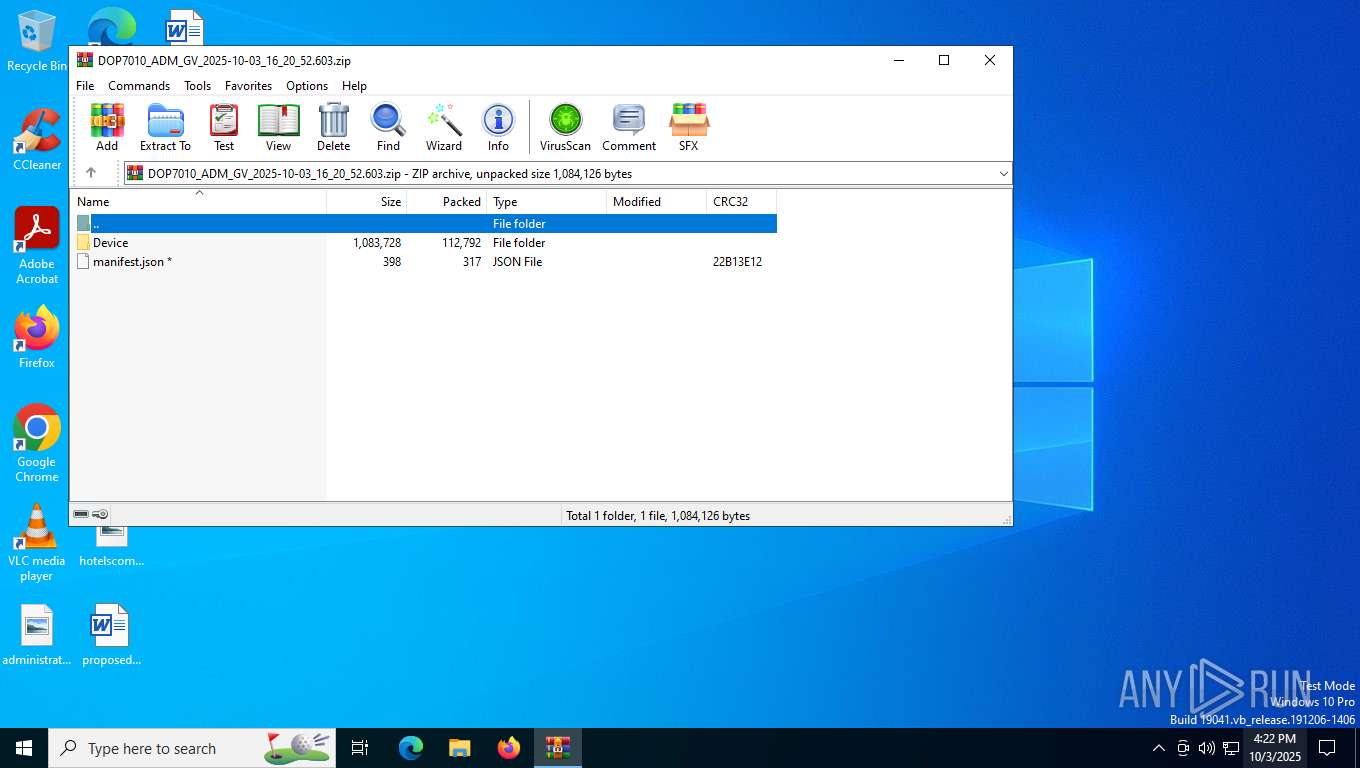
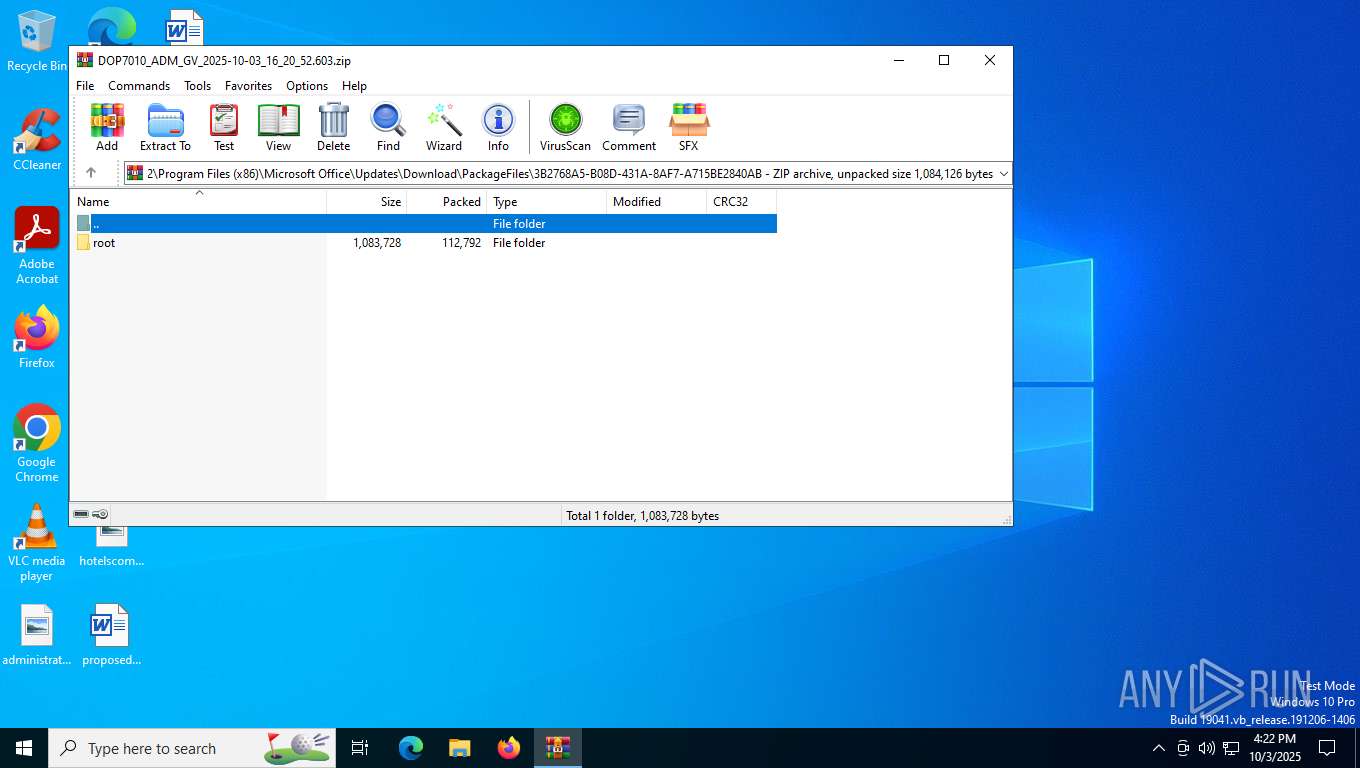
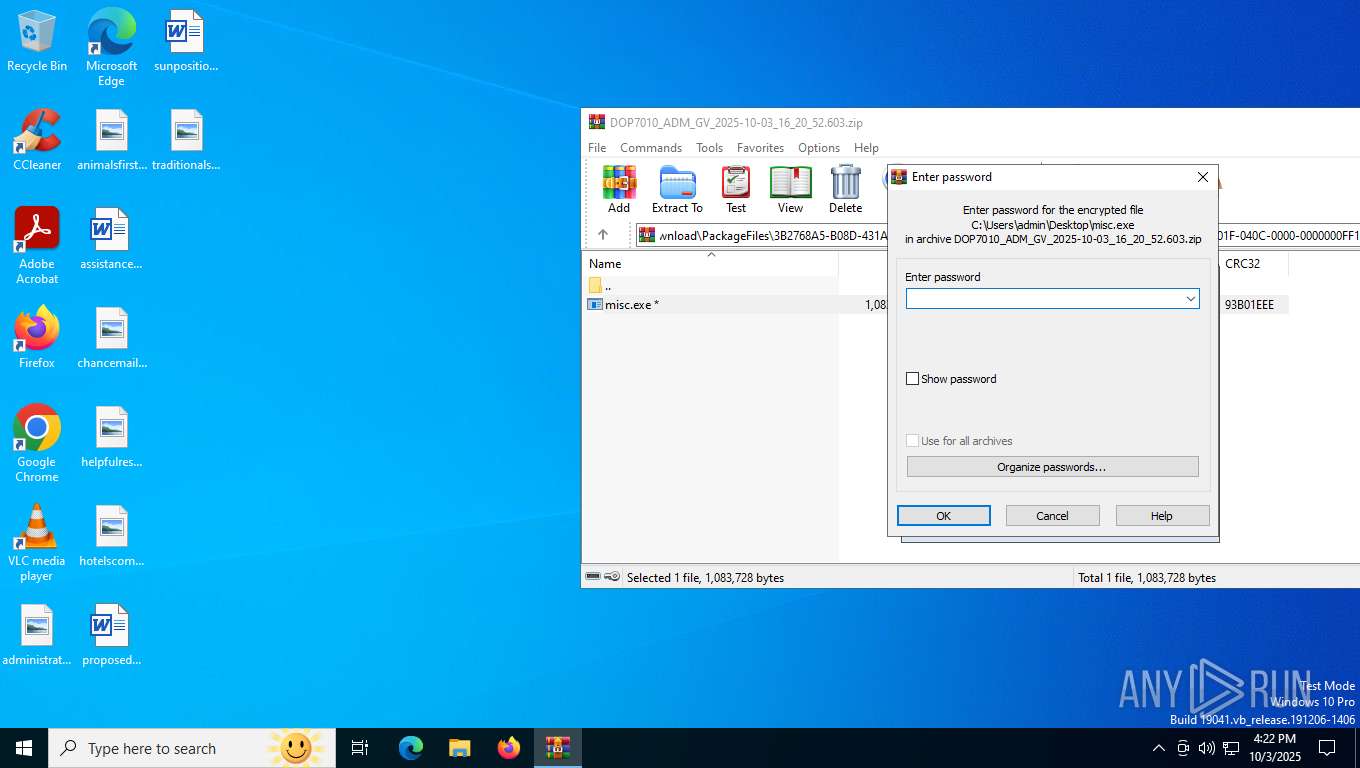
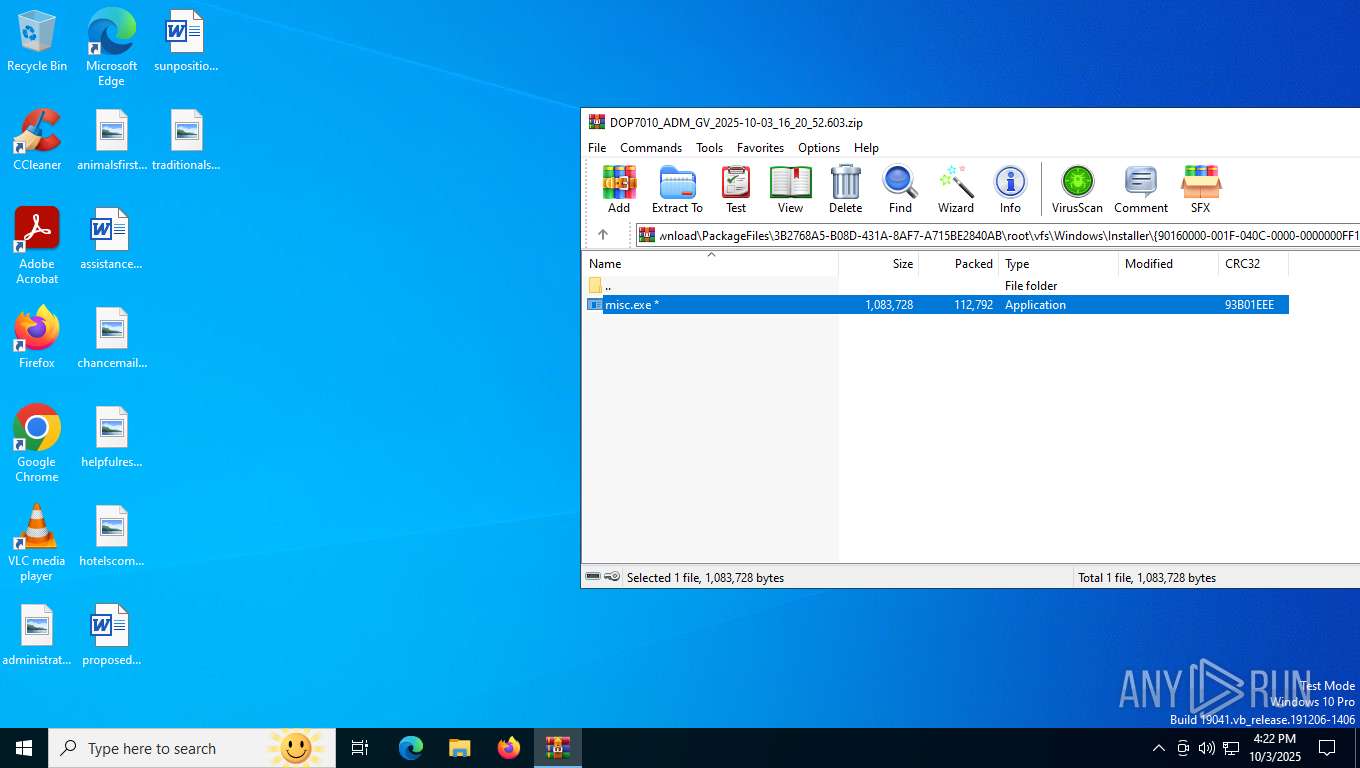
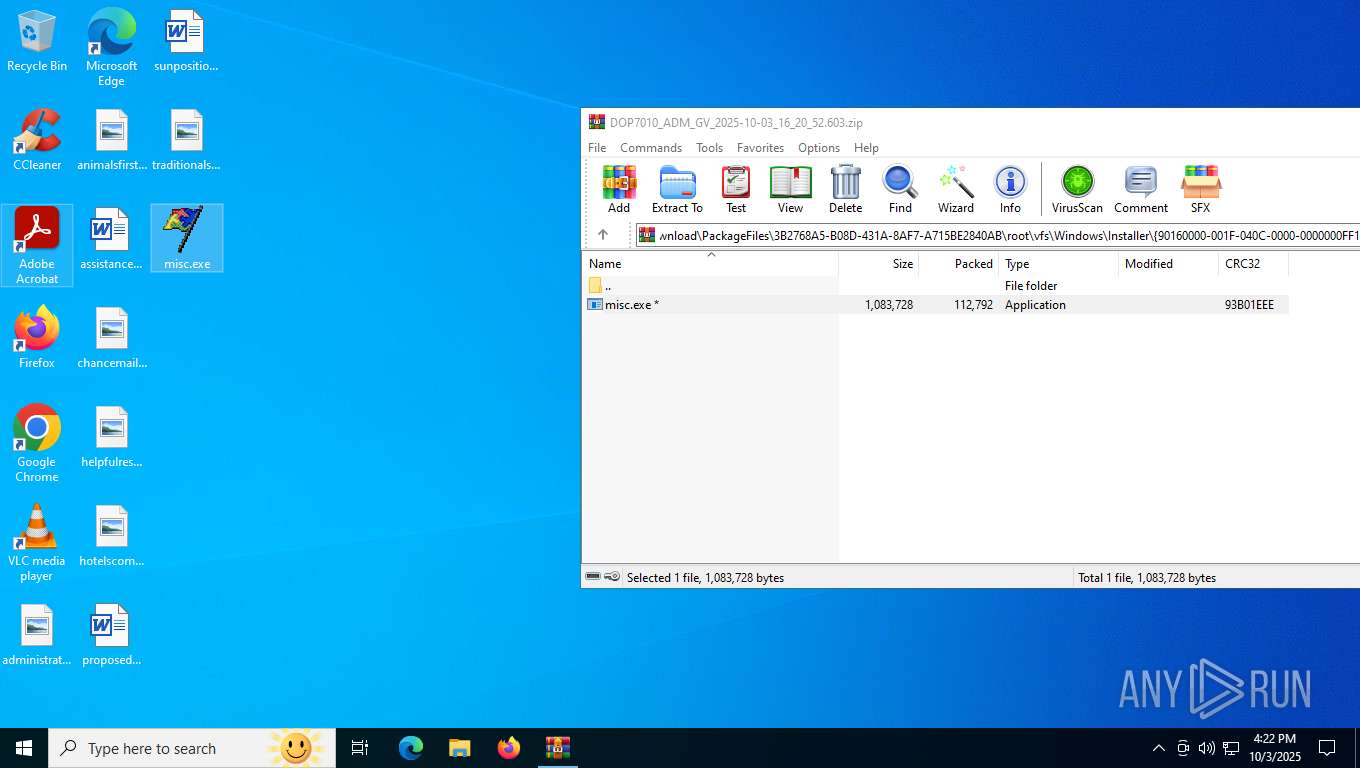
| File name: | DOP7010_ADM_GV_2025-10-03_16_20_52.603.zip |
| Full analysis: | https://app.any.run/tasks/c05ec889-034a-4235-b2b0-3d9071ba3f02 |
| Verdict: | Malicious activity |
| Analysis date: | October 03, 2025, 16:22:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | EA18523303DEE30AE4DEEB205AFAA409 |
| SHA1: | 09FCC4CF93990F82FCCC459751B27BCE93CEA1F0 |
| SHA256: | 943E0EEBCA3F0EAC7448E5BF56765FBEB2B329696568B1AA96EF014DD1339236 |
| SSDEEP: | 3072:A61rv7WgmD5/9mY32q0tv1l1YQjfavqW0rQGNarwzs+trYRh:l1rDWgMmEevr1Y+eqxkGNarwI+xU |
MALICIOUS
NESHTA mutex has been found
- misc.exe (PID: 6388)
- misc.exe (PID: 6244)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8)
- misc.exe (PID: 6388)
- misc.exe (PID: 6244)
Executable content was dropped or overwritten
- misc.exe (PID: 6388)
- misc.exe (PID: 6244)
Mutex name with non-standard characters
- misc.exe (PID: 6244)
- misc.exe (PID: 6388)
Process drops legitimate windows executable
- misc.exe (PID: 6388)
- misc.exe (PID: 6244)
INFO
Checks supported languages
- misc.exe (PID: 6388)
- misc.exe (PID: 6244)
Process checks computer location settings
- misc.exe (PID: 6388)
- misc.exe (PID: 6244)
Create files in a temporary directory
- misc.exe (PID: 6388)
- misc.exe (PID: 6244)
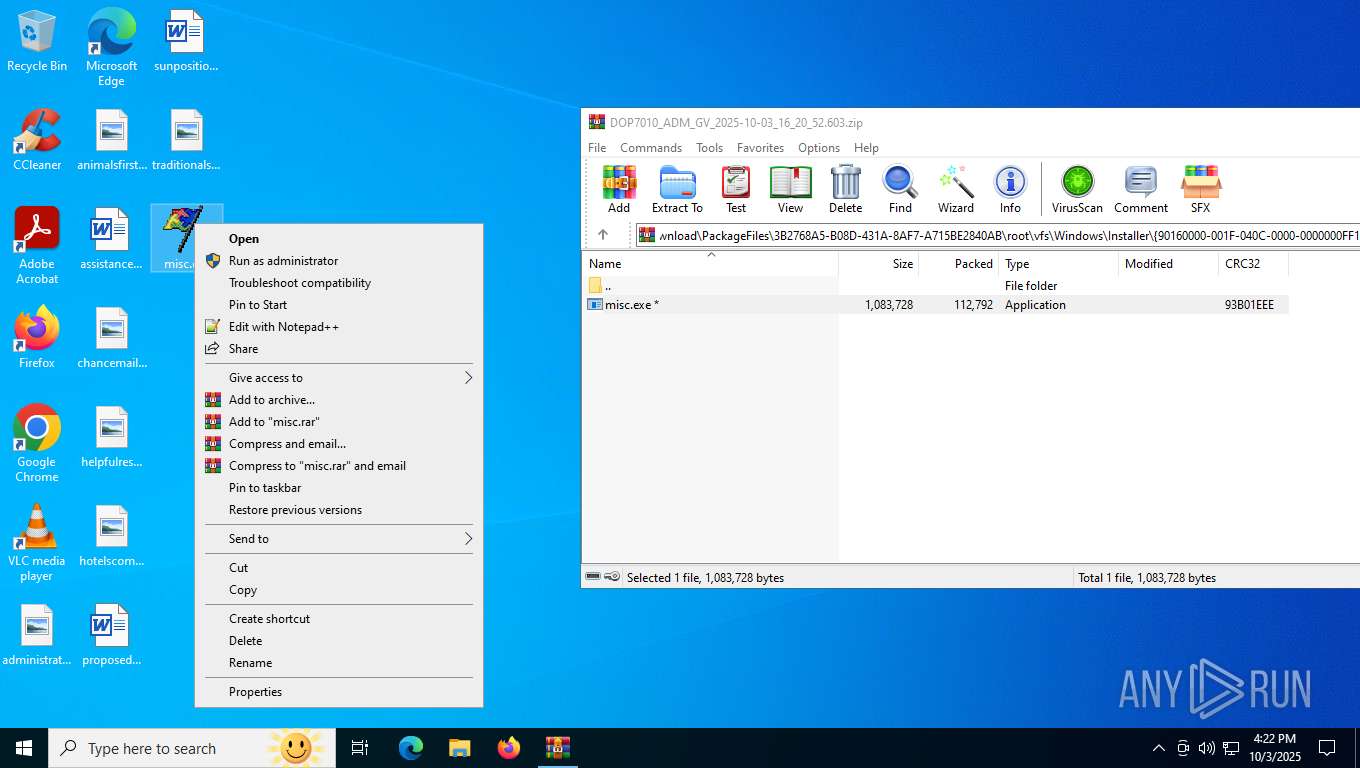
Manual execution by a user
- misc.exe (PID: 6244)
Reads the computer name
- misc.exe (PID: 6244)
- misc.exe (PID: 6388)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
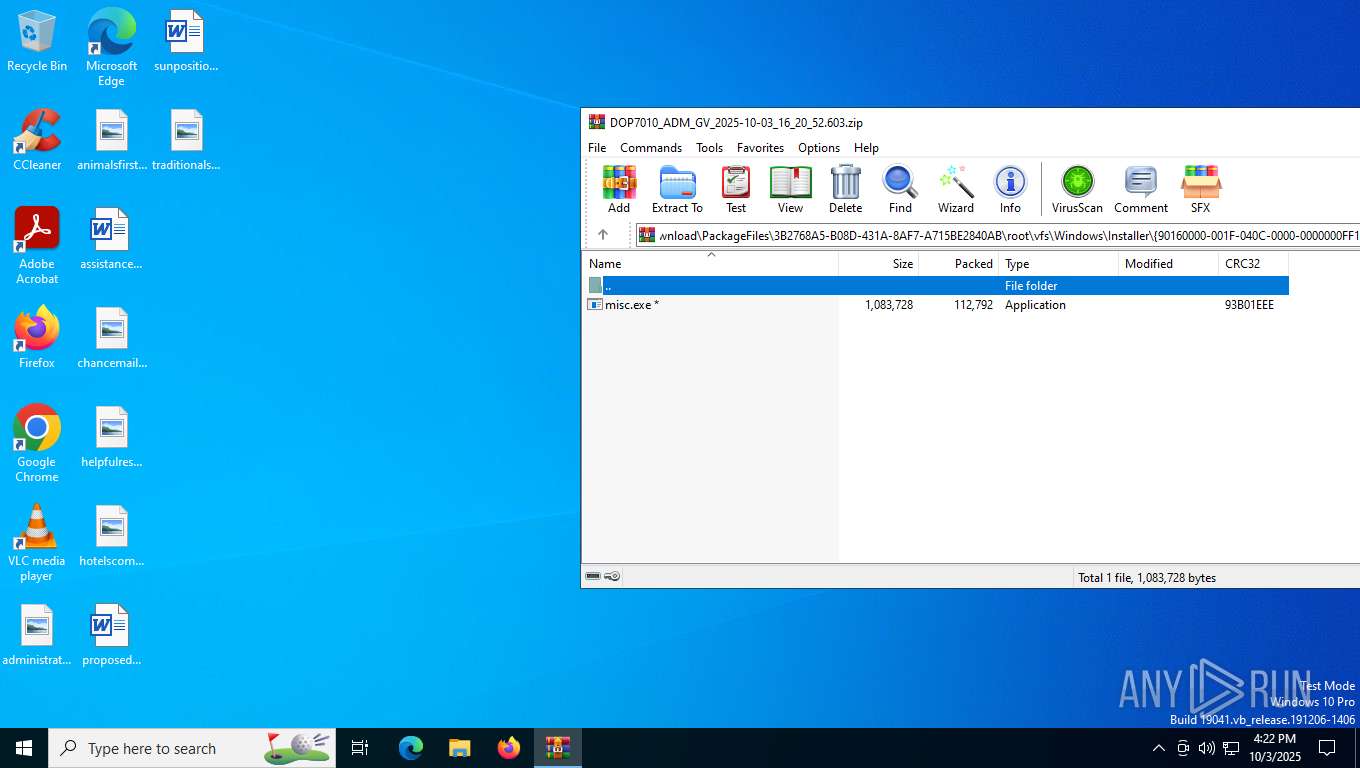
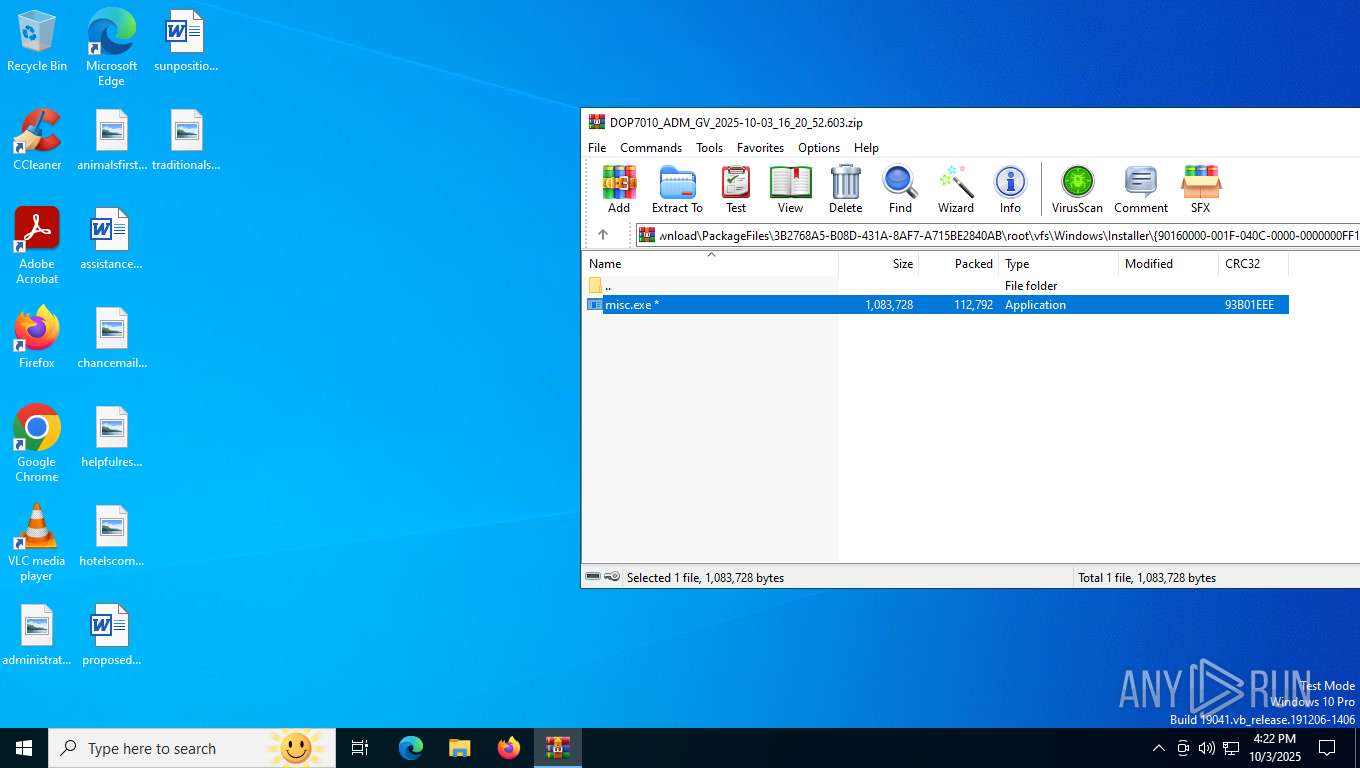
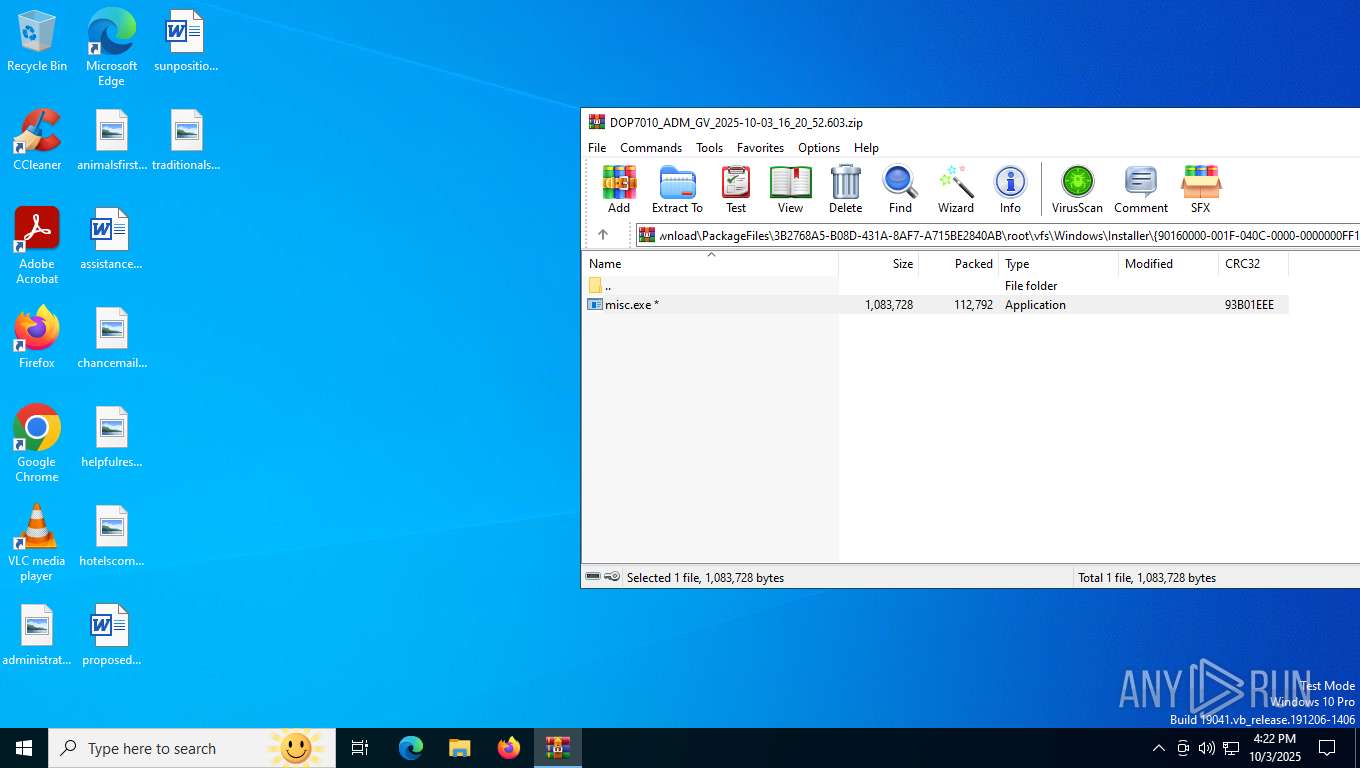
| ZipCRC: | 0x93b01eee |
| ZipCompressedSize: | 112792 |
| ZipUncompressedSize: | 1083728 |
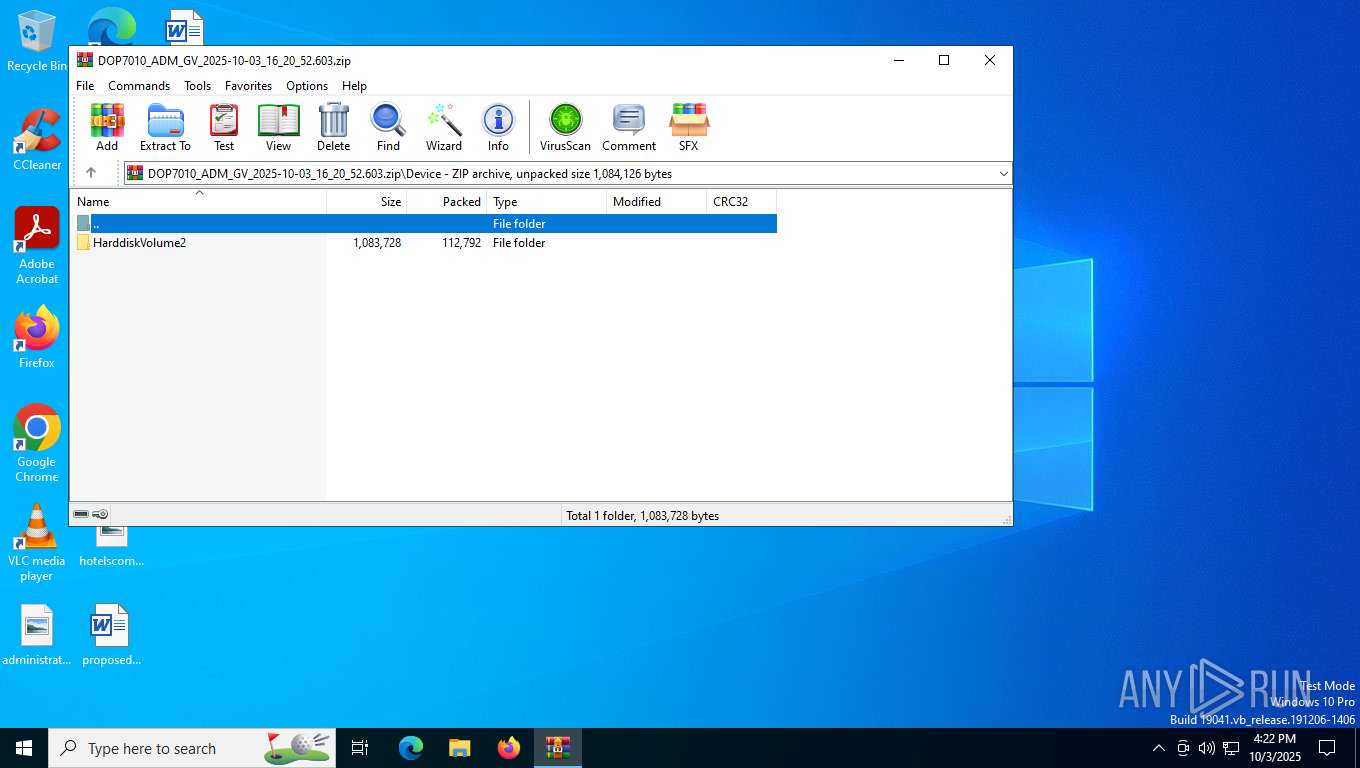
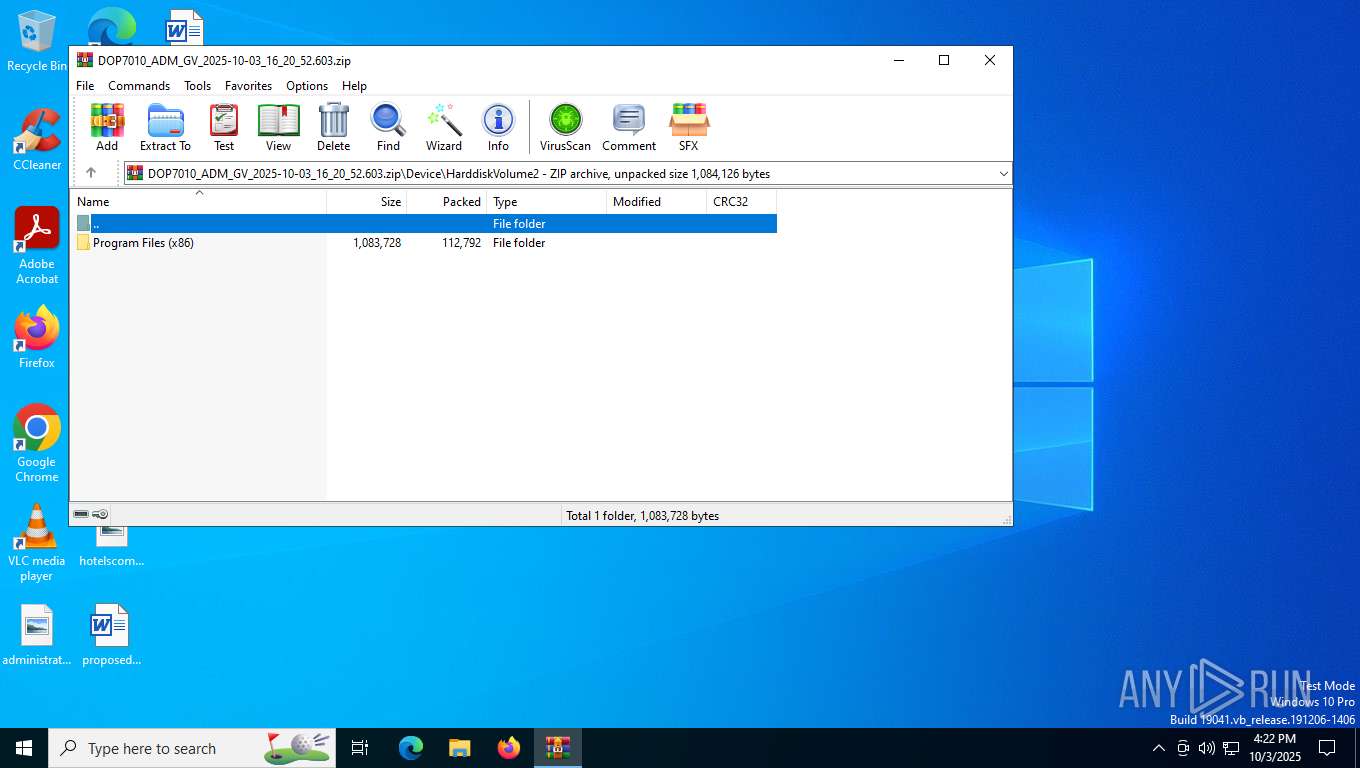
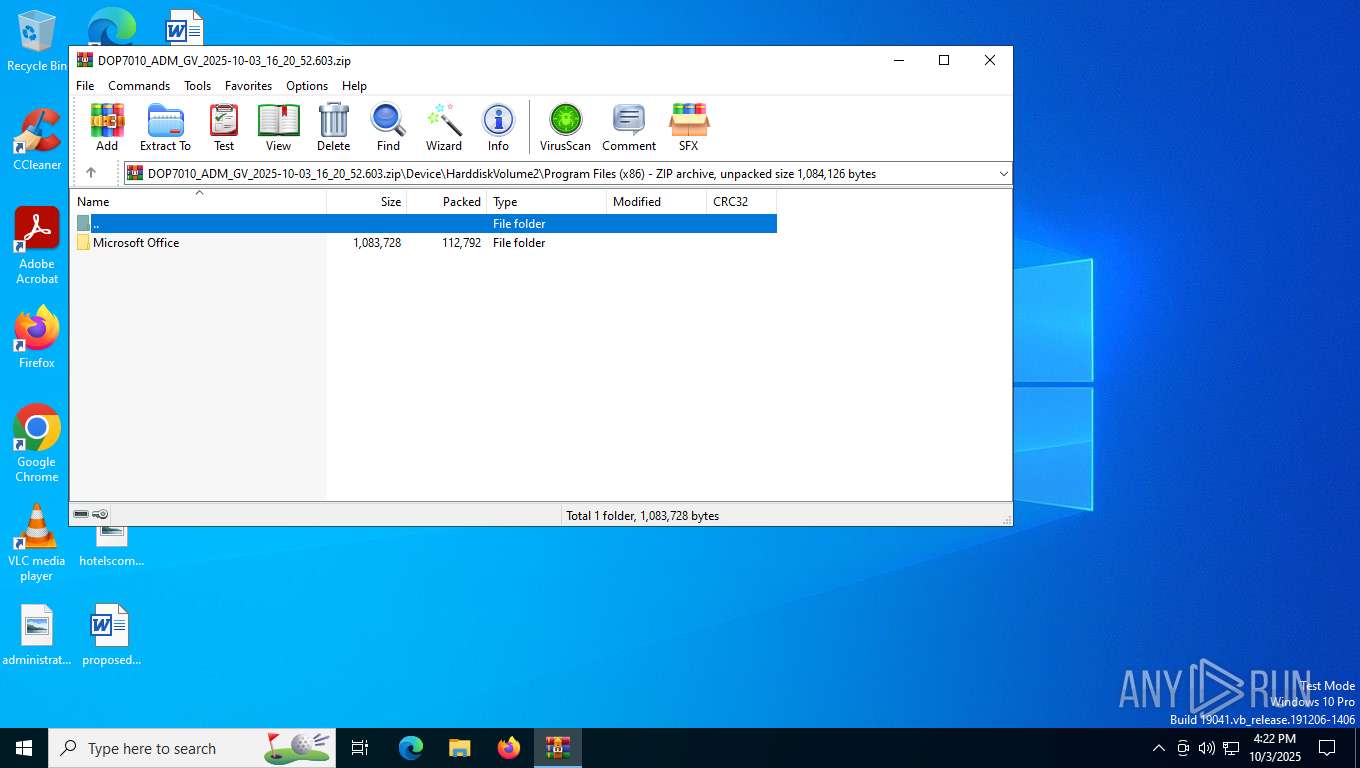
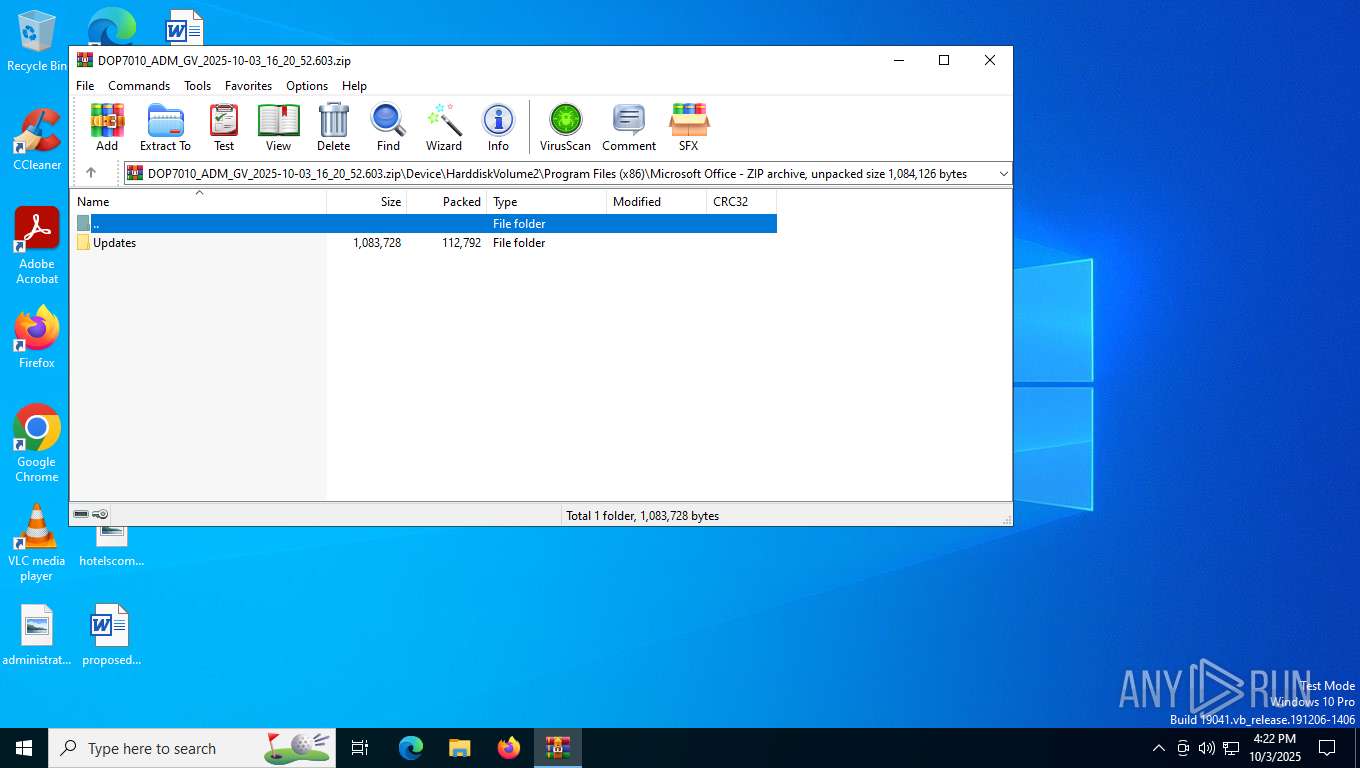
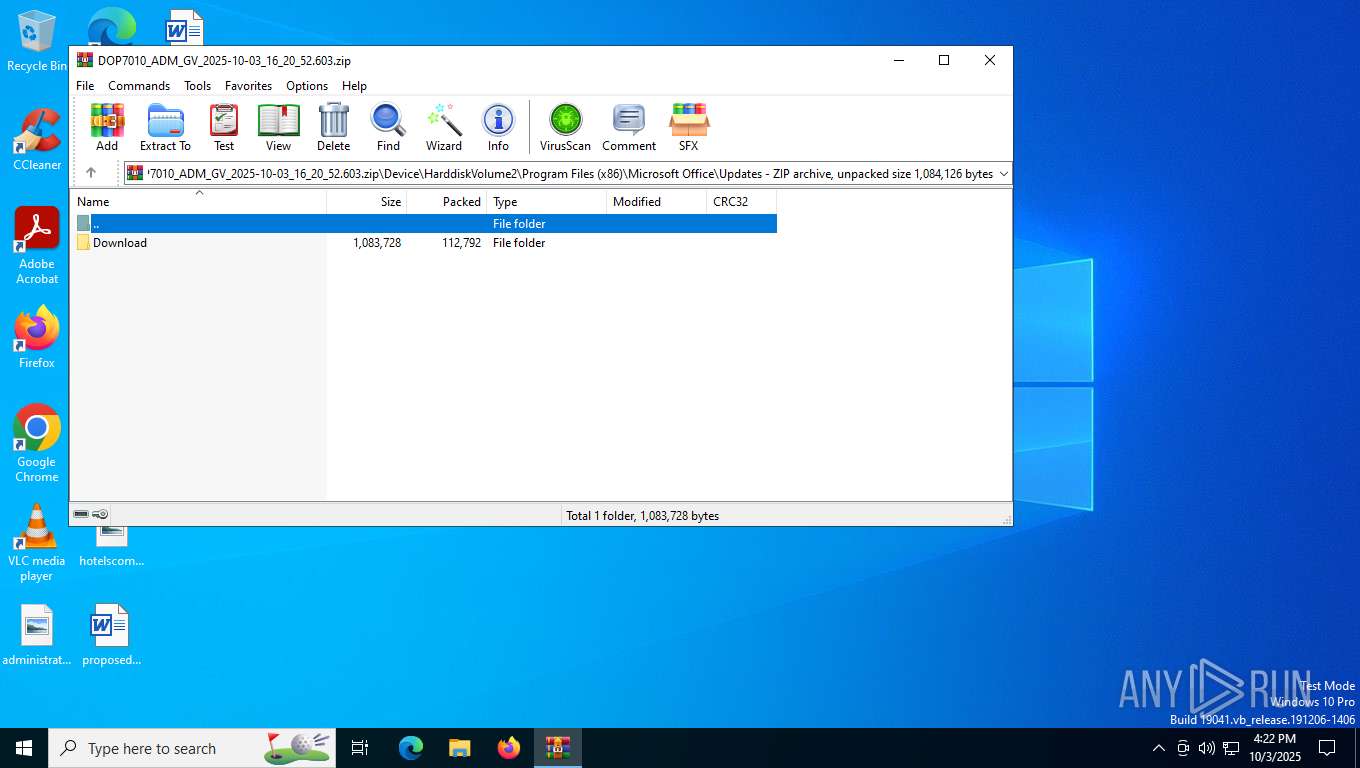
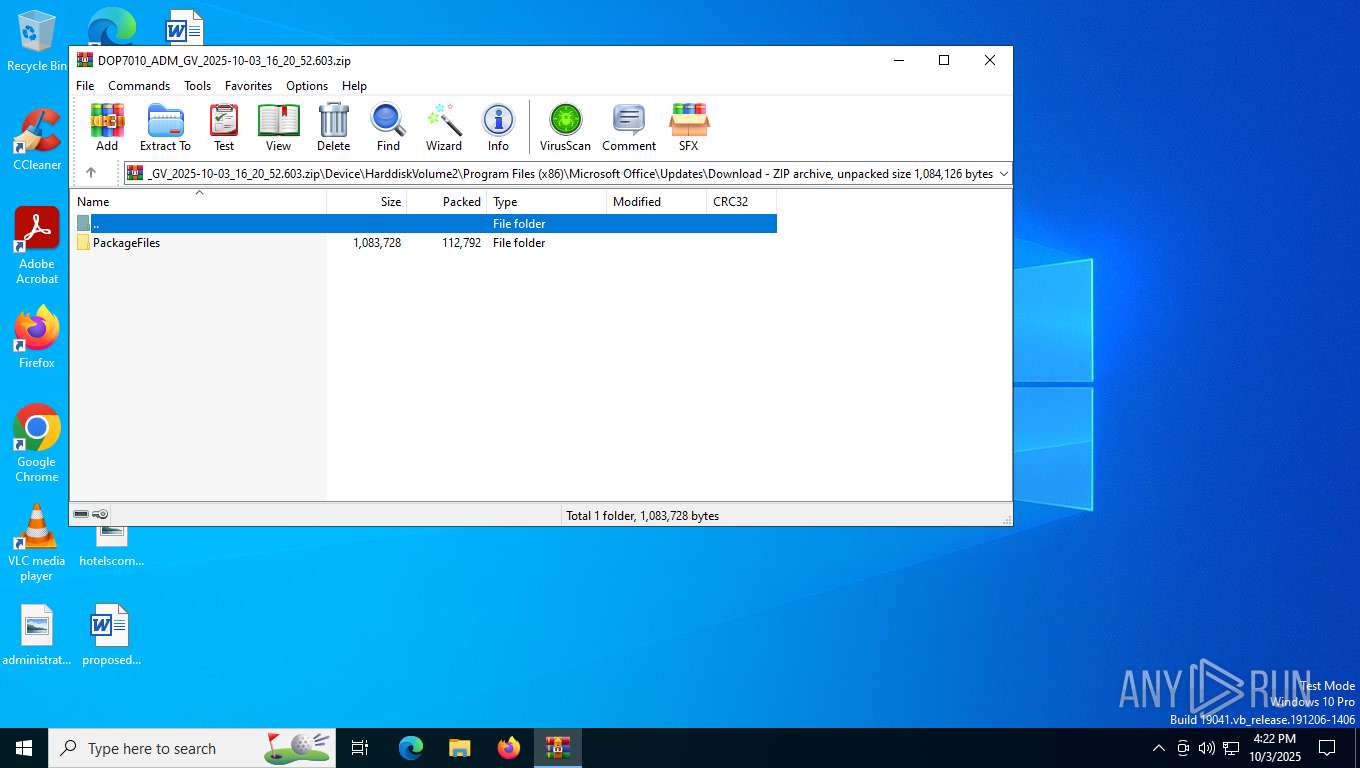
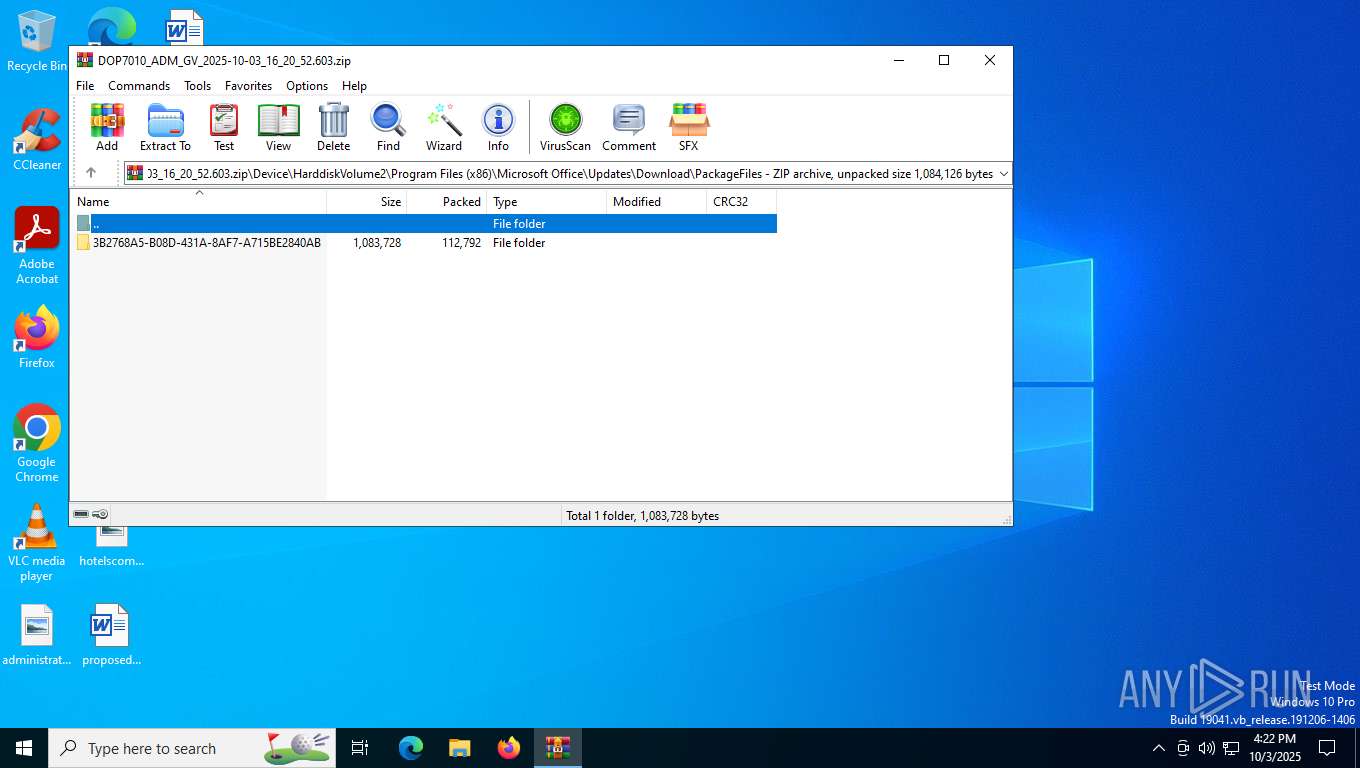
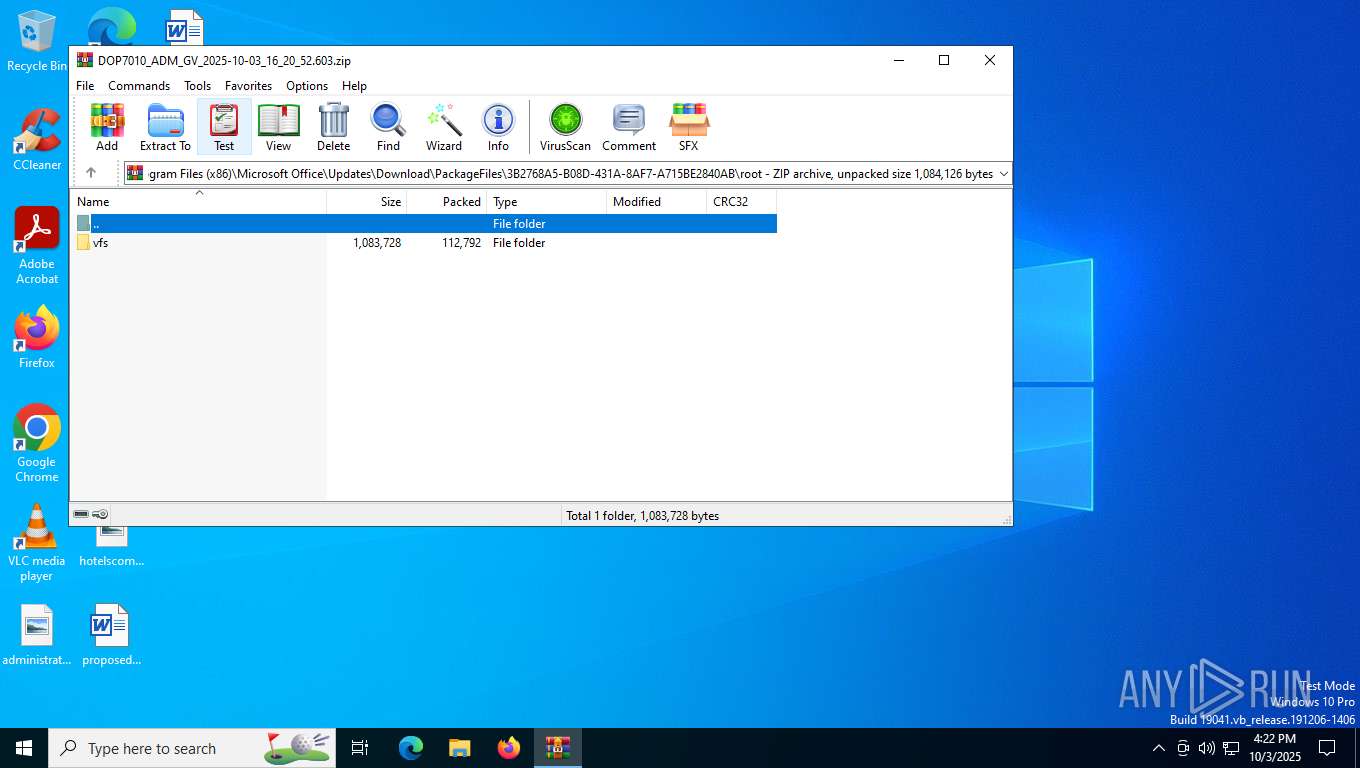
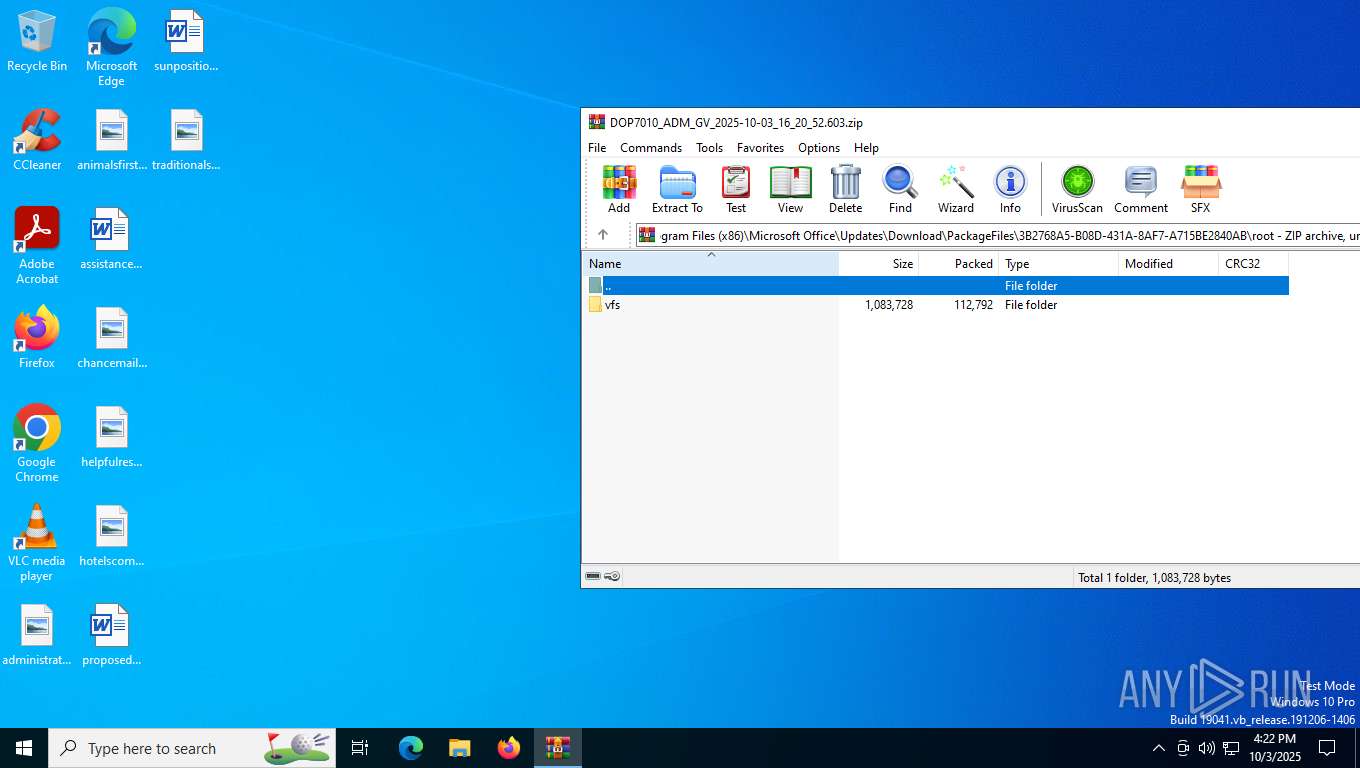
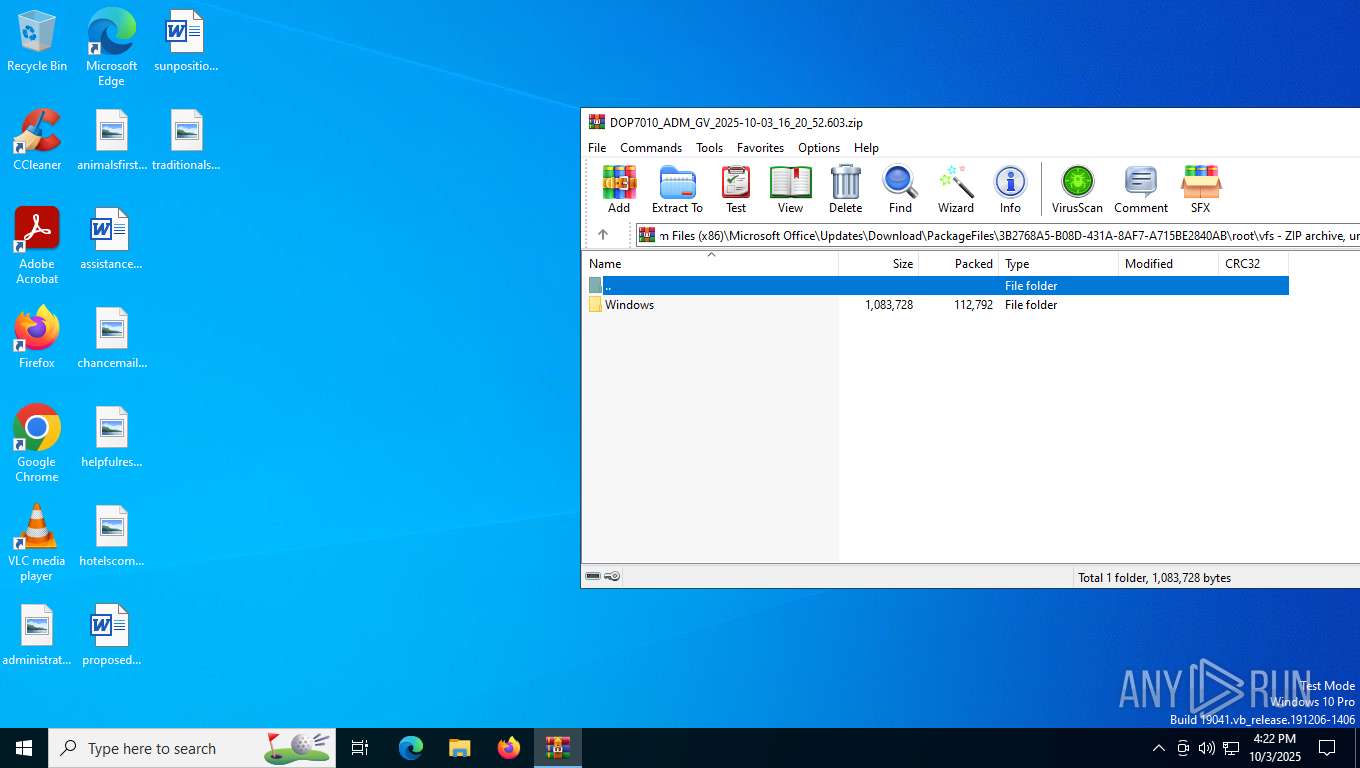
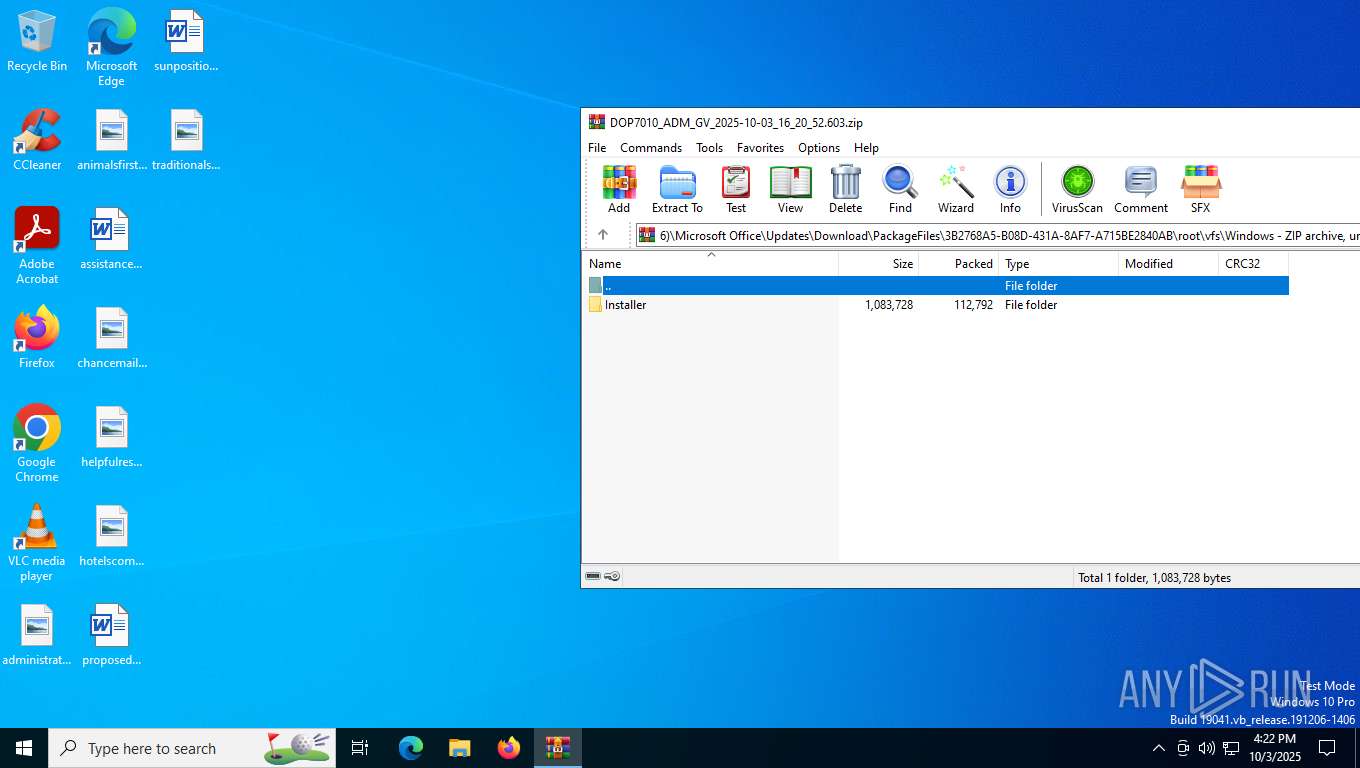
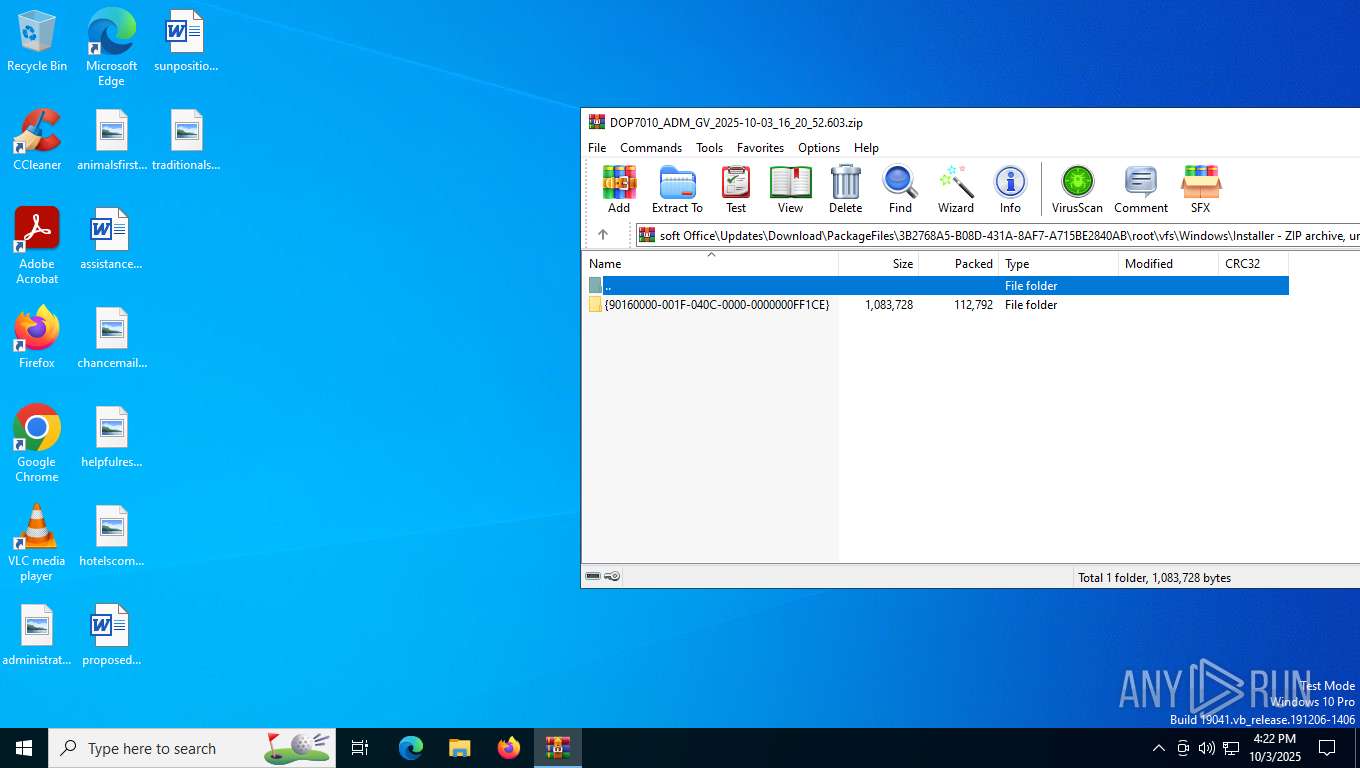
| ZipFileName: | Device/HarddiskVolume2/Program Files (x86)/Microsoft Office/Updates/Download/PackageFiles/3B2768A5-B08D-431A-8AF7-A715BE2840AB/root/vfs/Windows/Installer/{90160000-001F-040C-0000-0000000FF1CE}/misc.exe |
Total processes
171
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\DOP7010_ADM_GV_2025-10-03_16_20_52.603.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1408 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6244 | "C:\Users\admin\Desktop\misc.exe" | C:\Users\admin\Desktop\misc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
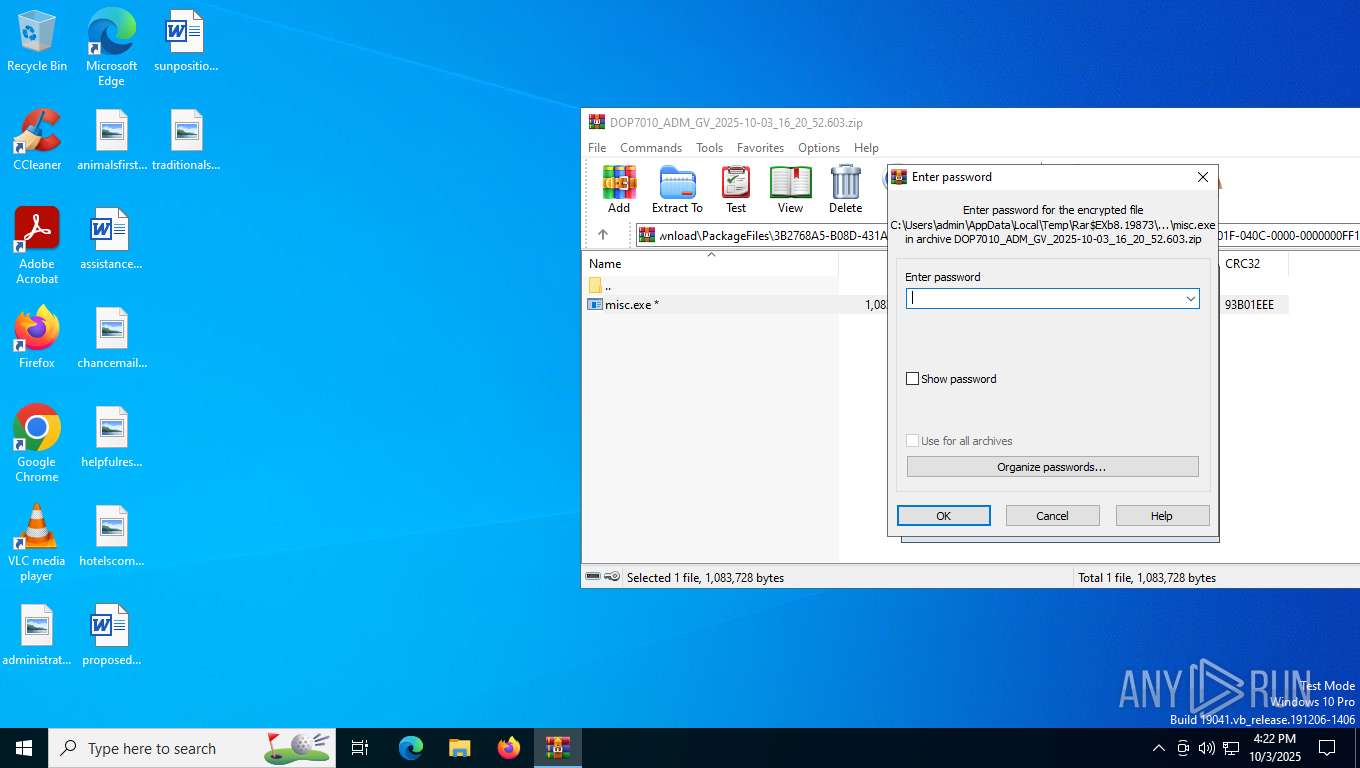
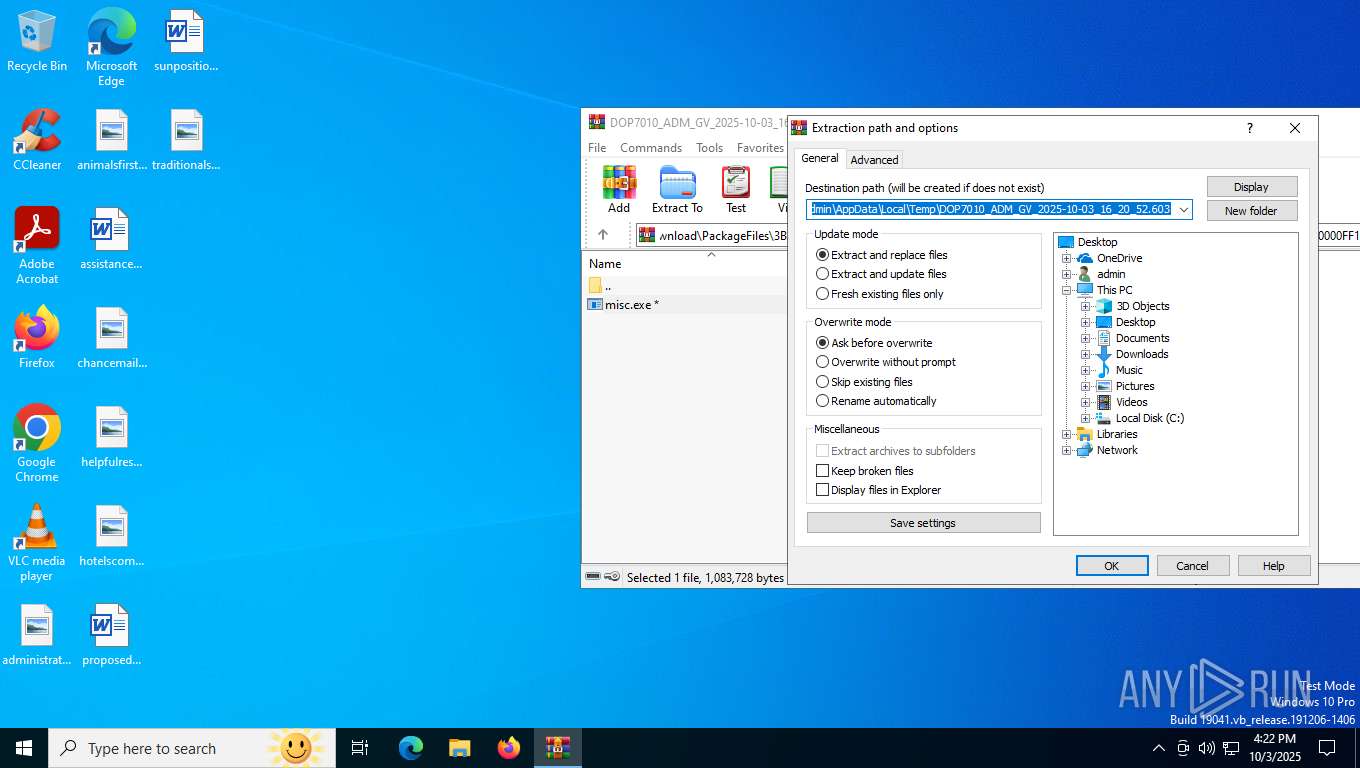
| 6388 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb8.19873\Device\HarddiskVolume2\Program Files (x86)\Microsoft Office\Updates\Download\PackageFiles\3B2768A5-B08D-431A-8AF7-A715BE2840AB\root\vfs\Windows\Installer\{90160000-001F-040C-0000-0000000FF1CE}\misc.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb8.19873\Device\HarddiskVolume2\Program Files (x86)\Microsoft Office\Updates\Download\PackageFiles\3B2768A5-B08D-431A-8AF7-A715BE2840AB\root\vfs\Windows\Installer\{90160000-001F-040C-0000-0000000FF1CE}\misc.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
9 193
Read events
9 165
Write events
15
Delete events
13
Modification events
| (PID) Process: | (8) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (8) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (8) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\DOP7010_ADM_GV_2025-10-03_16_20_52.603.zip | |||
| (PID) Process: | (8) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
12
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6388 | misc.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileSyncConfig.exe | executable | |
MD5:0C5EC1AE9A301408AF26032B445FBB08 | SHA256:3A8010F1E4E028782093877D969EB127B80AE48B7215A8D3F91E8AB9C165AC7A | |||
| 8 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb8.19873\manifest.json | text | |
MD5:0140EB2179F262FD5AB727B042327293 | SHA256:3D51E554709590462ADA81EE24A58B30552513137F248A3519A96113EC6534A7 | |||
| 8 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb8.19873\Device\HarddiskVolume2\Program Files (x86)\Microsoft Office\Updates\Download\PackageFiles\3B2768A5-B08D-431A-8AF7-A715BE2840AB\root\vfs\Windows\Installer\{90160000-001F-040C-0000-0000000FF1CE}\misc.exe | executable | |
MD5:5B08B3C105F7347F494DCDE0F01F925B | SHA256:1A910DF7C151057EEDEFFEF4706ACF70FA9C55D1390B11F25DDF933F83BCA4B0 | |||
| 6388 | misc.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileSyncHelper.exe | executable | |
MD5:1C0BE16E6ED8F5B6F0910650A25F4FA7 | SHA256:3028F6A6A7A10DC5D63F256FEEB8275F3818BF3371EAF8B20A2D0BF2FCD5F4A9 | |||
| 6388 | misc.exe | C:\ProgramData\Adobe\ARM\S\388\AdobeARMHelper.exe | executable | |
MD5:85A67D34298E33D2D5A9EC789B6AB594 | SHA256:1DEE143B4F88F2375B85C6271A58E2E78FED081BEAE4090678CB2DD7A37FB2D4 | |||
| 6388 | misc.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | executable | |
MD5:13C2D5BF03C4A2B28E930F990CCC32DB | SHA256:12D24D0BC0E7CDC902E3540A3C6F7B755094F011A8EAD49A47A00563710B8F80 | |||
| 6388 | misc.exe | C:\Users\admin\AppData\Local\Temp\3582-490\misc.exe | executable | |
MD5:95E34176109055679A086BAC9A245BA9 | SHA256:7843AF4338515FC79A6FFE7414320672A82FA4DFDFACB454C8009AAF9C3D53A4 | |||
| 6388 | misc.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\OneDriveUpdaterService.exe | executable | |
MD5:E73AC057B2CFEF016B8199389F0DF590 | SHA256:20ABA9D6001E5CDC287CD5BD452D0F2D05980D83F851D2B309BF49E9D9A8AC4C | |||
| 6388 | misc.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\OneDriveStandaloneUpdater.exe | executable | |
MD5:A747FA4161FE3C00C3FBB4BF391D4D4E | SHA256:B7BA59428AF7AE08C5BF927B57E326D5259E6ED31BD4237AA6A44378177364C1 | |||
| 6388 | misc.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\OneDrive.exe | executable | |
MD5:178B773B3FB050FCE26E40A9E8C2EE9A | SHA256:1E03573733F25B44004049A535E7E79366FD86FE953F6DFEDAAD05513B46A6C5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
30
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7988 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7988 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
688 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
7596 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
8020 | backgroundTaskHost.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1260 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6016 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6016 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6016 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5948 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5224 | SearchApp.exe | 2.18.29.176:443 | www.bing.com | Akamai International B.V. | PL | whitelisted |
7988 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7988 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |