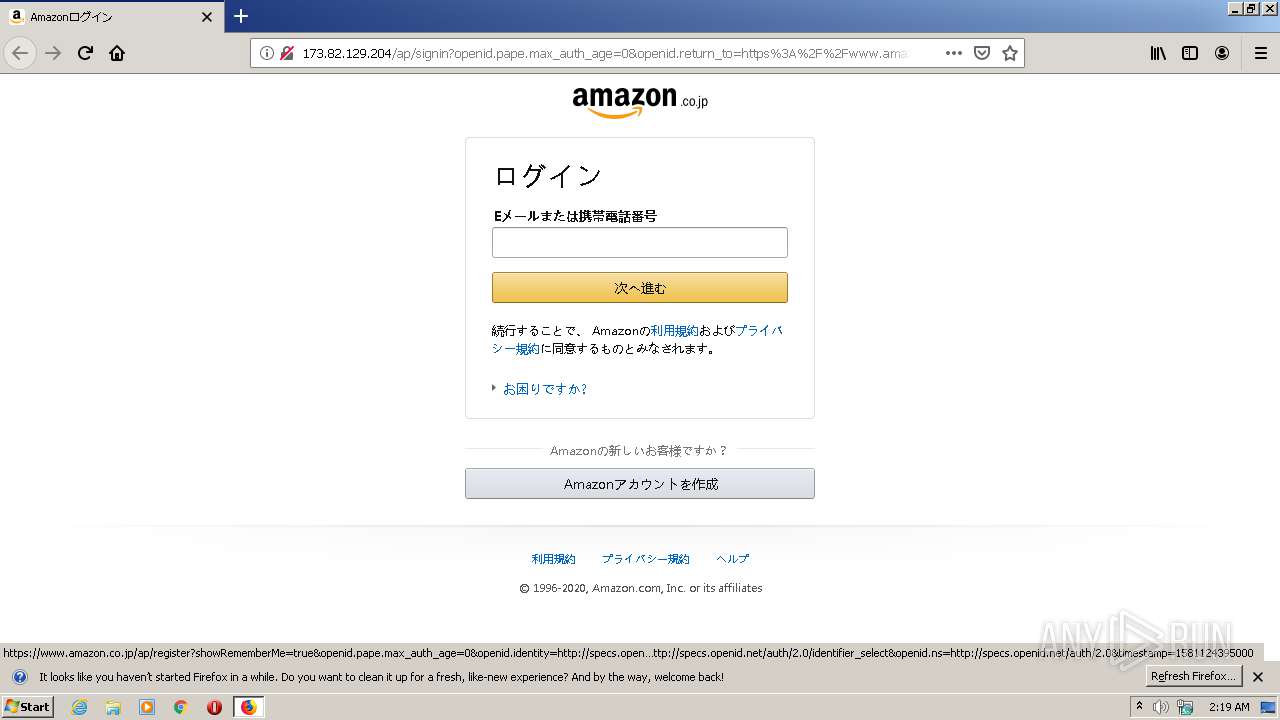
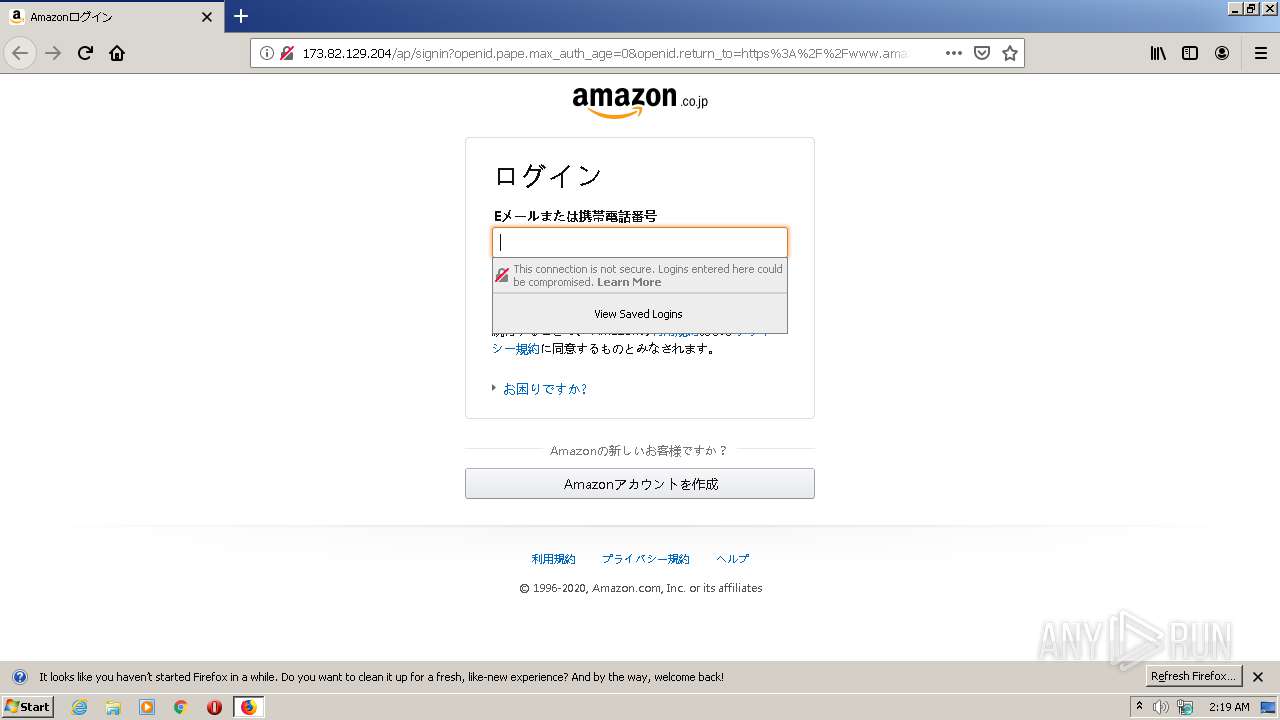
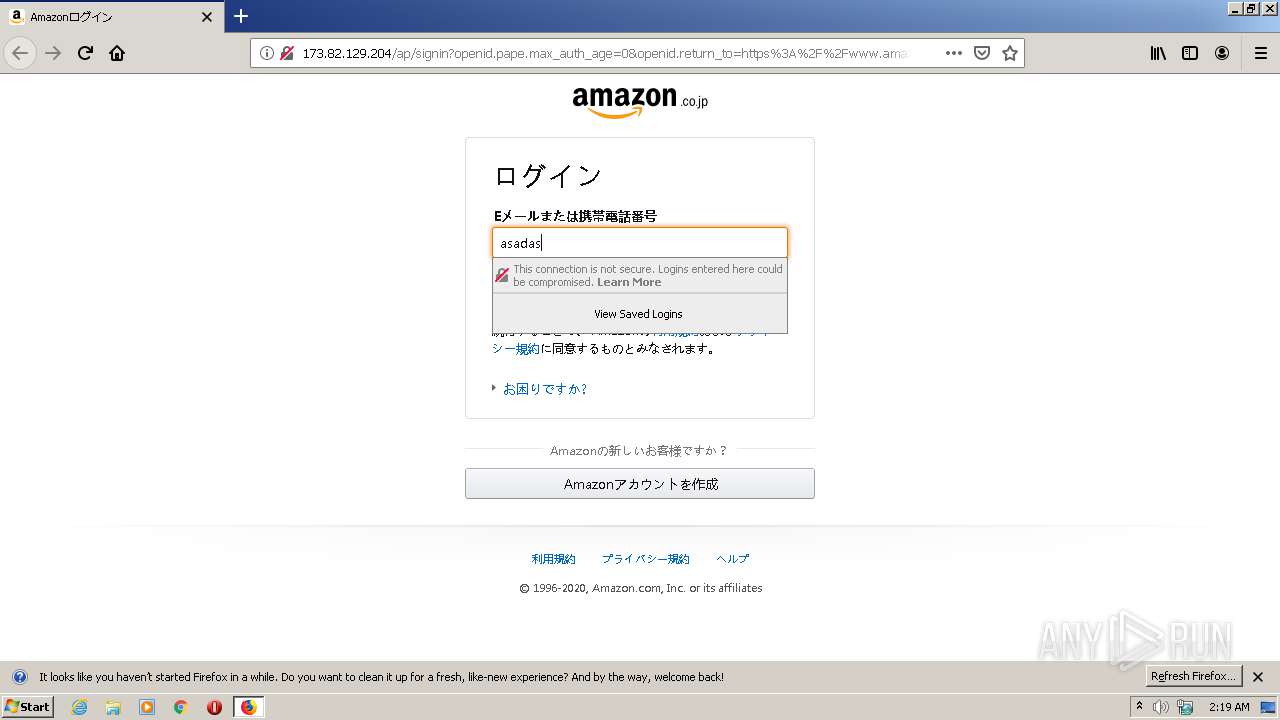
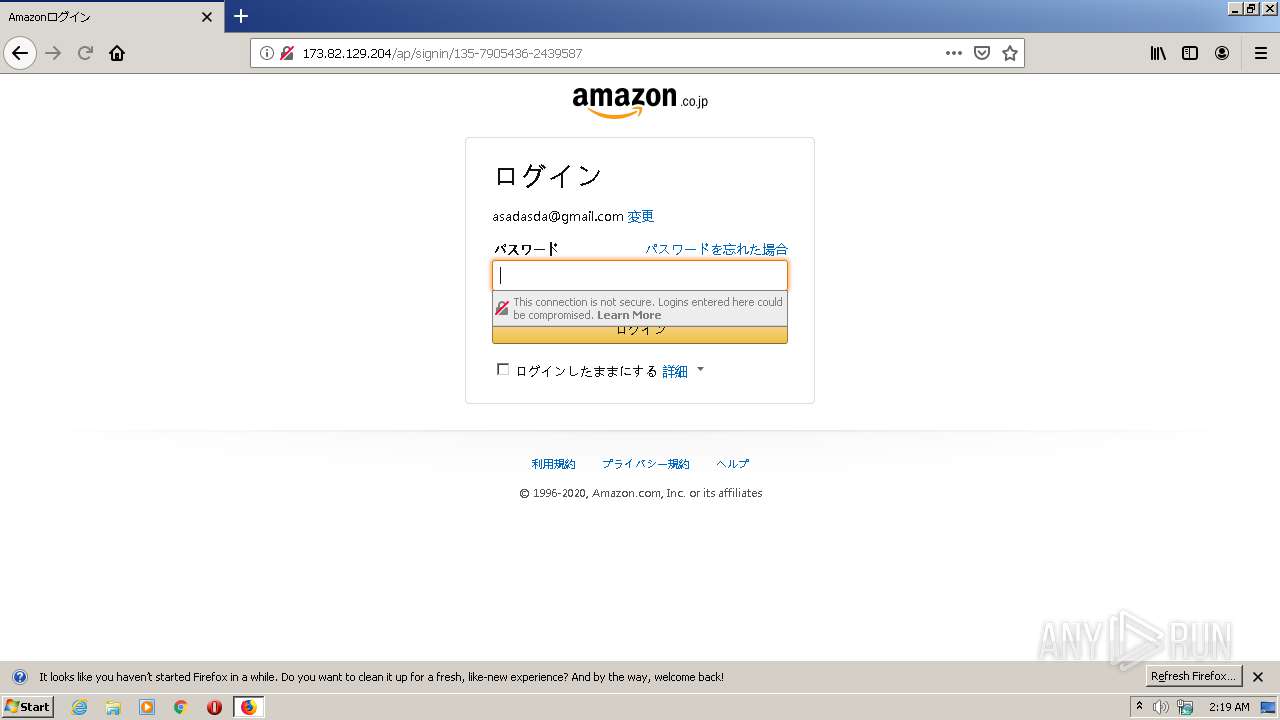
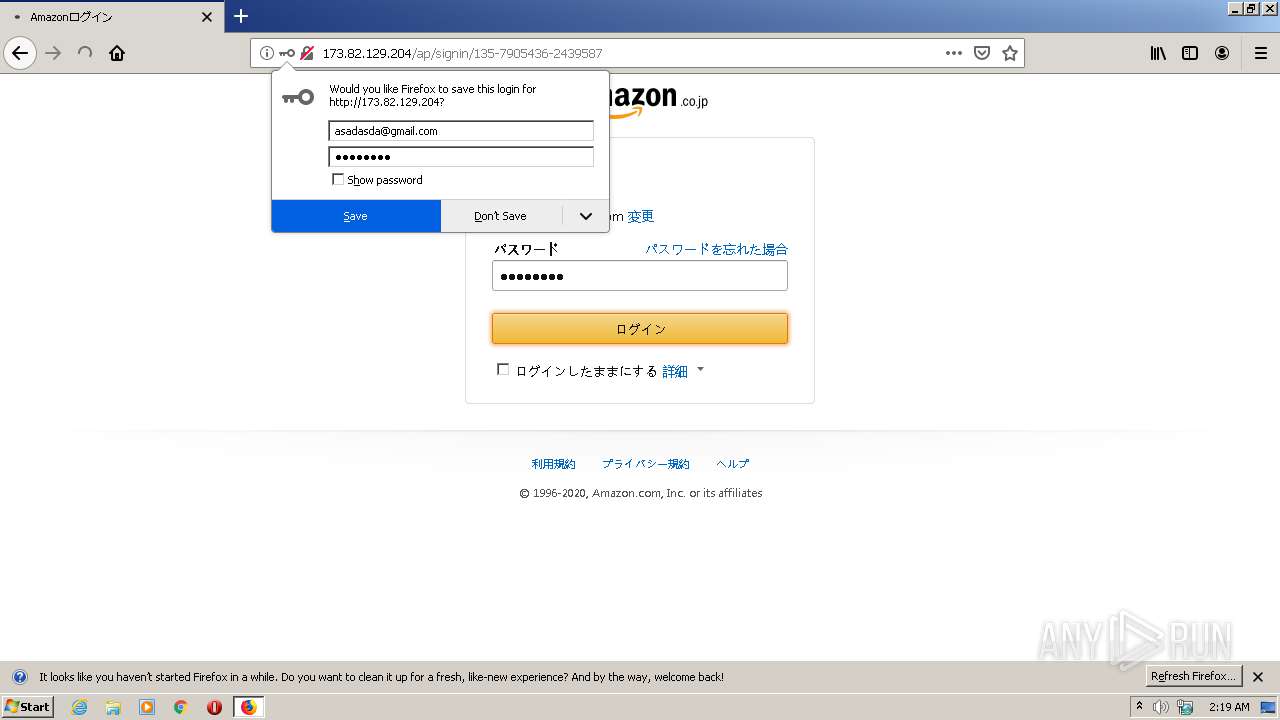
| URL: | http://173.82.129.204/ap/signin?openid.pape.max_auth_age=0&openid.return_to=https%3A%2F%2Fwww.amazon.co.jp%2F%3Fref_%3Dnav_em_hd_re_signin&openid.identity=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.assoc_handle=jpflex&openid.mode=checkid_setup&key=a@b.c&openid.claimed_id=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.ns=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0&&ref_=nav_em_hd_clc_signin |
| Full analysis: | https://app.any.run/tasks/51b84e8f-35ac-4e46-90b6-a800ee714630 |
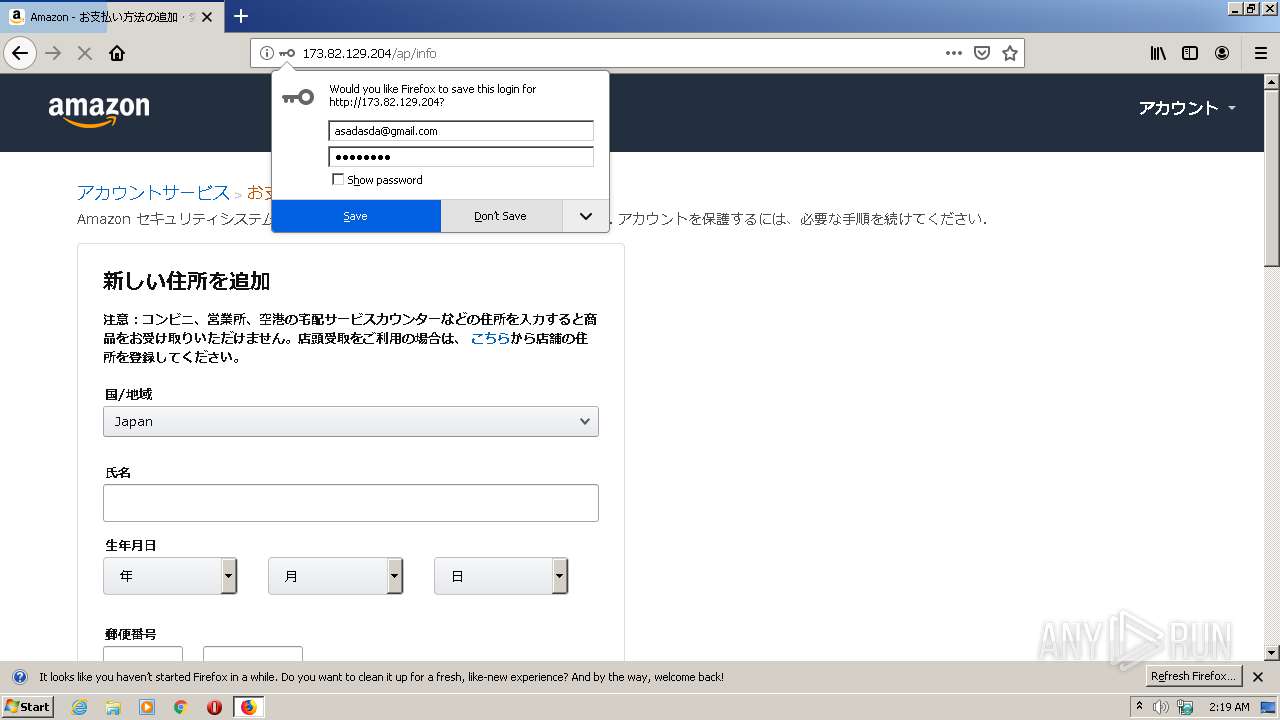
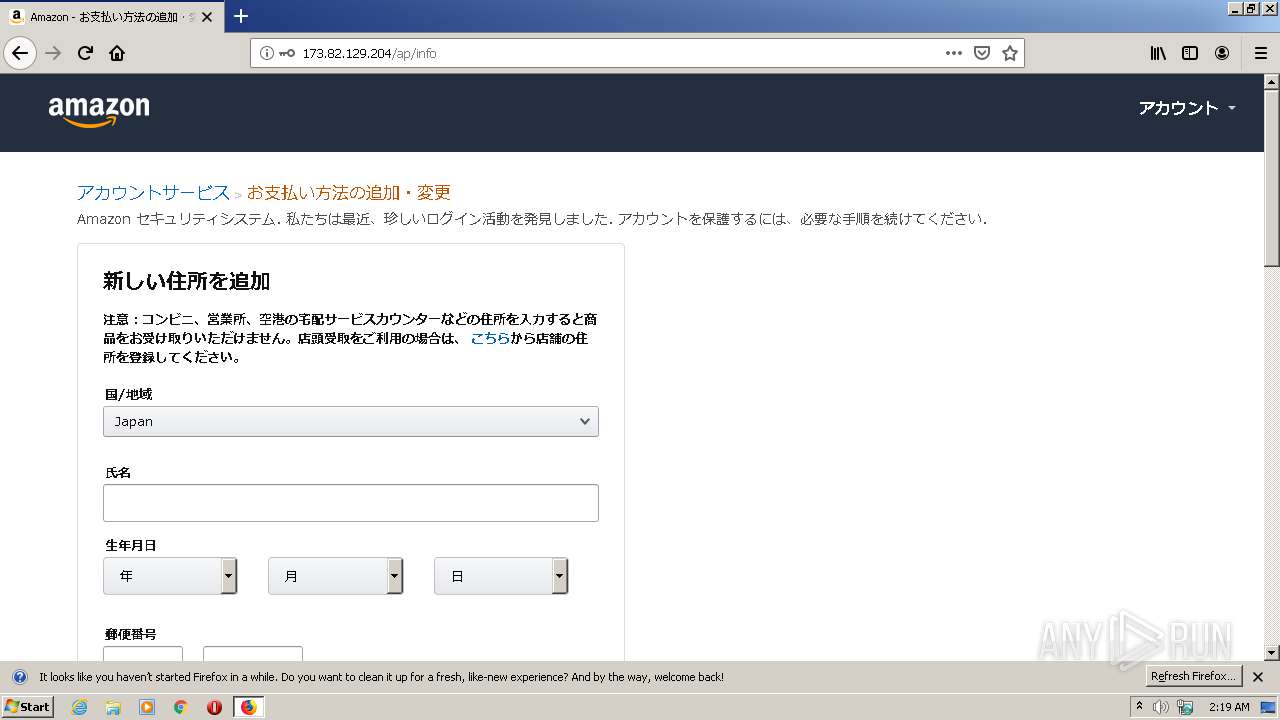
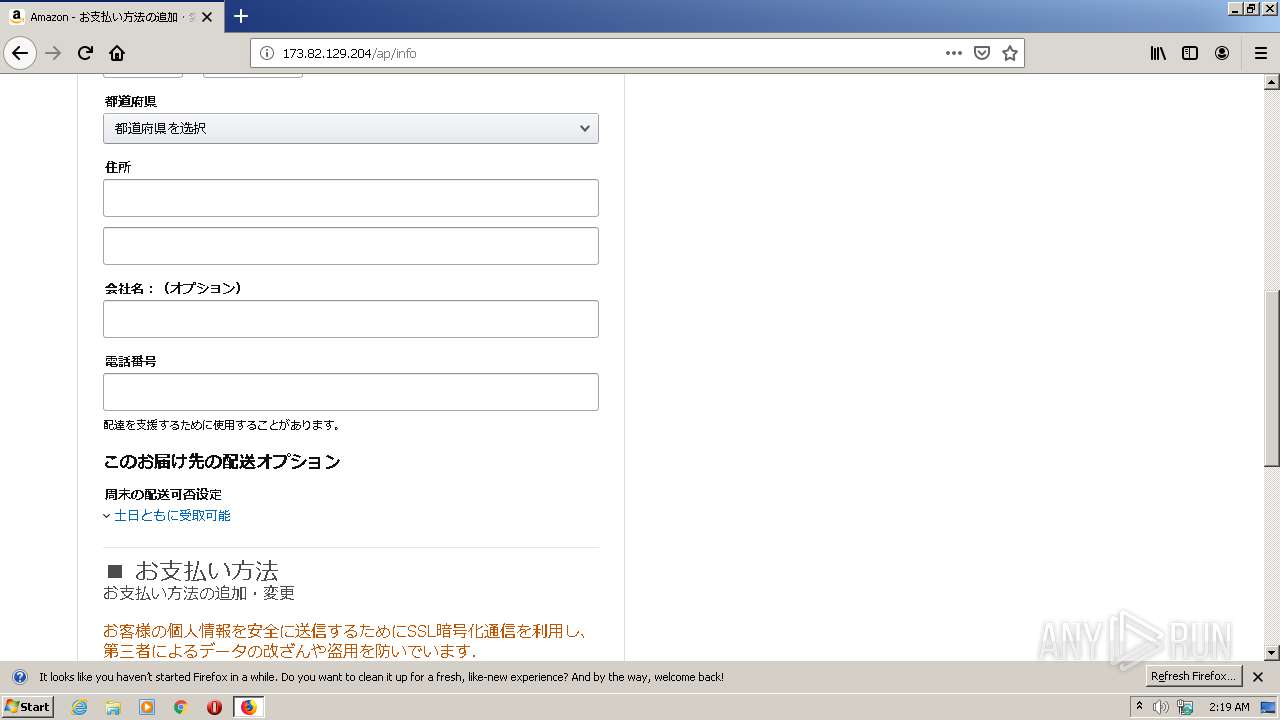
| Verdict: | Malicious activity |
| Analysis date: | November 27, 2020, 02:19:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 514B8A43F42FFECA51E8E31DB037A484 |
| SHA1: | 7ACB7B4B91E8E854A5D1B849B069C94FAC8C0005 |
| SHA256: | 943DD557857365BEAFC2873CFD3BE661F01EEF0B2BA81314F41D2F69F1B5BD1F |
| SSDEEP: | 12:ZW4nt3Oc8Q2LKS4HsQupmokihAtUs3QxysQupmokihAtUVdsQupmokihoOW6n:o4tr8Q5SU6oilsP6oilD6oiqUn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops a file with a compile date too recent
- firefox.exe (PID: 3320)
INFO
Application launched itself
- firefox.exe (PID: 3320)
- firefox.exe (PID: 3604)
Reads the computer name
- firefox.exe (PID: 3320)
- firefox.exe (PID: 3248)
- firefox.exe (PID: 2540)
- firefox.exe (PID: 3996)
- firefox.exe (PID: 2960)
Reads CPU info
- firefox.exe (PID: 3320)
Checks supported languages
- firefox.exe (PID: 3320)
- firefox.exe (PID: 3248)
- firefox.exe (PID: 3996)
- firefox.exe (PID: 2960)
Creates files in the user directory
- firefox.exe (PID: 3320)
Creates files in the program directory
- firefox.exe (PID: 3320)
Reads the date of Windows installation
- firefox.exe (PID: 3320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2540 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3320.0.226564742\1661217146" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3320 "\\.\pipe\gecko-crash-server-pipe.3320" 1152 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3320.20.1442094340\1786965704" -childID 3 -isForBrowser -prefsHandle 3648 -prefMapHandle 3660 -prefsLen 6718 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3320 "\\.\pipe\gecko-crash-server-pipe.3320" 3672 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3248 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3320.3.1558401152\785905379" -childID 1 -isForBrowser -prefsHandle 1716 -prefMapHandle 1712 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3320 "\\.\pipe\gecko-crash-server-pipe.3320" 1736 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3320 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://173.82.129.204/ap/signin?openid.pape.max_auth_age=0&openid.return_to=https%3A%2F%2Fwww.amazon.co.jp%2F%3Fref_%3Dnav_em_hd_re_signin&openid.identity=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.assoc_handle=jpflex&openid.mode=checkid_setup&key=a@b.c&openid.claimed_id=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.ns=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0&&ref_=nav_em_hd_clc_signin | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3604 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://173.82.129.204/ap/signin?openid.pape.max_auth_age=0&openid.return_to=https%3A%2F%2Fwww.amazon.co.jp%2F%3Fref_%3Dnav_em_hd_re_signin&openid.identity=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.assoc_handle=jpflex&openid.mode=checkid_setup&key=a@b.c&openid.claimed_id=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.ns=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0&&ref_=nav_em_hd_clc_signin" | C:\Program Files\Mozilla Firefox\firefox.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3996 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3320.13.872561746\2046136149" -childID 2 -isForBrowser -prefsHandle 2780 -prefMapHandle 2864 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3320 "\\.\pipe\gecko-crash-server-pipe.3320" 2920 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
6 135
Read events
6 130
Write events
5
Delete events
0
Modification events
| (PID) Process: | (3604) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: E7E6A30300000000 | |||
| (PID) Process: | (3320) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: EDE6A30300000000 | |||
| (PID) Process: | (3320) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3320) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A7000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3320) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
0
Suspicious files
178
Text files
41
Unknown types
58
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3320 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache.bin | — | |
MD5:— | SHA256:— | |||
| 3320 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache.bin | binary | |
MD5:DE9496ACA551ADE408EF6466A11833A1 | SHA256:8F9C7FDB3E0BC01024E43A8E242468FC4DD4F74C725E32A883571635203DC10A | |||
| 3320 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:C9CC83C01997C04445EFB26226E60ADC | SHA256:893EAE9F01E2540FD286A16385CF02CCF379318737C0567A4475A90C67E0A7E8 | |||
| 3320 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child.bin | binary | |
MD5:5027177F513CDAE07DB2330E1DED5934 | SHA256:0C53F16051E738287A4612F68E296238087627E594CFD6DDFA1FECC2E998328B | |||
| 3320 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-wal | sqlite-wal | |
MD5:F5DB9BDB1049F5A5D4AA5B66D65BC367 | SHA256:5F60DAF7EF8381947D199491BDA50F4C3B3731461A1614F0C4F0D032113540C2 | |||
| 3320 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\5EAB7360F6E662B871F8238FB97975A1F6A5E273 | compressed | |
MD5:01FB76375C3DF7DC6C341C67D525769C | SHA256:1669A0B9C7A94D5F7FCCF403911997ECE1985316C496C8267483B0355C8060AA | |||
| 3320 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | jsonlz4 | |
MD5:6D378E0D40B6EACA22C8BCE899A1C5C1 | SHA256:ADA2467B2477ACEFF837AC7820C435AD1EBBE844B2DA31C7AB9AE8D010C7A639 | |||
| 3320 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\08905C7337ECEA09737699287DCD512722FB05B9 | compressed | |
MD5:39600FD75058C243FA8C7B5FBA0FFDEC | SHA256:09AA25741EFEB68B628F7D42915C0BE4A824C9E143CBFDBAB64F47242D38EB80 | |||
| 3320 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:4A1220FC03E11726F09E9981834345DB | SHA256:6AE7FC0FDBE217104F4034BF6A580A461106B50309ABCCFF6E309124DCA5EF39 | |||
| 3320 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\29169603C7FE35DCC7C2ED49AA013283F3DD9161 | compressed | |
MD5:2E2E809CF9B15E3BC1C5C5CCA9D515BB | SHA256:6ADEFF5A0415ECD31A038BE26E1BF36BA61124C5131602C638FC1A61A3AC0C49 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
72
TCP/UDP connections
36
DNS requests
87
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3320 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
3320 | firefox.exe | GET | 200 | 173.82.129.204:80 | http://173.82.129.204/ap/signin?openid.pape.max_auth_age=0&openid.return_to=https%3A%2F%2Fwww.amazon.co.jp%2F%3Fref_%3Dnav_em_hd_re_signin&openid.identity=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.assoc_handle=jpflex&openid.mode=checkid_setup&key=a@b.c&openid.claimed_id=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.ns=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0&&ref_=nav_em_hd_clc_signin | US | html | 35.1 Kb | suspicious |
3320 | firefox.exe | GET | 200 | 173.82.129.204:80 | http://173.82.129.204/ap/uedata?ld&v=0.207204.0&id=8HSX8GW2CMQHB2HJV2G6&sw=1280&sh=720&vw=1280&vh=587&m=1&sc=8HSX8GW2CMQHB2HJV2G6&ue=0&bb=436&cf=436&be=436&pc=796&tc=-507&na_=-507&ul_=-1606443578990&_ul=-1606443578990&rd_=-1606443578990&_rd=-1606443578990&fe_=-507&lk_=-413&_lk=-413&co_=-413&_co=-398&sc_=-1606443578990&rq_=-398&rs_=-101&_rs=-101&dl_=-38&di_=462&de_=587&_de=587&_dc=774&ld_=774&_ld=-1606443578990&ntd=10&ty=0&rc=0&hob=0&hoe=0&ld=796&t=1606443579786&ctb=1&rt=cf:3-0-3-0-1-0-0__ld:8-5-3-0-1-0-0&csmtags=aui|aui:aui_build_date:3.19.8-2020-01-19|www-amazon-co-jp-2sc54kya23e65bcefd2kynmpjecdb2b5-com&viz=visible:0&pty=AuthenticationPortal&spty=SignInClaimCollect&pti=undefined&tid=8HSX8GW2CMQHB2HJV2G6&aftb=1 | US | compressed | 2.42 Kb | suspicious |
3320 | firefox.exe | GET | 200 | 173.82.129.204:80 | http://173.82.129.204/ap/uedata?at&v=0.207204.0&id=8HSX8GW2CMQHB2HJV2G6&m=1&sc=adblk_no&pc=1320&at=1320&t=1606443580310&csmtags=adblk_no&pty=AuthenticationPortal&spty=SignInClaimCollect&pti=undefined&tid=8HSX8GW2CMQHB2HJV2G6&aftb=1 | US | compressed | 2.42 Kb | suspicious |
3320 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3320 | firefox.exe | GET | 200 | 173.82.129.204:80 | http://173.82.129.204/ap/uedata?at&v=0.207204.0&id=8HSX8GW2CMQHB2HJV2G6&ctb=1&m=1&sc=8HSX8GW2CMQHB2HJV2G6&pc=1368&at=1368&t=1606443580358&pty=AuthenticationPortal&spty=SignInClaimCollect&pti=undefined&tid=8HSX8GW2CMQHB2HJV2G6&aftb=1&ui=2 | US | compressed | 35.1 Kb | suspicious |
3320 | firefox.exe | POST | 302 | 173.82.129.204:80 | http://173.82.129.204/ap/signin?openid.pape.max_auth_age=0&openid.return_to=https%3A%2F%2Fwww.amazon.co.jp%2F%3Fref_%3Dnav_em_hd_re_signin&openid.identity=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.assoc_handle=jpflex&openid.mode=checkid_setup&key=a@b.c&openid.claimed_id=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.ns=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0&&ref_=nav_em_hd_clc_signin | US | html | 267 b | suspicious |
3320 | firefox.exe | GET | 200 | 173.82.129.204:80 | http://173.82.129.204/ap/uedata?ld&v=0.207204.0&id=BX2YNWXH6WZ5GBNEG08W&sw=1280&sh=720&vw=1280&vh=587&m=1&sc=BX2YNWXH6WZ5GBNEG08W&ue=0&bb=65&cf=65&be=65&pc=163&tc=-346&na_=-346&ul_=13&_ul=13&rd_=-346&_rd=-159&fe_=-159&lk_=-159&_lk=-159&co_=-159&_co=-159&sc_=-1606443587394&rq_=-159&rs_=13&_rs=13&dl_=13&di_=75&de_=122&_de=122&_dc=185&ld_=185&_ld=-1606443587394&ntd=22&ty=0&rc=1&hob=0&hoe=0&ld=163&t=1606443587557&ctb=1&rt=cf:8-5-3-0-1-8-1__ld:8-5-3-0-1-8-0&csmtags=aui|aui:aui_build_date:3.19.8-2020-01-19|www-amazon-co-jp-2sc54kya23e65bcefd2kynmpjecdb2b5-com|adblk_no|csm-feature-touch-enabled:false&viz=visible:0&pty=AuthenticationPortal&spty=SignInPwdCollect&pti=undefined&tid=8HSX8GW2CMQHB2HJV2G6&aftb=1 | US | html | 232 b | suspicious |
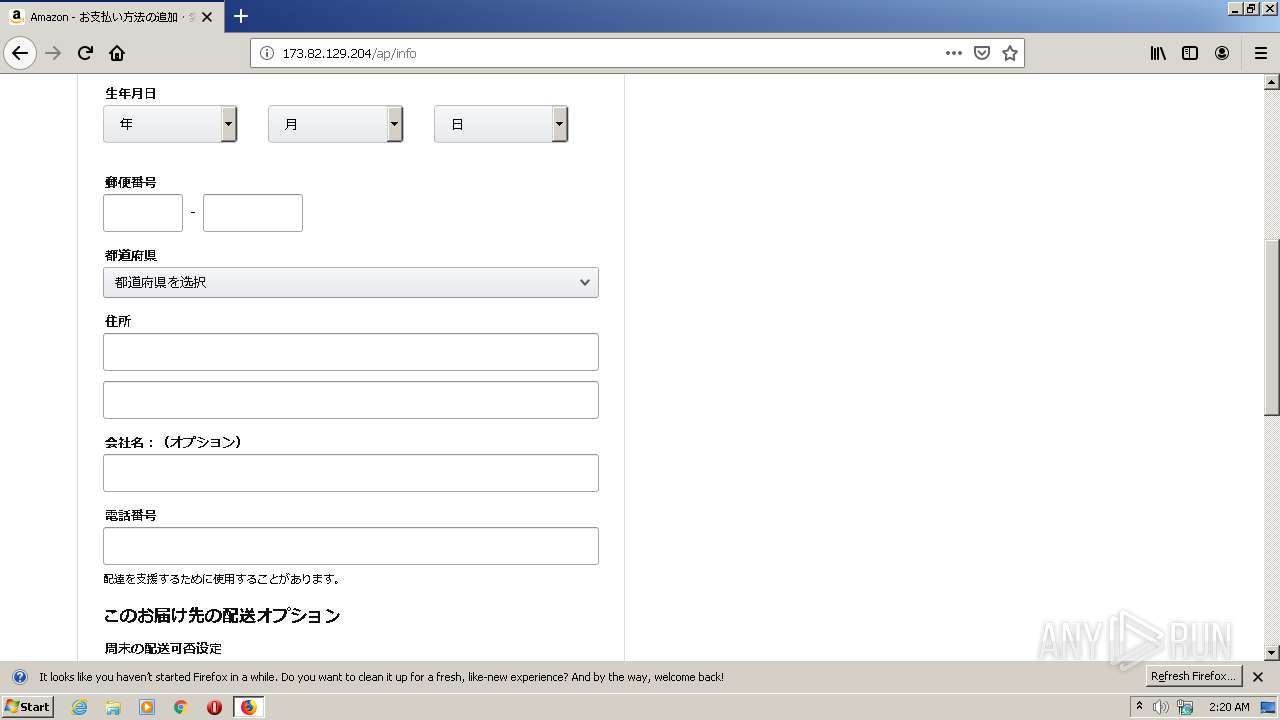
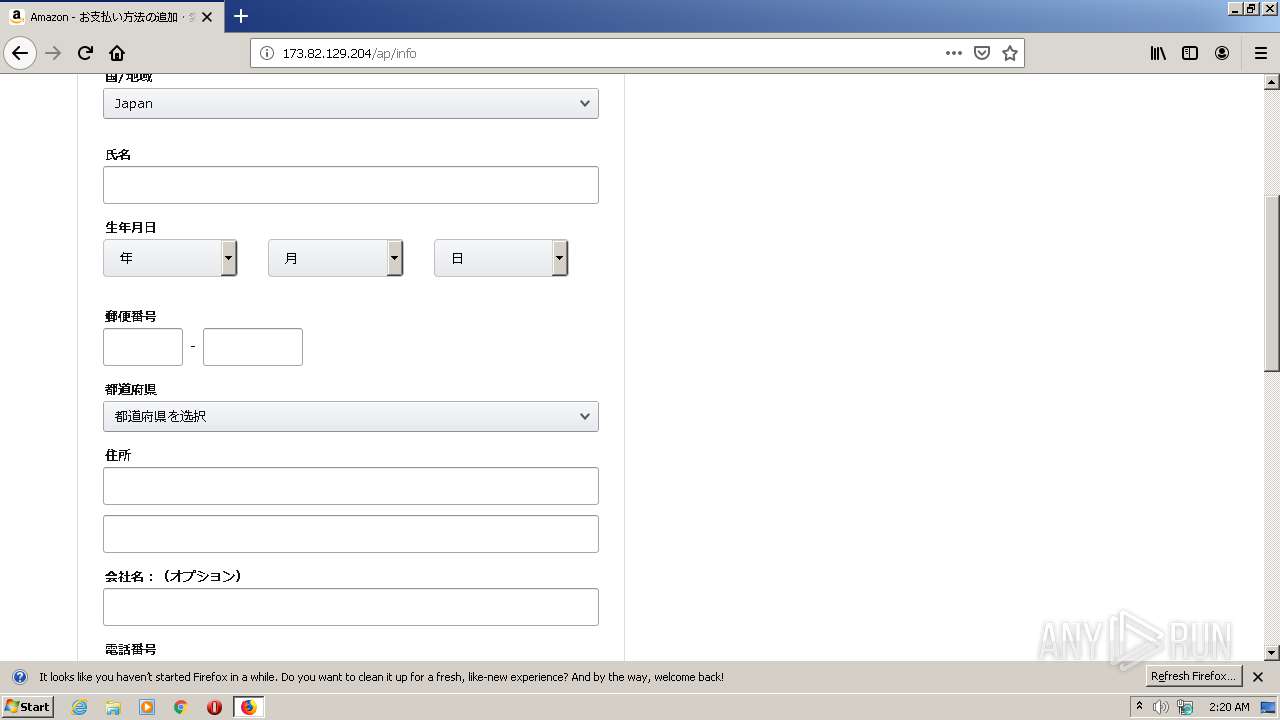
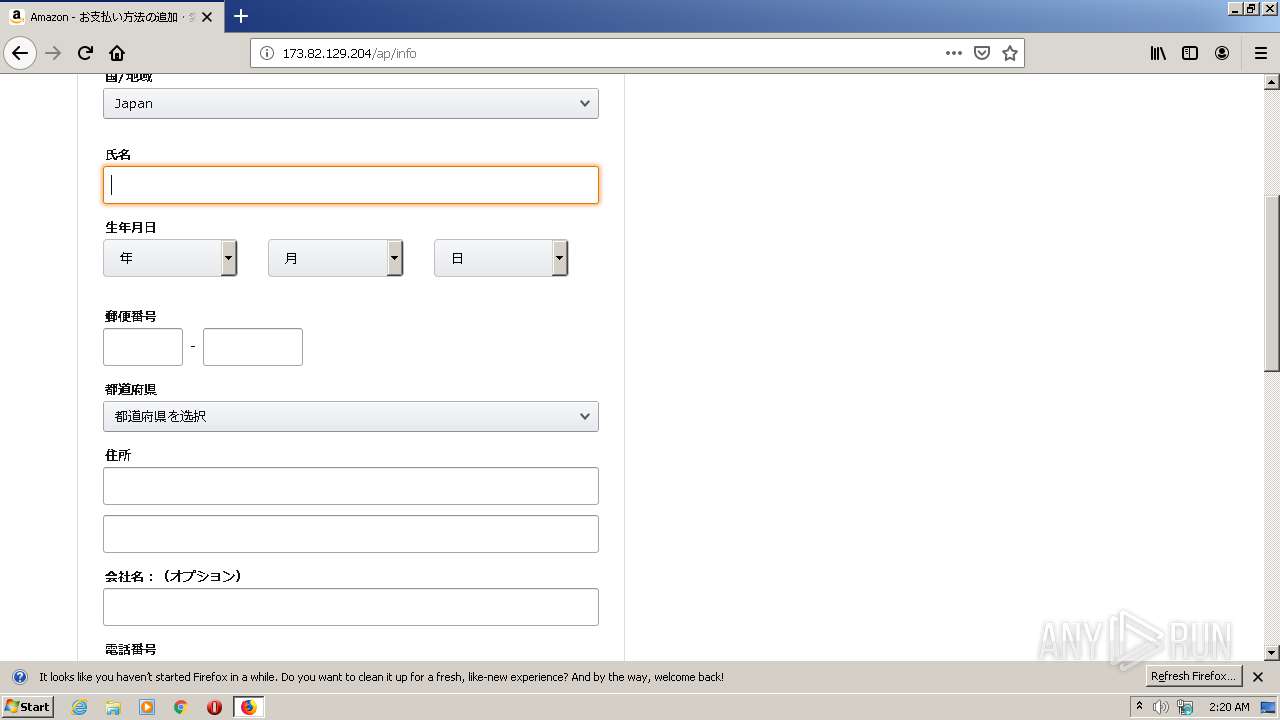
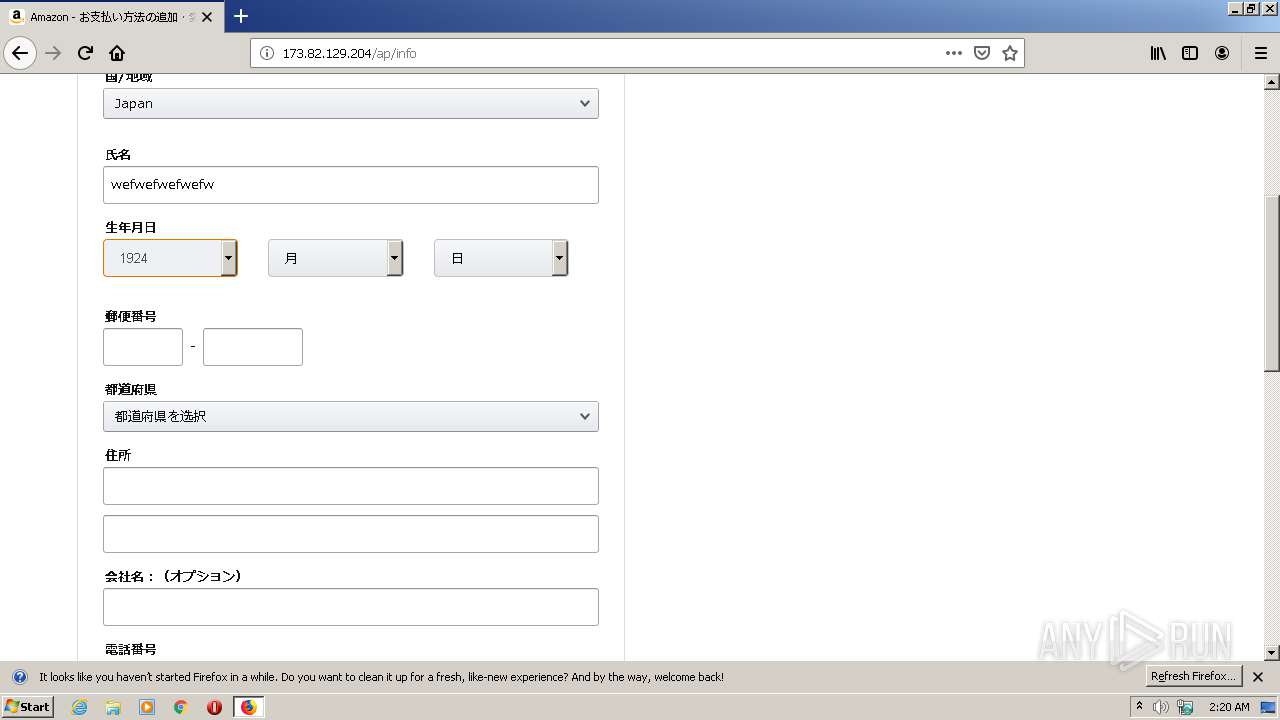
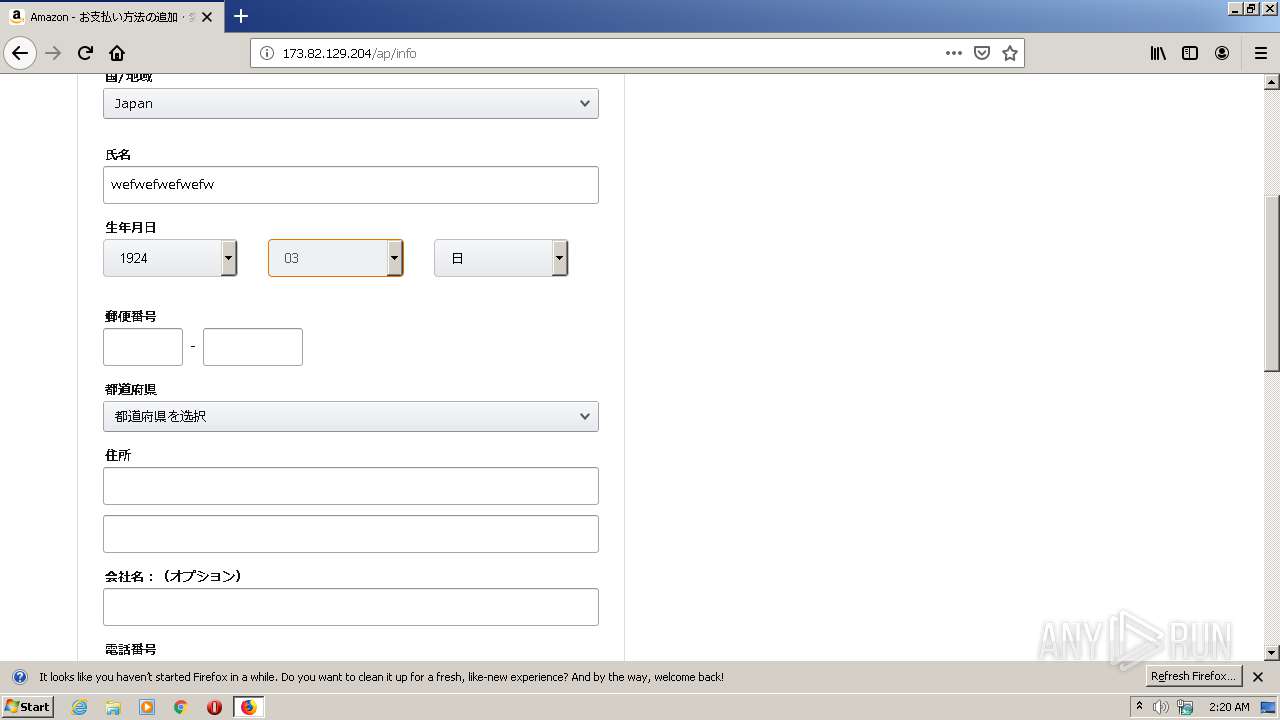
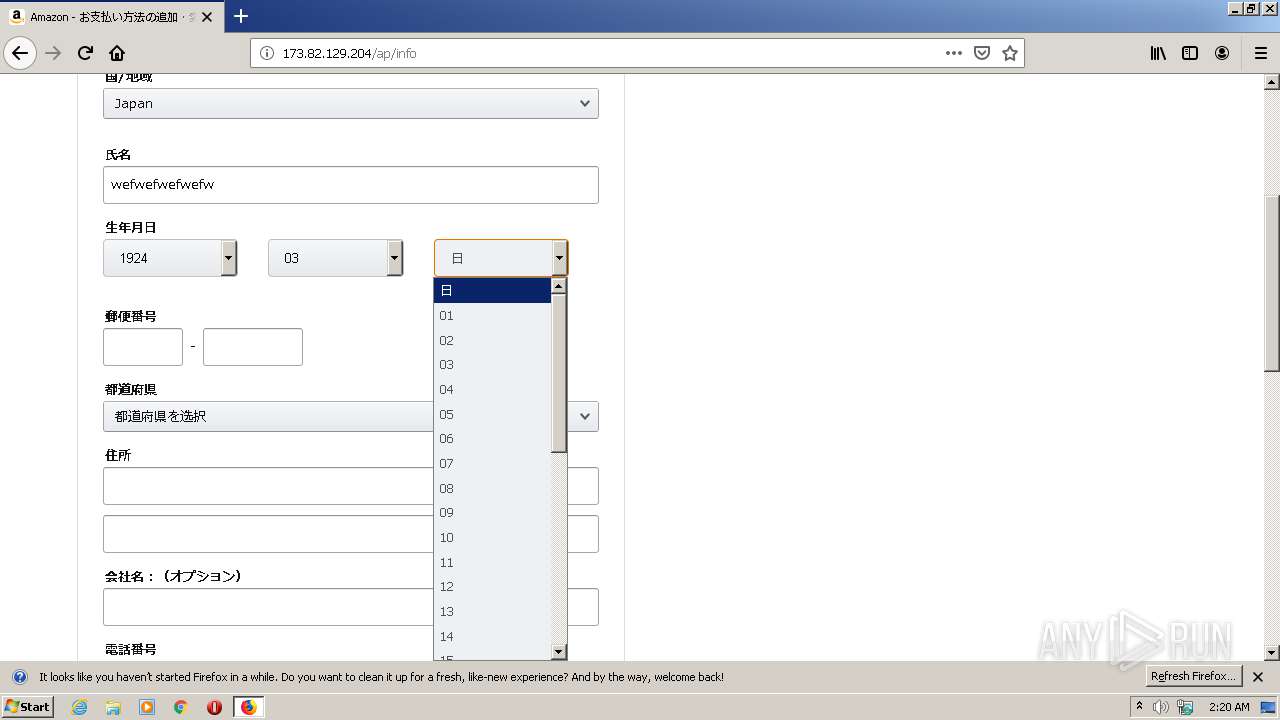
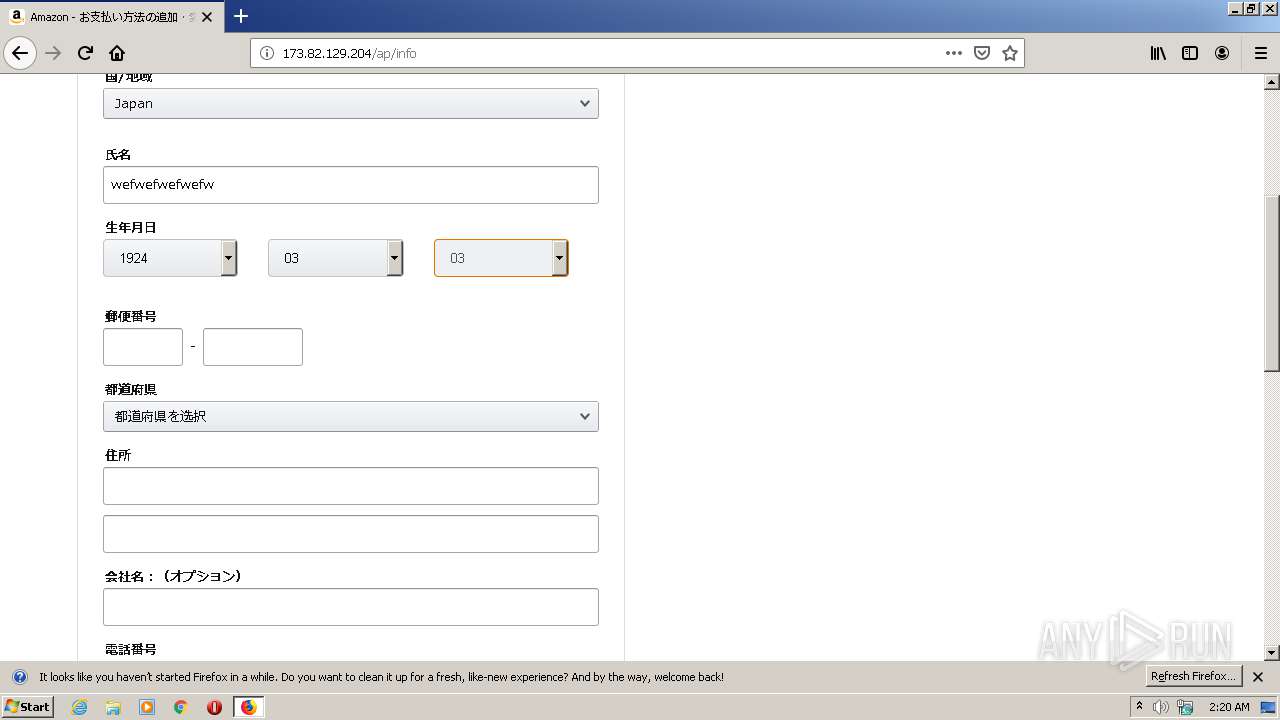
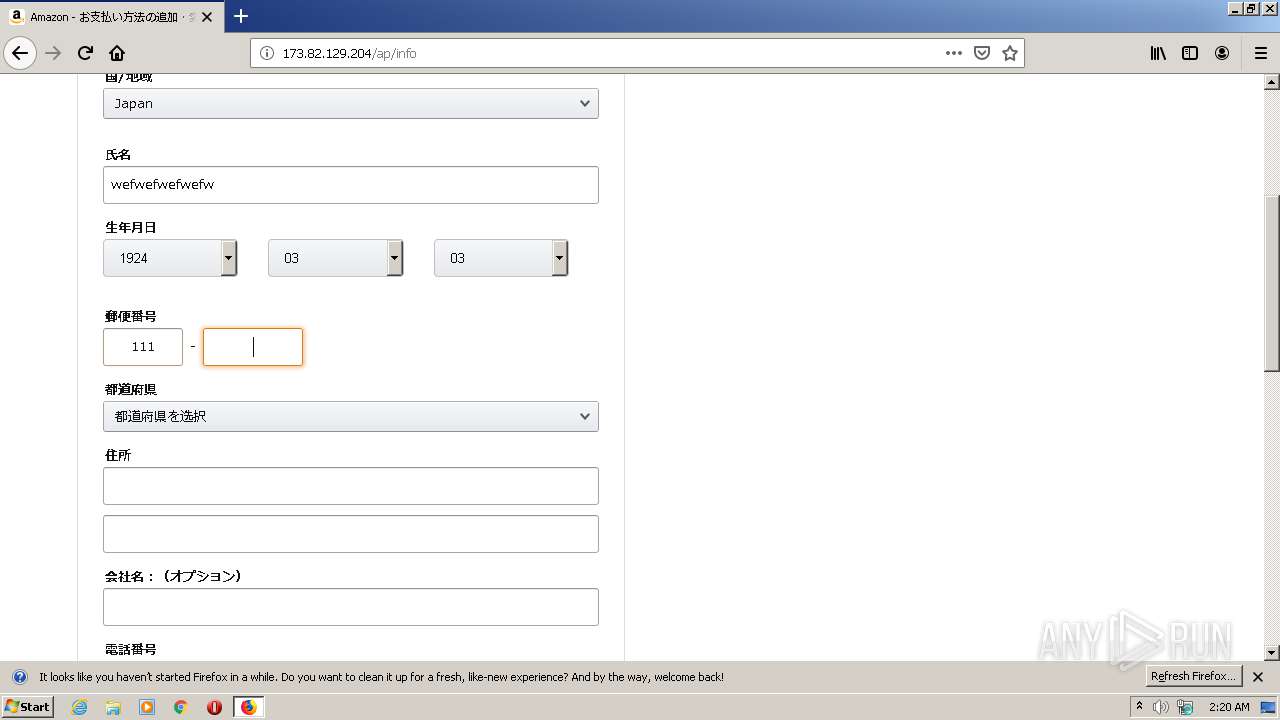
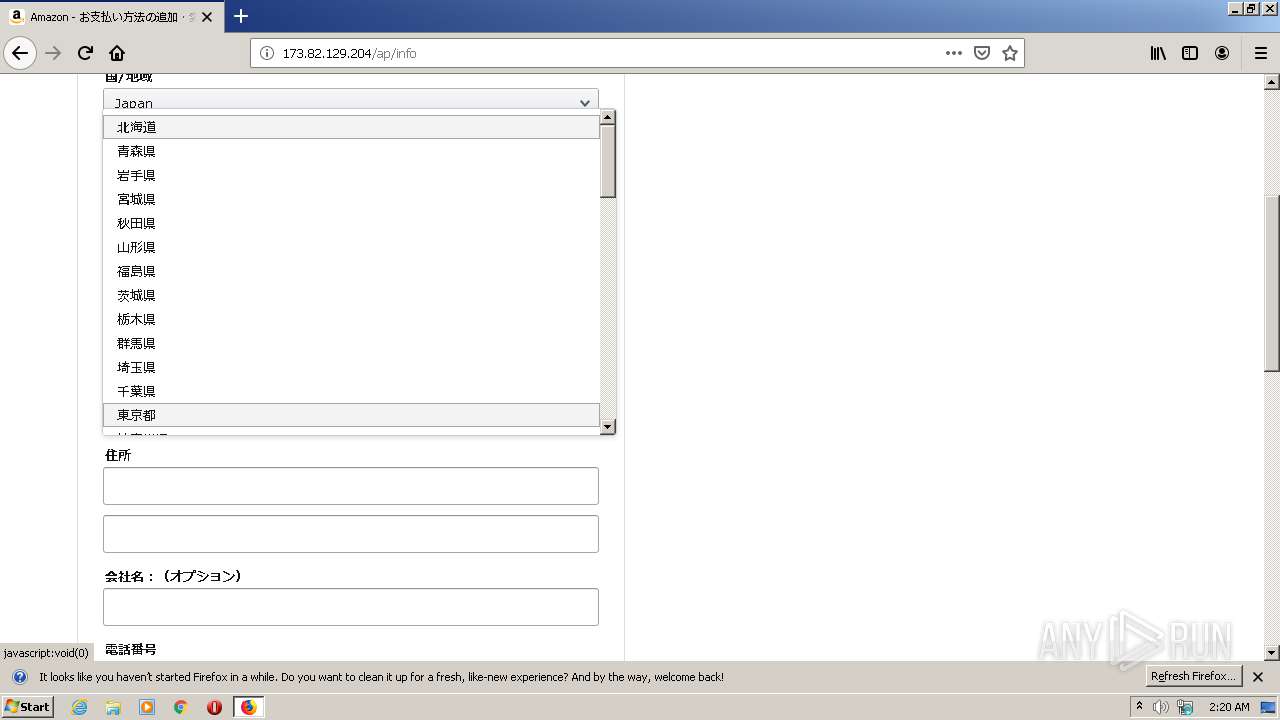
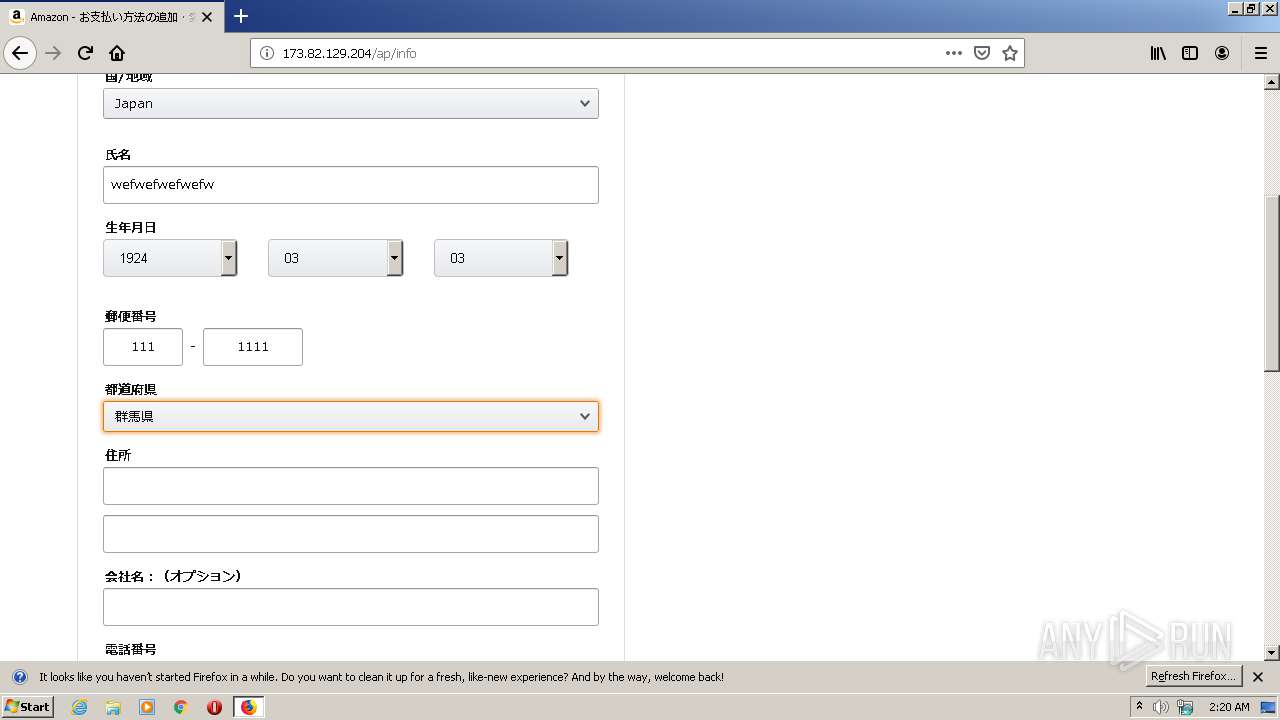
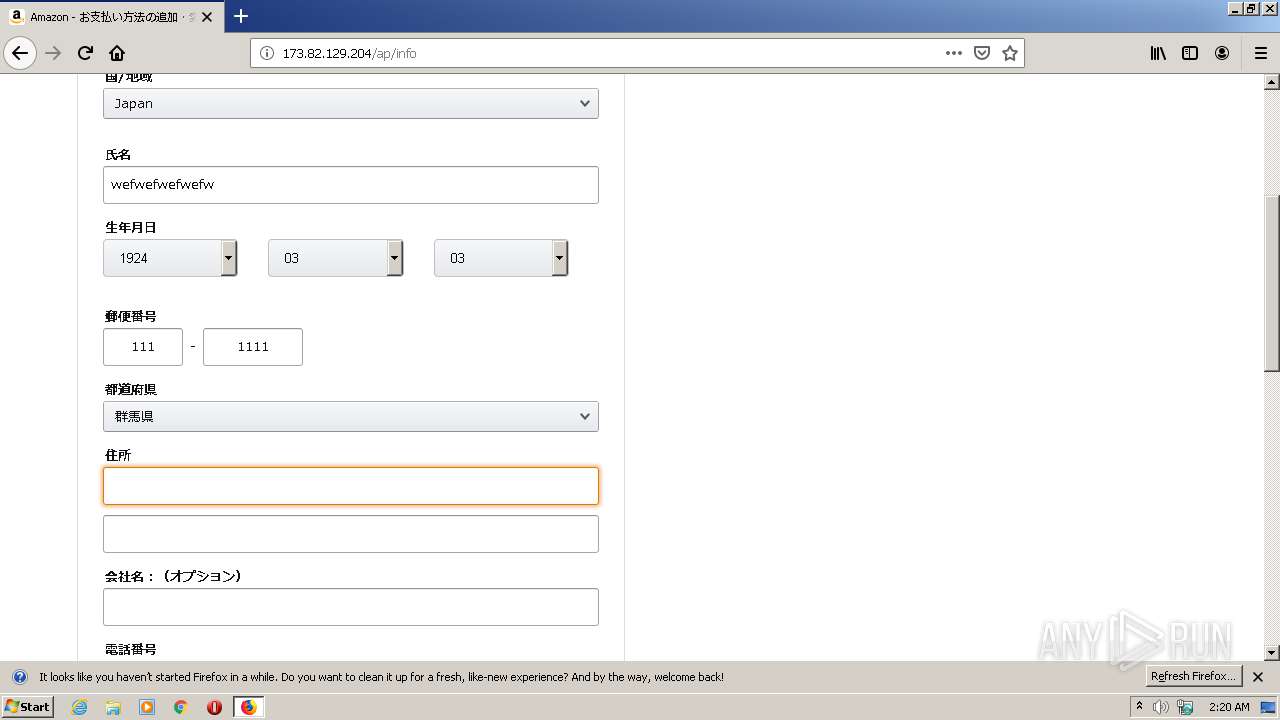
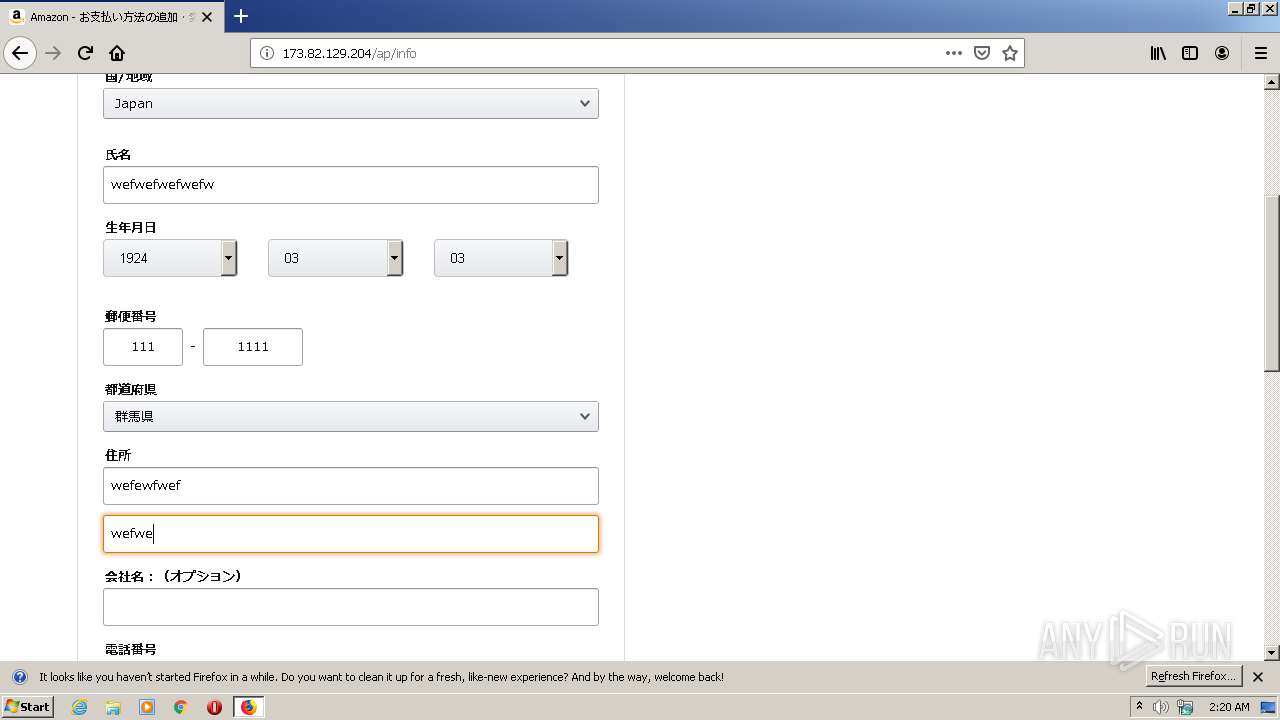
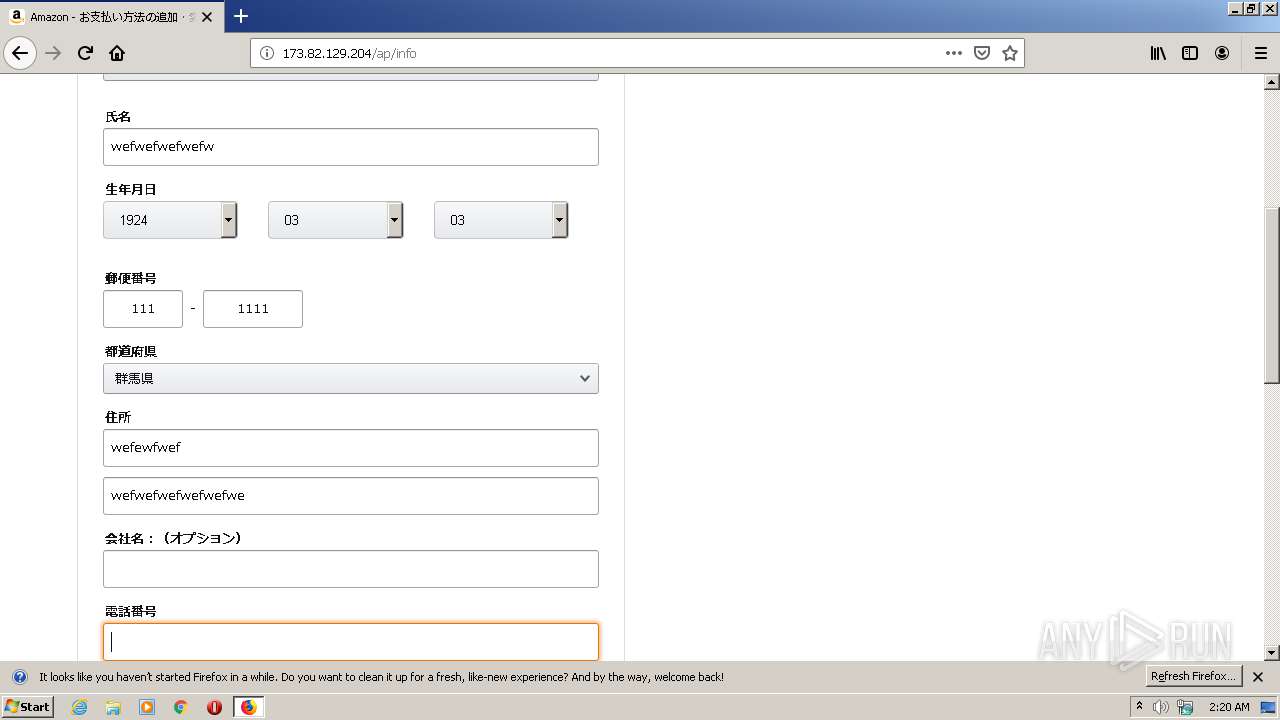
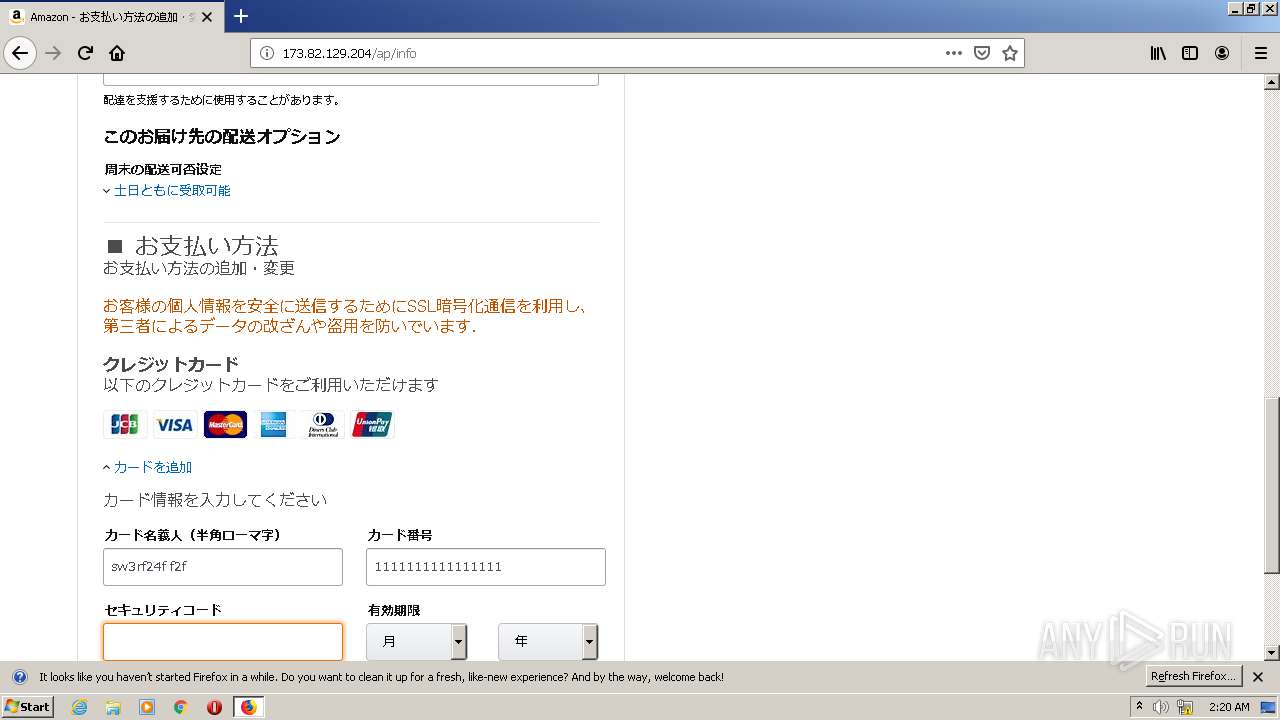
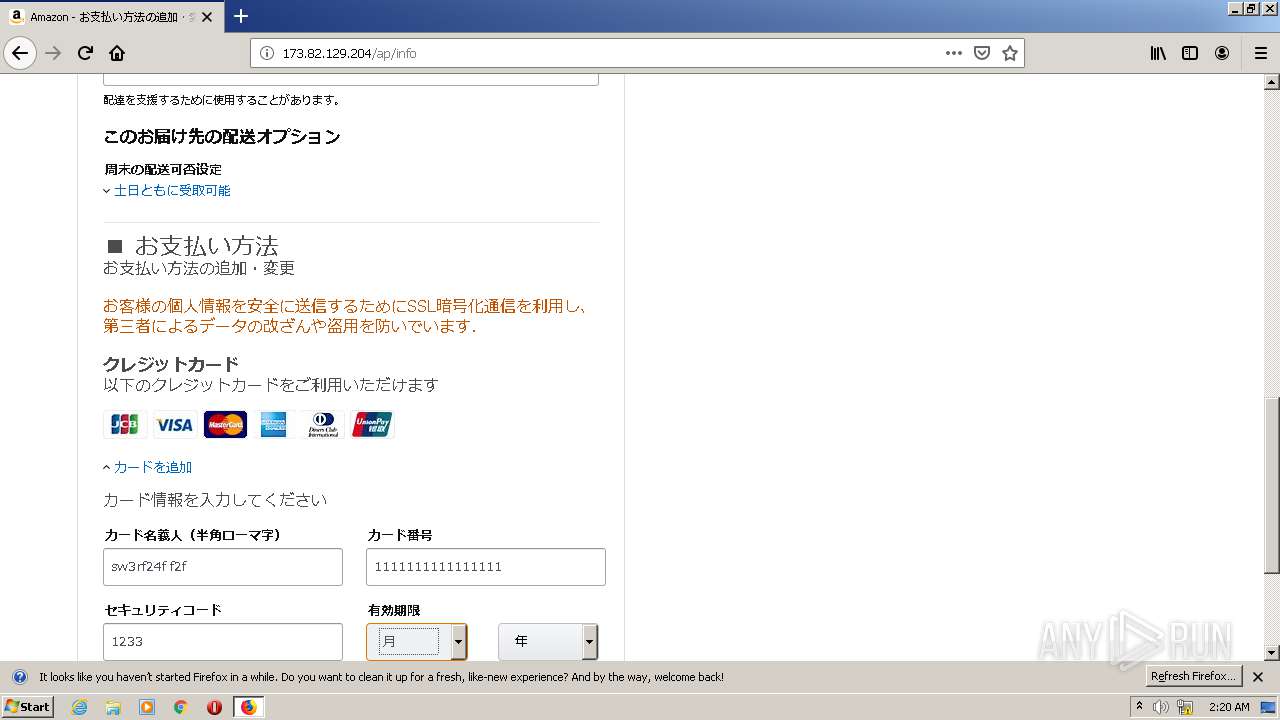
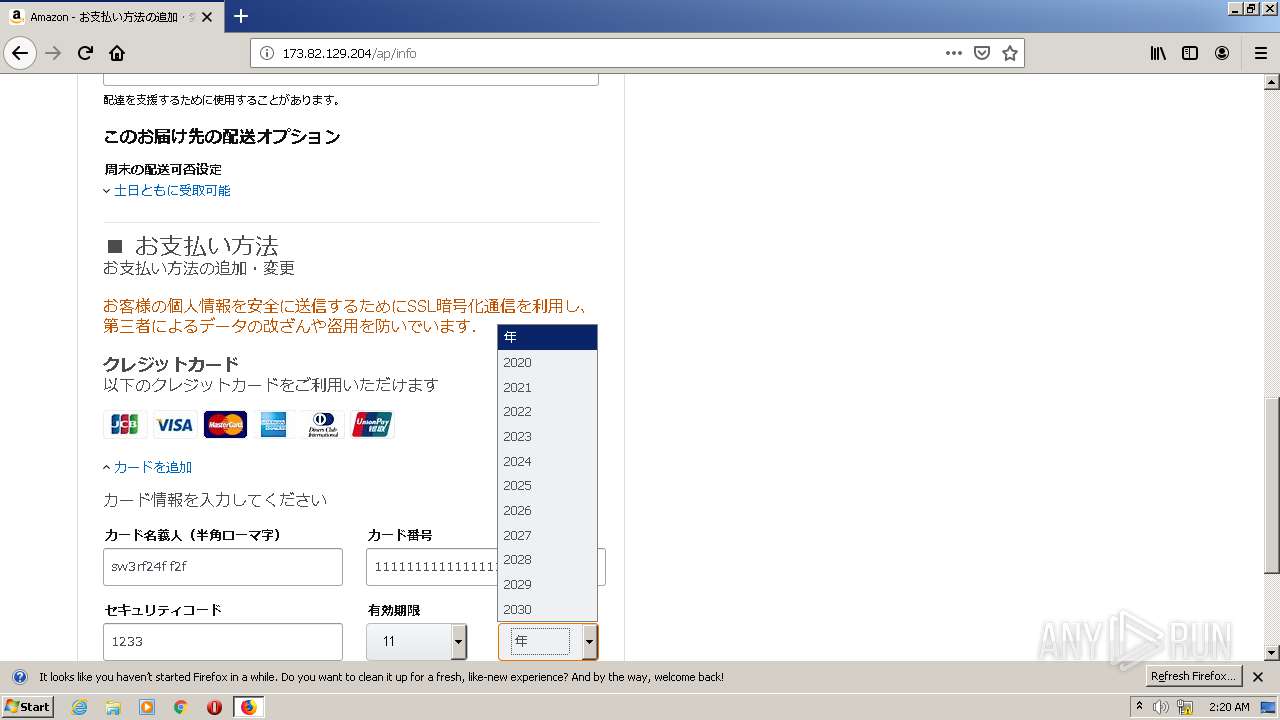
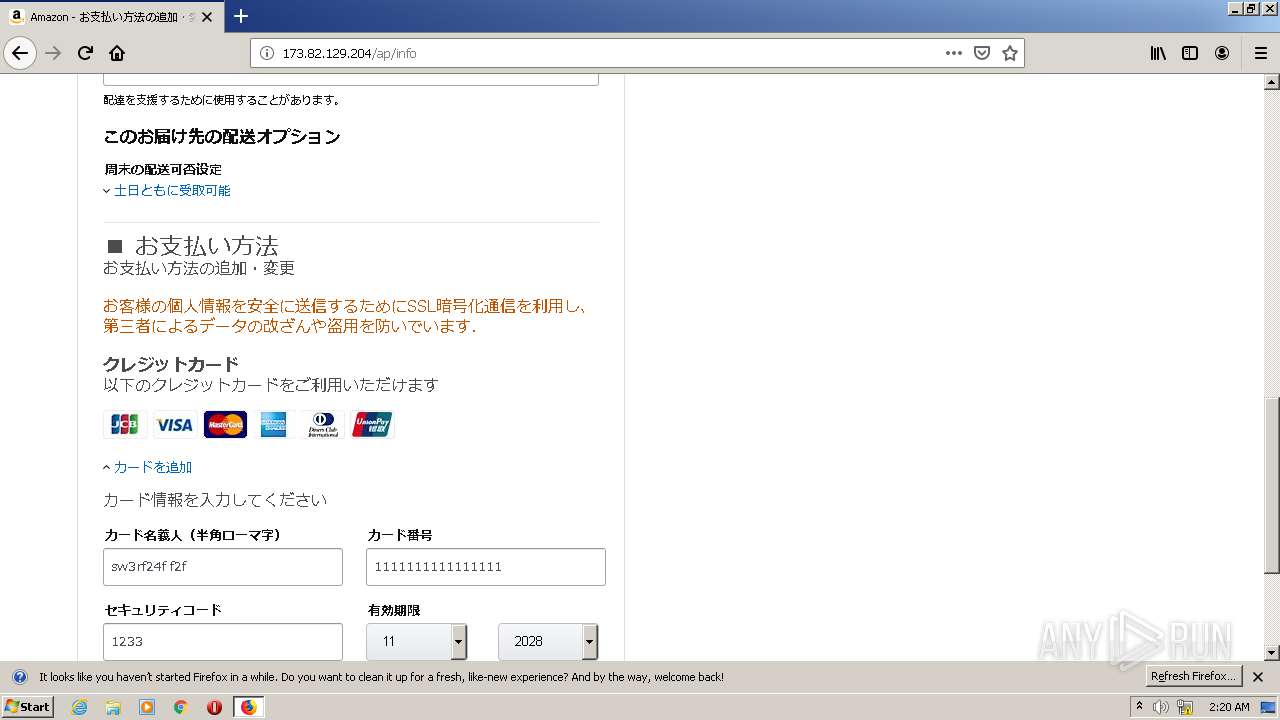
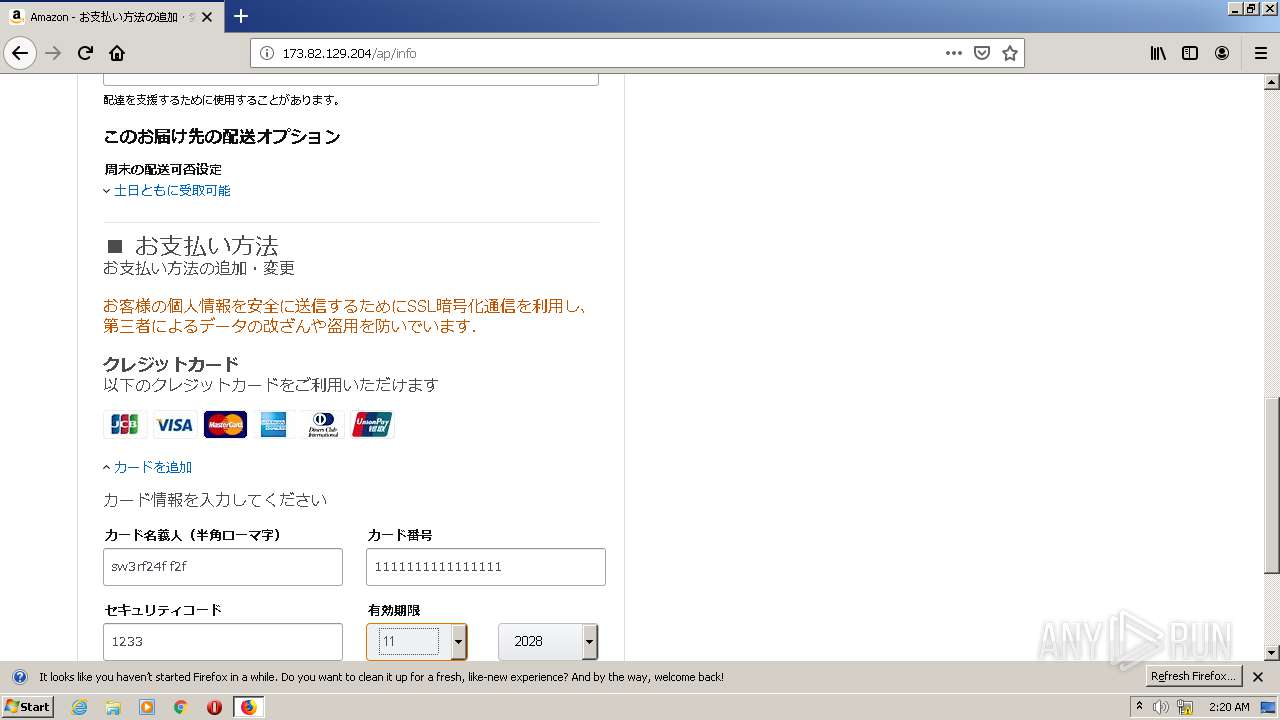
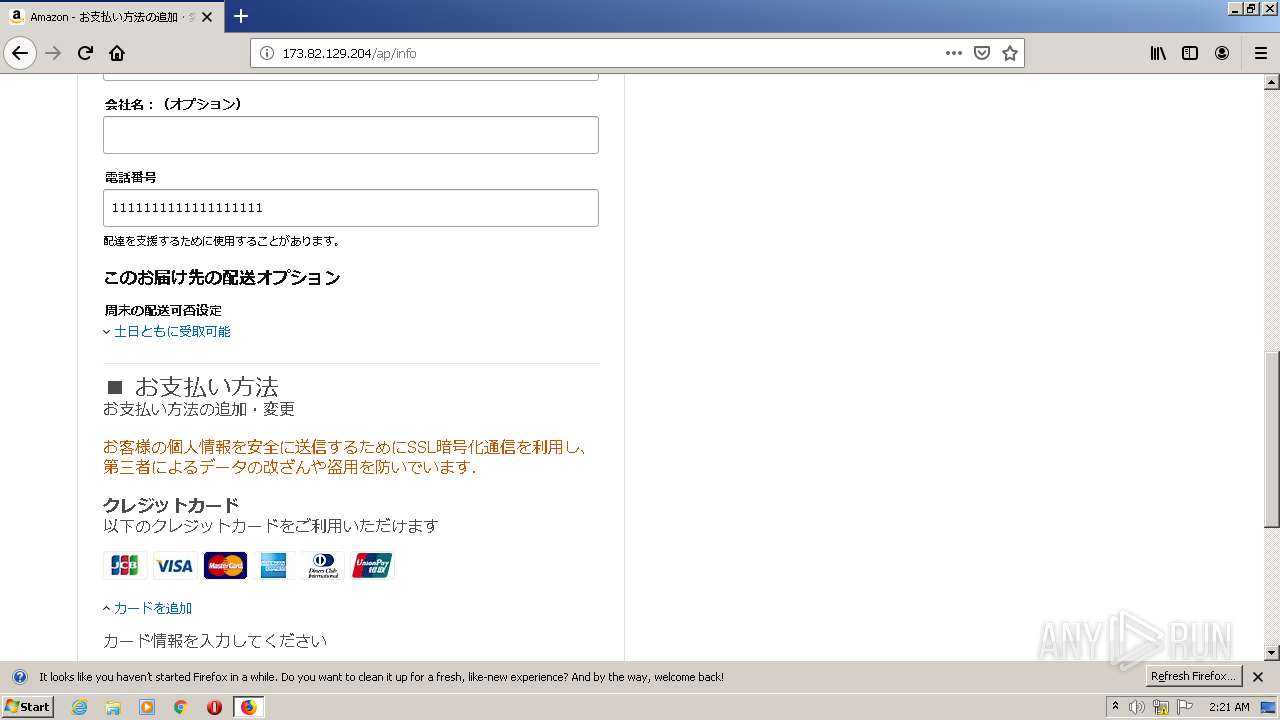
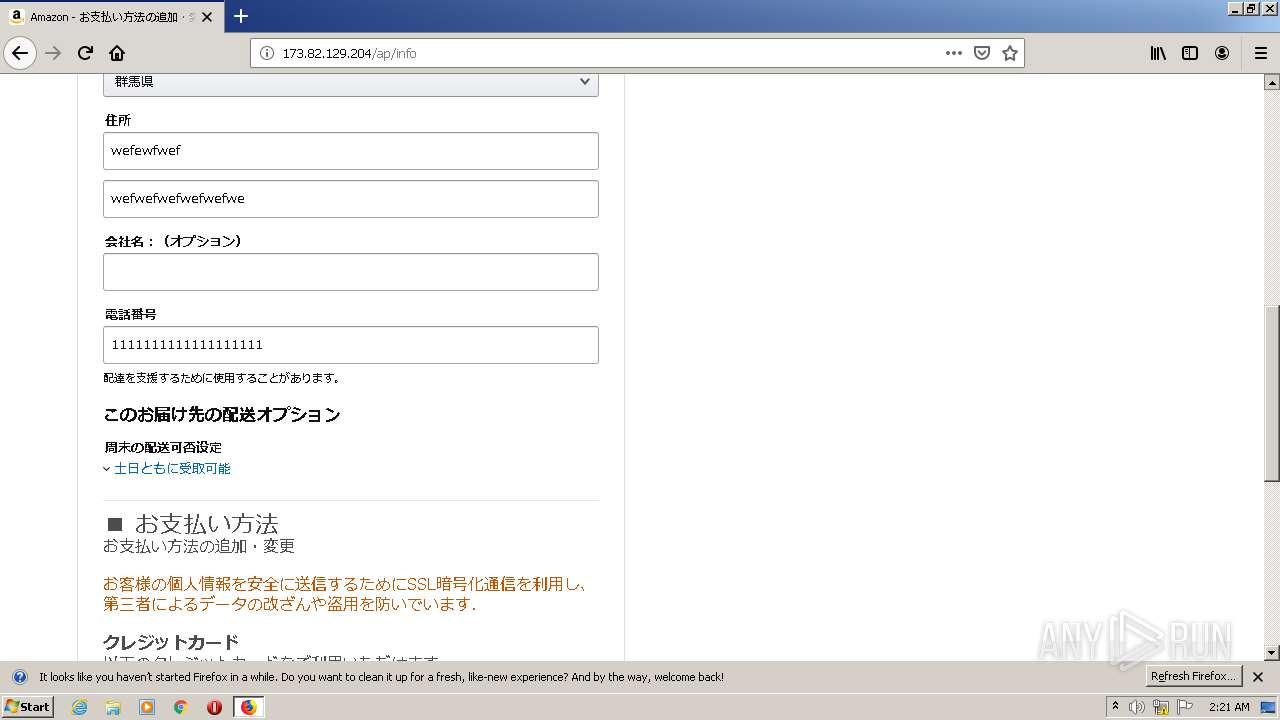
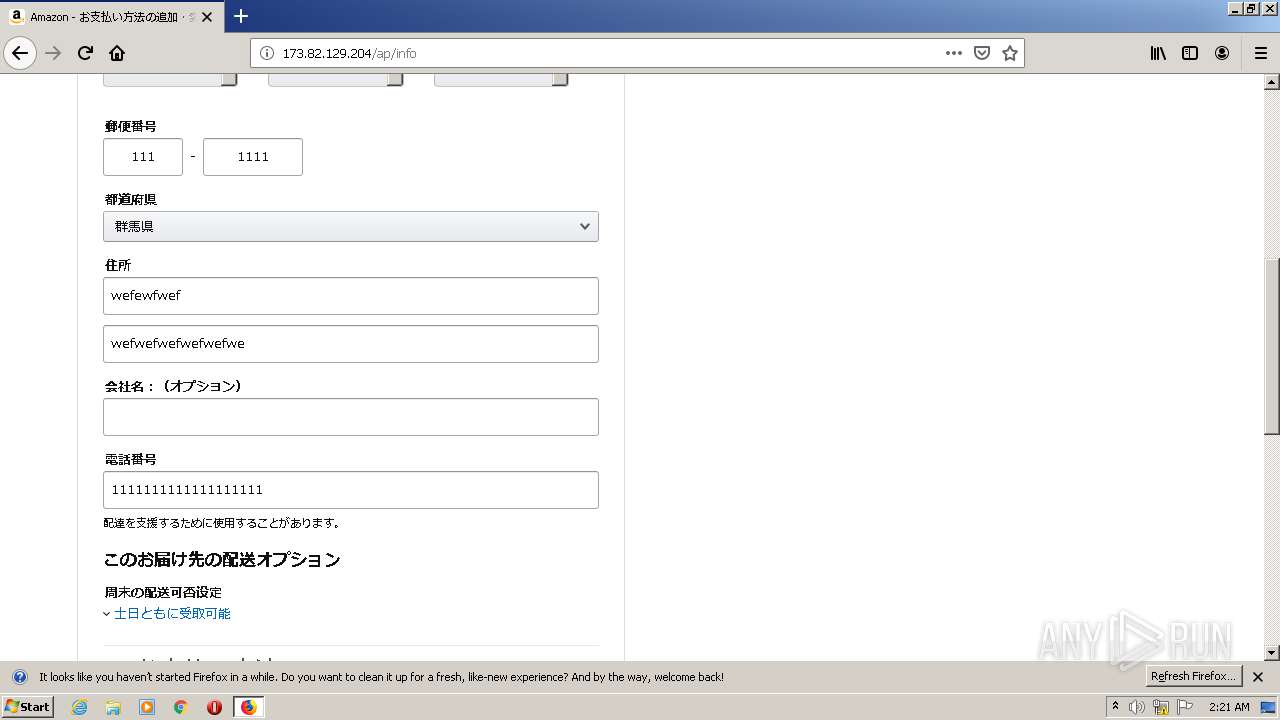
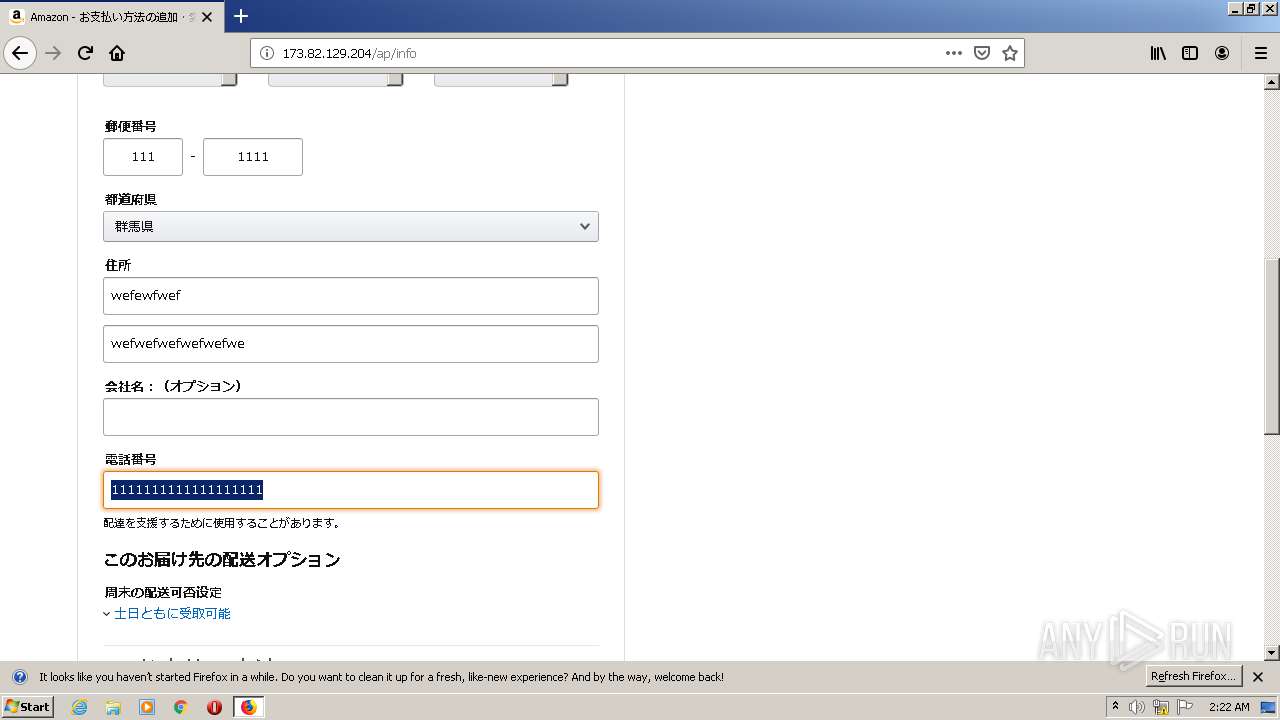
3320 | firefox.exe | GET | 200 | 173.82.129.204:80 | http://173.82.129.204/ap/info | US | html | 27.6 Kb | suspicious |
3320 | firefox.exe | GET | 200 | 173.82.129.204:80 | http://173.82.129.204/ap/signin/135-7905436-2439587 | US | html | 26.2 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3320 | firefox.exe | 173.82.129.204:80 | — | MULTACOM CORPORATION | US | suspicious |
3320 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
3320 | firefox.exe | 34.218.9.172:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
— | — | 99.86.5.42:443 | images-na.ssl-images-amazon.com | AT&T Services, Inc. | US | unknown |
3320 | firefox.exe | 100.20.6.188:443 | push.services.mozilla.com | — | US | unknown |
3320 | firefox.exe | 44.241.216.61:443 | shavar.services.mozilla.com | University of California, San Diego | US | unknown |
3320 | firefox.exe | 99.86.2.94:443 | content-signature-2.cdn.mozilla.net | AT&T Services, Inc. | US | unknown |
3320 | firefox.exe | 143.204.215.46:443 | tracking-protection.cdn.mozilla.net | — | US | suspicious |
3320 | firefox.exe | 100.20.233.245:80 | fls-fe.amazon.co.jp | — | US | unknown |
3320 | firefox.exe | 52.222.183.234:80 | www.amazon.co.jp | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
images-na.ssl-images-amazon.com |
| shared |
c.media-amazon.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
3 ETPRO signatures available at the full report