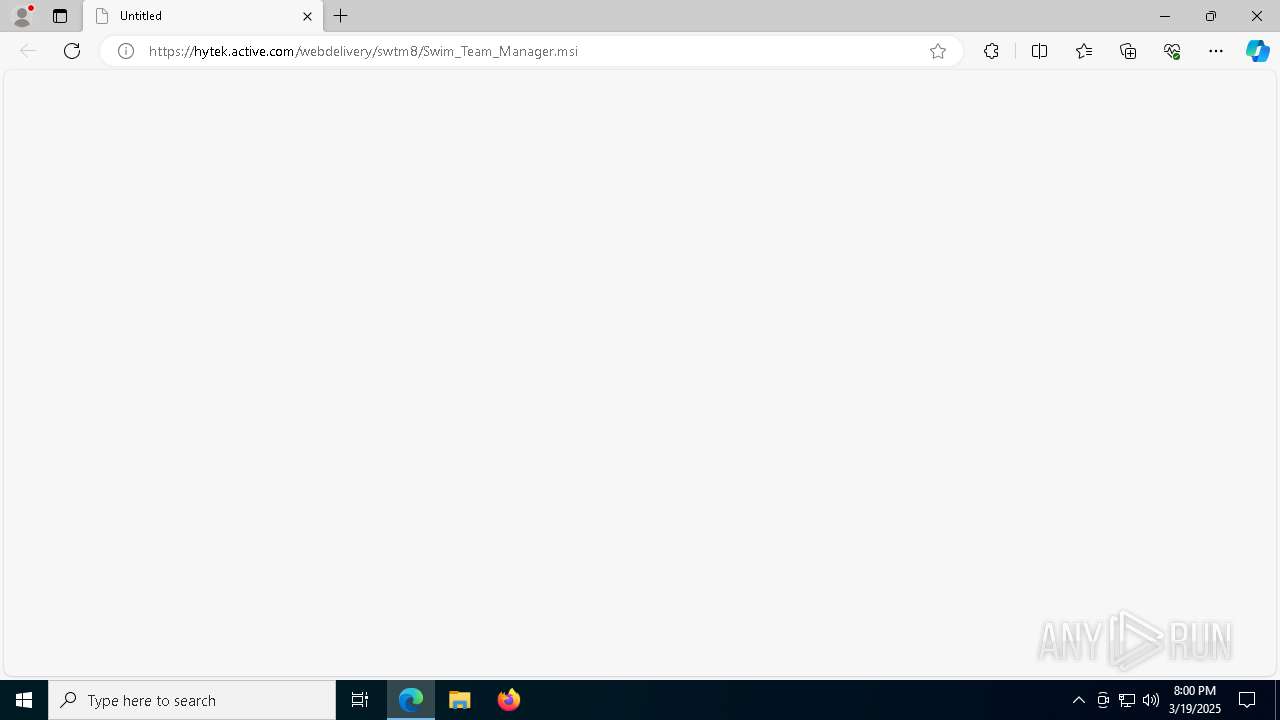
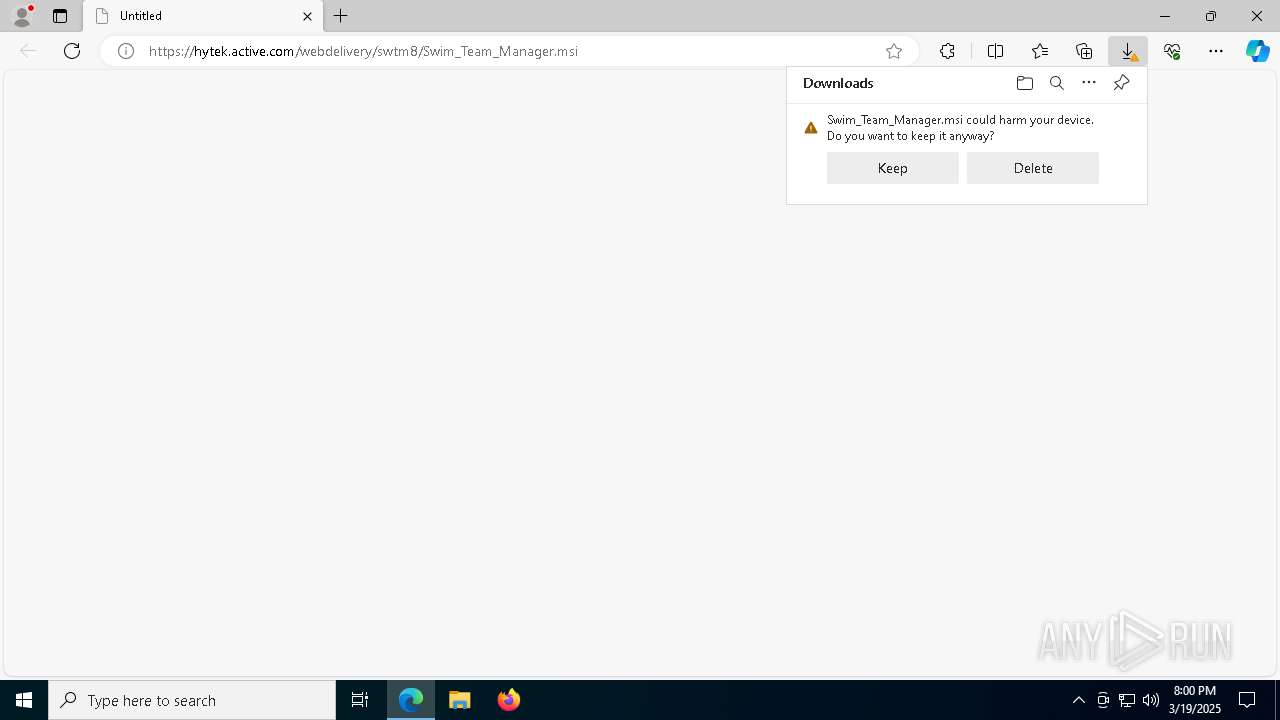
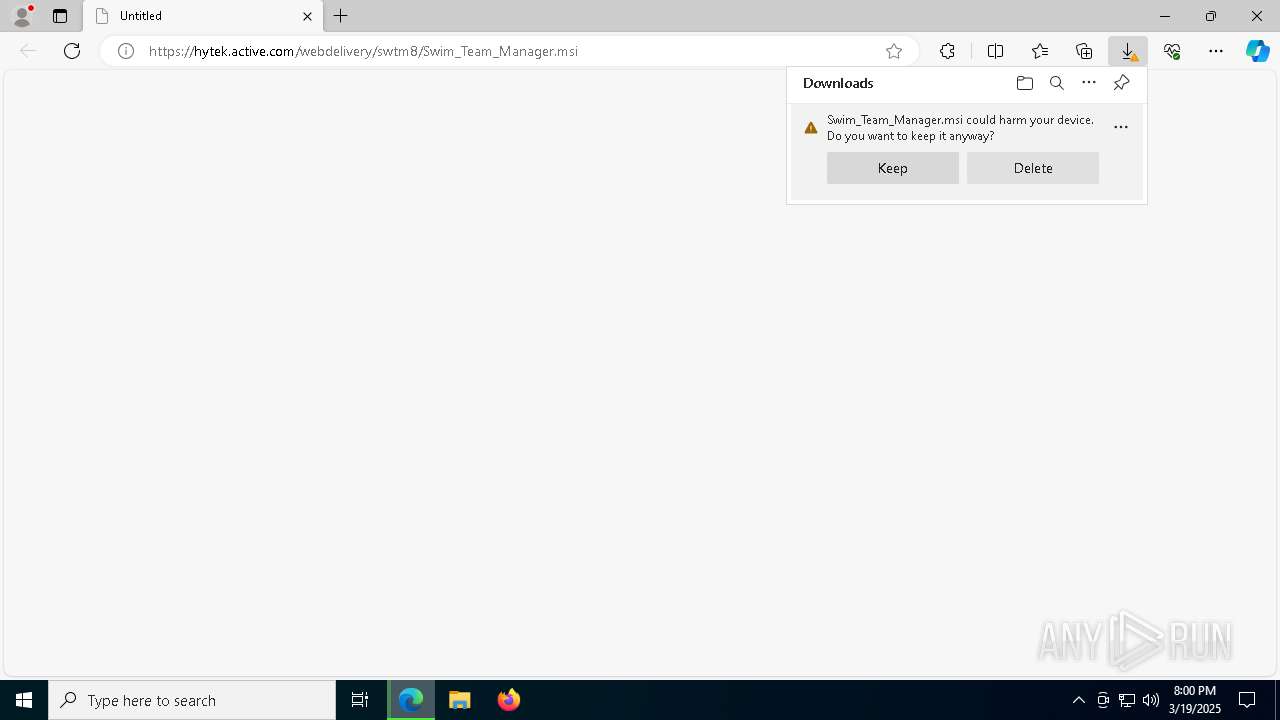
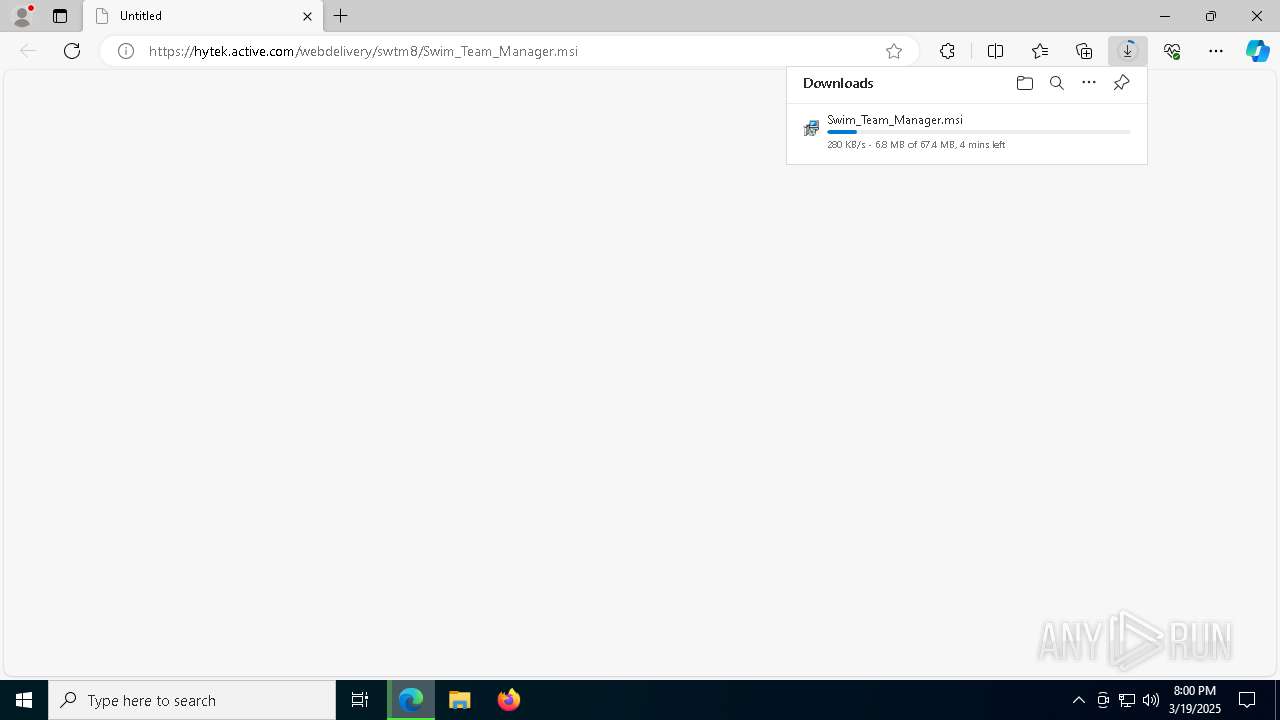
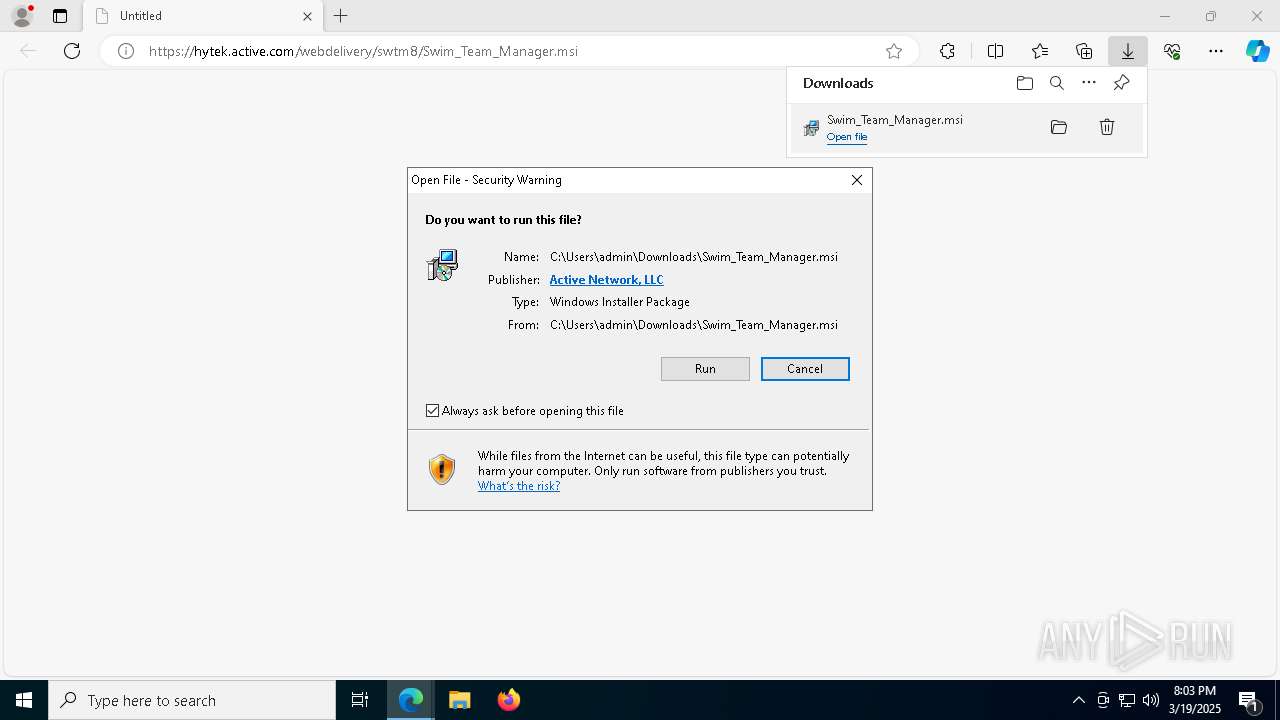
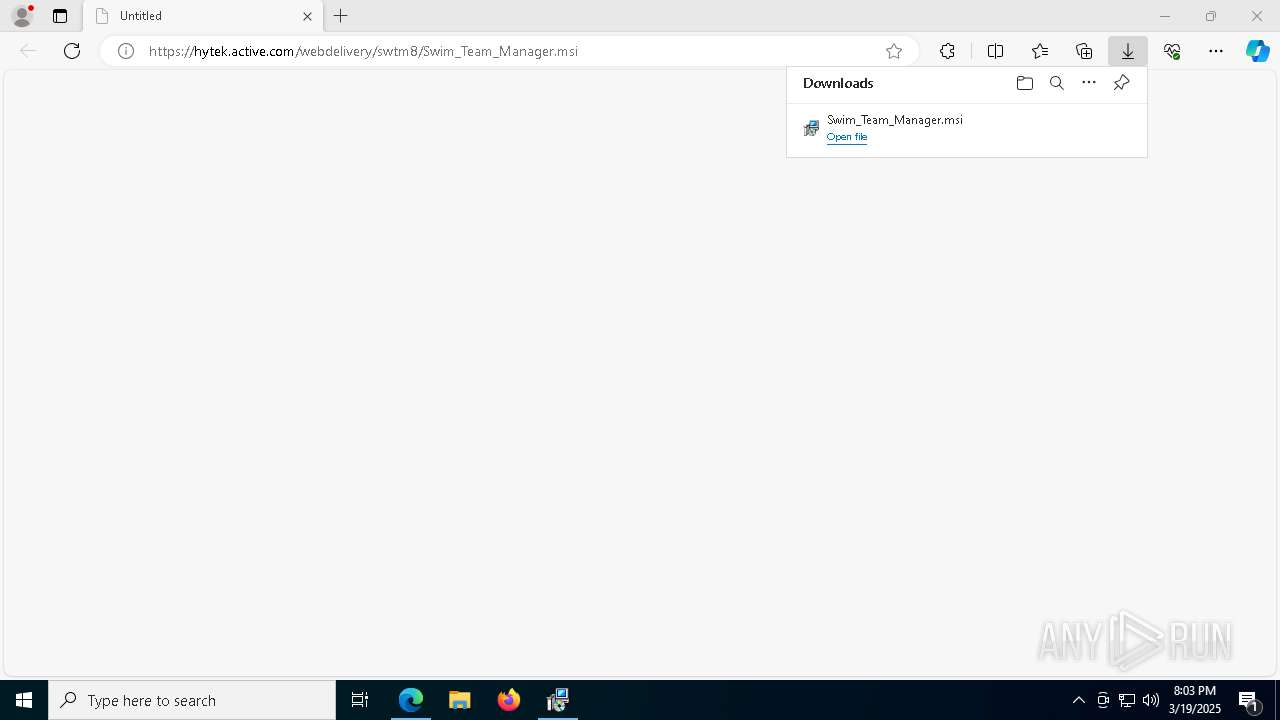
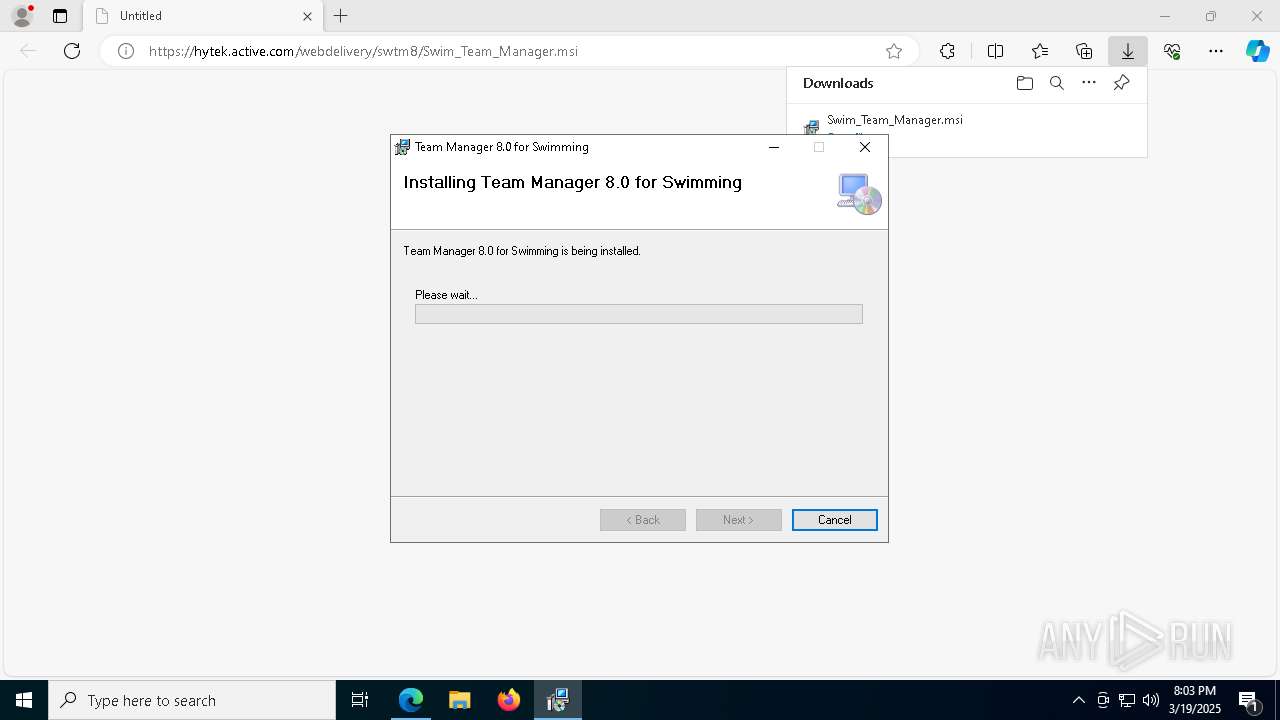
| URL: | https://hytek.active.com/webdelivery/swtm8/Swim_Team_Manager.msi |
| Full analysis: | https://app.any.run/tasks/45c6b4a9-ff31-4f93-a61f-987dd79403f5 |
| Verdict: | Malicious activity |
| Analysis date: | March 19, 2025, 19:59:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 476AE3564763E4B53F14C48364453E44 |
| SHA1: | F940994E6B0A256CF6D62D19E2273F90572337FC |
| SHA256: | 9499830F48A2A9D15B69EE020A9F3B678FD93389CC14ADC1D9DB3AF7C031C77C |
| SSDEEP: | 3:N8g5wwyKiAhACML71MILs1U8:2gu5FjV3LQU8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 6480)
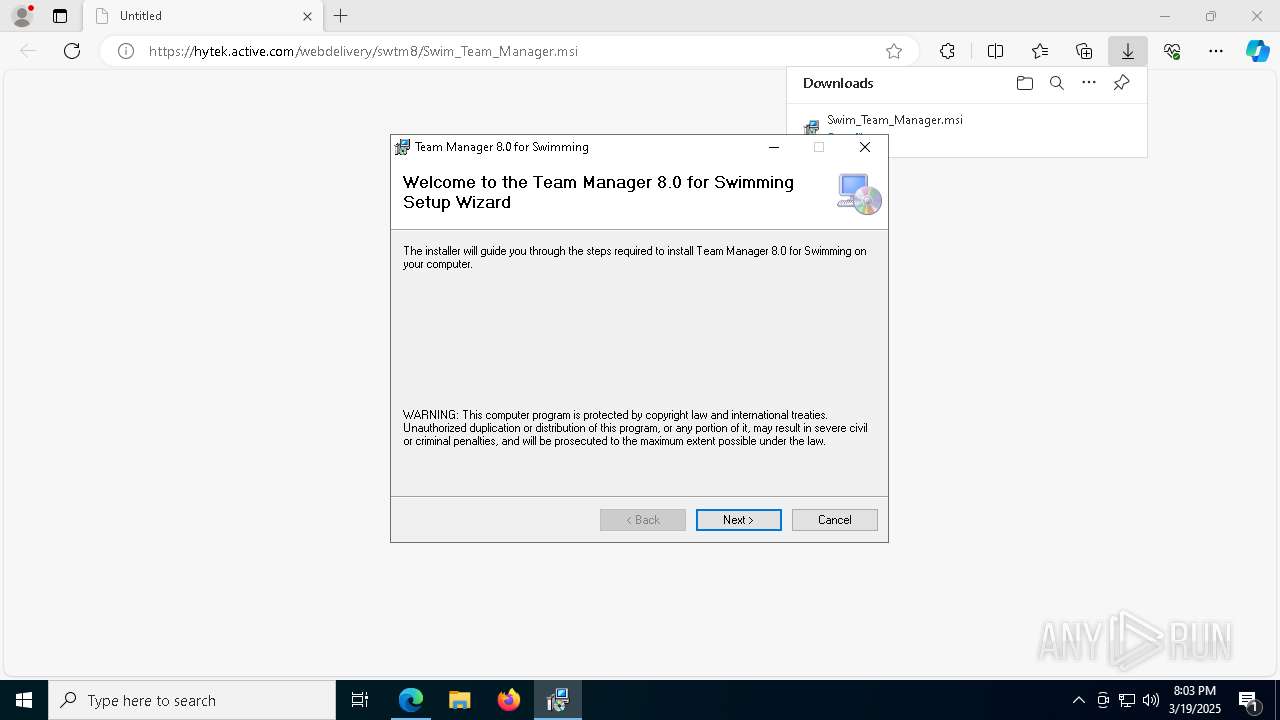
Executes as Windows Service
- VSSVC.exe (PID: 5232)
Process drops legitimate windows executable
- msiexec.exe (PID: 5164)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 8948)
- msiexec.exe (PID: 3124)
- msiexec.exe (PID: 1280)
- msiexec.exe (PID: 6228)
- msiexec.exe (PID: 7872)
- msiexec.exe (PID: 7720)
- msiexec.exe (PID: 7924)
- msiexec.exe (PID: 1600)
- msiexec.exe (PID: 6740)
- msiexec.exe (PID: 8824)
- msiexec.exe (PID: 8984)
- msiexec.exe (PID: 8084)
- msiexec.exe (PID: 9040)
INFO
Reads Environment values
- identity_helper.exe (PID: 8552)
Reads the computer name
- identity_helper.exe (PID: 8552)
- ShellExperienceHost.exe (PID: 6480)
- msiexec.exe (PID: 5164)
- msiexec.exe (PID: 5436)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 4740)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 5436)
- BackgroundTransferHost.exe (PID: 8916)
- BackgroundTransferHost.exe (PID: 8532)
- BackgroundTransferHost.exe (PID: 9044)
- BackgroundTransferHost.exe (PID: 4740)
- msiexec.exe (PID: 8220)
Checks supported languages
- identity_helper.exe (PID: 8552)
- ShellExperienceHost.exe (PID: 6480)
- msiexec.exe (PID: 5164)
- msiexec.exe (PID: 6208)
- msiexec.exe (PID: 5436)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 4740)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 4740)
- slui.exe (PID: 8456)
- slui.exe (PID: 8732)
- msiexec.exe (PID: 8220)
- msiexec.exe (PID: 5164)
Executable content was dropped or overwritten
- msedge.exe (PID: 8836)
- msiexec.exe (PID: 8220)
- msiexec.exe (PID: 5164)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6652)
The sample compiled with english language support
- msedge.exe (PID: 8836)
- msiexec.exe (PID: 8220)
- msiexec.exe (PID: 5164)
Create files in a temporary directory
- msiexec.exe (PID: 6208)
Reads the machine GUID from the registry
- msiexec.exe (PID: 5164)
Manages system restore points
- SrTasks.exe (PID: 444)
Reads mouse settings
- msiexec.exe (PID: 3124)
Application launched itself
- msedge.exe (PID: 6652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
292
Monitored processes
146
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | "C:\Windows\syswow64\MsiExec.exe" /Y "C:\WINDOWS\ipmon60.ocx" | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | "C:\Windows\syswow64\MsiExec.exe" /Y "C:\WINDOWS\msrd3x40.dll" | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | "C:\Windows\syswow64\MsiExec.exe" /Y "C:\WINDOWS\Talbarcd.ocx" | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | C:\Windows\syswow64\MsiExec.exe -Embedding DD9318307B55C63D91681DD4C8AF2132 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | "C:\Windows\syswow64\MsiExec.exe" /Y "C:\WINDOWS\titext8.ocx" | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1112 | "C:\Windows\syswow64\MsiExec.exe" /Y "C:\Program Files (x86)\Common Files\Business Objects\3.0\bin\webReporting.dll" | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Windows\syswow64\MsiExec.exe" /Y "C:\WINDOWS\DZSTACTX.DLL" | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | "C:\Windows\syswow64\MsiExec.exe" /Y "C:\WINDOWS\ExportModeller.dll" | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1584 | "C:\Windows\syswow64\MsiExec.exe" /Y "C:\Program Files (x86)\Common Files\Business Objects\3.0\bin\craxddrt.dll" | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
31 238
Read events
27 476
Write events
3 446
Delete events
316
Modification events
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D4EEC5BF4D8F2F00 | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6CBDFDBF4D8F2F00 | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721562 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D3CD9E5C-BA41-48FD-BCDC-BABAEC38609E} | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721562 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F20EC3CB-6FD2-4E35-8EE0-0E337774C679} | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 376B58C04D8F2F00 | |||
| (PID) Process: | (6652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
175
Suspicious files
660
Text files
118
Unknown types
123
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c601.TMP | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c620.TMP | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c620.TMP | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c630.TMP | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c611.TMP | — | |
MD5:— | SHA256:— | |||
| 6652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
65
DNS requests
67
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.7:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7600 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8048 | svchost.exe | HEAD | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e9f25f54-9a54-4e31-91fd-7fd2ad4f4a2f?P1=1743002077&P2=404&P3=2&P4=fL7Ec%2bzbgpZ0y%2fS5fmUPFUaRl6QUchg8pnOir9WJneK08wzxzZct9Wm4SHQYJe0asHWhrbmgt1KySHVuAwj2ig%3d%3d | unknown | — | — | whitelisted |
4740 | BackgroundTransferHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2320 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2320 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8048 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e9f25f54-9a54-4e31-91fd-7fd2ad4f4a2f?P1=1743002077&P2=404&P3=2&P4=fL7Ec%2bzbgpZ0y%2fS5fmUPFUaRl6QUchg8pnOir9WJneK08wzxzZct9Wm4SHQYJe0asHWhrbmgt1KySHVuAwj2ig%3d%3d | unknown | — | — | whitelisted |
8048 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e9f25f54-9a54-4e31-91fd-7fd2ad4f4a2f?P1=1743002077&P2=404&P3=2&P4=fL7Ec%2bzbgpZ0y%2fS5fmUPFUaRl6QUchg8pnOir9WJneK08wzxzZct9Wm4SHQYJe0asHWhrbmgt1KySHVuAwj2ig%3d%3d | unknown | — | — | whitelisted |
8048 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e9f25f54-9a54-4e31-91fd-7fd2ad4f4a2f?P1=1743002077&P2=404&P3=2&P4=fL7Ec%2bzbgpZ0y%2fS5fmUPFUaRl6QUchg8pnOir9WJneK08wzxzZct9Wm4SHQYJe0asHWhrbmgt1KySHVuAwj2ig%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.24.77.7:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6700 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6652 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7432 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7432 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
hytek.active.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
login.live.com |
| whitelisted |