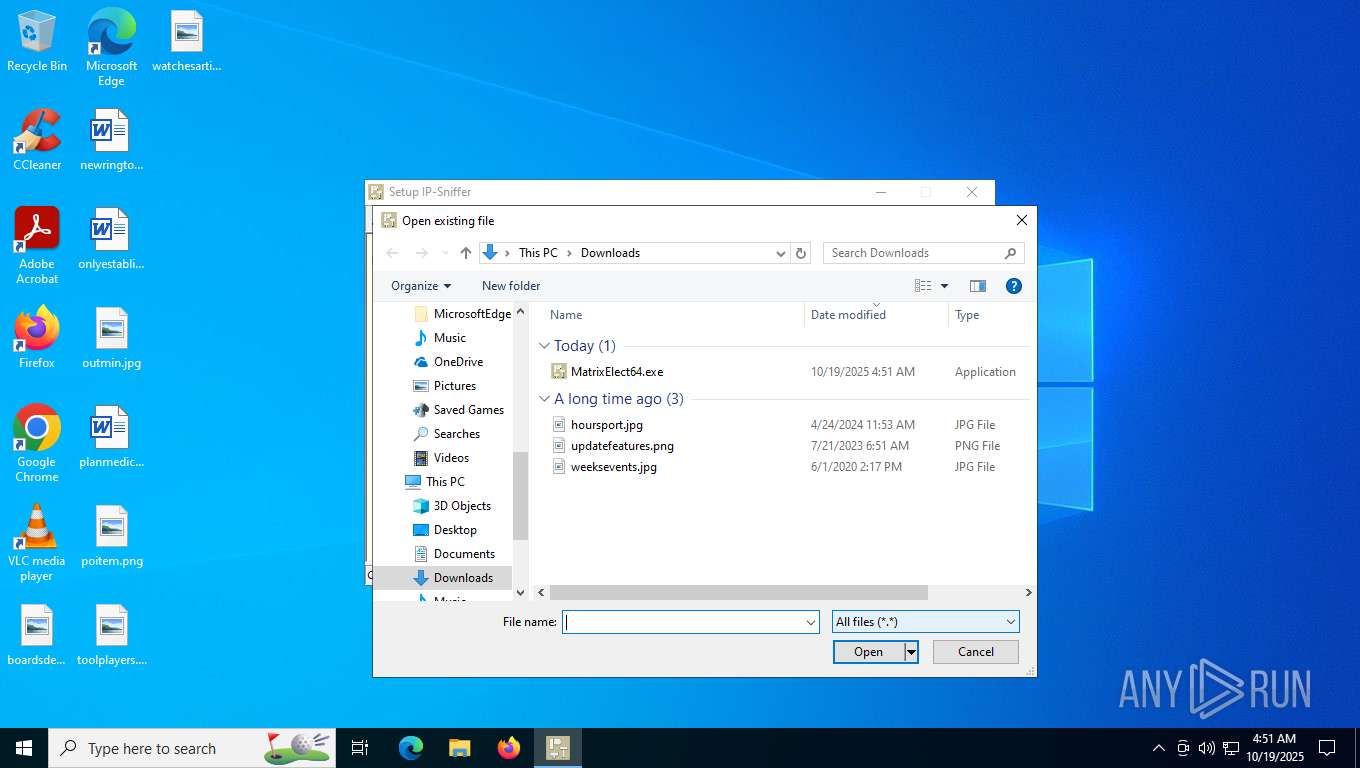
| File name: | MatrixElect64.exe |
| Full analysis: | https://app.any.run/tasks/35723d1d-46d5-4f3c-9e4b-a175eacdeaaf |
| Verdict: | Malicious activity |
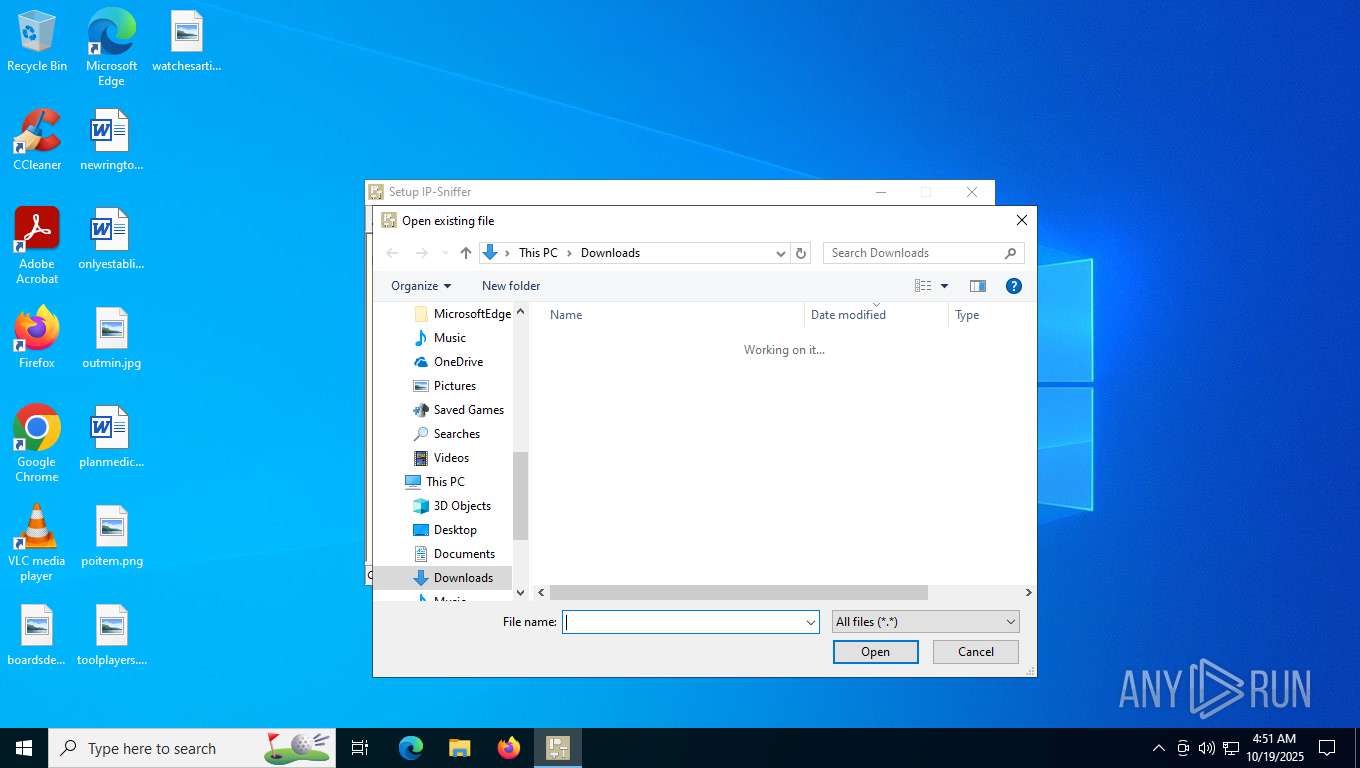
| Analysis date: | October 19, 2025, 04:51:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 9 sections |
| MD5: | 5AFADF74069C211A3C29BC1D788E02F7 |
| SHA1: | B568A6D0CBEFA473B26B02A9F5AEE08CDEBE03B7 |
| SHA256: | 9481DCA53C9AA408C8DCE20731FE6497FF79EEC1AA8D7BE5FC01EF48B6DC84B9 |
| SSDEEP: | 98304:fCnAo6tBq9RxcirwRSK3znR0R9dtQM+iDr5ukvKW1ASFXiDNtUDVR+hKpW:rg |
MALICIOUS
