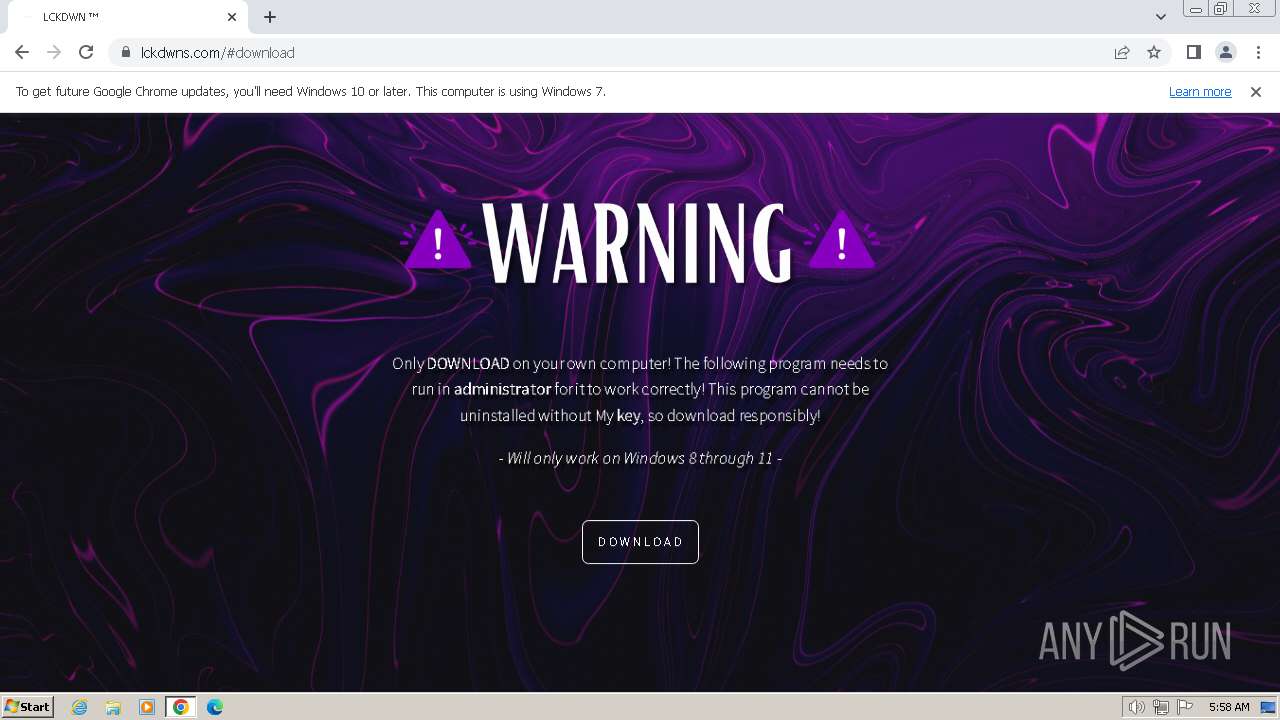
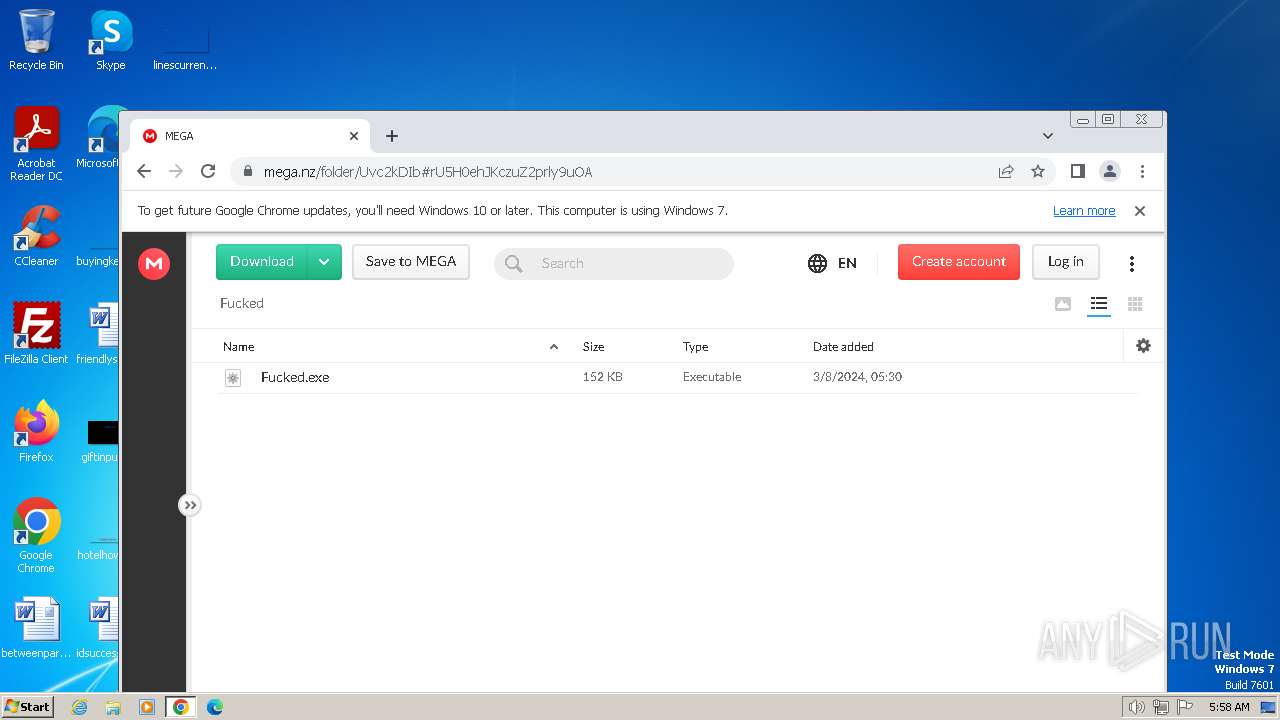
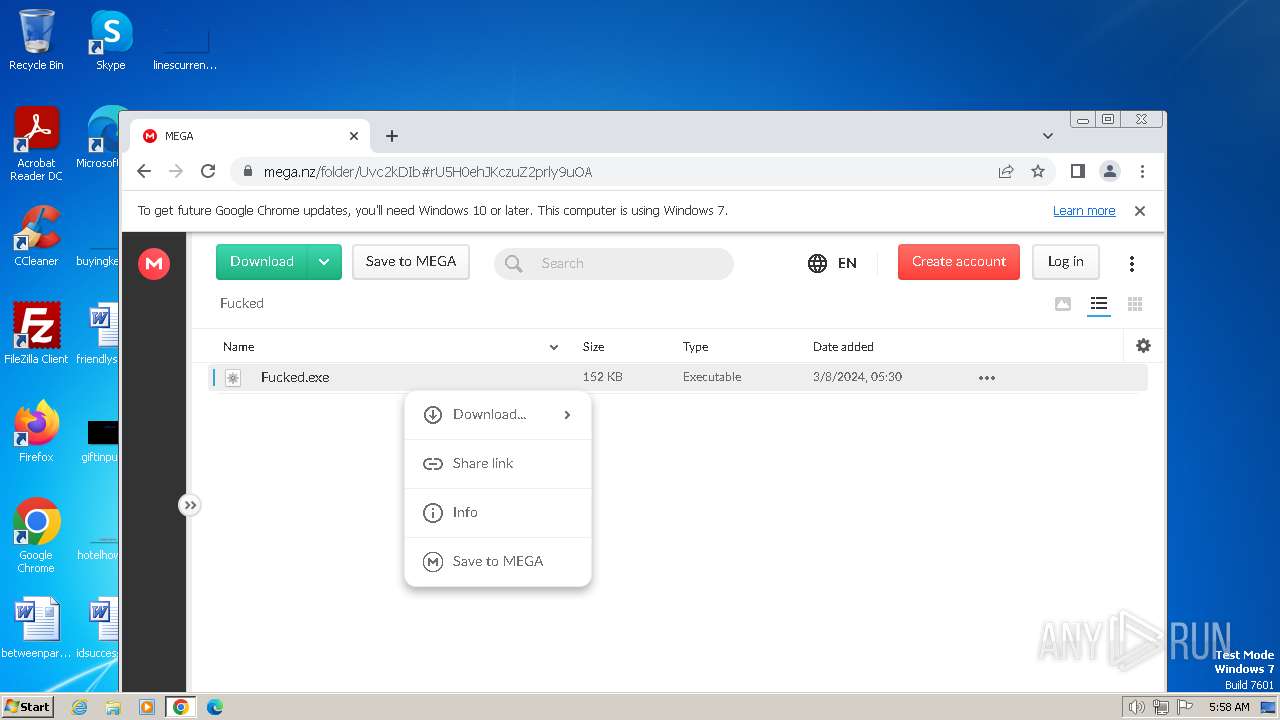
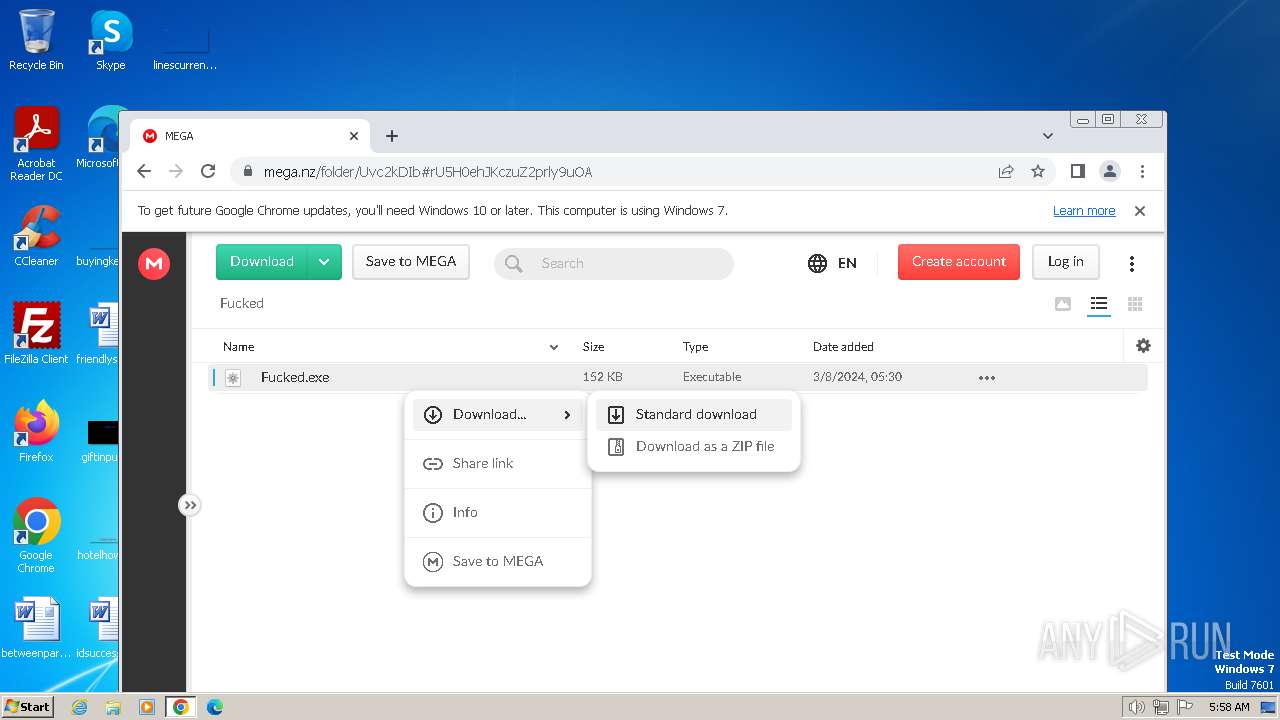
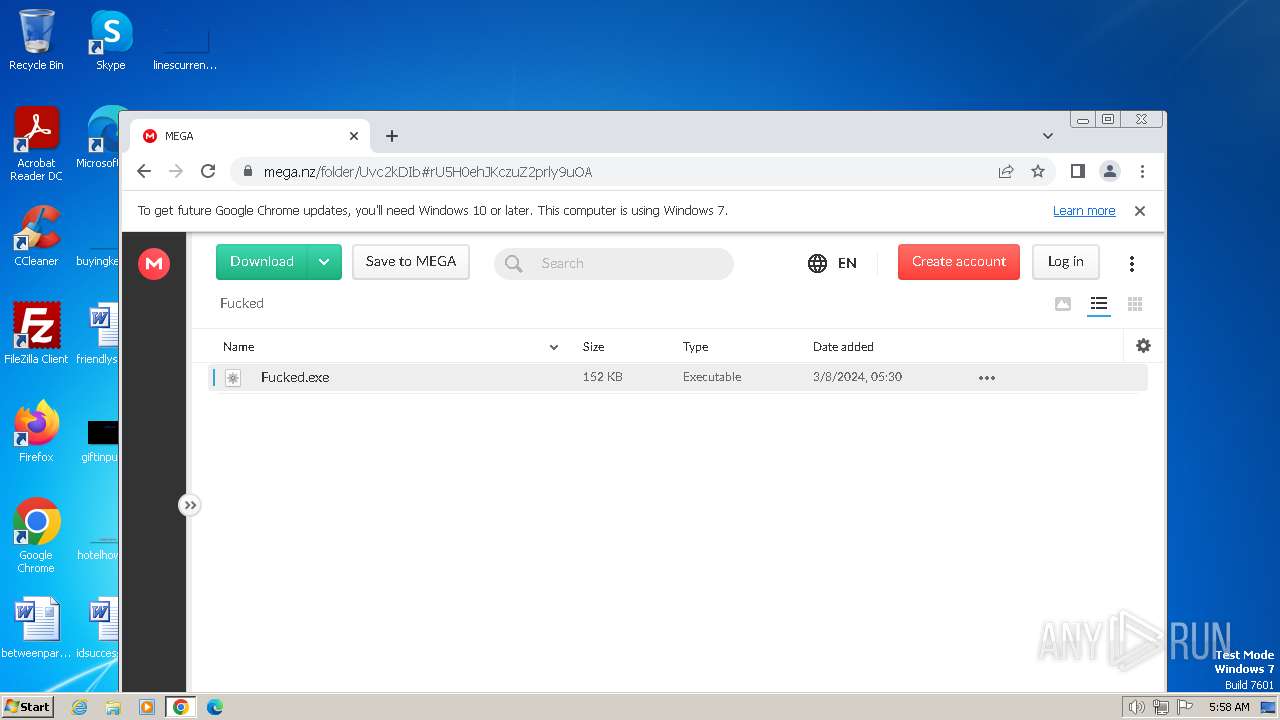
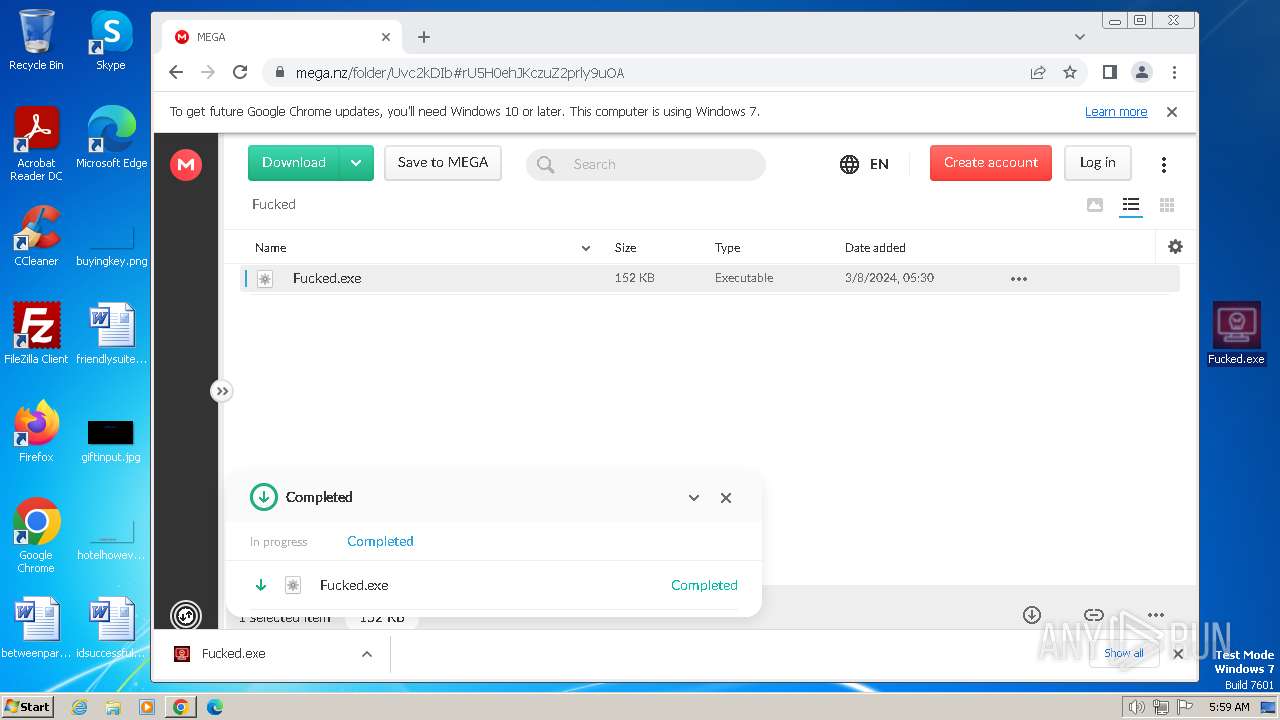
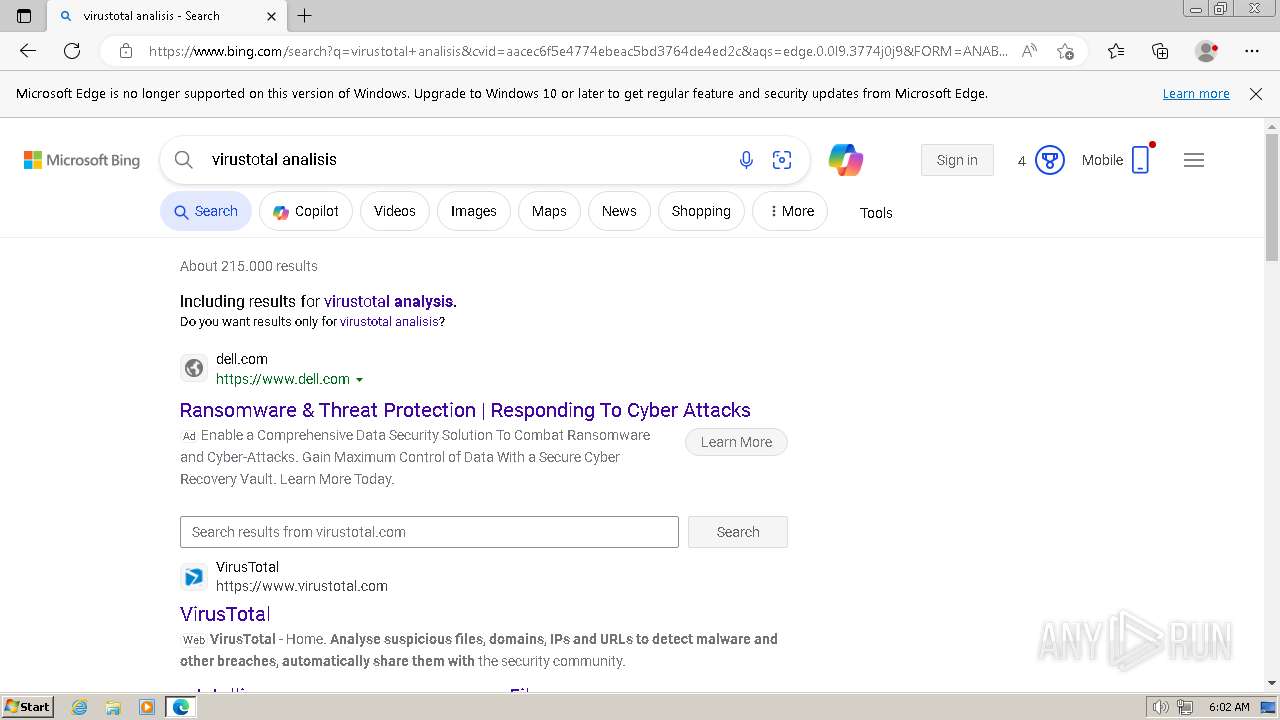
| URL: | https://lckdwns.com/ |
| Full analysis: | https://app.any.run/tasks/b19c17ae-e686-4ba3-8637-d35b8c001114 |
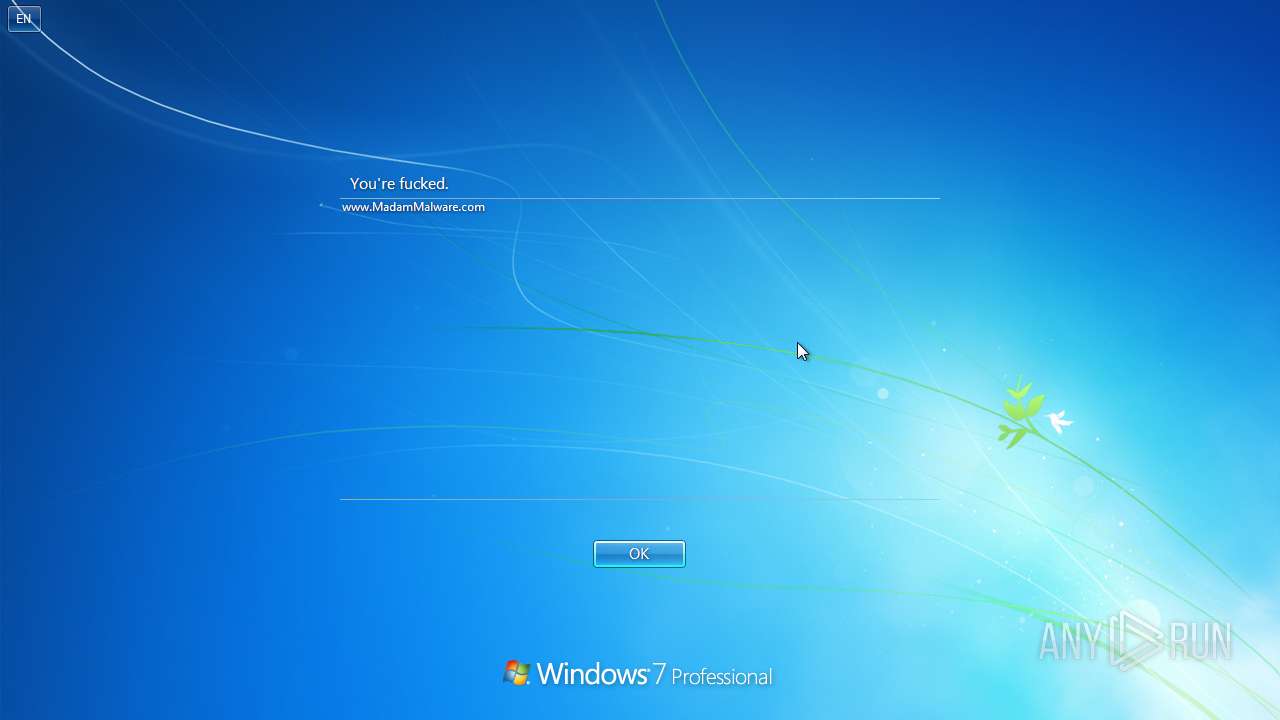
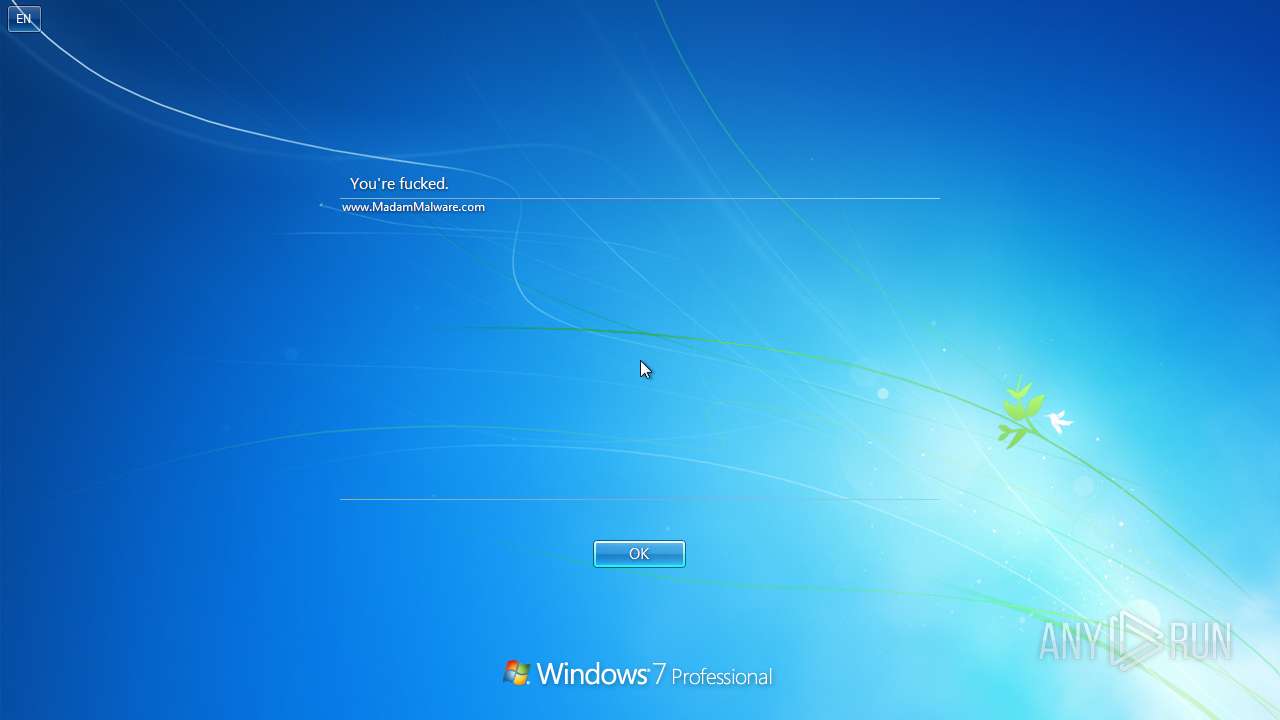
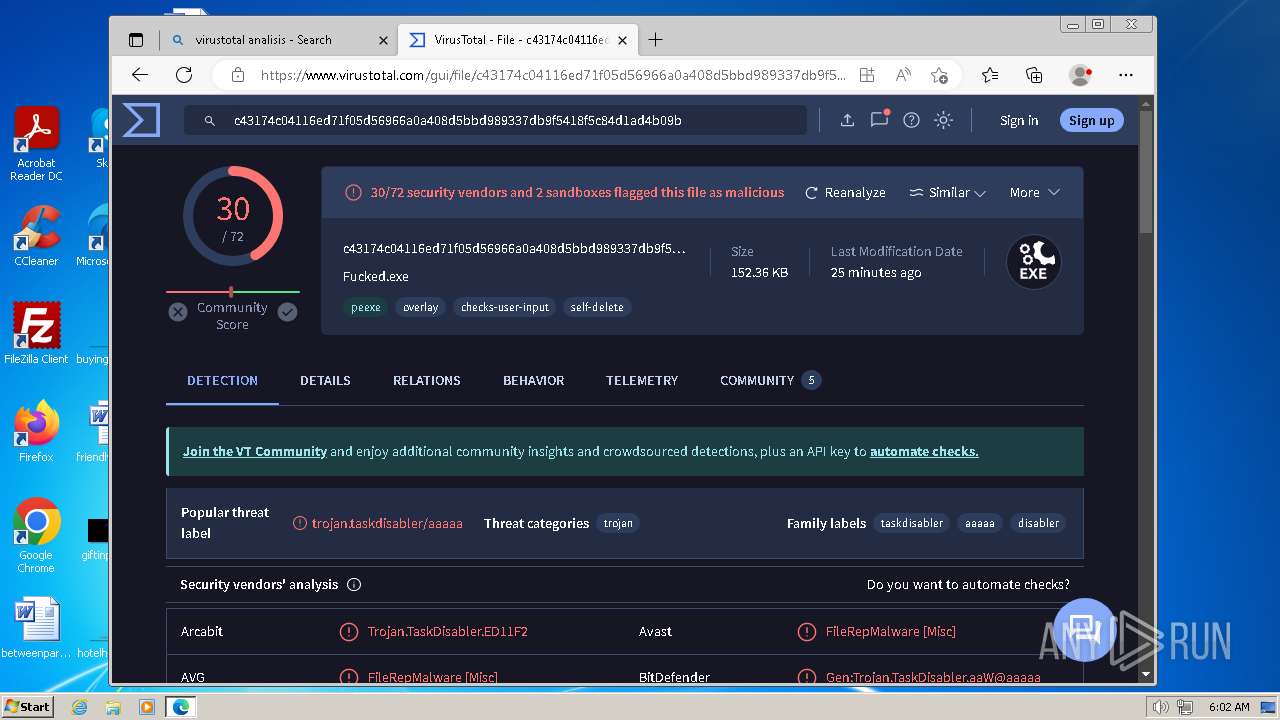
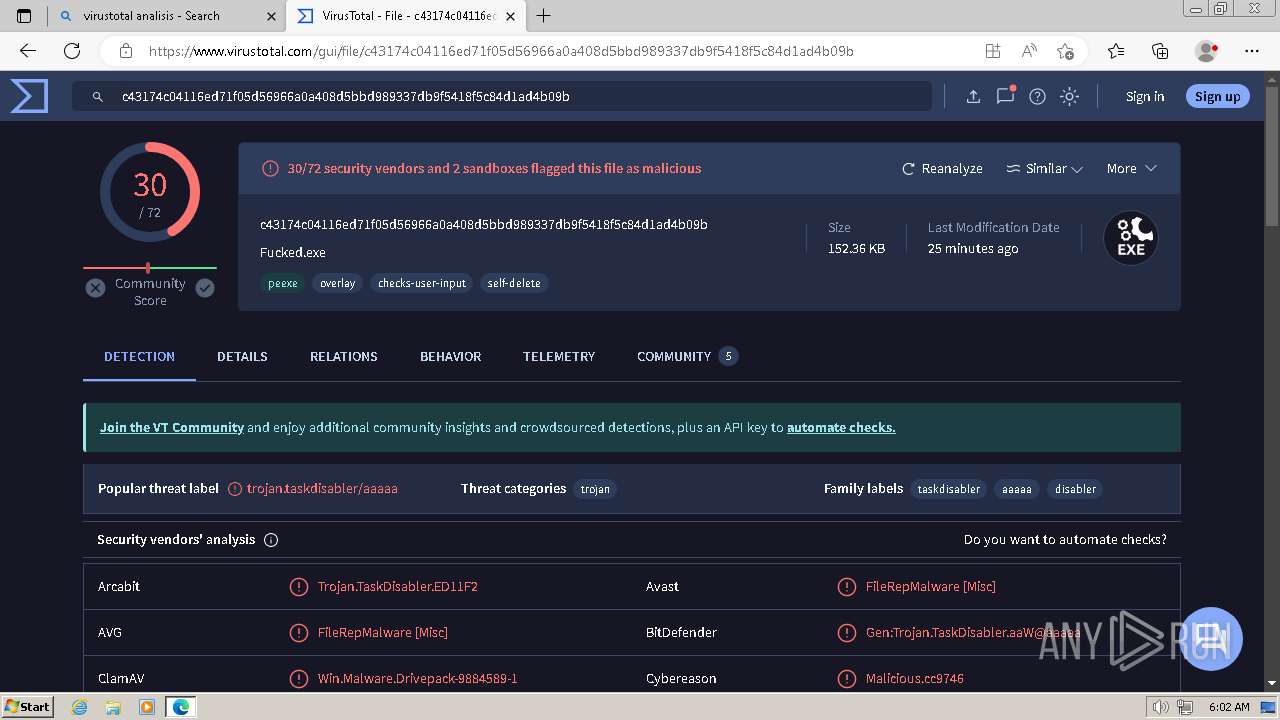
| Verdict: | Malicious activity |
| Analysis date: | March 09, 2024, 05:58:27 |
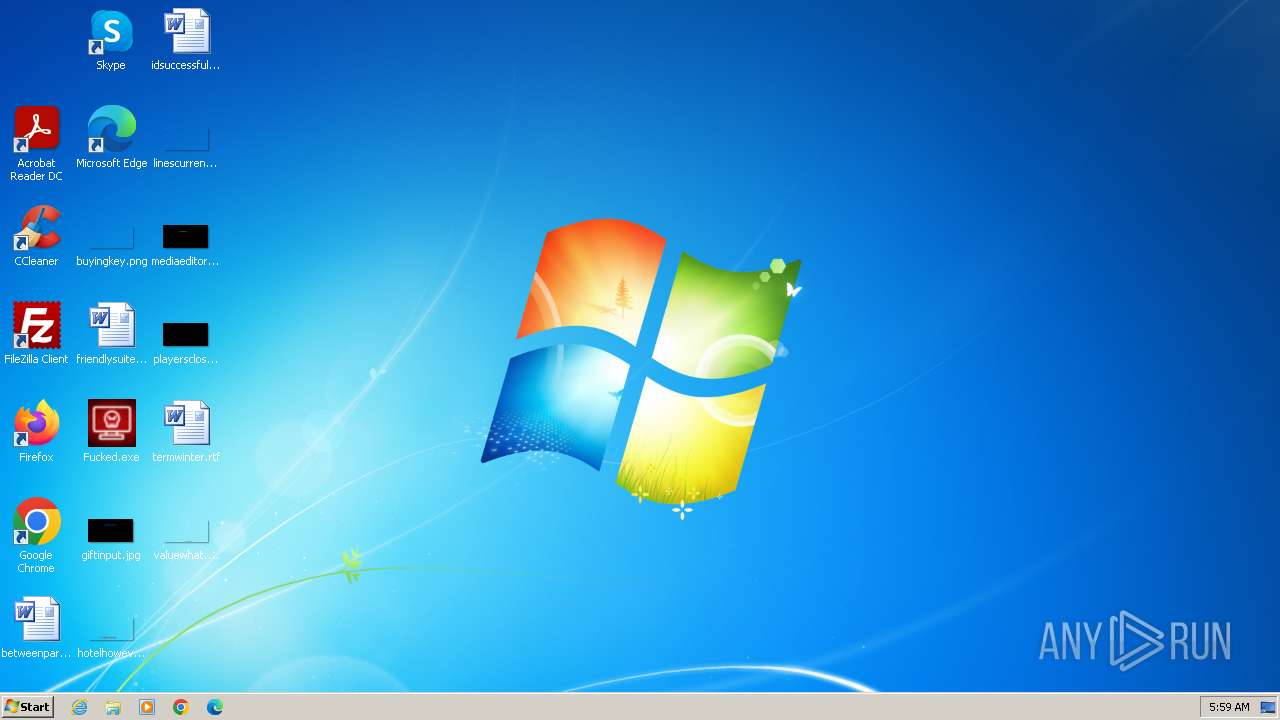
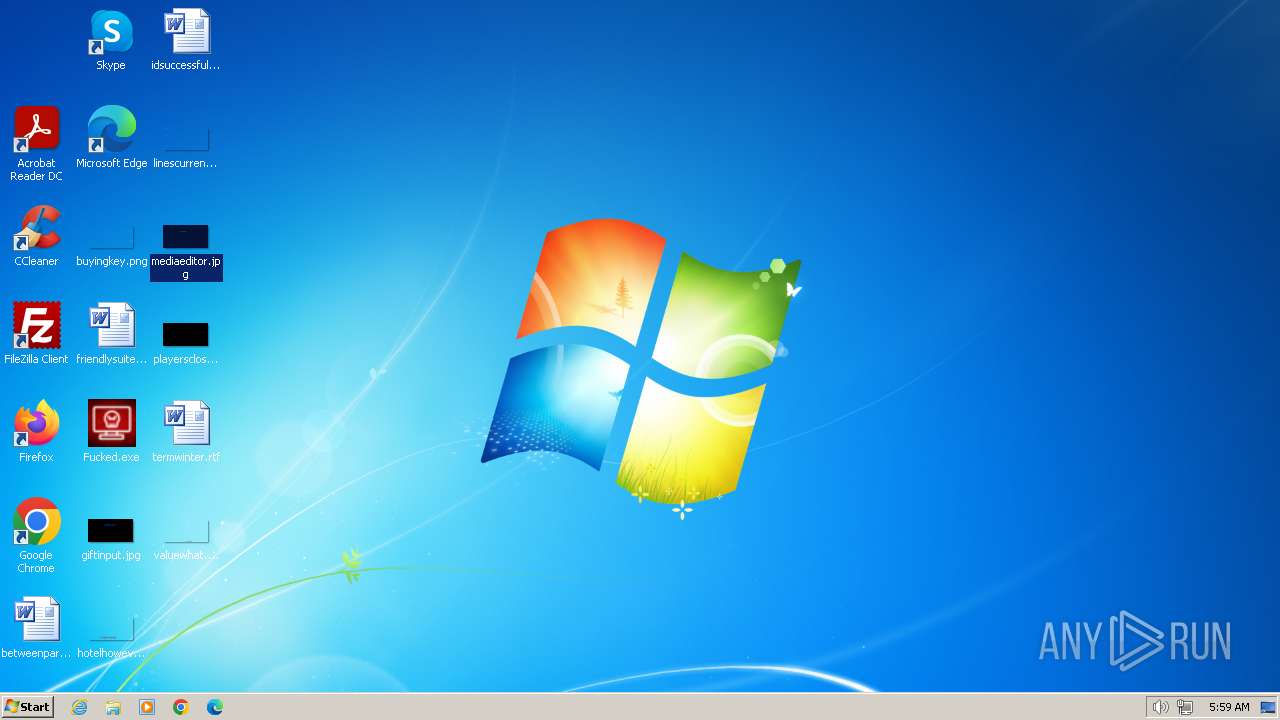
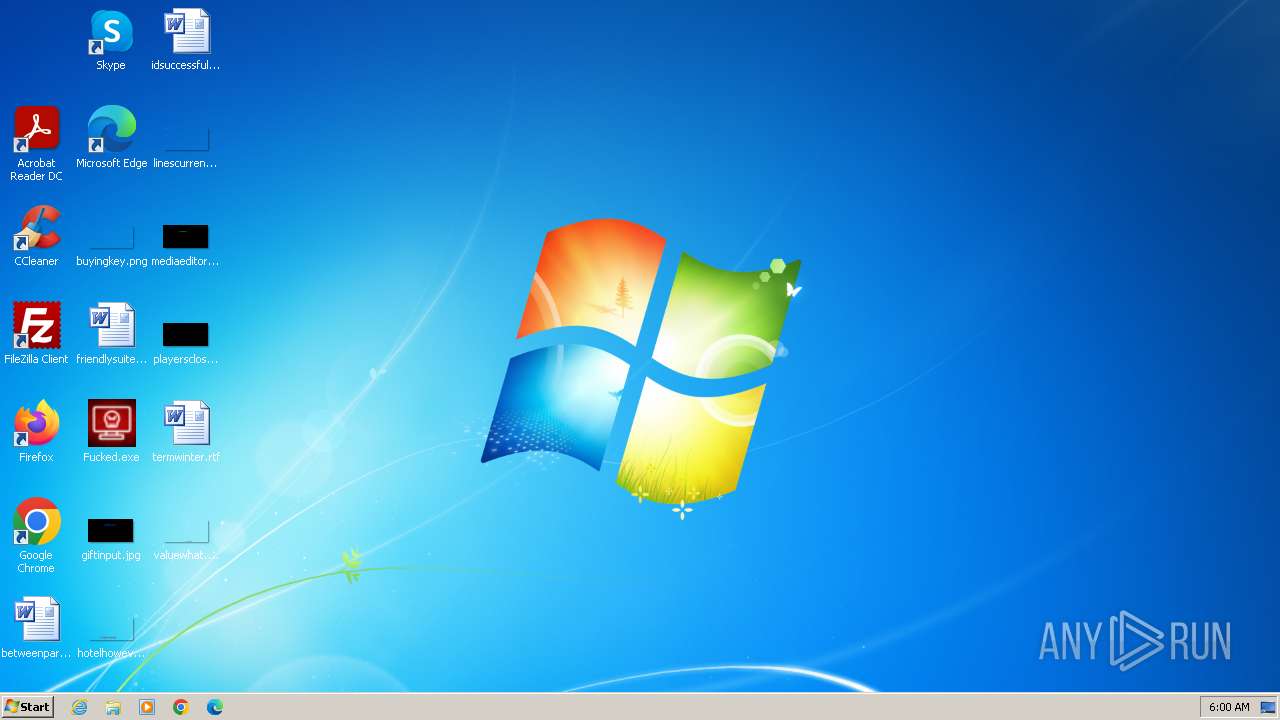
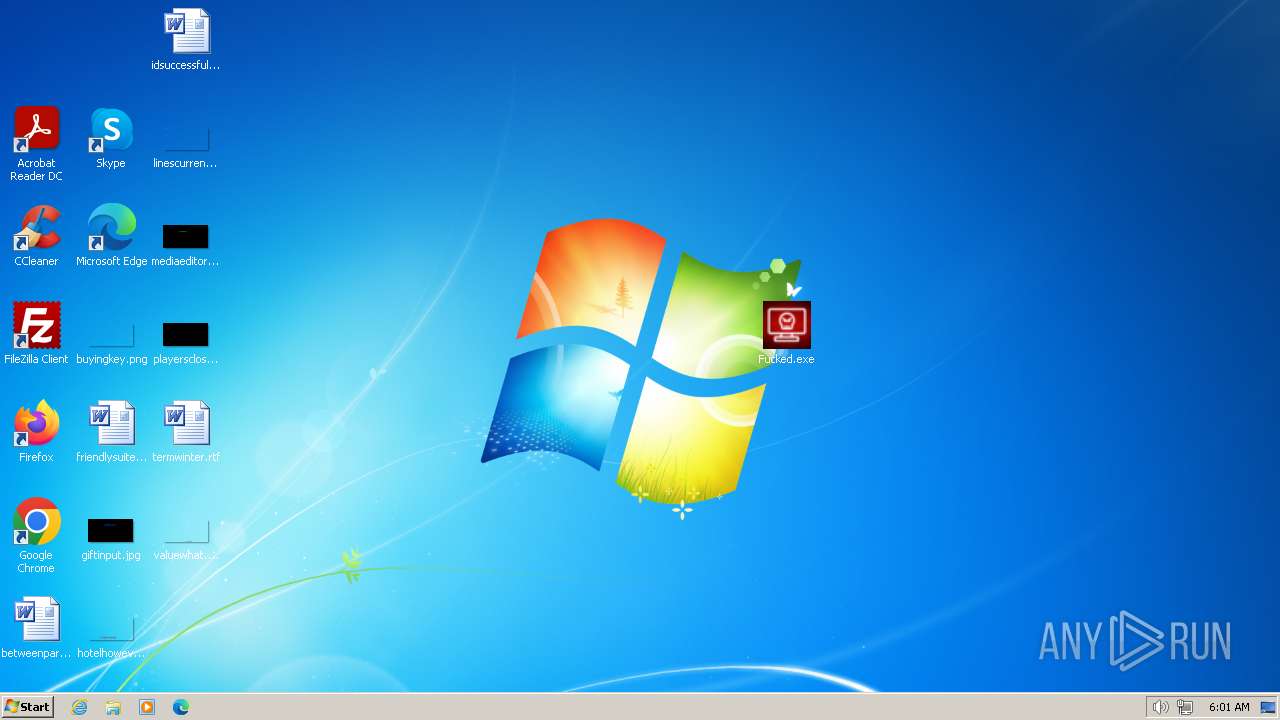
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A9E815F1752E909C8A202D8319863748 |
| SHA1: | 9859CCC12F08FA7CDBCE8D22E642128D9DA0326F |
| SHA256: | 94668EC785049A3252AA47DD6189107D67CE0A0979D79886BCE157304E67EAA1 |
| SSDEEP: | 3:N8GuSiLKK:2GdoR |
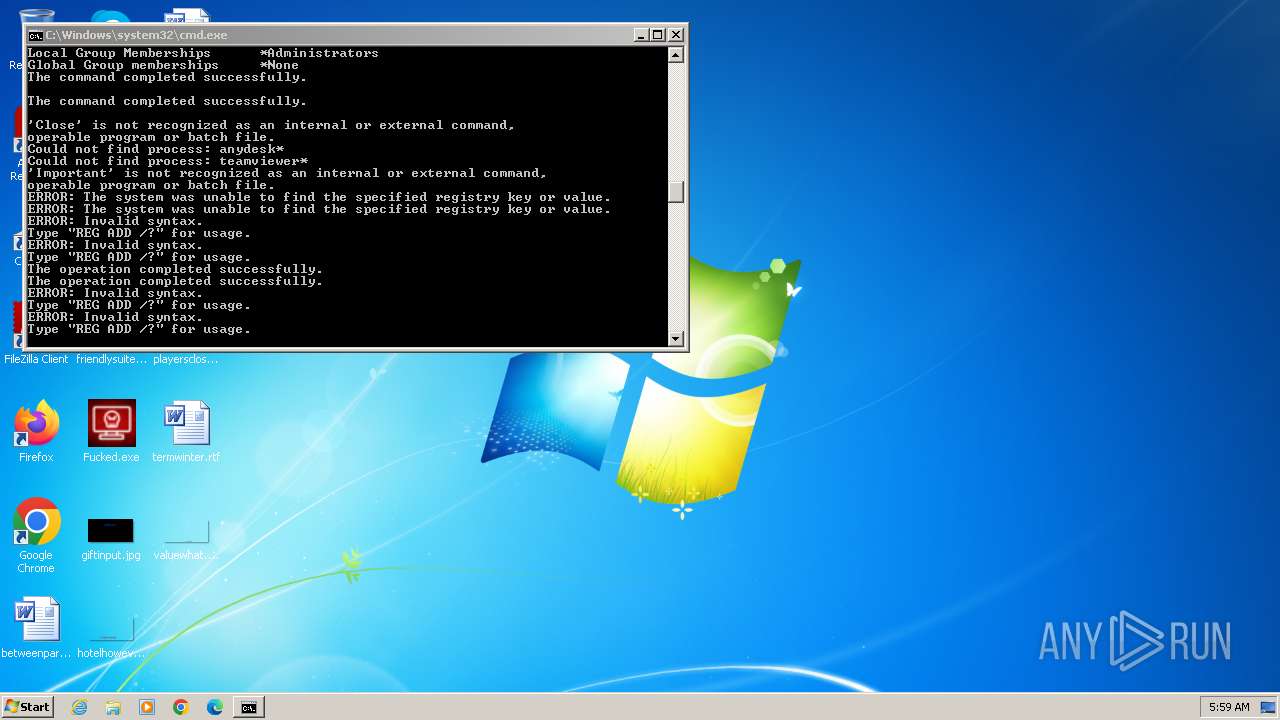
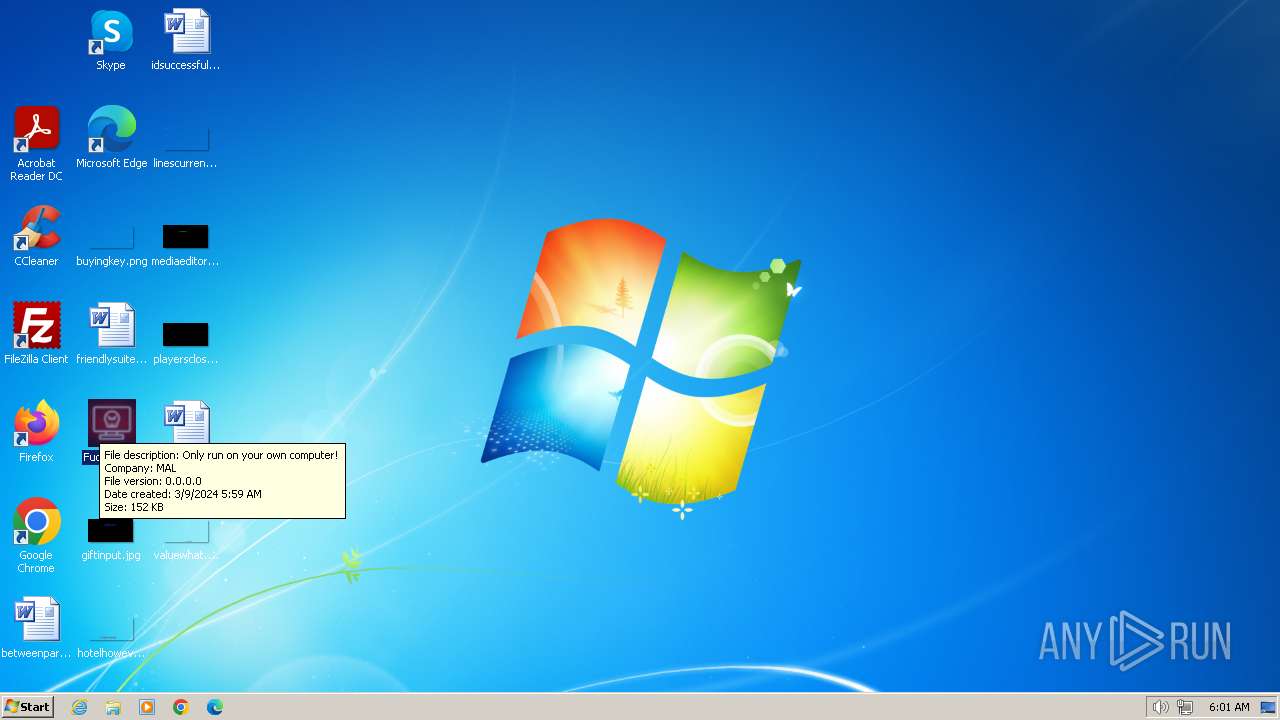
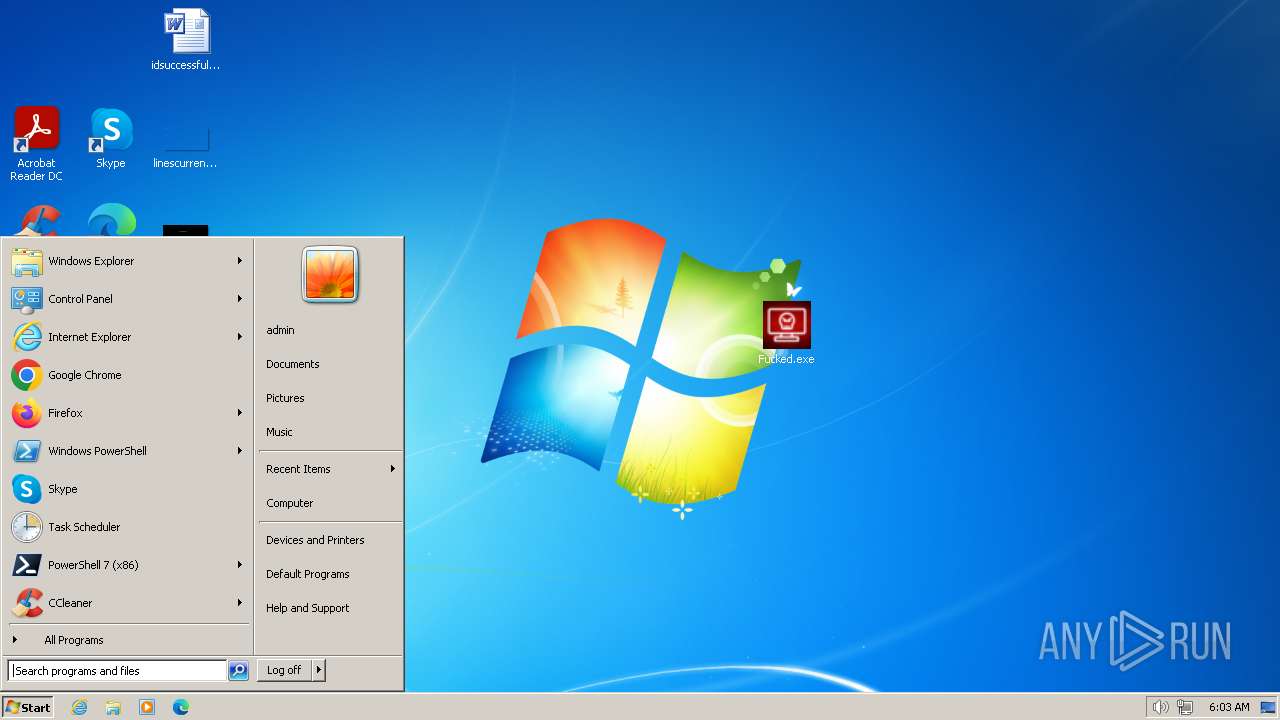
MALICIOUS
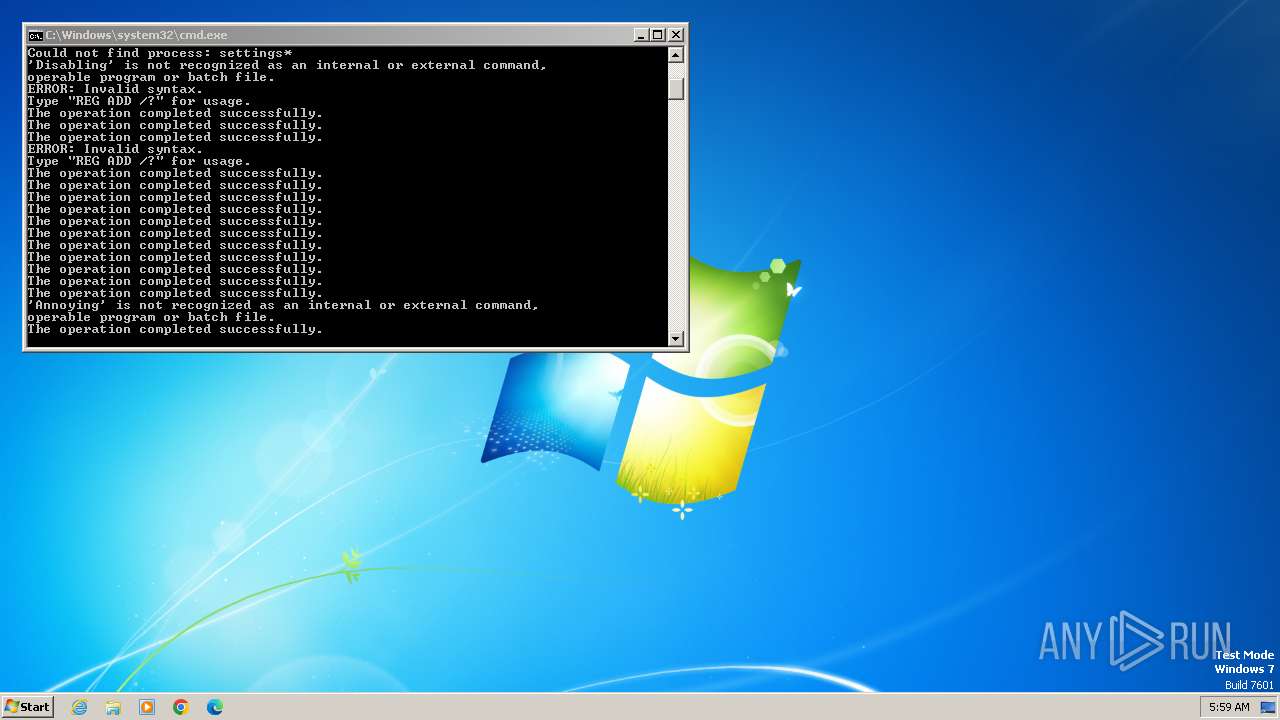
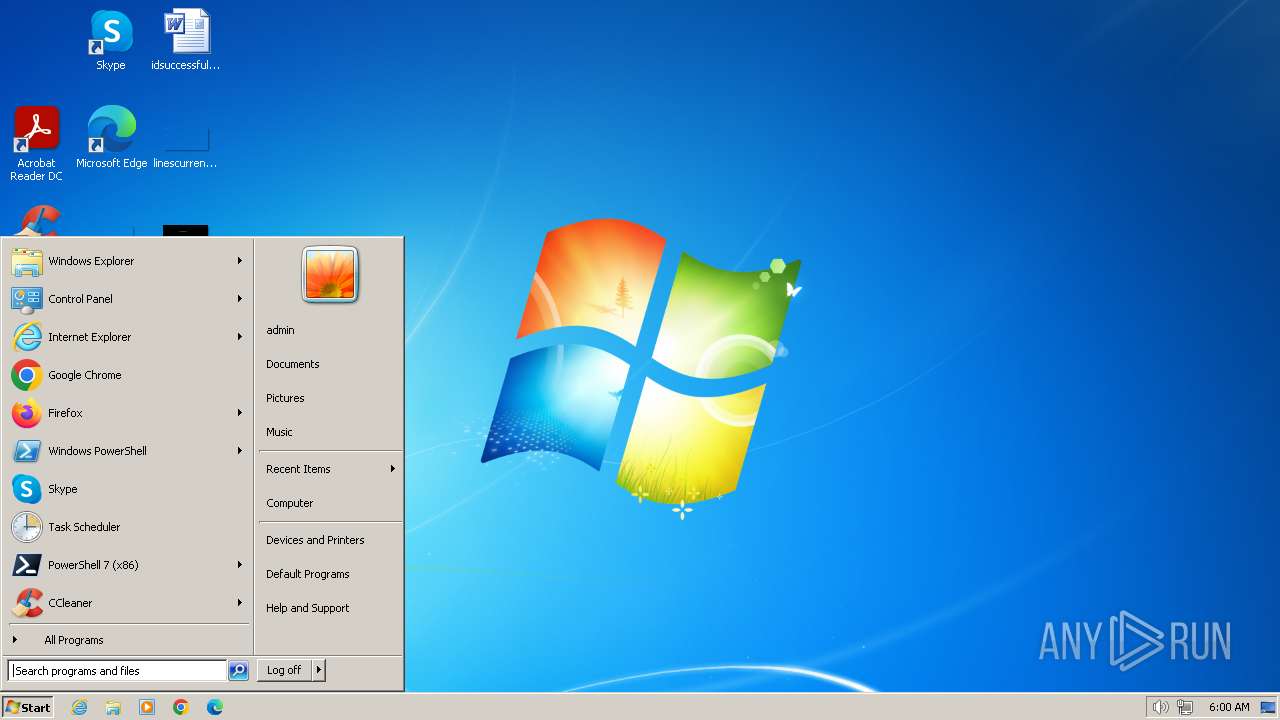
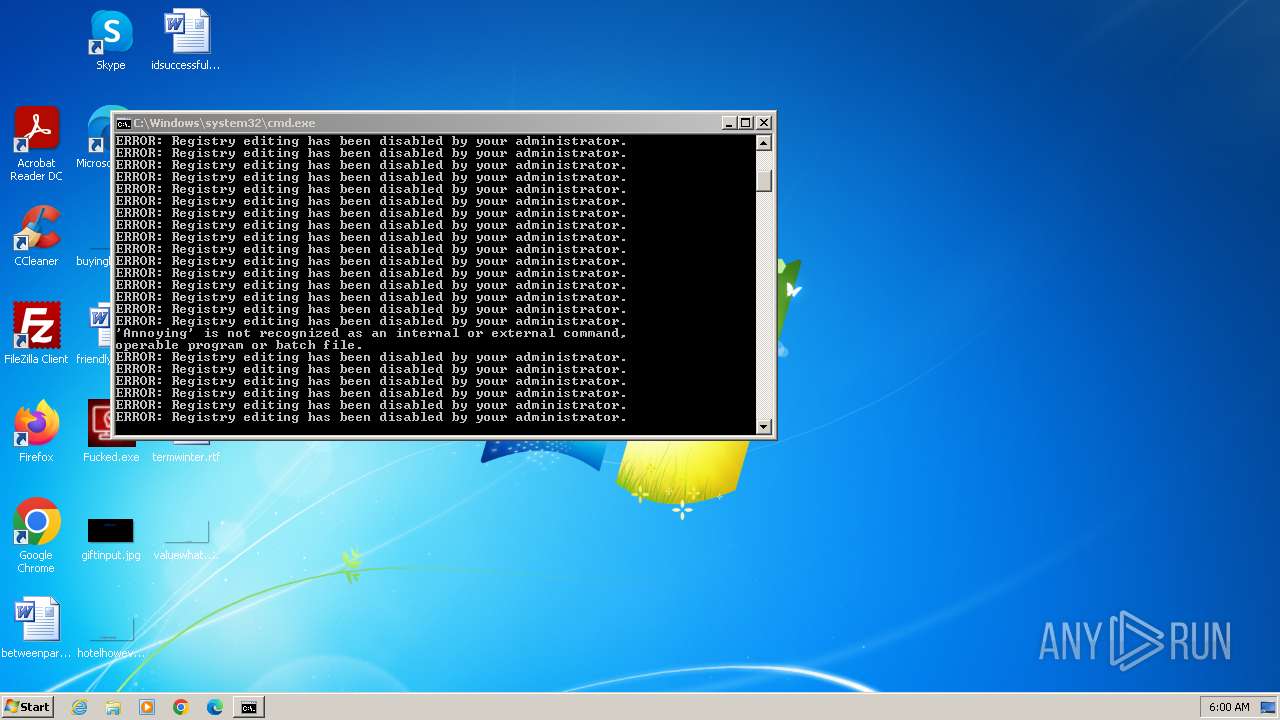
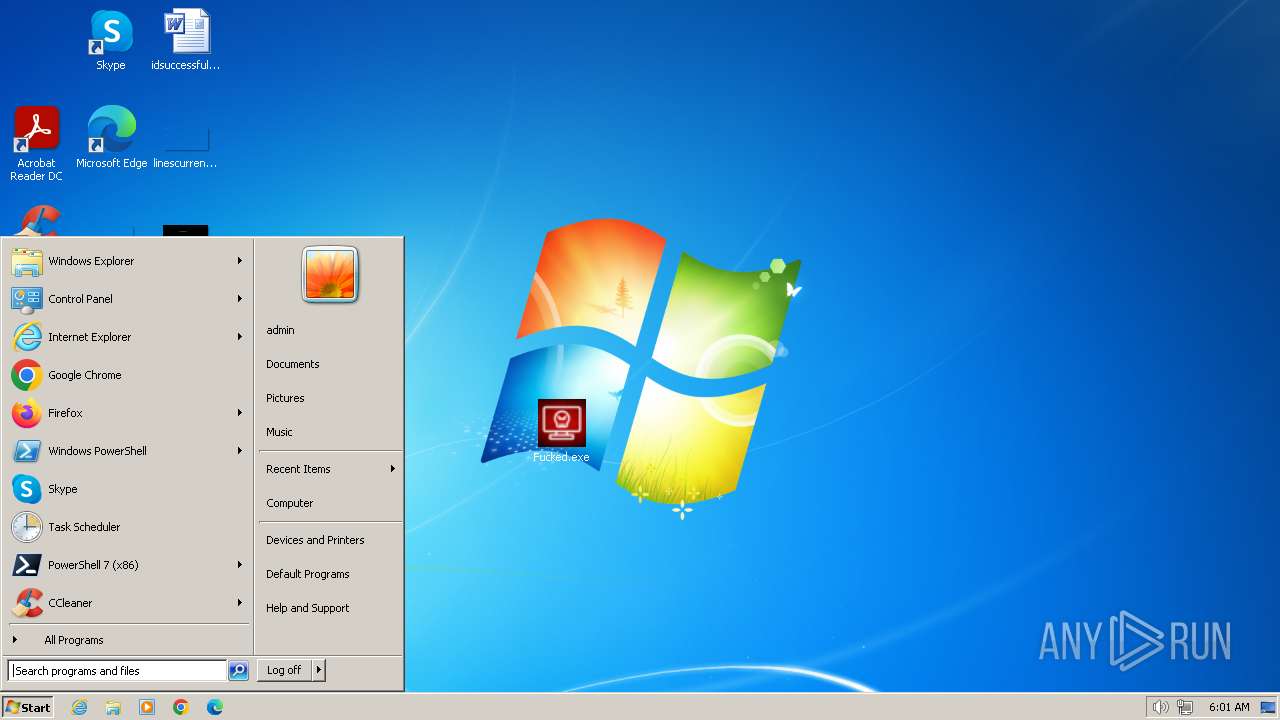
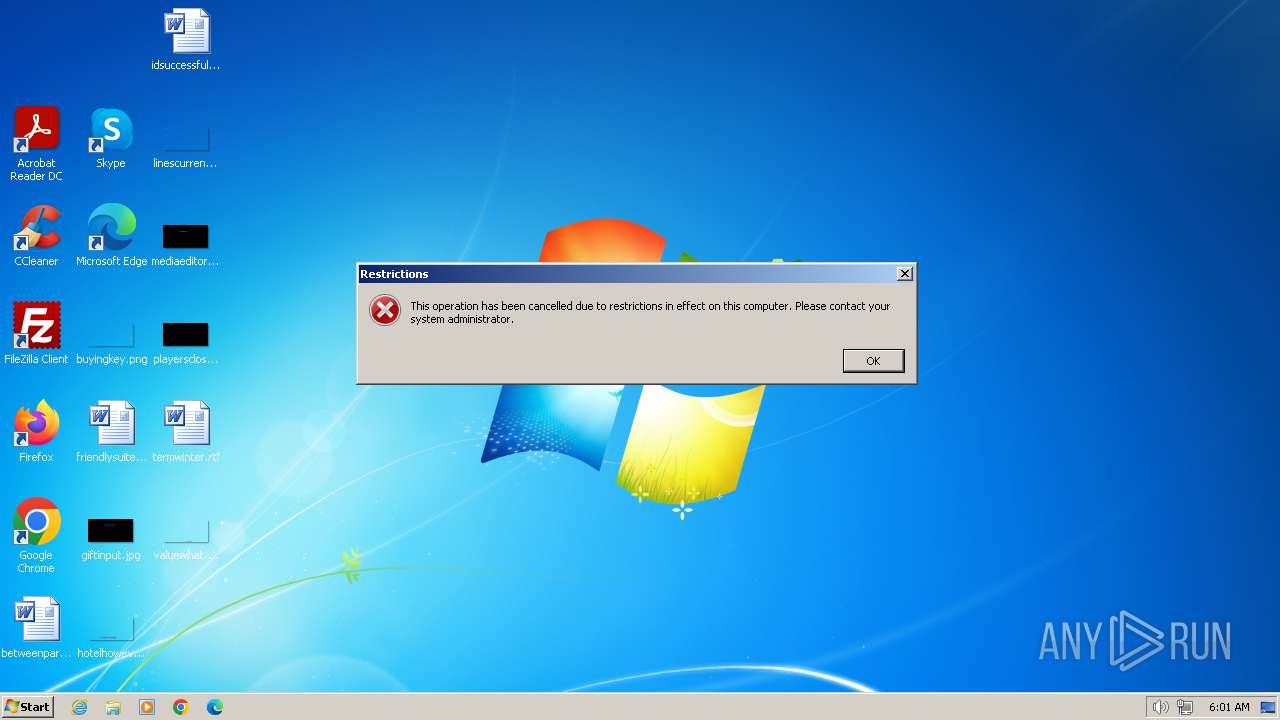
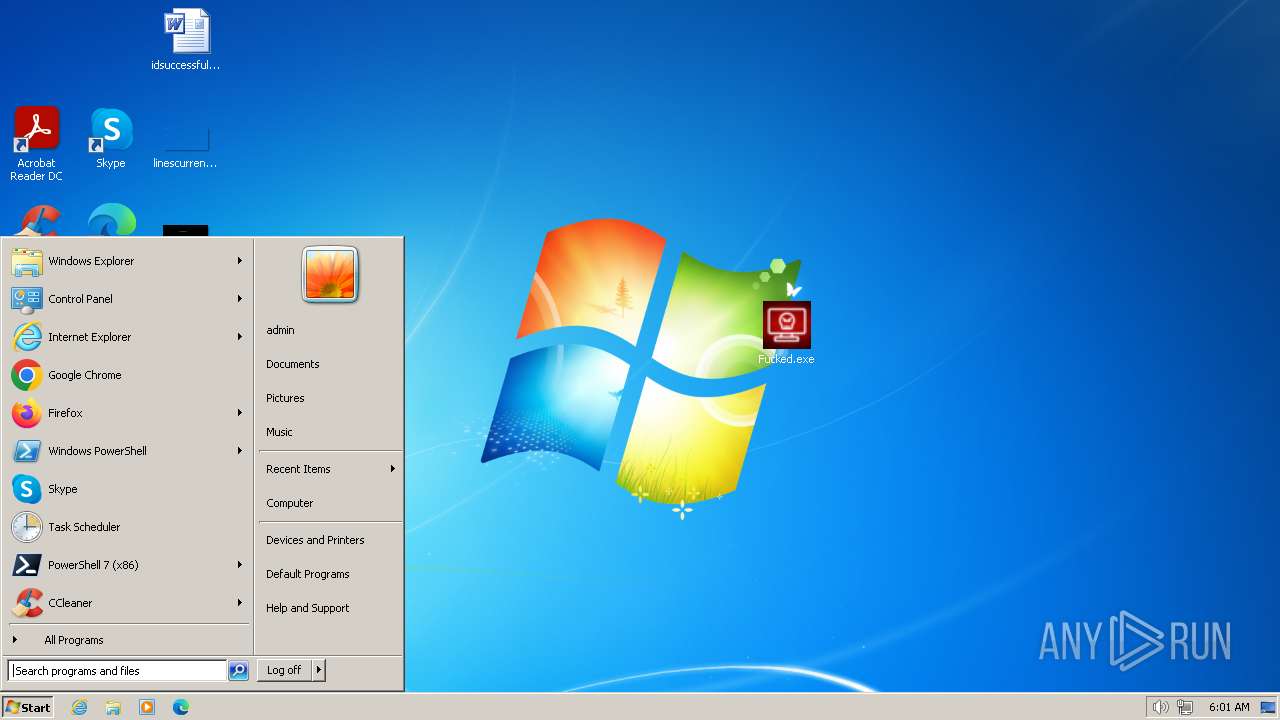
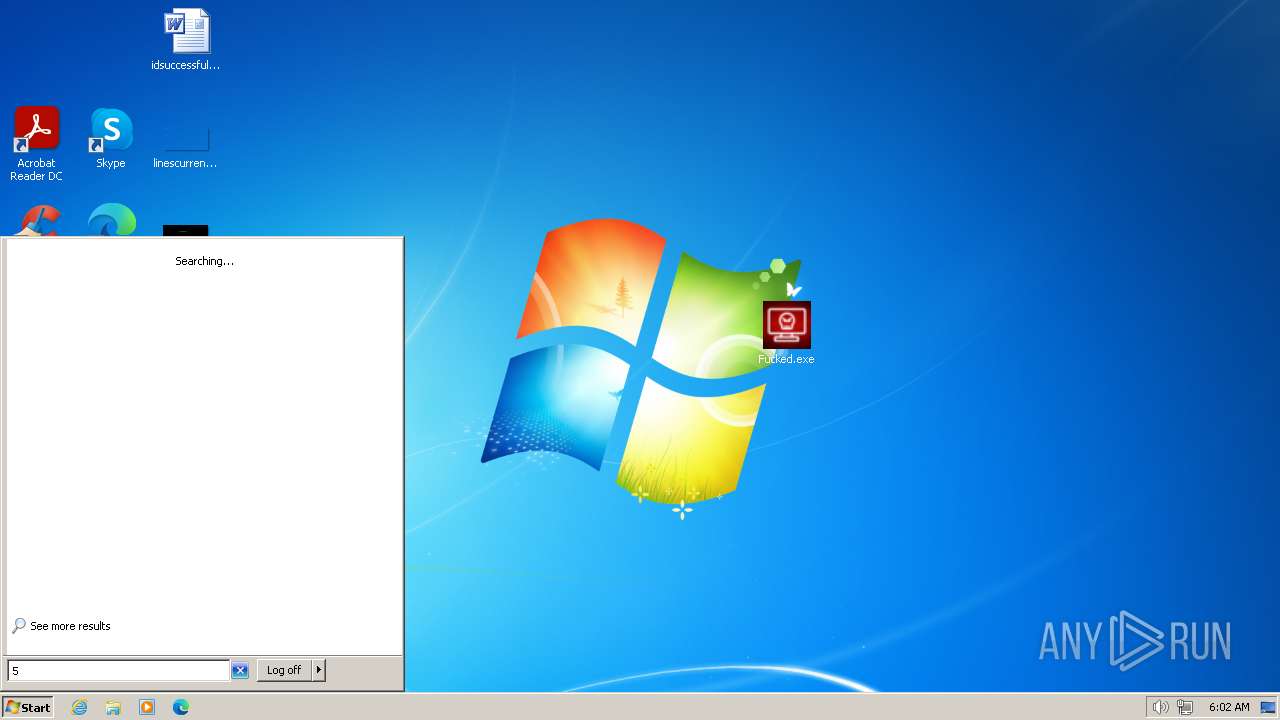
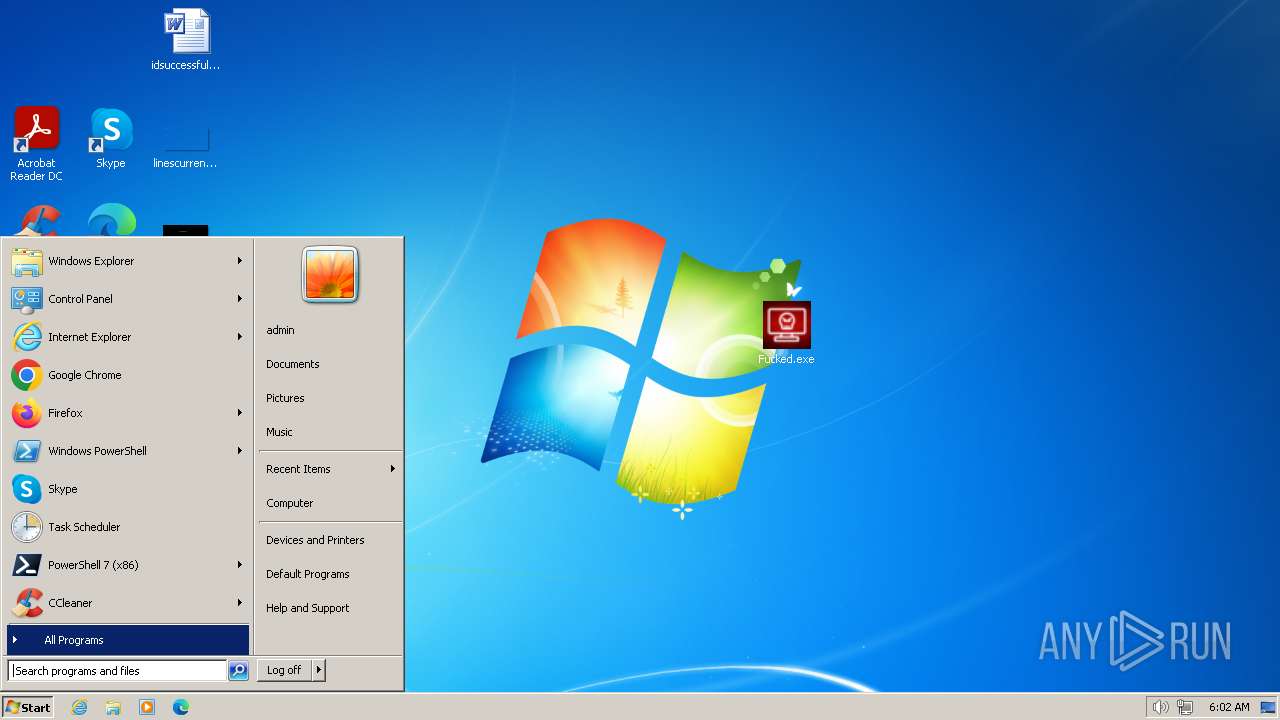
Disables the Run the Start menu
- reg.exe (PID: 1196)
Disables the LogOff the Start menu
- reg.exe (PID: 3480)
Disables the Shutdown in the Start menu
- reg.exe (PID: 2692)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 1172)
- net.exe (PID: 3936)
- net.exe (PID: 3992)
- net.exe (PID: 2616)
- cmd.exe (PID: 2844)
- net.exe (PID: 3964)
- net.exe (PID: 4036)
- net.exe (PID: 4072)
Starts NET.EXE to view/change users localgroup
- cmd.exe (PID: 1172)
- net.exe (PID: 1836)
- net.exe (PID: 4000)
- cmd.exe (PID: 2844)
SUSPICIOUS
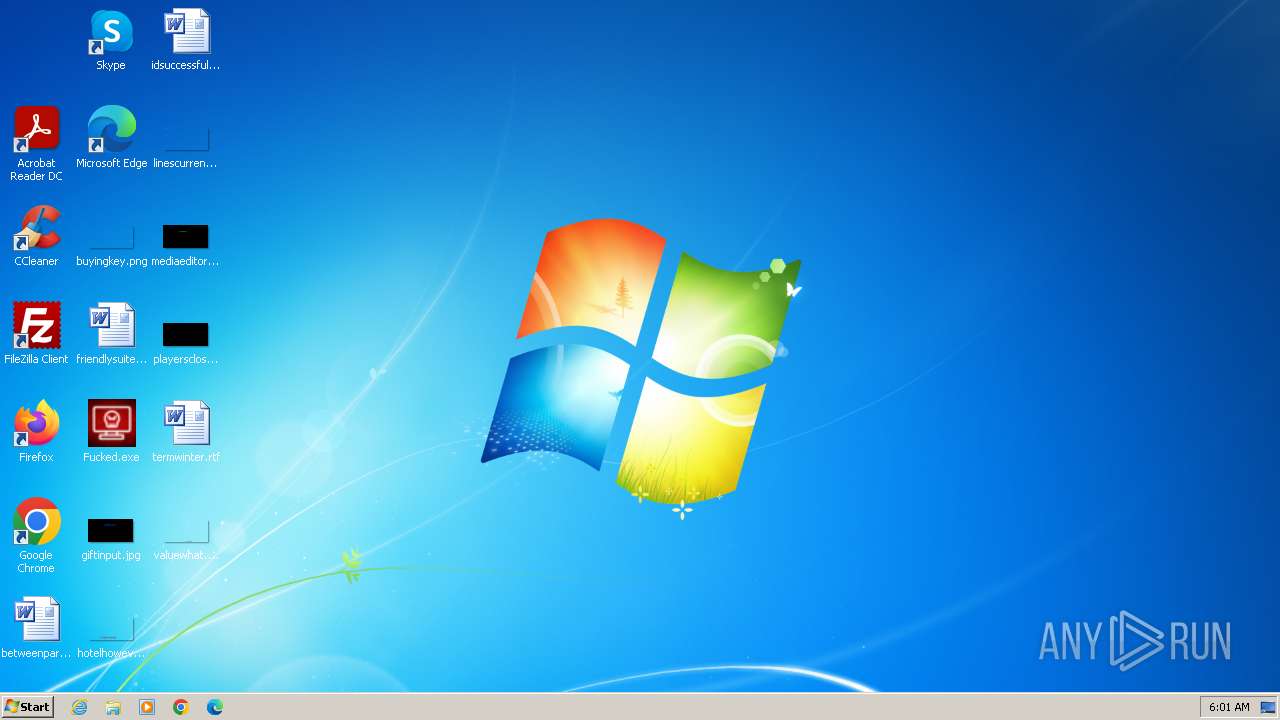
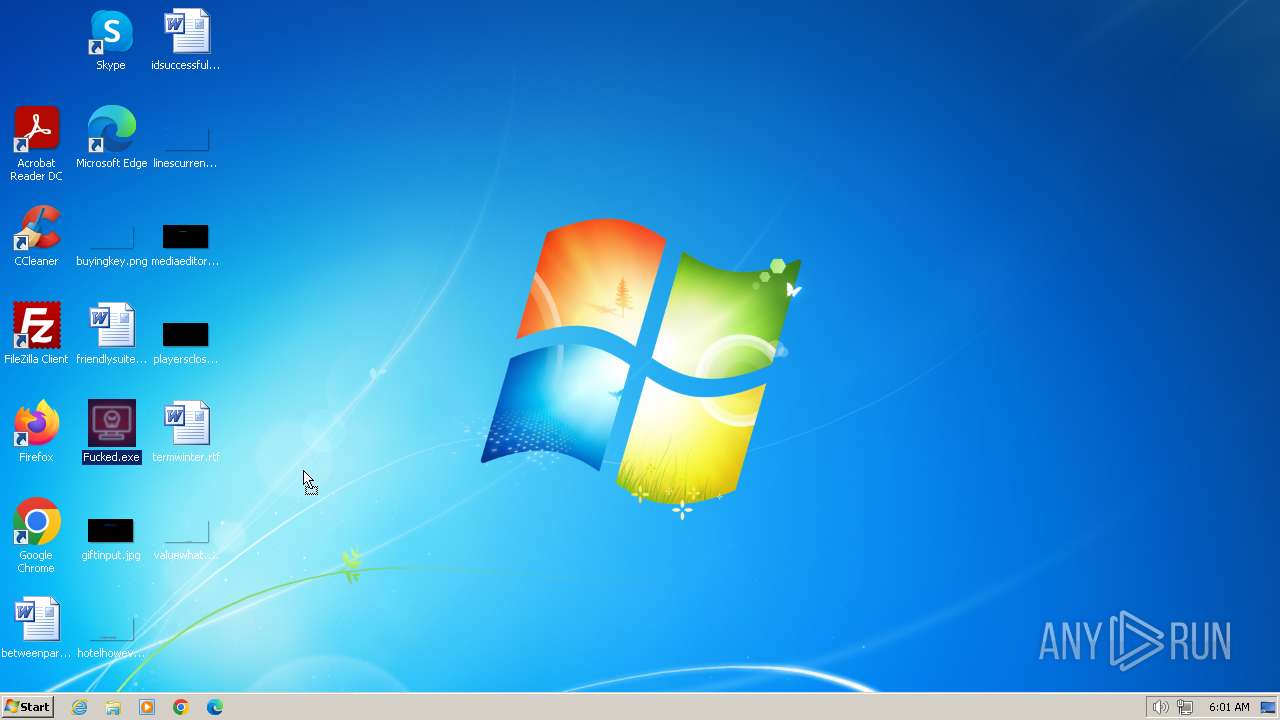
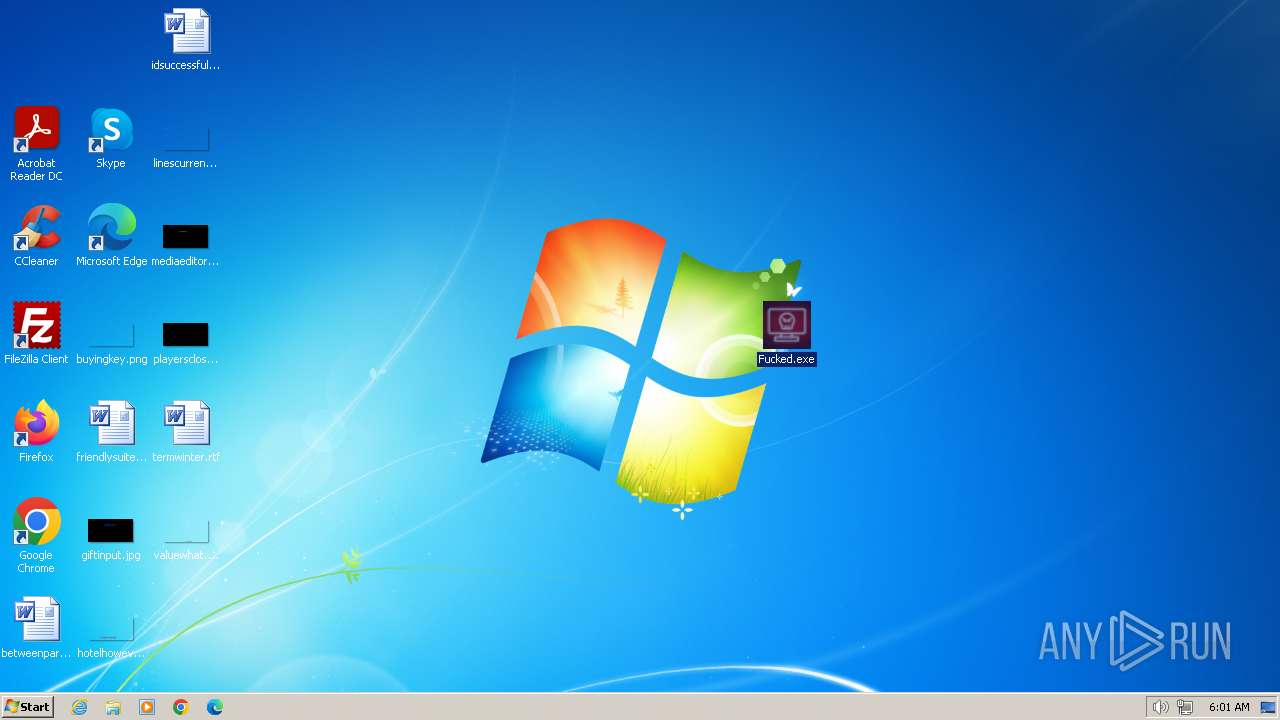
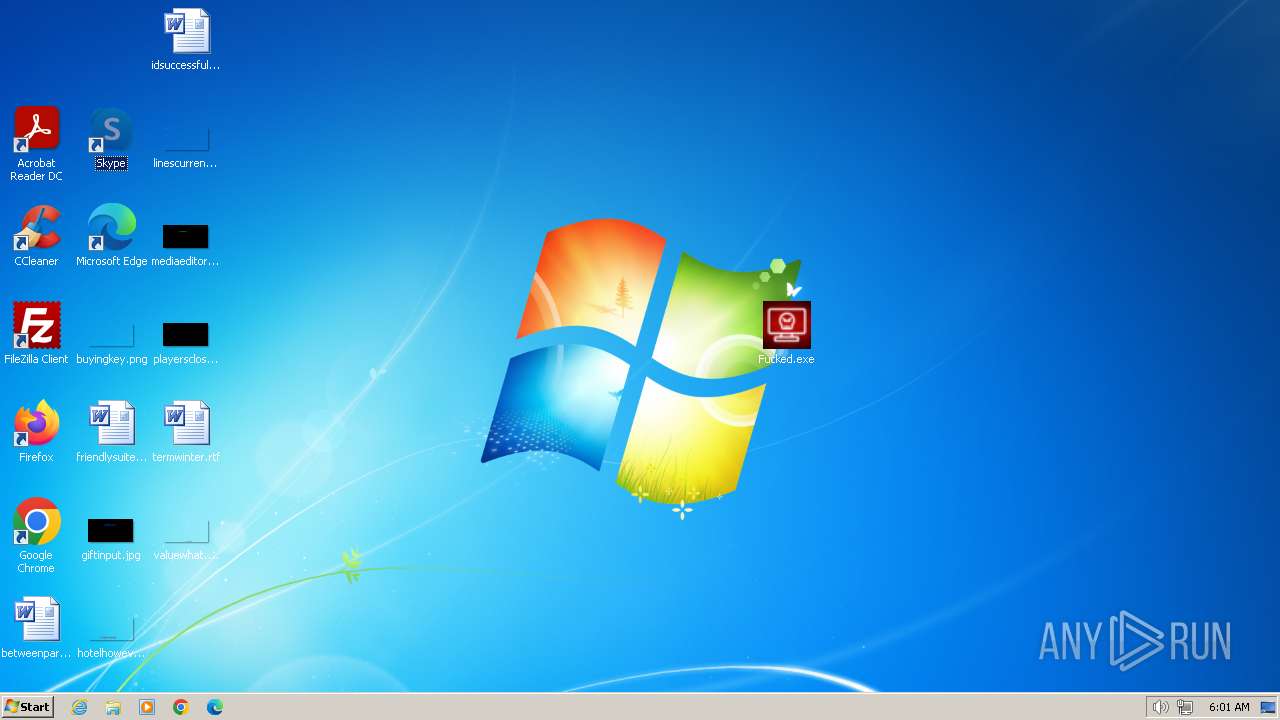
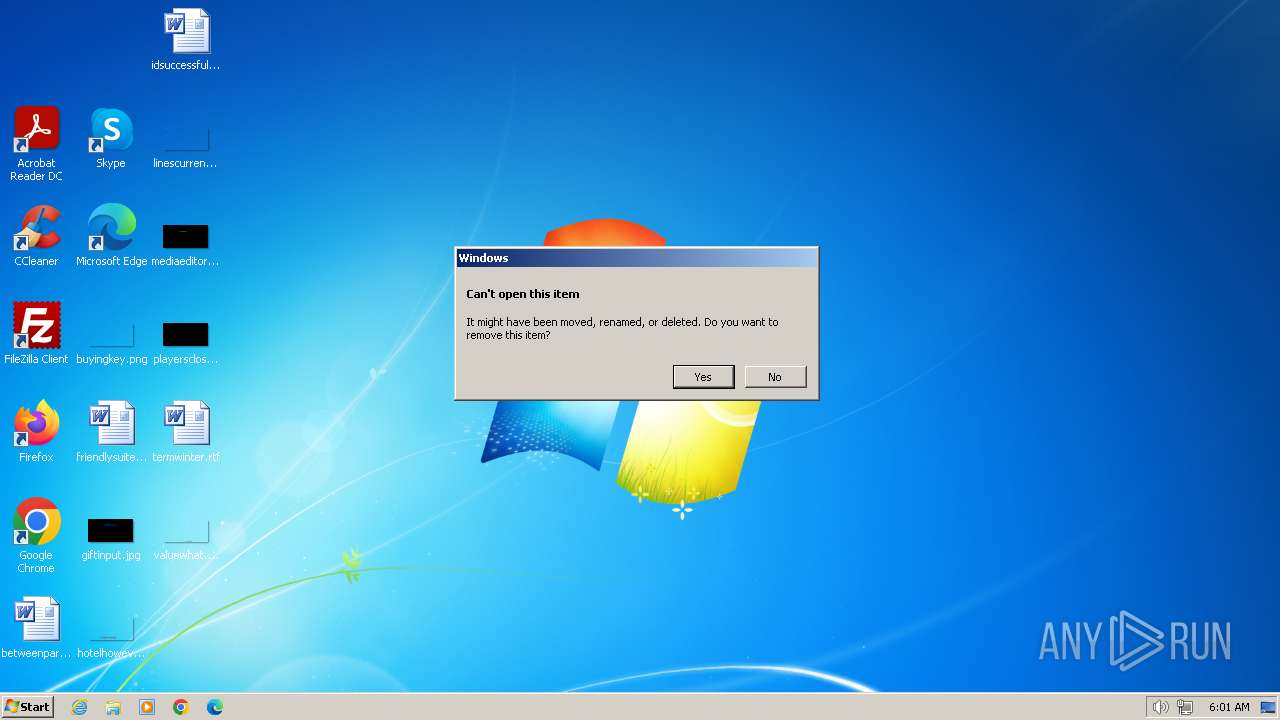
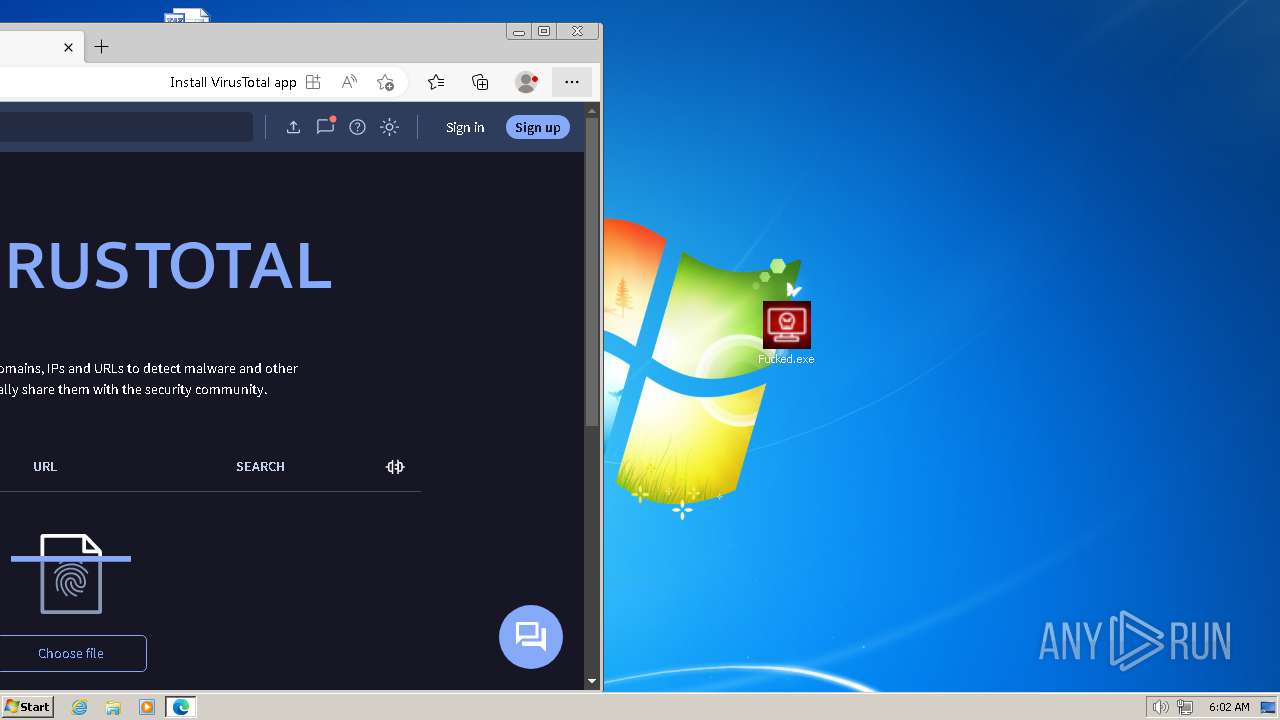
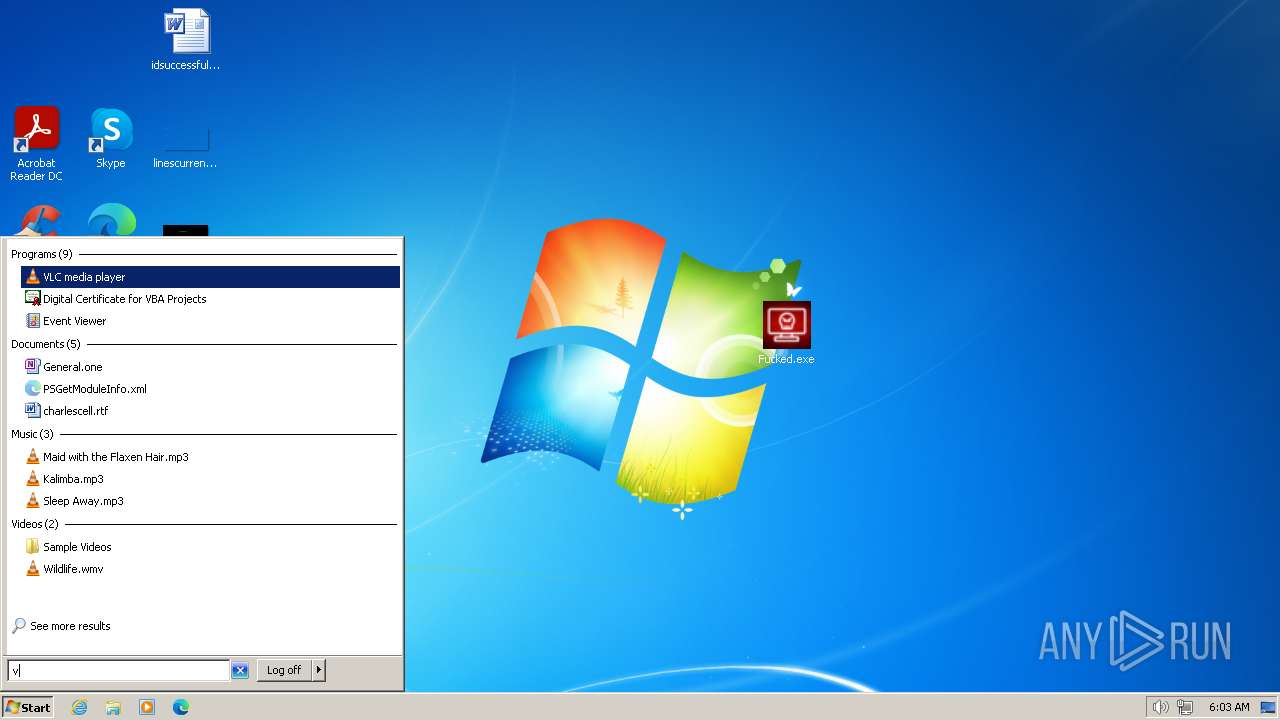
Application launched itself
- Fucked.exe (PID: 4064)
- Fucked.exe (PID: 2692)
Reads the Internet Settings
- Fucked.exe (PID: 4064)
- Fucked.exe (PID: 4092)
- sipnotify.exe (PID: 1204)
- Fucked.exe (PID: 2692)
- Fucked.exe (PID: 2820)
- sipnotify.exe (PID: 240)
Reads security settings of Internet Explorer
- Fucked.exe (PID: 4064)
- Fucked.exe (PID: 2692)
- Fucked.exe (PID: 2820)
- Fucked.exe (PID: 4092)
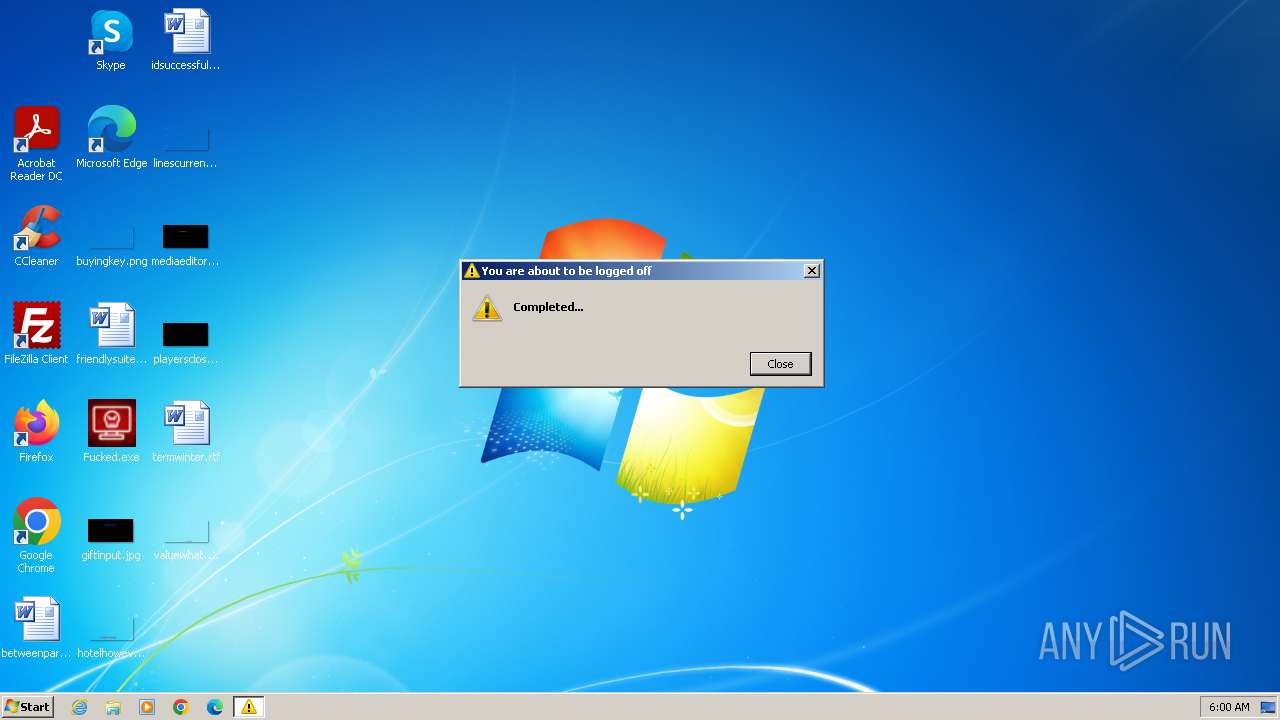
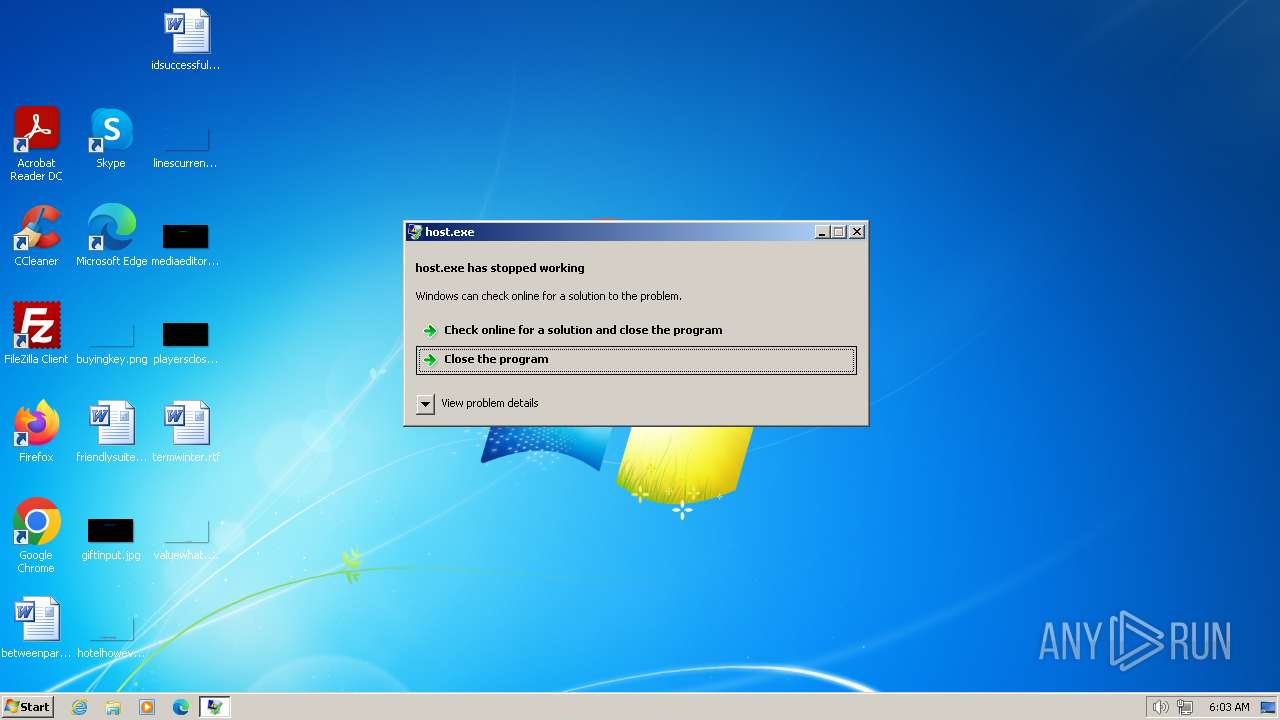
The system shut down or reboot
- cmd.exe (PID: 1172)
- cmd.exe (PID: 2844)
The process executes via Task Scheduler
- ctfmon.exe (PID: 348)
- sipnotify.exe (PID: 1204)
- sipnotify.exe (PID: 240)
- ctfmon.exe (PID: 2016)
Reads settings of System Certificates
- sipnotify.exe (PID: 1204)
- sipnotify.exe (PID: 240)
Starts CMD.EXE for commands execution
- Fucked.exe (PID: 2820)
- Fucked.exe (PID: 4092)
Executing commands from a ".bat" file
- Fucked.exe (PID: 2820)
- Fucked.exe (PID: 4092)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2844)
- cmd.exe (PID: 1172)
INFO
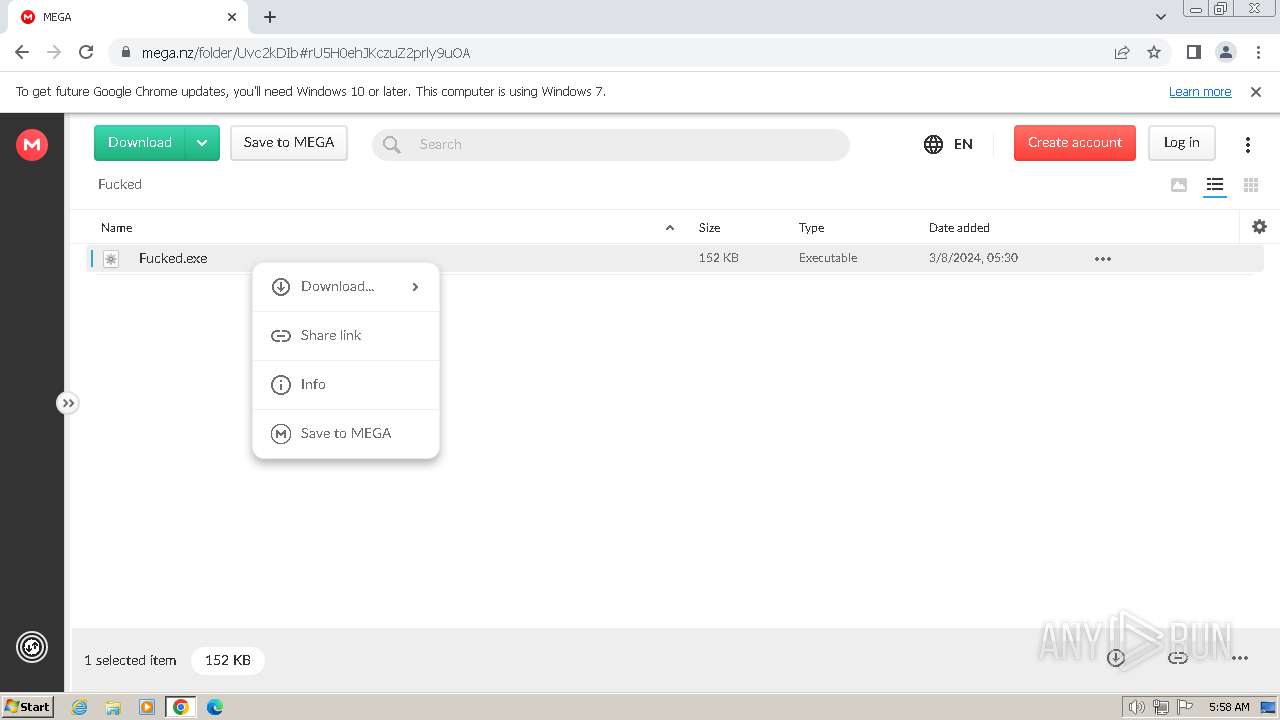
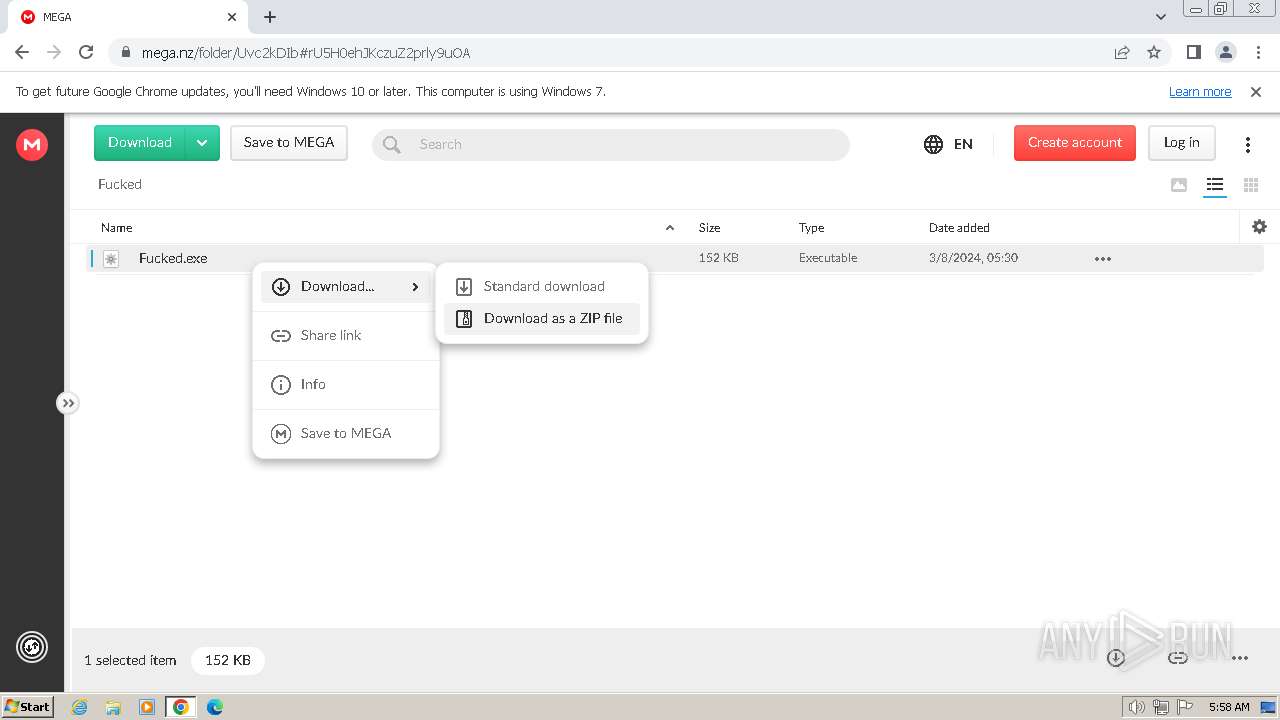
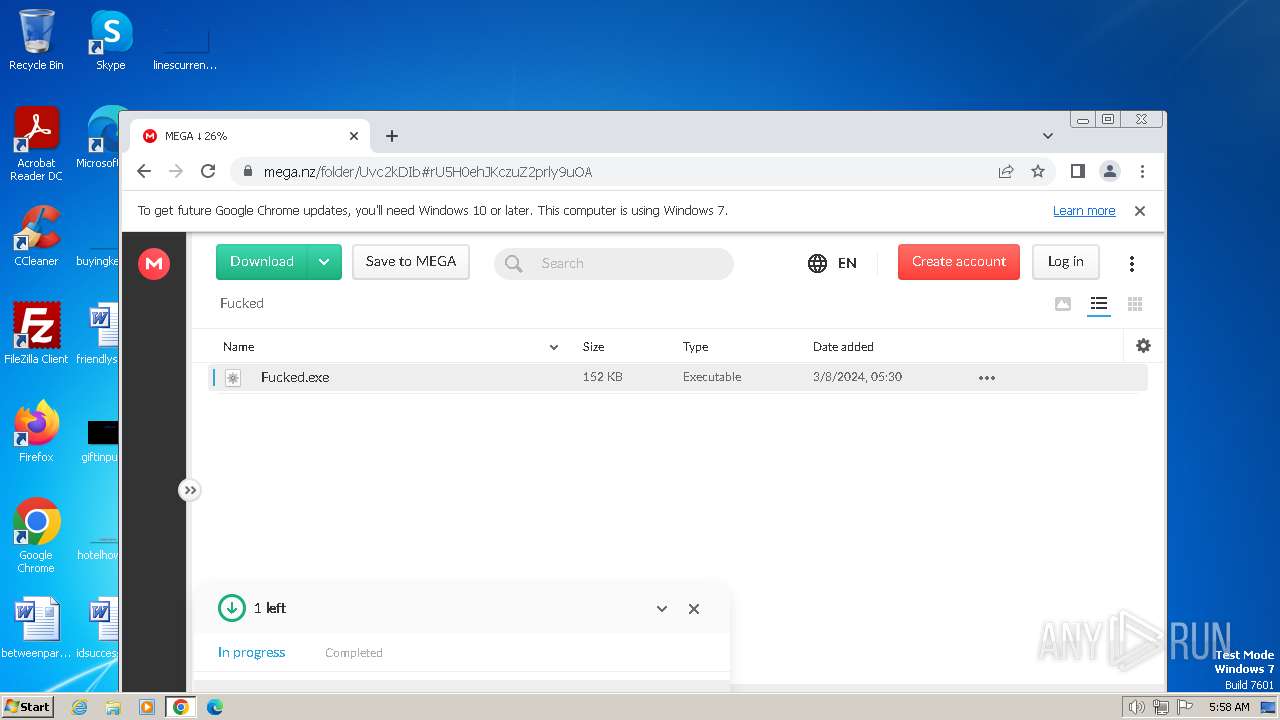
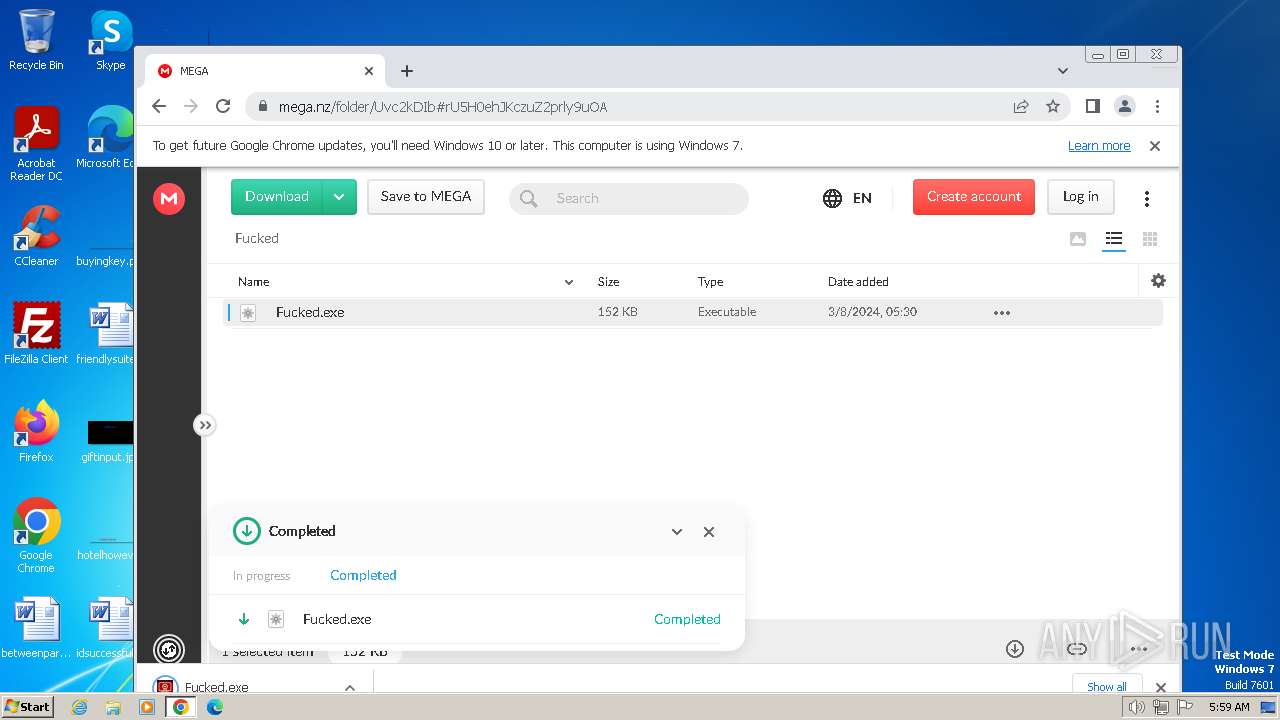
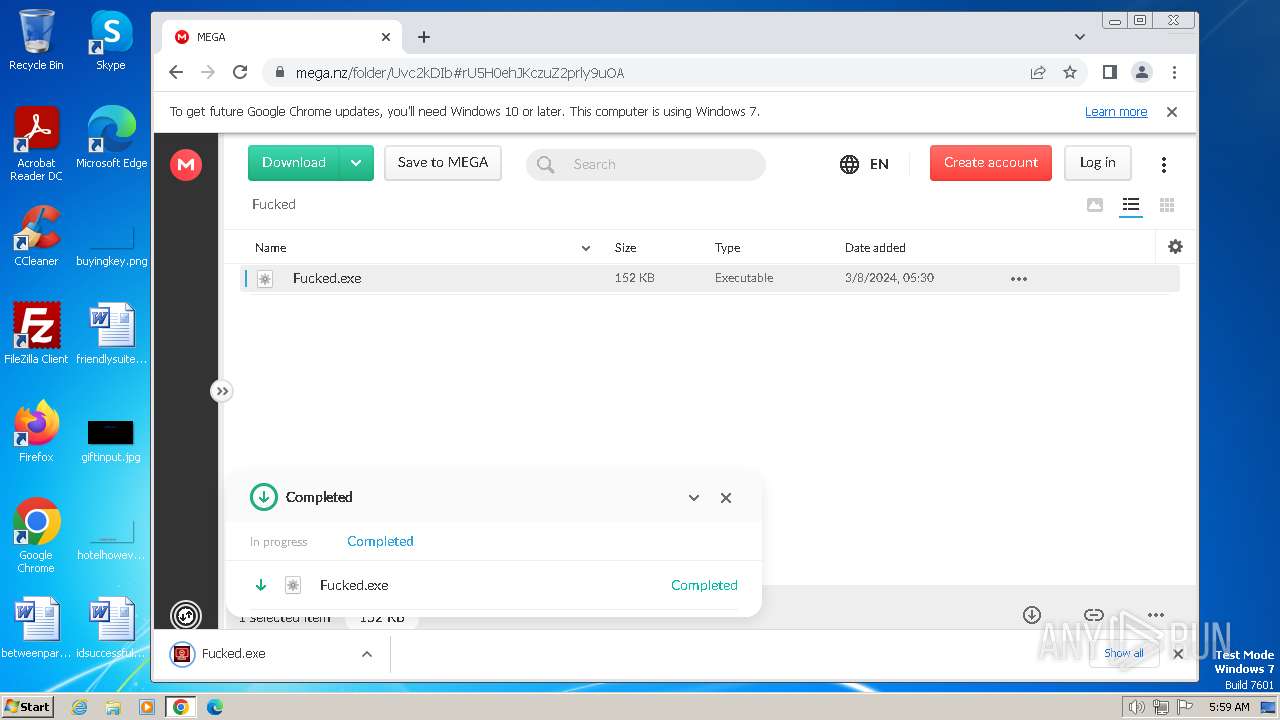
Executable content was dropped or overwritten
- chrome.exe (PID: 3864)
The process uses the downloaded file
- chrome.exe (PID: 3556)
- Fucked.exe (PID: 2692)
Checks supported languages
- Fucked.exe (PID: 4064)
- Fucked.exe (PID: 4092)
- wmpnscfg.exe (PID: 3100)
- wmpnscfg.exe (PID: 3700)
- IMEKLMG.EXE (PID: 2096)
- IMEKLMG.EXE (PID: 2104)
- wmpnscfg.exe (PID: 2356)
- wmpnscfg.exe (PID: 2396)
- Fucked.exe (PID: 2692)
- Fucked.exe (PID: 2820)
- wmpnscfg.exe (PID: 2608)
- wmpnscfg.exe (PID: 276)
- wmpnscfg.exe (PID: 2404)
- wmpnscfg.exe (PID: 2332)
- IMEKLMG.EXE (PID: 2072)
- IMEKLMG.EXE (PID: 2080)
Reads the computer name
- Fucked.exe (PID: 4064)
- wmpnscfg.exe (PID: 3700)
- wmpnscfg.exe (PID: 3100)
- IMEKLMG.EXE (PID: 2096)
- IMEKLMG.EXE (PID: 2104)
- wmpnscfg.exe (PID: 2356)
- wmpnscfg.exe (PID: 2396)
- Fucked.exe (PID: 2692)
- wmpnscfg.exe (PID: 2608)
- wmpnscfg.exe (PID: 276)
- Fucked.exe (PID: 4092)
- IMEKLMG.EXE (PID: 2080)
- IMEKLMG.EXE (PID: 2072)
- wmpnscfg.exe (PID: 2404)
- wmpnscfg.exe (PID: 2332)
- Fucked.exe (PID: 2820)
Drops the executable file immediately after the start
- chrome.exe (PID: 3864)
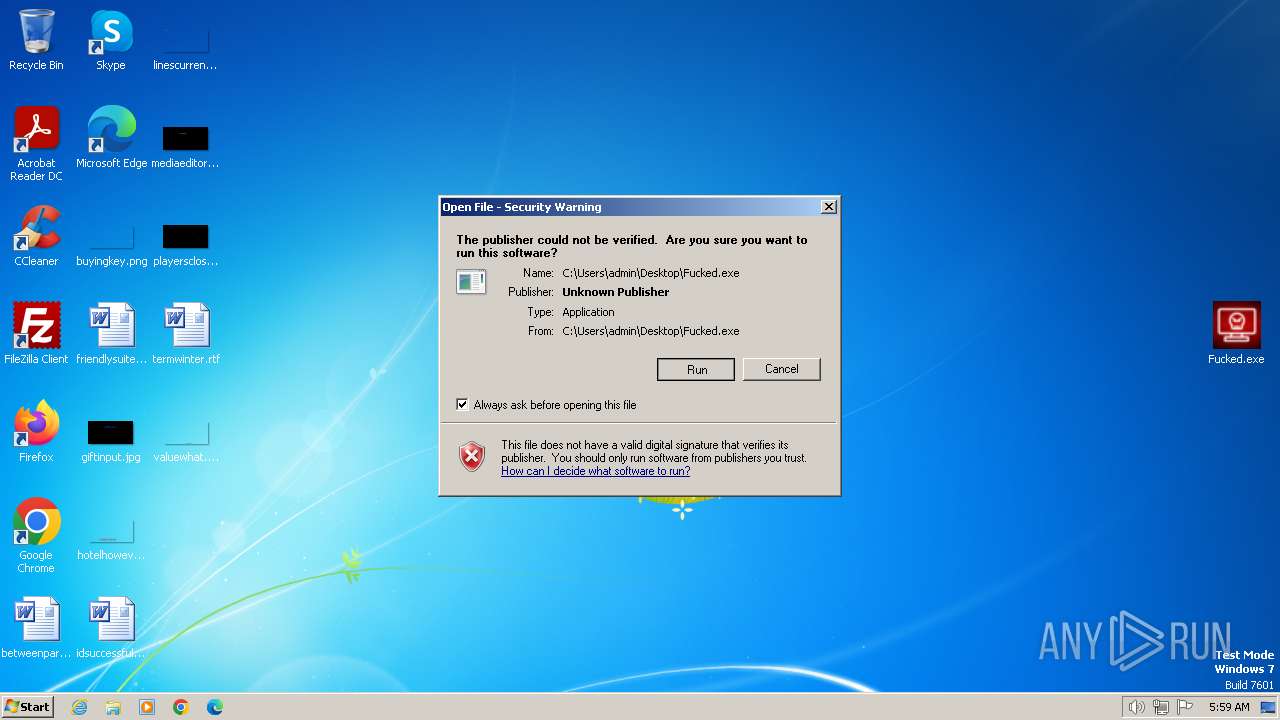
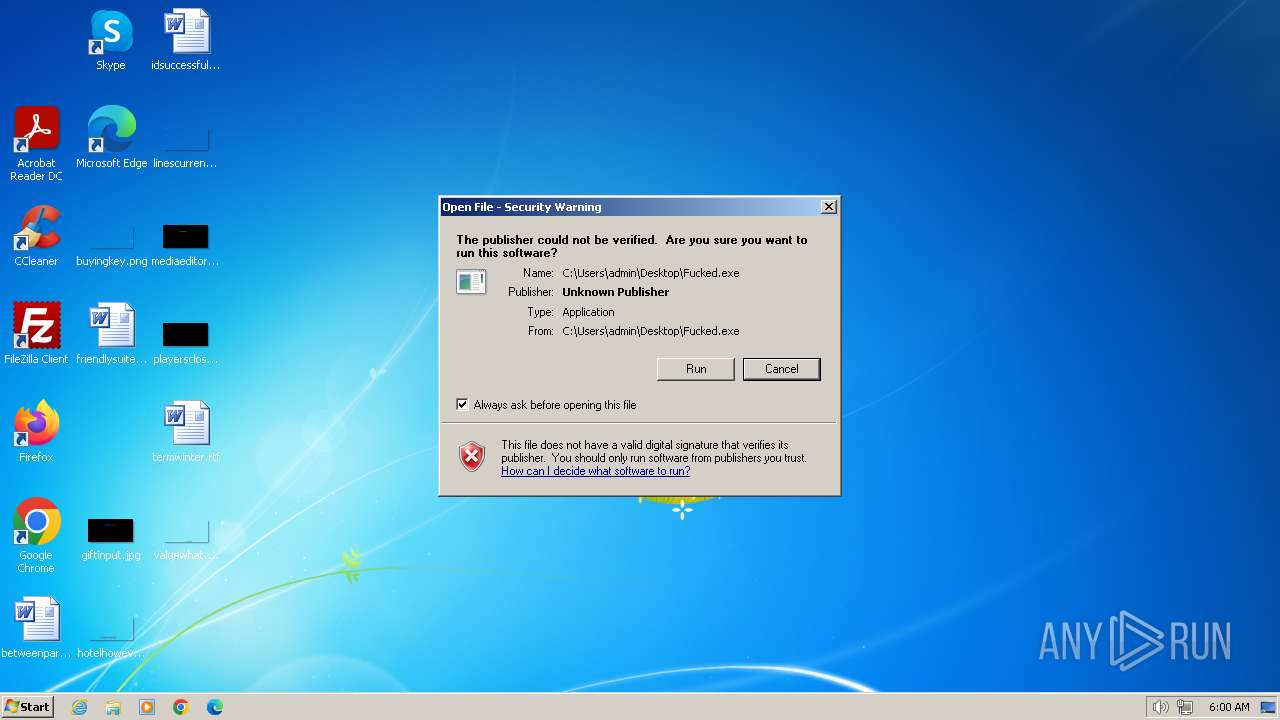
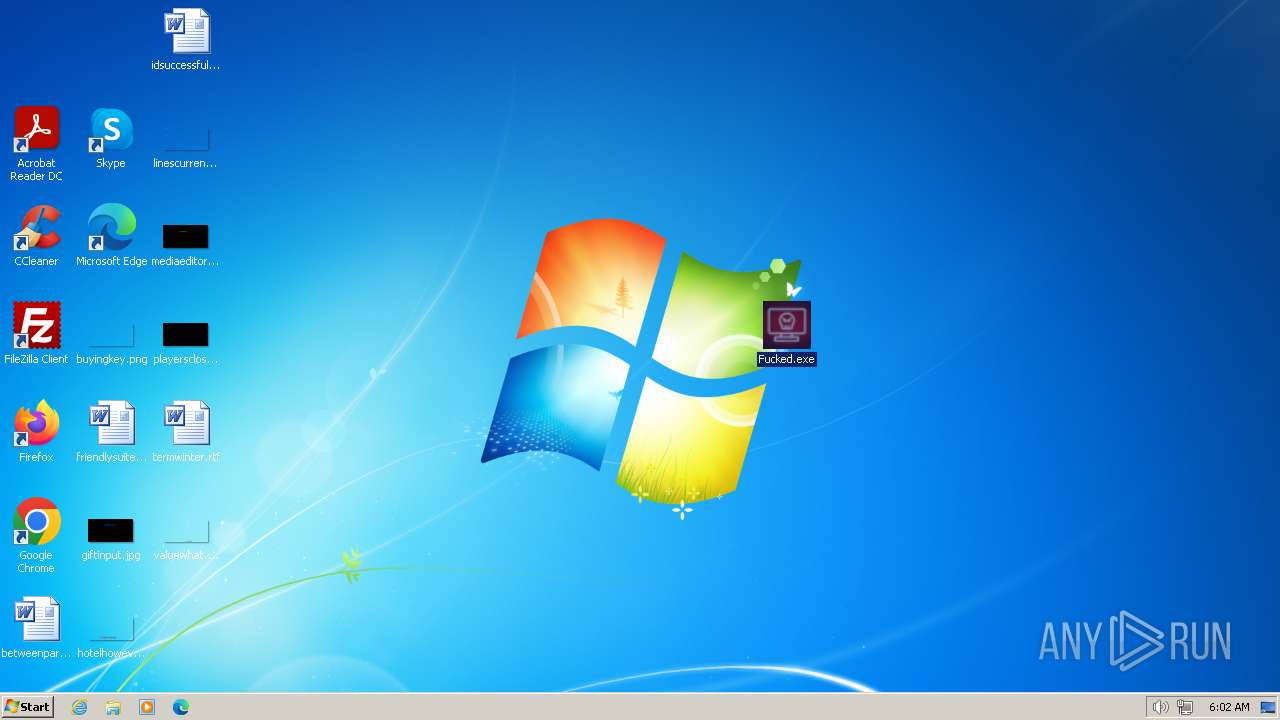
Manual execution by a user
- Fucked.exe (PID: 4064)
- wmpnscfg.exe (PID: 3700)
- wmpnscfg.exe (PID: 3100)
- IMEKLMG.EXE (PID: 2096)
- IMEKLMG.EXE (PID: 2104)
- wmpnscfg.exe (PID: 2356)
- wmpnscfg.exe (PID: 2396)
- Fucked.exe (PID: 2692)
- wmpnscfg.exe (PID: 2608)
- wmpnscfg.exe (PID: 276)
- IMEKLMG.EXE (PID: 2080)
- wmpnscfg.exe (PID: 2332)
- msedge.exe (PID: 2672)
- iexplore.exe (PID: 2516)
- wmpnscfg.exe (PID: 2404)
- IMEKLMG.EXE (PID: 2072)
Application launched itself
- chrome.exe (PID: 3864)
- iexplore.exe (PID: 2516)
- msedge.exe (PID: 2672)
Reads the time zone
- net1.exe (PID: 2120)
- net1.exe (PID: 3460)
- net1.exe (PID: 4044)
- net1.exe (PID: 4080)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 1204)
- sipnotify.exe (PID: 240)
Reads the software policy settings
- sipnotify.exe (PID: 1204)
- sipnotify.exe (PID: 240)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 2096)
- IMEKLMG.EXE (PID: 2104)
- IMEKLMG.EXE (PID: 2080)
- IMEKLMG.EXE (PID: 2072)
Create files in a temporary directory
- Fucked.exe (PID: 2820)
- Fucked.exe (PID: 4092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
409
Monitored processes
265
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 276 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | REG ADD HKEY_CURRENT_USER\Control Panel\Colors /v ButtonText /t REG_SZ /d 109 10 191 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | REG ADD HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows /v Personalization /t KEY /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 348 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | tskill /A Office* | C:\Windows\System32\tskill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Remote Desktop Services End Process Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | REG ADD HKEY_CURRENT_USER\Control Panel\Colors /v Background /t REG_SZ /d 109 10 191 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --mojo-platform-channel-handle=3620 --field-trial-handle=1132,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3456 --field-trial-handle=1288,i,11676830225024257549,9433083746014218597,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 696 | REG ADD HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer\DisallowRun /v 11 /t REG_SZ /d streaming_client.exe /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
35 314
Read events
34 983
Write events
279
Delete events
52
Modification events
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
21
Suspicious files
336
Text files
174
Unknown types
290
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f453.TMP | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF17f5d9.TMP | text | |
MD5:B36B68CE4A71A5BFAF89A4D1CC07893F | SHA256:6422CC04455EF100D67FD9F299AACFEF3BA4F77D0FA1D2440D89E7D1CF65EBBC | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17facb.TMP | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF17f55c.TMP | text | |
MD5:C383FD120B14BB0E98E99C1BCC9B43F6 | SHA256:56A3A5EACBD28BEE1CF8C1D0052321A5C27EE858BEF7B2FA1DE20806A0823CC1 | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF1806d1.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
98
DNS requests
114
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1204 | sipnotify.exe | HEAD | 200 | 23.197.138.118:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133544375749210000 | unknown | — | — | unknown |
1204 | sipnotify.exe | HEAD | 200 | 23.197.138.118:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133544376671400000 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3948 | chrome.exe | 23.21.157.88:443 | lckdwns.com | AMAZON-AES | US | unknown |
3864 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3948 | chrome.exe | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3948 | chrome.exe | 142.250.185.74:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3948 | chrome.exe | 172.217.23.99:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
3864 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3948 | chrome.exe | 31.216.145.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
lckdwns.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
mega.nz |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
gfs302n125.userstorage.mega.co.nz |
| unknown |
sb-ssl.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
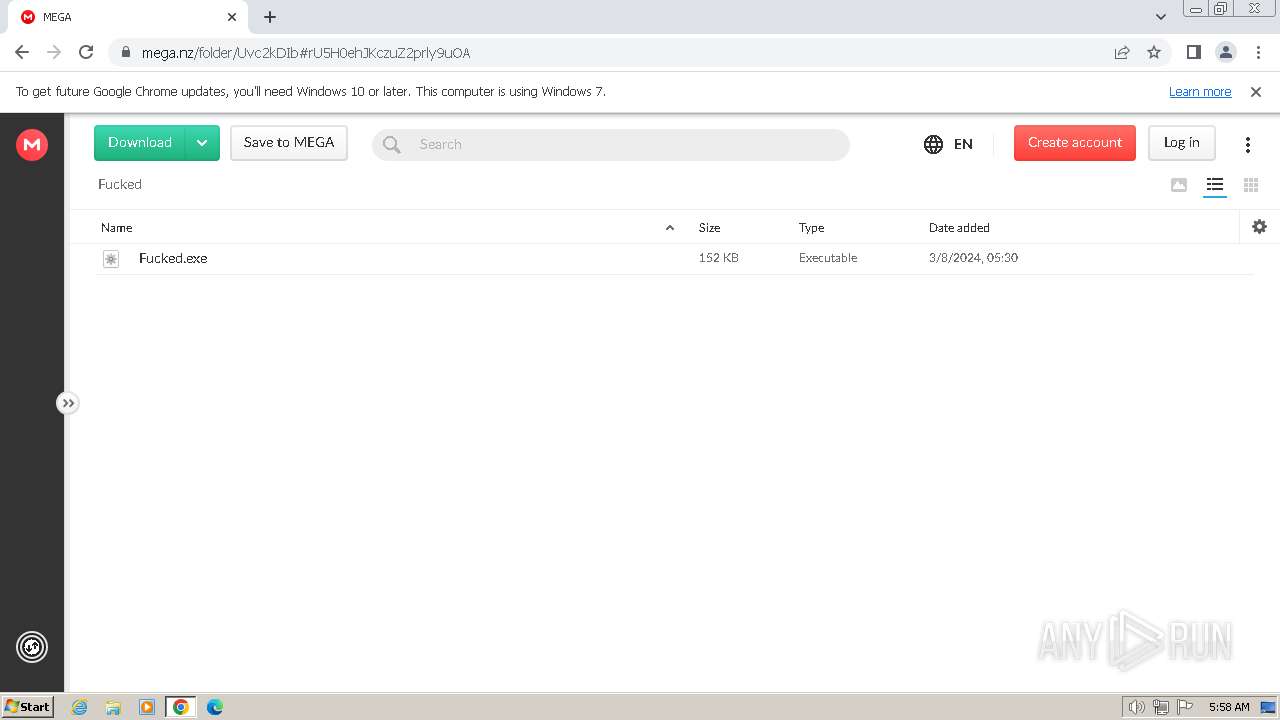
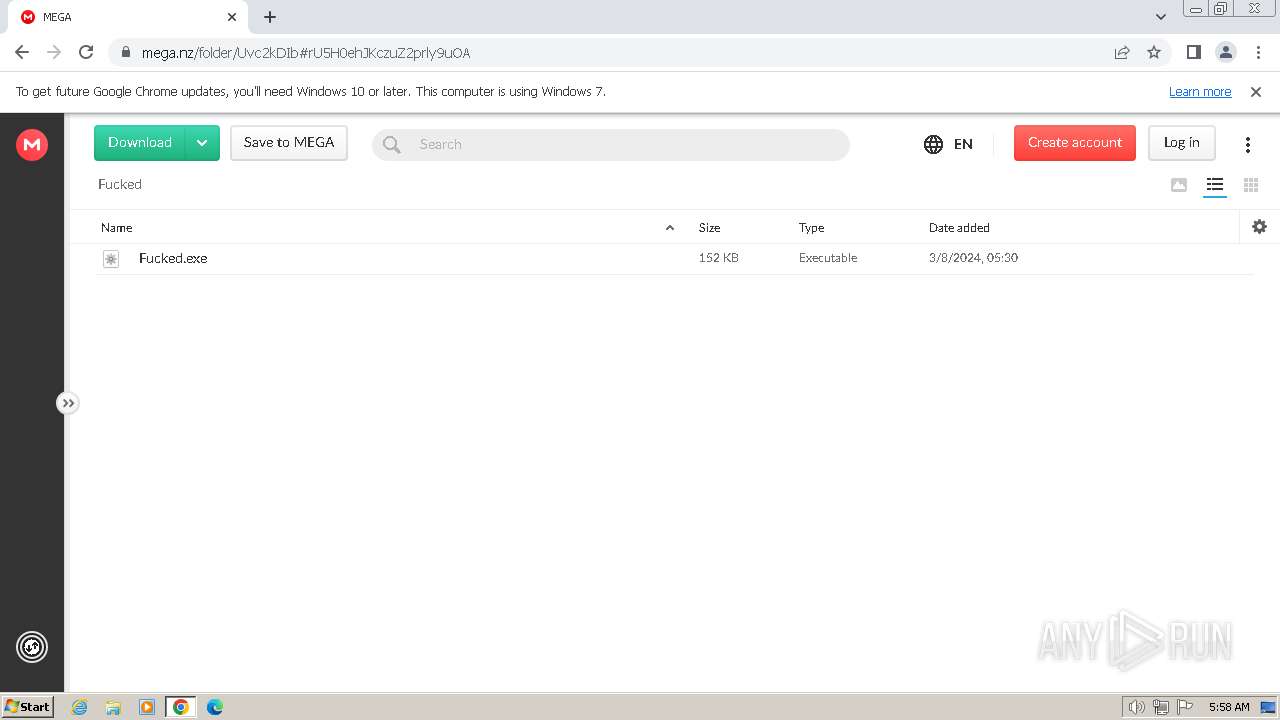
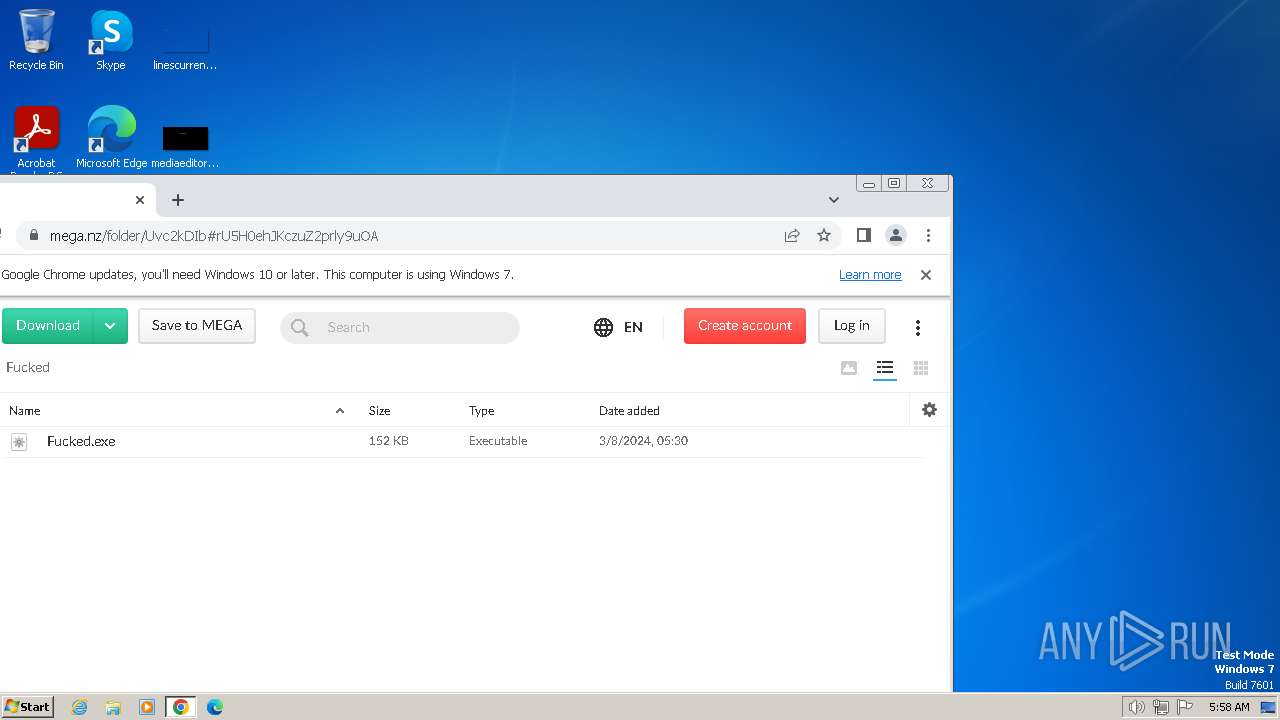
3948 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
3948 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
3948 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
3948 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
3948 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
3948 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
3948 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
3948 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
3948 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
3948 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |