| download: | krnl_bootstrapper_console_version.exe |
| Full analysis: | https://app.any.run/tasks/cac42f3c-eee4-43cc-a305-b03f811024a7 |
| Verdict: | Malicious activity |
| Analysis date: | June 05, 2020, 20:36:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 1929F21E17004FD0159DBB8F2B8E4165 |
| SHA1: | 707602519F4FEBCE10BC91CFD0DF8E6CE0ADB215 |
| SHA256: | 947F2A6ADED12C465E6E6B564A8836FCE696F0887A6AEC336481D7DF0341ABAE |
| SSDEEP: | 768:LptcUOoMlkTtlfd8KzimcMtQQck0YKsxSV:NtcUilkTtlf6uimAkuV |
MALICIOUS
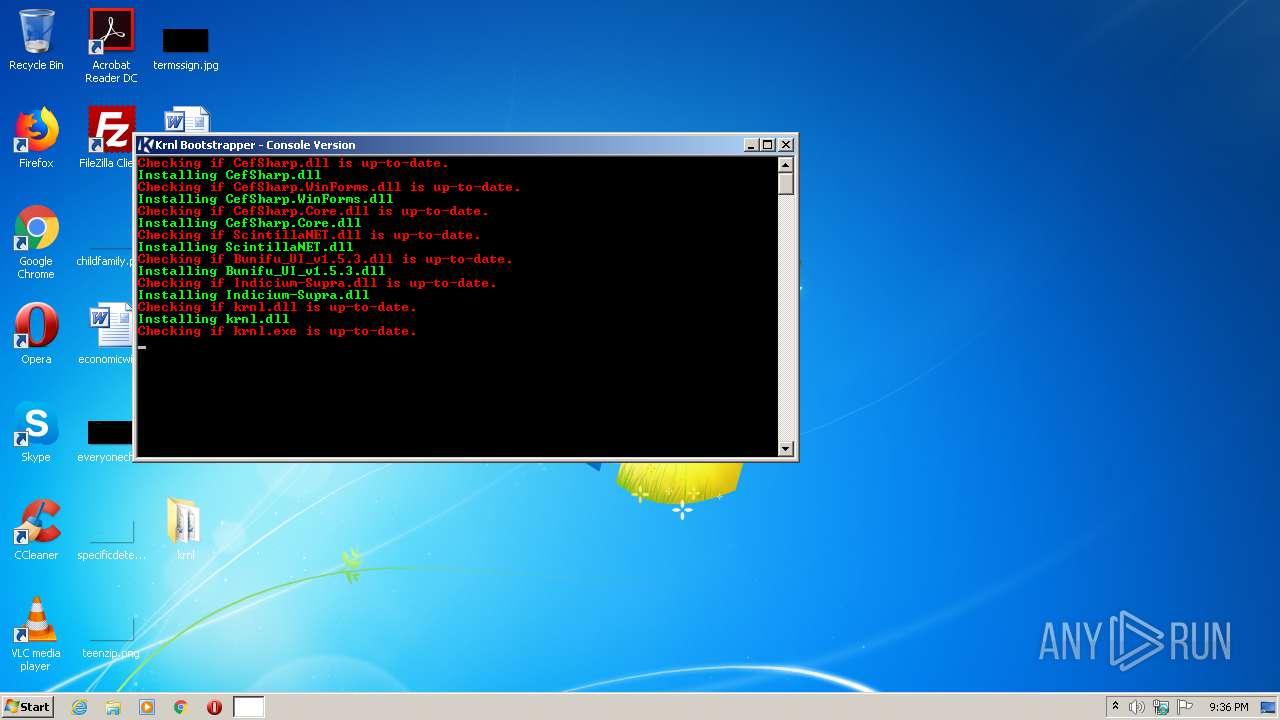
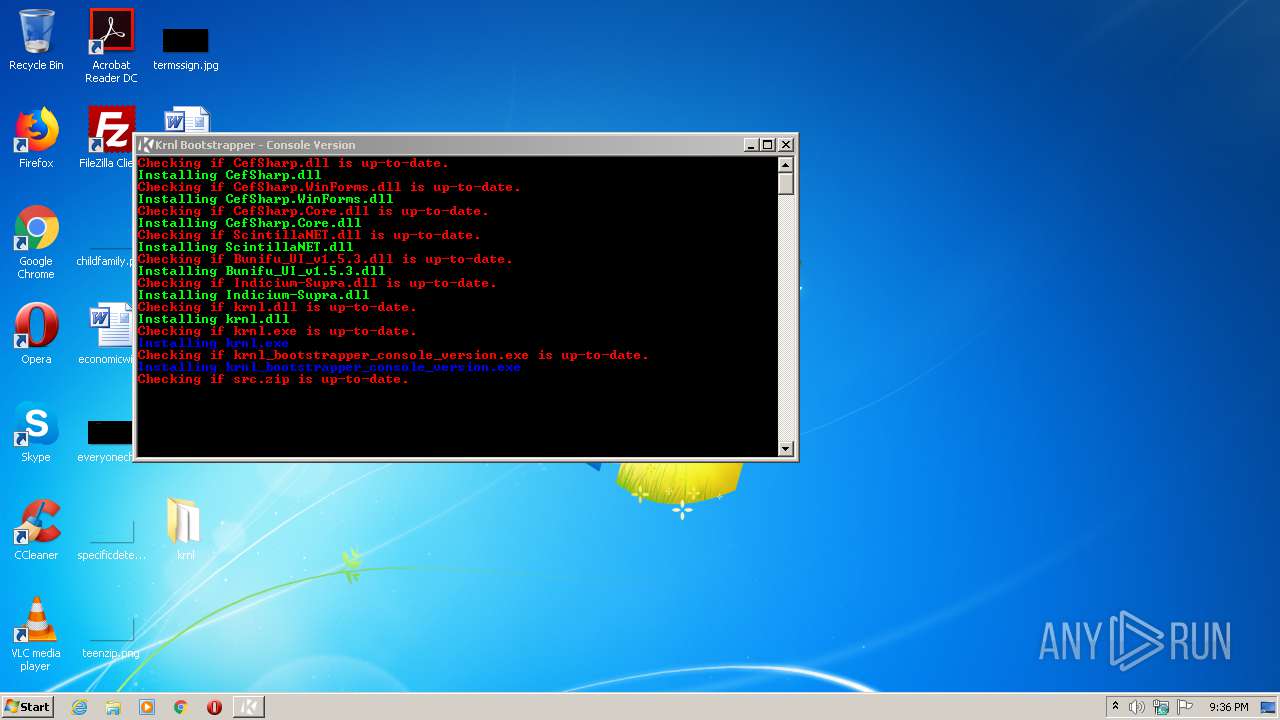
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3560)
- krnl.exe (PID: 2132)
Application was dropped or rewritten from another process
- krnl.exe (PID: 2132)
SUSPICIOUS
Executable content was dropped or overwritten
- krnl_bootstrapper_console_version.exe (PID: 1156)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2101:06:15 22:02:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 29184 |
| InitializedDataSize: | 190464 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x91c6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Krnl Bootstrapper (Console Version) |
| FileVersion: | 1.0.0.0 |
| InternalName: | krnl_bootstrapper_console_version.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | krnl_bootstrapper_console_version.exe |
| ProductName: | Krnl Bootstrapper (Console Version) |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 09-May-1965 13:33:59 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Krnl Bootstrapper (Console Version) |
| FileVersion: | 1.0.0.0 |
| InternalName: | krnl_bootstrapper_console_version.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFilename: | krnl_bootstrapper_console_version.exe |
| ProductName: | Krnl Bootstrapper (Console Version) |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 09-May-1965 13:33:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000071D4 | 0x00007200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.48523 |
.rsrc | 0x0000A000 | 0x0002E558 | 0x0002E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.24564 |
.reloc | 0x0003A000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 2.10543 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 1.9881 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 1.69507 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 1.07419 | 170248 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.88636 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
37
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1156 | "C:\Users\admin\Desktop\krnl_bootstrapper_console_version.exe" | C:\Users\admin\Desktop\krnl_bootstrapper_console_version.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Krnl Bootstrapper (Console Version) Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2132 | "C:\Users\admin\Desktop\krnl\krnl.exe" | C:\Users\admin\Desktop\krnl\krnl.exe | — | krnl_bootstrapper_console_version.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: krnlss Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3560 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
483
Read events
445
Write events
38
Delete events
0
Modification events
| (PID) Process: | (1156) krnl_bootstrapper_console_version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_bootstrapper_console_version_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1156) krnl_bootstrapper_console_version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_bootstrapper_console_version_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1156) krnl_bootstrapper_console_version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_bootstrapper_console_version_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1156) krnl_bootstrapper_console_version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_bootstrapper_console_version_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1156) krnl_bootstrapper_console_version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_bootstrapper_console_version_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1156) krnl_bootstrapper_console_version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_bootstrapper_console_version_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1156) krnl_bootstrapper_console_version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_bootstrapper_console_version_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1156) krnl_bootstrapper_console_version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_bootstrapper_console_version_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1156) krnl_bootstrapper_console_version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_bootstrapper_console_version_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1156) krnl_bootstrapper_console_version.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\krnl_bootstrapper_console_version_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
24
Suspicious files
1
Text files
10
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1156 | krnl_bootstrapper_console_version.exe | C:\Users\admin\Desktop\krnl\src.zip | — | |
MD5:— | SHA256:— | |||
| 1156 | krnl_bootstrapper_console_version.exe | C:\Users\admin\Desktop\krnl\src\src\CefSharp.BrowserSubprocess.Core.pdb | — | |
MD5:— | SHA256:— | |||
| 1156 | krnl_bootstrapper_console_version.exe | C:\Users\admin\Desktop\krnl\src\src\CefSharp.Core.pdb | — | |
MD5:— | SHA256:— | |||
| 1156 | krnl_bootstrapper_console_version.exe | C:\Users\admin\Desktop\krnl\krnl.exe | executable | |
MD5:— | SHA256:— | |||
| 1156 | krnl_bootstrapper_console_version.exe | C:\Users\admin\Desktop\krnl\Indicium-Supra.dll | executable | |
MD5:— | SHA256:— | |||
| 1156 | krnl_bootstrapper_console_version.exe | C:\Users\admin\Desktop\krnl\krnl.dll | executable | |
MD5:— | SHA256:— | |||
| 1156 | krnl_bootstrapper_console_version.exe | C:\Users\admin\Desktop\krnl\krnl_bootstrapper_console_version.exe | executable | |
MD5:— | SHA256:— | |||
| 1156 | krnl_bootstrapper_console_version.exe | C:\Users\admin\Desktop\krnl\CefSharp.WinForms.dll | executable | |
MD5:5E5FE029BFF022007C27D024AE7CF262 | SHA256:7BEE1EAD1FE16CC4BAE25758D1708163489724427F4B540B21CE1E943F070C3B | |||
| 1156 | krnl_bootstrapper_console_version.exe | C:\Users\admin\Desktop\krnl\Bunifu_UI_v1.5.3.dll | executable | |
MD5:2ECB51AB00C5F340380ECF849291DBCF | SHA256:F1B3E0F2750A9103E46A6A4A34F1CF9D17779725F98042CC2475EC66484801CF | |||
| 1156 | krnl_bootstrapper_console_version.exe | C:\Users\admin\Desktop\krnl\ScintillaNET.dll | executable | |
MD5:9166536C31F4E725E6BEFE85E2889A4B | SHA256:AD0CC5A4D4A6AAE06EE360339C851892B74B8A275CE89C1B48185672179F3163 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1156 | krnl_bootstrapper_console_version.exe | 104.23.99.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
1156 | krnl_bootstrapper_console_version.exe | 162.159.133.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
cdn.discordapp.com |
| shared |