Executing a file with an untrusted certificate
- MatrixElect64.exe (PID: 8300)
SUSPICIOUS
Reads security settings of Internet Explorer
- MatrixElect64.exe (PID: 8300)
INFO
The sample compiled with english language support
- MatrixElect64.exe (PID: 8300)
Checks supported languages
- MatrixElect64.exe (PID: 8300)
Reads the computer name
- MatrixElect64.exe (PID: 8300)
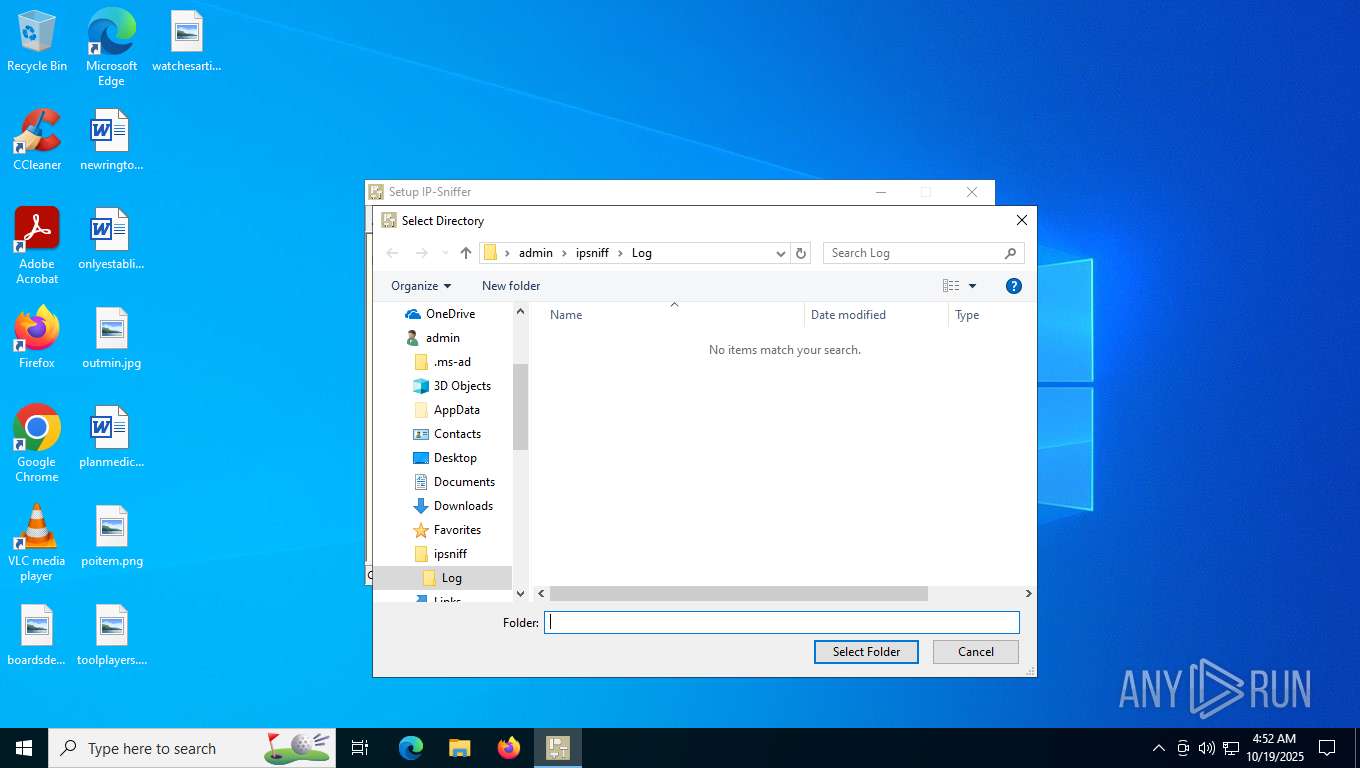
Creates files or folders in the user directory
- MatrixElect64.exe (PID: 8300)
Compiled with Borland Delphi (YARA)
- MatrixElect64.exe (PID: 8300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.2) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 3.22 |
| CodeSize: | 2913232 |
| InitializedDataSize: | 155316 |
| UninitializedDataSize: | 1115856 |
| EntryPoint: | 0x3130 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.8.5.2174 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
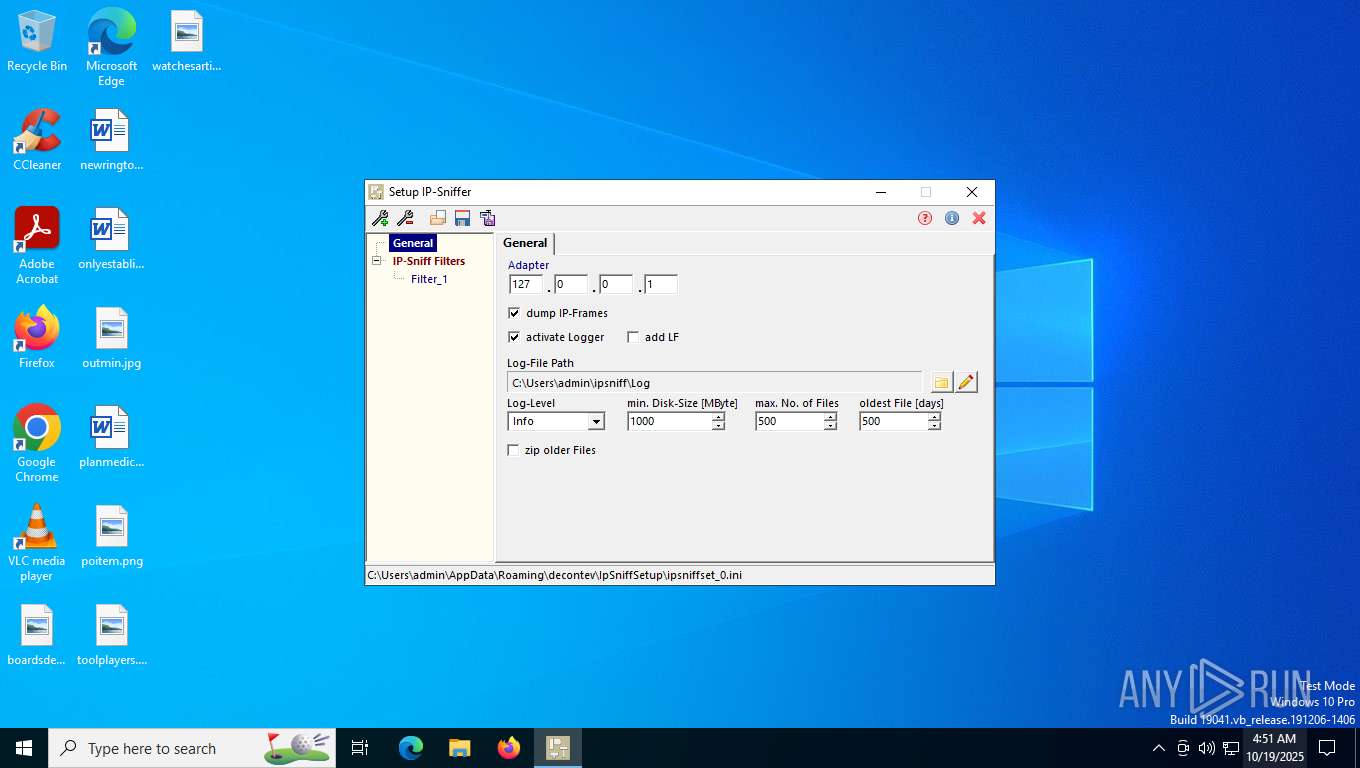
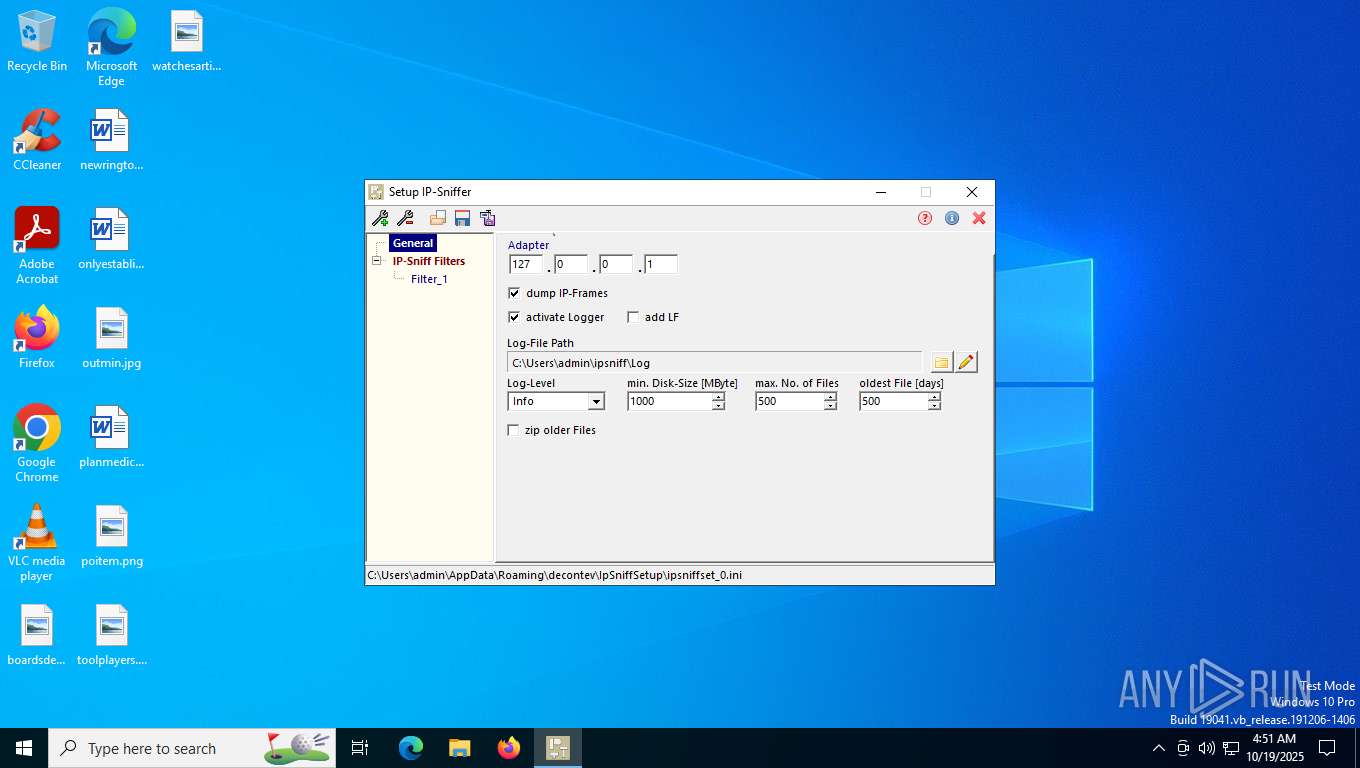
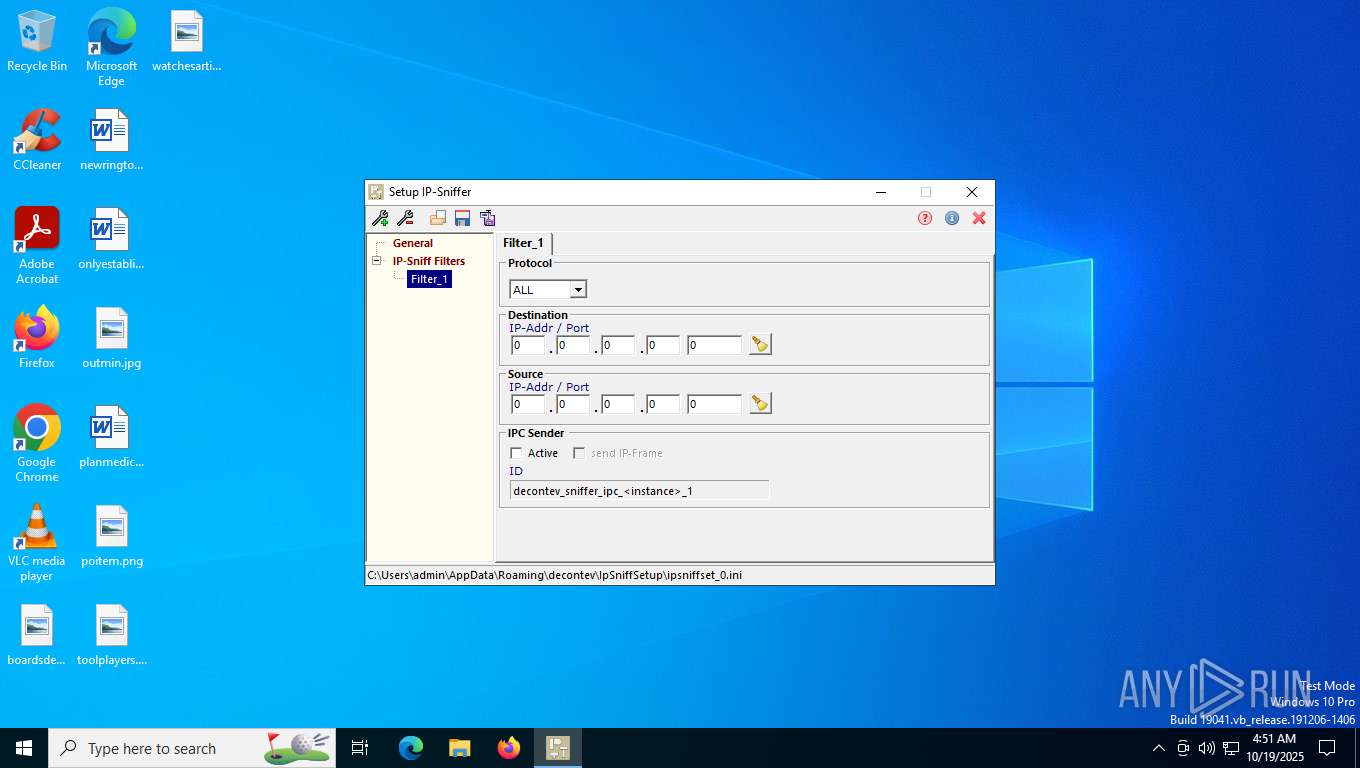
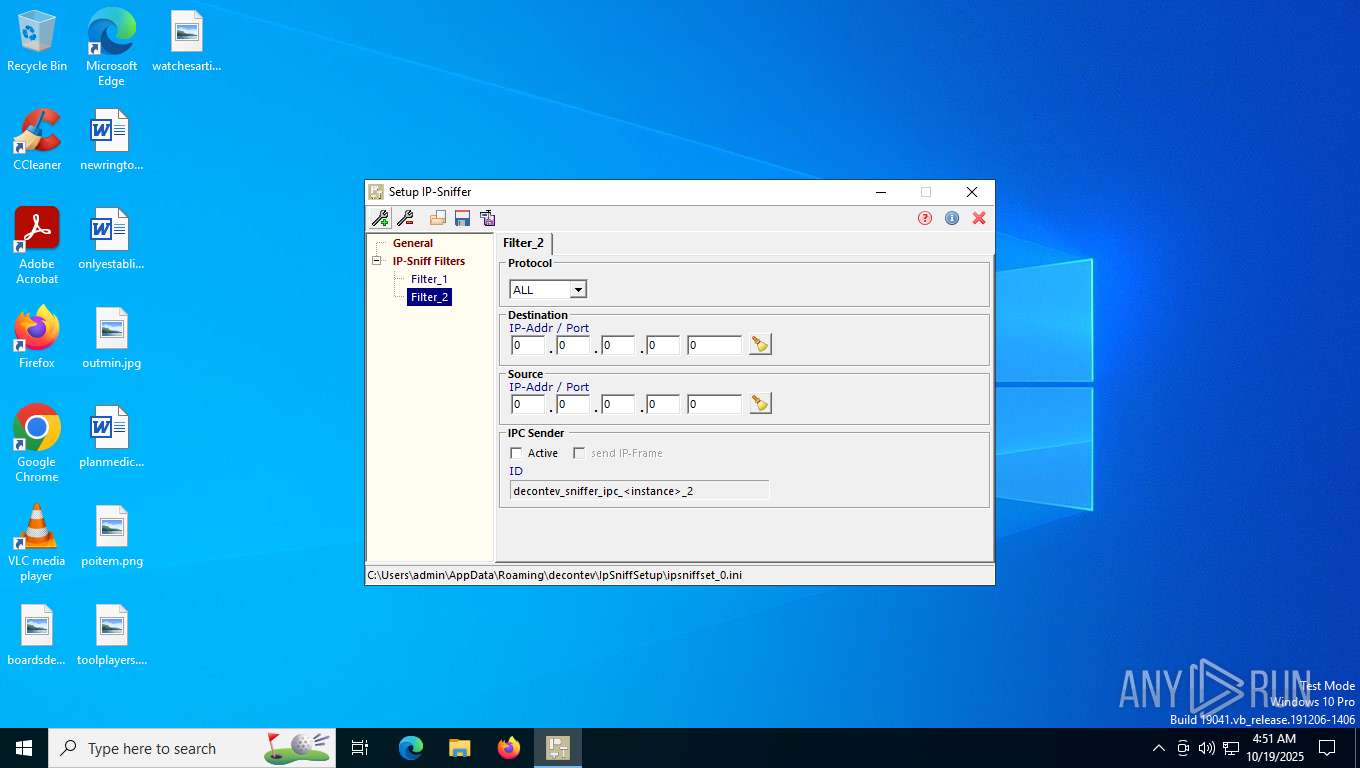
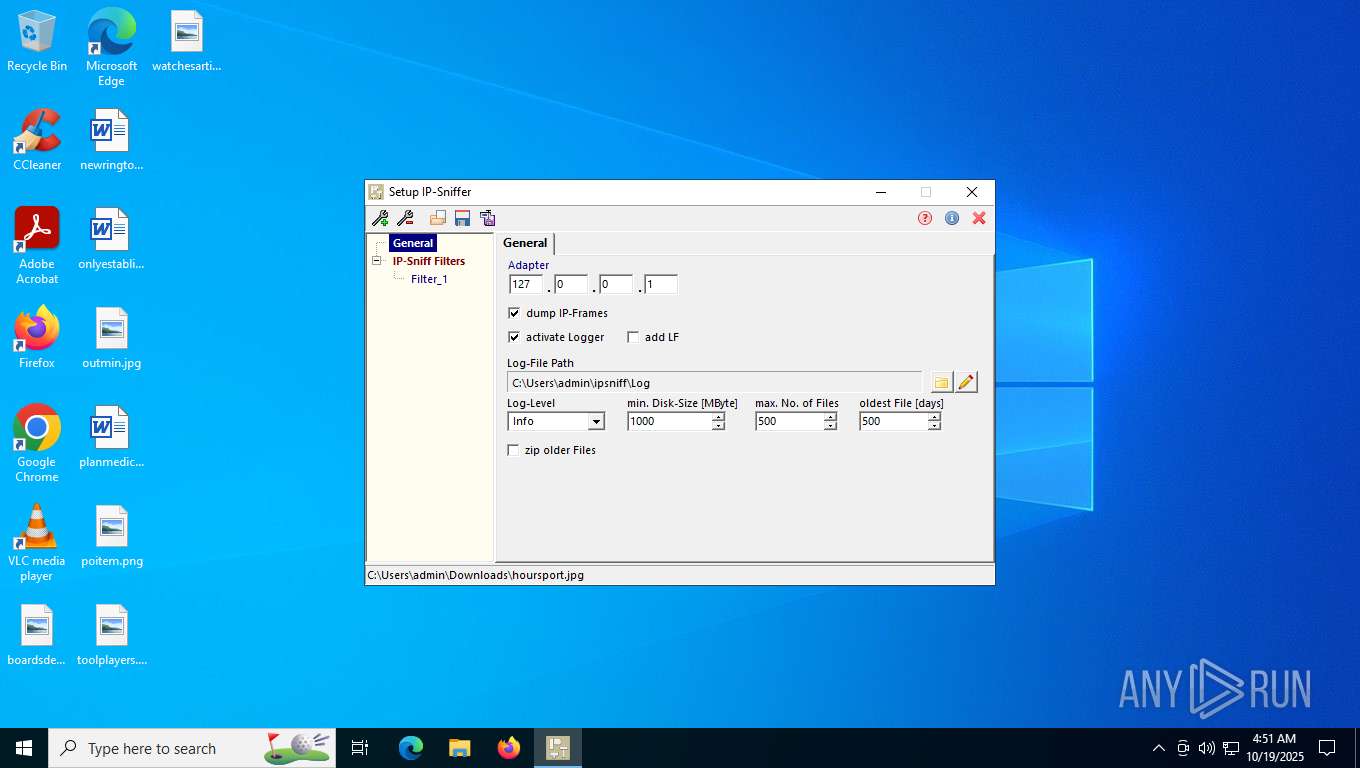
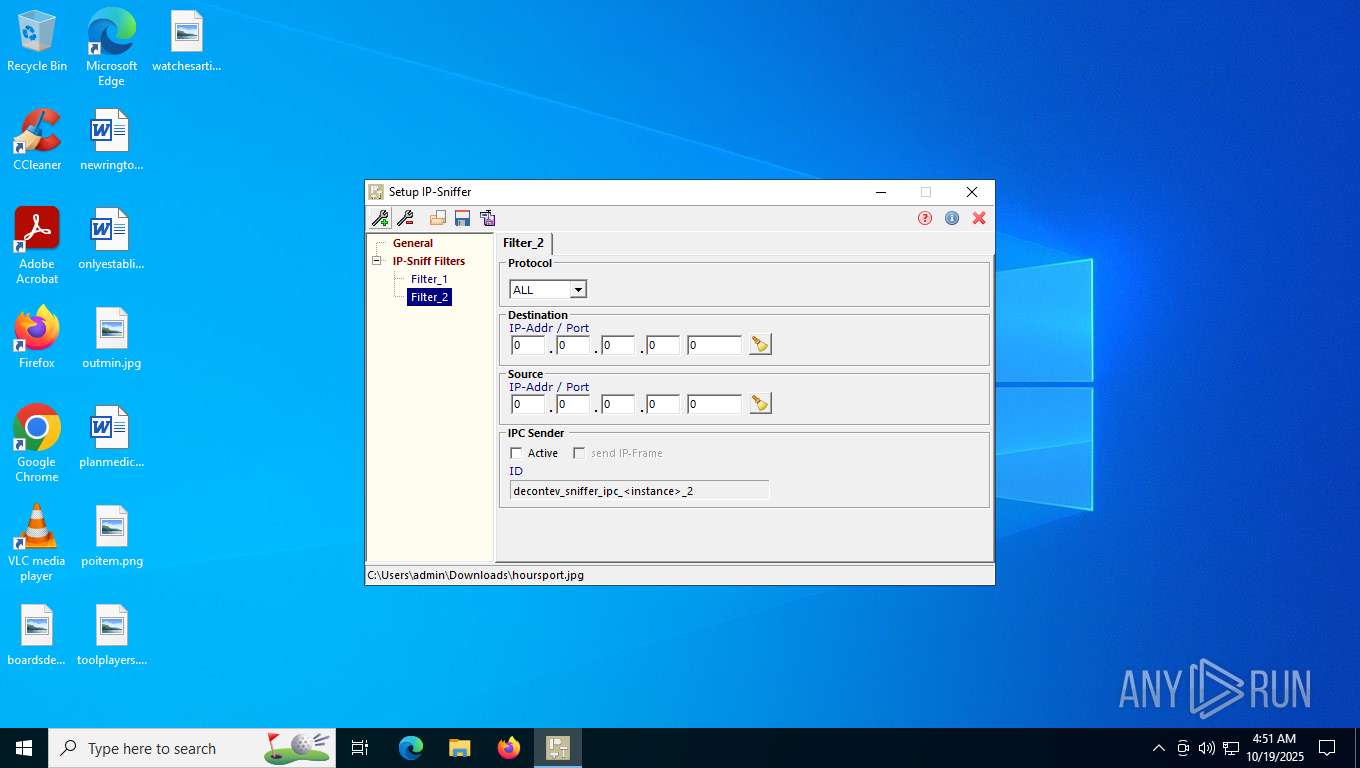
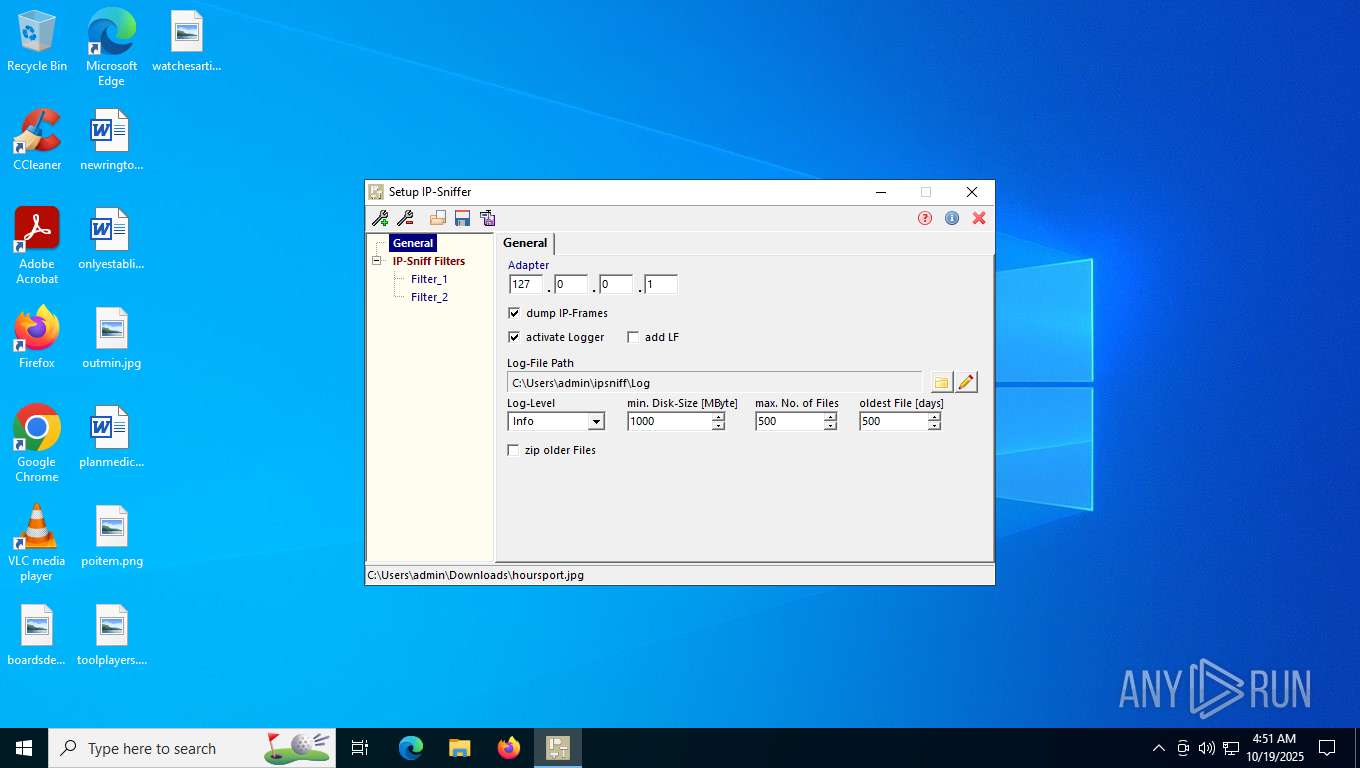
| CompanyName: | decontev |
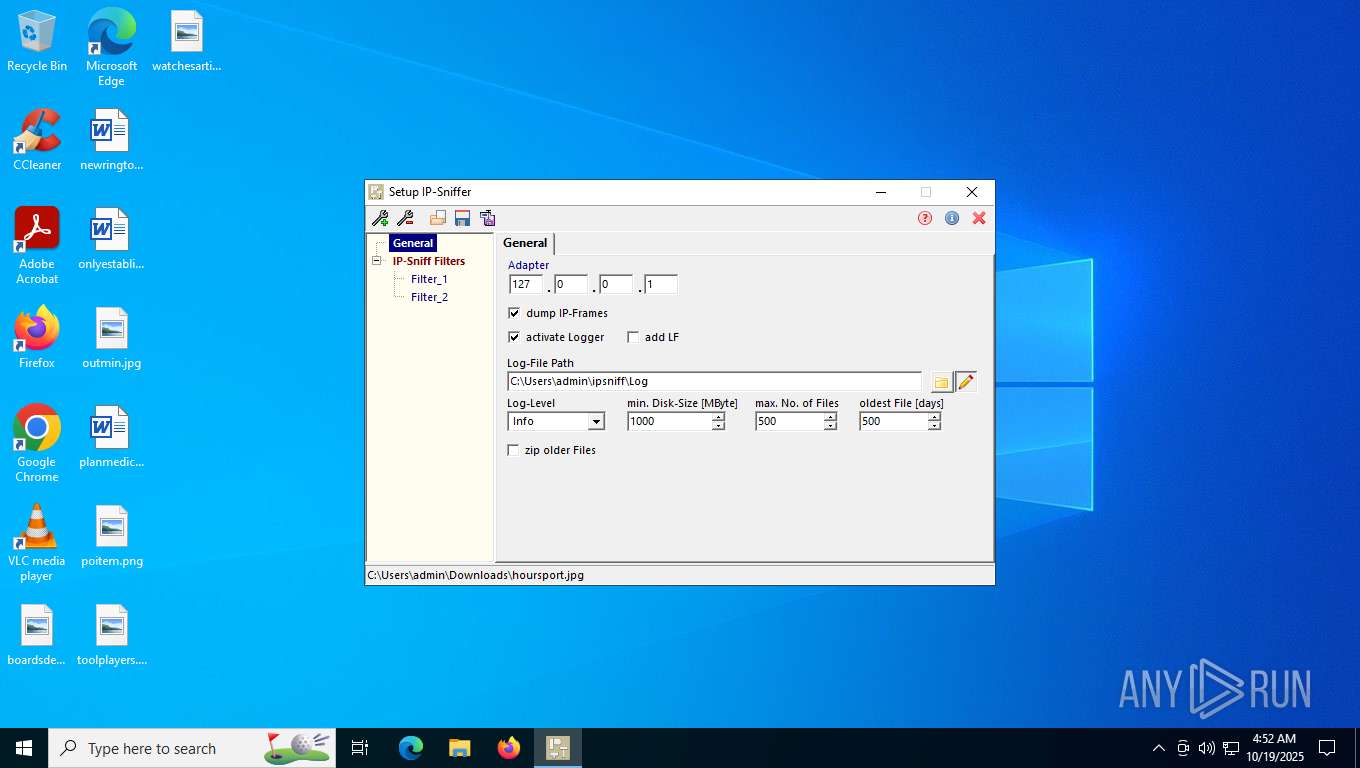
| FileDescription: | IP-Sniffer Setup |
| LegalCopyright: | Copyright (c) 2023 by decontev. All rights reserved. |
| ProductName: | IP-Tools |
| Comments: | - |
| FileVersion: | 5.8.5.2174 |
| InternalName: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductVersion: | - |
Total processes
161
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
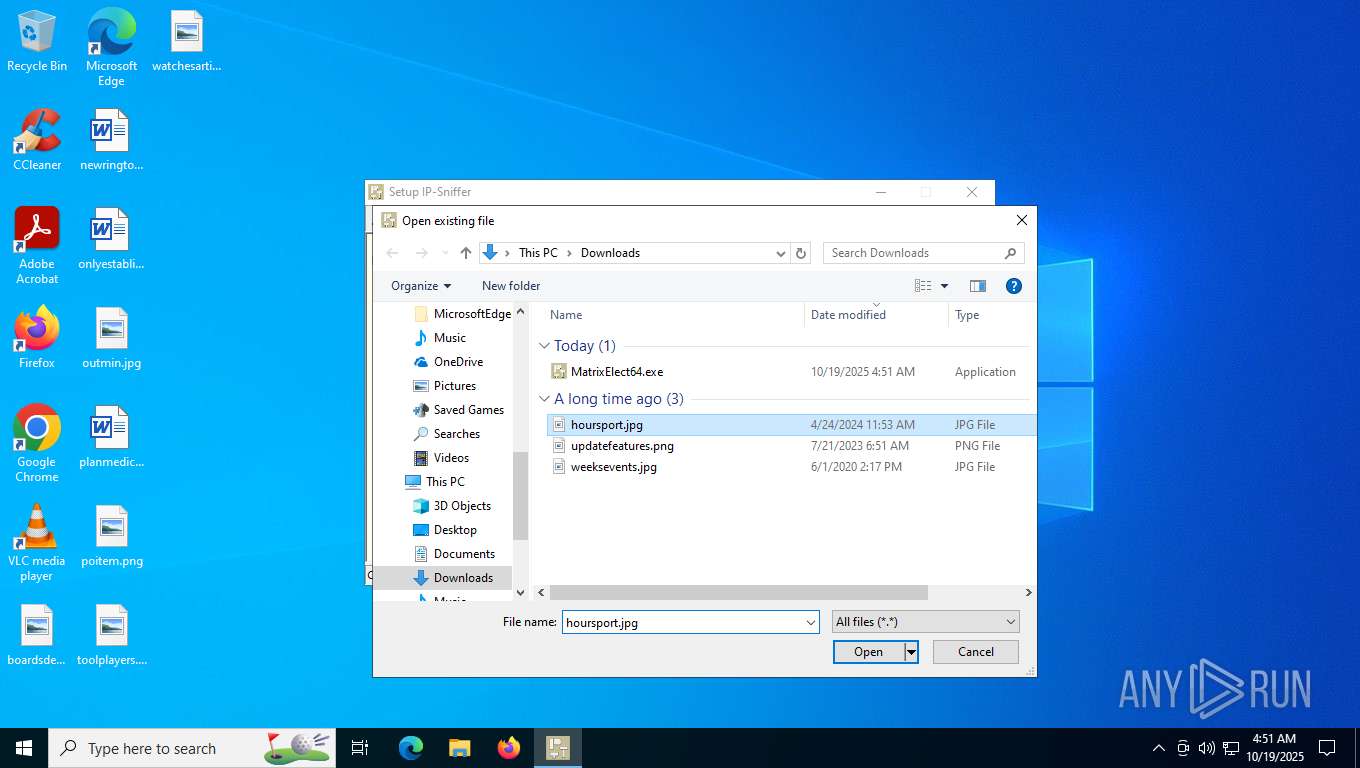
| 8300 | "C:\Users\admin\Downloads\MatrixElect64.exe" | C:\Users\admin\Downloads\MatrixElect64.exe | — | explorer.exe | |||||||||||
User: admin Company: decontev Integrity Level: MEDIUM Description: IP-Sniffer Setup Version: 5.8.5.2174 Modules
| |||||||||||||||
| 8776 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 873
Read events
5 787
Write events
81
Delete events
5
Modification events
| (PID) Process: | (8300) MatrixElect64.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (8300) MatrixElect64.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000300000000000000110000000E000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (8300) MatrixElect64.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\120\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Downloads | |||
| (PID) Process: | (8300) MatrixElect64.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\120\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Pictures | |||
| (PID) Process: | (8300) MatrixElect64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 130 | |||
| (PID) Process: | (8300) MatrixElect64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 556EF46800000000 | |||
| (PID) Process: | (8300) MatrixElect64.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\120\ComDlg\{885A186E-A440-4ADA-812B-DB871B942259} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (8300) MatrixElect64.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\120\ComDlg\{885A186E-A440-4ADA-812B-DB871B942259} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (8300) MatrixElect64.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\120\ComDlg\{885A186E-A440-4ADA-812B-DB871B942259} |
| Operation: | write | Name: | FFlags |
Value: | |||
| (PID) Process: | (8300) MatrixElect64.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\120\ComDlg\{885A186E-A440-4ADA-812B-DB871B942259} |
| Operation: | write | Name: | IconSize |
Value: 16 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8300 | MatrixElect64.exe | C:\Users\admin\AppData\Roaming\decontev\IpSniffSetup\ipsniffset_0.ini | text | |
MD5:D44A18CCC437D3CBB4135184579DFB44 | SHA256:897E8155C6EF8E63B7AC8580EF2FCA7555480177223A3CE92984E2841D1149A9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
4
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6016 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6868 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6016 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5948 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2960 | slui.exe | 4.154.209.85:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |