| File name: | Dism.exe |
| Full analysis: | https://app.any.run/tasks/ce081ae6-a843-4f97-92af-ffbb6bea7358 |
| Verdict: | Malicious activity |
| Analysis date: | May 31, 2019, 01:07:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6343B2B8428435803D24BDDE28FFDA84 |
| SHA1: | FA06B9EA1EA9F147E8F2FC2C23AEFA19C62383B6 |
| SHA256: | 948B72B42AF7B04DF658A4A670926EAF95B5C5DA5EC670E8388BA6F500FA46CE |
| SSDEEP: | 98304:NZjuPQSeJAn8T5SF0KnBaiZMLkENoQp70iYBAS5V:L8dn8lG0MIietMAS5 |
MALICIOUS
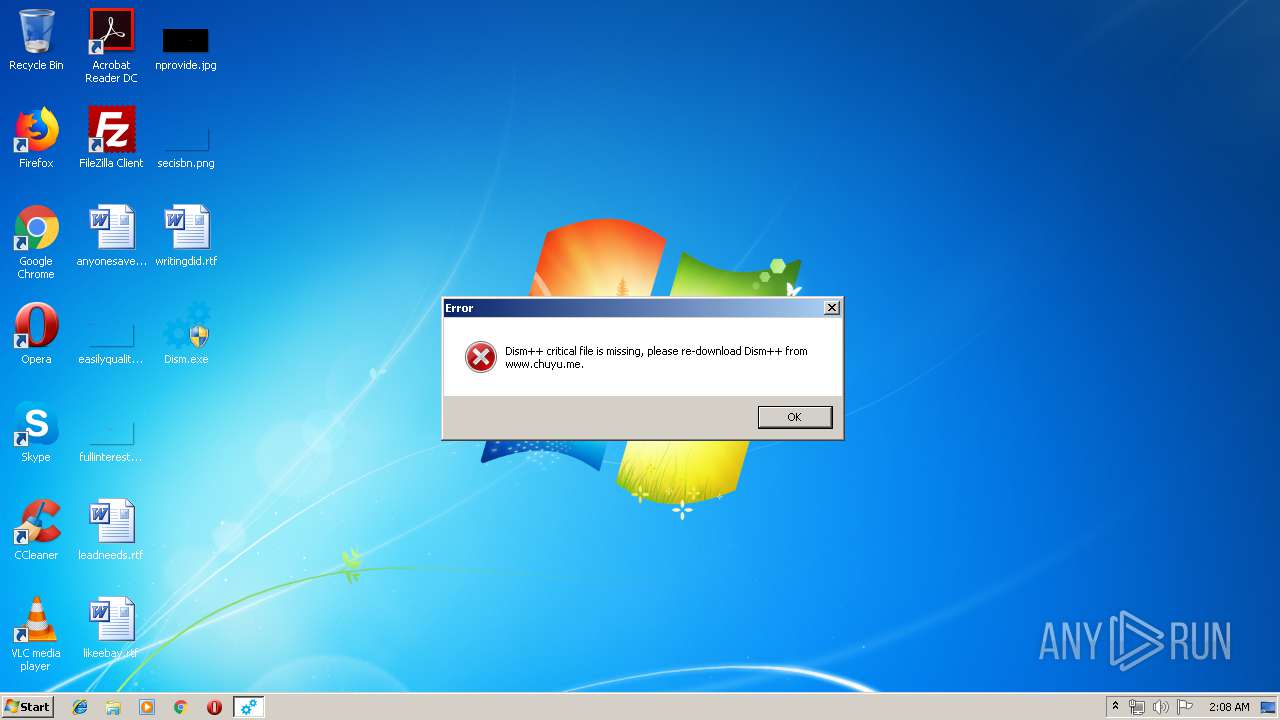
Application was dropped or rewritten from another process
- Dism++x86.exe (PID: 3072)
- run.exe (PID: 1876)
- Dism++x86.exe (PID: 2276)
Loads dropped or rewritten executable
- Dism++x86.exe (PID: 3072)
- Dism++x86.exe (PID: 2276)
SUSPICIOUS
Executable content was dropped or overwritten
- Dism.exe (PID: 2596)
- run.exe (PID: 1876)
Checks supported languages
- Dism++x86.exe (PID: 3072)
Checks Windows language
- Dism++x86.exe (PID: 3072)
Creates files in the user directory
- Dism++x86.exe (PID: 3072)
Application launched itself
- Dism++x86.exe (PID: 3072)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 107520 |
| InitializedDataSize: | 52224 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a238 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
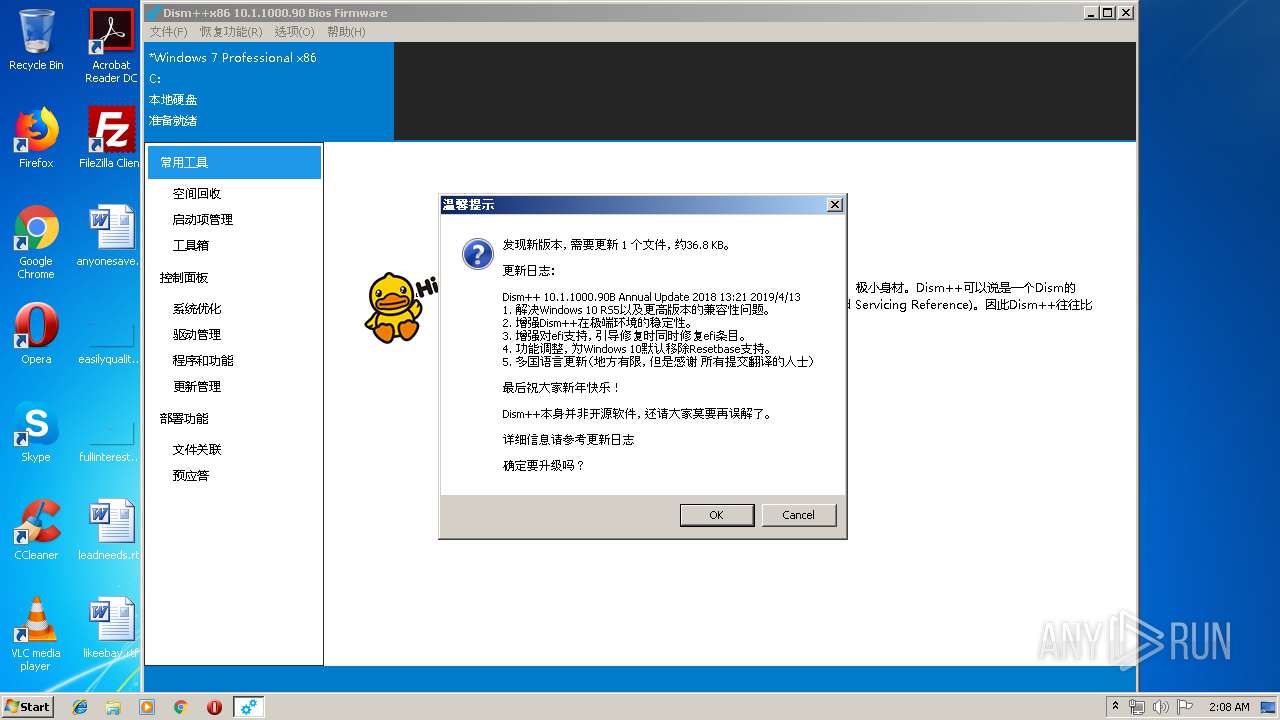
| FileVersionNumber: | 10.1.1000.90 |
| ProductVersionNumber: | 10.1.1000.90 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
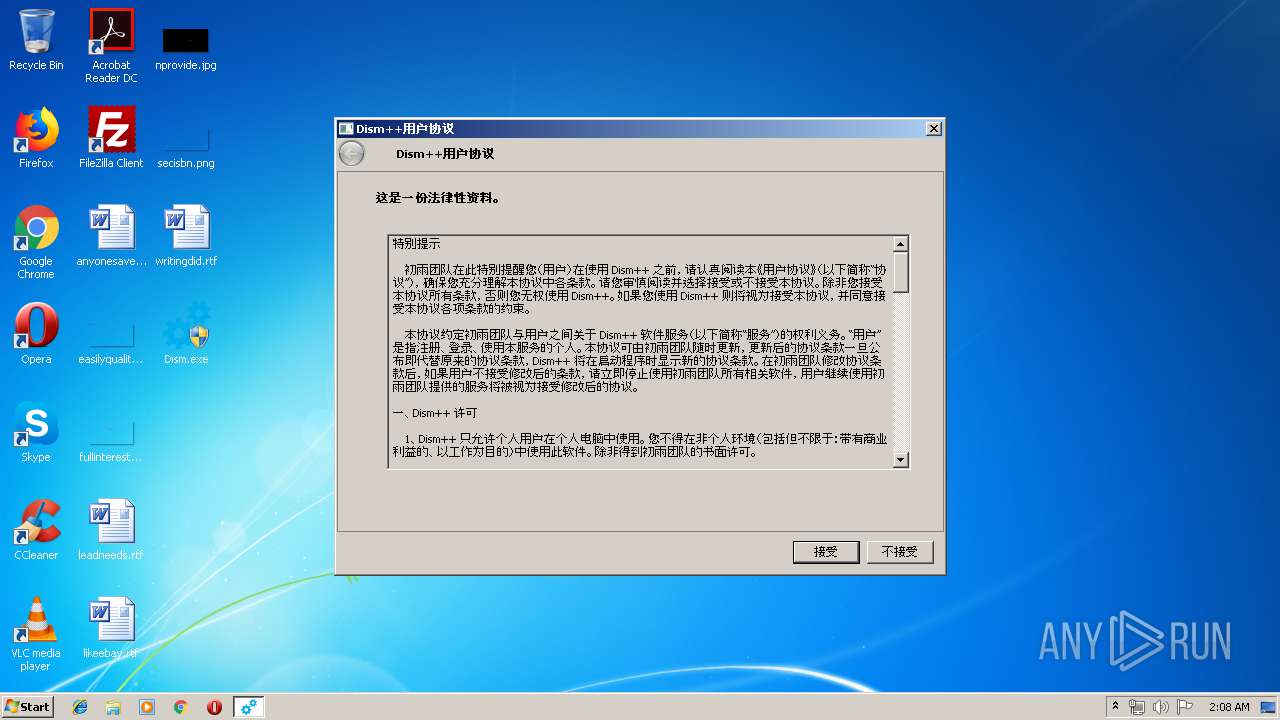
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 10.1.1000.90 |
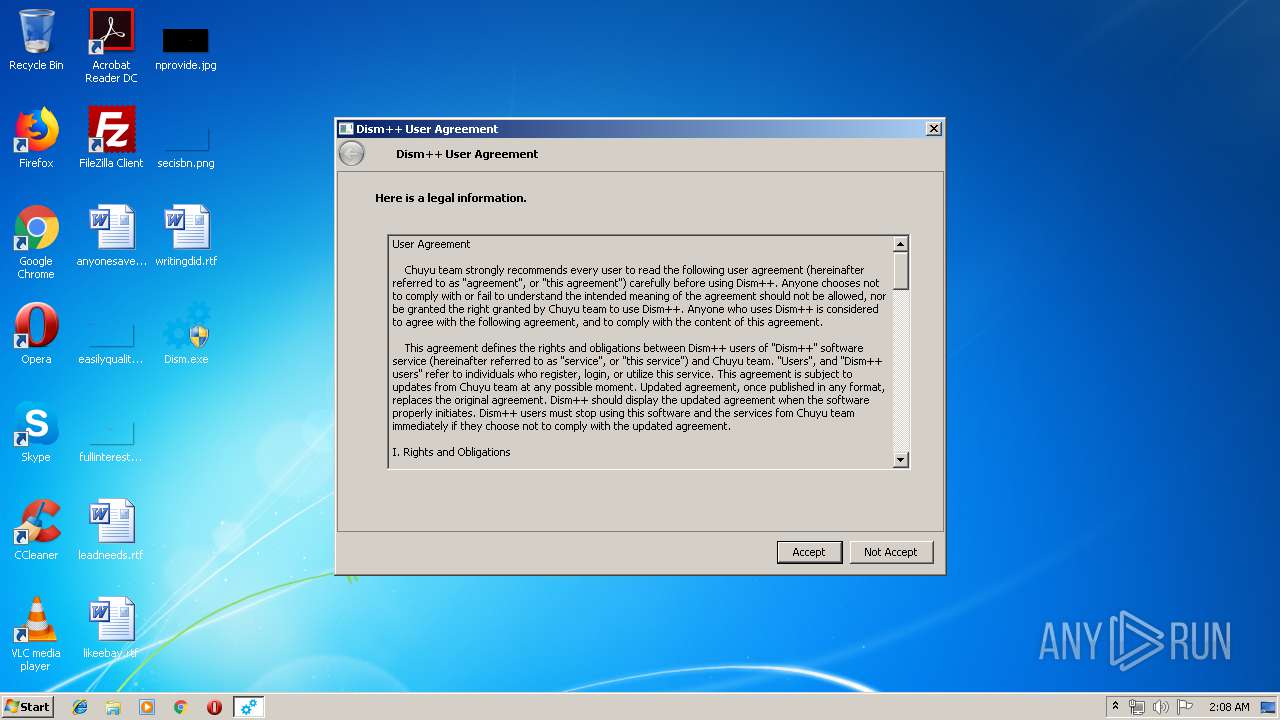
| Comments: | Chuyu Team |
| ProductVersion: | 10.1.1000.90 |
| LegalCopyright: | Chuyu. All rights reserved. |
| OriginalFileName: | Dism++.exe |
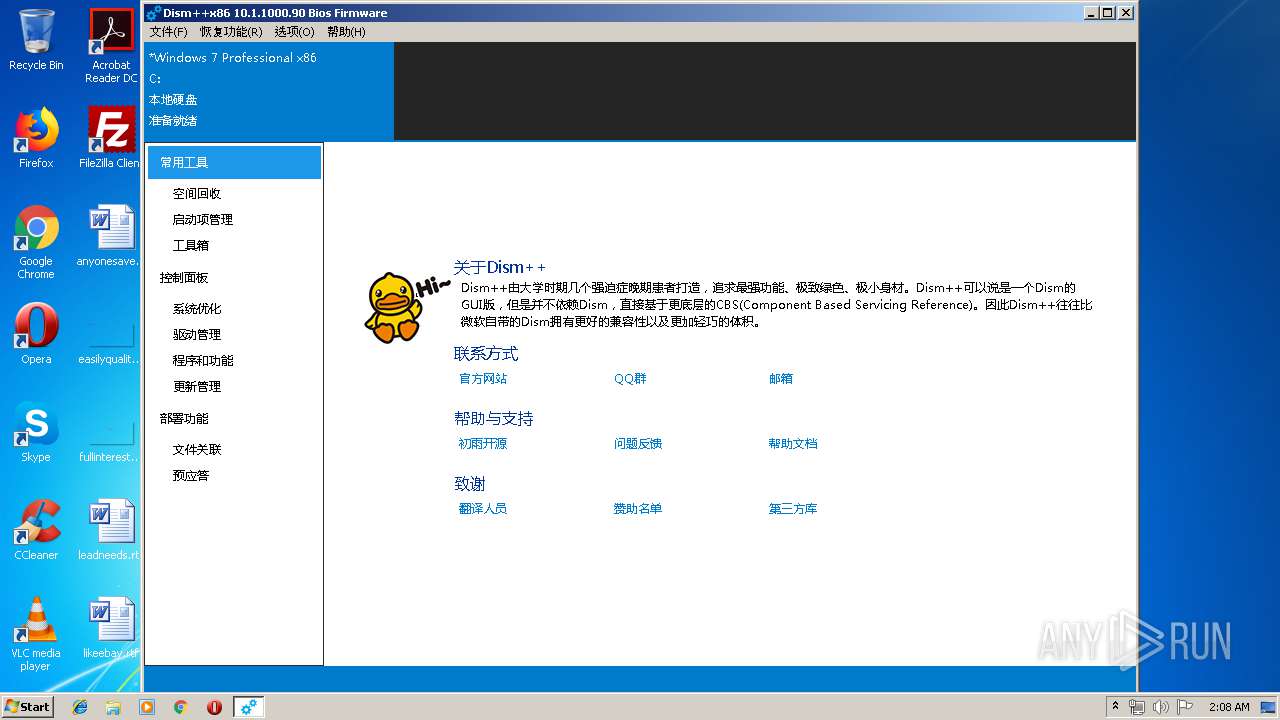
| ProductName: | Dism++ |
| InternalName: | Dism++.exe |
| FileDescription: | Dism++主程序 |
| CompanyName: | Chuyu Team |
| FCompiler: | D |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| FileVersion: | 10.1.1000.90 |
| Comments: | Chuyu Team |
| FileDescription: | Dism++主程序 |
| ProductVersion: | 10.1.1000.90 |
| LegalCopyright: | Chuyu. All rights reserved. |
| OriginalFilename: | Dism++.exe |
| ProductName: | Dism++ |
| InternalName: | Dism++.exe |
| CompanyName: | Chuyu Team |
| 编译工具: | AuMFCompiler(标准版) |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0001A3B0 | 0x0001A400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5068 |
DATA | 0x0001C000 | 0x00000D1C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43817 |
BSS | 0x0001D000 | 0x00A01E05 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00A1F000 | 0x00000EC4 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.63423 |
.tls | 0x00A20000 | 0x0000000C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00A21000 | 0x00000025 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.406078 |
.reloc | 0x00A22000 | 0x00001E0C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00A24000 | 0x0000AAF4 | 0x0000AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.93439 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.72869 | 420 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 2.30093 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 0.976578 | 1384 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 3.57235 | 1128 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 2.86599 | 744 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
6 | 1.65565 | 2216 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 2.97358 | 4264 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
8 | 2.66607 | 1640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
9 | 1.85548 | 3752 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
10 | 2.63546 | 9640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
40
Monitored processes
5
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1876 | "C:\Users\admin\AppData\Local\Temp\~sfx0074E4D1BE\run.exe" | C:\Users\admin\AppData\Local\Temp\~sfx0074E4D1BE\run.exe | Dism.exe | ||||||||||||
User: admin Company: Chuyu Team Integrity Level: HIGH Description: Dism++主程序 Exit code: 0 Version: 10.1.1000.90 Modules
| |||||||||||||||
| 2276 | "C:\_Dism_Temp\Dism++x86.exe" /Update | C:\_Dism_Temp\Dism++x86.exe | — | Dism++x86.exe | |||||||||||
User: admin Company: Chuyu Team Integrity Level: HIGH Description: Dism++主程序 Exit code: 0 Version: 10.1.1000.90 Modules
| |||||||||||||||
| 2596 | "C:\Users\admin\Desktop\Dism.exe" | C:\Users\admin\Desktop\Dism.exe | explorer.exe | ||||||||||||
User: admin Company: Chuyu Team Integrity Level: HIGH Description: Dism++主程序 Exit code: 0 Version: 10.1.1000.90 Modules
| |||||||||||||||
| 3072 | C:\\_Dism_Temp\Dism++x86.exe | C:\_Dism_Temp\Dism++x86.exe | run.exe | ||||||||||||
User: admin Company: Chuyu Team Integrity Level: HIGH Description: Dism++主程序 Exit code: 0 Version: 10.1.1000.90 Modules
| |||||||||||||||
| 3744 | "C:\Users\admin\Desktop\Dism.exe" | C:\Users\admin\Desktop\Dism.exe | — | explorer.exe | |||||||||||
User: admin Company: Chuyu Team Integrity Level: MEDIUM Description: Dism++主程序 Exit code: 3221226540 Version: 10.1.1000.90 Modules
| |||||||||||||||
Total events
448
Read events
426
Write events
22
Delete events
0
Modification events
| (PID) Process: | (2596) Dism.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2596) Dism.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3072) Dism++x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Dism++x86_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3072) Dism++x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Dism++x86_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3072) Dism++x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Dism++x86_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3072) Dism++x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Dism++x86_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3072) Dism++x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Dism++x86_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3072) Dism++x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Dism++x86_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3072) Dism++x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Dism++x86_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3072) Dism++x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Dism++x86_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
33
Suspicious files
8
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2596 | Dism.exe | C:\Users\admin\AppData\Local\Temp\~sfx0074E4D1BE\Config\amd64\bcdboot.exe | executable | |
MD5:BE14BE7C8F7F0F4E397B89979CB9CF6B | SHA256:309F3ECCB0093CC6CC98F858BD3CE67B00BB810728FFB177B7BD287FB3C92B97 | |||
| 2596 | Dism.exe | C:\Users\admin\AppData\Local\Temp\~sfx0074E4D1BE\Config\x86\bcdboot.exe | executable | |
MD5:805A3ACFB09848CE0255D20F7B993313 | SHA256:0B85157E004EE59CFE054AD5BDA6D8A9C3E3270D002BEFB07CDDC6ACB7497388 | |||
| 1876 | run.exe | C:\Users\admin\AppData\Local\Temp\aut9FB.tmp | — | |
MD5:— | SHA256:— | |||
| 1876 | run.exe | C:\Users\admin\AppData\Local\Temp\1876phzyfnt | — | |
MD5:— | SHA256:— | |||
| 2596 | Dism.exe | C:\Users\admin\AppData\Local\Temp\~sfx0074E4D1BE\Config\x86\NCleaner.dll | executable | |
MD5:5E6AD60DD9CF1154FE548EC36D0E1AC3 | SHA256:B597507F0C90C8AA97756E7170FF4E790454FA853CB666B5718E1B38994A0480 | |||
| 2596 | Dism.exe | C:\Users\admin\AppData\Local\Temp\~sfx0074E4D1BE\Config\Languages\zh-Hans.zip | compressed | |
MD5:A4FA2B5A0F9BC8DA19549442AAA0D62D | SHA256:B6CFCE094BF429022F08E22C8F93ACCAC526FFB289EEDC713A70B306C2B78A94 | |||
| 2596 | Dism.exe | C:\Users\admin\AppData\Local\Temp\~sfx0074E4D1BE\Config\amd64\CBSHost.dll | executable | |
MD5:4890CB628DC84C1888102BB467646A4F | SHA256:77D8CB87EE991EDC73B944E7FE9528D2B5F57D2BC0AF165D5B932E907FB575BC | |||
| 2596 | Dism.exe | C:\Users\admin\AppData\Local\Temp\~sfx0074E4D1BE\Config\amd64\wimgapi.dll | executable | |
MD5:379C96D981D4794AD2D55EDDCF572C51 | SHA256:CCA556A7A442C4B354CA028DDC2E2A70655BBDF197A4B998DE7F058A61B6F25E | |||
| 2596 | Dism.exe | C:\Users\admin\AppData\Local\Temp\~sfx0074E4D1BE\Config\default.ui.zip | compressed | |
MD5:E4B7BEF45A8F48832BA59396509DCB76 | SHA256:1A90365AC33C37EEAE4DD712F84062466C10948CF5B567574055E0B8B0F70534 | |||
| 2596 | Dism.exe | C:\Users\admin\AppData\Local\Temp\~sfx0074E4D1BE\Config\Plugins\FrogPlugins_Pcn7FMvReAsVWfCQBfRJCw\Plugin.amd64.dll | executable | |
MD5:DB9E0F558CE60C5067BA356DA47E8E66 | SHA256:4AEDE63CE9AAFC391A8703995C98F98389EF277D53BCC5C54CF55F3B49FCCB6B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3072 | Dism++x86.exe | GET | 206 | 162.159.209.91:80 | http://cdn.chuyu.me/files/Config_Languages_en.zip_2019-01-12..zip | unknown | compressed | 36.8 Kb | shared |
3072 | Dism++x86.exe | POST | 200 | 119.188.131.130:80 | http://web1612151818153.bj01.bdysite.com/chuyu-analysis/client_update.php | CN | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3072 | Dism++x86.exe | 119.188.131.130:80 | web1612151818153.bj01.bdysite.com | CHINA UNICOM China169 Backbone | CN | malicious |
3072 | Dism++x86.exe | 162.159.209.91:80 | cdn.chuyu.me | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
web1612151818153.bj01.bdysite.com |
| malicious |
cdn.chuyu.me |
| unknown |