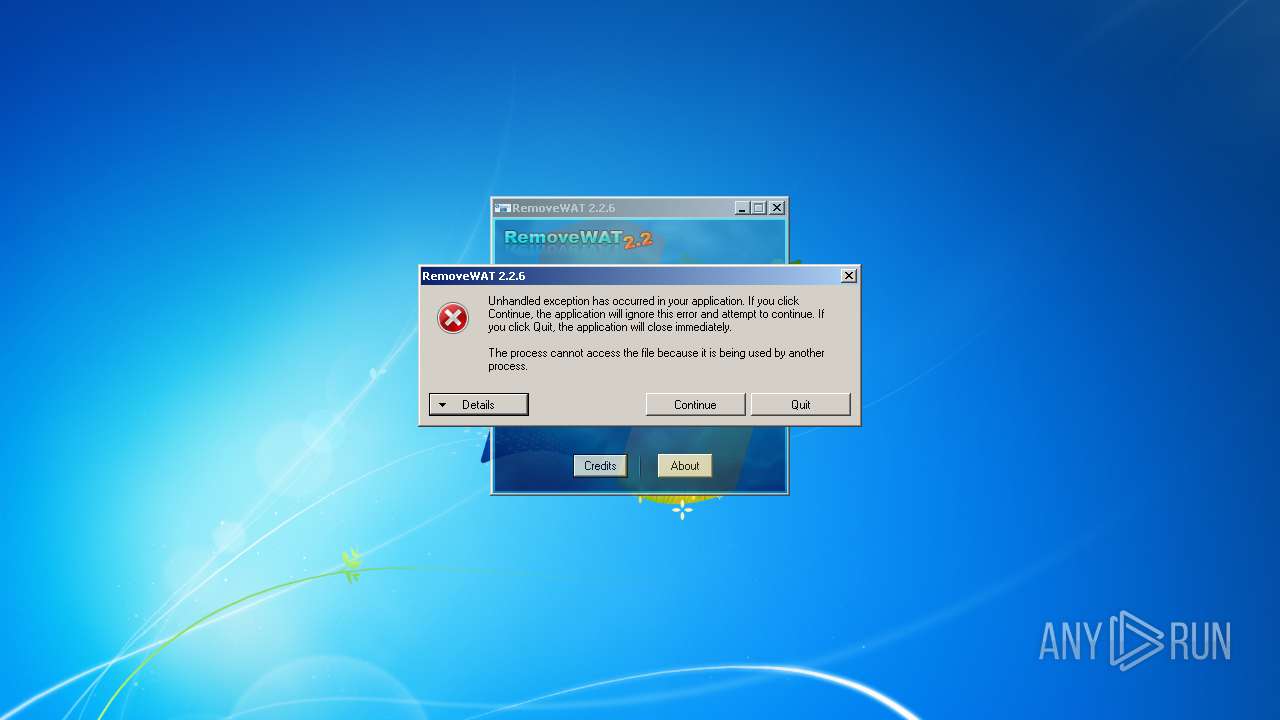
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2764)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1476)
- schtasks.exe (PID: 3148)
SUSPICIOUS
Creates files in the Windows directory
- wusa.exe (PID: 3408)
- RemoveWAT 2.2.6.exe (PID: 3336)
Uses TASKKILL.EXE to kill process
- RemoveWAT 2.2.6.exe (PID: 3336)
- cmd.exe (PID: 2364)
Removes files from Windows directory
- RemoveWAT 2.2.6.exe (PID: 3336)
Executed via COM
- DrvInst.exe (PID: 3644)
Starts CMD.EXE for commands execution
- RemoveWAT 2.2.6.exe (PID: 3336)
Executed as Windows Service
- vssvc.exe (PID: 3420)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 3792)
- cmd.exe (PID: 1924)
- cmd.exe (PID: 2092)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 3420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ax | | | DirectShow filter (42.2) |
|---|---|---|
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (15.3) |
| .exe | | | InstallShield setup (9) |
| .exe | | | Win64 Executable (generic) (5.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:09:20 13:05:56+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 6560256 |
| InitializedDataSize: | 103936 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x64390e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.6.0 |
| ProductVersionNumber: | 2.2.6.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Removes Windows Activation Technologies |
| CompanyName: | Hazar & Co. |
| FileDescription: | RemoveWAT |
| FileVersion: | 2.2.6.0 |
| InternalName: | RemoveWAT.exe |
| LegalCopyright: | Copyright Hazar & Co. © 2010 |
| OriginalFileName: | RemoveWAT.exe |
| ProductName: | RemoveWAT |
| ProductVersion: | 2.2.6.0 |
| AssemblyVersion: | 2.2.6.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Sep-2010 11:05:56 |
| Comments: | Removes Windows Activation Technologies |
| CompanyName: | Hazar & Co. |
| FileDescription: | RemoveWAT |
| FileVersion: | 2.2.6.0 |
| InternalName: | RemoveWAT.exe |
| LegalCopyright: | Copyright Hazar & Co. © 2010 |
| OriginalFilename: | RemoveWAT.exe |
| ProductName: | RemoveWAT |
| ProductVersion: | 2.2.6.0 |
| Assembly Version: | 2.2.6.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 20-Sep-2010 11:05:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00641914 | 0x00641A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.18493 |
.rsrc | 0x00644000 | 0x00019390 | 0x00019400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.01226 |
.reloc | 0x0065E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94169 | 2271 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.20012 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.06029 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.13335 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.82912 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 2.67305 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.86004 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
69
Monitored processes
24
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1476 | schtasks /change /disable /tn "\Microsoft\Windows\Windows Activation Technologies\ValidationTask" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1924 | "C:\Windows\System32\cmd.exe" /c takeown /f "C:\Windows\System32\Wat\WatUX.exe" & icacls "C:\Windows\System32\Wat\WatUX.exe" /reset & icacls "C:\Windows\System32\Wat\WatUX.exe" /deny *S-1-1-0:(X) | C:\Windows\System32\cmd.exe | — | RemoveWAT 2.2.6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2092 | "C:\Windows\System32\cmd.exe" /c takeown /f "C:\Windows\System32\user32.dll" & icacls "C:\Windows\System32\user32.dll" /reset & icacls "C:\Windows\System32\user32.dll" /grant *S-1-1-0:F | C:\Windows\System32\cmd.exe | — | RemoveWAT 2.2.6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2364 | "C:\Windows\System32\cmd.exe" /c taskkill /f /im WatAdminSvc.exe & taskkill /f /im WatUX.exe | C:\Windows\System32\cmd.exe | — | RemoveWAT 2.2.6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2380 | icacls "C:\Windows\System32\Wat\WatAdminSvc.exe" /reset | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2684 | takeown /f "C:\Windows\System32\Wat\WatUX.exe" | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2736 | taskkill /f /im WatAdminSvc.