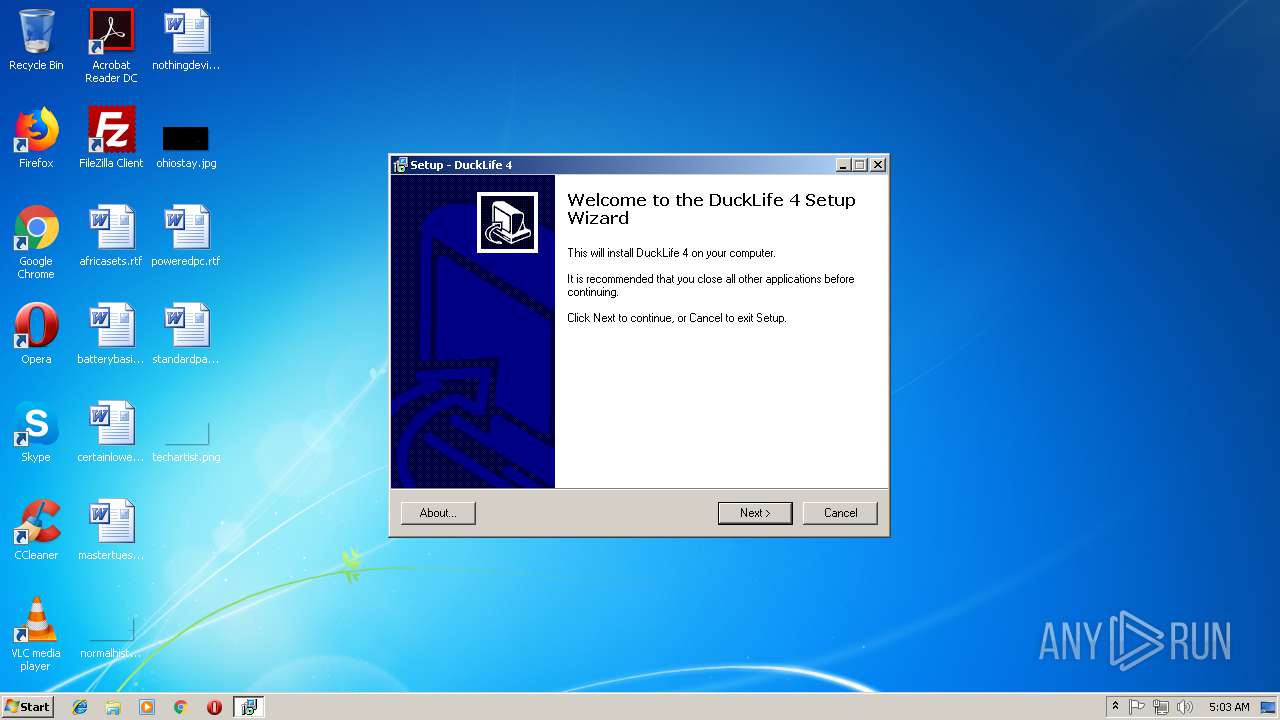
| File name: | duckLife-4.exe |
| Full analysis: | https://app.any.run/tasks/3b4710cf-1d1e-4269-bff2-fa8d80057b63 |
| Verdict: | Malicious activity |
| Analysis date: | October 11, 2018, 04:02:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A1A9DC9DF2426A9A485C3A62909E2E82 |
| SHA1: | 6878E3D0323631B36D5D3E659CE75266F3503A3C |
| SHA256: | 948620A761F4DB57DE345D8394F621E2D239E0A88826418EE5451089CF3FCEFD |
| SSDEEP: | 196608:tD2UNUn90oV0cClV0fjJzG9AXw0Y5SOJTCfdEcNzGnk:8UOn9vXK0rJzWmY5FTClEc1D |
MALICIOUS
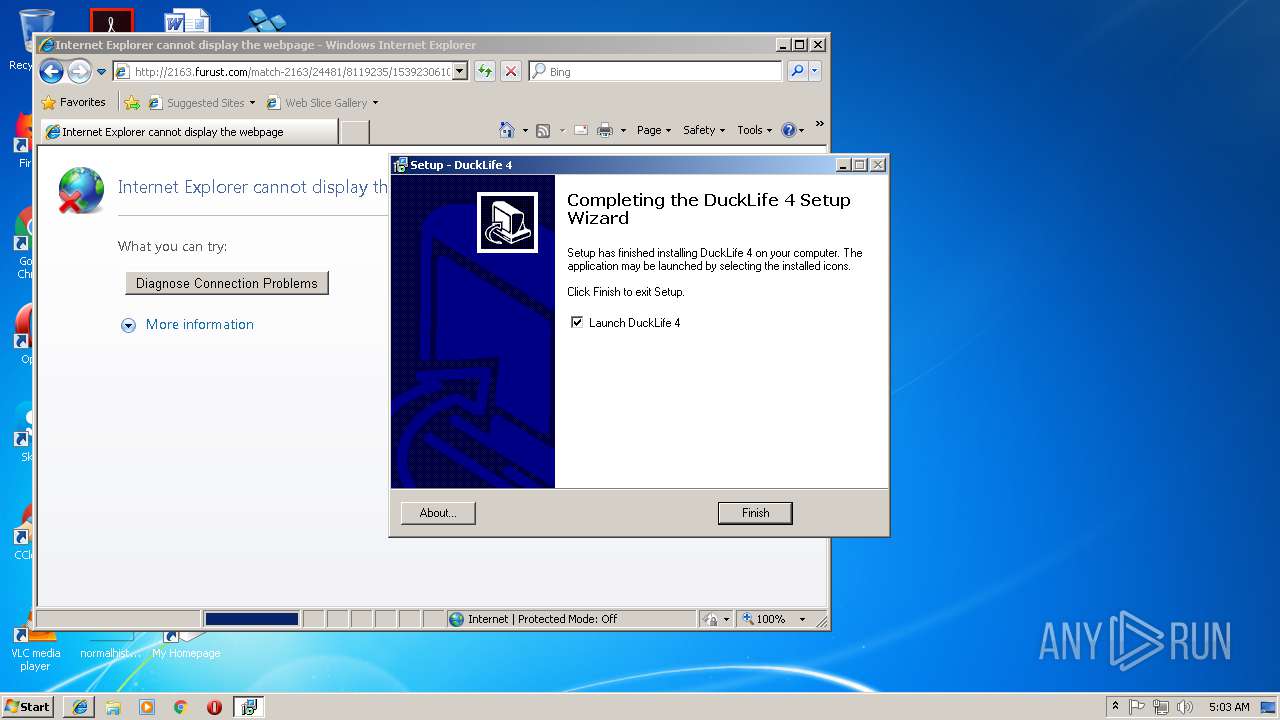
Connects to CnC server
- iexplore.exe (PID: 2084)
- iexplore.exe (PID: 476)
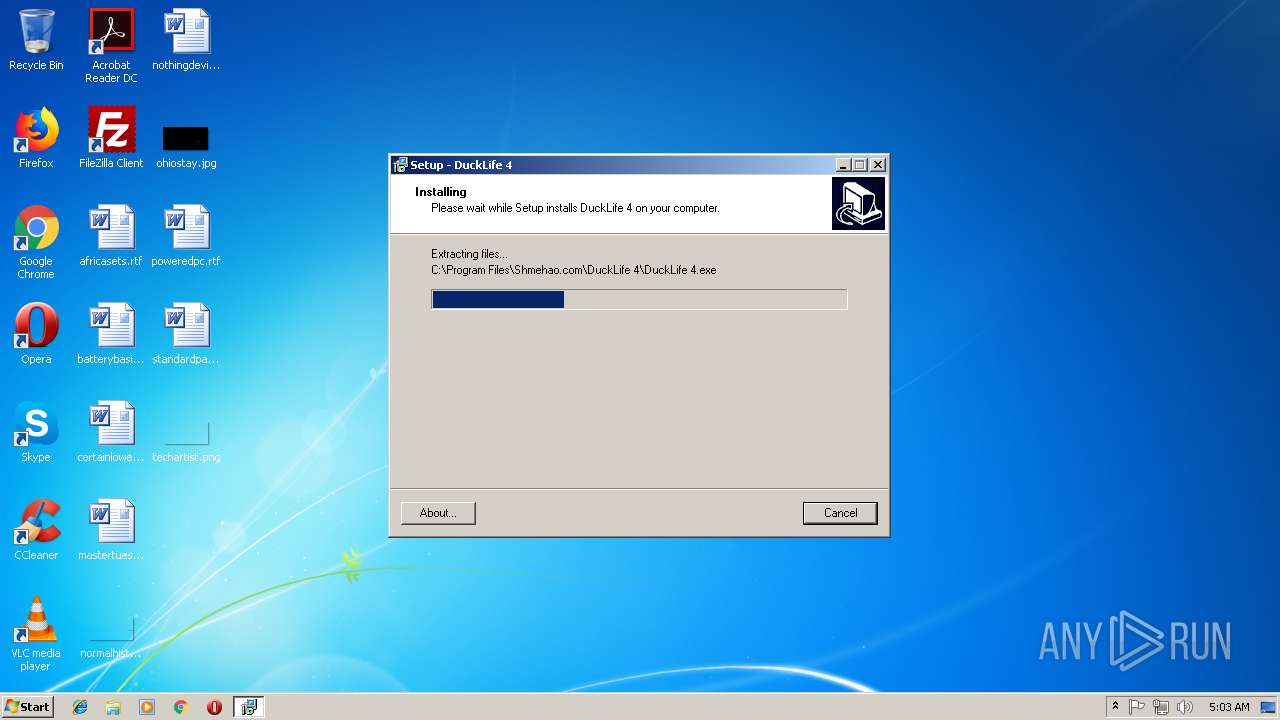
Application was dropped or rewritten from another process
- DuckLife 4.exe (PID: 1488)
SUSPICIOUS
Executable content was dropped or overwritten
- duckLife-4.exe (PID: 3464)
- duckLife-4.exe (PID: 2208)
- duckLife-4.tmp (PID: 3748)
Creates files in the user directory
- DuckLife 4.exe (PID: 1488)
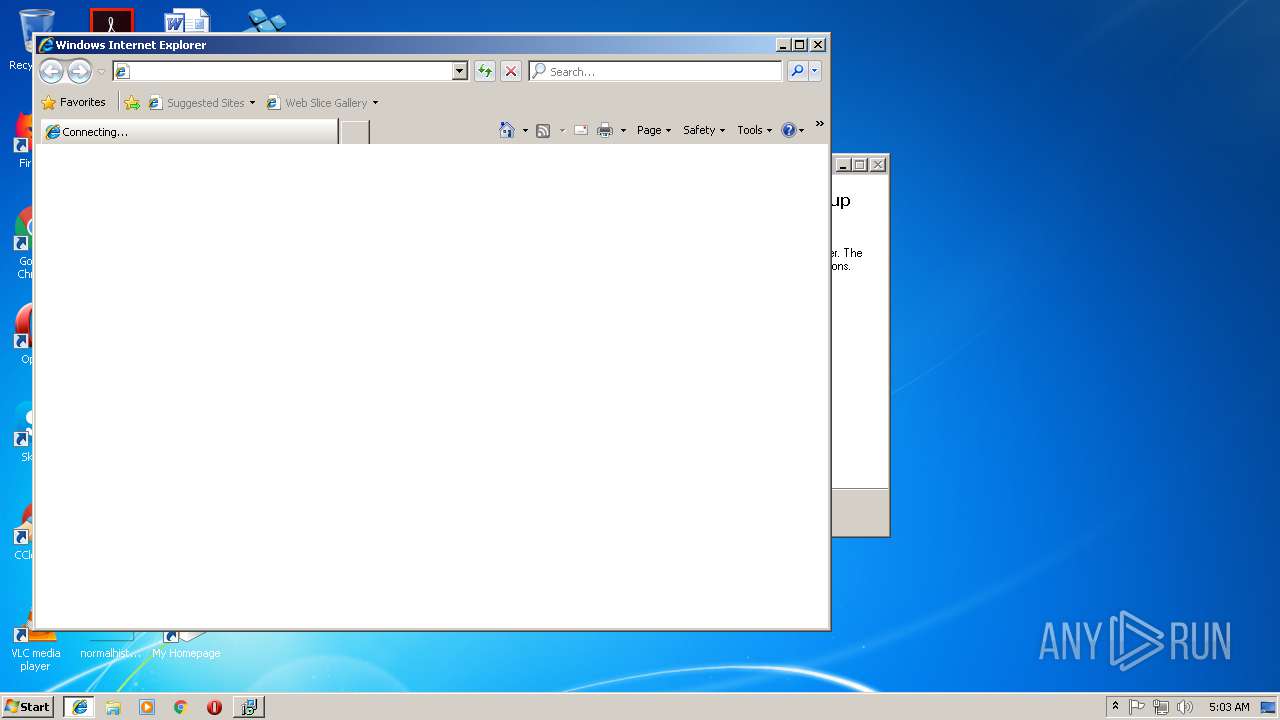
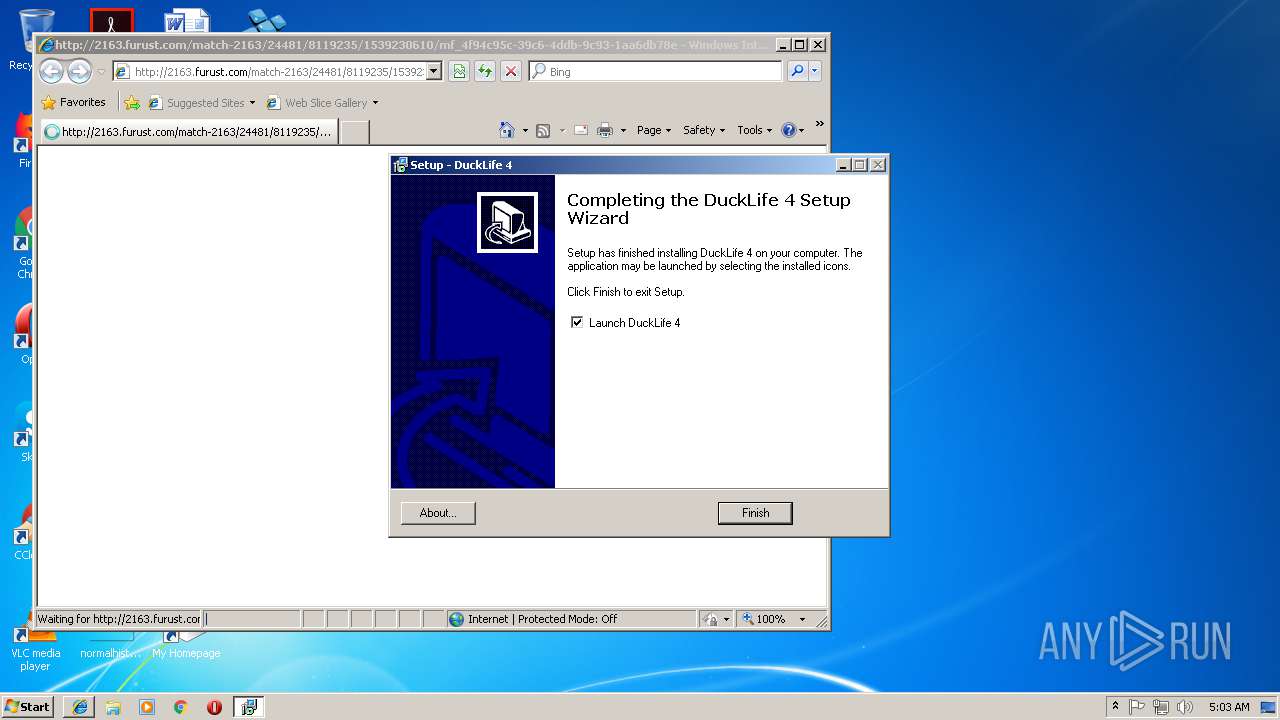
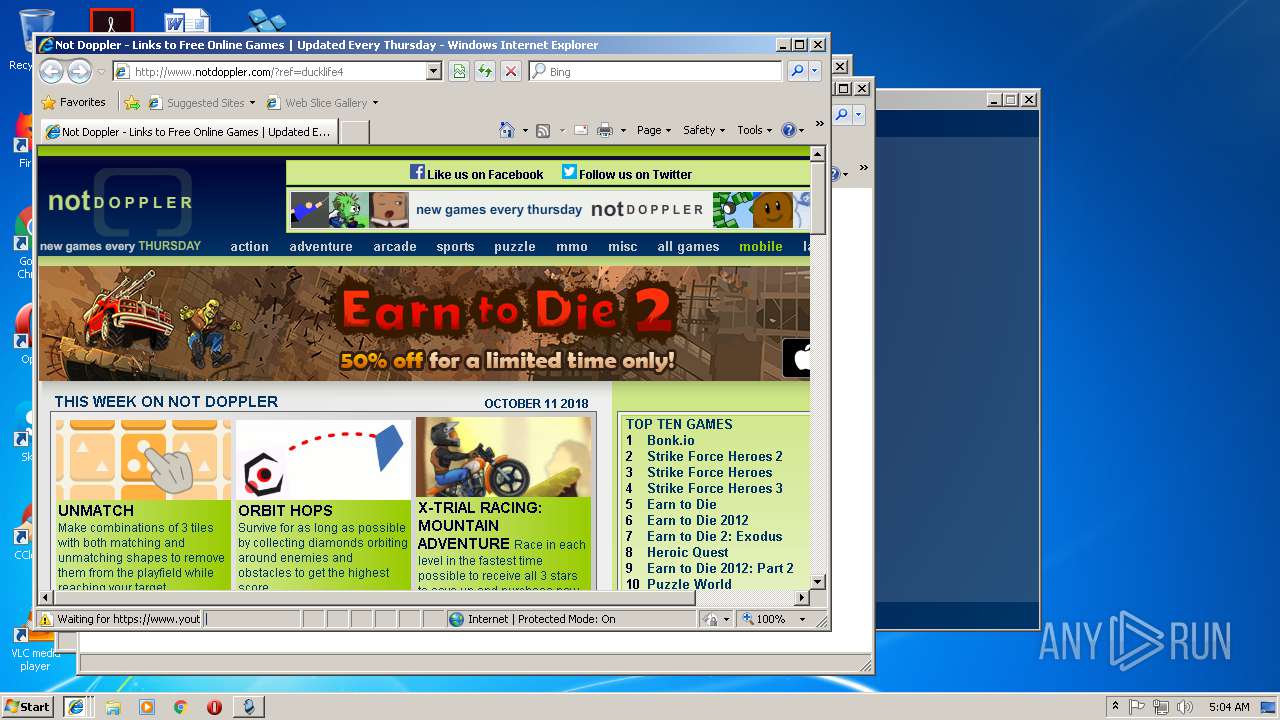
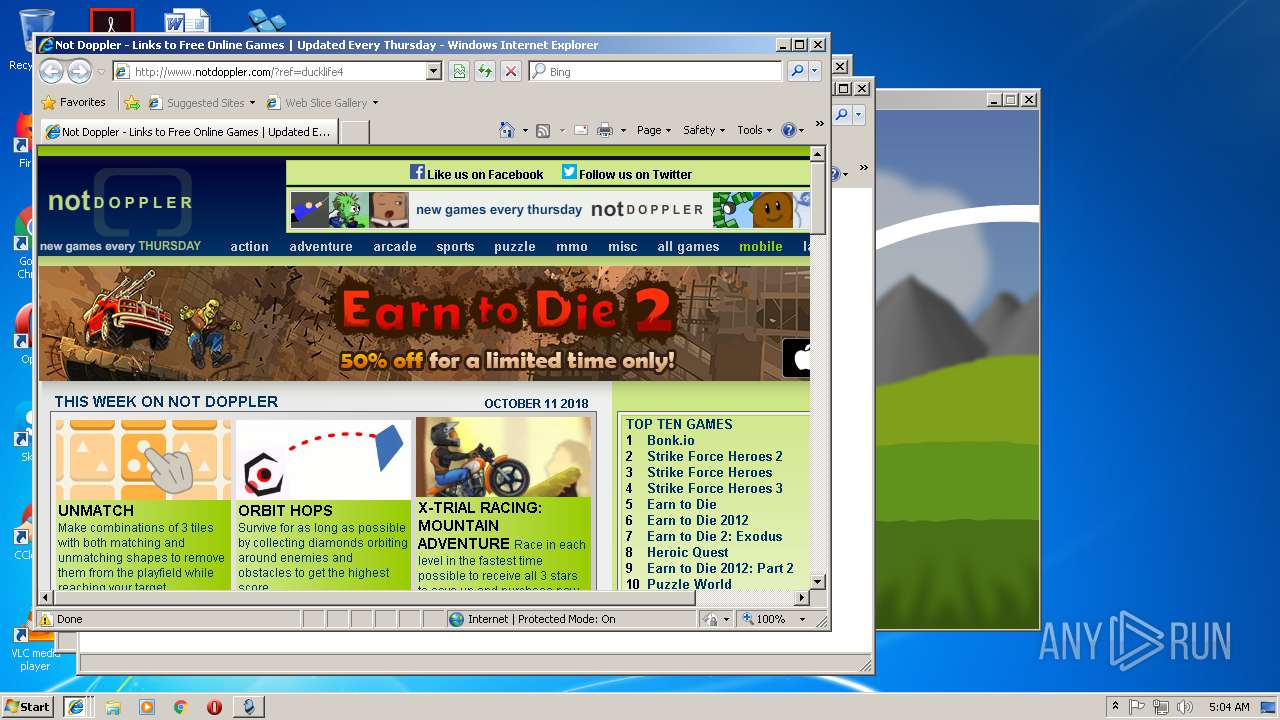
Starts Internet Explorer
- DuckLife 4.exe (PID: 1488)
- duckLife-4.tmp (PID: 3748)
INFO
Application was dropped or rewritten from another process
- duckLife-4.tmp (PID: 1412)
- duckLife-4.tmp (PID: 3748)
Reads Internet Cache Settings
- iexplore.exe (PID: 2084)
- iexplore.exe (PID: 1256)
- iexplore.exe (PID: 2660)
- iexplore.exe (PID: 476)
- iexplore.exe (PID: 2760)
- iexplore.exe (PID: 2956)
Loads dropped or rewritten executable
- duckLife-4.tmp (PID: 3748)
Creates a software uninstall entry
- duckLife-4.tmp (PID: 3748)
Application launched itself
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 1724)
- iexplore.exe (PID: 3192)
- iexplore.exe (PID: 4064)
- iexplore.exe (PID: 2968)
Creates files in the program directory
- duckLife-4.tmp (PID: 3748)
Creates files in the user directory
- iexplore.exe (PID: 2084)
- iexplore.exe (PID: 2660)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3572)
- iexplore.exe (PID: 3192)
- iexplore.exe (PID: 476)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2084)
Changes internet zones settings
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 3192)
- iexplore.exe (PID: 4064)
- iexplore.exe (PID: 1724)
- iexplore.exe (PID: 2968)
Reads internet explorer settings
- iexplore.exe (PID: 2084)
- iexplore.exe (PID: 2660)
- iexplore.exe (PID: 476)
Changes settings of System certificates
- iexplore.exe (PID: 2084)
Reads settings of System Certificates
- iexplore.exe (PID: 3192)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9b24 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
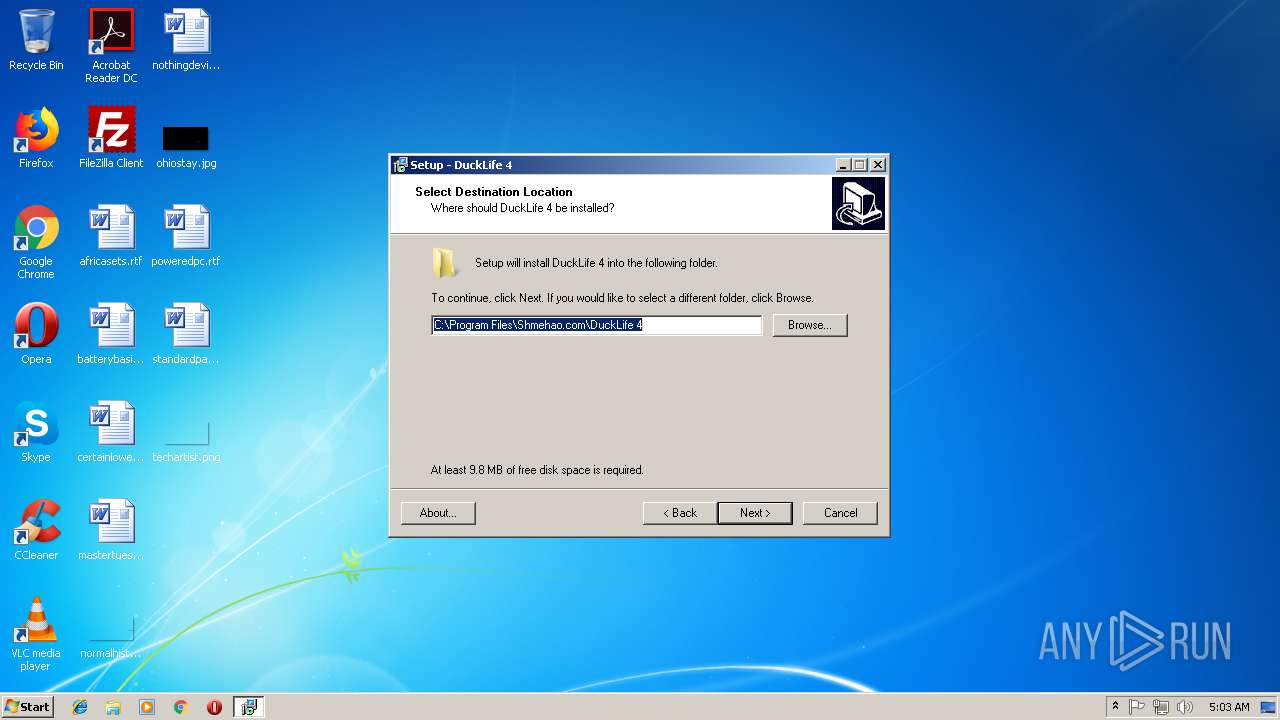
| CompanyName: | Shmehao.com |
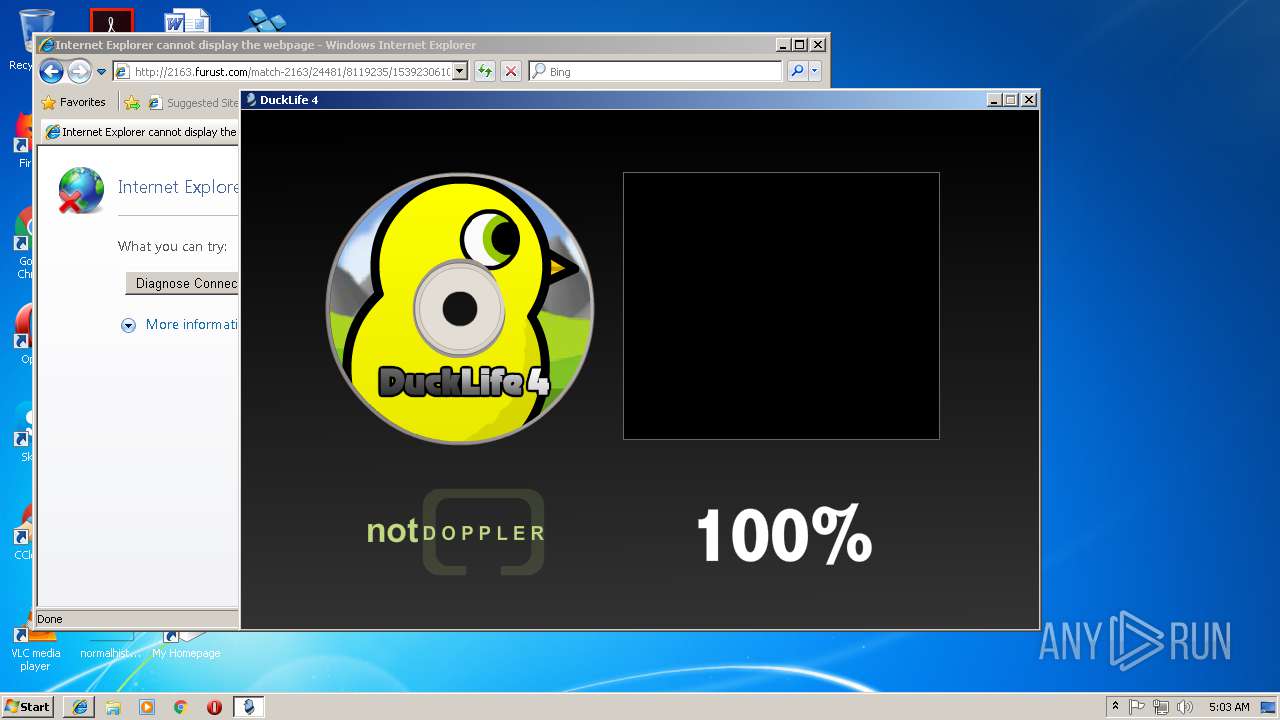
| FileDescription: | DuckLife 4 Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | DuckLife 4 |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Shmehao.com |
| FileDescription: | DuckLife 4 Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | DuckLife 4 |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009244 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53087 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.73544 |
BSS | 0x0000C000 | 0x00000E4C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00002C00 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.45713 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05007 | 1376 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
55
Monitored processes
17
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3192 CREDAT:6403 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1724 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1412 | "C:\Users\admin\AppData\Local\Temp\is-I83HA.tmp\duckLife-4.tmp" /SL5="$2D0202,9268592,54272,C:\Users\admin\AppData\Local\Temp\duckLife-4.exe" | C:\Users\admin\AppData\Local\Temp\is-I83HA.tmp\duckLife-4.tmp | — | duckLife-4.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.50.0.0 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Shmehao.com\DuckLife 4\DuckLife 4.exe" | C:\Program Files\Shmehao.com\DuckLife 4\DuckLife 4.exe | duckLife-4.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | DuckLife 4.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3444 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2208 | "C:\Users\admin\AppData\Local\Temp\duckLife-4.exe" | C:\Users\admin\AppData\Local\Temp\duckLife-4.exe | explorer.exe | ||||||||||||
User: admin Company: Shmehao.com Integrity Level: MEDIUM Description: DuckLife 4 Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3192 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4064 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2968 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 605
Read events
2 275
Write events
326
Delete events
4
Modification events
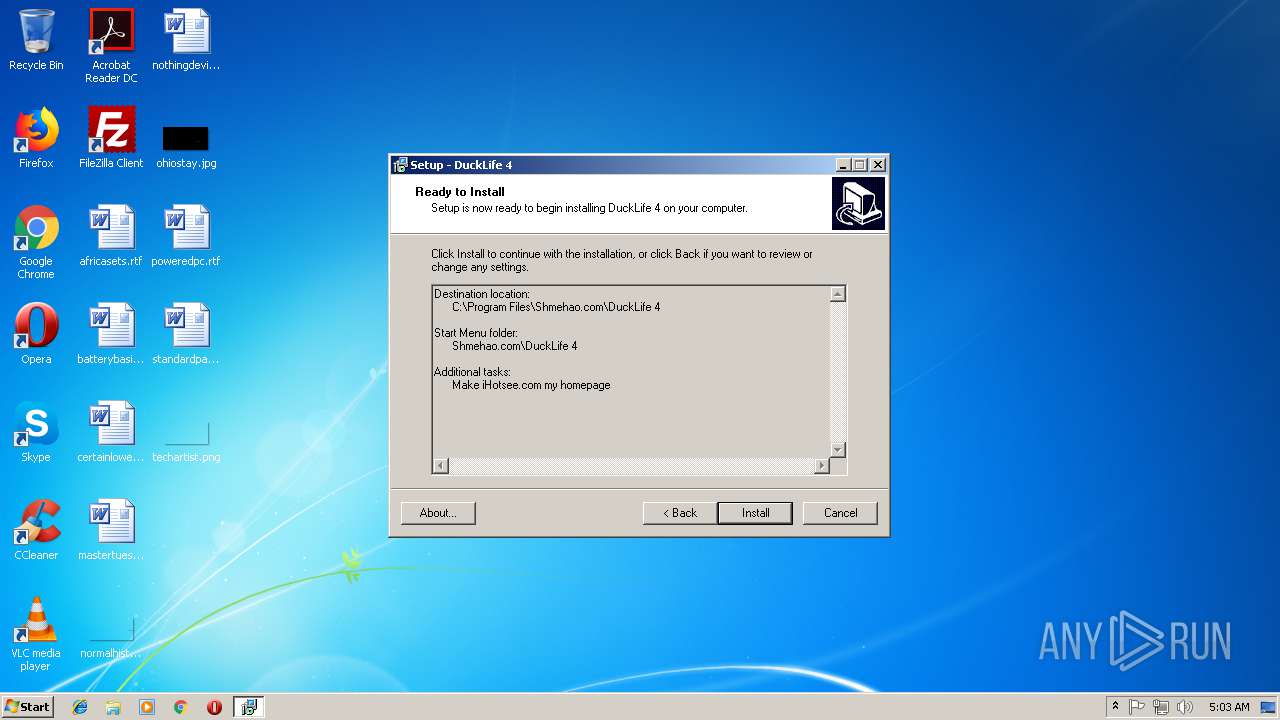
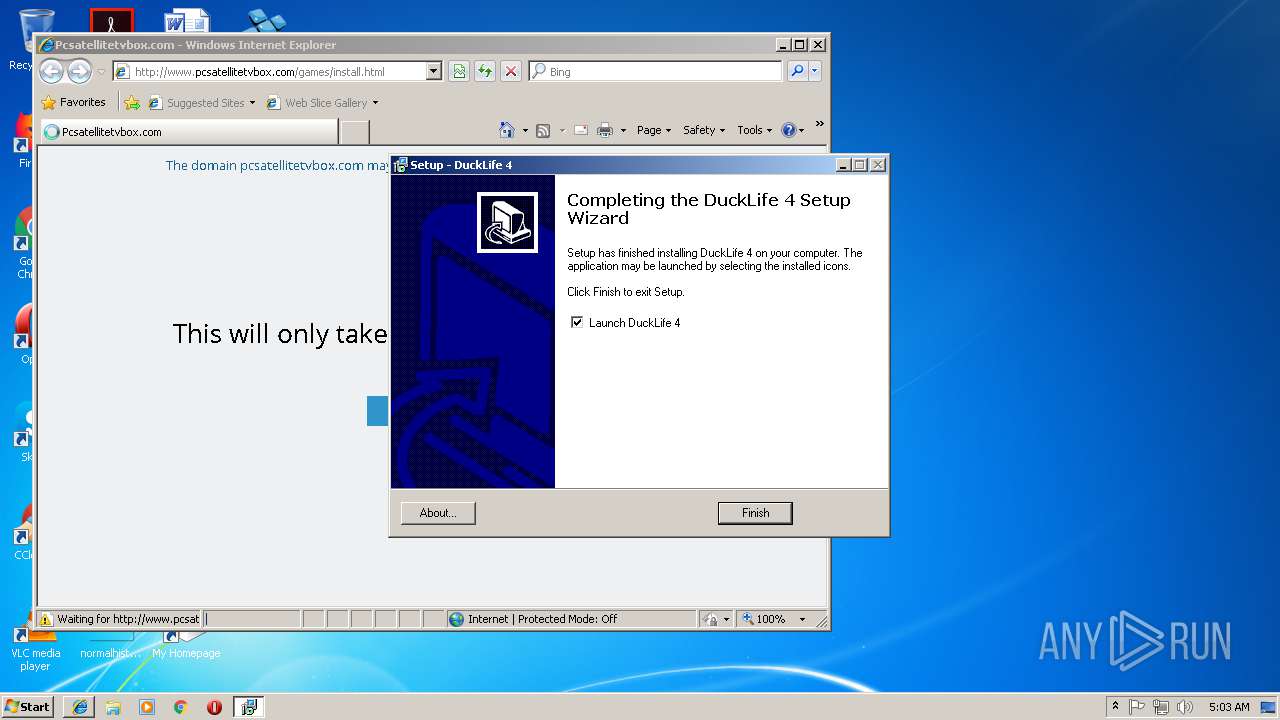
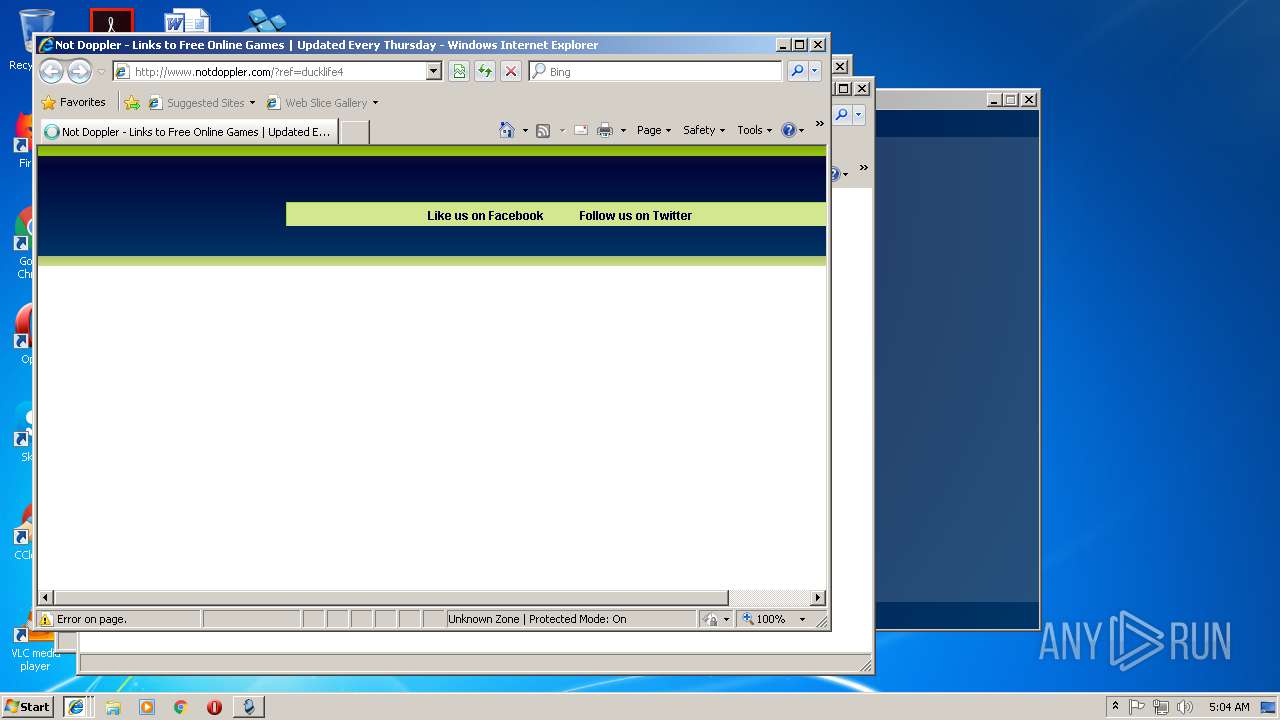
| (PID) Process: | (3748) duckLife-4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | Start Page |
Value: http://www.ihotsee.com/ | |||
| (PID) Process: | (3748) duckLife-4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DuckLife 4_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.3.7 (a) | |||
| (PID) Process: | (3748) duckLife-4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DuckLife 4_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Shmehao.com\DuckLife 4 | |||
| (PID) Process: | (3748) duckLife-4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DuckLife 4_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Shmehao.com\DuckLife 4\ | |||
| (PID) Process: | (3748) duckLife-4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DuckLife 4_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Shmehao.com\DuckLife 4 | |||
| (PID) Process: | (3748) duckLife-4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DuckLife 4_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (3748) duckLife-4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DuckLife 4_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: changestartpage | |||
| (PID) Process: | (3748) duckLife-4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DuckLife 4_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: | |||
| (PID) Process: | (3748) duckLife-4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DuckLife 4_is1 |
| Operation: | write | Name: | DisplayName |
Value: DuckLife 4 | |||
| (PID) Process: | (3748) duckLife-4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DuckLife 4_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Shmehao.com\DuckLife 4\unins000.exe" | |||
Executable files
6
Suspicious files
3
Text files
203
Unknown types
48
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3748 | duckLife-4.tmp | C:\Program Files\Shmehao.com\DuckLife 4\is-CST5U.tmp | — | |
MD5:— | SHA256:— | |||
| 3748 | duckLife-4.tmp | C:\Program Files\Shmehao.com\DuckLife 4\is-9CT7C.tmp | — | |
MD5:— | SHA256:— | |||
| 3748 | duckLife-4.tmp | C:\Program Files\Shmehao.com\is-DG6TR.tmp | — | |
MD5:— | SHA256:— | |||
| 3748 | duckLife-4.tmp | C:\Program Files\Shmehao.com\is-QOEQF.tmp | — | |
MD5:— | SHA256:— | |||
| 3748 | duckLife-4.tmp | C:\Program Files\Shmehao.com\is-0CJ6P.tmp | — | |
MD5:— | SHA256:— | |||
| 3748 | duckLife-4.tmp | C:\Program Files\Shmehao.com\is-RD1ML.tmp | — | |
MD5:— | SHA256:— | |||
| 3444 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3444 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3748 | duckLife-4.tmp | C:\Program Files\Shmehao.com\ihotsee.ico | image | |
MD5:— | SHA256:— | |||
| 3748 | duckLife-4.tmp | C:\Program Files\Shmehao.com\Shmehao.ico | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
97
TCP/UDP connections
132
DNS requests
33
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1488 | DuckLife 4.exe | GET | 200 | 93.184.221.133:80 | http://cdn3.cpmstar.com/cached/creatives/1101470/DAUN_215_v04_WEAPONS-FINAL_640x440_15sec.swf?clickTAG=http%3A%2F%2Fserver%2Ecpmstar%2Ecom%2Fclick%2Easpx%3Fpoolid%3D1377%26subpoolid%3D100089%26campaignid%3D418936%26creativeid%3D1101470&ov_completeurl=http%3A%2F%2Fserver%2Ecpmstar%2Ecom%2Fpixel%2Easpx%3Fpoolid%3D1377%26subpoolid%3D100089%26campaignid%3D418936%26creativeid%3D1101470%26pixelid%3Dvid100&ov_firstquartileurl=http%3A%2F%2Fserver%2Ecpmstar%2Ecom%2Fpixel%2Easpx%3Fpoolid%3D1377%26subpoolid%3D100089%26campaignid%3D418936%26creativeid%3D1101470%26pixelid%3Dvid25&ov_midpointurl=http%3A%2F%2Fserver%2Ecpmstar%2Ecom%2Fpixel%2Easpx%3Fpoolid%3D1377%26subpoolid%3D100089%26campaignid%3D418936%26creativeid%3D1101470%26pixelid%3Dvid50&ov_starturl=http%3A%2F%2Fserver%2Ecpmstar%2Ecom%2Fpixel%2Easpx%3Fpoolid%3D1377%26subpoolid%3D100089%26campaignid%3D418936%26creativeid%3D1101470%26pixelid%3Dvid0&ov_thirdquartileurl=http%3A%2F%2Fserver%2Ecpmstar%2Ecom%2Fpixel%2Easpx%3Fpoolid%3D1377%26subpoolid%3D100089%26campaignid%3D418936%26creativeid%3D1101470%26pixelid%3Dvid75&ov_videoduration=15&ov_videourl=http%3A%2F%2Fcdn3%2Ecpmstar%2Ecom%2Fcached%2Fcreatives%2F1101470%2FDAUN%5F215%5Fv04%5FWEAPONS%2DFINAL%5F640x360%5F15sec%2Eflv&lcname=_cpmstar_23205&width=750&height=420 | US | — | 7.00 Kb | whitelisted |
2084 | iexplore.exe | GET | 302 | 198.54.112.216:80 | http://2163.furust.com/match-2163/24481/8119235/1539230610/mf_4f94c95c-39c6-4ddb-9c93-1aa6db78eaf2/YXBpeDAzLXBjc2F0ZWxsaXRldHZib3guY29t | US | — | — | malicious |
1488 | DuckLife 4.exe | GET | — | 50.22.46.25:80 | http://server.cpmstar.com/pixel.aspx?poolid=1377&subpoolid=100089&campaignid=418936&creativeid=1101470&pixelid=vid0 | US | — | — | suspicious |
1488 | DuckLife 4.exe | GET | — | 50.22.46.25:80 | http://server.cpmstar.com/viewcontent.aspx?xml=1&contentspotid=6395Q99B9541C&maxwidth=750&maxheight=420&srcurl=file%3A%2F%2FC%3A%5CUsers%5Cadmin%5CAppData%5CLocal%5CTemp%5C%5C7m4tk1j9%2Eswf&fv=10&allowscript=1&interstitial=0&overlaytime=0&noadtypeid=3,24,34 | US | — | — | suspicious |
1488 | DuckLife 4.exe | GET | — | 50.22.46.25:80 | http://server.cpmstar.com/pixel.aspx?poolid=1377&subpoolid=100089&campaignid=418936&creativeid=1101470&pixelid=vid50 | US | — | — | suspicious |
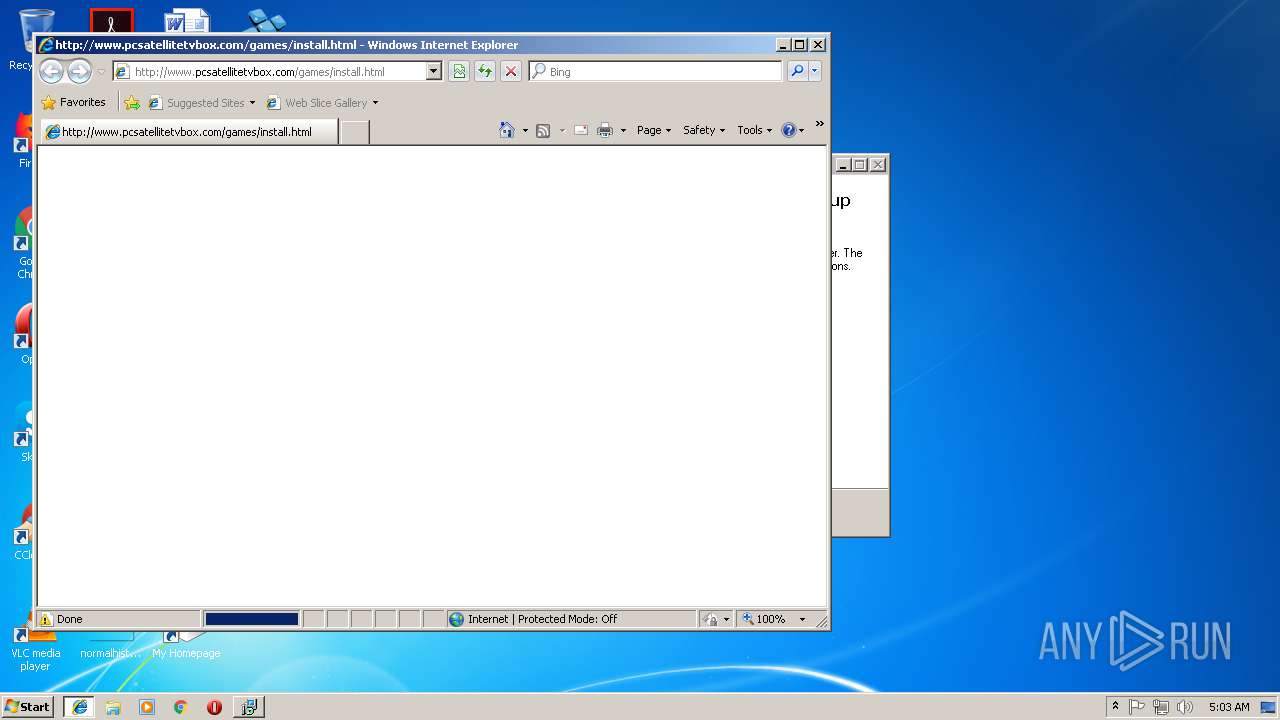
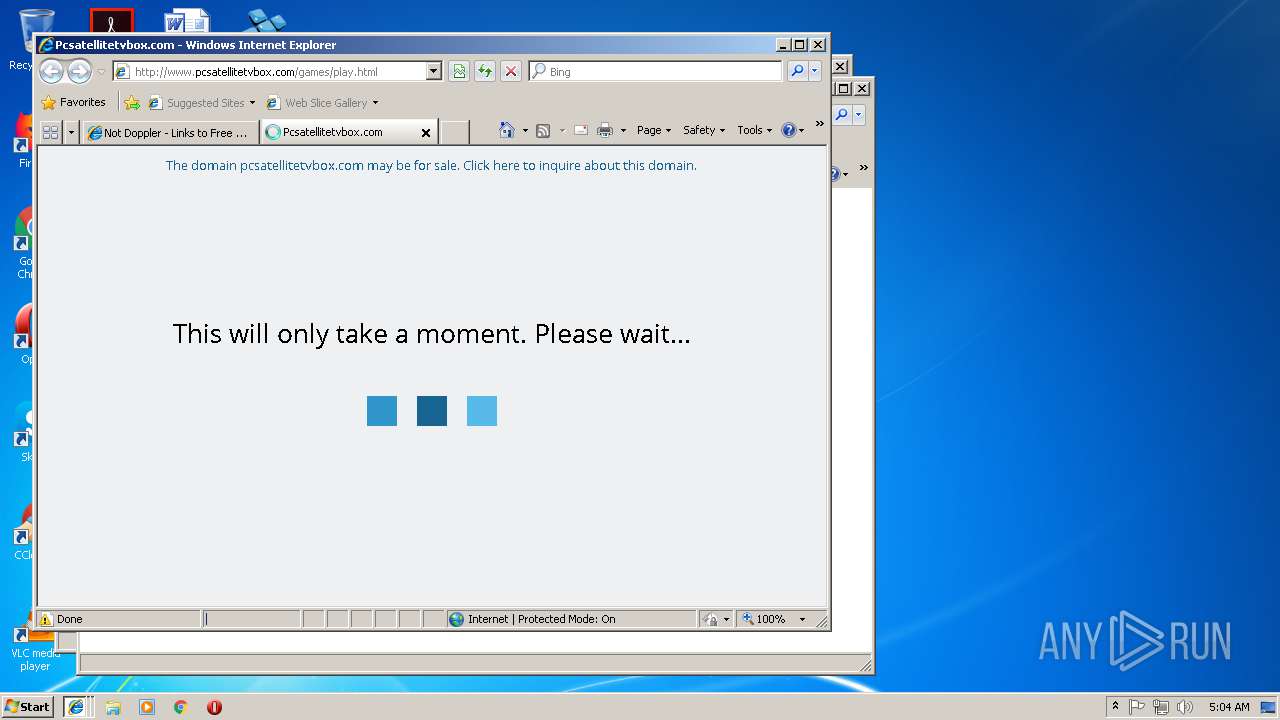
2084 | iexplore.exe | GET | 200 | 199.59.242.151:80 | http://www.pcsatellitetvbox.com/games/install.html | US | html | 3.84 Kb | malicious |
2084 | iexplore.exe | GET | 200 | 199.59.242.151:80 | http://www.pcsatellitetvbox.com/glp?r=&u=http%3A%2F%2Fwww.pcsatellitetvbox.com%2Fgames%2Finstall.html&rw=1280&rh=720&ww=788&wh=460&ie=8 | US | text | 8.53 Kb | malicious |
2084 | iexplore.exe | POST | 200 | 199.59.242.151:80 | http://www.pcsatellitetvbox.com/gzb | US | text | 223 b | malicious |
1488 | DuckLife 4.exe | GET | 200 | 50.22.46.25:80 | http://server.cpmstar.com/crossdomain.xml | US | xml | 278 b | suspicious |
2084 | iexplore.exe | GET | 200 | 216.58.212.132:80 | http://www.google.com/adsense/domains/caf.js | US | text | 69.8 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3444 | iexplore.exe | 204.79.197.229:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2084 | iexplore.exe | 216.58.212.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2084 | iexplore.exe | 216.58.212.132:80 | www.google.com | Google Inc. | US | whitelisted |
2084 | iexplore.exe | 172.217.20.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1488 | DuckLife 4.exe | 50.22.46.25:80 | server.cpmstar.com | SoftLayer Technologies Inc. | US | suspicious |
1488 | DuckLife 4.exe | 93.184.221.133:80 | cdn3.cpmstar.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1724 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3192 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2084 | iexplore.exe | 198.54.112.216:80 | 2163.furust.com | Namecheap, Inc. | US | malicious |
4064 | iexplore.exe | 204.79.197.229:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.ihotsee.com |
| malicious |
www.shmehao.com |
| malicious |
www.bing.com |
| whitelisted |
www.pcsatellitetvbox.com |
| malicious |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
2163.furust.com |
| malicious |
kq6.bestworkserv.company |
| unknown |
server.cpmstar.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2084 | iexplore.exe | A Network Trojan was detected | SC WORM Worm:Win32/Esfury - C&C checkin |
1488 | DuckLife 4.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |
1488 | DuckLife 4.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |
476 | iexplore.exe | A Network Trojan was detected | SC WORM Worm:Win32/Esfury - C&C checkin |