| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/c37b2c04-3284-4666-b57e-e1e99d81c503 |
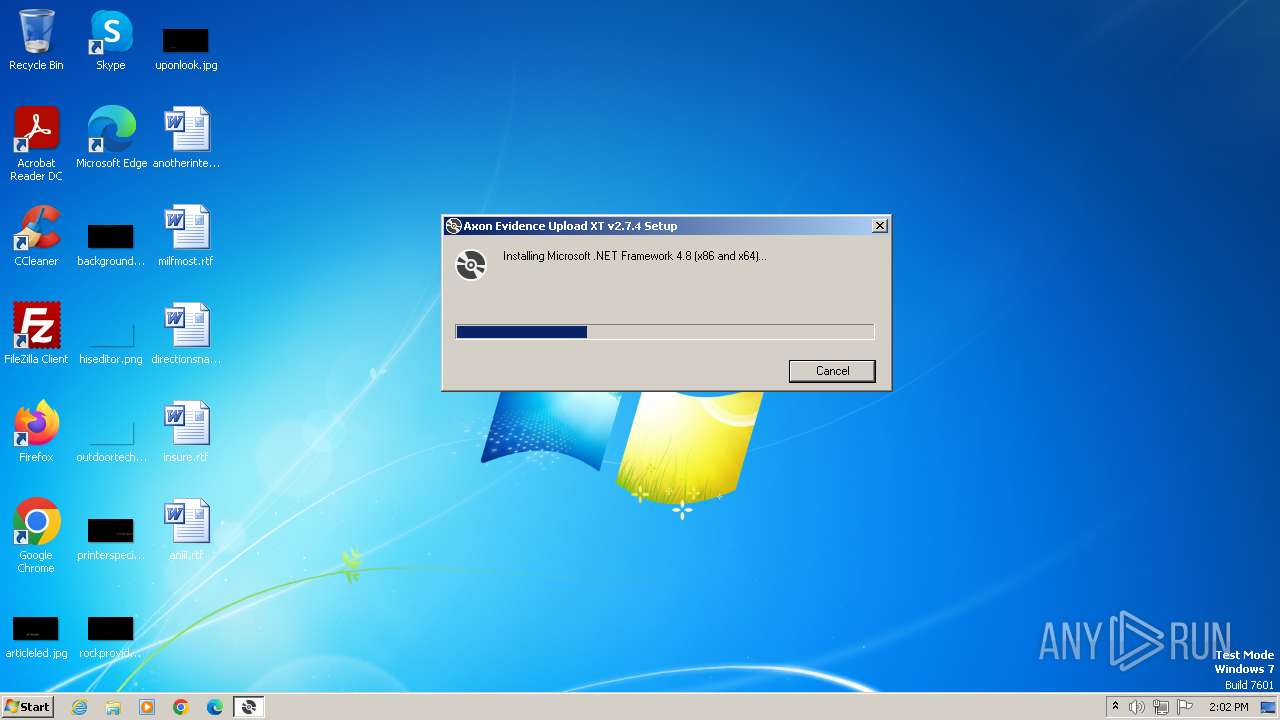
| Verdict: | Malicious activity |
| Analysis date: | November 22, 2023, 13:57:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 717A0C46B0BA79497C61176FDA6601E1 |
| SHA1: | 07859D077F8A093EE46CFA55DAB45DDCF8850577 |
| SHA256: | 944A49BA89C4A973EDA1C1449CB6D8B6549B728F5E091BD0263DD8570FEBBAA6 |
| SSDEEP: | 12288:Eu/4aRMhRs2dvhp3BKdccceIVtqZZrAttJVVVVVVVVVVVVVVVVVVVOVVVVVVVVVf:EsDMhRsQho656lde+ |
MALICIOUS
Drops the executable file immediately after the start
- setup.exe (PID: 3428)
- NDP48-Web.exe (PID: 3732)
SUSPICIOUS
Reads the Internet Settings
- setup.exe (PID: 3428)
- Setup.exe (PID: 4004)
Reads security settings of Internet Explorer
- setup.exe (PID: 3428)
- Setup.exe (PID: 4004)
Reads settings of System Certificates
- setup.exe (PID: 3428)
- Setup.exe (PID: 4004)
Checks Windows Trust Settings
- setup.exe (PID: 3428)
- Setup.exe (PID: 4004)
Process drops legitimate windows executable
- setup.exe (PID: 3428)
- NDP48-Web.exe (PID: 3732)
INFO
Checks proxy server information
- setup.exe (PID: 3428)
Reads the machine GUID from the registry
- setup.exe (PID: 3428)
- wmpnscfg.exe (PID: 3472)
- NDP48-Web.exe (PID: 3732)
- Setup.exe (PID: 4004)
- SetupUtility.exe (PID: 3872)
Checks supported languages
- setup.exe (PID: 3428)
- NDP48-Web.exe (PID: 3732)
- wmpnscfg.exe (PID: 3472)
- Setup.exe (PID: 4004)
- SetupUtility.exe (PID: 3684)
- SetupUtility.exe (PID: 3872)
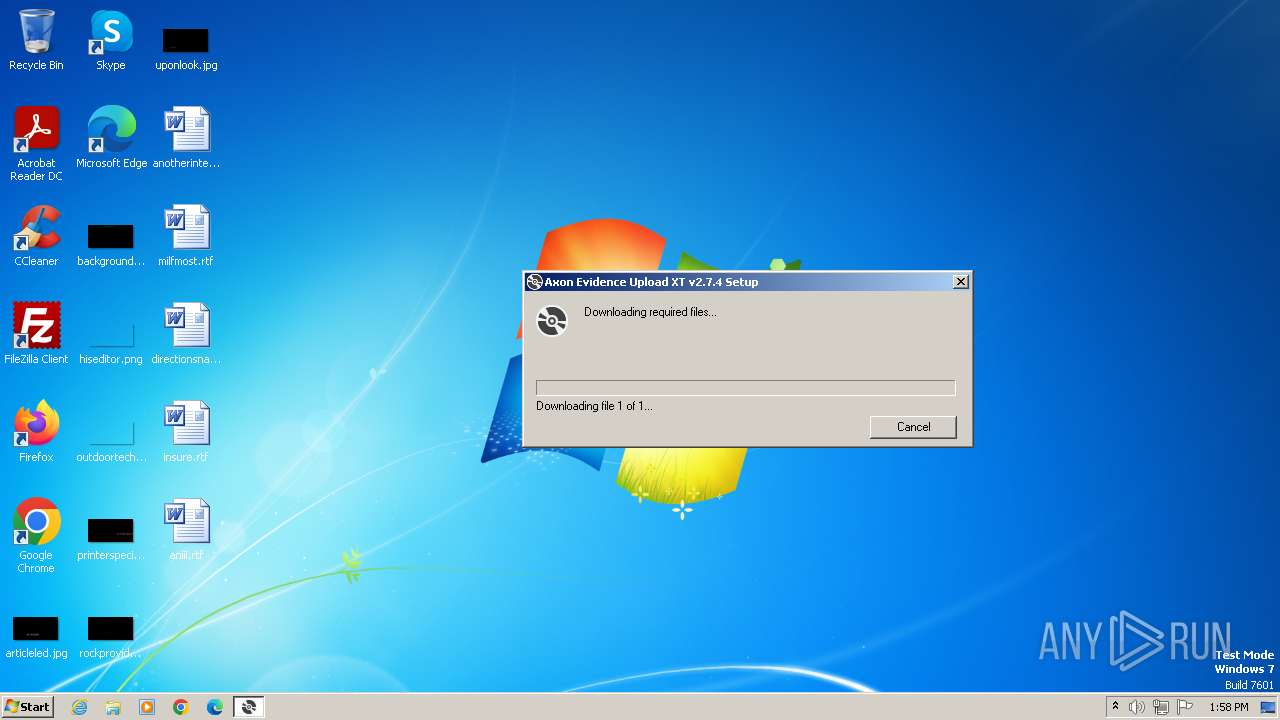
Create files in a temporary directory
- setup.exe (PID: 3428)
- Setup.exe (PID: 4004)
- NDP48-Web.exe (PID: 3732)
- SetupUtility.exe (PID: 3872)
Reads the computer name
- NDP48-Web.exe (PID: 3732)
- setup.exe (PID: 3428)
- wmpnscfg.exe (PID: 3472)
- Setup.exe (PID: 4004)
- SetupUtility.exe (PID: 3684)
- SetupUtility.exe (PID: 3872)
Manual execution by a user
- wmpnscfg.exe (PID: 3472)
Creates files or folders in the user directory
- setup.exe (PID: 3428)
- Setup.exe (PID: 4004)
Reads CPU info
- Setup.exe (PID: 4004)
Reads Environment values
- Setup.exe (PID: 4004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:01:12 21:48:08+01:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.32 |
| CodeSize: | 391168 |
| InitializedDataSize: | 166912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x39de4 |
| OSVersion: | 5.1 |
| ImageVersion: | 10 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 17.0.33312.129 |
| ProductVersionNumber: | 17.0.33312.129 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | Setup |
| FileVersion: | 17.0.33312.129 built by: D17.5 |
| InternalName: | setup.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | setup.exe |
| ProductName: | - |
| ProductVersion: | 17.0.33312.129 |
Total processes
45
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3428 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Exit code: 0 Version: 17.0.33312.129 built by: D17.5 Modules
| |||||||||||||||
| 3472 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3684 | SetupUtility.exe /screboot | C:\046678841f2debd5084157ecf7\SetupUtility.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.5 Setup Exit code: 0 Version: 14.8.4110.0 built by: NET48REL1LAST_B Modules
| |||||||||||||||
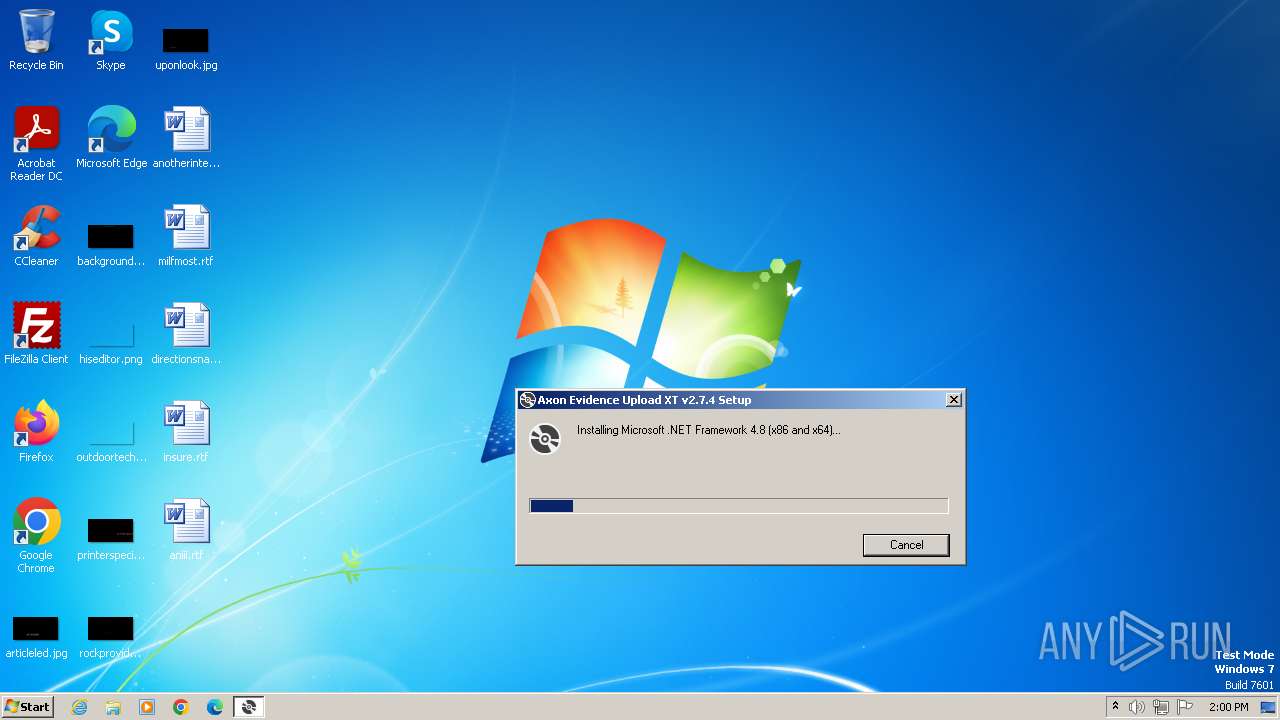
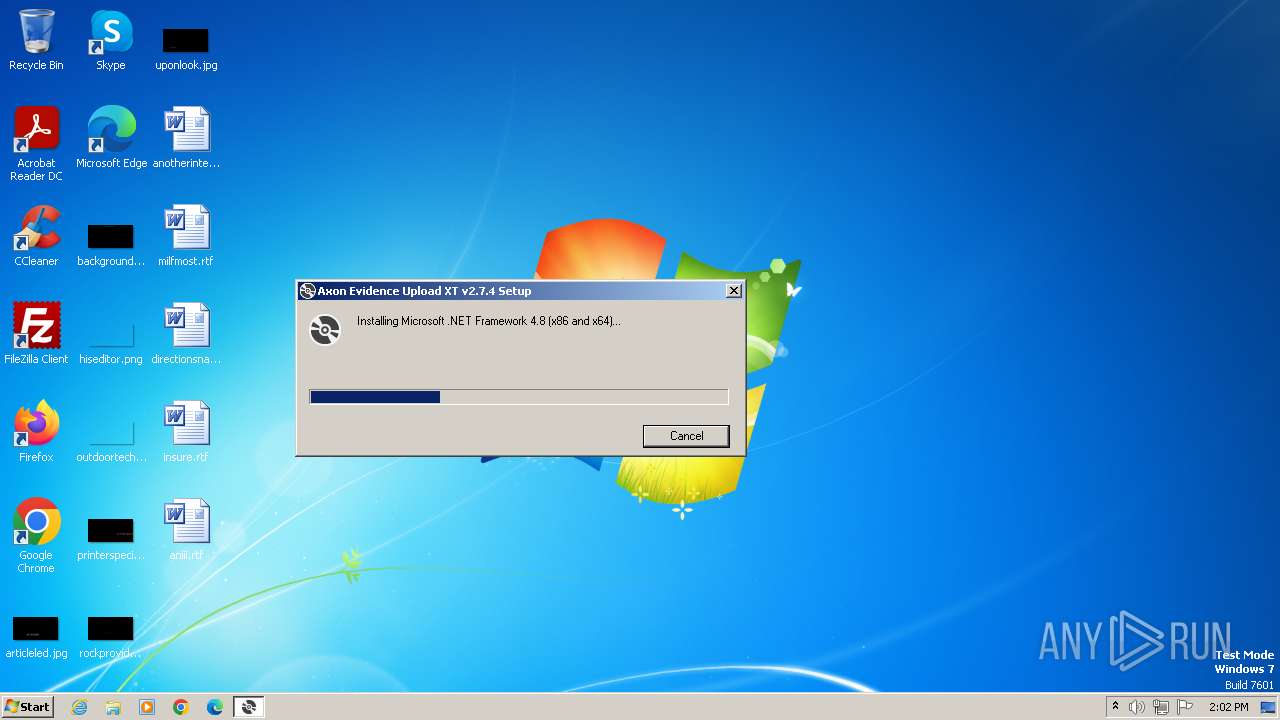
| 3732 | "C:\Users\admin\AppData\Local\Temp\VSD7999.tmp\DotNetFX48\NDP48-Web.exe" /q /norestart /ChainingPackage FullX64Bootstrapper /lcid 1033 | C:\Users\admin\AppData\Local\Temp\VSD7999.tmp\DotNetFX48\NDP48-Web.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.8 Setup Exit code: 0 Version: 4.8.04115.00 Modules
| |||||||||||||||
| 3828 | "C:\Users\admin\AppData\Local\Temp\VSD7999.tmp\DotNetFX48\NDP48-Web.exe" /q /norestart /ChainingPackage FullX64Bootstrapper /lcid 1033 | C:\Users\admin\AppData\Local\Temp\VSD7999.tmp\DotNetFX48\NDP48-Web.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework 4.8 Setup Exit code: 3221226540 Version: 4.8.04115.00 Modules
| |||||||||||||||
| 3872 | SetupUtility.exe /aupause | C:\046678841f2debd5084157ecf7\SetupUtility.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.5 Setup Exit code: 0 Version: 14.8.4110.0 built by: NET48REL1LAST_B Modules
| |||||||||||||||
| 4004 | C:\046678841f2debd5084157ecf7\\Setup.exe /q /norestart /ChainingPackage FullX64Bootstrapper /lcid 1033 /x86 /x64 /web | C:\046678841f2debd5084157ecf7\Setup.exe | NDP48-Web.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 14.8.4110.0 built by: NET48REL1LAST_B Modules
| |||||||||||||||
Total events
10 492
Read events
10 453
Write events
36
Delete events
3
Modification events
| (PID) Process: | (3428) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3428) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3428) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3428) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3428) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3428) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000059010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3428) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3428) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3472) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{632685C7-1C38-4F2C-9E48-212AFD654D44}\{654C6E4B-88B8-423A-91EF-F5A40373EBAF} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3472) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{632685C7-1C38-4F2C-9E48-212AFD654D44} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
32
Suspicious files
14
Text files
80
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3428 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3428 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:1CAB7BC814A92D41C8D3BD5C9577449D | SHA256:A9826BA2C7389E30F8EE191ED8830004D8E93C056E43AF4421D5A76FAD7C539B | |||
| 3732 | NDP48-Web.exe | C:\046678841f2debd5084157ecf7\SplashScreen.bmp | image | |
MD5:BC32088BFAA1C76BA4B56639A2DEC592 | SHA256:B05141DBC71669A7872A8E735E5E43A7F9713D4363B7A97543E1E05DCD7470A7 | |||
| 3428 | setup.exe | C:\Users\admin\AppData\Local\Temp\VSD7999.tmp\setup.exe | executable | |
MD5:717A0C46B0BA79497C61176FDA6601E1 | SHA256:944A49BA89C4A973EDA1C1449CB6D8B6549B728F5E091BD0263DD8570FEBBAA6 | |||
| 3428 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:412E1A9B73F94EB79968A313E507683E | SHA256:479505588CCFDB782ADE1F2800A694836BEBCBFCFCD1CA5EAD95938D5CDD418A | |||
| 3428 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:FC02C66B632C0FF121F2D1A2680DB18E | SHA256:543FA8142B9CCB06DCE98B4689DA1C939CB440AB8EF35FB252E96E57D6A5CF91 | |||
| 3732 | NDP48-Web.exe | C:\046678841f2debd5084157ecf7\DisplayIcon.ico | image | |
MD5:F9657D290048E169FFABBBB9C7412BE0 | SHA256:B74AD253B9B8F9FCADE725336509143828EE739CC2B24782BE3ECFF26F229160 | |||
| 3428 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\ndp48-web[1].exe | executable | |
MD5:34A5C76979563918B953E66E0D39C7EF | SHA256:0BBA3094588C4BFEC301939985222A20B340BF03431563DEC8B2B4478B06FFFA | |||
| 3428 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F9C57C8B55E84B295CBBD8CF3D95BF44 | binary | |
MD5:D646EF5B0DADF630A5C84F18F4FEF969 | SHA256:962F500CA73BD11C870E945BA06A62E2E29D87EC8C9494034706959E1BFD476C | |||
| 3732 | NDP48-Web.exe | C:\046678841f2debd5084157ecf7\Graphics\Rotate2.ico | image | |
MD5:F824905E5501603E6720B784ADD71BDD | SHA256:D15A6F1EEFEFE4F9CD51B7B22E9C7B07C7ACAD72FD53E5F277E6D4E0976036C3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
16
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
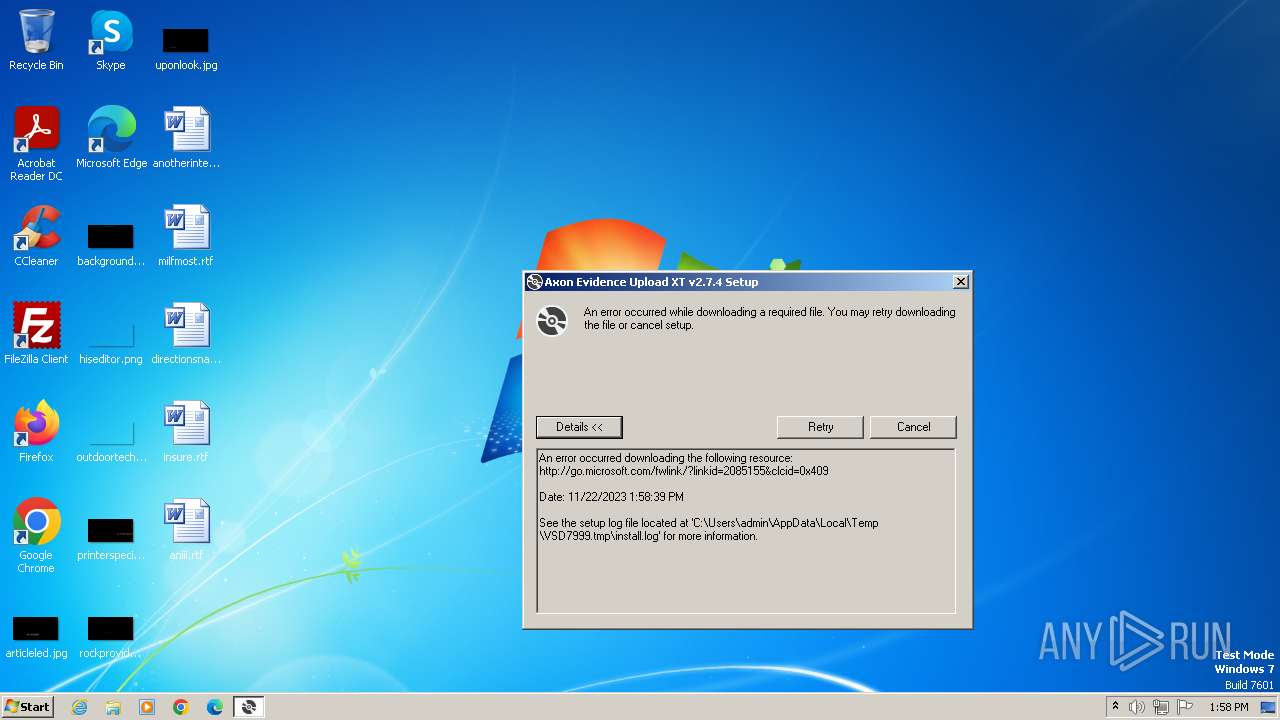
3428 | setup.exe | GET | 302 | 23.32.186.57:80 | http://go.microsoft.com/fwlink/?linkid=2085155&clcid=0x409 | unknown | — | — | unknown |
3428 | setup.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
3428 | setup.exe | GET | — | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
3428 | setup.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | binary | 1.05 Kb | unknown |
4004 | Setup.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | binary | 519 b | unknown |
868 | svchost.exe | HEAD | 302 | 23.32.186.57:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03761.00&sar=x86&o1=netfx_Full.mzz | unknown | — | — | unknown |
4004 | Setup.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | binary | 1.11 Kb | unknown |
3428 | setup.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/certs/MicCodSigPCA2011_2011-07-08.crt | unknown | binary | 1.87 Kb | unknown |
4004 | Setup.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | binary | 1.05 Kb | unknown |
4004 | Setup.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | binary | 767 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
868 | svchost.exe | 95.101.148.135:80 | armmf.adobe.com | Akamai International B.V. | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3428 | setup.exe | 23.32.186.57:80 | go.microsoft.com | AKAMAI-AS | BR | unknown |
3428 | setup.exe | 68.232.34.200:443 | download.visualstudio.microsoft.com | EDGECAST | US | whitelisted |
3428 | setup.exe | 8.241.122.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
3428 | setup.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3428 | setup.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
3428 | setup.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
download.visualstudio.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |