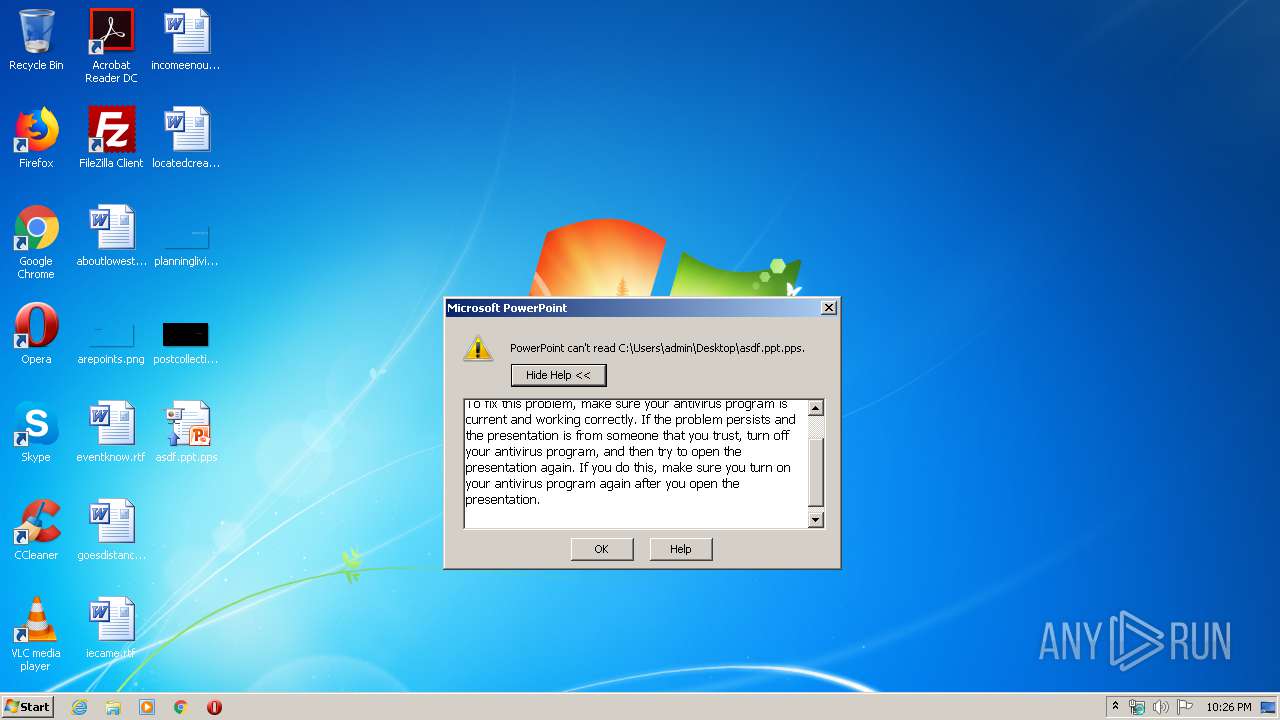
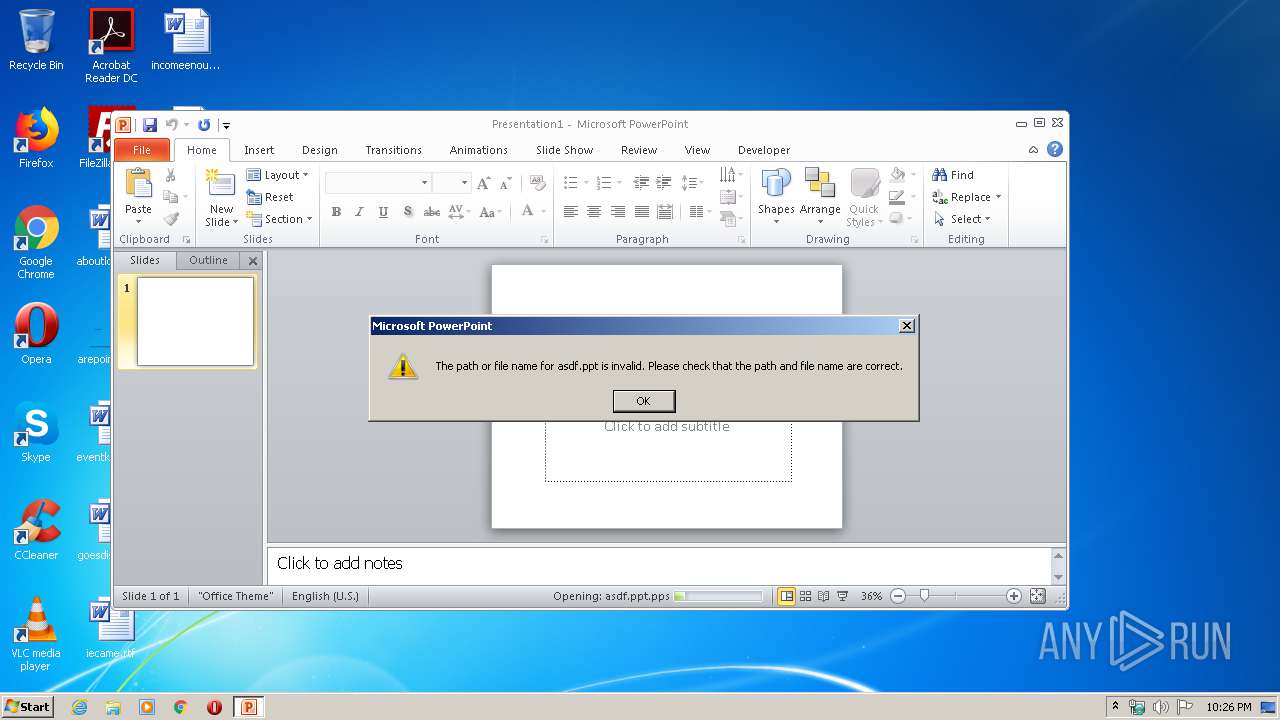
| File name: | asdf.ppt |
| Full analysis: | https://app.any.run/tasks/e6ed7271-8017-4ef3-94d3-95f7c1737981 |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2020, 21:26:00 |
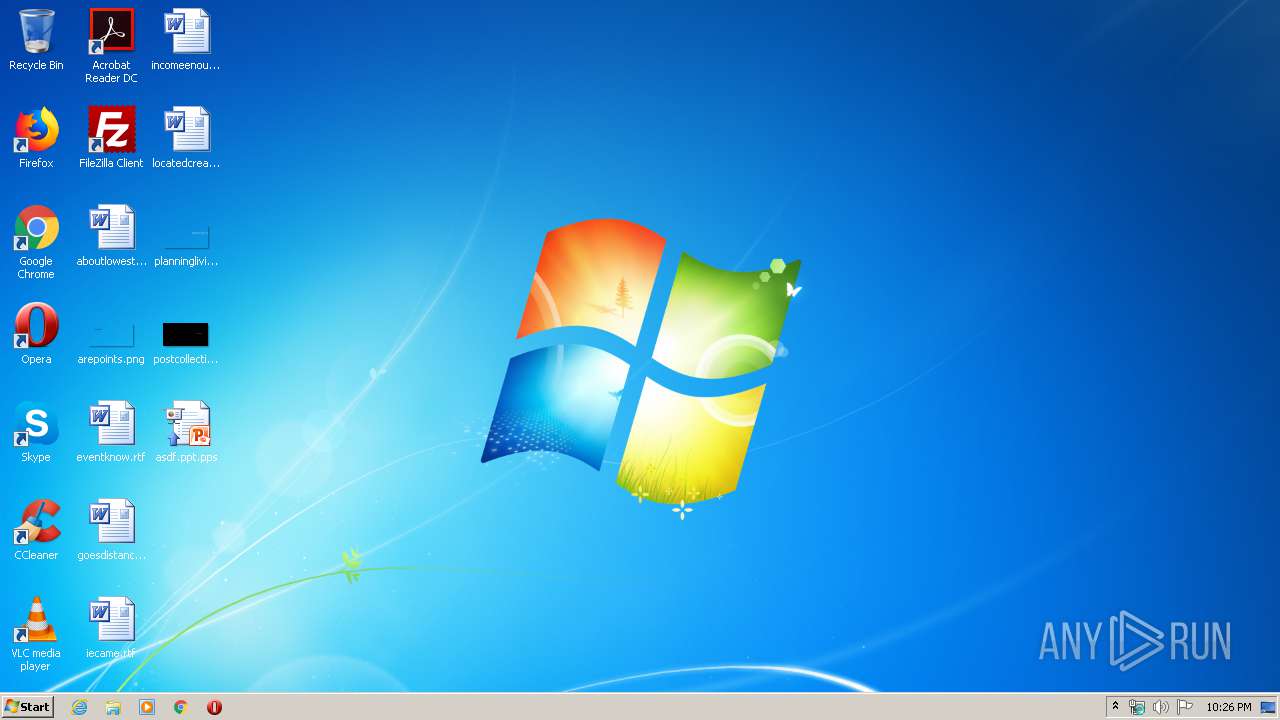
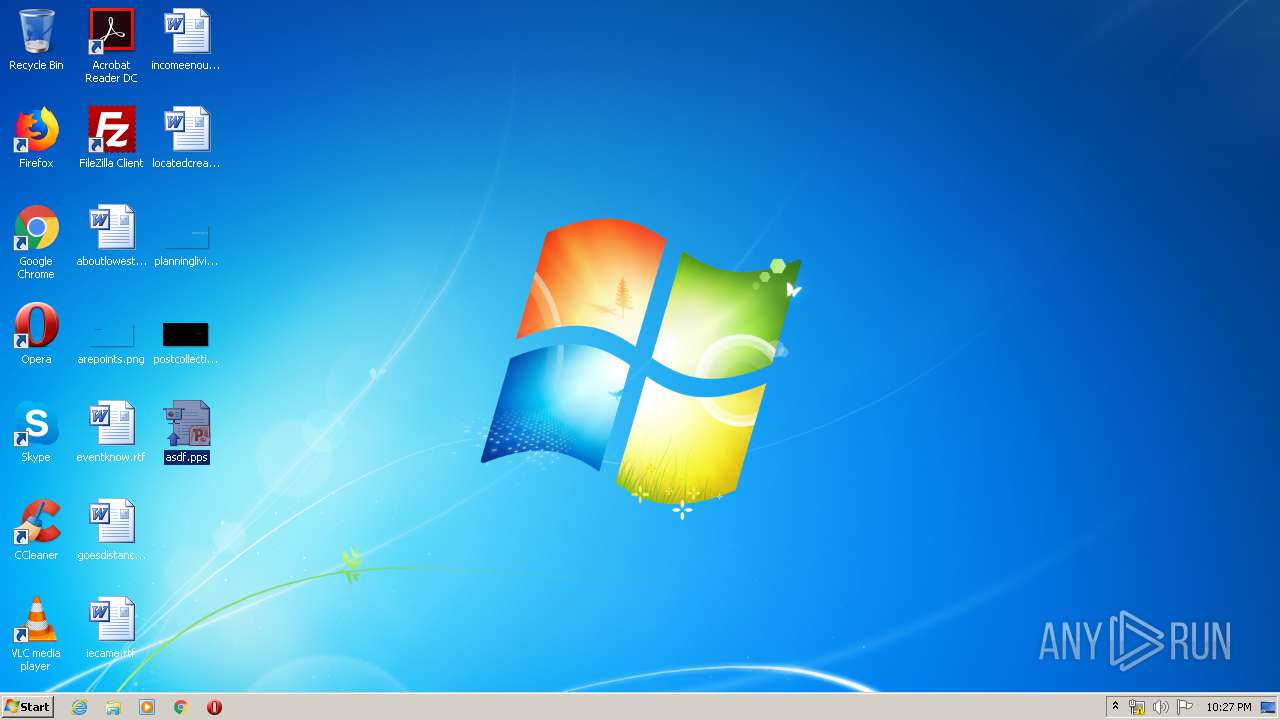
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-powerpoint |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Title: asasa, Subject: asa, Author: asdasdsadasdsa, Keywords: a;asss, Template: TM04033917[[fn=Berlin]], Last Saved By: Administrator, Revision Number: 1, Name of Creating Application: Microsoft Office PowerPoint, Total Editing Time: 06:07, Create Time/Date: Mon Apr 13 16:21:57 2020, Last Saved Time/Date: Mon Apr 13 16:28:05 2020, Number of Words: 0 |
| MD5: | BF79C28D86E3F5649C8653CA28E9B6AE |
| SHA1: | E733D7F041731155E82615C6AE690DC63B23F99C |
| SHA256: | 9457395ABEB8B919897CF36B4104A98A0BAB70E460FD0A309788CA2F5C06180C |
| SSDEEP: | 768:R/tqzyzsCzYpQ/0l3k1IYZ8IsUZgBTsY1mRwCSxybL1OTifzWJU:jqGwCzYpQ/0l3k1KNxAp |
MALICIOUS
Actions looks like stealing of personal data
- POWERPNT.EXE (PID: 2524)
SUSPICIOUS
Checks supported languages
- POWERPNT.EXE (PID: 3052)
- POWERPNT.EXE (PID: 2524)
- POWERPNT.EXE (PID: 3320)
INFO
Reads Microsoft Office registry keys
- POWERPNT.EXE (PID: 3320)
- POWERPNT.EXE (PID: 3052)
- POWERPNT.EXE (PID: 2524)
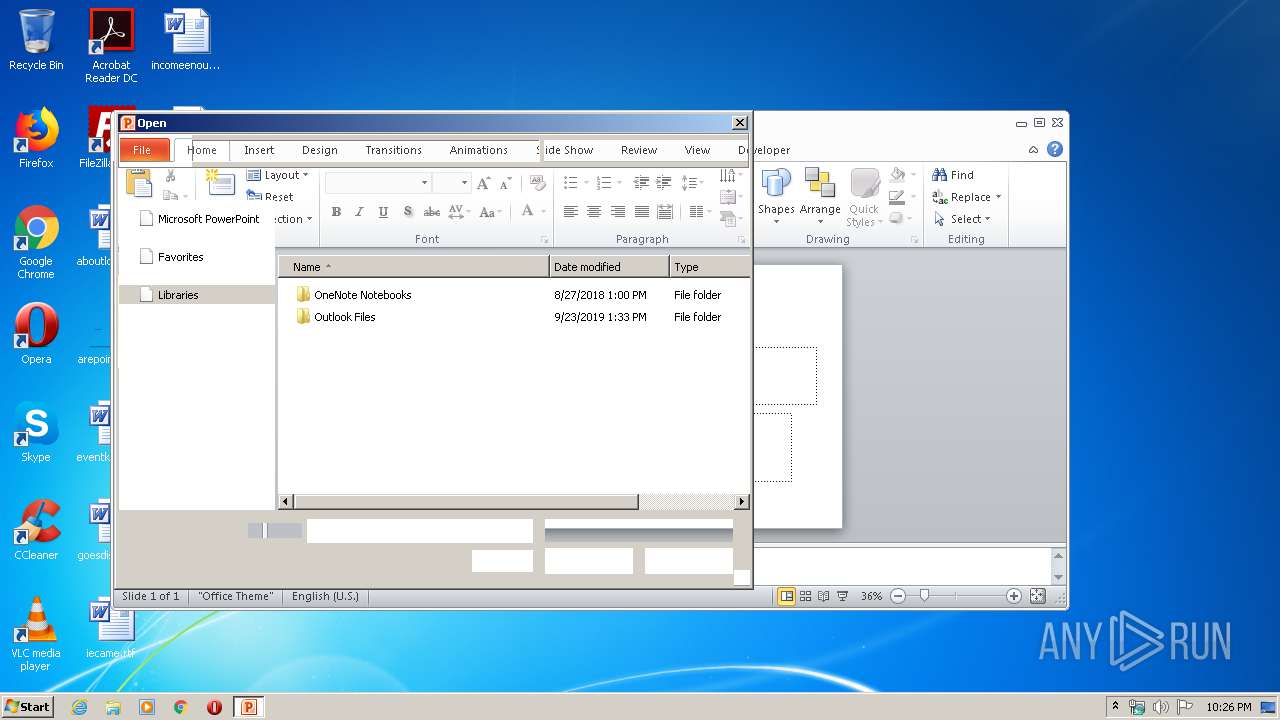
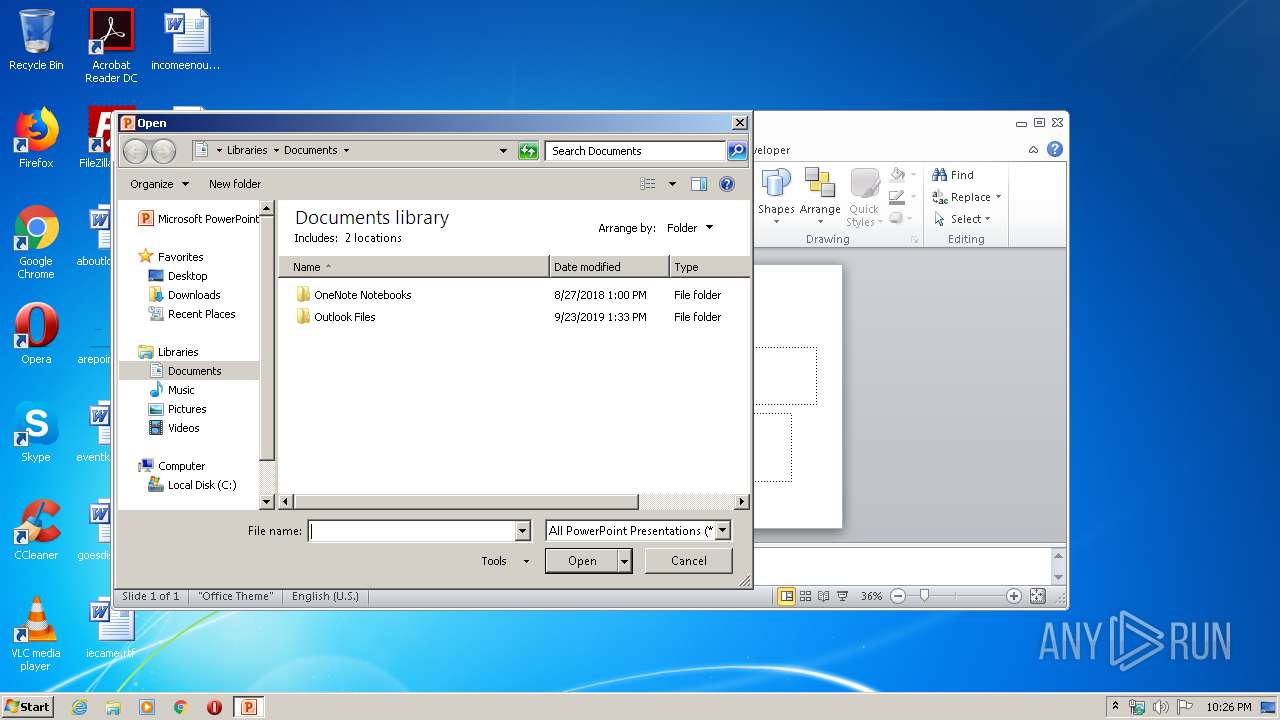
Manual execution by user
- POWERPNT.EXE (PID: 3052)
- POWERPNT.EXE (PID: 2524)
Creates files in the user directory
- POWERPNT.EXE (PID: 3052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .pps/ppt | | | Microsoft PowerPoint document (79.7) |
|---|
EXIF
FlashPix
| Title: | asasa |
|---|---|
| Subject: | asa |
| Author: | asdasdsadasdsa |
| Keywords: | a;asss |
| Template: | TM04033917[[fn=Berlin]] |
| LastModifiedBy: | Administrator |
| RevisionNumber: | 1 |
| Software: | Microsoft Office PowerPoint |
| TotalEditTime: | 6.1 minutes |
| CreateDate: | 2020:04:13 15:21:57 |
| ModifyDate: | 2020:04:13 15:28:05 |
| Words: | - |
| ThumbnailClip: | (Binary data 43336 bytes, use -b option to extract) |
| CodePage: | Windows Latin 1 (Western European) |
| PresentationTarget: | Widescreen |
| Bytes: | - |
| Paragraphs: | - |
| Slides: | 6 |
| Notes: | - |
| HiddenSlides: | - |
| MMClips: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
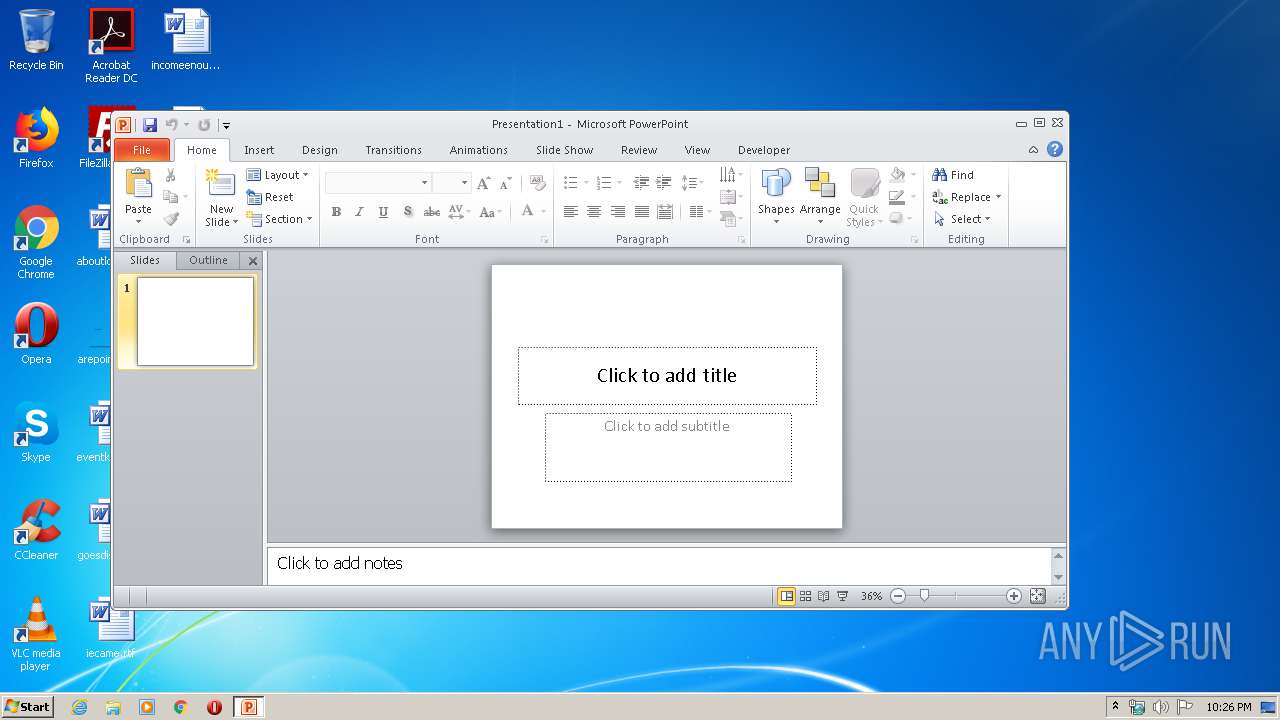
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
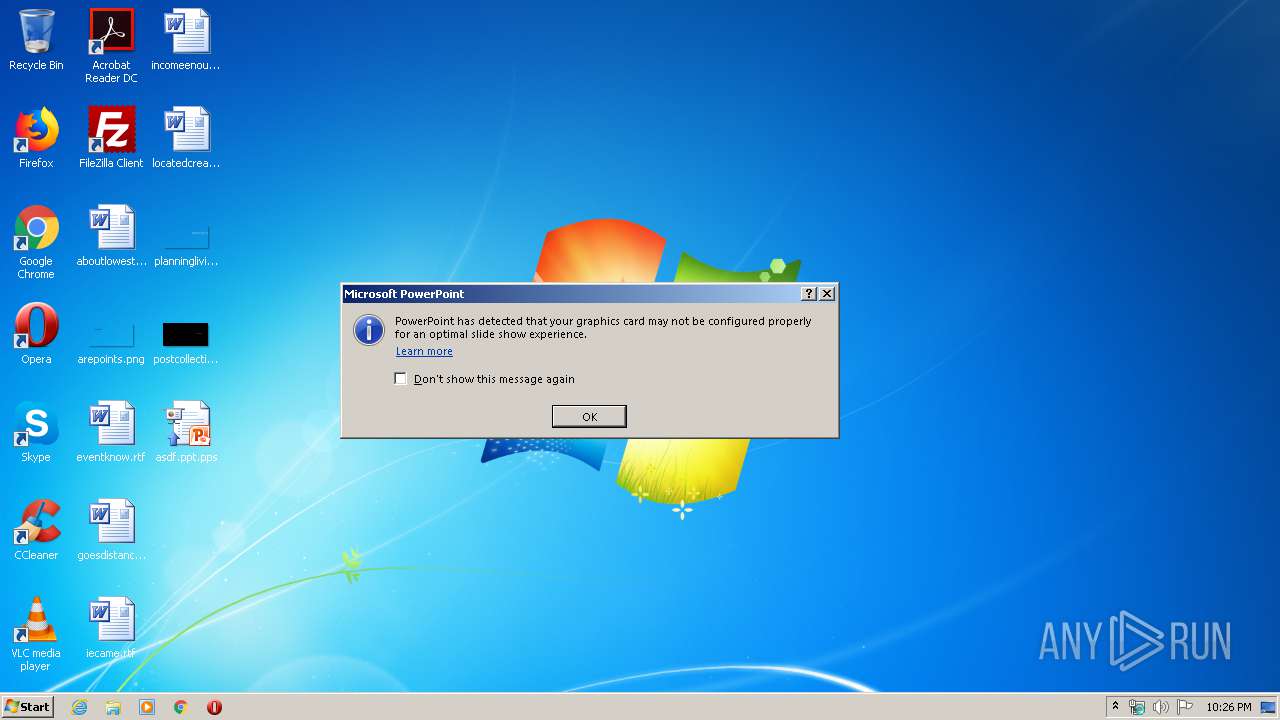
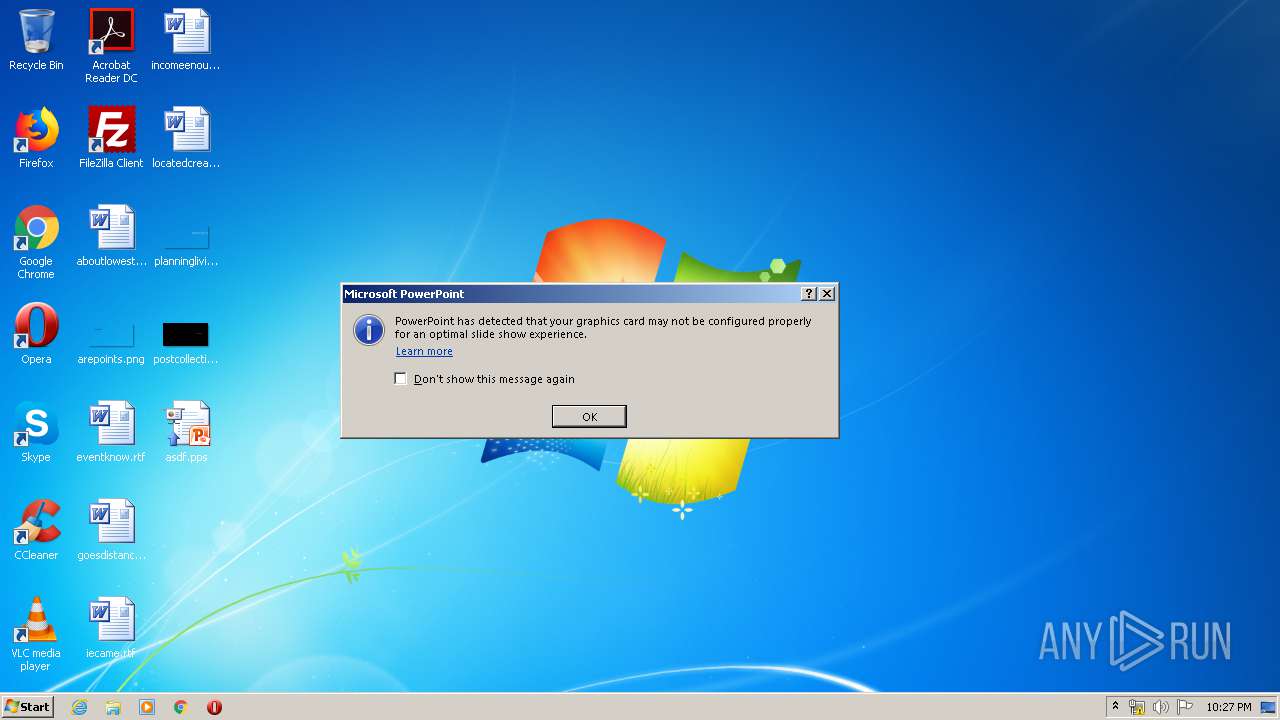
| 2524 | "C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE" | C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Exit code: 0 Version: 14.0.6009.1000 Modules
| |||||||||||||||
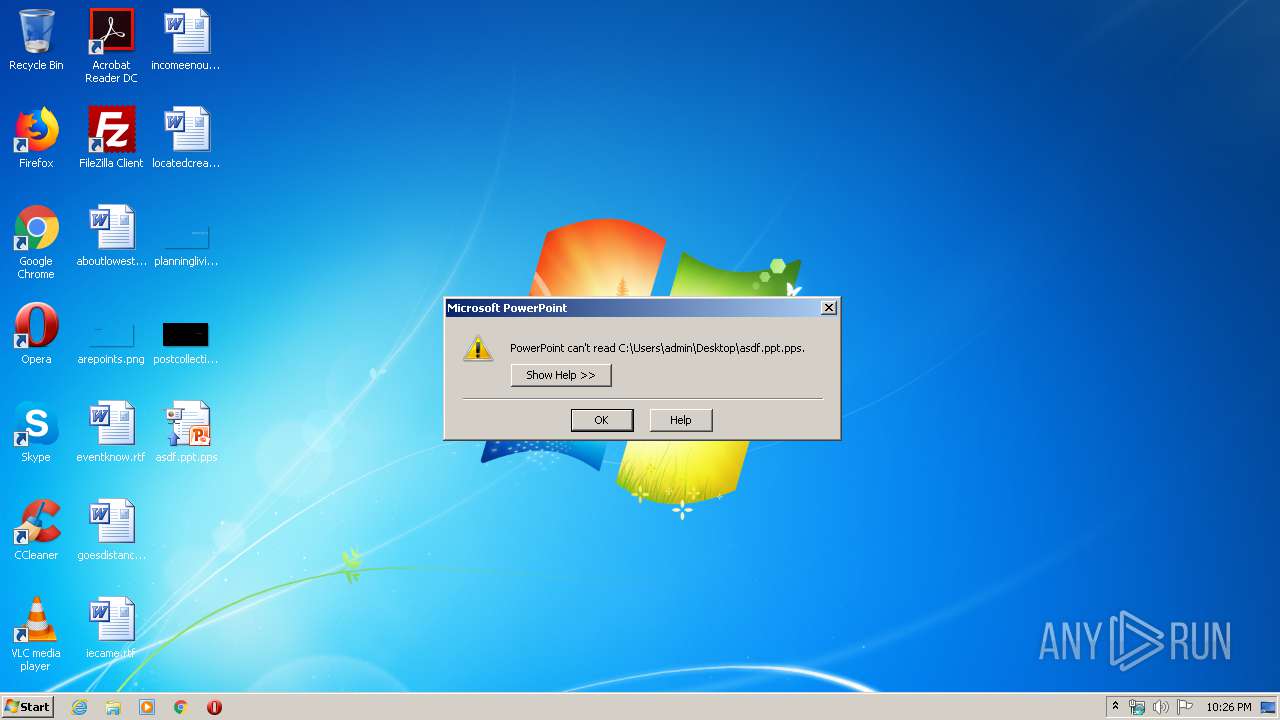
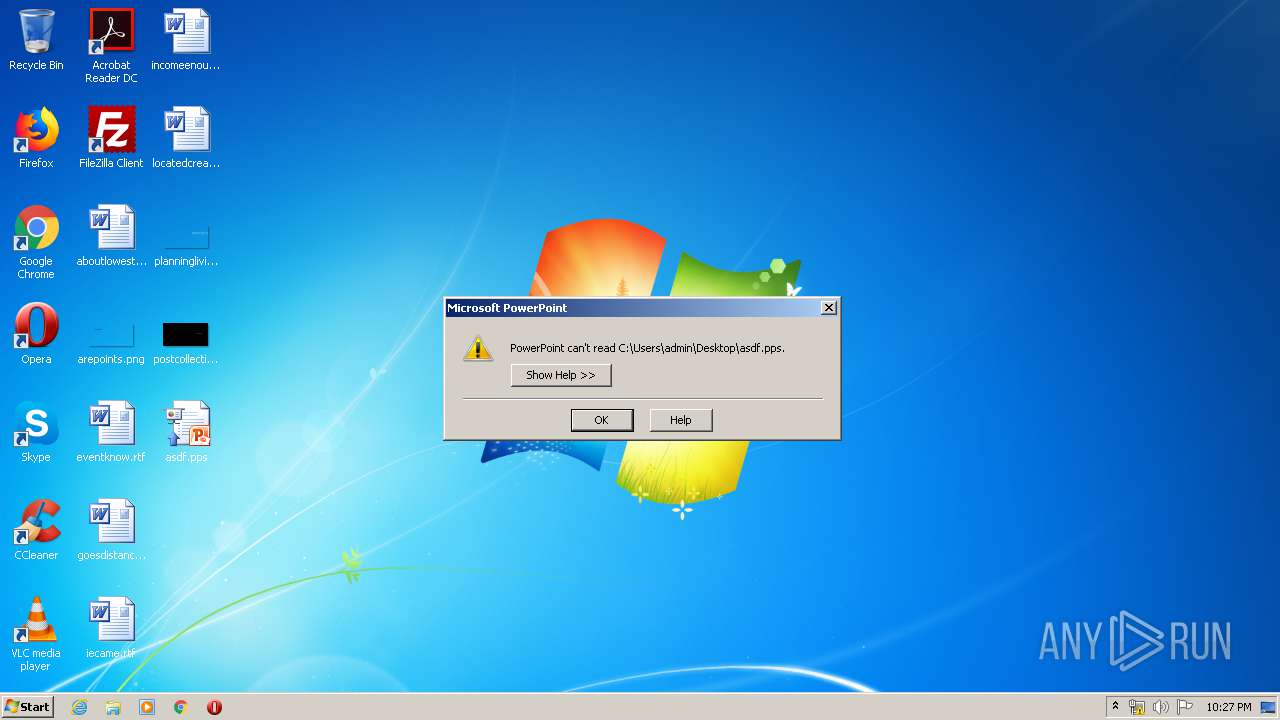
| 3052 | "C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE" /s "C:\Users\admin\Desktop\asdf.pps" | C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Exit code: 0 Version: 14.0.6009.1000 Modules
| |||||||||||||||
| 3320 | "C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE" /s "C:\Users\admin\Desktop\asdf.ppt.pps" | C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Exit code: 0 Version: 14.0.6009.1000 Modules
| |||||||||||||||
Total events
2 143
Read events
1 928
Write events
189
Delete events
26
Modification events
| (PID) Process: | (3320) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\StartupItems |
| Operation: | write | Name: | %l3 |
Value: 256C3300F80C0000010000000000000000000000 | |||
| (PID) Process: | (3320) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3320) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3320) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3320) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3320) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3320) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3320) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3320) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3320) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
2
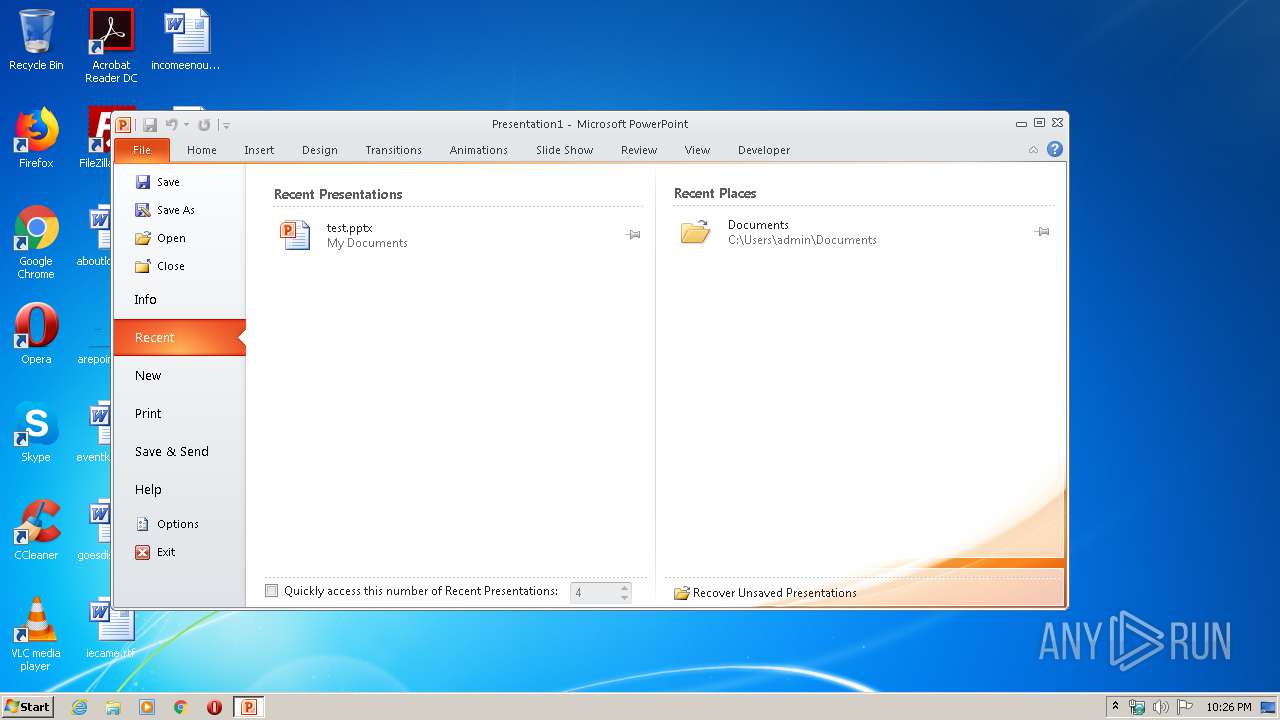
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3320 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\CVRE0B4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2524 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\CVR3859.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3052 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\CVRB440.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3052 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\~DF13E22E45D44641A5.TMP | — | |
MD5:— | SHA256:— | |||
| 3052 | POWERPNT.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\asdf.pps.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3052 | POWERPNT.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report