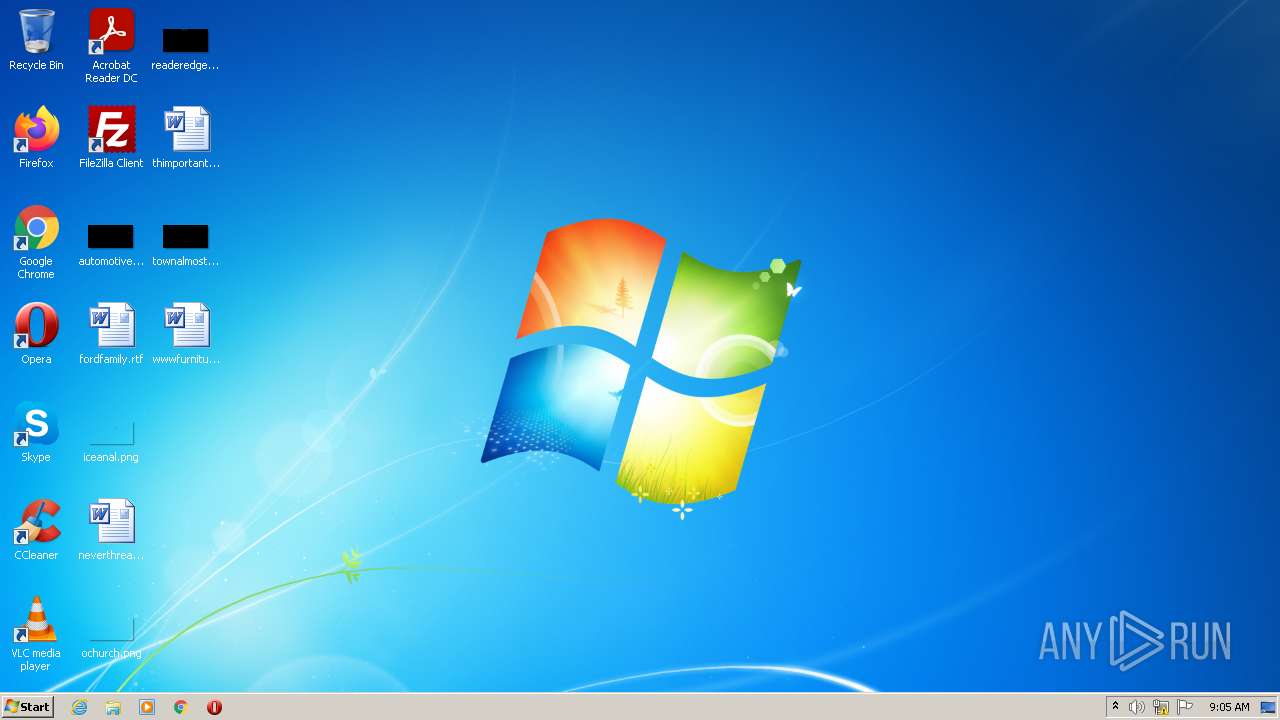
| File name: | Windows 10 Rounded.exe |
| Full analysis: | https://app.any.run/tasks/f725683b-79dd-4b31-92bb-54c2aa6a2f4f |
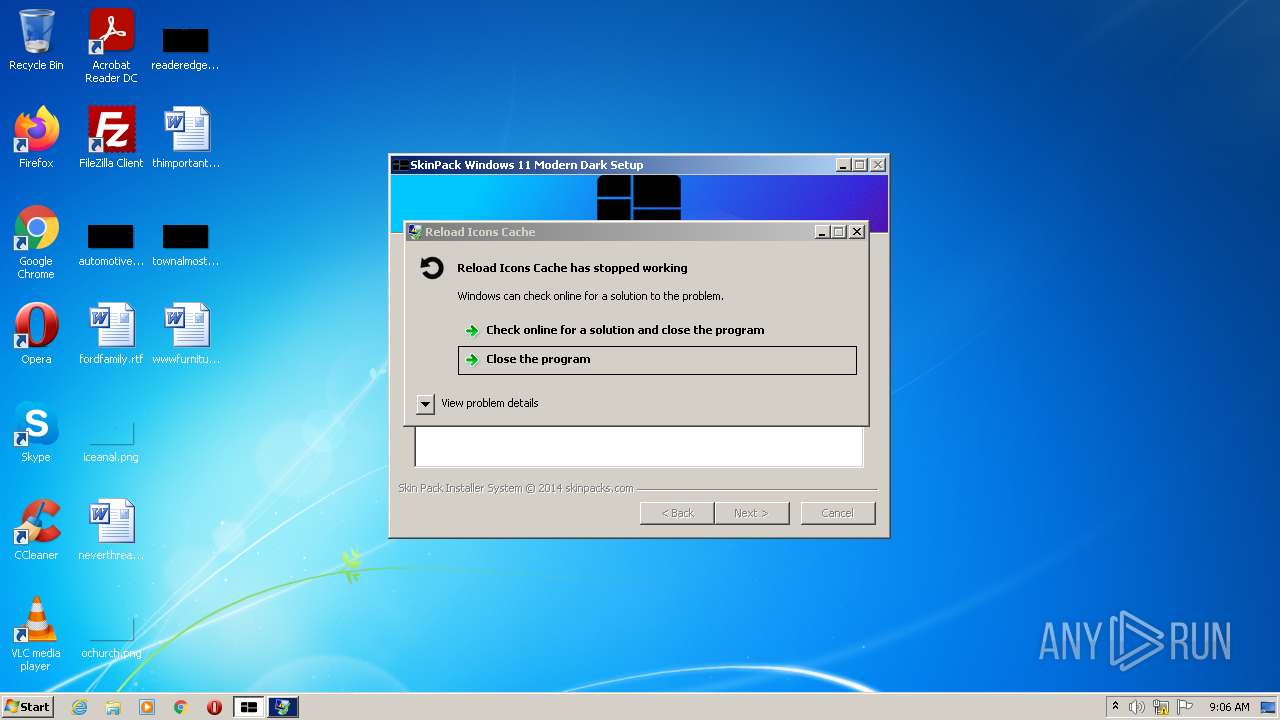
| Verdict: | Malicious activity |
| Analysis date: | January 20, 2022, 09:05:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 11FF322997D98D02AFE198C20B613FF3 |
| SHA1: | 48E70395F187454BDDC01484A6CBCF1C5F1753FC |
| SHA256: | 9482BE3FCB23242751DFC68C1F239C92DE3999618CA2D3AE0D7C9F5F596876F4 |
| SSDEEP: | 49152:DXNPtf+dAGSXAZGxgF3Nr13EfePGBT5OHTdg5K6EnCN11Y:DPxD5g1p9keGLc+SH |
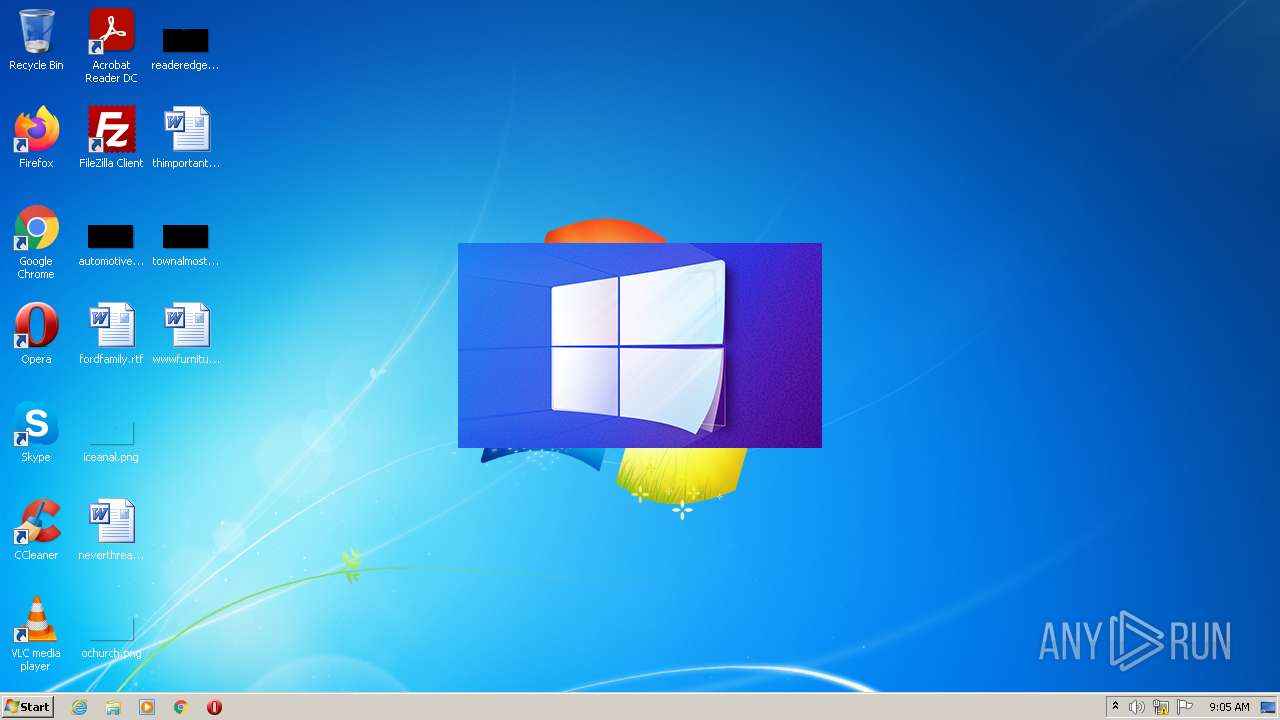
MALICIOUS
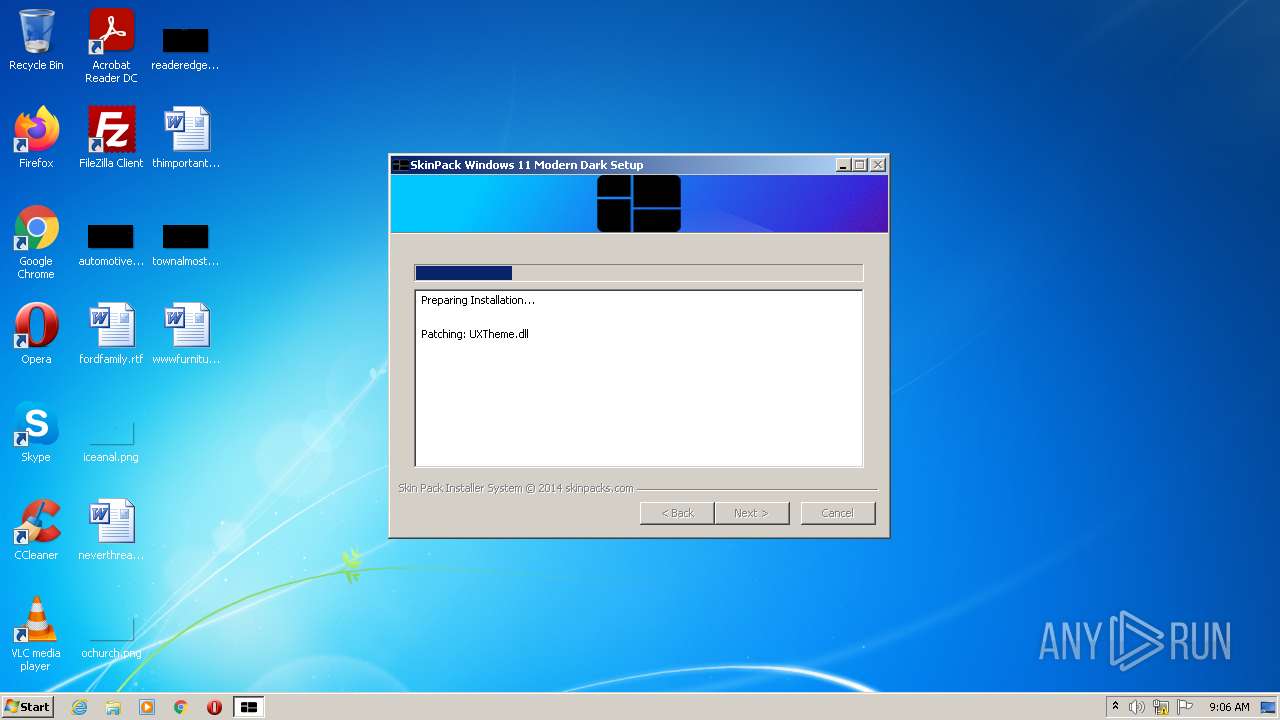
Drops executable file immediately after starts
- Windows 10 Rounded.exe (PID: 1060)
- UXTheme.exe (PID: 2656)
Loads dropped or rewritten executable
- Windows 10 Rounded.exe (PID: 1060)
- UXTheme.exe (PID: 2656)
Application was dropped or rewritten from another process
- UXTheme.exe (PID: 2656)
- RD.exe (PID: 400)
- ric.exe (PID: 2180)
Registers / Runs the DLL via REGSVR32.EXE
- RD.exe (PID: 400)
SUSPICIOUS
Reads the computer name
- Windows 10 Rounded.exe (PID: 1060)
- UXTheme.exe (PID: 2656)
- ric.exe (PID: 2180)
- RD.exe (PID: 400)
Checks supported languages
- Windows 10 Rounded.exe (PID: 1060)
- ns9B35.tmp (PID: 304)
- UXTheme.exe (PID: 2656)
- RD.exe (PID: 400)
- ric.exe (PID: 2180)
Starts application with an unusual extension
- Windows 10 Rounded.exe (PID: 1060)
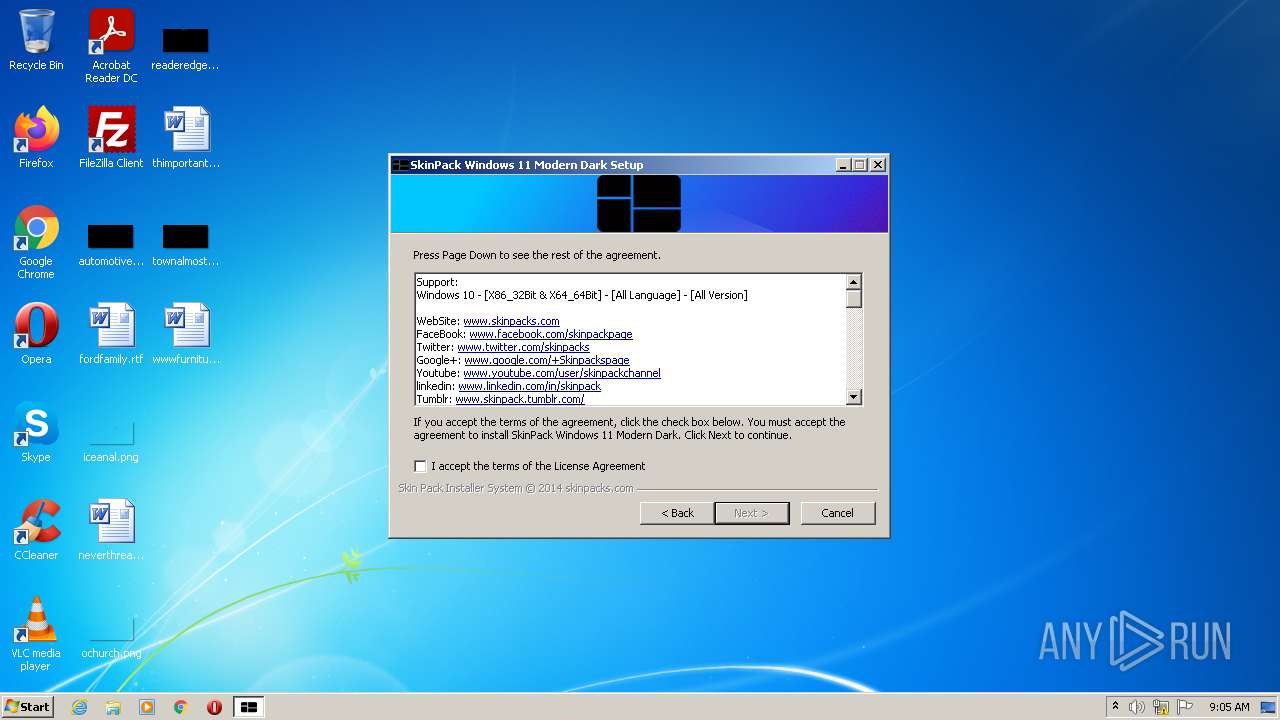
Creates a software uninstall entry
- Windows 10 Rounded.exe (PID: 1060)
- UXTheme.exe (PID: 2656)
Reads Environment values
- UXTheme.exe (PID: 2656)
- vssvc.exe (PID: 1444)
Executable content was dropped or overwritten
- UXTheme.exe (PID: 2656)
- Windows 10 Rounded.exe (PID: 1060)
Executed as Windows Service
- vssvc.exe (PID: 1444)
Executed via COM
- DllHost.exe (PID: 2072)
Searches for installed software
- DllHost.exe (PID: 2072)
- UXTheme.exe (PID: 2656)
Drops a file that was compiled in debug mode
- UXTheme.exe (PID: 2656)
- Windows 10 Rounded.exe (PID: 1060)
Drops a file with too old compile date
- UXTheme.exe (PID: 2656)
- Windows 10 Rounded.exe (PID: 1060)
Uses ICACLS.EXE to modify access control list
- UXTheme.exe (PID: 2656)
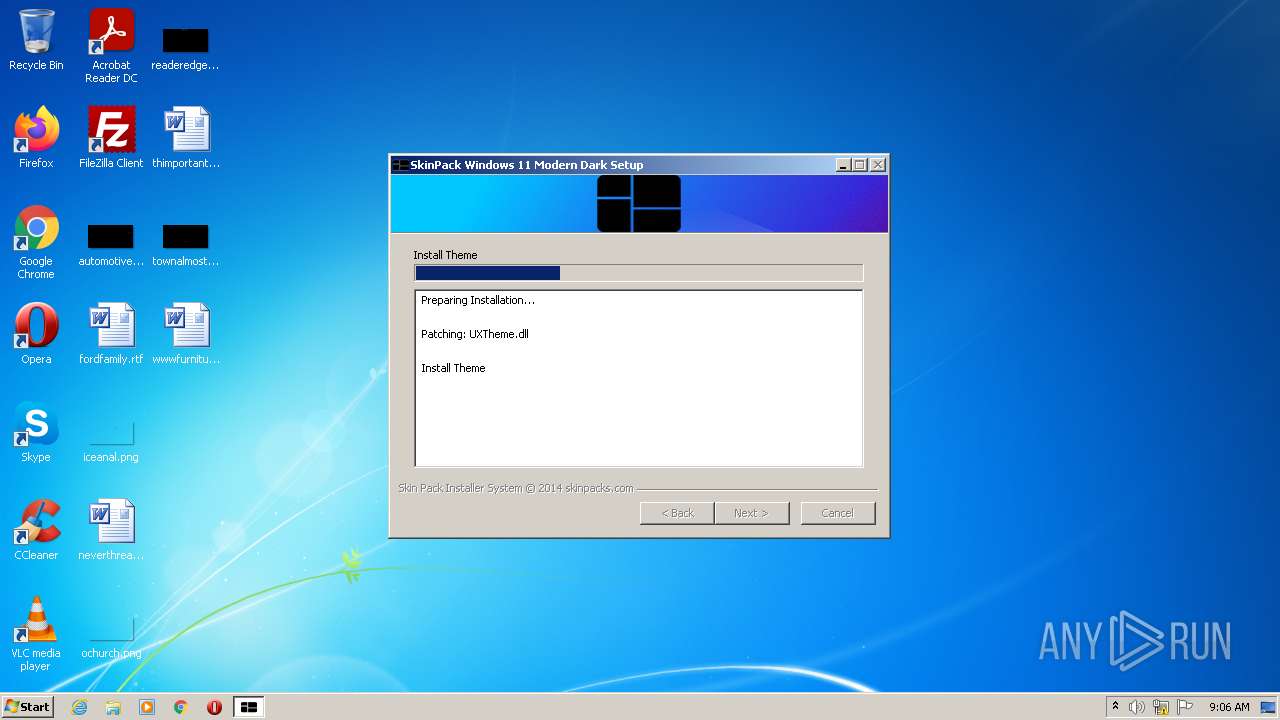
Creates files in the Windows directory
- UXTheme.exe (PID: 2656)
- Windows 10 Rounded.exe (PID: 1060)
Removes files from Windows directory
- UXTheme.exe (PID: 2656)
Creates a directory in Program Files
- UXTheme.exe (PID: 2656)
Creates files in the program directory
- UXTheme.exe (PID: 2656)
Drops a file with a compile date too recent
- Windows 10 Rounded.exe (PID: 1060)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2648)
INFO
Reads the computer name
- vssvc.exe (PID: 1444)
- DllHost.exe (PID: 2072)
- icacls.exe (PID: 540)
- takeown.exe (PID: 2496)
- takeown.exe (PID: 3048)
- icacls.exe (PID: 3176)
- takeown.exe (PID: 3644)
- icacls.exe (PID: 3108)
Checks supported languages
- vssvc.exe (PID: 1444)
- DllHost.exe (PID: 2072)
- takeown.exe (PID: 3048)
- takeown.exe (PID: 2496)
- icacls.exe (PID: 540)
- takeown.exe (PID: 3644)
- icacls.exe (PID: 3176)
- regsvr32.exe (PID: 2648)
- regsvr32.exe (PID: 2928)
- icacls.exe (PID: 3108)
Dropped object may contain Bitcoin addresses
- UXTheme.exe (PID: 2656)
- Windows 10 Rounded.exe (PID: 1060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x3461 |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 118784 |
| CodeSize: | 25600 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2020:08:01 04:43:48+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2020 02:43:48 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2020 02:43:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000623C | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40258 |
.rdata | 0x00008000 | 0x00001274 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0575 |
.data | 0x0000A000 | 0x0001A858 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.08975 |
.ndata | 0x00025000 | 0x00015000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003A000 | 0x00008280 | 0x00008400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.03853 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.14431 | 898 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.92071 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 2.10715 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 2.50372 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 2.50341 | 1640 | UNKNOWN | English - United States | RT_ICON |
6 | 6.82974 | 1450 | UNKNOWN | English - United States | RT_ICON |
7 | 1.77641 | 1384 | UNKNOWN | English - United States | RT_ICON |
8 | 3.66853 | 1128 | UNKNOWN | English - United States | RT_ICON |
9 | 5.94444 | 1019 | UNKNOWN | English - United States | RT_ICON |
10 | 3.16563 | 744 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
63
Monitored processes
16
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Users\admin\AppData\Local\Temp\nsa3016.tmp\ns9B35.tmp" "C:\Users\admin\AppData\Local\Temp\nsa3016.tmp\UXTheme.exe" /S | C:\Users\admin\AppData\Local\Temp\nsa3016.tmp\ns9B35.tmp | — | Windows 10 Rounded.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 400 | "C:\SkinPack\RD.exe" | C:\SkinPack\RD.exe | — | Windows 10 Rounded.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1003 Modules
| |||||||||||||||
| 540 | "C:\Windows\system32\icacls.exe" "C:\Windows\system32\uxtheme.dll" /grant admin:(d,wdac) | C:\Windows\system32\icacls.exe | — | UXTheme.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1060 | "C:\Users\admin\AppData\Local\Temp\Windows 10 Rounded.exe" | C:\Users\admin\AppData\Local\Temp\Windows 10 Rounded.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1444 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2072 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
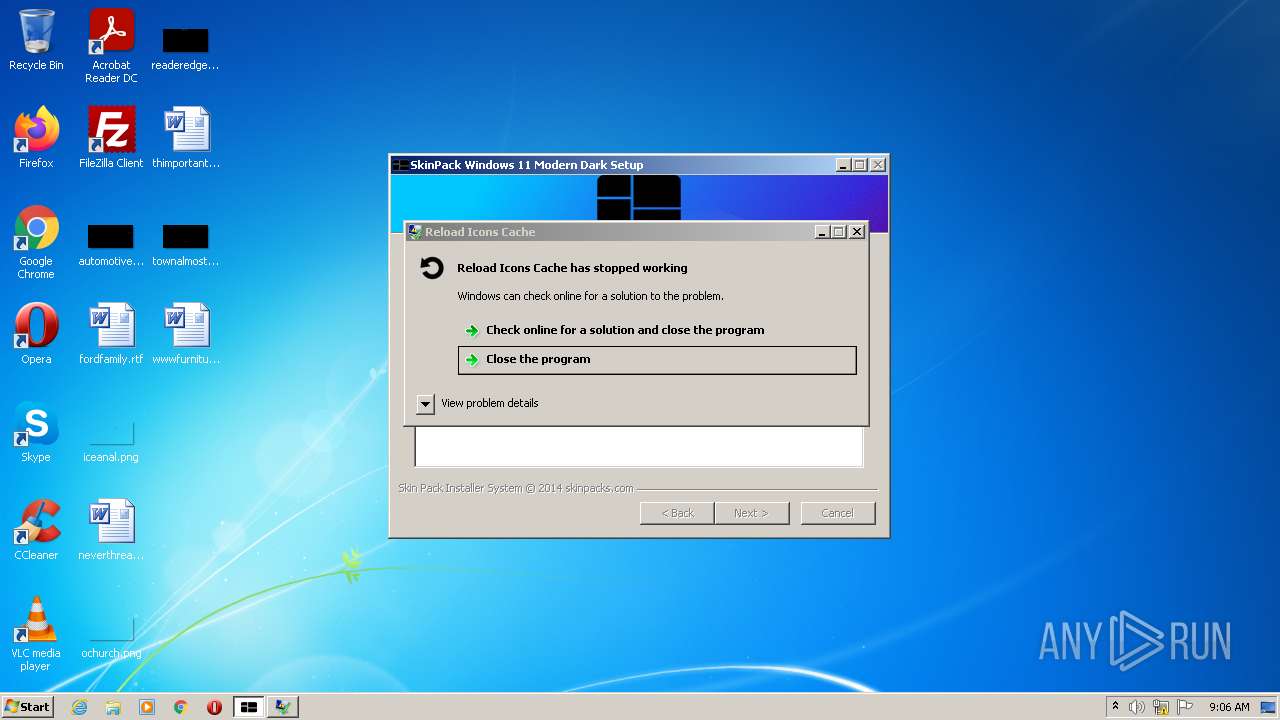
| 2180 | "C:\SkinPack\ric.exe" | C:\SkinPack\ric.exe | Windows 10 Rounded.exe | ||||||||||||
User: admin Company: Mr Blade Design's Integrity Level: HIGH Description: Reload Icons Cache Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2224 | "C:\Users\admin\AppData\Local\Temp\Windows 10 Rounded.exe" | C:\Users\admin\AppData\Local\Temp\Windows 10 Rounded.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2496 | "C:\Windows\system32\takeown.exe" /f "C:\Windows\system32\uxtheme.dll" | C:\Windows\system32\takeown.exe | — | UXTheme.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2648 | "C:\Windows\System32\regsvr32.exe" /s C:\skinpack\OldNewExplorer32.dll | C:\Windows\System32\regsvr32.exe | — | RD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 488
Read events
3 287
Write events
201
Delete events
0
Modification events
| (PID) Process: | (1060) Windows 10 Rounded.exe | Key: | HKEY_CURRENT_USER\AppEvents\Schemes\Apps\.Default\Close\.Current |
| Operation: | write | Name: | (default) |
Value: | |||
| (PID) Process: | (1060) Windows 10 Rounded.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | AllowProtectedRenames |
Value: 1 | |||
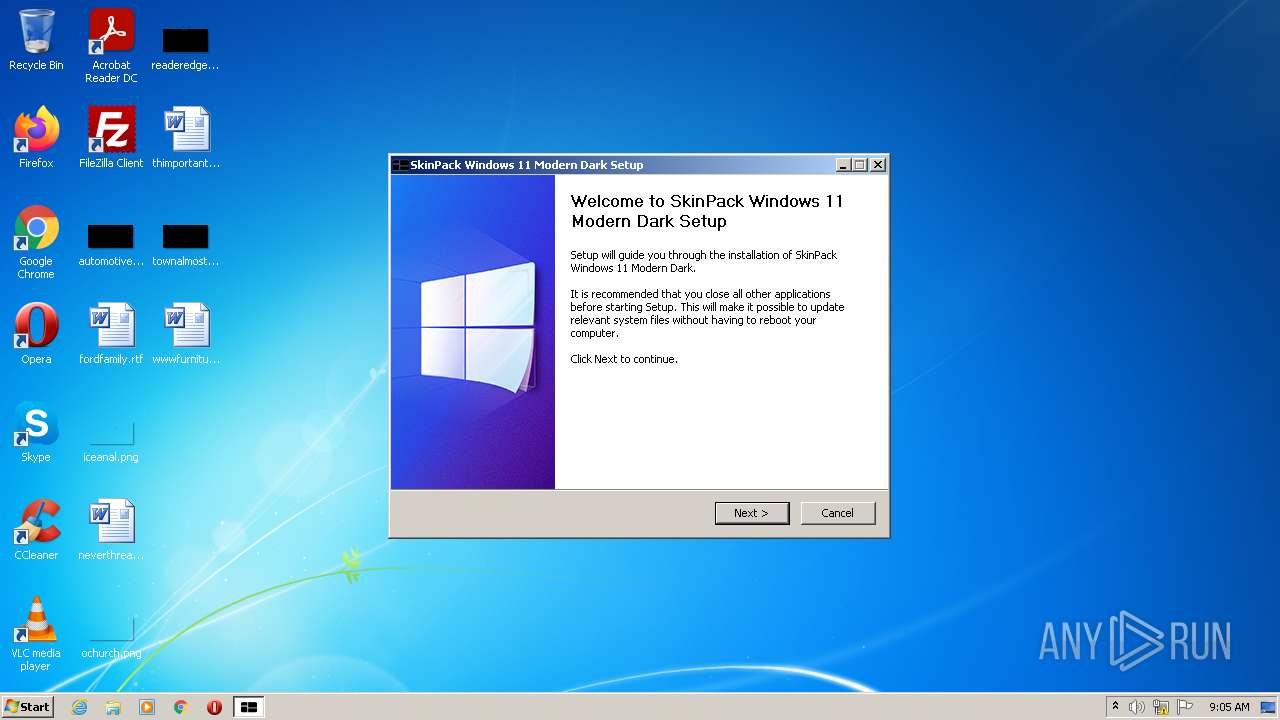
| (PID) Process: | (1060) Windows 10 Rounded.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SkinPack |
| Operation: | write | Name: | DisplayName |
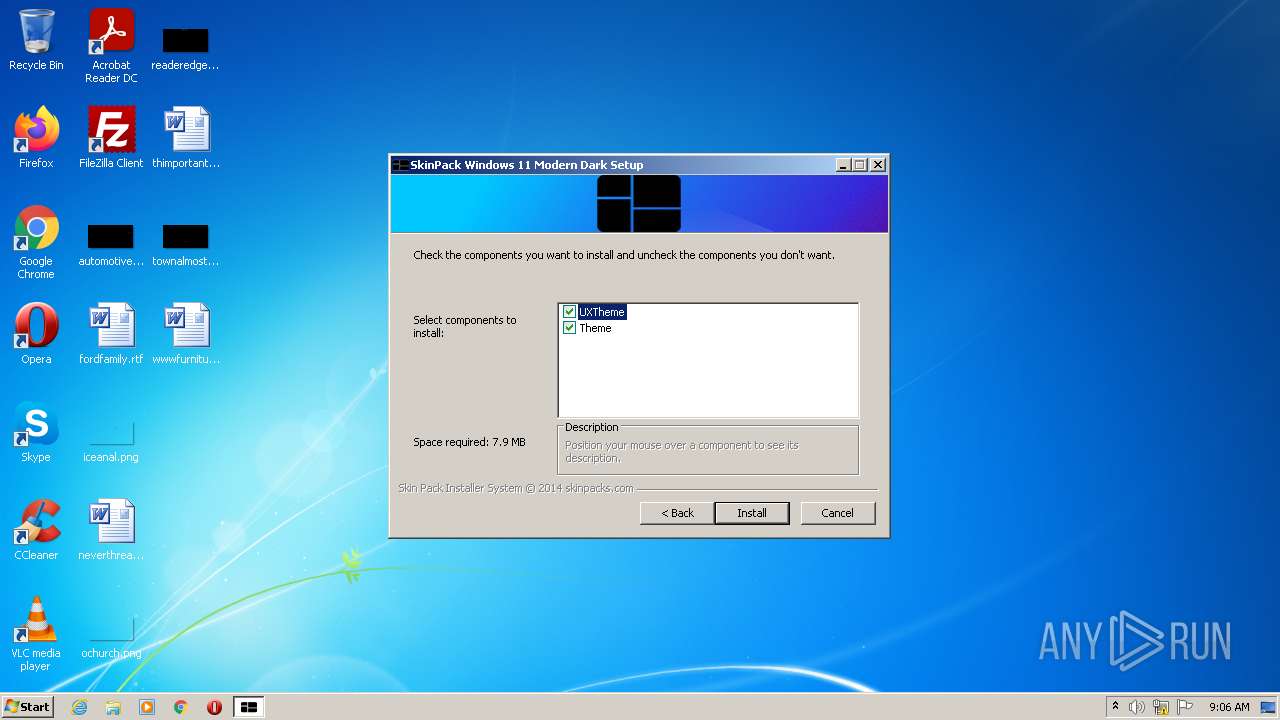
Value: SkinPack Windows 11 Modern Dark | |||
| (PID) Process: | (1060) Windows 10 Rounded.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SkinPack |
| Operation: | write | Name: | UninstallString |
Value: C:\SkinPack\uninst.exe | |||
| (PID) Process: | (1060) Windows 10 Rounded.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SkinPack |
| Operation: | write | Name: | DisplayIcon |
Value: C:\SkinPack\Install.ico | |||
| (PID) Process: | (1060) Windows 10 Rounded.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SkinPack |
| Operation: | write | Name: | DisplayVersion |
Value: Windows 11 Modern Dark | |||
| (PID) Process: | (1060) Windows 10 Rounded.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SkinPack |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.skinpacks.com | |||
| (PID) Process: | (1060) Windows 10 Rounded.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SkinPack |
| Operation: | write | Name: | Publisher |
Value: SkinPack | |||
| (PID) Process: | (2656) UXTheme.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000009B60E1F4DC0DD801600A00005C0A0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2656) UXTheme.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000009B60E1F4DC0DD801600A00005C0A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
54
Suspicious files
3
Text files
24
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2072 | DllHost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1060 | Windows 10 Rounded.exe | C:\Users\admin\AppData\Local\Temp\nsa3016.tmp\Aero.dll | executable | |
MD5:243BF44688B131C3171F2827A93E39DC | SHA256:04A577DF50431EB0FF6FB103566402BF66C50415BCC1F8A86B9C235053131455 | |||
| 1060 | Windows 10 Rounded.exe | C:\Users\admin\AppData\Local\Temp\nsa3016.tmp\modern-header.bmp | image | |
MD5:D7896A36E3707EEFF22295E8D04F61CD | SHA256:BFEE9AAD1D895B830107587CADDDE942D43C3920773E19F08D1C62E3C7D2430E | |||
| 1060 | Windows 10 Rounded.exe | C:\Users\admin\AppData\Local\Temp\nsa3016.tmp\modern-wizard.bmp | image | |
MD5:5B6CC42CC68A4FA0DFC40C160F9FF94A | SHA256:01E755C383FE88A0D09B141CBBC334C55E4F3F205CF773EC750C7E3707B914E9 | |||
| 2072 | DllHost.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 2072 | DllHost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{77c78899-07d9-453e-b4c2-9e868fd866c8}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 1060 | Windows 10 Rounded.exe | C:\Users\admin\AppData\Local\Temp\spltmp.bmp | image | |
MD5:21AA890D8476D74E76FFA1566711BAF7 | SHA256:E08F7C06992C7AD8F48A999EF9E0C67203312910380758740E933F3C6BB16E59 | |||
| 2656 | UXTheme.exe | C:\Windows\System32\uxtheme.dll.new | executable | |
MD5:63BFDF555DA2075A77D677829C3CCCD0 | SHA256:13B0C0576A0158FBEE6C216136F8C66373C8E6592895D3D824EC67147B9190E9 | |||
| 1060 | Windows 10 Rounded.exe | C:\Users\admin\AppData\Local\Temp\nsa3016.tmp\UXTheme.exe | executable | |
MD5:14044C6159982AC9BCE2DA9A354CEAAF | SHA256:826186B0C1AA55646DFD2D7699A05192D78F7F0B76413A6525EFFA894CF83BF2 | |||
| 1060 | Windows 10 Rounded.exe | C:\Users\admin\AppData\Local\Temp\nsa3016.tmp\nsExec.dll | executable | |
MD5:09C2E27C626D6F33018B8A34D3D98CB6 | SHA256:114C6941A8B489416C84563E94FD266EA5CAD2B518DB45CD977F1F9761E00CB1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report