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2764 | "C:\Windows\System32\cmd.exe" /c schtasks /change /disable /tn "\Microsoft\Windows\Windows Activation Technologies\ValidationTask" & schtasks /change /disable /tn "\Microsoft\Windows\Windows Activation Technologies\ValidationTaskDeadline" | C:\Windows\System32\cmd.exe | — | RemoveWAT 2.2.6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2772 | takeown /f "C:\Windows\System32\user32.dll" | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3144 | icacls "C:\Windows\System32\Wat\WatUX.exe" /reset | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
316
Read events
181
Write events
134
Delete events
1
Modification events
| (PID) Process: | (3336) RemoveWAT 2.2.6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3336) RemoveWAT 2.2.6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3408) wusa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WUSA |
| Operation: | write | Name: | WUSACommandLine |
Value: /quiet | |||
| (PID) Process: | (3420) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000A213F133B237D5015C0D0000FC0D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3420) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000A213F133B237D5015C0D0000040C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3420) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000A213F133B237D5015C0D0000340F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3420) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000A213F133B237D5015C0D0000840F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3420) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000B03AF833B237D5015C0D0000340F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3420) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000000A9DFA33B237D5015C0D0000840F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3420) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 400000000000000064FFFC33B237D5015C0D0000040C0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
4
Text files
39
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3408 | wusa.exe | C:\0be01495414c970ad2e85509\$dpx$.tmp\7ce204eb96ff1e4aa9b62ff5c1eb515b.tmp | — | |
MD5:— | SHA256:— | |||
| 3408 | wusa.exe | C:\0be01495414c970ad2e85509\$dpx$.tmp\ff701cfd0331ca44a73f907915b2c604.tmp | — | |
MD5:— | SHA256:— | |||
| 3408 | wusa.exe | C:\0be01495414c970ad2e85509\$dpx$.tmp\6a371d85b6bc1c4f991a1ee9a6d008fb.tmp | — | |
MD5:— | SHA256:— | |||
| 3408 | wusa.exe | C:\0be01495414c970ad2e85509\$dpx$.tmp\3ed0c2dcf75f8047a9bb9ad147969b2f.tmp | — | |
MD5:— | SHA256:— | |||
| 3420 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3408 | wusa.exe | C:\Windows\Logs\DPX\setuperr.log | — | |
MD5:— | SHA256:— | |||
| 3336 | RemoveWAT 2.2.6.exe | C:\Windows\wat.MSU | msu | |
MD5:2B2CB791AA5C80018454DE799D178541 | SHA256:AD8E8C2DE3784438D584E612B8ED787AC8F905429AAB7E23958D64DAAA89109D | |||
| 3644 | DrvInst.exe | C:\Windows\INF\setupapi.ev1 | binary | |
MD5:31C9C0B73E2B8D1E1851494E88DD648B | SHA256:FC49BD713DDD4F0764262520DECF779FEBE474C4DFC60EDB5F354B762070AC7F | |||
| 3408 | wusa.exe | C:\0be01495414c970ad2e85509\Windows6.1-KB971033-x86-pkgProperties.txt | text | |
MD5:2A935916F7EA88AA5EE735B1775C228E | SHA256:D71B35046C13D0638ADBC20F5D9835E5E363AE685E23CECC3A47E66C79510337 | |||
| 3408 | wusa.exe | C:\Windows\WindowsUpdate.log | text | |
MD5:C62AA831F60362A3D5D944F5C2272C84 | SHA256:6BFCF56D3D97E8AB9FE142B70C176F6AD19AEF499868A770AEBE8C1DBFF42823 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report