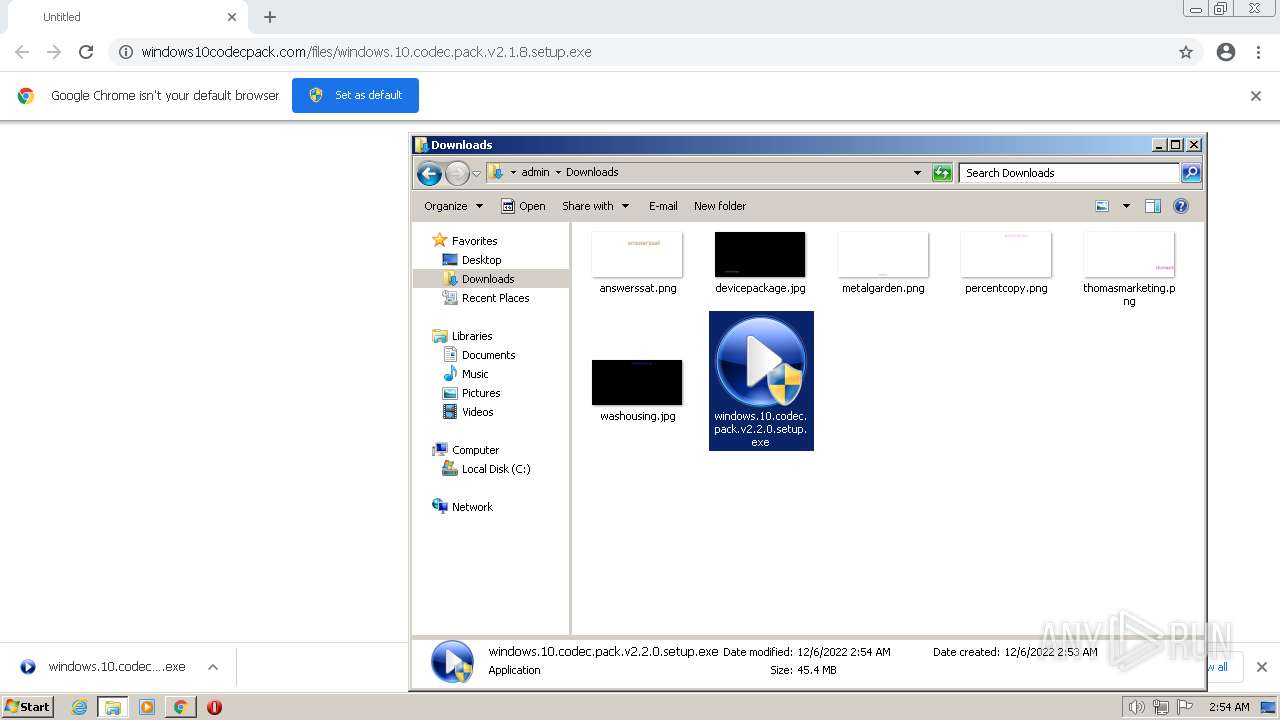
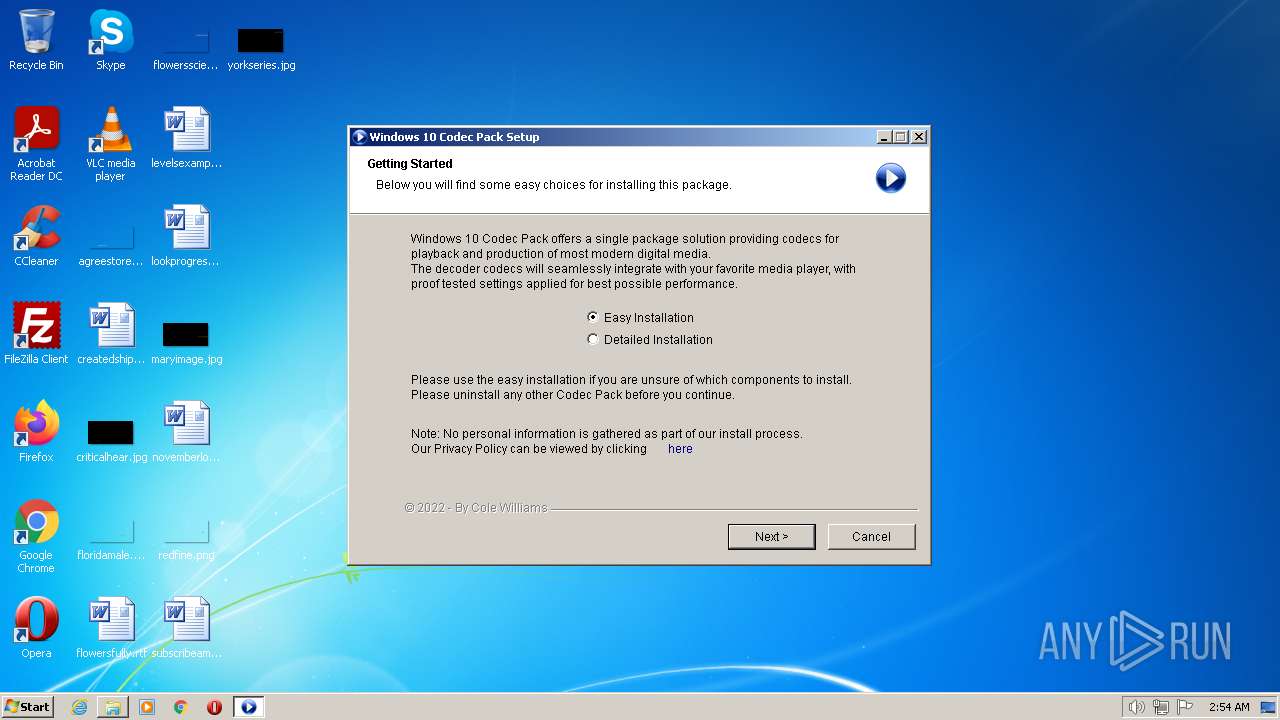
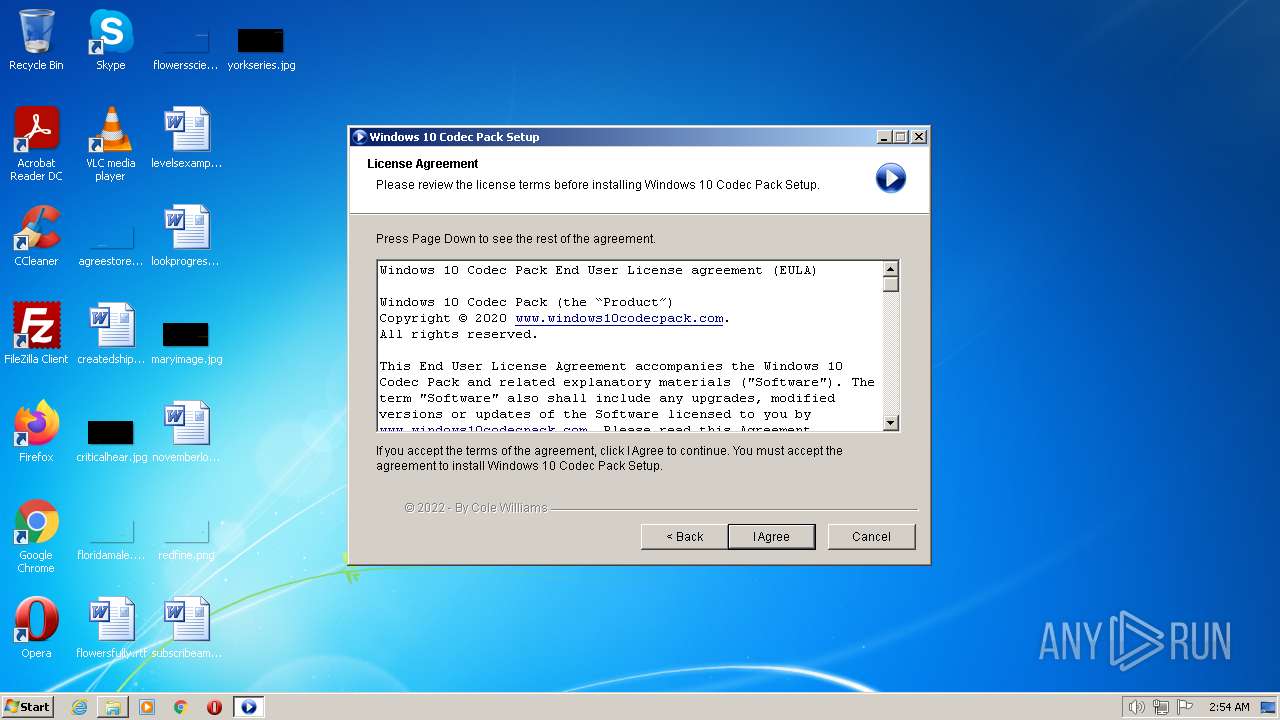
| URL: | https://www.windows10codecpack.com/files/windows.10.codec.pack.v2.1.8.setup.exe |
| Full analysis: | https://app.any.run/tasks/ac7ee9cd-6637-4901-a2e6-3629e9d43b5c |
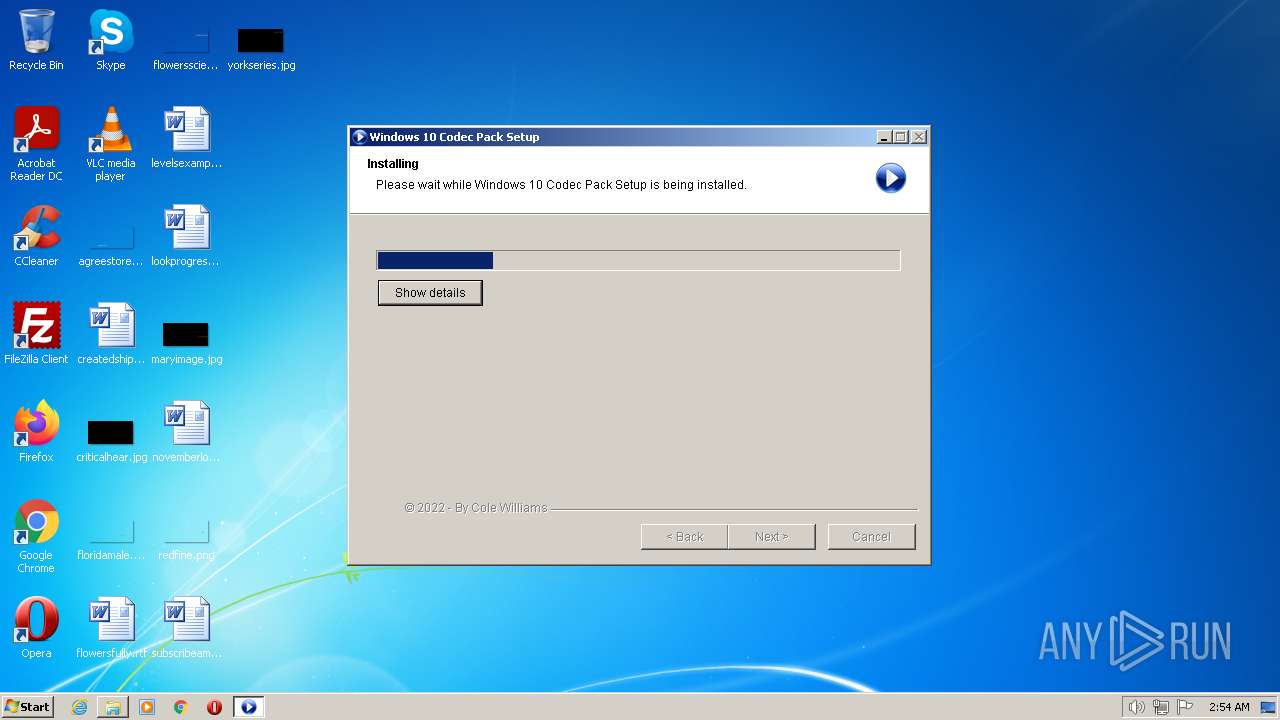
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2022, 02:53:15 |
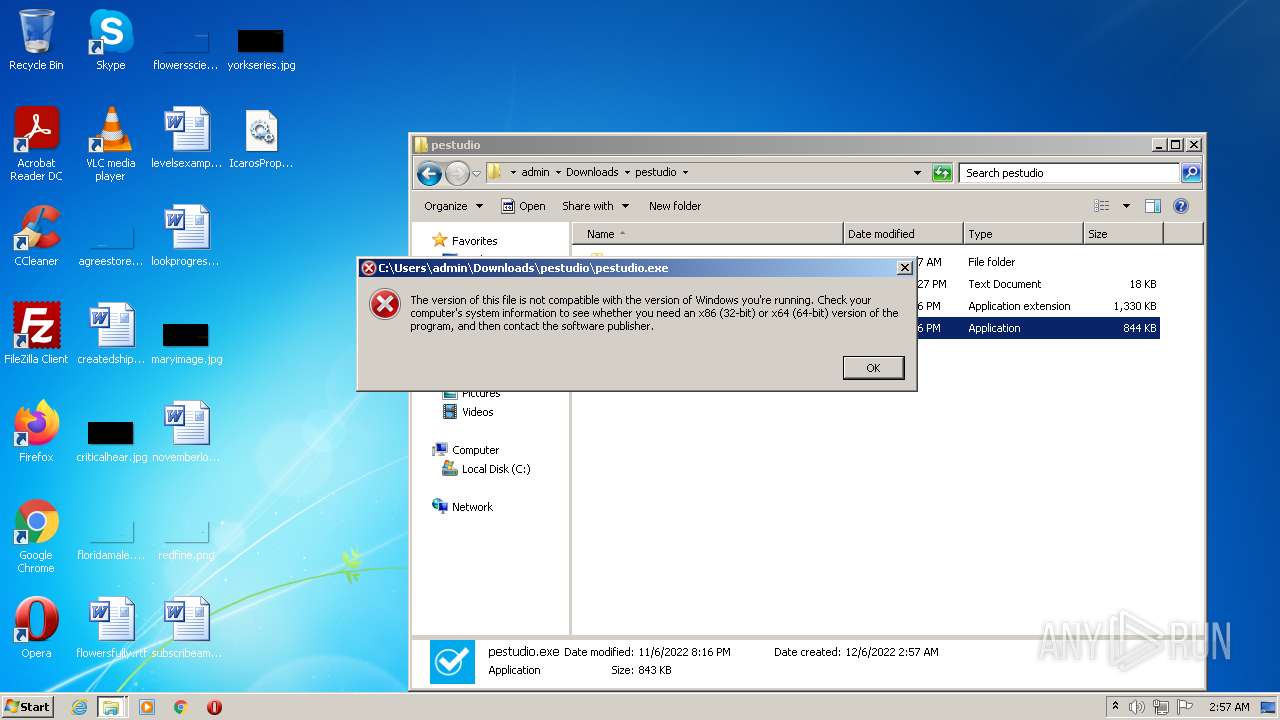
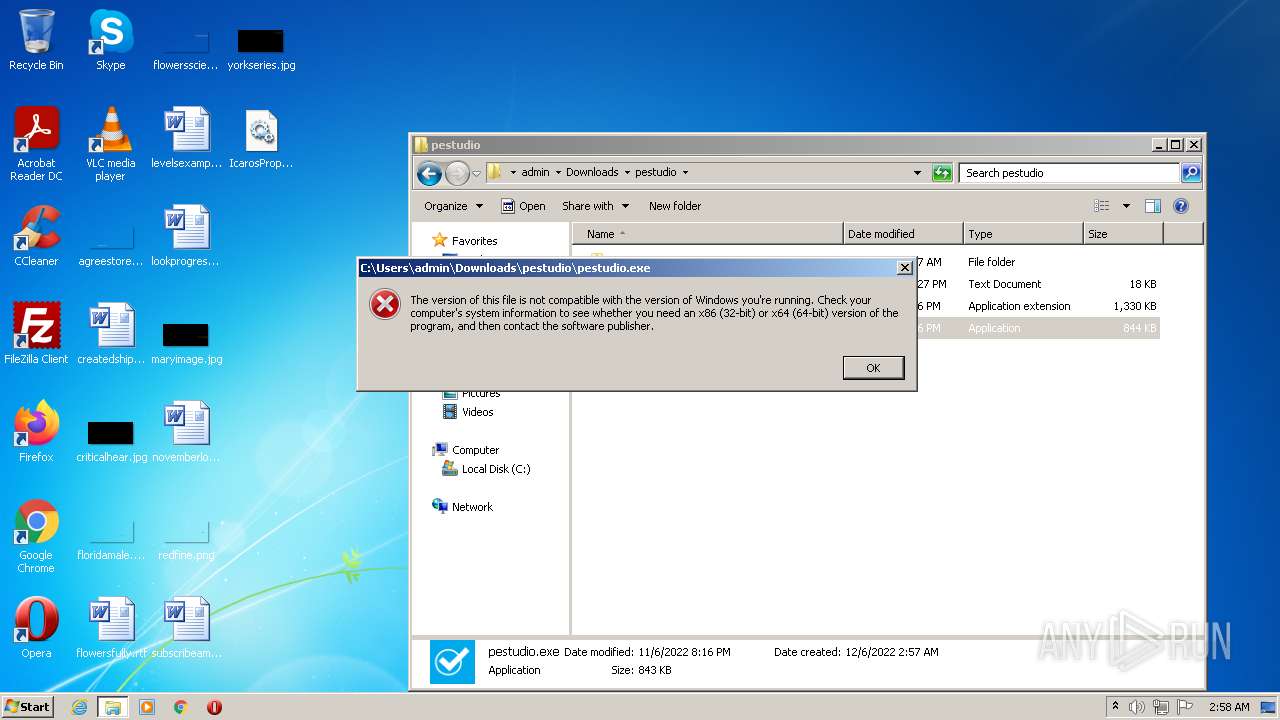
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C843CE7A7654CECBEF646D631A239D20 |
| SHA1: | 0756B60A465526CE16BB9468A50CA72F45708FBB |
| SHA256: | 948FF6729383BCFDABBA0098C6EB3B8FCB61A4FD95D4F0376C59299EA52A12E9 |
| SSDEEP: | 3:N8DSLgas2LKIyQK2kvkcSkA:2OLgV2H3I9PA |
MALICIOUS
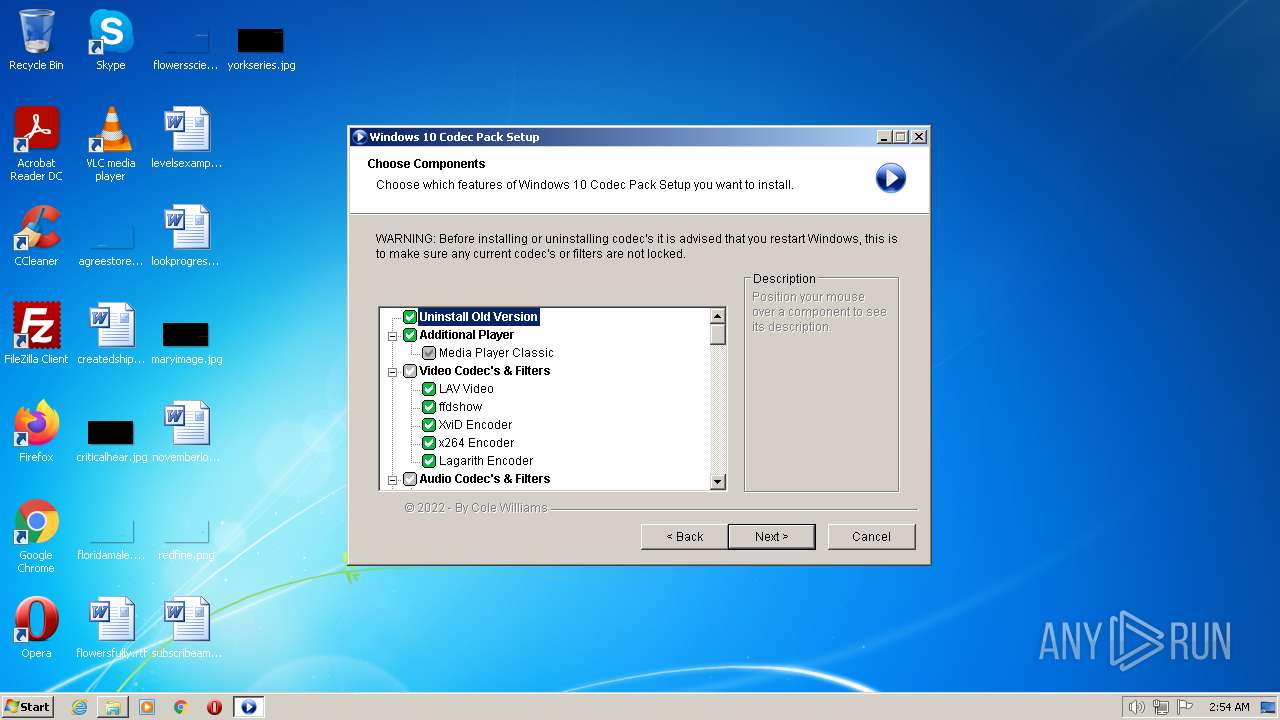
Application was dropped or rewritten from another process
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 2544)
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
- SetACL.exe (PID: 3004)
- SetACL.exe (PID: 2608)
- SetACL.exe (PID: 3536)
- SetACL.exe (PID: 1932)
- SetACL.exe (PID: 3636)
- SetACL.exe (PID: 3380)
- SetACL.exe (PID: 2296)
- SetACL.exe (PID: 3132)
- SetACL.exe (PID: 3708)
- SetACL.exe (PID: 1000)
- SetACL.exe (PID: 3124)
- SetACL.exe (PID: 3272)
- SetACL.exe (PID: 4028)
- SetACL.exe (PID: 2772)
- TrayMenu.exe (PID: 1944)
- SetACL.exe (PID: 3248)
- SetACL.exe (PID: 1916)
- SetACL.exe (PID: 3488)
- SetACL.exe (PID: 3832)
- SetACL.exe (PID: 2072)
- SetACL.exe (PID: 1396)
- SetACL.exe (PID: 2660)
- SetACL.exe (PID: 3960)
- SetACL.exe (PID: 3780)
- SetACL.exe (PID: 3068)
- SetACL.exe (PID: 2608)
- SetACL.exe (PID: 1764)
- SetACL.exe (PID: 3692)
- SetACL.exe (PID: 2160)
- SetACL.exe (PID: 2012)
- SetACL.exe (PID: 2300)
- SetACL.exe (PID: 1528)
- SetACL.exe (PID: 124)
- SetACL.exe (PID: 1820)
- SetACL.exe (PID: 2080)
- SetACL.exe (PID: 3876)
- SetACL.exe (PID: 2332)
- SetACL.exe (PID: 3448)
- SetACL.exe (PID: 2572)
- SetACL.exe (PID: 1400)
- SetACL.exe (PID: 2872)
- SetACL.exe (PID: 1328)
- SetACL.exe (PID: 3676)
- SetACL.exe (PID: 3224)
- SetACL.exe (PID: 3600)
- SetACL.exe (PID: 1752)
- SetACL.exe (PID: 2732)
- SetACL.exe (PID: 3304)
- SetACL.exe (PID: 1916)
- SetACL.exe (PID: 3832)
- SetACL.exe (PID: 1812)
- SetACL.exe (PID: 2520)
- SetACL.exe (PID: 3220)
- SetACL.exe (PID: 2936)
- SetACL.exe (PID: 3148)
- SetACL.exe (PID: 3804)
- SetACL.exe (PID: 1244)
- SetACL.exe (PID: 2964)
- SetACL.exe (PID: 3504)
- SetACL.exe (PID: 3316)
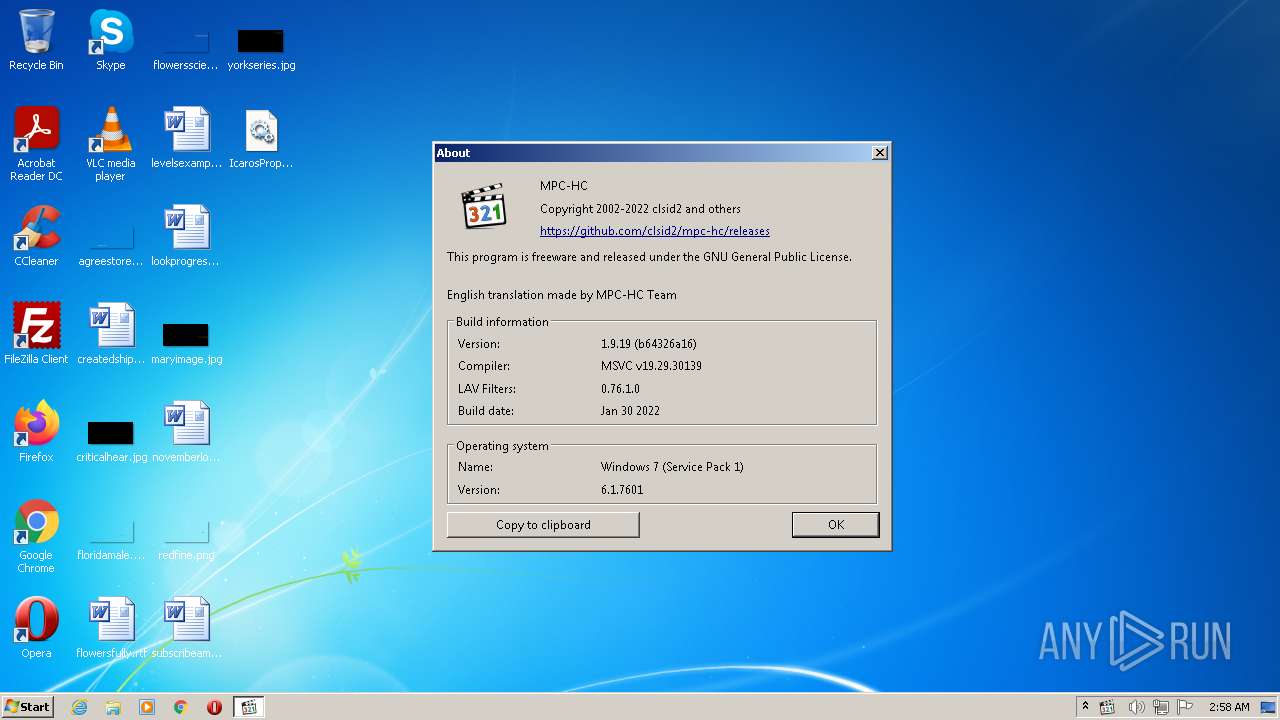
- mpc-hc.exe (PID: 3504)
Loads dropped or rewritten executable
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 2948)
- Regasm.exe (PID: 2780)
- chrome.exe (PID: 1276)
- SearchProtocolHost.exe (PID: 2456)
- Explorer.EXE (PID: 1084)
- chrome.exe (PID: 2672)
- mpc-hc.exe (PID: 3504)
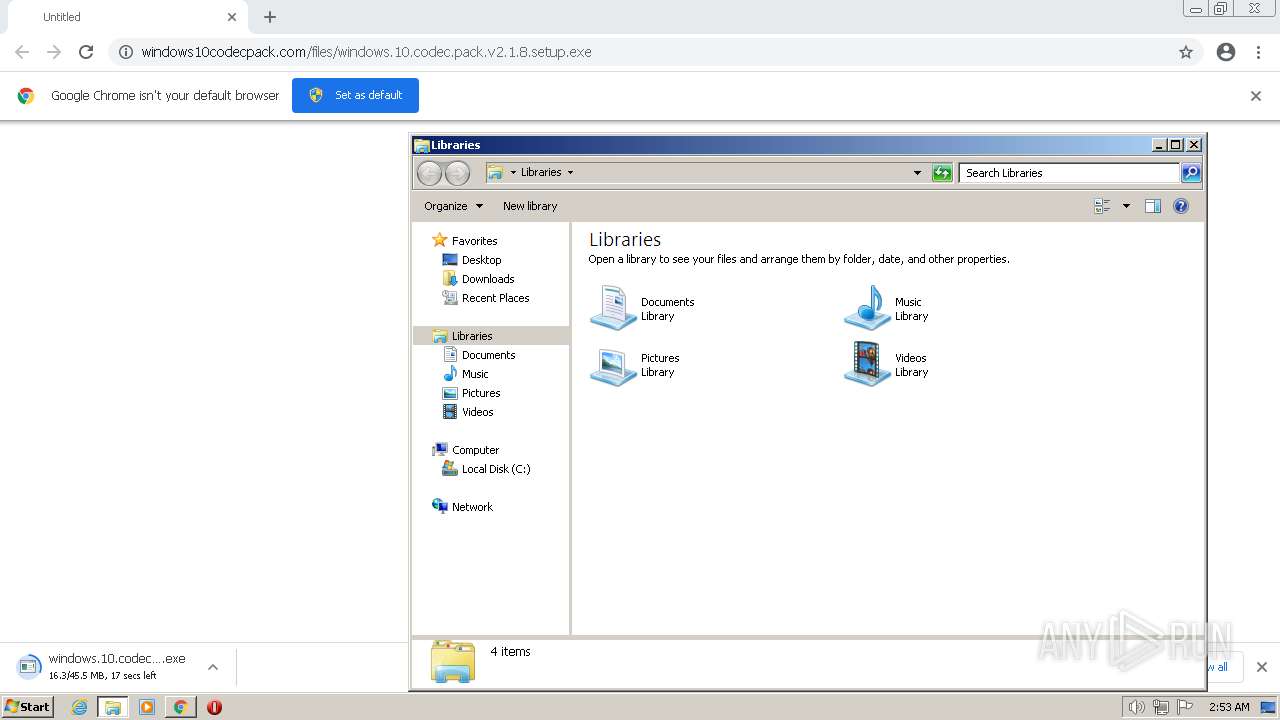
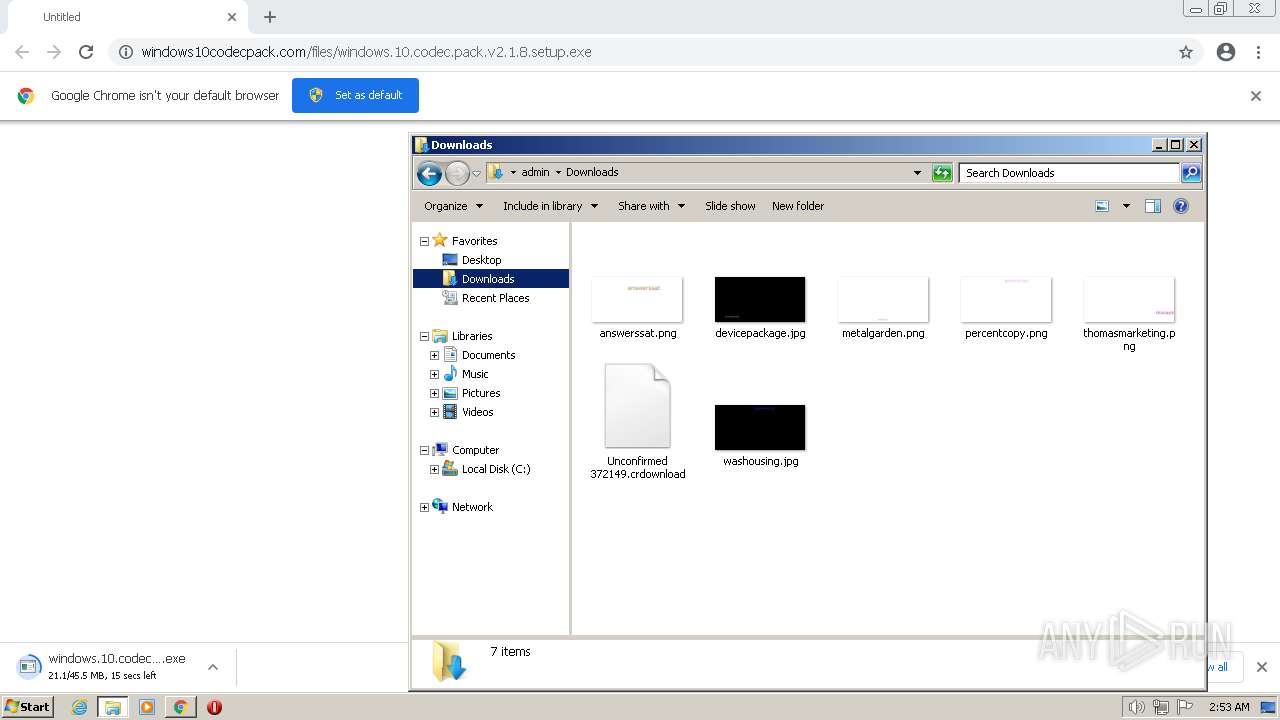
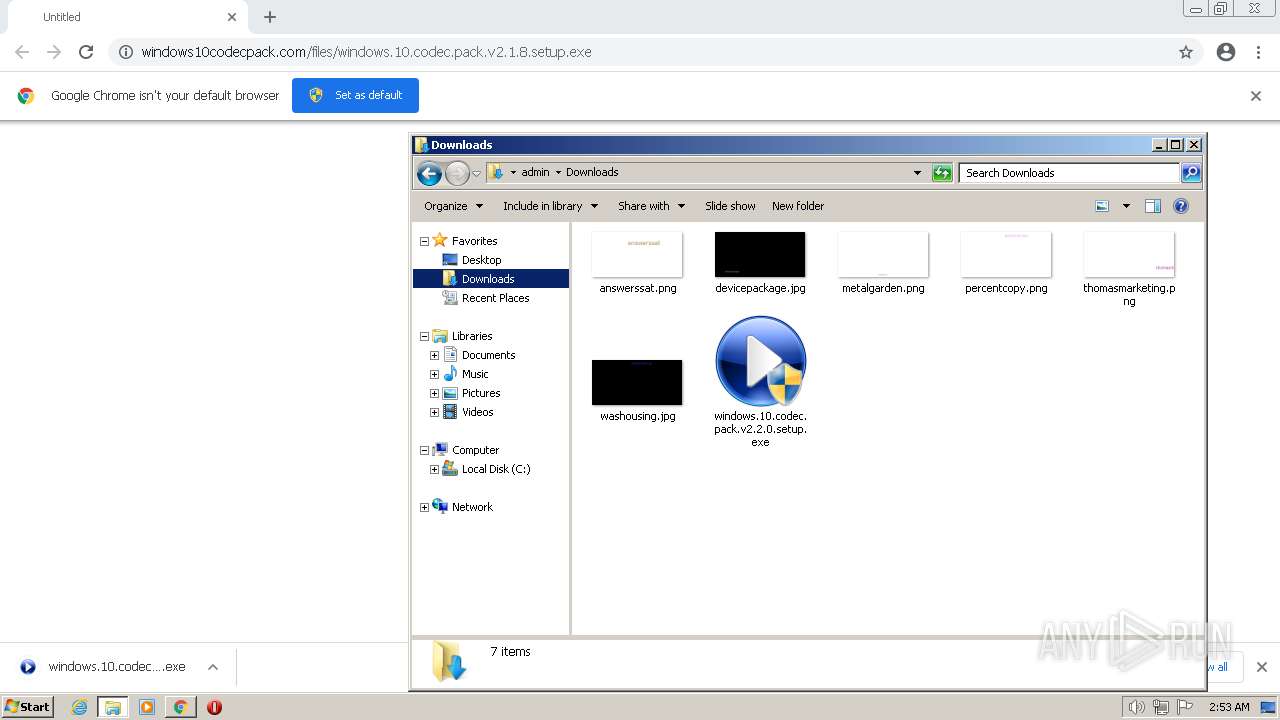
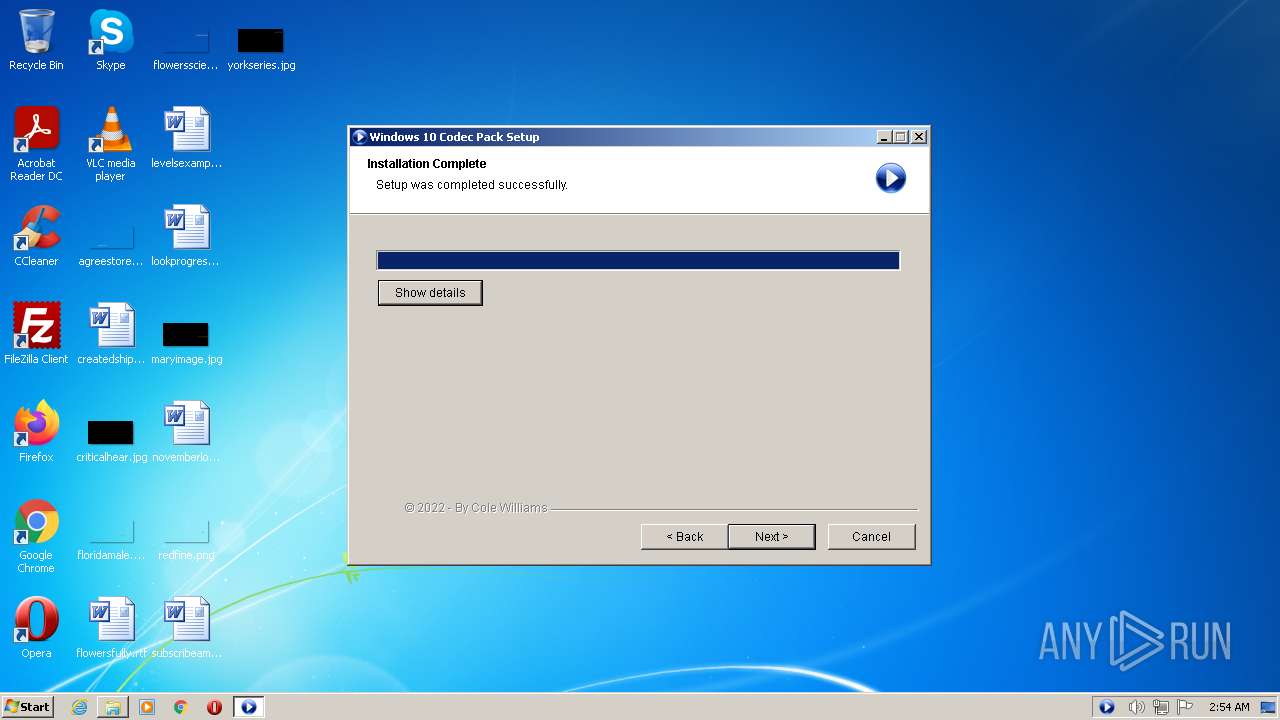
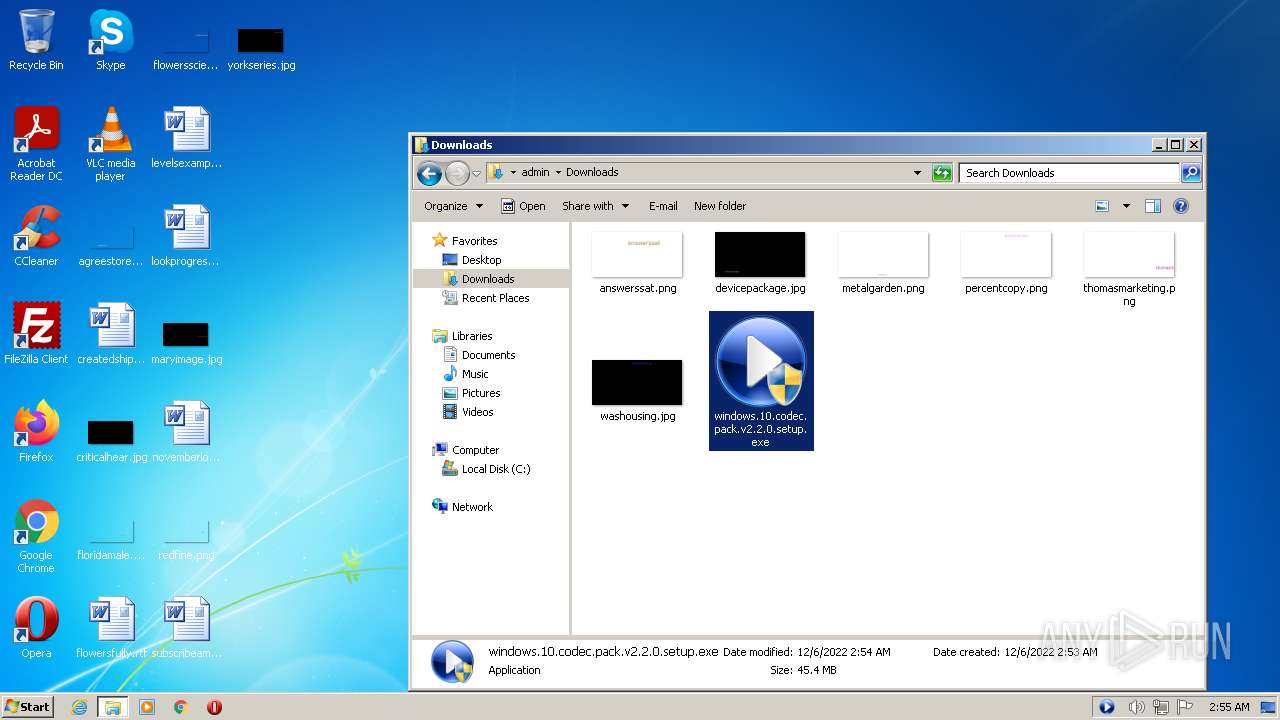
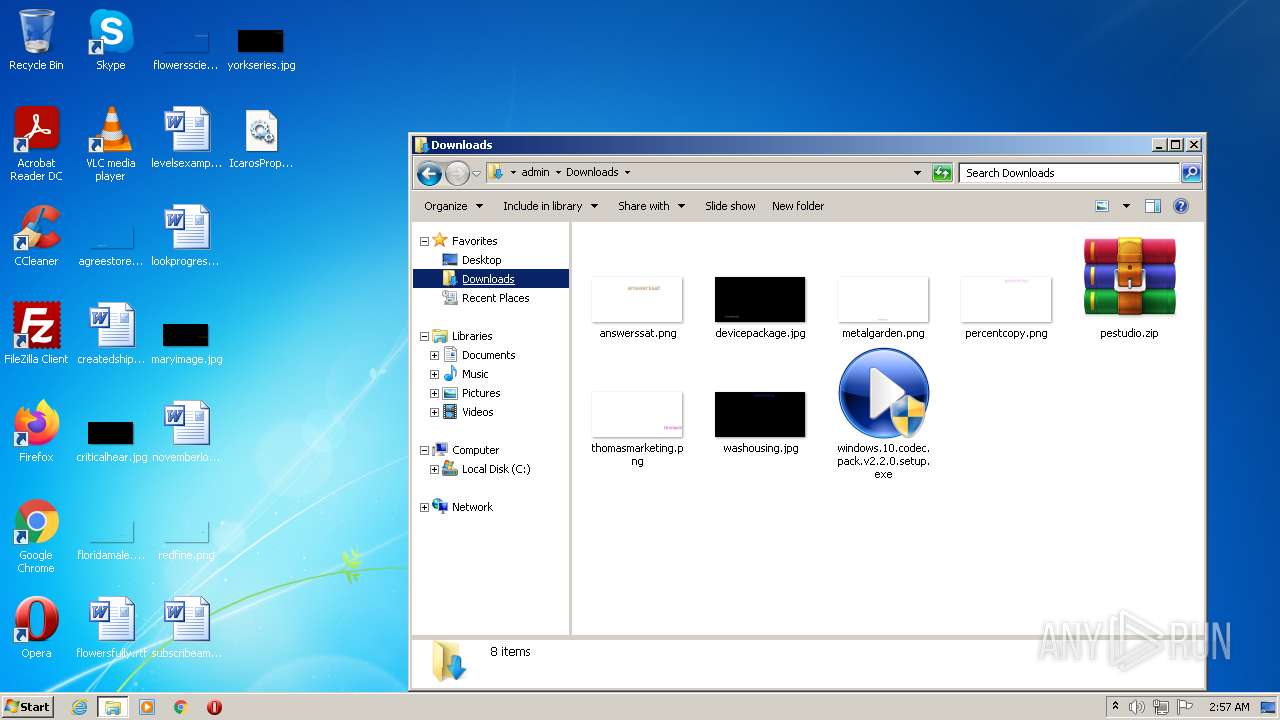
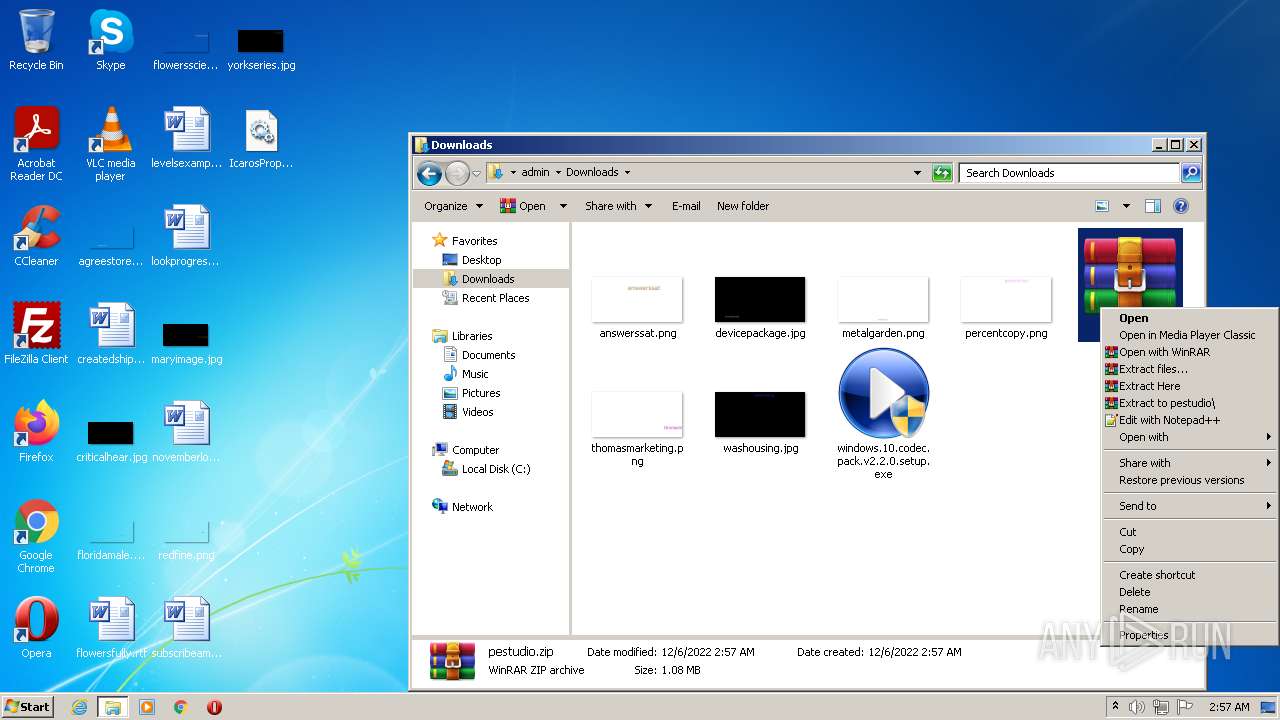
Drops the executable file immediately after the start
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
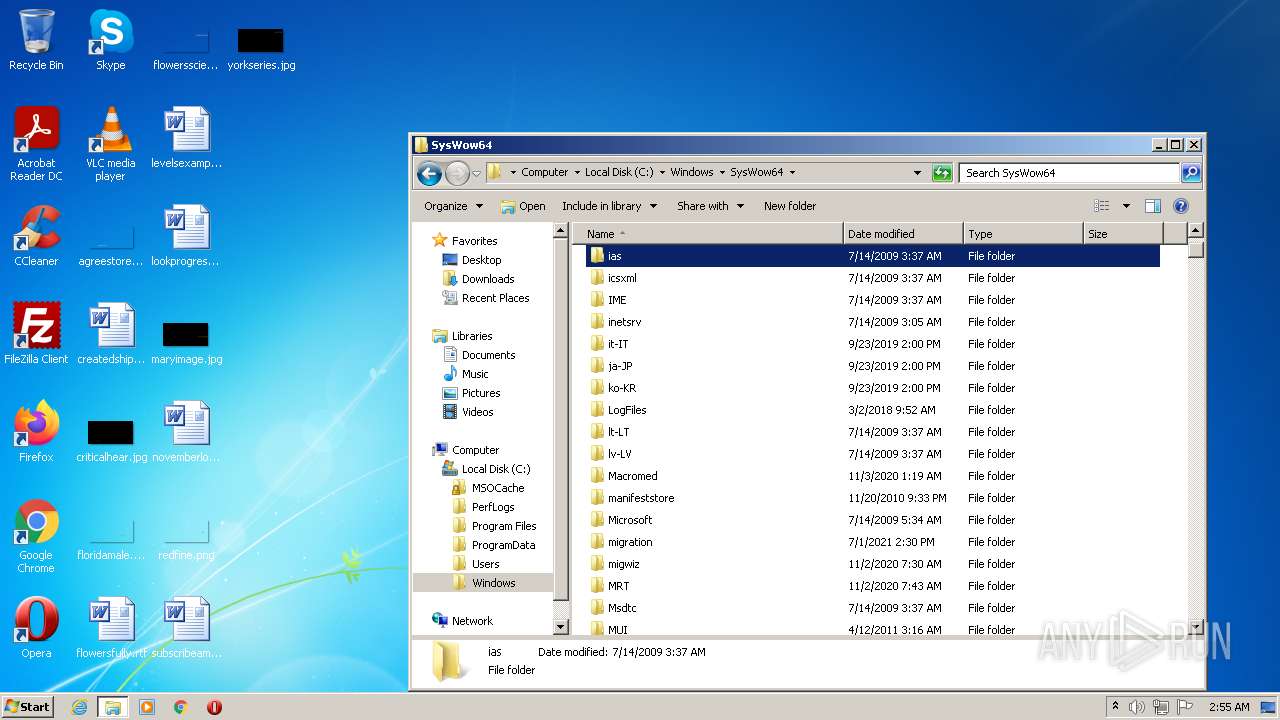
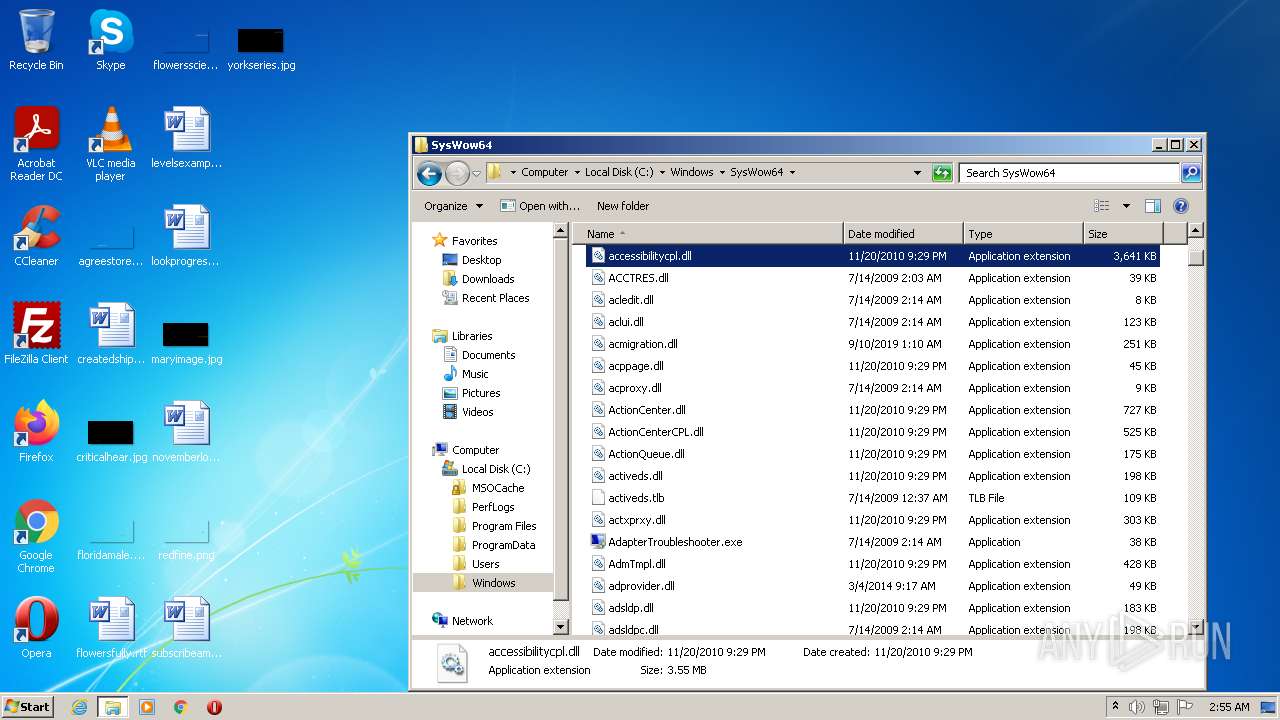
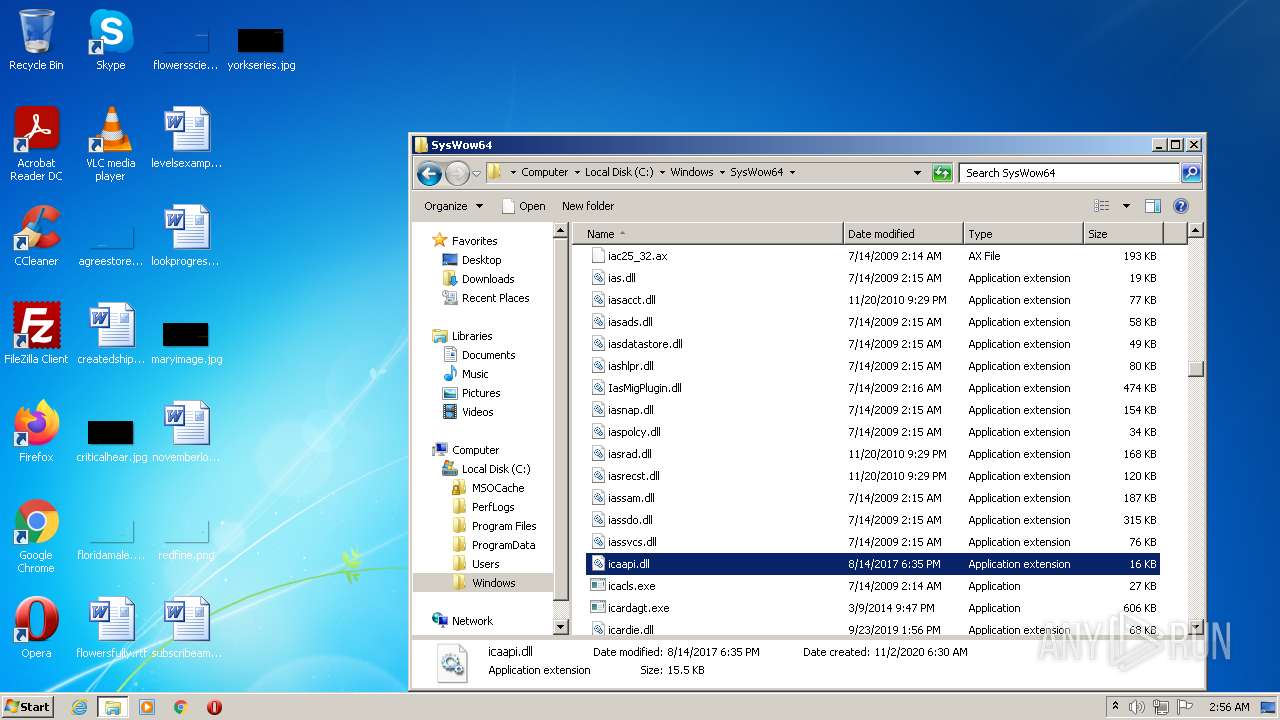
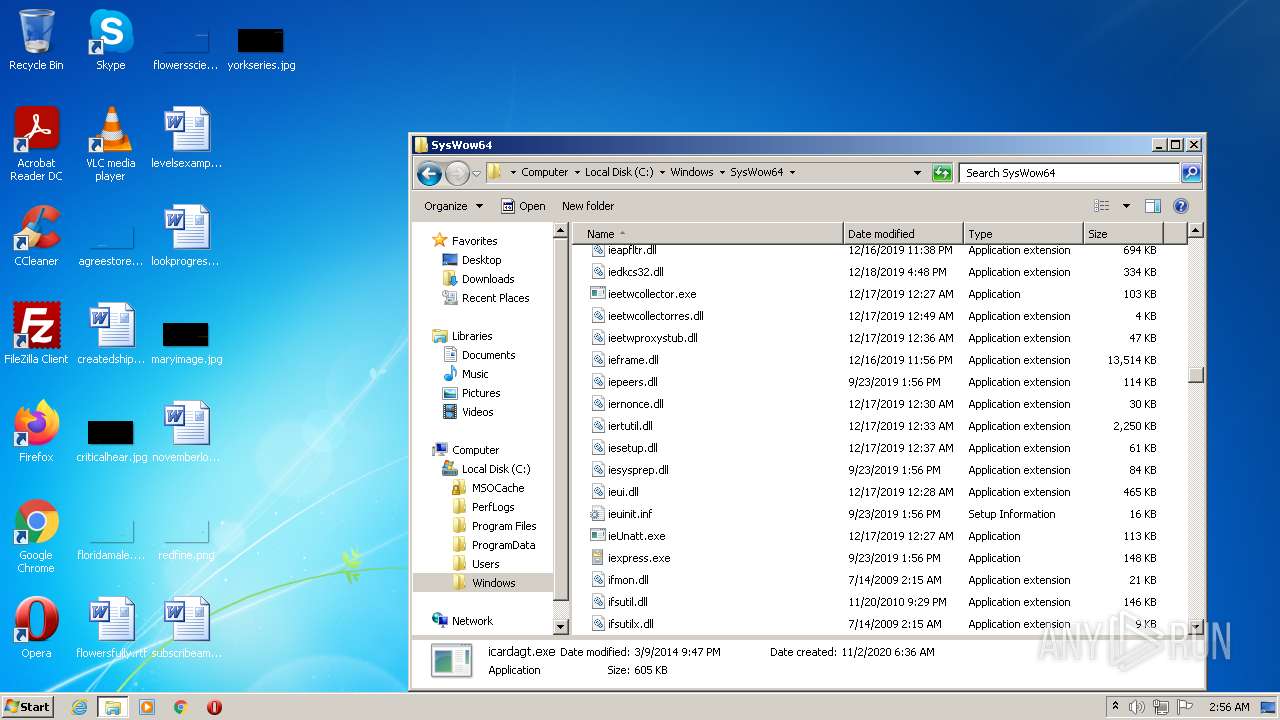
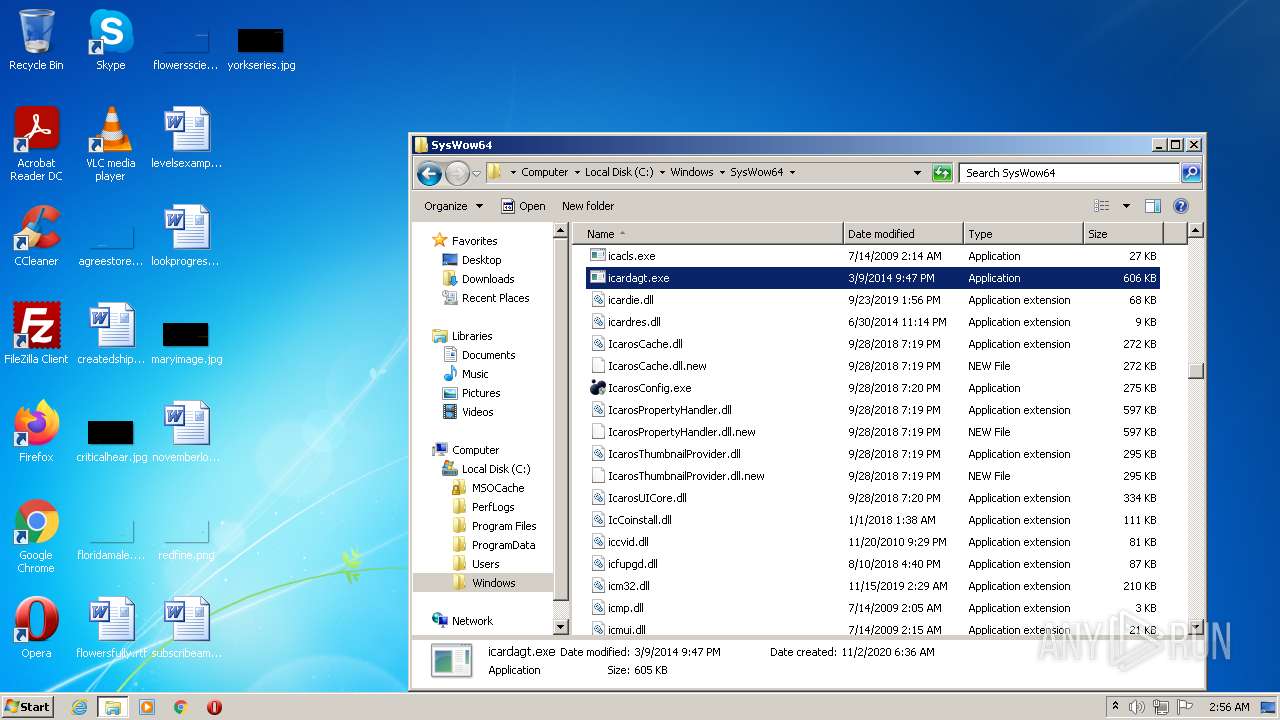
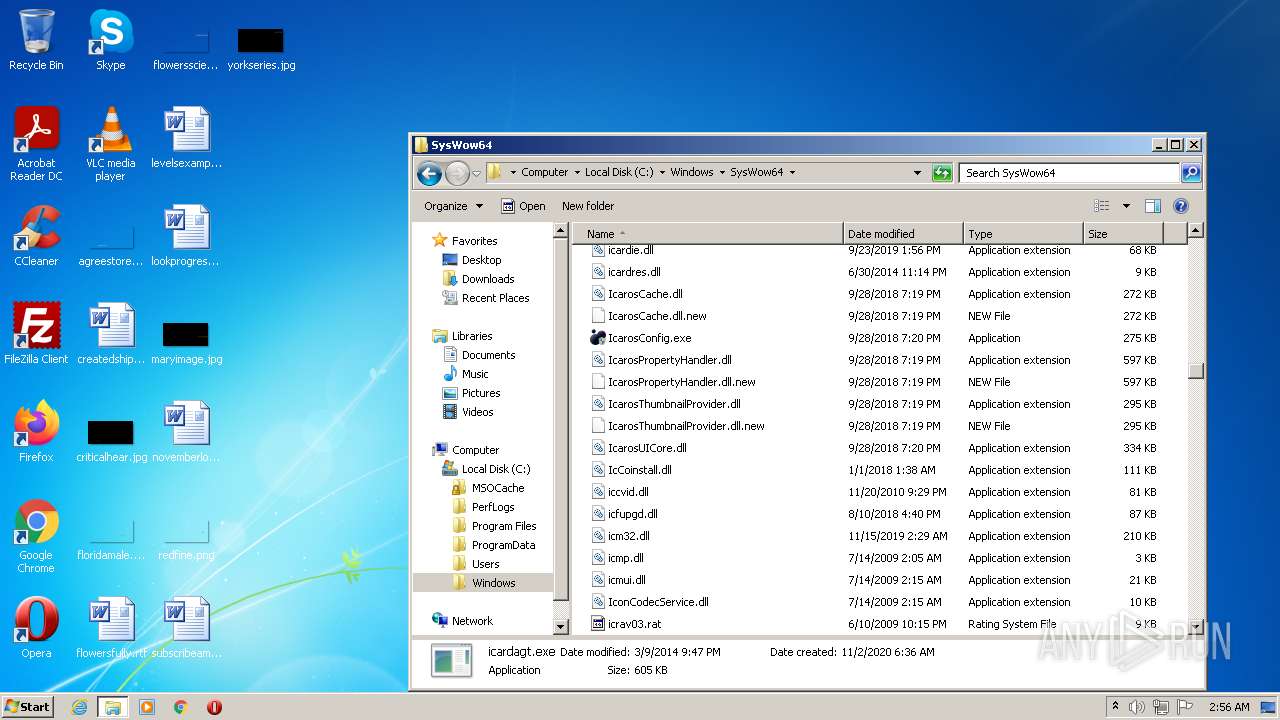
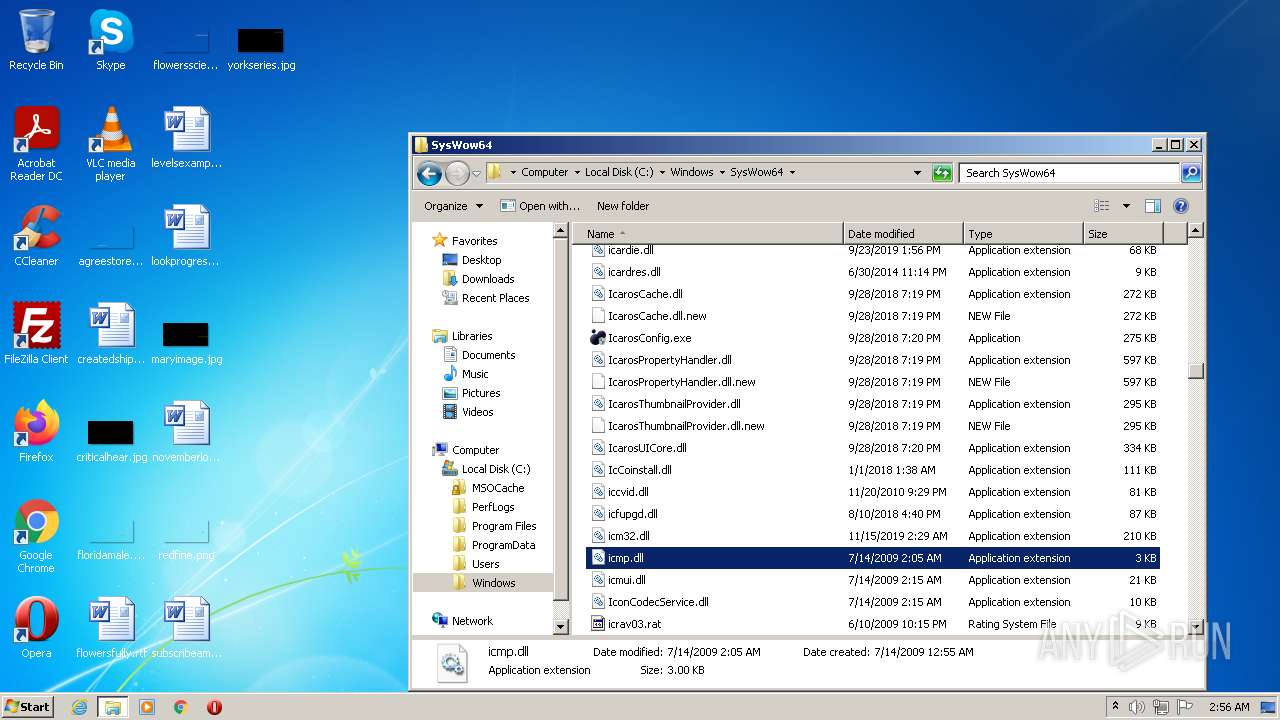
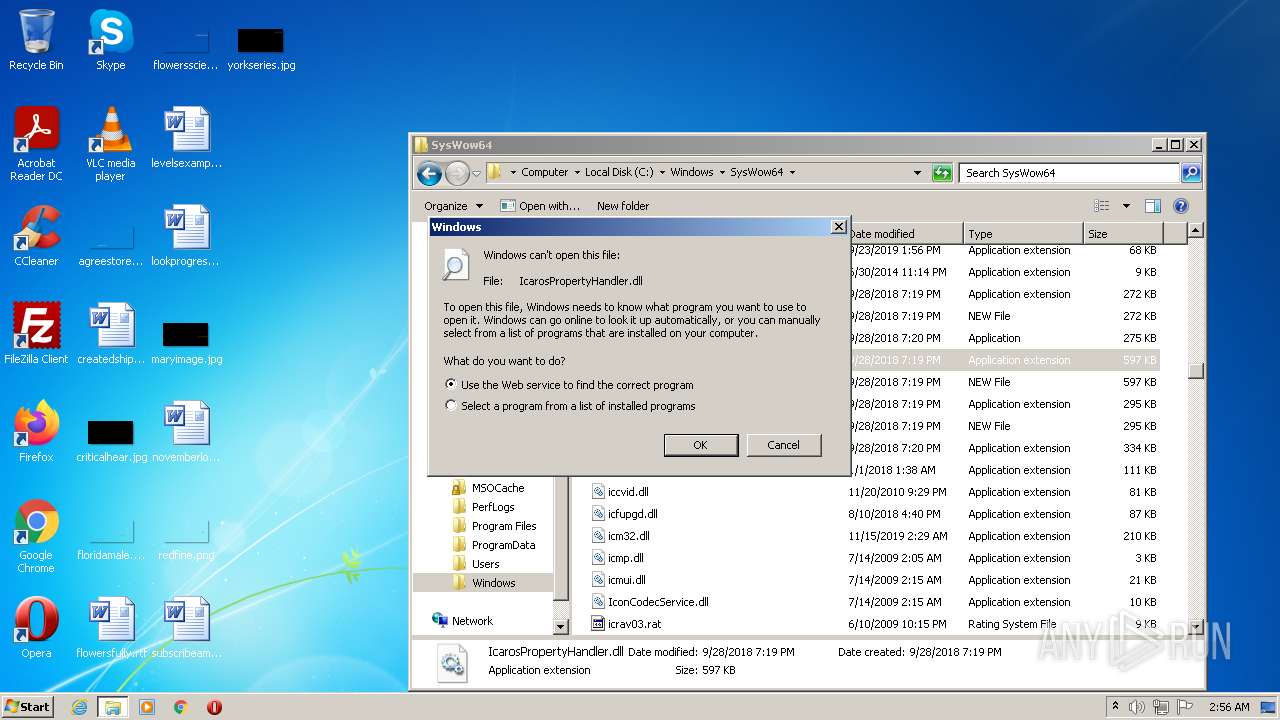
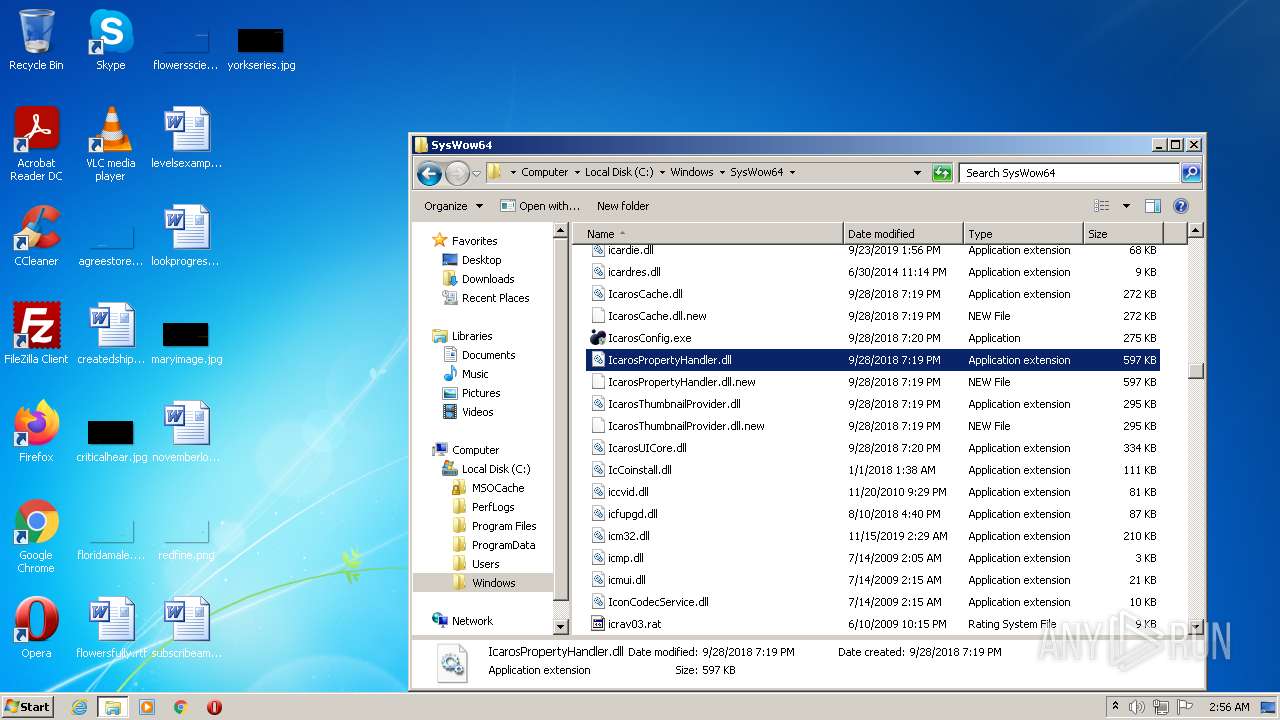
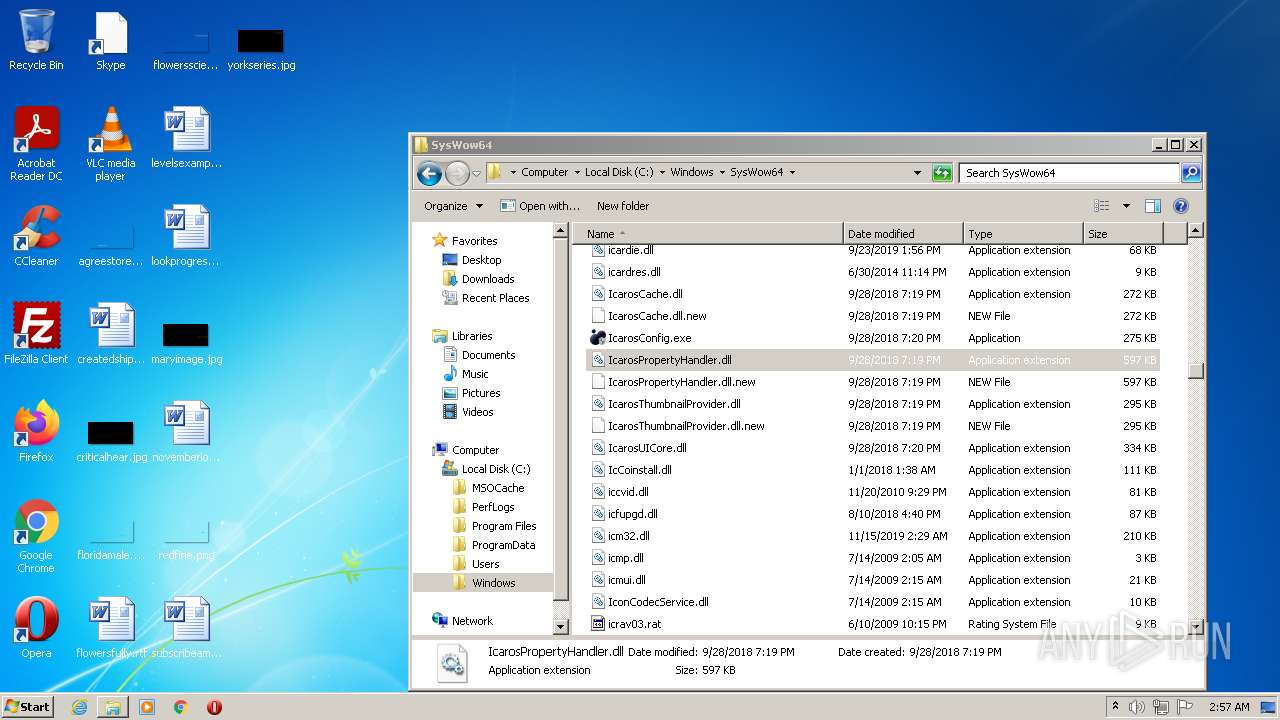
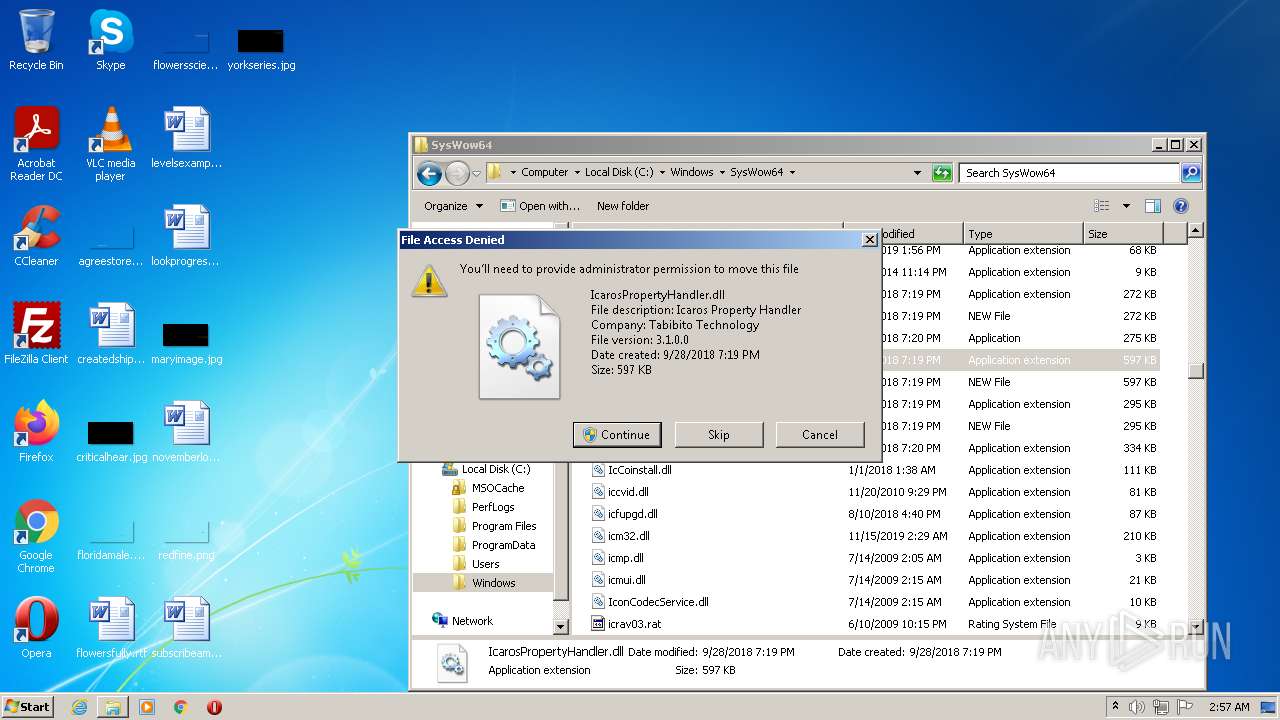
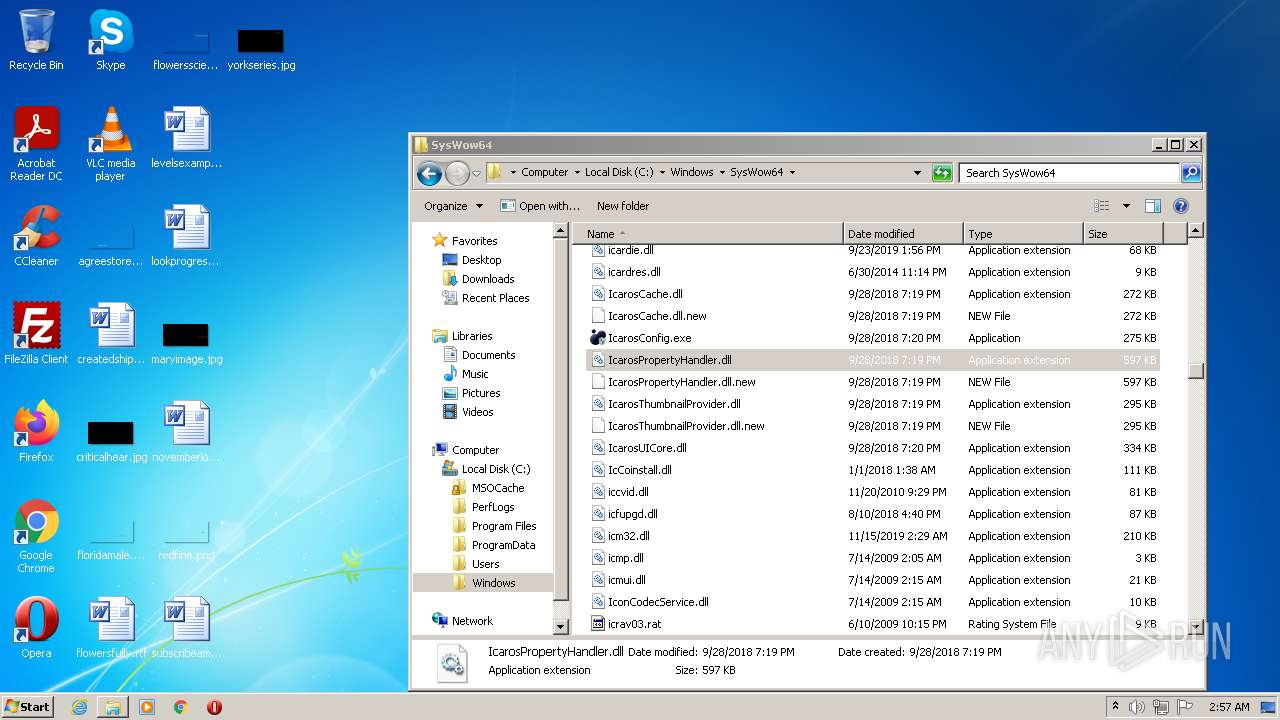
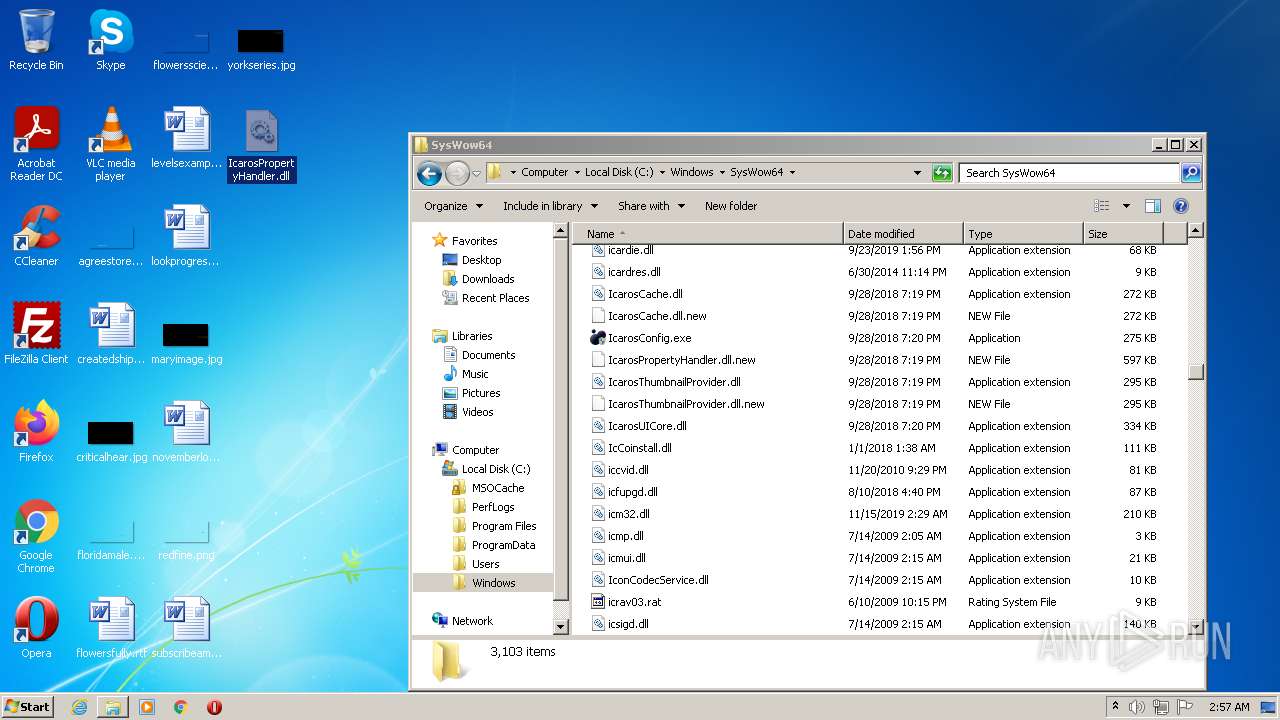
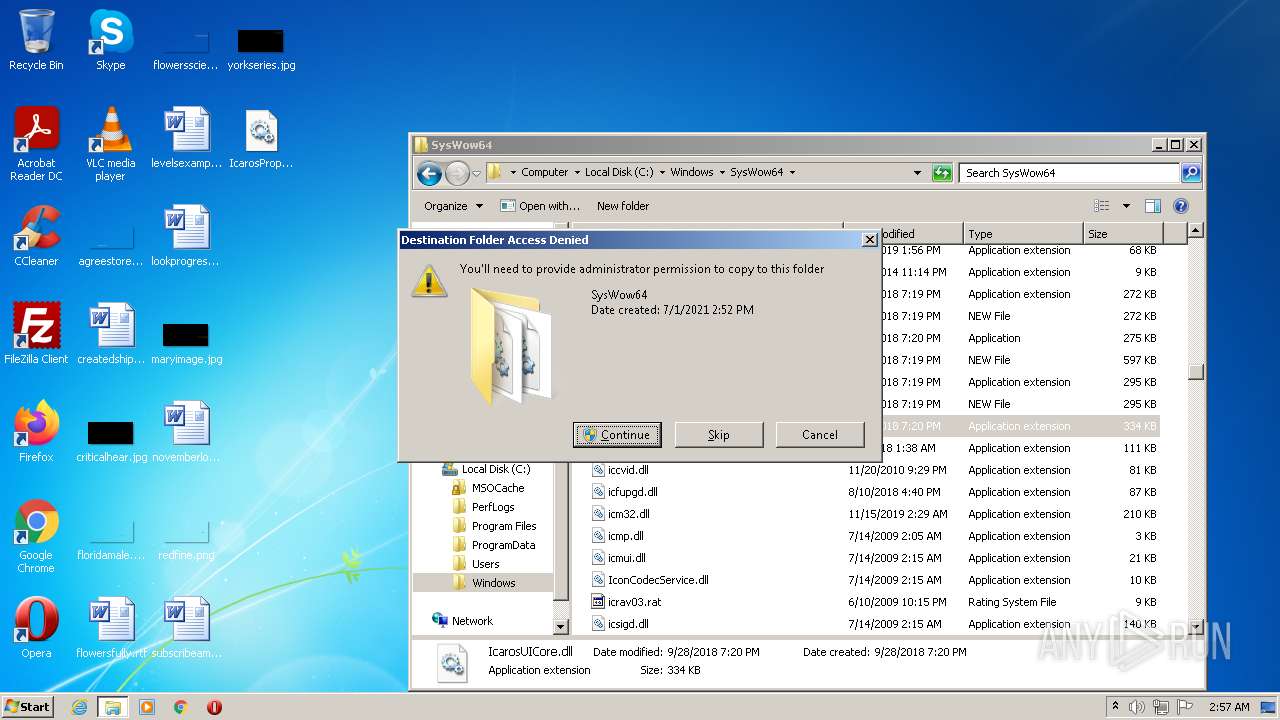
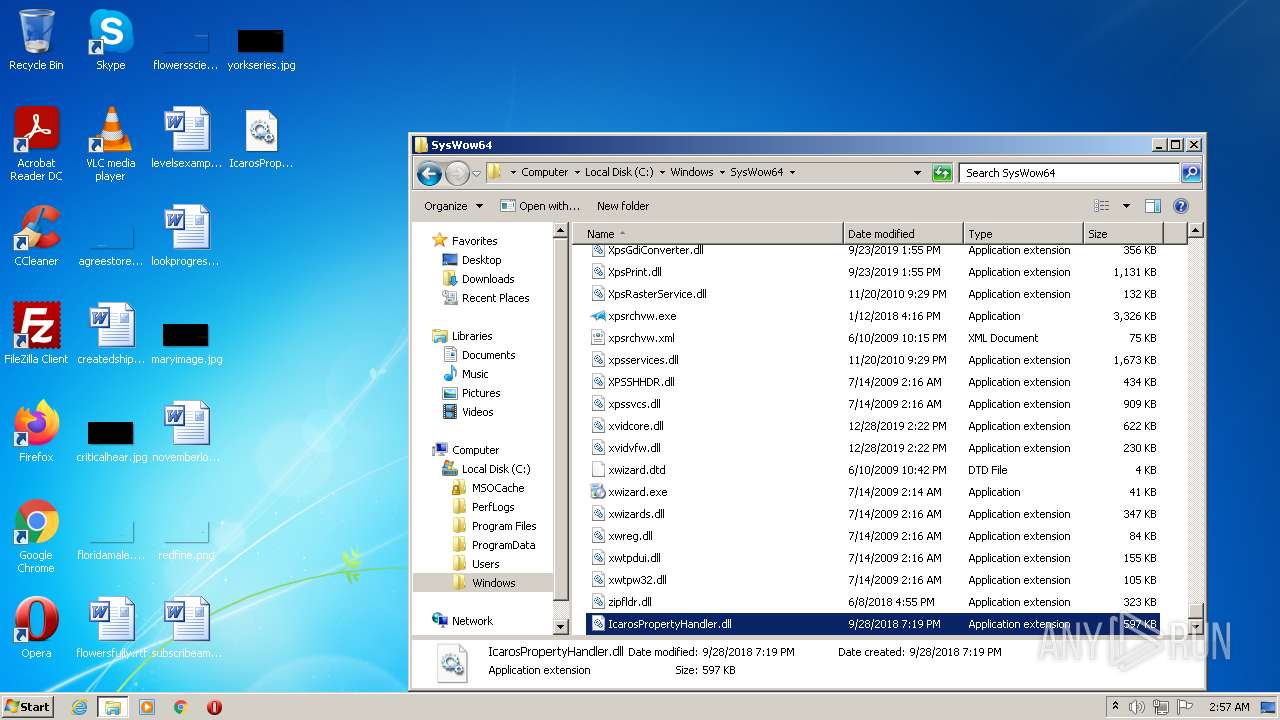
Creates a writable file the system directory
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
- DllHost.exe (PID: 1912)
Writes to the Start menu file
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
Changes the autorun value in the registry
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
SUSPICIOUS
Reads settings of System Certificates
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
Detected use of alternative data streams (AltDS)
- Explorer.EXE (PID: 1084)
Reads the Internet Settings
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
- Regasm.exe (PID: 2780)
- mpc-hc.exe (PID: 3504)
Executable content was dropped or overwritten
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
Creates a software uninstall entry
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
Drops a file with too old compile date
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
Searches for installed software
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
Creates/Modifies COM task schedule object
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
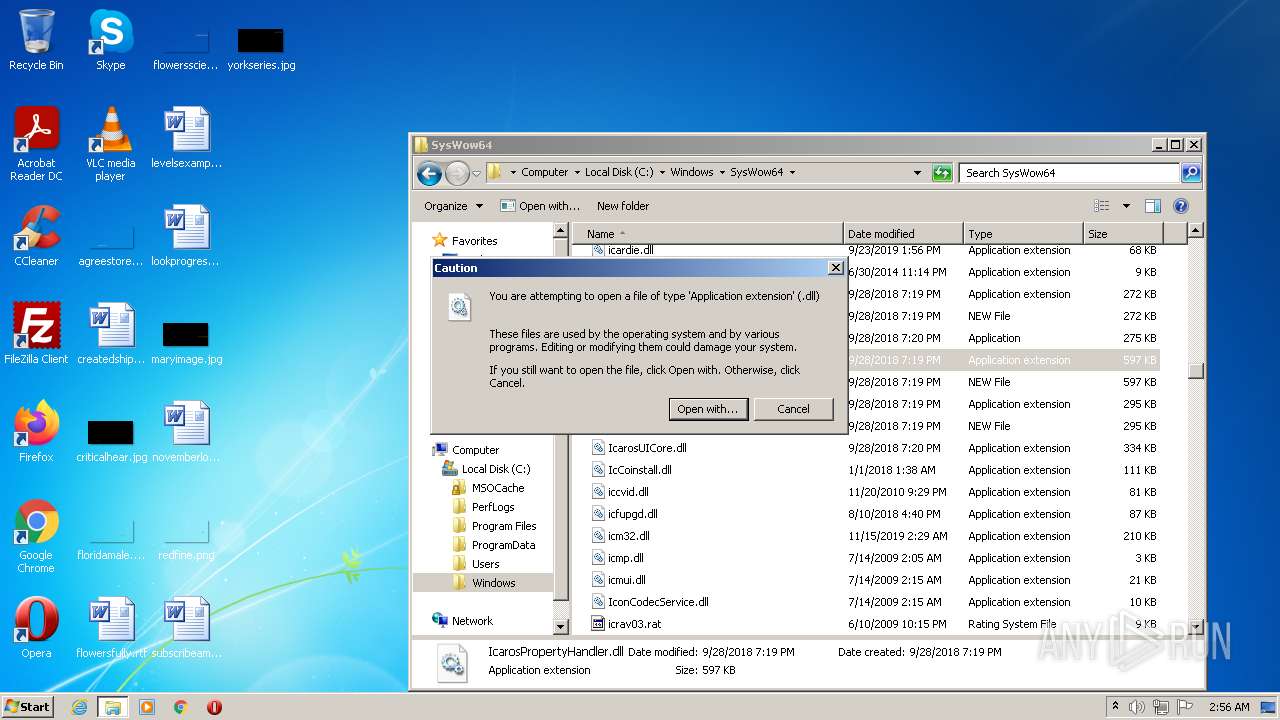
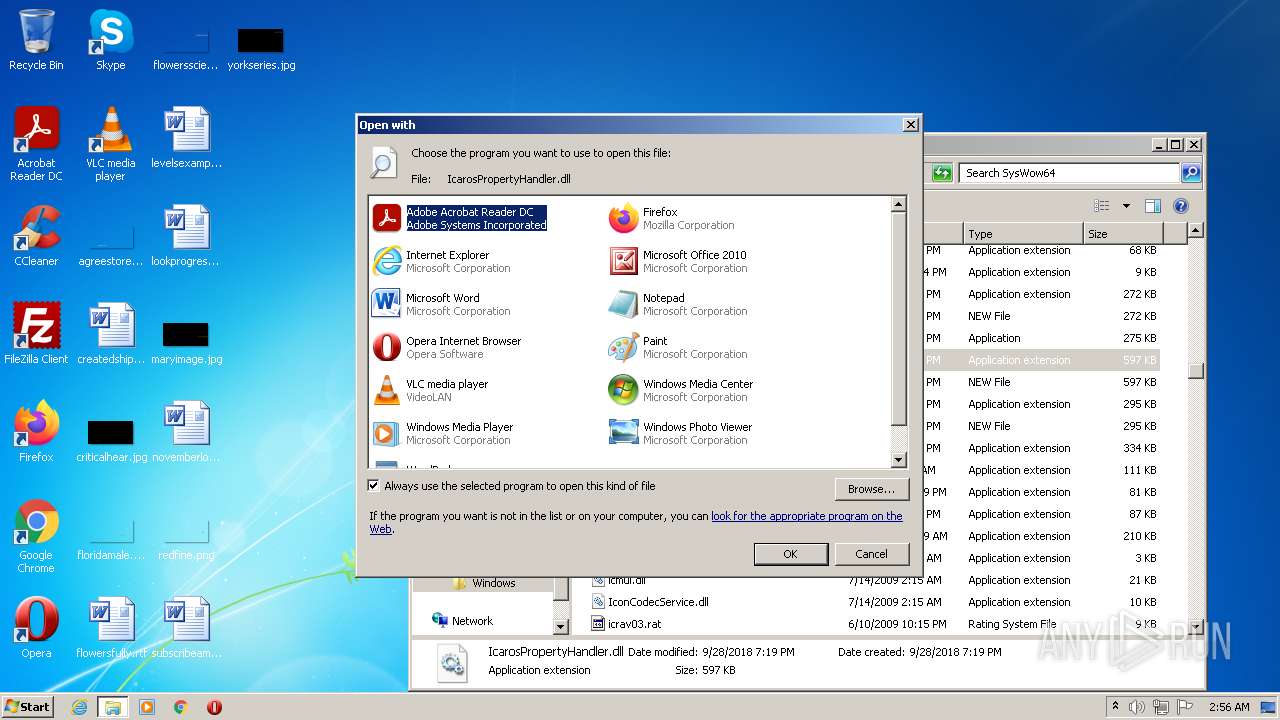
Changes default file association
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
Uses RUNDLL32.EXE to load library
- Explorer.EXE (PID: 1084)
Application launched itself
- Explorer.EXE (PID: 1084)
INFO
Application launched itself
- chrome.exe (PID: 2056)
- chrome.exe (PID: 3740)
Reads Environment values
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
Checks supported languages
- nsF8FB.tmp (PID: 3244)
- nsF979.tmp (PID: 2928)
- SetACL.exe (PID: 3004)
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
- nsFA75.tmp (PID: 120)
- nsF9F7.tmp (PID: 3796)
- SetACL.exe (PID: 2608)
- nsFAF3.tmp (PID: 2148)
- nsFB61.tmp (PID: 2896)
- nsFCCB.tmp (PID: 3052)
- nsFBDF.tmp (PID: 3876)
- nsFC5D.tmp (PID: 2008)
- SetACL.exe (PID: 3380)
- SetACL.exe (PID: 1932)
- nsFD3A.tmp (PID: 3844)
- SetACL.exe (PID: 3536)
- nsFDA8.tmp (PID: 3800)
- SetACL.exe (PID: 3636)
- nsFE17.tmp (PID: 3688)
- nsFF81.tmp (PID: 3600)
- SetACL.exe (PID: 3132)
- nsFE95.tmp (PID: 1832)
- nsFF13.tmp (PID: 2364)
- SetACL.exe (PID: 2296)
- nsFFEF.tmp (PID: 2216)
- Regasm.exe (PID: 2780)
- TrayMenu.exe (PID: 1944)
- ns1C81.tmp (PID: 2836)
- SetACL.exe (PID: 3708)
- ns1D1E.tmp (PID: 952)
- SetACL.exe (PID: 1000)
- ns1D8C.tmp (PID: 860)
- ns1E0A.tmp (PID: 372)
- SetACL.exe (PID: 3124)
- SetACL.exe (PID: 3272)
- ns1E79.tmp (PID: 2060)
- SetACL.exe (PID: 4028)
- ns1EE7.tmp (PID: 3688)
- SetACL.exe (PID: 2772)
- ns1F65.tmp (PID: 1016)
- SetACL.exe (PID: 3248)
- SetACL.exe (PID: 1916)
- ns1FE3.tmp (PID: 3608)
- ns2061.tmp (PID: 3400)
- SetACL.exe (PID: 3488)
- ns20DF.tmp (PID: 3252)
- SetACL.exe (PID: 2072)
- ns223A.tmp (PID: 1024)
- ns22A8.tmp (PID: 3304)
- SetACL.exe (PID: 3832)
- ns215D.tmp (PID: 2052)
- SetACL.exe (PID: 2660)
- ns21CC.tmp (PID: 1772)
- SetACL.exe (PID: 3960)
- SetACL.exe (PID: 1764)
- ns2385.tmp (PID: 3244)
- SetACL.exe (PID: 3780)
- ns2471.tmp (PID: 1812)
- ns2403.tmp (PID: 3784)
- SetACL.exe (PID: 3068)
- SetACL.exe (PID: 2608)
- SetACL.exe (PID: 1396)
- ns2317.tmp (PID: 3648)
- ns24EF.tmp (PID: 876)
- SetACL.exe (PID: 2300)
- ns255E.tmp (PID: 2400)
- SetACL.exe (PID: 3692)
- ns25CC.tmp (PID: 1396)
- SetACL.exe (PID: 2012)
- SetACL.exe (PID: 1528)
- ns2737.tmp (PID: 3068)
- SetACL.exe (PID: 124)
- SetACL.exe (PID: 1820)
- ns27A5.tmp (PID: 3640)
- ns2823.tmp (PID: 3080)
- SetACL.exe (PID: 2080)
- SetACL.exe (PID: 2160)
- ns264A.tmp (PID: 1660)
- ns26B9.tmp (PID: 3680)
- ns2891.tmp (PID: 1384)
- SetACL.exe (PID: 3876)
- SetACL.exe (PID: 2332)
- ns2900.tmp (PID: 3668)
- SetACL.exe (PID: 3448)
- ns296E.tmp (PID: 2024)
- ns29EC.tmp (PID: 2792)
- ns2A6A.tmp (PID: 1472)
- SetACL.exe (PID: 2572)
- SetACL.exe (PID: 3600)
- ns2B66.tmp (PID: 2140)
- SetACL.exe (PID: 1400)
- ns2BD4.tmp (PID: 3456)
- SetACL.exe (PID: 2872)
- SetACL.exe (PID: 3676)
- ns2C43.tmp (PID: 2968)
- SetACL.exe (PID: 3224)
- ns2AE8.tmp (PID: 928)
- SetACL.exe (PID: 1328)
- ns2D3F.tmp (PID: 2596)
- SetACL.exe (PID: 1752)
- ns2DAD.tmp (PID: 3540)
- SetACL.exe (PID: 2732)
- ns2E2B.tmp (PID: 1600)
- SetACL.exe (PID: 3304)
- ns2E9A.tmp (PID: 632)
- SetACL.exe (PID: 1916)
- ns2CC1.tmp (PID: 2676)
- ns2F08.tmp (PID: 2312)
- ns2F96.tmp (PID: 3736)
- SetACL.exe (PID: 3832)
- ns3004.tmp (PID: 556)
- SetACL.exe (PID: 1812)
- ns3082.tmp (PID: 3092)
- SetACL.exe (PID: 2520)
- ns30F0.tmp (PID: 2456)
- SetACL.exe (PID: 3220)
- SetACL.exe (PID: 2936)
- ns315F.tmp (PID: 3632)
- SetACL.exe (PID: 3148)
- SetACL.exe (PID: 3804)
- SetACL.exe (PID: 3504)
- ns323B.tmp (PID: 2936)
- ns3328.tmp (PID: 588)
- SetACL.exe (PID: 1244)
- SetACL.exe (PID: 2964)
- ns31CD.tmp (PID: 3944)
- ns32B9.tmp (PID: 3784)
- ns3396.tmp (PID: 876)
- SetACL.exe (PID: 3316)
- mpc-hc.exe (PID: 3504)
Starts application with an unusual extension
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
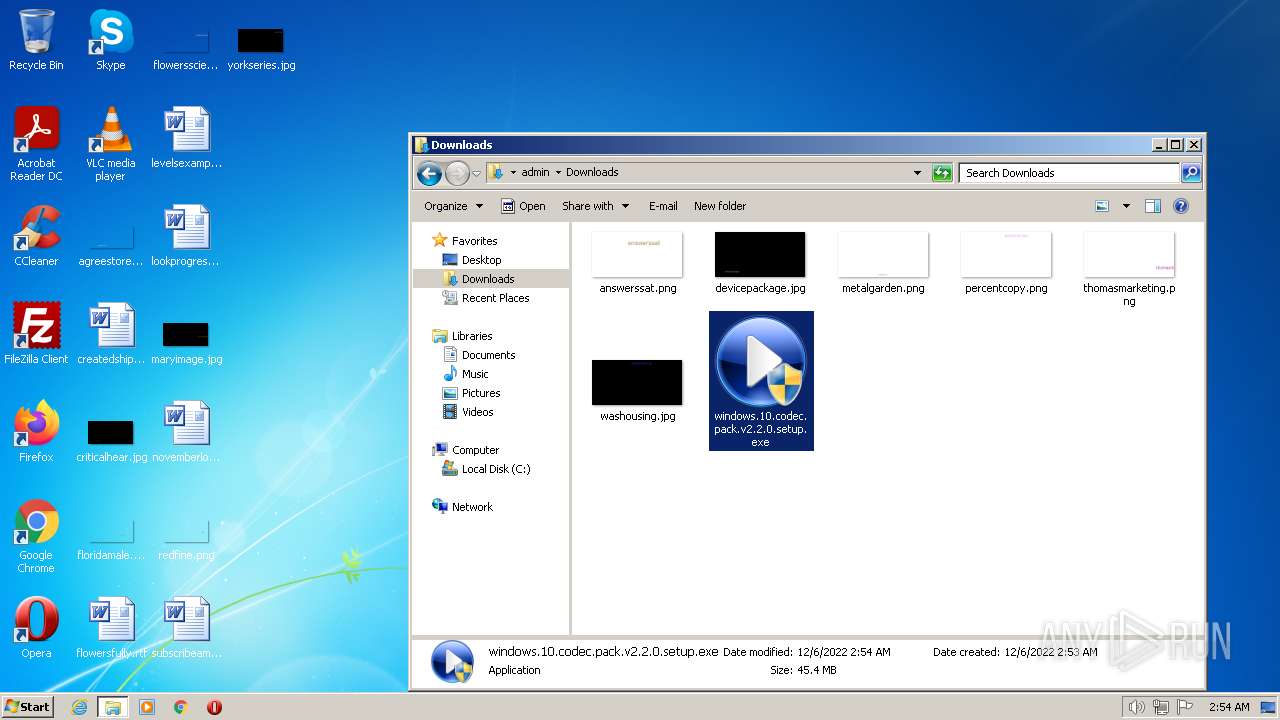
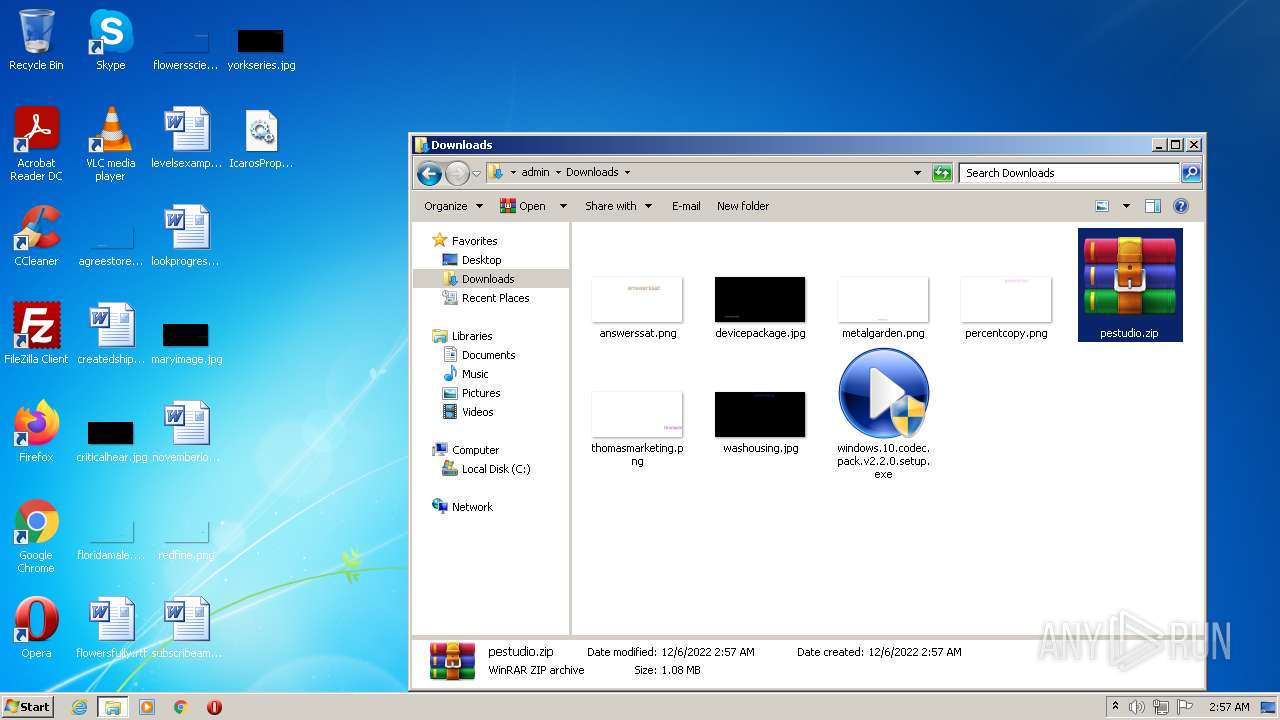
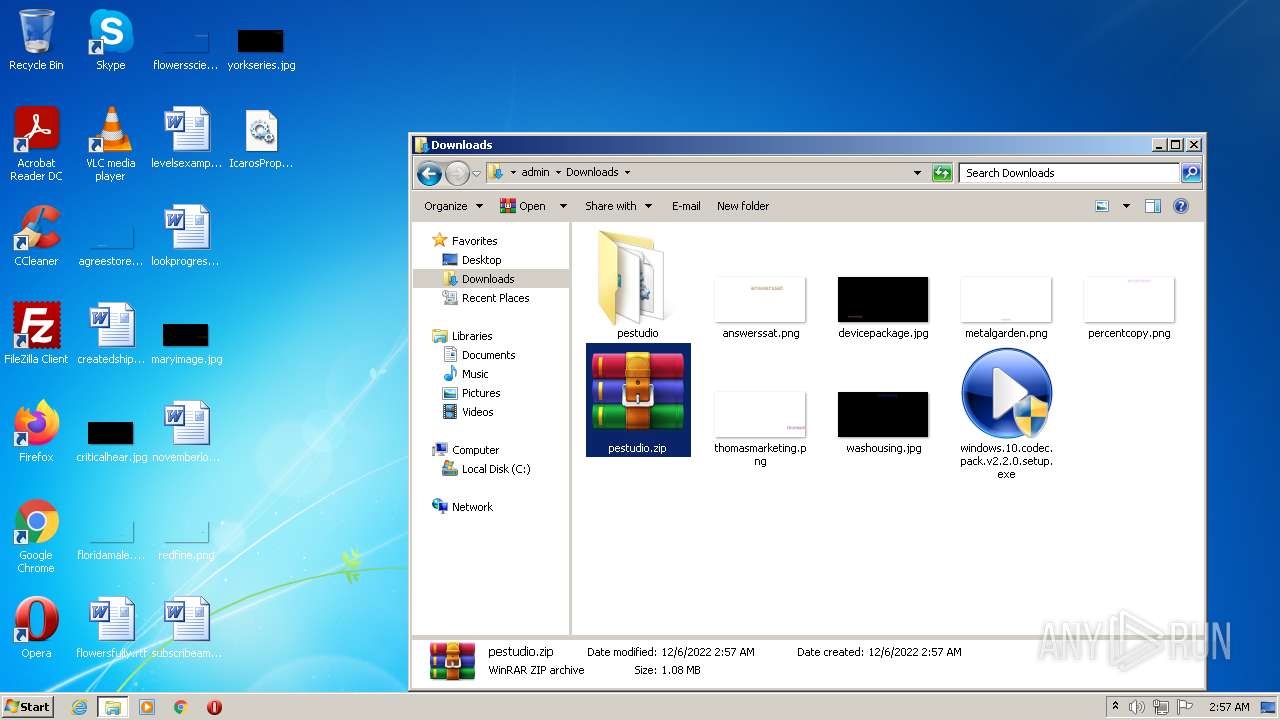
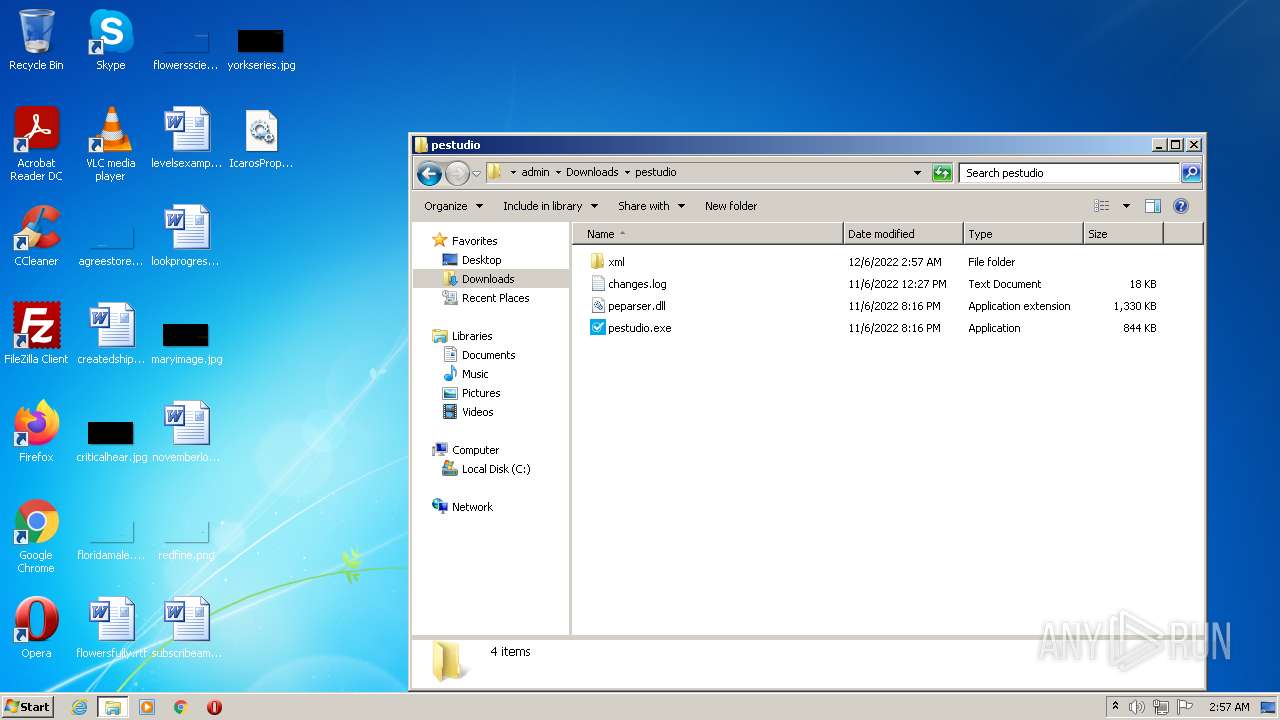
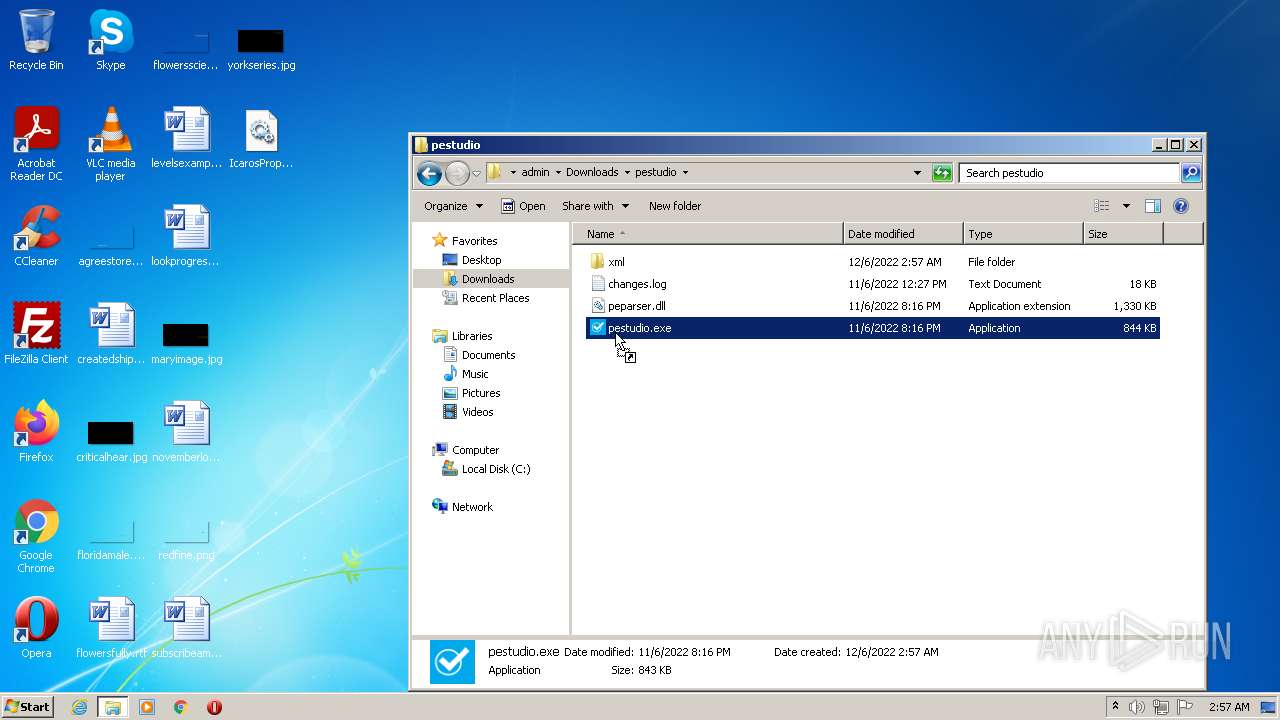
Manual execution by a user
- explorer.exe (PID: 1796)
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 2544)
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
Reads the computer name
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
- SetACL.exe (PID: 3004)
- SetACL.exe (PID: 2608)
- SetACL.exe (PID: 3380)
- SetACL.exe (PID: 1932)
- SetACL.exe (PID: 3536)
- SetACL.exe (PID: 3636)
- SetACL.exe (PID: 2296)
- SetACL.exe (PID: 3132)
- Regasm.exe (PID: 2780)
- SetACL.exe (PID: 3708)
- SetACL.exe (PID: 1000)
- SetACL.exe (PID: 3272)
- SetACL.exe (PID: 4028)
- SetACL.exe (PID: 3124)
- SetACL.exe (PID: 2772)
- SetACL.exe (PID: 3248)
- SetACL.exe (PID: 1916)
- SetACL.exe (PID: 3488)
- SetACL.exe (PID: 3960)
- SetACL.exe (PID: 2072)
- SetACL.exe (PID: 3832)
- SetACL.exe (PID: 2660)
- SetACL.exe (PID: 1764)
- SetACL.exe (PID: 3780)
- SetACL.exe (PID: 3068)
- SetACL.exe (PID: 1396)
- SetACL.exe (PID: 2300)
- SetACL.exe (PID: 3692)
- SetACL.exe (PID: 2160)
- SetACL.exe (PID: 2608)
- SetACL.exe (PID: 124)
- SetACL.exe (PID: 1820)
- SetACL.exe (PID: 2080)
- SetACL.exe (PID: 2012)
- SetACL.exe (PID: 1528)
- SetACL.exe (PID: 3876)
- SetACL.exe (PID: 3448)
- SetACL.exe (PID: 2332)
- SetACL.exe (PID: 2572)
- SetACL.exe (PID: 3600)
- SetACL.exe (PID: 1400)
- SetACL.exe (PID: 2872)
- SetACL.exe (PID: 3676)
- SetACL.exe (PID: 3224)
- SetACL.exe (PID: 2732)
- SetACL.exe (PID: 1328)
- SetACL.exe (PID: 1752)
- SetACL.exe (PID: 3304)
- SetACL.exe (PID: 1916)
- SetACL.exe (PID: 2936)
- SetACL.exe (PID: 3832)
- SetACL.exe (PID: 1812)
- SetACL.exe (PID: 2520)
- SetACL.exe (PID: 3220)
- SetACL.exe (PID: 3148)
- SetACL.exe (PID: 3504)
- SetACL.exe (PID: 1244)
- SetACL.exe (PID: 2964)
- SetACL.exe (PID: 3804)
- SetACL.exe (PID: 3316)
- mpc-hc.exe (PID: 3504)
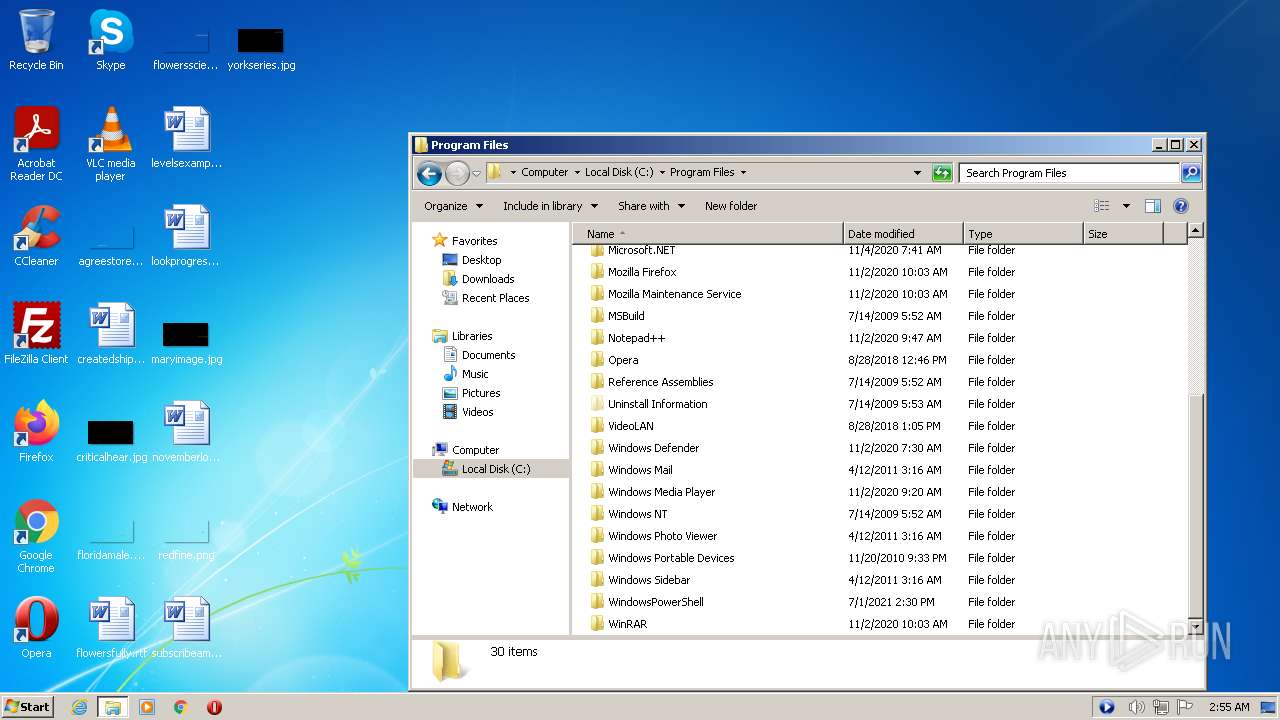
Creates files in the program directory
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
Drops a file that was compiled in debug mode
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
Reads CPU info
- windows.10.codec.pack.v2.2.0.setup.exe (PID: 3308)
Checks transactions between databases Windows and Oracle
- Explorer.EXE (PID: 1084)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3740)
Checks proxy server information
- mpc-hc.exe (PID: 3504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
305
Monitored processes
185
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\nsFA75.tmp" "C:\Windows\system32\Codecs\SetACL.exe" MACHINE\SOFTWARE\Classes\MediaFoundation\MediaSources\Preferred /registry /grant S-1-5-32-544 /full /r:cont_obj /sid /silent | C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\nsFA75.tmp | — | windows.10.codec.pack.v2.2.0.setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 3 Modules
| |||||||||||||||
| 124 | C:\Windows\system32\Codecs\SetACL.exe -on HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectShow\Preferred -ot reg -actn ace -ace n:S-1-5-32-544;s:y;p:read -silent | C:\Windows\system32\Codecs\SetACL.exe | — | ns2737.tmp | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 0 Version: 3.0.6.0 Modules
| |||||||||||||||
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,6514088662931445458,12024778434633522598,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1024 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 372 | "C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\ns1E0A.tmp" C:\Windows\system32\Codecs\SetACL.exe -on HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MediaFoundation\MediaSources\DoNotUse -ot reg -actn ace -ace n:S-1-5-32-544;s:y;p:full -silent | C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\ns1E0A.tmp | — | windows.10.codec.pack.v2.2.0.setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 556 | "C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\ns3004.tmp" C:\Windows\system32\Codecs\SetACL.exe -on "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Foundation\ByteStreamHandlers\.m4v" -ot reg -actn setowner -ownr n:S-1-5-80-956008885-3418522649-1831038044-1853292631-2271478464;s:y -silent | C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\ns3004.tmp | — | windows.10.codec.pack.v2.2.0.setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 588 | "C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\ns3328.tmp" C:\Windows\system32\Codecs\SetACL.exe -on "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Foundation\ByteStreamHandlers\.mp4v" -ot reg -actn ace -ace n:S-1-5-80-956008885-3418522649-1831038044-1853292631-2271478464;s:y;p:full -silent | C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\ns3328.tmp | — | windows.10.codec.pack.v2.2.0.setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 25 Modules
| |||||||||||||||
| 632 | "C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\ns2E9A.tmp" C:\Windows\system32\Codecs\SetACL.exe -on "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Foundation\ByteStreamHandlers\.m4a" -ot reg -actn setowner -ownr n:S-1-5-80-956008885-3418522649-1831038044-1853292631-2271478464;s:y -silent | C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\ns2E9A.tmp | — | windows.10.codec.pack.v2.2.0.setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,2493241228483067563,6911261494295617624,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3932 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 860 | "C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\ns1D8C.tmp" C:\Windows\system32\Codecs\SetACL.exe -on HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MediaFoundation\MediaSources\DoNotUse -ot reg -actn setowner -ownr n:S-1-5-32-544;s:y -silent | C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\ns1D8C.tmp | — | windows.10.codec.pack.v2.2.0.setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 876 | "C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\ns24EF.tmp" C:\Windows\system32\Codecs\SetACL.exe -on HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MediaFoundation\MediaSources\DoNotUse -ot reg -actn ace -ace n:S-1-5-32-544;s:y;p:full -silent | C:\Users\admin\AppData\Local\Temp\nsm986A.tmp\ns24EF.tmp | — | windows.10.codec.pack.v2.2.0.setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
53 191
Read events
46 828
Write events
6 348
Delete events
15
Modification events
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
327
Suspicious files
205
Text files
274
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-638EAEA2-808.pma | — | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2b1529fb-e1e7-4b79-9ac4-96677c9b327c.tmp | text | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e072e810-748e-4dc1-9f80-70e9d9b31a93.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF106fa92.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF1070129.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF106f8fb.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RF106fd70.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 2272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF106f90b.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
36
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2440 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
2440 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?1a3cdbb77afe116e | US | compressed | 61.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2140 | chrome.exe | 142.250.186.109:443 | accounts.google.com | GOOGLE | US | whitelisted |
2140 | chrome.exe | 142.250.186.174:443 | clients2.google.com | GOOGLE | US | whitelisted |
2140 | chrome.exe | 142.250.184.227:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
3308 | windows.10.codec.pack.v2.2.0.setup.exe | 18.66.92.163:443 | d3j6hg32mwjrha.cloudfront.net | — | US | unknown |
2140 | chrome.exe | 51.195.149.65:443 | www.windows10codecpack.com | OVH SAS | FR | suspicious |
2140 | chrome.exe | 142.250.186.142:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
2440 | chrome.exe | 142.250.185.68:443 | www.google.com | GOOGLE | US | whitelisted |
3308 | windows.10.codec.pack.v2.2.0.setup.exe | 18.65.40.204:443 | d2cp8mgeqj97lj.cloudfront.net | AMAZON-02 | US | unknown |
2440 | chrome.exe | 216.58.212.174:443 | clients2.google.com | GOOGLE | US | whitelisted |
2440 | chrome.exe | 142.250.186.109:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.windows10codecpack.com |
| suspicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
d3j6hg32mwjrha.cloudfront.net |
| whitelisted |
d2cp8mgeqj97lj.cloudfront.net |
| whitelisted |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |